Cisco Email Security Appliance
Overview
Cisco Email Security Appliance (ESA) is an email gateway appliance that provides protection against spam, malware, viruses, and other email threats.
- Vendor: Cisco
- Supported environment: On Premise
- Version compatibility: from 14.X to 16.X
- Detection based on: Telemetry
- Supported application or feature: Email threat protection
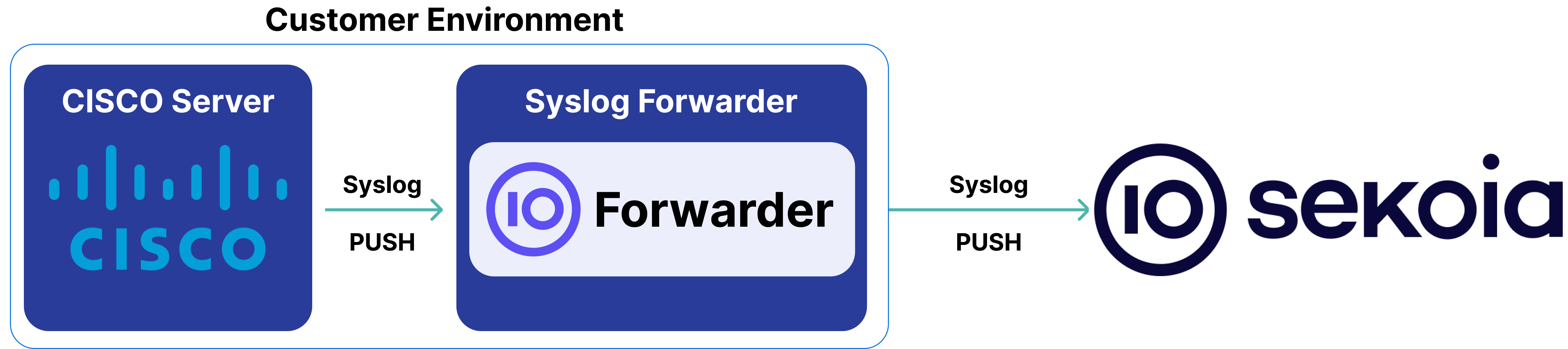
High-Level Architecture Diagram
- Type of integration: Outbound (PUSH to Sekoia.io)
- Schema
Specification
Prerequisites
- Resource:
- Self-managed syslog forwarder
- Network:
- Outbound traffic allowed
- Permissions:
- Administrator or Root access to the Cisco Email Security Appliance
- Root access to the Linux server with the syslog forwarder
Transport Protocol/Method
- Indirect Syslog
Logs details
- Supported functionalities: See section Overview
- Supported type(s) of structure: CEF
- Supported verbosity level: Informational
Note
Log levels are based on the taxonomy of RFC5424. Adapt according to the terminology used by the editor.
Step-by-Step Configuration Procedure
Instructions on the 3rd Party Solution
Forward Cisco Email Security Appliance Logs to Sekoia.io
This setup guide will show you how to provide an integration between Cisco Email Security Appliance events and Sekoia.io.
Detailed Procedure:
- Enable Syslog Forwarding:
- Log in to your Cisco appliance
- Go to
System Administration > Log Subscriptions - In
Add Log Subscription, selectConsolidated Event Logsas the log type - Select the fields that you want in the consolidated event logs
- In
Retrieval Method, checkSyslog Pushand fill the form with the IP address and the port of your log concentrator - Submit and commit your changes
Instruction on Sekoia
Configure Your Intake
This section will guide you through creating the intake object in Sekoia, which provides a unique identifier called the "Intake key." The Intake key is essential for later configuration, as it references the Community, Entity, and Parser (Intake Format) used when receiving raw events on Sekoia.
- Go to the Sekoia Intake page.
- Click on the
+ New Intakebutton at the top right of the page. - Search for your Intake by the product name in the search bar.
- Give it a Name and associate it with an Entity (and a Community if using multi-tenant mode).
- Click on
Create.
Note
For more details on how to use the Intake page and to find the Intake key you just created, refer to this documentation.
Configure a forwarder
To forward events using syslog to Sekoia.io, you need to update the syslog header with the intake key you previously created. Here is an example of your message before the forwarder
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG RAW_MESSAGE
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG [SEKOIA@53288 intake_key=\"YOUR_INTAKE_KEY\"] RAW_MESSAGE
To achieve this you can:
- Use the Sekoia.io forwarder which is the official supported way to collect data using the syslog protocol in Sekoia.io. In charge of centralizing data coming from many equipments/sources and forwarding them to Sekoia.io with the apporpriated format, it is a prepackaged option. You only have to provide your intake key as parameter.
- Use your own Syslog service instance. Maybe you already have an intance of one of these components on your side and want to reuse it in order to centralize data before forwarding them to Sekoia.io. When using this mode, you have to configure and maintain your component in order to respect the expected Sekoia.io format.
Warning
Only the Sekoia.io forwarder is officially supported. Other options are documented for reference purposes but do not have official support.
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
CEF:0|Cisco|C300V Secure Email Gateway Virtual|16.0.2-112|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=0c5a26da-3a9d-46ac-bbbb-11404914a72c ESAMID=11111111 ESAICID=22222222 ESADCID=3333333 cs4Label=ExternalMsgID cs4='<11111111111111111111111111111111111111@mail.example.org>' src=52.101.167.81 shost=mailer.example.org ESAAVVerdict=NEGATIVE ESAAMPVerdict=UNKNOWN cfp1Label=SBRSScore cfp1=4.2 suser=john.doe@example.org cs2Label=SenderCountry cs2=France ESASPFVerdict={'mailfrom': {'result': 'Pass', 'sender': 'john.doe@example.org'}, 'helo': {'result': 'Pass', 'sender': 'postmaster@example.org'}, 'pra': {'result': 'None', 'sender': 'john.doe@example.org'}} msg='My Subject' duser=jane.doe@example.org ESAAttachmentDetails={'image.png': {'AMP':
CEF:0|Cisco|C390 Email Security Appliance|14.2.2-004|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=FFFFFFFFFFFF-AAAAAAAAAAA ESAMID=111111 ESAICID=2222222 ESADCID=444444 ESAAMPVerdict=UNKNOWN ESAASVerdict=NEGATIVE ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Fri Jun 23 15:56:47 2023 ESADKIMVerdict=pass ESADMARCVerdict=Skipped dvc=5.6.7.8 ESAAttachmentDetails={"sreenshot.jpg": {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b'}}, "schermata.jpg": {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': ['01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b', '01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b', '01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b']}}, "Capture d'\xc3\xa9cran.jpg": {'BodyScanner': {}}, "Capture d'\xc3\xa9cran 2.jpg": {'BodyScanner': {}}} ESAFriendlyFrom="John Doe" <john.doe@example.org> ESAGMVerdict=NEGATIVE startTime=Fri Jun 23 15:56:46 2023 deviceInboundInterface=IncomingMail deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=john.doe@example.org cs1Label=MailPolicy cs1=AdresseGenerique cs2Label=SenderCountry cs2=Italy ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<aaaaaaaaaaaa$bbbbbbbb$cccccccc$@example.org>' ESAMsgSize=340614 ESAOFVerdict=NEGATIVE duser=jane.doe@example.com ESAHeloDomain=smtp.smtpout.example.org ESAHeloIP=5.6.7.8 cfp1Label=SBRSScore cfp1=3.5 ESASDRDomainAge=30 days (or greater) cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Neutral ESASPFVerdict={'mailfrom': {'result': 'Pass', 'sender': 'john.doe@example.org'}, 'helo': {'result': 'Pass', 'sender': 'postmaster@smtp.smtpout.example.org'}, 'pra': {'result': 'None', 'sender': 'john.doe@example.org'}} sourceHostName=smtp.smtpout.example.org ESASenderGroup=UNKNOWNLIST sourceAddress=1.2.3.4 msg='My subject' ESAURLDetails={'http://schemas.microsoft.com/office/2004/12/omml': {'WbrsScore': 9.1999999999999993}, 'http://www.w3.org/TR/REC-html40': {'WbrsScore': 9.1999999999999993}}
CEF:0|Cisco|C300V Email Security Virtual Appliance|13.0.0-392|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=4202A33F31B0BAAB537A-FBD06D401234 ESAMID=1251793 ESAICID=7186532 ESADCID=925893 ESAASVerdict=NEGATIVE ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Mon May 11 16:56:58 2020 ESADLPVerdict=NOT_EVALUATED ESADMARCVerdict=Skipped dvc=1.2.3.4 ESAAttachmentDetails={'resume.docx': {'AMP': {'Verdict': 'MALICIOUS', 'fileHash': 'b26a1d694a9cebd742cfa5d09e5f5e4697f522cc12c2e9f23638c1078bb7b0c2'}, 'BodyScanner': {}}} ESAFriendlyFrom=senderexample@example.com ESAGMVerdict=NOT_EVALUATED startTime=Mon May 11 16:56:56 2020 deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=senderexample@example.com cs1Label=MailPolicy cs1=remove_webmail_quota_spam cs2Label=SenderCountry cs2=Spain ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<ADR4500000227856433302E0EC2F783B1EEAA4F2E836DF8C5DBD@MAILERP.EXAMPLE.COM>' ESAOFVerdict=NEGATIVE duser=example@otherexample.com ESAHeloDomain=mail.example.com ESAHeloIP=1.2.3.4 cfp1Label=SBRSScore cfp1=3.5 ESASDRDomainAge=9 years 6 months 21 days cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Weak ESASPFVerdict=None sourceHostName=mailhost.example.es ESASenderGroup=UNKNOWNLIST sourceAddress=1.2.3.4 msg='A cool subject 123' ESATLSInCipher=ECDHE-RSA-AES256-GCM-SHA384 ESATLSInConnStatus=Success ESATLSInProtocol=TLSv1.2 ESATLSOutCipher=ECDHE-RSA-AES256-GCM-SHA384 ESATLSOutConnStatus=Success ESATLSOutProtocol=TLSv1.2
CEF:0|Cisco|C300V Email Security Virtual Appliance|13.0.0-252|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=420D4F36AAEBC0093B4F-B9E72189A021 ESAMID=4631 ESAAMPVerdict=SKIPPED ESAASVerdict=NEGATIVE ESAAVVerdict=NEGATIVE ESACFVerdict=MATCH ESADCID=66096 endTime=Tue Aug 13 15:15:48 2019 ESADKIMVerdict=pass ESADLPVerdict=NOT_EVALUATED ESADMARCVerdict=pass dvc=3.4.5.6 ESAAttachmentDetails={'presentation.pptx': {'AMP': {'Verdict': 'LOWRISK', 'fileHash': 'e4a4f9b7c4b4c7fb62b3df3c7e9e05811dc52c38eb8b76d3847f41ef299399e4'}, 'BodyScanner': {}}} ESAFriendlyFrom=no-reply@example.org ESAGMVerdict=NEGATIVE ESAICID=36050 startTime=Tue Aug 13 15:15:45 2019 deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=no-reply@example.org cs1Label=MailPolicy cs1=DEFAULT cs2Label=SenderCountry cs2=United States ESAMFVerdict=MATCH act=BOUNCED ESAFinalActionDetails=5.1.0 - Unknown address error cs4Label=ExternalMsgID cs4='<5d528dcf33830_812b56878564dc@ip-10-22-10-56.mail>' ESAOFVerdict=NEGATIVE duser=john.doe@example.org ESAHeloDomain=mail.example.orgm ESAHeloIP=10.0.0.0 cfp1Label=SBRSScore cfp1=0.9 ESASDRDomainAge=9 years 3 months 14 days cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Neutral ESASPFVerdict=SoftFail sourceHostName=esa1.hc3033-47.iphmx.com ESASenderGroup=GREYLIST sourceAddress=1.2.3.4 msg=Cisco=20Advanced=20Phishing=20Protection=20System=20Notification=20for=20bce-demo ESATLSInCipher=ECDHE-RSA-AES128-GCM-SHA256 ESATLSInConnStatus=Success ESATLSInProtocol=TLSv1.2 ESATLSOutCipher=ECDHE-RSA-AES256-SHA384 ESATLSOutConnStatus=Success ESATLSOutProtocol=TLSv1.2 ESAURLDetails={'https://bce-demo.appc.cisco.com/sensors/a7b04388-0f6e-11e9-8def-0242ac110002': {'Category': 'Computers and Internet', 'WbrsScore': '7.3'}, 'http://mandrill.appc.cisco.com/track/open.php?u=30372747&id=d57275a6c9df40418a90fd977e3bf506': {'Category': 'Computers and Internet', 'WbrsScore': '7.3'}} deviceInboundInterface=IncomingMail
CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=254be28187994bc7a37f496ceac54edd ESAMID=11111111 ESAICID=333333 ESADCID=2222222 ESAAMPVerdict=NOT_EVALUATED ESAASVerdict=NOT_EVALUATED ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Wed Mar 1 19:02:03 2023 dvc=3.4.5.6 ESAAttachmentDetails={'resume.pdf': {'AMP': {'Verdict': 'HIGHRISK', 'fileHash': 'f41c7c5d8e3b3c2b5d5b787bc5e5f9e5e5c23d60933a24d8c36df3847c61ef1'}, 'BodyScanner': {}}} ESAFriendlyFrom=no-reply@example.org ESAGMVerdict=NOT_EVALUATED startTime=Wed Mar 1 19:02:03 2023 deviceOutboundInterface=OutgoingMail deviceDirection=1 ESAMailFlowPolicy=RELAY suser=no-reply@example.org cs1Label=MailPolicy cs1=RestrictionEmetteur cs2Label=SenderCountry cs2=not enabled ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<11111111.2222222222222222222.JavaMail.ccccccccccc@dddddddddddddddd>' ESAMsgSize=3762 ESAOFVerdict=NOT_EVALUATED duser=john.doe@example.org ESAHeloDomain=mail.example.org ESAHeloIP=10.0.0.0 ESAReplyTo=no-reply@example.org cfp1Label=SBRSScore cfp1=not enabled sourceHostName=unknown ESASenderGroup=RELAYLIST sourceAddress=1.2.3.4 msg='\=?UTF-8?Q?Nice to Meet you?\='
CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=254be28187994bc7a37f496ceac54edd ESAMID=11111111 ESAICID=333333 ESADCID=2222222 ESAAMPVerdict=NOT_EVALUATED ESAASVerdict=NOT_EVALUATED ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Wed Mar 1 19:02:03 2023 dvc=3.4.5.6 ESAAttachmentDetails={'invoice.pdf': {'AMP': {'Verdict': 'LOWRISK', 'fileHash': '01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b'}, 'BodyScanner': {}}} ESAFriendlyFrom=JOHN DOE <john.doe@example.com> ESAGMVerdict=NOT_EVALUATED startTime=Wed Mar 1 19:02:03 2023 deviceOutboundInterface=OutgoingMail deviceDirection=1 ESAMailFlowPolicy=RELAY suser=veuillez-ne-pas-repondre@example.org cs1Label=MailPolicy cs1=RestrictionEmetteur cs2Label=SenderCountry cs2=not enabled ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<11111111111111111111111111111@ddddddd>' ESAMsgSize=111066 ESAOFVerdict=NOT_EVALUATED duser=jane.doe@example.org ESAHeloDomain=mail.example.org ESAHeloIP=10.0.0.0 cfp1Label=SBRSScore cfp1=not enabled sourceHostName=unknown ESASenderGroup=RELAYLISTTELEDEP sourceAddress=1.2.3.4 msg='\=?utf-8?Q?For the meeting?\='
CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=254be28187994bc7a37f496ceac54edd ESAMID=11111111 ESAICID=333333 ESADCID=2222222 ESAAMPVerdict=LOW_RISK ESAASVerdict=NEGATIVE ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Wed Mar 1 19:02:04 2023 ESADMARCVerdict=pass dvc=3.4.5.6 ESAAttachmentDetails={'invoice.pdf': {'AMP': {'Verdict': 'LOWRISK', 'fileHash': '01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b'}, 'BodyScanner': {}}} ESAFriendlyFrom=John Doe <john.doe@example.org> ESAGMVerdict=NEGATIVE startTime=Wed Mar 1 19:02:02 2023 deviceInboundInterface=IncomingMail deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=john.doe@example.org cs1Label=MailPolicy cs1=DEFAULT cs2Label=SenderCountry cs2=Netherlands ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<44444444444444444444444444444444444444@77777777777777777777777777.EXAMPLE.COM>' ESAMsgSize=1197675 ESAOFVerdict=NEGATIVE duser=jane.doe@example.fr ESAHeloDomain=mail.example.org ESAHeloIP=10.0.0.0 cfp1Label=SBRSScore cfp1=3.5 ESASDRDomainAge=30 days (or greater) cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Neutral ESASPFVerdict={'mailfrom': {'result': 'Pass', 'sender': 'john.doe@example.org'}, 'helo': {'result': 'Pass', 'sender': 'postmaster@example.org'}, 'pra': {'result': 'None', 'sender': 'john.doe@example.org'}} sourceHostName=outbound.example.com ESASenderGroup=UNKNOWNLIST sourceAddress=1.2.3.4 msg='Perso' ESAURLDetails={'https://tinyurl.es/tbdra': {'WbrsScore': 9.1999999999999993, 'ExpandedUrl': 'https://facebook.com/u/john.doe'}, 'www.twitter.com': {'WbrsScore': 0.0, 'AttachmentWithUrl': 'My document.pdf'}, 'https://tiktok.com': {'WbrsScore': 4.9000000000000004}}
CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=254be28187994bc7a37f496ceac54edd ESAMID=11111111 ESAICID=333333 ESADCID=2222222 ESAAMPVerdict=UNKNOWN ESAASVerdict=NEGATIVE ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Wed Mar 1 19:02:05 2023 ESADKIMVerdict=pass ESADMARCVerdict=pass dvc=3.4.5.6 ESAAttachmentDetails={'unknown': {'AMP': {'Verdict': ['FILE UNKNOWN'], 'fileHash': ['87428fc522803d31065e7bce3cf03fe475096631e5e07bbd7a0fde60c4cf25c7']}}} ESAFriendlyFrom=John Doe <john.doe@example.org> ESAGMVerdict=NEGATIVE startTime=Wed Mar 1 19:02:02 2023 deviceInboundInterface=IncomingMail deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=john.doe@example.org cs1Label=MailPolicy cs1=DEFAULT cs2Label=SenderCountry cs2=United States ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<111111111111111111111@mal.example.org>' ESAMsgSize=73748 ESAOFVerdict=NEGATIVE duser=jane.doe@example.org ESAHeloDomain=mail.example.org ESAHeloIP=10.0.0.0 cfp1Label=SBRSScore cfp1=3.5 ESASDRDomainAge=30 days (or greater) cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Neutral ESASPFVerdict={'mailfrom': {'result': 'Pass', 'sender': 'john.doe@example.org'}, 'helo': {'result': 'Pass', 'sender': 'postmaster@example.org'}, 'pra': {'result': 'None', 'sender': 'no-reply@example.org'}} sourceHostName=outboun
CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=254be28187994bc7a37f496ceac54edd ESAMID=11111111 ESAICID=333333 ESAAMPVerdict=FA_PENDING ESAASVerdict=BULK_MAIL ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Wed Mar 1 19:01:47 2023 ESADKIMVerdict=pass ESADMARCVerdict=Skipped dvc=3.4.5.6 ESAAttachmentDetails={'twitter.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b'}, 'BodyScanner': {}}, 'appointement.ics': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '87428fc522803d31065e7bce3cf03fe475096631e5e07bbd7a0fde60c4cf25c7'}}, 'icon-linkedin.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': 'a3a5e715f0cc574a73c3f9bebb6bc24f32ffd5b67b387244c2c909da779a1478'}, 'BodyScanner': {}}, 'fond-gris.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '8d74beec1be996322ad76813bafb92d40839895d6dd7ee808b17ca201eac98be'}, 'BodyScanner': {}}, 'bg-desktop-default-header.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '768c71d785bf6bbbf8c4d6af6582041f2659027140a962cd0c55b11eddfd5e3d'}, 'BodyScanner': {}}} ESAFriendlyFrom=John Doe <john.doe@example.org> ESAGMVerdict=POSITIVE startTime=Wed Mar 1 19:01:45 2023 deviceInboundInterface=IncomingMail deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=john.doe@example.org cs1Label=MailPolicy cs1=DEFAULT cs2Label=SenderCountry cs2=France ESAMFVerdict=NO_MATCH act=DQ ESAFinalActionDetails=Message held temporarily in Delay Quarantine cs4Label=ExternalMsgID cs4='<111111111111111111111@mal.example.org>' ESAMsgSize=174552 ESAOFVerdict=NEGATIVE duser=jane.doe@example.org ESAHeloDomain=mail.example.org ESAHeloIP=10.0.0.0 cfp1Label=SBRSScore cfp1=5.4 ESASDRDomainAge=30 days (or greater) cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Neutral ESASPFVerdict={'mailfrom': {'result': 'Pass', 'sender': 'john.doe@example.org'}, 'helo': {'result': 'Pass', 'sender': 'postmaster@example.org'}, 'pra': {'result': 'None', 'sender': 'no-reply@example.org'}} sourceHostName=outbound.example.com ESASenderGroup=UNKNOWNLIST sourceAddress=1.2.3.4 msg='Validation of your request' ESAURLDetails={}
CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=254be28187994bc7a37f496ceac54edd ESAMID=11111111 ESADCID=2222222 ESAStatus=QUEUED
CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=00F66XXXX-FCH2025V2LQ ESAMID=351452154 ESAICID=317589723 ESADCID=192175459 ESADLPVerdict=NOT EVALUATED ESAASVerdict=NOT_EVALUATED ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Mon Jun 13 08:02:06 2023 ESADKIMVerdict=pass ESADMARCVerdict=pass dvc=5.6.7.8 ESAAttachmentDetails={'bob.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '2062932a5c017252038b001b14e1dfd09501742faeb7275da8e031eacfa963ed'}, 'BodyScanner': {}}, 'Signature Jean Dupont.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': 'a0e121e017afed94380de0658e51f4bed14f6cffc3d7f2026f5c3cafcf8273f4'}, 'BodyScanner': {}}, 'FICHE.pdf': {'AMP': {'Verdict': 'LOWRISK', 'fileHash': 'e4b2d60cea9c09a0871d0f94fe9ca38010ef8e552f67e7cdec7489d2a1818354'}, 'BodyScanner': {}}} ESAFriendlyFrom=Marc Dupont <m.dupont@corp.fr> ESAGMVerdict=NEGATIVE startTime=Mon Jun 13 08:02:04 2023 deviceInboundInterface=IncomingMail deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=m.dupont@corp.fr cs1Label=MailPolicy cs1=DEFAULT cs2Label=SenderCountry cs2=Switzerland ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<17f42d91-1908-aecb-adfd-a6e9c92e623e@corp.fr>' ESAMsgSize=418081 ESAOFVerdict=POSITIVE duser=evil@corp.fr ESAHeloDomain=example.org ESAHeloIP=192.168.10.244 cfp1Label=SBRSScore cfp1=None ESASDRDomainAge=30 days (or greater) cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Neutral ESASPFVerdict={'mailfrom': {'result': 'Pass', 'sender': 'lol@evil.fr'}, 'helo': {'result': 'None', 'sender': 'postmaster@example.org'}, 'pra': {'result': 'None', 'sender': 'm.dupont@corp.fr'}} sourceHostName=example.org ESASenderGroup=SUSPECTLIST sourceAddress=1.2.3.4 msg='\=?UTF-8?Q?N\=c2\=b0_CORP\= \=?UTF-8?Q?020?\='
CEF:0|Cisco|C600V Email Security Virtual Appliance|15.0.0-104|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=42306A91288AD54F334B-220D2F3E82D1 ESAMID=75132386 ESAICID=9038012 ESADCID=3259121 ESAAMPVerdict=UNKNOWN ESAASVerdict=NEGATIVE ESAAVVerdict=NEGATIVE ESACFVerdict=MATCH end=Wed Aug 6 07:46:00 2025 ESADLPVerdict=NOT_EVALUATED dvc=1.2.3.4 ESAAttachmentDetails={'image.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '6b86b273ff34fce19d6b804eff5a3f5747ada4eaa22f1d49c01e52ddb7875b4b'}, 'BodyScanner': {}}, 'Test.pdf': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': 'd4735e3a265e16eee03f59718b9b5d03019c07d8b6c51f90da3a666eec13ab35'}, 'BodyScanner': {}}} ESAFriendlyFrom=From <sender@sender-domain.com> ESAGMVerdict=NEGATIVE start=Wed Aug 6 07:45:58 2025 deviceInboundInterface=incoming deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=sender@sender-domain.com cs1Label=MailPolicy cs1=Policy cs2Label=SenderCountry cs2=not applicable ESAMFVerdict=MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<ABC@PARP264MB5994.FRAP264.PROD.OUTLOOK.COM>' ESAMsgSize=798896 ESAOFVerdict=NEGATIVE duser=dest1@reception.com;dest2@reception.com ESAHeloDomain=example.domain ESAHeloIP=1.2.3.4 cfp1Label=SBRSScore cfp1=rfc1918 shost=sourcehost ESASenderGroup=SEG src=1.2.3.4 msg='Subject'
CEF:0|Cisco|C300V Secure Email Gateway Virtual|16.0.0-054|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=111111111111111111111111111111111 ESAMID=15798304 ESADCID=9624426 end=Wed Mar 12 11:02:25 2025 ESADLPVerdict=NOT_EVALUATED ESAAttachmentDetails={'winmail.dat': {'BodyScanner': {}}} ESAGMVerdict=NOT_EVALUATED deviceDirection=0 cs1Label=MailPolicy cs1=DEFAULT ESAMFVerdict=NOT_EVALUATED act=DELIVERED ESAOFVerdict=NOT_EVALUATED ESATLSOutCipher=ECDHE-RSA-AES256-GCM-SHA384 ESATLSOutConnStatus=Success ESATLSOutProtocol=TLSv1.2 ESAAMPVerdict=LOW_RISK ESAASVerdict=NOT_EVALUATED ESAAVVerdict=NOT_EVALUATED ESACFVerdict=NOT_EVALUATED ESALogHeaders={'X-ThreatScanner-Verdict': ['Negative']}
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake Cisco ESA. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x Cisco ESA on ATT&CK Navigator
Bazar Loader DGA (Domain Generation Algorithm)
Detects Bazar Loader domains based on the Bazar Loader DGA
- Effort: elementary
Burp Suite Tool Detected
Burp Suite is a cybersecurity tool. When used as a proxy service, its purpose is to intercept packets and modify them to send them to the server. Burp Collaborator is a network service that Burp Suite uses to help discover many kinds of vulnerabilities (vulnerabilities scanner).
- Effort: intermediate
CVE-2020-0688 Microsoft Exchange Server Exploit
Detects the exploitation of CVE-2020-0688. The POC exploit a .NET serialization vulnerability in the Exchange Control Panel (ECP) web page. The vulnerability is due to Microsoft Exchange Server not randomizing the keys on a per-installation basis resulting in them using the same validationKey and decryptionKey values. With knowledge of these, values an attacker can craft a special viewstate to use an OS command to be executed by NT_AUTHORITY\SYSTEM using .NET deserialization. To exploit this vulnerability, an attacker needs to leverage the credentials of an account it had already compromised to authenticate to OWA.
- Effort: elementary
CVE-2020-17530 Apache Struts RCE
Detects the exploitation of the Apache Struts RCE vulnerability (CVE-2020-17530).
- Effort: intermediate
CVE-2021-20021 SonicWall Unauthenticated Administrator Access
Detects the exploitation of SonicWall Unauthenticated Admin Access.
- Effort: advanced
CVE-2021-20023 SonicWall Arbitrary File Read
Detects Arbitrary File Read, which can be used with other vulnerabilities as a mean to obtain outputs generated by attackers, or sensitive data.
- Effort: advanced
CVE-2021-22893 Pulse Connect Secure RCE Vulnerability
Detects potential exploitation of the authentication by-pass vulnerability that can allow an unauthenticated user to perform remote arbitrary file execution on the Pulse Connect Secure gateway. It is highly recommended to apply the Pulse Secure mitigations and seach for indicators of compromise on affected servers if you are in doubt over the integrity of your Pulse Connect Secure product.
- Effort: intermediate
Covenant Default HTTP Beaconing
Detects potential Covenant communications through the user-agent and specific urls
- Effort: intermediate
Cryptomining
Detection of domain names potentially related to cryptomining activities.
- Effort: master
Detect requests to Konni C2 servers
This rule detects requests to Konni C2 servers. These patterns come from an analysis done in 2022, September.
- Effort: elementary
Discord Suspicious Download
Discord is a messaging application. It allows users to create their own communities to share messages and attachments. Those attachments have little to no overview and can be downloaded by almost anyone, which has been abused by attackers to host malicious payloads.
- Effort: advanced
Download Files From Suspicious TLDs
Detects download of certain file types from hosts in suspicious TLDs
- Effort: master
Dynamic DNS Contacted
Detect communication with dynamic dns domain. This kind of domain is often used by attackers. This rule can trigger false positive in non-controlled environment because dynamic dns is not always malicious.
- Effort: master
EvilProxy Phishing Domain
Detects subdomains potentially generated by the EvilProxy adversary-in-the-middle phishing platform. Inspect the other subdomains of the domain to identify the landing page, and determine if the user submitted credentials. This rule has a small percentage of false positives on legitimate domains.
- Effort: intermediate
Exfiltration Domain
Detects traffic toward a domain flagged as a possible exfiltration vector.
- Effort: master
Koadic MSHTML Command
Detects Koadic payload using MSHTML module
- Effort: intermediate
Nimbo-C2 User Agent
Nimbo-C2 Uses an unusual User-Agent format in its implants.
- Effort: intermediate
Possible Malicious File Double Extension
Detects request to potential malicious file with double extension
- Effort: elementary
Potential Bazar Loader User-Agents
Detects potential Bazar loader communications through the user-agent
- Effort: elementary
Potential Lemon Duck User-Agent
Detects LemonDuck user agent. The format used two sets of alphabetical characters separated by dashes, for example "User-Agent: Lemon-Duck-[A-Z]-[A-Z]".
- Effort: elementary
ProxyShell Microsoft Exchange Suspicious Paths
Detects suspicious calls to Microsoft Exchange resources, in locations related to webshells observed in campaigns using this vulnerability.
- Effort: elementary
Raccoon Stealer 2.0 Legitimate Third-Party DLL Download URL
Detects Raccoon Stealer 2.0 malware downloading legitimate third-party DLLs from its C2 server. These legitimate DLLs are used by the information stealer to collect data on the compromised hosts.
- Effort: elementary
Remote Access Tool Domain
Detects traffic toward a domain flagged as a Remote Administration Tool (RAT).
- Effort: master
Remote Monitoring and Management Software - AnyDesk
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool AnyDesk.
- Effort: master
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
Sekoia.io EICAR Detection
Detects observables in Sekoia.io CTI tagged as EICAR, which are fake samples meant to test detection.
- Effort: master
Suspicious Download Links From Legitimate Services
Detects users clicking on Google docs links to download suspicious files. This technique was used a lot by Bazar Loader in the past.
- Effort: intermediate
Suspicious TOR Gateway
Detects suspicious TOR gateways. Gateways are often used by the victim to pay and decrypt the encrypted files without installing TOR. Tor intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: advanced
Suspicious URI Used In A Lazarus Campaign
Detects suspicious requests to a specific URI, usually on an .asp page. The website is often compromised.
- Effort: intermediate
TOR Usage Generic Rule
Detects TOR usage globally, whether the IP is a destination or source. TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
TrevorC2 HTTP Communication
Detects TrevorC2 HTTP communication based on the HTTP request URI and the user-agent.
- Effort: elementary
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Email gateway |
Cisco ESA logs many details on every handled message |
Mail server |
Cisco ESA logs many details on every handled message |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "CEF:0|Cisco|C300V Secure Email Gateway Virtual|16.0.2-112|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=0c5a26da-3a9d-46ac-bbbb-11404914a72c ESAMID=11111111 ESAICID=22222222 ESADCID=3333333 cs4Label=ExternalMsgID cs4='<11111111111111111111111111111111111111@mail.example.org>' src=52.101.167.81 shost=mailer.example.org ESAAVVerdict=NEGATIVE ESAAMPVerdict=UNKNOWN cfp1Label=SBRSScore cfp1=4.2 suser=john.doe@example.org cs2Label=SenderCountry cs2=France ESASPFVerdict={'mailfrom': {'result': 'Pass', 'sender': 'john.doe@example.org'}, 'helo': {'result': 'Pass', 'sender': 'postmaster@example.org'}, 'pra': {'result': 'None', 'sender': 'john.doe@example.org'}} msg='My Subject' duser=jane.doe@example.org ESAAttachmentDetails={'image.png': {'AMP':\n",
"event": {
"severity": 5
},
"cisco": {
"esa": {
"authentication": {
"spf": {
"verdict": "{\"helo\":{\"result\":\"Pass\",\"sender\":\"postmaster@example.org\"},\"mailfrom\":{\"result\":\"Pass\",\"sender\":\"john.doe@example.org\"},\"pra\":{\"result\":\"None\",\"sender\":\"john.doe@example.org\"}}"
}
},
"delivery": {
"connection_id": "3333333"
},
"injection": {
"connection_id": "22222222"
},
"protection": {
"amp": {
"verdict": "UNKNOWN"
},
"antivirus": {
"verdict": "NEGATIVE"
}
}
}
},
"email": {
"from": {
"address": [
"john.doe@example.org"
]
},
"local_id": "11111111",
"message_id": "11111111111111111111111111111111111111@mail.example.org",
"subject": "My Subject",
"to": {
"address": [
"jane.doe@example.org"
]
}
},
"host": {
"hostname": "mailer.example.org",
"id": "0c5a26da-3a9d-46ac-bbbb-11404914a72c",
"name": "mailer.example.org"
},
"observer": {
"type": "C300V Secure Email Gateway Virtual",
"vendor": "Cisco",
"version": "16.0.2-112"
},
"related": {
"hosts": [
"mailer.example.org"
],
"ip": [
"52.101.167.81"
]
},
"source": {
"address": "52.101.167.81",
"ip": "52.101.167.81"
}
}
{
"message": "CEF:0|Cisco|C390 Email Security Appliance|14.2.2-004|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=FFFFFFFFFFFF-AAAAAAAAAAA ESAMID=111111 ESAICID=2222222 ESADCID=444444 ESAAMPVerdict=UNKNOWN ESAASVerdict=NEGATIVE ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Fri Jun 23 15:56:47 2023 ESADKIMVerdict=pass ESADMARCVerdict=Skipped dvc=5.6.7.8 ESAAttachmentDetails={\"sreenshot.jpg\": {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b'}}, \"schermata.jpg\": {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': ['01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b', '01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b', '01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b']}}, \"Capture d'\\xc3\\xa9cran.jpg\": {'BodyScanner': {}}, \"Capture d'\\xc3\\xa9cran 2.jpg\": {'BodyScanner': {}}} ESAFriendlyFrom=\"John Doe\" <john.doe@example.org> ESAGMVerdict=NEGATIVE startTime=Fri Jun 23 15:56:46 2023 deviceInboundInterface=IncomingMail deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=john.doe@example.org cs1Label=MailPolicy cs1=AdresseGenerique cs2Label=SenderCountry cs2=Italy ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<aaaaaaaaaaaa$bbbbbbbb$cccccccc$@example.org>' ESAMsgSize=340614 ESAOFVerdict=NEGATIVE duser=jane.doe@example.com ESAHeloDomain=smtp.smtpout.example.org ESAHeloIP=5.6.7.8 cfp1Label=SBRSScore cfp1=3.5 ESASDRDomainAge=30 days (or greater) cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Neutral ESASPFVerdict={'mailfrom': {'result': 'Pass', 'sender': 'john.doe@example.org'}, 'helo': {'result': 'Pass', 'sender': 'postmaster@smtp.smtpout.example.org'}, 'pra': {'result': 'None', 'sender': 'john.doe@example.org'}} sourceHostName=smtp.smtpout.example.org ESASenderGroup=UNKNOWNLIST sourceAddress=1.2.3.4 msg='My subject' ESAURLDetails={'http://schemas.microsoft.com/office/2004/12/omml': {'WbrsScore': 9.1999999999999993}, 'http://www.w3.org/TR/REC-html40': {'WbrsScore': 9.1999999999999993}}\n",
"event": {
"action": "delivered",
"end": "2023-06-23T15:56:47Z",
"severity": 5,
"start": "2023-06-23T15:56:46Z"
},
"@timestamp": "2023-06-23T15:56:46Z",
"cisco": {
"esa": {
"authentication": {
"dkim": {
"verdict": "pass"
},
"dmarc": {
"verdict": "Skipped"
},
"spf": {
"verdict": "{\"helo\":{\"result\":\"Pass\",\"sender\":\"postmaster@smtp.smtpout.example.org\"},\"mailfrom\":{\"result\":\"Pass\",\"sender\":\"john.doe@example.org\"},\"pra\":{\"result\":\"None\",\"sender\":\"john.doe@example.org\"}}"
}
},
"delivery": {
"connection_id": "444444"
},
"email": {
"message_size": "340614"
},
"friendly": {
"from": "\"John Doe\" <john.doe@example.org>"
},
"helo": {
"domain": "smtp.smtpout.example.org",
"ip": "5.6.7.8"
},
"injection": {
"connection_id": "2222222"
},
"protection": {
"amp": {
"verdict": "UNKNOWN"
},
"antivirus": {
"verdict": "NOT_EVALUATED"
},
"graymail": {
"verdict": "NEGATIVE"
},
"spam": {
"verdict": "NEGATIVE"
}
},
"sender_group": "UNKNOWNLIST",
"source": {
"domain": {
"age": "30 days (or greater)"
}
},
"url": [
"http://schemas.microsoft.com/office/2004/12/omml",
"http://www.w3.org/TR/REC-html40"
],
"url_domain": [
"schemas.microsoft.com",
"www.w3.org"
]
}
},
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "sreenshot.jpg"
}
},
{
"file": {
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "schermata.jpg"
}
},
{
"file": {
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "schermata.jpg"
}
},
{
"file": {
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "schermata.jpg"
}
},
{
"file": {
"name": "Capture d'\u00c3\u00a9cran.jpg"
}
},
{
"file": {
"name": "Capture d'\u00c3\u00a9cran 2.jpg"
}
}
],
"from": {
"address": [
"john.doe@example.org"
]
},
"local_id": "111111",
"message_id": "aaaaaaaaaaaa$bbbbbbbb$cccccccc$@example.org",
"subject": "My subject",
"to": {
"address": [
"jane.doe@example.com"
]
}
},
"host": {
"hostname": "smtp.smtpout.example.org",
"id": "FFFFFFFFFFFF-AAAAAAAAAAA",
"name": "smtp.smtpout.example.org"
},
"network": {
"direction": "inbound"
},
"observer": {
"ingress": {
"interface": {
"name": "IncomingMail"
}
},
"type": "C390 Email Security Appliance",
"vendor": "Cisco",
"version": "14.2.2-004"
},
"related": {
"hosts": [
"smtp.smtpout.example.org"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"rule": {
"name": "AdresseGenerique"
},
"server": {
"ip": "5.6.7.8"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "CEF:0|Cisco|C300V Email Security Virtual Appliance|13.0.0-392|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=4202A33F31B0BAAB537A-FBD06D401234 ESAMID=1251793 ESAICID=7186532 ESADCID=925893 ESAASVerdict=NEGATIVE ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Mon May 11 16:56:58 2020 ESADLPVerdict=NOT_EVALUATED ESADMARCVerdict=Skipped dvc=1.2.3.4 ESAAttachmentDetails={'resume.docx': {'AMP': {'Verdict': 'MALICIOUS', 'fileHash': 'b26a1d694a9cebd742cfa5d09e5f5e4697f522cc12c2e9f23638c1078bb7b0c2'}, 'BodyScanner': {}}} ESAFriendlyFrom=senderexample@example.com ESAGMVerdict=NOT_EVALUATED startTime=Mon May 11 16:56:56 2020 deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=senderexample@example.com cs1Label=MailPolicy cs1=remove_webmail_quota_spam cs2Label=SenderCountry cs2=Spain ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<ADR4500000227856433302E0EC2F783B1EEAA4F2E836DF8C5DBD@MAILERP.EXAMPLE.COM>' ESAOFVerdict=NEGATIVE duser=example@otherexample.com ESAHeloDomain=mail.example.com ESAHeloIP=1.2.3.4 cfp1Label=SBRSScore cfp1=3.5 ESASDRDomainAge=9 years 6 months 21 days cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Weak ESASPFVerdict=None sourceHostName=mailhost.example.es ESASenderGroup=UNKNOWNLIST sourceAddress=1.2.3.4 msg='A cool subject 123' ESATLSInCipher=ECDHE-RSA-AES256-GCM-SHA384 ESATLSInConnStatus=Success ESATLSInProtocol=TLSv1.2 ESATLSOutCipher=ECDHE-RSA-AES256-GCM-SHA384 ESATLSOutConnStatus=Success ESATLSOutProtocol=TLSv1.2",
"event": {
"action": "delivered",
"end": "2020-05-11T16:56:58Z",
"severity": 5,
"start": "2020-05-11T16:56:56Z"
},
"@timestamp": "2020-05-11T16:56:56Z",
"cisco": {
"esa": {
"authentication": {
"dmarc": {
"verdict": "Skipped"
}
},
"delivery": {
"connection_id": "925893"
},
"friendly": {
"from": "senderexample@example.com"
},
"helo": {
"domain": "mail.example.com",
"ip": "1.2.3.4"
},
"injection": {
"connection_id": "7186532"
},
"protection": {
"antivirus": {
"verdict": "NOT_EVALUATED"
},
"dlp": {
"verdict": "NOT_EVALUATED"
},
"graymail": {
"verdict": "NOT_EVALUATED"
},
"spam": {
"verdict": "NEGATIVE"
}
},
"sender_group": "UNKNOWNLIST",
"source": {
"domain": {
"age": "9 years 6 months 21 days"
}
}
}
},
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "b26a1d694a9cebd742cfa5d09e5f5e4697f522cc12c2e9f23638c1078bb7b0c2"
},
"name": "resume.docx"
}
}
],
"from": {
"address": [
"senderexample@example.com"
]
},
"local_id": "1251793",
"message_id": "ADR4500000227856433302E0EC2F783B1EEAA4F2E836DF8C5DBD@MAILERP.EXAMPLE.COM",
"subject": "A cool subject 123",
"to": {
"address": [
"example@otherexample.com"
]
}
},
"host": {
"hostname": "mailhost.example.es",
"id": "4202A33F31B0BAAB537A-FBD06D401234",
"name": "mailhost.example.es"
},
"network": {
"direction": "inbound"
},
"observer": {
"type": "C300V Email Security Virtual Appliance",
"vendor": "Cisco",
"version": "13.0.0-392"
},
"related": {
"hosts": [
"mailhost.example.es"
],
"ip": [
"1.2.3.4"
]
},
"rule": {
"name": "remove_webmail_quota_spam"
},
"server": {
"ip": "1.2.3.4"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"tls": {
"cipher": "ECDHE-RSA-AES256-GCM-SHA384",
"client": {
"supported_ciphers": [
"ECDHE-RSA-AES256-GCM-SHA384"
]
},
"established": true,
"version": "1.2",
"version_protocol": "tls"
}
}
{
"message": "CEF:0|Cisco|C300V Email Security Virtual Appliance|13.0.0-252|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=420D4F36AAEBC0093B4F-B9E72189A021 ESAMID=4631 ESAAMPVerdict=SKIPPED ESAASVerdict=NEGATIVE ESAAVVerdict=NEGATIVE ESACFVerdict=MATCH ESADCID=66096 endTime=Tue Aug 13 15:15:48 2019 ESADKIMVerdict=pass ESADLPVerdict=NOT_EVALUATED ESADMARCVerdict=pass dvc=3.4.5.6 ESAAttachmentDetails={'presentation.pptx': {'AMP': {'Verdict': 'LOWRISK', 'fileHash': 'e4a4f9b7c4b4c7fb62b3df3c7e9e05811dc52c38eb8b76d3847f41ef299399e4'}, 'BodyScanner': {}}} ESAFriendlyFrom=no-reply@example.org ESAGMVerdict=NEGATIVE ESAICID=36050 startTime=Tue Aug 13 15:15:45 2019 deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=no-reply@example.org cs1Label=MailPolicy cs1=DEFAULT cs2Label=SenderCountry cs2=United States ESAMFVerdict=MATCH act=BOUNCED ESAFinalActionDetails=5.1.0 - Unknown address error cs4Label=ExternalMsgID cs4='<5d528dcf33830_812b56878564dc@ip-10-22-10-56.mail>' ESAOFVerdict=NEGATIVE duser=john.doe@example.org ESAHeloDomain=mail.example.orgm ESAHeloIP=10.0.0.0 cfp1Label=SBRSScore cfp1=0.9 ESASDRDomainAge=9 years 3 months 14 days cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Neutral ESASPFVerdict=SoftFail sourceHostName=esa1.hc3033-47.iphmx.com ESASenderGroup=GREYLIST sourceAddress=1.2.3.4 msg=Cisco=20Advanced=20Phishing=20Protection=20System=20Notification=20for=20bce-demo ESATLSInCipher=ECDHE-RSA-AES128-GCM-SHA256 ESATLSInConnStatus=Success ESATLSInProtocol=TLSv1.2 ESATLSOutCipher=ECDHE-RSA-AES256-SHA384 ESATLSOutConnStatus=Success ESATLSOutProtocol=TLSv1.2 ESAURLDetails={'https://bce-demo.appc.cisco.com/sensors/a7b04388-0f6e-11e9-8def-0242ac110002': {'Category': 'Computers and Internet', 'WbrsScore': '7.3'}, 'http://mandrill.appc.cisco.com/track/open.php?u=30372747&id=d57275a6c9df40418a90fd977e3bf506': {'Category': 'Computers and Internet', 'WbrsScore': '7.3'}} deviceInboundInterface=IncomingMail",
"event": {
"action": "bounced",
"end": "2019-08-13T15:15:48Z",
"severity": 5,
"start": "2019-08-13T15:15:45Z"
},
"@timestamp": "2019-08-13T15:15:45Z",
"cisco": {
"esa": {
"authentication": {
"dkim": {
"verdict": "pass"
},
"dmarc": {
"verdict": "pass"
},
"spf": {
"verdict": "SoftFail"
}
},
"delivery": {
"connection_id": "66096"
},
"event": {
"action_details": "5.1.0 - Unknown address error"
},
"friendly": {
"from": "no-reply@example.org"
},
"helo": {
"domain": "mail.example.orgm",
"ip": "10.0.0.0"
},
"injection": {
"connection_id": "36050"
},
"protection": {
"amp": {
"verdict": "SKIPPED"
},
"antivirus": {
"verdict": "NEGATIVE"
},
"dlp": {
"verdict": "NOT_EVALUATED"
},
"graymail": {
"verdict": "NEGATIVE"
},
"spam": {
"verdict": "NEGATIVE"
}
},
"sender_group": "GREYLIST",
"source": {
"domain": {
"age": "9 years 3 months 14 days"
}
},
"url": [
"http://mandrill.appc.cisco.com/track/open.php?u=30372747&id=d57275a6c9df40418a90fd977e3bf506",
"https://bce-demo.appc.cisco.com/sensors/a7b04388-0f6e-11e9-8def-0242ac110002"
],
"url_domain": [
"bce-demo.appc.cisco.com",
"mandrill.appc.cisco.com"
]
}
},
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "e4a4f9b7c4b4c7fb62b3df3c7e9e05811dc52c38eb8b76d3847f41ef299399e4"
},
"name": "presentation.pptx"
}
}
],
"from": {
"address": [
"no-reply@example.org"
]
},
"local_id": "4631",
"message_id": "5d528dcf33830_812b56878564dc@ip-10-22-10-56.mail",
"subject": "Cisco=20Advanced=20Phishing=20Protection=20System=20Notification=20for=20bce-demo",
"to": {
"address": [
"john.doe@example.org"
]
}
},
"host": {
"hostname": "esa1.hc3033-47.iphmx.com",
"id": "420D4F36AAEBC0093B4F-B9E72189A021",
"name": "esa1.hc3033-47.iphmx.com"
},
"network": {
"direction": "inbound"
},
"observer": {
"ingress": {
"interface": {
"name": "IncomingMail"
}
},
"type": "C300V Email Security Virtual Appliance",
"vendor": "Cisco",
"version": "13.0.0-252"
},
"related": {
"hosts": [
"esa1.hc3033-47.iphmx.com"
],
"ip": [
"1.2.3.4",
"3.4.5.6"
]
},
"rule": {
"name": "DEFAULT"
},
"server": {
"ip": "3.4.5.6"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"tls": {
"cipher": "ECDHE-RSA-AES256-SHA384",
"client": {
"supported_ciphers": [
"ECDHE-RSA-AES128-GCM-SHA256"
]
},
"established": true,
"version": "1.2",
"version_protocol": "tls"
}
}
{
"message": "CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=254be28187994bc7a37f496ceac54edd ESAMID=11111111 ESAICID=333333 ESADCID=2222222 ESAAMPVerdict=NOT_EVALUATED ESAASVerdict=NOT_EVALUATED ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Wed Mar 1 19:02:03 2023 dvc=3.4.5.6 ESAAttachmentDetails={'resume.pdf': {'AMP': {'Verdict': 'HIGHRISK', 'fileHash': 'f41c7c5d8e3b3c2b5d5b787bc5e5f9e5e5c23d60933a24d8c36df3847c61ef1'}, 'BodyScanner': {}}} ESAFriendlyFrom=no-reply@example.org ESAGMVerdict=NOT_EVALUATED startTime=Wed Mar 1 19:02:03 2023 deviceOutboundInterface=OutgoingMail deviceDirection=1 ESAMailFlowPolicy=RELAY suser=no-reply@example.org cs1Label=MailPolicy cs1=RestrictionEmetteur cs2Label=SenderCountry cs2=not enabled ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<11111111.2222222222222222222.JavaMail.ccccccccccc@dddddddddddddddd>' ESAMsgSize=3762 ESAOFVerdict=NOT_EVALUATED duser=john.doe@example.org ESAHeloDomain=mail.example.org ESAHeloIP=10.0.0.0 ESAReplyTo=no-reply@example.org cfp1Label=SBRSScore cfp1=not enabled sourceHostName=unknown ESASenderGroup=RELAYLIST sourceAddress=1.2.3.4 msg='\\=?UTF-8?Q?Nice to Meet you?\\='\n",
"event": {
"action": "delivered",
"end": "2023-03-01T19:02:03Z",
"severity": 5,
"start": "2023-03-01T19:02:03Z"
},
"@timestamp": "2023-03-01T19:02:03Z",
"cisco": {
"esa": {
"delivery": {
"connection_id": "2222222"
},
"email": {
"message_size": "3762"
},
"friendly": {
"from": "no-reply@example.org"
},
"helo": {
"domain": "mail.example.org",
"ip": "10.0.0.0"
},
"injection": {
"connection_id": "333333"
},
"protection": {
"amp": {
"verdict": "NOT_EVALUATED"
},
"antivirus": {
"verdict": "NOT_EVALUATED"
},
"graymail": {
"verdict": "NOT_EVALUATED"
},
"spam": {
"verdict": "NOT_EVALUATED"
}
},
"sender_group": "RELAYLIST"
}
},
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "f41c7c5d8e3b3c2b5d5b787bc5e5f9e5e5c23d60933a24d8c36df3847c61ef1"
},
"name": "resume.pdf"
}
}
],
"from": {
"address": [
"no-reply@example.org"
]
},
"local_id": "11111111",
"message_id": "11111111.2222222222222222222.JavaMail.ccccccccccc@dddddddddddddddd",
"reply_to": {
"address": "no-reply@example.org"
},
"subject": "'\\=?UTF-8?Q?Nice to Meet you?\\='",
"to": {
"address": [
"john.doe@example.org"
]
}
},
"host": {
"hostname": "unknown",
"id": "254be28187994bc7a37f496ceac54edd",
"name": "unknown"
},
"network": {
"direction": "outbound"
},
"observer": {
"egress": {
"interface": {
"name": "OutgoingMail"
}
},
"type": "C390 Email Security Appliance",
"vendor": "Cisco",
"version": "14.2.1-015"
},
"related": {
"hosts": [
"unknown"
],
"ip": [
"1.2.3.4",
"3.4.5.6"
]
},
"rule": {
"name": "RestrictionEmetteur"
},
"server": {
"ip": "3.4.5.6"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=254be28187994bc7a37f496ceac54edd ESAMID=11111111 ESAICID=333333 ESADCID=2222222 ESAAMPVerdict=NOT_EVALUATED ESAASVerdict=NOT_EVALUATED ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Wed Mar 1 19:02:03 2023 dvc=3.4.5.6 ESAAttachmentDetails={'invoice.pdf': {'AMP': {'Verdict': 'LOWRISK', 'fileHash': '01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b'}, 'BodyScanner': {}}} ESAFriendlyFrom=JOHN DOE <john.doe@example.com> ESAGMVerdict=NOT_EVALUATED startTime=Wed Mar 1 19:02:03 2023 deviceOutboundInterface=OutgoingMail deviceDirection=1 ESAMailFlowPolicy=RELAY suser=veuillez-ne-pas-repondre@example.org cs1Label=MailPolicy cs1=RestrictionEmetteur cs2Label=SenderCountry cs2=not enabled ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<11111111111111111111111111111@ddddddd>' ESAMsgSize=111066 ESAOFVerdict=NOT_EVALUATED duser=jane.doe@example.org ESAHeloDomain=mail.example.org ESAHeloIP=10.0.0.0 cfp1Label=SBRSScore cfp1=not enabled sourceHostName=unknown ESASenderGroup=RELAYLISTTELEDEP sourceAddress=1.2.3.4 msg='\\=?utf-8?Q?For the meeting?\\='",
"event": {
"action": "delivered",
"end": "2023-03-01T19:02:03Z",
"severity": 5,
"start": "2023-03-01T19:02:03Z"
},
"@timestamp": "2023-03-01T19:02:03Z",
"cisco": {
"esa": {
"delivery": {
"connection_id": "2222222"
},
"email": {
"message_size": "111066"
},
"friendly": {
"from": "JOHN DOE <john.doe@example.com>"
},
"helo": {
"domain": "mail.example.org",
"ip": "10.0.0.0"
},
"injection": {
"connection_id": "333333"
},
"protection": {
"amp": {
"verdict": "NOT_EVALUATED"
},
"antivirus": {
"verdict": "NOT_EVALUATED"
},
"graymail": {
"verdict": "NOT_EVALUATED"
},
"spam": {
"verdict": "NOT_EVALUATED"
}
},
"sender_group": "RELAYLISTTELEDEP"
}
},
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "invoice.pdf"
}
}
],
"from": {
"address": [
"veuillez-ne-pas-repondre@example.org"
]
},
"local_id": "11111111",
"message_id": "11111111111111111111111111111@ddddddd",
"subject": "\\=?utf-8?Q?For the meeting?\\=",
"to": {
"address": [
"jane.doe@example.org"
]
}
},
"host": {
"hostname": "unknown",
"id": "254be28187994bc7a37f496ceac54edd",
"name": "unknown"
},
"network": {
"direction": "outbound"
},
"observer": {
"egress": {
"interface": {
"name": "OutgoingMail"
}
},
"type": "C390 Email Security Appliance",
"vendor": "Cisco",
"version": "14.2.1-015"
},
"related": {
"hosts": [
"unknown"
],
"ip": [
"1.2.3.4",
"3.4.5.6"
]
},
"rule": {
"name": "RestrictionEmetteur"
},
"server": {
"ip": "3.4.5.6"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=254be28187994bc7a37f496ceac54edd ESAMID=11111111 ESAICID=333333 ESADCID=2222222 ESAAMPVerdict=LOW_RISK ESAASVerdict=NEGATIVE ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Wed Mar 1 19:02:04 2023 ESADMARCVerdict=pass dvc=3.4.5.6 ESAAttachmentDetails={'invoice.pdf': {'AMP': {'Verdict': 'LOWRISK', 'fileHash': '01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b'}, 'BodyScanner': {}}} ESAFriendlyFrom=John Doe <john.doe@example.org> ESAGMVerdict=NEGATIVE startTime=Wed Mar 1 19:02:02 2023 deviceInboundInterface=IncomingMail deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=john.doe@example.org cs1Label=MailPolicy cs1=DEFAULT cs2Label=SenderCountry cs2=Netherlands ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<44444444444444444444444444444444444444@77777777777777777777777777.EXAMPLE.COM>' ESAMsgSize=1197675 ESAOFVerdict=NEGATIVE duser=jane.doe@example.fr ESAHeloDomain=mail.example.org ESAHeloIP=10.0.0.0 cfp1Label=SBRSScore cfp1=3.5 ESASDRDomainAge=30 days (or greater) cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Neutral ESASPFVerdict={'mailfrom': {'result': 'Pass', 'sender': 'john.doe@example.org'}, 'helo': {'result': 'Pass', 'sender': 'postmaster@example.org'}, 'pra': {'result': 'None', 'sender': 'john.doe@example.org'}} sourceHostName=outbound.example.com ESASenderGroup=UNKNOWNLIST sourceAddress=1.2.3.4 msg='Perso' ESAURLDetails={'https://tinyurl.es/tbdra': {'WbrsScore': 9.1999999999999993, 'ExpandedUrl': 'https://facebook.com/u/john.doe'}, 'www.twitter.com': {'WbrsScore': 0.0, 'AttachmentWithUrl': 'My document.pdf'}, 'https://tiktok.com': {'WbrsScore': 4.9000000000000004}}",
"event": {
"action": "delivered",
"end": "2023-03-01T19:02:04Z",
"severity": 5,
"start": "2023-03-01T19:02:02Z"
},
"@timestamp": "2023-03-01T19:02:02Z",
"cisco": {
"esa": {
"authentication": {
"dmarc": {
"verdict": "pass"
},
"spf": {
"verdict": "{\"helo\":{\"result\":\"Pass\",\"sender\":\"postmaster@example.org\"},\"mailfrom\":{\"result\":\"Pass\",\"sender\":\"john.doe@example.org\"},\"pra\":{\"result\":\"None\",\"sender\":\"john.doe@example.org\"}}"
}
},
"delivery": {
"connection_id": "2222222"
},
"email": {
"message_size": "1197675"
},
"friendly": {
"from": "John Doe <john.doe@example.org>"
},
"helo": {
"domain": "mail.example.org",
"ip": "10.0.0.0"
},
"injection": {
"connection_id": "333333"
},
"protection": {
"amp": {
"verdict": "LOW_RISK"
},
"antivirus": {
"verdict": "NOT_EVALUATED"
},
"graymail": {
"verdict": "NEGATIVE"
},
"spam": {
"verdict": "NEGATIVE"
}
},
"sender_group": "UNKNOWNLIST",
"source": {
"domain": {
"age": "30 days (or greater)"
}
},
"url": [
"https://facebook.com/u/john.doe",
"https://tiktok.com",
"https://tinyurl.es/tbdra",
"www.twitter.com"
],
"url_domain": [
"facebook.com",
"tiktok.com",
"tinyurl.es",
"www.twitter.com"
]
}
},
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "invoice.pdf"
}
}
],
"from": {
"address": [
"john.doe@example.org"
]
},
"local_id": "11111111",
"message_id": "44444444444444444444444444444444444444@77777777777777777777777777.EXAMPLE.COM",
"subject": "Perso",
"to": {
"address": [
"jane.doe@example.fr"
]
}
},
"host": {
"hostname": "outbound.example.com",
"id": "254be28187994bc7a37f496ceac54edd",
"name": "outbound.example.com"
},
"network": {
"direction": "inbound"
},
"observer": {
"ingress": {
"interface": {
"name": "IncomingMail"
}
},
"type": "C390 Email Security Appliance",
"vendor": "Cisco",
"version": "14.2.1-015"
},
"related": {
"hosts": [
"outbound.example.com"
],
"ip": [
"1.2.3.4",
"3.4.5.6"
]
},
"rule": {
"name": "DEFAULT"
},
"server": {
"ip": "3.4.5.6"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=254be28187994bc7a37f496ceac54edd ESAMID=11111111 ESAICID=333333 ESADCID=2222222 ESAAMPVerdict=UNKNOWN ESAASVerdict=NEGATIVE ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Wed Mar 1 19:02:05 2023 ESADKIMVerdict=pass ESADMARCVerdict=pass dvc=3.4.5.6 ESAAttachmentDetails={'unknown': {'AMP': {'Verdict': ['FILE UNKNOWN'], 'fileHash': ['87428fc522803d31065e7bce3cf03fe475096631e5e07bbd7a0fde60c4cf25c7']}}} ESAFriendlyFrom=John Doe <john.doe@example.org> ESAGMVerdict=NEGATIVE startTime=Wed Mar 1 19:02:02 2023 deviceInboundInterface=IncomingMail deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=john.doe@example.org cs1Label=MailPolicy cs1=DEFAULT cs2Label=SenderCountry cs2=United States ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<111111111111111111111@mal.example.org>' ESAMsgSize=73748 ESAOFVerdict=NEGATIVE duser=jane.doe@example.org ESAHeloDomain=mail.example.org ESAHeloIP=10.0.0.0 cfp1Label=SBRSScore cfp1=3.5 ESASDRDomainAge=30 days (or greater) cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Neutral ESASPFVerdict={'mailfrom': {'result': 'Pass', 'sender': 'john.doe@example.org'}, 'helo': {'result': 'Pass', 'sender': 'postmaster@example.org'}, 'pra': {'result': 'None', 'sender': 'no-reply@example.org'}} sourceHostName=outboun",
"event": {
"action": "delivered",
"end": "2023-03-01T19:02:05Z",
"severity": 5,
"start": "2023-03-01T19:02:02Z"
},
"@timestamp": "2023-03-01T19:02:02Z",
"cisco": {
"esa": {
"authentication": {
"dkim": {
"verdict": "pass"
},
"dmarc": {
"verdict": "pass"
},
"spf": {
"verdict": "{\"helo\":{\"result\":\"Pass\",\"sender\":\"postmaster@example.org\"},\"mailfrom\":{\"result\":\"Pass\",\"sender\":\"john.doe@example.org\"},\"pra\":{\"result\":\"None\",\"sender\":\"no-reply@example.org\"}}"
}
},
"delivery": {
"connection_id": "2222222"
},
"email": {
"message_size": "73748"
},
"friendly": {
"from": "John Doe <john.doe@example.org>"
},
"helo": {
"domain": "mail.example.org",
"ip": "10.0.0.0"
},
"injection": {
"connection_id": "333333"
},
"protection": {
"amp": {
"verdict": "UNKNOWN"
},
"antivirus": {
"verdict": "NOT_EVALUATED"
},
"graymail": {
"verdict": "NEGATIVE"
},
"spam": {
"verdict": "NEGATIVE"
}
},
"source": {
"domain": {
"age": "30 days (or greater)"
}
}
}
},
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "87428fc522803d31065e7bce3cf03fe475096631e5e07bbd7a0fde60c4cf25c7"
},
"name": "unknown"
}
}
],
"from": {
"address": [
"john.doe@example.org"
]
},
"local_id": "11111111",
"message_id": "111111111111111111111@mal.example.org",
"to": {
"address": [
"jane.doe@example.org"
]
}
},
"host": {
"hostname": "outboun",
"id": "254be28187994bc7a37f496ceac54edd",
"name": "outboun"
},
"network": {
"direction": "inbound"
},
"observer": {
"ingress": {
"interface": {
"name": "IncomingMail"
}
},
"type": "C390 Email Security Appliance",
"vendor": "Cisco",
"version": "14.2.1-015"
},
"related": {
"hosts": [
"outboun"
],
"ip": [
"3.4.5.6"
]
},
"rule": {
"name": "DEFAULT"
},
"server": {
"ip": "3.4.5.6"
}
}
{
"message": "CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=254be28187994bc7a37f496ceac54edd ESAMID=11111111 ESAICID=333333 ESAAMPVerdict=FA_PENDING ESAASVerdict=BULK_MAIL ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Wed Mar 1 19:01:47 2023 ESADKIMVerdict=pass ESADMARCVerdict=Skipped dvc=3.4.5.6 ESAAttachmentDetails={'twitter.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b'}, 'BodyScanner': {}}, 'appointement.ics': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '87428fc522803d31065e7bce3cf03fe475096631e5e07bbd7a0fde60c4cf25c7'}}, 'icon-linkedin.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': 'a3a5e715f0cc574a73c3f9bebb6bc24f32ffd5b67b387244c2c909da779a1478'}, 'BodyScanner': {}}, 'fond-gris.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '8d74beec1be996322ad76813bafb92d40839895d6dd7ee808b17ca201eac98be'}, 'BodyScanner': {}}, 'bg-desktop-default-header.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '768c71d785bf6bbbf8c4d6af6582041f2659027140a962cd0c55b11eddfd5e3d'}, 'BodyScanner': {}}} ESAFriendlyFrom=John Doe <john.doe@example.org> ESAGMVerdict=POSITIVE startTime=Wed Mar 1 19:01:45 2023 deviceInboundInterface=IncomingMail deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=john.doe@example.org cs1Label=MailPolicy cs1=DEFAULT cs2Label=SenderCountry cs2=France ESAMFVerdict=NO_MATCH act=DQ ESAFinalActionDetails=Message held temporarily in Delay Quarantine cs4Label=ExternalMsgID cs4='<111111111111111111111@mal.example.org>' ESAMsgSize=174552 ESAOFVerdict=NEGATIVE duser=jane.doe@example.org ESAHeloDomain=mail.example.org ESAHeloIP=10.0.0.0 cfp1Label=SBRSScore cfp1=5.4 ESASDRDomainAge=30 days (or greater) cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Neutral ESASPFVerdict={'mailfrom': {'result': 'Pass', 'sender': 'john.doe@example.org'}, 'helo': {'result': 'Pass', 'sender': 'postmaster@example.org'}, 'pra': {'result': 'None', 'sender': 'no-reply@example.org'}} sourceHostName=outbound.example.com ESASenderGroup=UNKNOWNLIST sourceAddress=1.2.3.4 msg='Validation of your request' ESAURLDetails={}",
"event": {
"action": "dq",
"end": "2023-03-01T19:01:47Z",
"severity": 5,
"start": "2023-03-01T19:01:45Z"
},
"@timestamp": "2023-03-01T19:01:45Z",
"cisco": {
"esa": {
"authentication": {
"dkim": {
"verdict": "pass"
},
"dmarc": {
"verdict": "Skipped"
},
"spf": {
"verdict": "{\"helo\":{\"result\":\"Pass\",\"sender\":\"postmaster@example.org\"},\"mailfrom\":{\"result\":\"Pass\",\"sender\":\"john.doe@example.org\"},\"pra\":{\"result\":\"None\",\"sender\":\"no-reply@example.org\"}}"
}
},
"email": {
"message_size": "174552"
},
"event": {
"action_details": "Message held temporarily in Delay Quarantine"
},
"friendly": {
"from": "John Doe <john.doe@example.org>"
},
"helo": {
"domain": "mail.example.org",
"ip": "10.0.0.0"
},
"injection": {
"connection_id": "333333"
},
"protection": {
"amp": {
"verdict": "FA_PENDING"
},
"antivirus": {
"verdict": "NOT_EVALUATED"
},
"graymail": {
"verdict": "POSITIVE"
},
"spam": {
"verdict": "BULK_MAIL"
}
},
"sender_group": "UNKNOWNLIST",
"source": {
"domain": {
"age": "30 days (or greater)"
}
}
}
},
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "twitter.png"
}
},
{
"file": {
"hash": {
"sha256": "87428fc522803d31065e7bce3cf03fe475096631e5e07bbd7a0fde60c4cf25c7"
},
"name": "appointement.ics"
}
},
{
"file": {
"hash": {
"sha256": "a3a5e715f0cc574a73c3f9bebb6bc24f32ffd5b67b387244c2c909da779a1478"
},
"name": "icon-linkedin.png"
}
},
{
"file": {
"hash": {
"sha256": "8d74beec1be996322ad76813bafb92d40839895d6dd7ee808b17ca201eac98be"
},
"name": "fond-gris.png"
}
},
{
"file": {
"hash": {
"sha256": "768c71d785bf6bbbf8c4d6af6582041f2659027140a962cd0c55b11eddfd5e3d"
},
"name": "bg-desktop-default-header.png"
}
}
],
"from": {
"address": [
"john.doe@example.org"
]
},
"local_id": "11111111",
"message_id": "111111111111111111111@mal.example.org",
"subject": "Validation of your request",
"to": {
"address": [
"jane.doe@example.org"
]
}
},
"host": {
"hostname": "outbound.example.com",
"id": "254be28187994bc7a37f496ceac54edd",
"name": "outbound.example.com"
},
"network": {
"direction": "inbound"
},
"observer": {
"ingress": {
"interface": {
"name": "IncomingMail"
}
},
"type": "C390 Email Security Appliance",
"vendor": "Cisco",
"version": "14.2.1-015"
},
"related": {
"hosts": [
"outbound.example.com"
],
"ip": [
"1.2.3.4",
"3.4.5.6"
]
},
"rule": {
"name": "DEFAULT"
},
"server": {
"ip": "3.4.5.6"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=254be28187994bc7a37f496ceac54edd ESAMID=11111111 ESADCID=2222222 ESAStatus=QUEUED",
"event": {
"severity": 5
},
"cisco": {
"esa": {
"delivery": {
"connection_id": "2222222"
},
"status": "QUEUED"
}
},
"email": {
"local_id": "11111111"
},
"host": {
"id": "254be28187994bc7a37f496ceac54edd"
},
"observer": {
"type": "C390 Email Security Appliance",
"vendor": "Cisco",
"version": "14.2.1-015"
}
}
{
"message": "CEF:0|Cisco|C390 Email Security Appliance|14.2.1-015|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=00F66XXXX-FCH2025V2LQ ESAMID=351452154 ESAICID=317589723 ESADCID=192175459 ESADLPVerdict=NOT EVALUATED ESAASVerdict=NOT_EVALUATED ESAAVVerdict=NOT_EVALUATED ESACFVerdict=MATCH endTime=Mon Jun 13 08:02:06 2023 ESADKIMVerdict=pass ESADMARCVerdict=pass dvc=5.6.7.8 ESAAttachmentDetails={'bob.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '2062932a5c017252038b001b14e1dfd09501742faeb7275da8e031eacfa963ed'}, 'BodyScanner': {}}, 'Signature Jean Dupont.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': 'a0e121e017afed94380de0658e51f4bed14f6cffc3d7f2026f5c3cafcf8273f4'}, 'BodyScanner': {}}, 'FICHE.pdf': {'AMP': {'Verdict': 'LOWRISK', 'fileHash': 'e4b2d60cea9c09a0871d0f94fe9ca38010ef8e552f67e7cdec7489d2a1818354'}, 'BodyScanner': {}}} ESAFriendlyFrom=Marc Dupont <m.dupont@corp.fr> ESAGMVerdict=NEGATIVE startTime=Mon Jun 13 08:02:04 2023 deviceInboundInterface=IncomingMail deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=m.dupont@corp.fr cs1Label=MailPolicy cs1=DEFAULT cs2Label=SenderCountry cs2=Switzerland ESAMFVerdict=NO_MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<17f42d91-1908-aecb-adfd-a6e9c92e623e@corp.fr>' ESAMsgSize=418081 ESAOFVerdict=POSITIVE duser=evil@corp.fr ESAHeloDomain=example.org ESAHeloIP=192.168.10.244 cfp1Label=SBRSScore cfp1=None ESASDRDomainAge=30 days (or greater) cs3Label=SDRThreatCategory cs3=N/A cs6Label=SDRRepScore cs6=Neutral ESASPFVerdict={'mailfrom': {'result': 'Pass', 'sender': 'lol@evil.fr'}, 'helo': {'result': 'None', 'sender': 'postmaster@example.org'}, 'pra': {'result': 'None', 'sender': 'm.dupont@corp.fr'}} sourceHostName=example.org ESASenderGroup=SUSPECTLIST sourceAddress=1.2.3.4 msg='\\=?UTF-8?Q?N\\=c2\\=b0_CORP\\= \\=?UTF-8?Q?020?\\='",
"event": {
"action": "delivered",
"end": "2023-06-13T08:02:06Z",
"severity": 5,
"start": "2023-06-13T08:02:04Z"
},
"@timestamp": "2023-06-13T08:02:04Z",
"cisco": {
"esa": {
"authentication": {
"dkim": {
"verdict": "pass"
},
"dmarc": {
"verdict": "pass"
},
"spf": {
"verdict": "{\"helo\":{\"result\":\"None\",\"sender\":\"postmaster@example.org\"},\"mailfrom\":{\"result\":\"Pass\",\"sender\":\"lol@evil.fr\"},\"pra\":{\"result\":\"None\",\"sender\":\"m.dupont@corp.fr\"}}"
}
},
"delivery": {
"connection_id": "192175459"
},
"email": {
"message_size": "418081"
},
"friendly": {
"from": "Marc Dupont <m.dupont@corp.fr>"
},
"helo": {
"domain": "example.org",
"ip": "192.168.10.244"
},
"injection": {
"connection_id": "317589723"
},
"protection": {
"antivirus": {
"verdict": "NOT_EVALUATED"
},
"dlp": {
"verdict": "NOT EVALUATED"
},
"graymail": {
"verdict": "NEGATIVE"
},
"spam": {
"verdict": "NOT_EVALUATED"
}
},
"sender_group": "SUSPECTLIST",
"source": {
"domain": {
"age": "30 days (or greater)"
}
}
}
},
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "2062932a5c017252038b001b14e1dfd09501742faeb7275da8e031eacfa963ed"
},
"name": "bob.png"
}
},
{
"file": {
"hash": {
"sha256": "a0e121e017afed94380de0658e51f4bed14f6cffc3d7f2026f5c3cafcf8273f4"
},
"name": "Signature Jean Dupont.png"
}
},
{
"file": {
"hash": {
"sha256": "e4b2d60cea9c09a0871d0f94fe9ca38010ef8e552f67e7cdec7489d2a1818354"
},
"name": "FICHE.pdf"
}
}
],
"from": {
"address": [
"m.dupont@corp.fr"
]
},
"local_id": "351452154",
"message_id": "17f42d91-1908-aecb-adfd-a6e9c92e623e@corp.fr",
"subject": "\\=?UTF-8?Q?N\\=c2\\=b0_CORP\\= \\=?UTF-8?Q?020?\\=",
"to": {
"address": [
"evil@corp.fr"
]
}
},
"host": {
"hostname": "example.org",
"id": "00F66XXXX-FCH2025V2LQ",
"name": "example.org"
},
"network": {
"direction": "inbound"
},
"observer": {
"ingress": {
"interface": {
"name": "IncomingMail"
}
},
"type": "C390 Email Security Appliance",
"vendor": "Cisco",
"version": "14.2.1-015"
},
"related": {
"hosts": [
"example.org"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"rule": {
"name": "DEFAULT"
},
"server": {
"ip": "5.6.7.8"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "CEF:0|Cisco|C600V Email Security Virtual Appliance|15.0.0-104|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=42306A91288AD54F334B-220D2F3E82D1 ESAMID=75132386 ESAICID=9038012 ESADCID=3259121 ESAAMPVerdict=UNKNOWN ESAASVerdict=NEGATIVE ESAAVVerdict=NEGATIVE ESACFVerdict=MATCH end=Wed Aug 6 07:46:00 2025 ESADLPVerdict=NOT_EVALUATED dvc=1.2.3.4 ESAAttachmentDetails={'image.png': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': '6b86b273ff34fce19d6b804eff5a3f5747ada4eaa22f1d49c01e52ddb7875b4b'}, 'BodyScanner': {}}, 'Test.pdf': {'AMP': {'Verdict': 'FILE UNKNOWN', 'fileHash': 'd4735e3a265e16eee03f59718b9b5d03019c07d8b6c51f90da3a666eec13ab35'}, 'BodyScanner': {}}} ESAFriendlyFrom=From <sender@sender-domain.com> ESAGMVerdict=NEGATIVE start=Wed Aug 6 07:45:58 2025 deviceInboundInterface=incoming deviceDirection=0 ESAMailFlowPolicy=ACCEPT suser=sender@sender-domain.com cs1Label=MailPolicy cs1=Policy cs2Label=SenderCountry cs2=not applicable ESAMFVerdict=MATCH act=DELIVERED cs4Label=ExternalMsgID cs4='<ABC@PARP264MB5994.FRAP264.PROD.OUTLOOK.COM>' ESAMsgSize=798896 ESAOFVerdict=NEGATIVE duser=dest1@reception.com;dest2@reception.com ESAHeloDomain=example.domain ESAHeloIP=1.2.3.4 cfp1Label=SBRSScore cfp1=rfc1918 shost=sourcehost ESASenderGroup=SEG src=1.2.3.4 msg='Subject'",
"event": {
"action": "delivered",
"end": "2025-08-06T07:46:00Z",
"severity": 5,
"start": "2025-08-06T07:45:58Z"
},
"@timestamp": "2025-08-06T07:45:58Z",
"cisco": {
"esa": {
"delivery": {
"connection_id": "3259121"
},
"email": {
"message_size": "798896"
},
"friendly": {
"from": "From <sender@sender-domain.com>"
},
"helo": {
"domain": "example.domain",
"ip": "1.2.3.4"
},
"injection": {
"connection_id": "9038012"
},
"protection": {
"amp": {
"verdict": "UNKNOWN"
},
"antivirus": {
"verdict": "NEGATIVE"
},
"dlp": {
"verdict": "NOT_EVALUATED"
},
"graymail": {
"verdict": "NEGATIVE"
},
"spam": {
"verdict": "NEGATIVE"
}
},
"sender_group": "SEG"
}
},
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "6b86b273ff34fce19d6b804eff5a3f5747ada4eaa22f1d49c01e52ddb7875b4b"
},
"name": "image.png"
}
},
{
"file": {
"hash": {
"sha256": "d4735e3a265e16eee03f59718b9b5d03019c07d8b6c51f90da3a666eec13ab35"
},
"name": "Test.pdf"
}
}
],
"from": {
"address": [
"sender@sender-domain.com"
]
},
"local_id": "75132386",
"message_id": "ABC@PARP264MB5994.FRAP264.PROD.OUTLOOK.COM",
"subject": "Subject",
"to": {
"address": [
"dest1@reception.com",
"dest2@reception.com"
]
}
},
"host": {
"hostname": "sourcehost",
"id": "42306A91288AD54F334B-220D2F3E82D1",
"name": "sourcehost"
},
"network": {
"direction": "inbound"
},
"observer": {
"ingress": {
"interface": {
"name": "incoming"
}
},
"type": "C600V Email Security Virtual Appliance",
"vendor": "Cisco",
"version": "15.0.0-104"
},
"related": {
"hosts": [
"sourcehost"
],
"ip": [
"1.2.3.4"
]
},
"rule": {
"name": "Policy"
},
"server": {
"ip": "1.2.3.4"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "CEF:0|Cisco|C300V Secure Email Gateway Virtual|16.0.0-054|ESA_CONSOLIDATED_LOG_EVENT|Consolidated Log Event|5|deviceExternalId=111111111111111111111111111111111 ESAMID=15798304 ESADCID=9624426 end=Wed Mar 12 11:02:25 2025 ESADLPVerdict=NOT_EVALUATED ESAAttachmentDetails={'winmail.dat': {'BodyScanner': {}}} ESAGMVerdict=NOT_EVALUATED deviceDirection=0 cs1Label=MailPolicy cs1=DEFAULT ESAMFVerdict=NOT_EVALUATED act=DELIVERED ESAOFVerdict=NOT_EVALUATED ESATLSOutCipher=ECDHE-RSA-AES256-GCM-SHA384 ESATLSOutConnStatus=Success ESATLSOutProtocol=TLSv1.2 ESAAMPVerdict=LOW_RISK ESAASVerdict=NOT_EVALUATED ESAAVVerdict=NOT_EVALUATED ESACFVerdict=NOT_EVALUATED ESALogHeaders={'X-ThreatScanner-Verdict': ['Negative']}\n\n",
"event": {
"action": "delivered",
"end": "2025-03-12T11:02:25Z",
"severity": 5
},
"@timestamp": "2025-03-12T11:02:25Z",
"cisco": {
"esa": {
"delivery": {
"connection_id": "9624426"
},
"log_headers": {
"X-ThreatScanner-Verdict": [
"Negative"
]
},
"protection": {
"amp": {
"verdict": "LOW_RISK"
},
"antivirus": {
"verdict": "NOT_EVALUATED"
},
"dlp": {
"verdict": "NOT_EVALUATED"
},
"graymail": {
"verdict": "NOT_EVALUATED"
},
"spam": {
"verdict": "NOT_EVALUATED"
}
}
}
},
"email": {
"attachments": [
{
"file": {
"name": "winmail.dat"
}
}
],
"local_id": "15798304"
},
"host": {
"id": "111111111111111111111111111111111"
},
"network": {
"direction": "inbound"
},
"observer": {
"type": "C300V Secure Email Gateway Virtual",
"vendor": "Cisco",
"version": "16.0.0-054"
},
"rule": {
"name": "DEFAULT"
},
"tls": {
"cipher": "ECDHE-RSA-AES256-GCM-SHA384",
"established": true,
"version": "1.2",
"version_protocol": "tls"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
cisco.esa.authentication.dkim.verdict |
keyword |
This field indicates the verdict assigned to a message by the ESA's DKIM authentication mechanism. DKIM is a protocol used to verify the integrity of an email message by checking a digital signature applied by the sender's domain. |
cisco.esa.authentication.dmarc.verdict |
keyword |
This field indicates the verdict assigned to a message by the ESA's Domain-based Message Authentication, Reporting & Conformance (DMARC) mechanism. DMARC is a protocol used to verify the authenticity of email messages by checking various authentication mechanisms, such as Sender Policy Framework (SPF) and DomainKeys Identified Mail (DKIM). |
cisco.esa.authentication.spf.verdict |
keyword |
This field indicates the verdict assigned to a message by the ESA's SPF authentication mechanism. SPF is a protocol used to verify that an email message was sent from an authorized IP address for the sender's domain. |
cisco.esa.delivery.connection_id |
keyword |
|
cisco.esa.email.message_size |
keyword |
This field represents the size of the email message |
cisco.esa.event.action_details |
keyword |
This field contains the details about the action of the event |
cisco.esa.friendly.from |
keyword |
This field is the friendly header that is displayed in most email clients before the user email address |
cisco.esa.helo.domain |
keyword |
This field indicates the domain name associated with the HELO (or EHLO) command used by the sending |
cisco.esa.helo.ip |
ip |
This field indicates the IP address associated with the HELO (or EHLO) command used by the sending server during the SMTP handshake. The HELO command is used to identify the sending server to the receiving server, and the IP address can be used to help identify the geographic location of the sending server. |
cisco.esa.injection.connection_id |
keyword |
This field is similar to the cisco.esa.connection_id field, but it specifically refers to the connection ID associated with an incoming message that is being injected into the ESA for processing. |
cisco.esa.log_headers |
object |
Custom Log Headers |
cisco.esa.protection.amp.verdict |
keyword |
This field indicates the verdict assigned to a message by the ESA's Advanced Malware Protection (AMP). A verdict can be either clean (indicating that the message does not contain any known viruses or malware) or malicious (indicating that the message contains one or more viruses or malware). |
cisco.esa.protection.antivirus.verdict |
keyword |
This field indicates the verdict assigned to a message by the ESA's antivirus protection mechanism. A verdict can be either clean (indicating that the message does not contain any known viruses or malware) or infected (indicating that the message contains one or more viruses or malware). |
cisco.esa.protection.dlp.verdict |
keyword |
This field indicates the verdict assigned to a message by the ESA's data loss prevention (DLP) protection mechanism. DLP is a set of tools and techniques used to prevent sensitive or confidential data from being disclosed or leaked, and the verdict for a message can indicate whether it contains any such data. |
cisco.esa.protection.graymail.verdict |
keyword |
This field indicates the verdict assigned to a message by the ESA's graymail protection mechanism. A verdict can be either NOT EVALUATED (indicating that the message has not been processed) POSITIVE (indicating that the message is considered as a graymail such as Marketing Email, Social Network Email, Bulk Email... ) or NEGATIVE (indicating that the message is not considered as a graymail) |
cisco.esa.protection.spam.verdict |
keyword |
This field indicates the verdict assigned to a message by the ESA's spam protection mechanism. A verdict can be either spam (indicating that the message is likely unwanted or malicious) or not spam (indicating that the message is legitimate). |
cisco.esa.sender_group |
keyword |
This field refers to the sender group assigned to a message by the ESA. A sender group is a way to categorize email senders based on various criteria, such as domain name, IP address, or other attributes. By assigning a sender group to a message, the ESA can apply different policies or filtering rules based on the characteristics of the sender. |
cisco.esa.source.domain.age |
keyword |
This field indicates the age of the domain associated with the sender of a message. Older domains are generally considered more trustworthy than newer domains, so this field can be used as a factor in determining whether a message is legitimate or spam. |
cisco.esa.status |
keyword |
|
cisco.esa.url |
keyword |
the declaration of the cisco urls |
cisco.esa.url_domain |
keyword |
|
email.attachments |
nested |
List of objects describing the attachments. |
email.from.address |
array |
A list of source email |
email.local_id |
keyword |
Unique identifier given by the source. |
email.message_id |
wildcard |
Value from the Message-ID header. |
email.reply_to.address |
keyword |
Address replies should be delivered to. |
email.subject |
keyword |
The subject of the email message. |
email.to.address |
array |
A list of destination email |
event.action |
keyword |
The action captured by the event. |
event.end |
date |
event.end contains the date when the event ended or when the activity was last observed. |
event.severity |
long |
Numeric severity of the event. |
event.start |
date |
event.start contains the date when the event started or when the activity was first observed. |
host.hostname |
keyword |
Hostname of the host. |
host.id |
keyword |
Unique host id. |
host.name |
keyword |
Name of the host. |
log.syslog.facility.name |
keyword |
Syslog text-based facility of the event. |
observer.egress.interface.name |
keyword |
Interface name |
observer.ingress.interface.name |
keyword |
Interface name |
observer.type |
keyword |
The type of the observer the data is coming from. |
observer.vendor |
keyword |
Vendor name of the observer. |
observer.version |
keyword |
Observer version. |
rule.name |
keyword |
Rule name |
server.ip |
ip |
IP address of the server. |
source.ip |
ip |
IP address of the source. |
tls.cipher |
keyword |
String indicating the cipher used during the current connection. |
tls.client.supported_ciphers |
keyword |
Array of ciphers offered by the client during the client hello. |
tls.established |
boolean |
Boolean flag indicating if the TLS negotiation was successful and transitioned to an encrypted tunnel. |
tls.version |
keyword |
Numeric part of the version parsed from the original string. |
tls.version_protocol |
keyword |
Normalized lowercase protocol name parsed from original string. |
url.domain |
keyword |
Domain of the url. |
url.original |
wildcard |
Unmodified original url as seen in the event source. |
user_agent.original |
keyword |
Unparsed user_agent string. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.