HornetSecurity Spam and Malware Protection
Overview
Hornetsecurity is a leading provider of cloud-based email security and data protection services. Our solutions are designed to protect businesses from spam, malware, phishing, and other email-borne threats. With a focus on simplicity and reliability, Hornetsecurity offers advanced threat protection, email archiving, encryption, and continuity services to ensure secure and uninterrupted communication for organizations of all sizes.
- Vendor: Hornetsecurity
- Supported environment: Control Panel
- Detection based on: Telemetry
- Supported application or feature: Email gateway, Anti-virus
Warning
Important note - This format is currently in beta. We highly value your feedback to improve its performance.
Configure
Create a Token in the Hornetsecurity Control Panel
- Go to the Hornetsecurity Control Panel.
-
Sign in with your credentials.
-
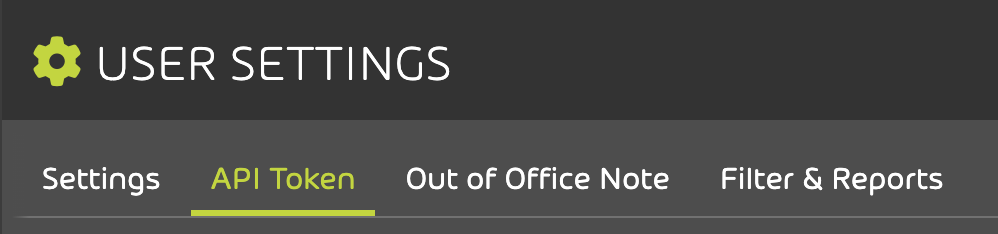
In the top-right menu, click on User settings.

-
On the User settings page, go to the API Token tab.
-
Click on the Create token button.
-
Enter a name for your token, then click Create.

-
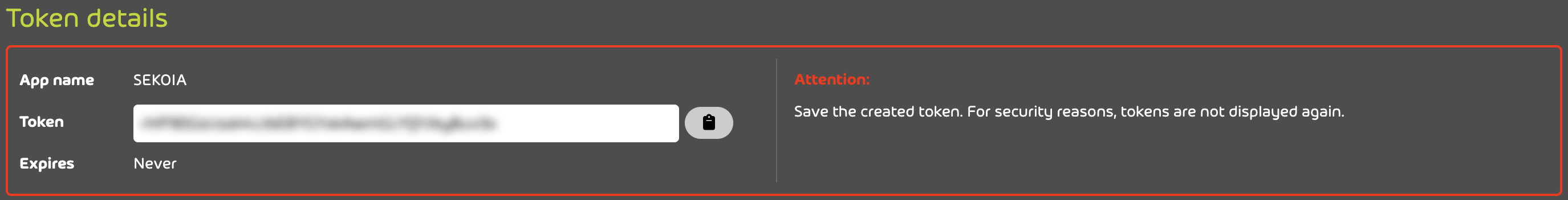
Copy your token from the Token details section.
-
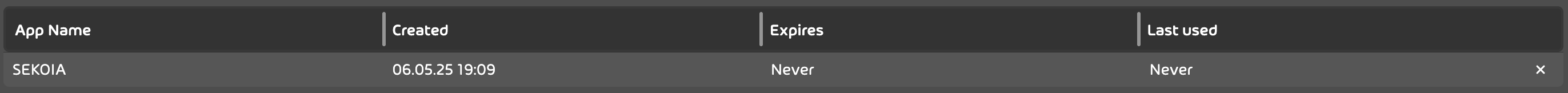
You can view your token(s), expiration date(s), and other details in the table on this page.
Create your intake
- Go to the intake page and create a new intake from the
HornetSecurity Spam and Malware Protection. - Set the intake account configuration with the
api_tokenand thebase_urlfrom the previous step.
Enjoy your events on the Events page
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
{
"direction": 1,
"date": "2025-06-12T14:26:00Z",
"msg_id": "11111111111111111111111111111111111111111111111111111111111111111",
"source_hostname": "malicious.example.com",
"destination_hostname": "smtp.example.net",
"gateway": "mx-gate1-ex",
"source_ip": "1.2.3.4",
"destination_ip": "5.6.7.8",
"message_id": "1111111111111111111111111111111111111111",
"smtp_dialog": [
"2025-06-12T14:26:00Z;SMTP;smtp.example.net[5.6.7.8];250 2.0.0 Ok: queued as F127D17407D7;END_SEND;CIPHER=NONE;IDENTITY=NONE;TLS_VER=NONE;TLS_CSUITE=NONE;TLS_WARN=NONE"
],
"smtp_status": "2025-06-12T14:26:00Z;SMTP;smtp.example.net[5.6.7.8];250 2.0.0 Ok: queued as F127D17407D7;END_SEND;CIPHER=NONE;IDENTITY=NONE;TLS_VER=NONE;TLS_CSUITE=NONE;TLS_WARN=NONE",
"owner": "test@example.net",
"owner_domain": "example.net",
"comm_partner": "malicious@example.com",
"smtp_status_code": 250,
"last_remediation_actions": "",
"last_remediation_type": "",
"last_remediation_folder": "",
"last_remediation_effectiveness": "",
"last_report_type": "",
"has_url_rewritten": false,
"history": "",
"is_archived": false,
"fix_ids": "",
"es_mail_id": "rk5Jm1-BQEmieVi61uwiX",
"crypt_type_in": {
"id": 7,
"text": "TLS"
},
"crypt_type_out": {
"id": 1,
"text": "NONE"
},
"classification": {
"id": 2,
"text": "clean"
},
"status": {
"id": 1,
"text": "Delivered"
},
"size": {
"value": 0,
"unit": "KB"
},
"private": false,
"reason": "good sender reputation",
"subject": "ELT Log Event [ID:07b1578b73e9e928] [20250612-1625] [To:test@example.com]",
"attachments": [],
"last_remediation": {
"remediation_type": null,
"remediation_actions": null,
"remediation_folder": null,
"remediation_tag": null,
"remediation_effectiveness": false,
"report_type": null,
"has_url_rewritten": false
},
"raw_header": "Received: from malicious.example.com (1.2.3.4) by mx-gate1-ex.example.com;\n Thu, 12 Jun 2025 16:26:00 +0200\nFrom: malicious@example.com\nTo: test@example.net\nSubject: Test 12345\nX-antispameurope-MSGID: 11111111111111111111111111111111111111111111111111111111111111111\nX-antispameurope-Spamstatus:CLEAN\nX-antispameurope-Virusscan:CLEAN"
}
{
"direction": 0,
"date": "2025-06-12T14:26:00Z",
"msg_id": "11111111111111111111111111111111111111111111111111111111111111111",
"source_hostname": "malicious.example.com",
"destination_hostname": "smtp.example.net",
"gateway": "mx-gate1-ex",
"source_ip": "1.2.3.4",
"destination_ip": "5.6.7.8",
"message_id": "1111111111111111111111111111111111111111",
"smtp_dialog": [
"2025-06-12T14:26:00Z;SMTP;smtp.example.net[5.6.7.8];250 2.0.0 Ok: queued as F127D17407D7;END_SEND;CIPHER=NONE;IDENTITY=NONE;TLS_VER=NONE;TLS_CSUITE=NONE;TLS_WARN=NONE"
],
"smtp_status": "2025-06-12T14:26:00Z;SMTP;smtp.example.net[5.6.7.8];250 2.0.0 Ok: queued as F127D17407D7;END_SEND;CIPHER=NONE;IDENTITY=NONE;TLS_VER=NONE;TLS_CSUITE=NONE;TLS_WARN=NONE",
"owner": "test@example.net",
"owner_domain": "example.net",
"comm_partner": "malicious@example.com",
"smtp_status_code": 250,
"last_remediation_actions": [
"Test action"
],
"last_remediation_type": "",
"last_remediation_folder": "",
"last_remediation_effectiveness": "",
"last_report_type": "",
"has_url_rewritten": false,
"history": "",
"is_archived": false,
"fix_ids": "",
"es_mail_id": "rk5Jm1-BQEmieVi61uwiX",
"crypt_type_in": {
"id": 7,
"text": "TLS"
},
"crypt_type_out": {
"id": 1,
"text": "NONE"
},
"classification": {
"id": 2,
"text": "clean"
},
"status": {
"id": 1,
"text": "Delivered"
},
"size": {
"value": 0,
"unit": "KB"
},
"private": false,
"reason": "good sender reputation",
"subject": "ELT Log Event [ID:07b1578b73e9e928] [20250612-1625] [To:test@example.com]",
"attachments": [],
"last_remediation": {
"remediation_type": null,
"remediation_actions": null,
"remediation_folder": null,
"remediation_tag": null,
"remediation_effectiveness": false,
"report_type": null,
"has_url_rewritten": false
},
"raw_header": "Received: from malicious.example.com (1.2.3.4) by mx-gate1-ex.example.com;\n Thu, 12 Jun 2025 16:26:00 +0200\nFrom: malicious@example.com\nTo: test@example.net\nSubject: Test 12345\nX-antispameurope-MSGID: 11111111111111111111111111111111111111111111111111111111111111111\nX-antispameurope-Spamstatus:CLEAN\nX-antispameurope-Virusscan:CLEAN"
}
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Email gateway |
Hornetsecurity provides email protection from phishing, malware, and spam. |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | `` |
| Category | email |
| Type | info |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "{\n \"direction\": 1,\n \"date\": \"2025-06-12T14:26:00Z\",\n \"msg_id\": \"11111111111111111111111111111111111111111111111111111111111111111\",\n \"source_hostname\": \"malicious.example.com\",\n \"destination_hostname\": \"smtp.example.net\",\n \"gateway\": \"mx-gate1-ex\",\n \"source_ip\": \"1.2.3.4\",\n \"destination_ip\": \"5.6.7.8\",\n \"message_id\": \"1111111111111111111111111111111111111111\",\n \"smtp_dialog\": [\n \"2025-06-12T14:26:00Z;SMTP;smtp.example.net[5.6.7.8];250 2.0.0 Ok: queued as F127D17407D7;END_SEND;CIPHER=NONE;IDENTITY=NONE;TLS_VER=NONE;TLS_CSUITE=NONE;TLS_WARN=NONE\"\n ],\n \"smtp_status\": \"2025-06-12T14:26:00Z;SMTP;smtp.example.net[5.6.7.8];250 2.0.0 Ok: queued as F127D17407D7;END_SEND;CIPHER=NONE;IDENTITY=NONE;TLS_VER=NONE;TLS_CSUITE=NONE;TLS_WARN=NONE\",\n \"owner\": \"test@example.net\",\n \"owner_domain\": \"example.net\",\n \"comm_partner\": \"malicious@example.com\",\n \"smtp_status_code\": 250,\n \"last_remediation_actions\": \"\",\n \"last_remediation_type\": \"\",\n \"last_remediation_folder\": \"\",\n \"last_remediation_effectiveness\": \"\",\n \"last_report_type\": \"\",\n \"has_url_rewritten\": false,\n \"history\": \"\",\n \"is_archived\": false,\n \"fix_ids\": \"\",\n \"es_mail_id\": \"rk5Jm1-BQEmieVi61uwiX\",\n \"crypt_type_in\": {\n \"id\": 7,\n \"text\": \"TLS\"\n },\n \"crypt_type_out\": {\n \"id\": 1,\n \"text\": \"NONE\"\n },\n \"classification\": {\n \"id\": 2,\n \"text\": \"clean\"\n },\n \"status\": {\n \"id\": 1,\n \"text\": \"Delivered\"\n },\n \"size\": {\n \"value\": 0,\n \"unit\": \"KB\"\n },\n \"private\": false,\n \"reason\": \"good sender reputation\",\n \"subject\": \"ELT Log Event [ID:07b1578b73e9e928] [20250612-1625] [To:test@example.com]\",\n \"attachments\": [],\n \"last_remediation\": {\n \"remediation_type\": null,\n \"remediation_actions\": null,\n \"remediation_folder\": null,\n \"remediation_tag\": null,\n \"remediation_effectiveness\": false,\n \"report_type\": null,\n \"has_url_rewritten\": false\n },\n \"raw_header\": \"Received: from malicious.example.com (1.2.3.4) by mx-gate1-ex.example.com;\\n Thu, 12 Jun 2025 16:26:00 +0200\\nFrom: malicious@example.com\\nTo: test@example.net\\nSubject: Test 12345\\nX-antispameurope-MSGID: 11111111111111111111111111111111111111111111111111111111111111111\\nX-antispameurope-Spamstatus:CLEAN\\nX-antispameurope-Virusscan:CLEAN\"\n}",
"event": {
"action": "No action",
"category": [
"email"
],
"reason": "good sender reputation",
"type": [
"info"
]
},
"@timestamp": "2025-06-12T14:26:00Z",
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8"
},
"email": {
"direction": "Incoming",
"from": {
"address": [
"malicious@example.com"
]
},
"message_id": "1111111111111111111111111111111111111111",
"subject": "ELT Log Event [ID:07b1578b73e9e928] [20250612-1625] [To:test@example.com]",
"to": {
"address": [
"test@example.net"
]
}
},
"hornetsecurity": {
"spam_malware_protection": {
"classification": "Clean",
"crypt_type_in": "TLS",
"crypt_type_out": "NONE",
"destination_hostname": "smtp.example.net",
"gateway": "mx-gate1-ex",
"has_url_rewritten": false,
"private": false,
"size": "0 KB",
"source_hostname": "malicious.example.com",
"status": "Delivered"
}
},
"related": {
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "{\n \"direction\": 0,\n \"date\": \"2025-06-12T14:26:00Z\",\n \"msg_id\": \"11111111111111111111111111111111111111111111111111111111111111111\",\n \"source_hostname\": \"malicious.example.com\",\n \"destination_hostname\": \"smtp.example.net\",\n \"gateway\": \"mx-gate1-ex\",\n \"source_ip\": \"1.2.3.4\",\n \"destination_ip\": \"5.6.7.8\",\n \"message_id\": \"1111111111111111111111111111111111111111\",\n \"smtp_dialog\": [\n \"2025-06-12T14:26:00Z;SMTP;smtp.example.net[5.6.7.8];250 2.0.0 Ok: queued as F127D17407D7;END_SEND;CIPHER=NONE;IDENTITY=NONE;TLS_VER=NONE;TLS_CSUITE=NONE;TLS_WARN=NONE\"\n ],\n \"smtp_status\": \"2025-06-12T14:26:00Z;SMTP;smtp.example.net[5.6.7.8];250 2.0.0 Ok: queued as F127D17407D7;END_SEND;CIPHER=NONE;IDENTITY=NONE;TLS_VER=NONE;TLS_CSUITE=NONE;TLS_WARN=NONE\",\n \"owner\": \"test@example.net\",\n \"owner_domain\": \"example.net\",\n \"comm_partner\": \"malicious@example.com\",\n \"smtp_status_code\": 250,\n \"last_remediation_actions\": [\"Test action\"],\n \"last_remediation_type\": \"\",\n \"last_remediation_folder\": \"\",\n \"last_remediation_effectiveness\": \"\",\n \"last_report_type\": \"\",\n \"has_url_rewritten\": false,\n \"history\": \"\",\n \"is_archived\": false,\n \"fix_ids\": \"\",\n \"es_mail_id\": \"rk5Jm1-BQEmieVi61uwiX\",\n \"crypt_type_in\": {\n \"id\": 7,\n \"text\": \"TLS\"\n },\n \"crypt_type_out\": {\n \"id\": 1,\n \"text\": \"NONE\"\n },\n \"classification\": {\n \"id\": 2,\n \"text\": \"clean\"\n },\n \"status\": {\n \"id\": 1,\n \"text\": \"Delivered\"\n },\n \"size\": {\n \"value\": 0,\n \"unit\": \"KB\"\n },\n \"private\": false,\n \"reason\": \"good sender reputation\",\n \"subject\": \"ELT Log Event [ID:07b1578b73e9e928] [20250612-1625] [To:test@example.com]\",\n \"attachments\": [],\n \"last_remediation\": {\n \"remediation_type\": null,\n \"remediation_actions\": null,\n \"remediation_folder\": null,\n \"remediation_tag\": null,\n \"remediation_effectiveness\": false,\n \"report_type\": null,\n \"has_url_rewritten\": false\n },\n \"raw_header\": \"Received: from malicious.example.com (1.2.3.4) by mx-gate1-ex.example.com;\\n Thu, 12 Jun 2025 16:26:00 +0200\\nFrom: malicious@example.com\\nTo: test@example.net\\nSubject: Test 12345\\nX-antispameurope-MSGID: 11111111111111111111111111111111111111111111111111111111111111111\\nX-antispameurope-Spamstatus:CLEAN\\nX-antispameurope-Virusscan:CLEAN\"\n}",
"event": {
"action": "Test action",
"category": [
"email"
],
"reason": "good sender reputation",
"type": [
"info"
]
},
"@timestamp": "2025-06-12T14:26:00Z",
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8"
},
"email": {
"direction": "Outgoing",
"from": {
"address": [
"test@example.net"
]
},
"message_id": "1111111111111111111111111111111111111111",
"subject": "ELT Log Event [ID:07b1578b73e9e928] [20250612-1625] [To:test@example.com]",
"to": {
"address": [
"malicious@example.com"
]
}
},
"hornetsecurity": {
"spam_malware_protection": {
"classification": "Clean",
"crypt_type_in": "TLS",
"crypt_type_out": "NONE",
"destination_hostname": "smtp.example.net",
"gateway": "mx-gate1-ex",
"has_url_rewritten": false,
"private": false,
"size": "0 KB",
"source_hostname": "malicious.example.com",
"status": "Delivered"
}
},
"related": {
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
destination.domain |
keyword |
The domain name of the destination. |
destination.ip |
ip |
IP address of the destination. |
email.direction |
keyword |
Direction of the message. |
email.from.address |
keyword |
The sender's email address. |
email.message_id |
wildcard |
Value from the Message-ID header. |
email.subject |
keyword |
The subject of the email message. |
email.to.address |
keyword |
Email address of recipient |
event.action |
keyword |
The action captured by the event. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.reason |
keyword |
Reason why this event happened, according to the source |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
hornetsecurity.spam_malware_protection.classification |
keyword |
The category in which the email was classified. |
hornetsecurity.spam_malware_protection.crypt_type_in |
keyword |
The used encryption method for inbound mail traffic to the gate. |
hornetsecurity.spam_malware_protection.crypt_type_out |
keyword |
The used encryption method for outbound mail traffic from the gate. |
hornetsecurity.spam_malware_protection.destination_hostname |
keyword |
The hostname of the destination mailserver. |
hornetsecurity.spam_malware_protection.gateway |
keyword |
The hostname of the gateway where the email was processed. |
hornetsecurity.spam_malware_protection.has_url_rewritten |
boolean |
Indicates whether the URLs in the email have been rewritten. |
hornetsecurity.spam_malware_protection.private |
boolean |
Whether the email is marked as private. |
hornetsecurity.spam_malware_protection.size |
keyword |
The size of the email including attachments. |
hornetsecurity.spam_malware_protection.source_hostname |
keyword |
The hostname of the source mailserver. |
hornetsecurity.spam_malware_protection.status |
keyword |
The delivery status of the email. |
source.ip |
ip |
IP address of the source. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.