Office 365
Overview
- Vendor: Microsoft
- Supported environment: Cloud
- Detection based on: Telemetry / Alert
- Supported application or feature:
Office 365 is a line of subscription services offered by Microsoft as part of the Microsoft Office product line.
Microsoft Office365 logs
Sekoia.io can pull four categories of logs from Microsoft Office 365 Management API:
- Microsoft Entra ID (Azure AD) audit events (
Audit.AzureActiveDirectory) - Microsoft Exchange audit events (
Audit.Exchange) - Microsoft SharePoint audit events (
Audit.SharePoint) - General audit events not included in the other log categories (
Audit.General)
The Office 365 Management Activity API Schema documents the schema leveraged by Sekoia.io to monitor activities within your organization.
The Audit logging is turned on by default for Microsoft 365 and Office 365 enterprise organizations. However, when setting up an organization, you should verify the auditing status.
Microsoft provides instructions to verify and configure the auditing status for your organization in the article Turn auditing on or off.
Configure
Prerequisites
To send Microsoft 365 logs to Sekoia.io, there are some prerequisites:
- Have access to the Sekoia.io XDR Operations Center
- Be a Microsoft Office 365 Administrator (role
Global Administrator) to consent to the interconnection - Have auditing turned on for your organization (see Turn auditing on or off)
Important
Audit log activation can take up to 60 minutes to take effect on Office365 (see Office365 documentation).
Until the activation is completed, the integration will not be able to collect any logs and may face errors (e.g: tenant not found).
Please wait for the activation to be completed before creating the intake on Sekoia.io.
To generate logs:
-
For some advanced logs, an Azure Premium P1 or Azure Premium P2 license may be required.
-
Configure the Microsoft Office 365 logging in Sekoia.io XDR
Collect events
Create an Azure application
- On the Azure Portal, in the search bar, go to
App registrations - Click
+ New registration - Type a name
- Select
Accounts in this organizational directory onlyoption as account type - Click
Register - From the
Overviewpage, copyApplication (client) IDandDirectory (tenant) ID
Create a client secret
- Go to
Manage>Certificates & secrets - Click
+ New client secret - Type a description and select the desirated expiration period
- Click
Add - Copy the
Valueof the client secret
Add permissions
- Go to
Manage>API permissions - Click
Add a permissions - On the right panel, Select
APIs my organization usestab - Click
Office 365 Management APIs - Click
Application permissions - Select
ActivityFeed.Read - Click
Add permissions - In the
API permissionspage, clickGrant admin consent for TENANT_NAME - Click
Yesin theGrant admin consent confirmationmodal
Add role
- On the Azure Portal, in the search bar, go to
Microsoft Entra ID - Go to
Manage>Roles and administrators - Search and open
Global Reader - Use the
+ Add assignmentsto add this role to your application
For a detailed explanation, please read the related documentation Azure portal - Assign a role.
Create your intake
Go to your Sekoia.io Intakes page, and follow these steps:
- Click
+ Intakebutton to create a new one - Choose
Microsoft 365/Office 365, give it a name and choose the relevant Entity - Edit the intake configuration:
- Type the
Application (client) IDin theclient idfield - Type the
Directory (tenant) IDin thetenant idfield - Type the
Valueof the client secret in theclient secretfield
- Type the
Important
Once the integration is created on Sekoia.io, it may take up to 12 hours for the Microsoft API to make data available for the first time. After validation from the Microsoft API, it will take at least 15 minutes to retrieve the first events. Refer to this guide for instructions on how to enable or verify the activation status of audit logs in Office 365.
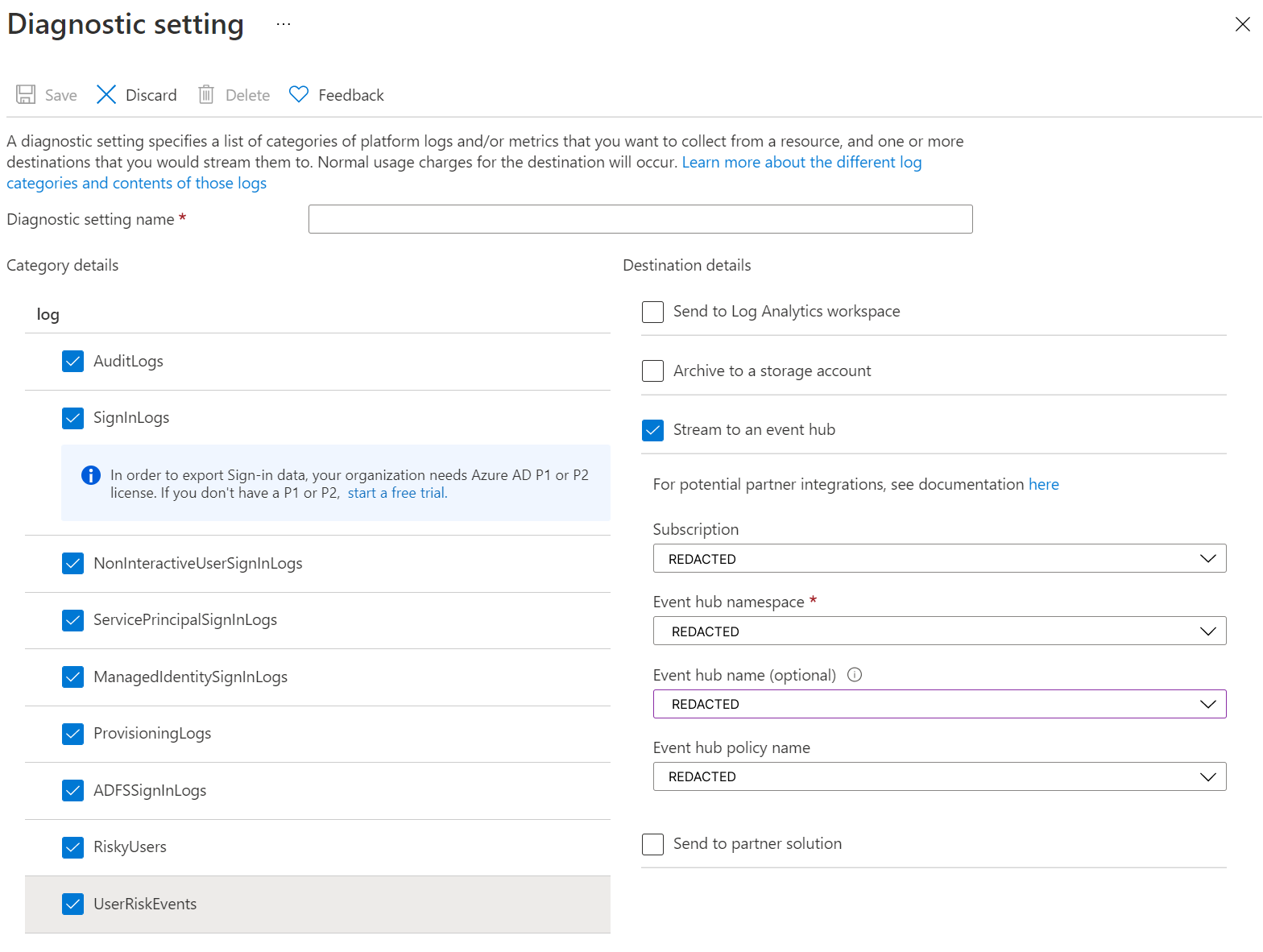
Alternative mode
If you are unable or you don't want to collect Office 365 logs through the management API, Sekoia.io also supports Office 365 log collection through Azure EventHub. Follow this guide for more details on this solution.
Collect Microsoft Defender for Office365 events
If your organization use Microsoft Defender for Office 365, you can forward malware and threat intelligence events to Sekoia.io. Refer to this guide to turn on Defender events in the audit logs. These events will be automatically forward with the Office365 integration.
Enjoy your events
You can go to the events page to access your incoming events.
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
{
"CreationTime": "2020-09-29T08:59:26",
"Id": "e1717ca5-c13e-4382-ad7e-4864faa11e85",
"Operation": "UserLoggedIn",
"OrganizationId": "ANONYMIZED",
"RecordType": 15,
"ResultStatus": "Succeeded",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ClientIP": "1.2.3.4",
"ObjectId": "cc15fd57-2c6c-4117-a88c-83b1d56b4bbe",
"UserId": "user1",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "UserAgent",
"Value": "Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.121 Safari/537.36"
},
{
"Name": "UserAuthenticationMethod",
"Value": "1"
},
{
"Name": "RequestType",
"Value": "OAuth2:Authorize"
},
{
"Name": "ResultStatusDetail",
"Value": "Redirect"
},
{
"Name": "KeepMeSignedIn",
"Value": "True"
}
],
"ModifiedProperties": [],
"Actor": [
{
"ID": "cb42ef6c-989f-49d0-86cd-7706b8d14528",
"Type": 0
},
{
"ID": "user1",
"Type": 5
},
{
"ID": "10030000A9F382C6",
"Type": 3
}
],
"ActorContextId": "ANONYMIZED",
"ActorIpAddress": "1.2.3.4",
"InterSystemsId": "d23dd5d2-ccc8-4928-b7a0-f446a2ca4a90",
"IntraSystemId": "a196489a-9a7c-4824-b35a-5bfdec600c00",
"SupportTicketId": "",
"Target": [
{
"ID": "cc15fd57-2c6c-4117-a88c-83b1d56b4bbe",
"Type": 0
}
],
"TargetContextId": "ANONYMIZED",
"ApplicationId": "5e3ce6c0-2b1f-4285-8d4b-75ee78787346"
}
{
"CreationTime": "2023-08-22T13:51:38",
"Id": "3e4f9ff8",
"Operation": "UserLoggedIn",
"OrganizationId": "ANONYMIZED",
"RecordType": 15,
"ResultStatus": "Success",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ClientIP": "1.2.3.4",
"ObjectId": "16aeb910",
"UserId": "user1",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "ResultStatusDetail",
"Value": "Success"
},
{
"Name": "UserAgent",
"Value": "Mozilla/5.0"
},
{
"Name": "RequestType",
"Value": "OAuth2:Token"
}
],
"ModifiedProperties": [],
"Actor": [
{
"ID": "user1",
"Type": 0
},
{
"ID": "joe.doe@user.fr",
"Type": 5
}
],
"ActorContextId": "ANONYMIZED",
"ActorIpAddress": "1.2.3.4",
"InterSystemsId": "d8254b84",
"IntraSystemId": "3e4f9ff8",
"SupportTicketId": "",
"Target": [
{
"ID": "16aeb910",
"Type": 0
}
],
"TargetContextId": "ANONYMIZED",
"ApplicationId": "1b3c667f",
"DeviceProperties": [
{
"Name": "OS",
"Value": "Windows10"
},
{
"Name": "BrowserType",
"Value": "Edge"
},
{
"Name": "IsCompliantAndManaged",
"Value": "False"
},
{
"Name": "SessionId",
"Value": "8e2cdebf"
}
],
"ErrorNumber": "0"
}
{
"CreationTime": "2025-11-18T19:56:44",
"Id": "99999999-9999-9999-9999-999999999999",
"Operation": "Consent to application.",
"OrganizationId": "redacted",
"RecordType": 8,
"ResultStatus": "Success",
"UserKey": "1234567890@example.com",
"UserType": 0,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ObjectId": "11111111-1111-1111-1111-111111111111",
"UserId": "john.doe@example.com",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "additionalDetails",
"Value": "{\"User-Agent\":\"EvoSTS\",\"AppId\":\"11111111-1111-1111-1111-111111111111\"}"
},
{
"Name": "extendedAuditEventCategory",
"Value": "ServicePrincipal"
}
],
"ModifiedProperties": [
{
"Name": "ConsentContext.IsAdminConsent",
"NewValue": "False",
"OldValue": ""
},
{
"Name": "ConsentContext.IsAppOnly",
"NewValue": "False",
"OldValue": ""
},
{
"Name": "ConsentContext.OnBehalfOfAll",
"NewValue": "False",
"OldValue": ""
},
{
"Name": "ConsentContext.Tags",
"NewValue": "WindowsAzureActiveDirectoryIntegratedApp",
"OldValue": ""
},
{
"Name": "ConsentAction.Permissions",
"NewValue": "[] => [[Id: REDACTED, ClientId: 33333333-3333-3333-3333-333333333333, PrincipalId: 55555555-5555-5555-5555-555555555555, ResourceId: 22222222-1111-1111-1111-222222222222, ConsentType: Principal, Scope: openid profile email offline_access, CreatedDateTime: , LastModifiedDateTime ]]; ",
"OldValue": ""
},
{
"Name": "TargetId.ServicePrincipalNames",
"NewValue": "11111111-1111-1111-1111-111111111111",
"OldValue": ""
}
],
"Actor": [
{
"ID": "john.doe@example.com",
"Type": 5
},
{
"ID": "1234567890",
"Type": 3
},
{
"ID": "Azure ESTS Service",
"Type": 1
},
{
"ID": "44444444-4444-4444-4444-444444444444",
"Type": 2
},
{
"ID": "User_55555555-5555-5555-5555-555555555555",
"Type": 2
},
{
"ID": "55555555-5555-5555-5555-555555555555",
"Type": 2
},
{
"ID": "User",
"Type": 2
}
],
"ActorContextId": "redacted",
"InterSystemsId": "77777777-7777-7777-7777-777777777777",
"IntraSystemId": "66666666-6666-6666-6666-666666666666",
"SupportTicketId": "",
"Target": [
{
"ID": "ServicePrincipal_33333333-3333-3333-3333-333333333333",
"Type": 2
},
{
"ID": "33333333-3333-3333-3333-333333333333",
"Type": 2
},
{
"ID": "ServicePrincipal",
"Type": 2
},
{
"ID": "APPNAME",
"Type": 1
},
{
"ID": "11111111-1111-1111-1111-111111111111",
"Type": 2
},
{
"ID": "11111111-1111-1111-1111-111111111111",
"Type": 4
}
],
"TargetContextId": "redacted",
"AssociatedAdminUnits": [
"88888888-8888-8888-8888-888888888888"
]
}
{
"CreationTime": "2026-01-27T20:11:38",
"Id": "44444444-4444-4444-4444-444444444444",
"Operation": "Update PasswordProfile.",
"OrganizationId": "22222222-2222-2222-2222-222222222222",
"RecordType": 8,
"ResultStatus": "Success",
"UserKey": "Not Available",
"UserType": 4,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ObjectId": "jonh.doe@example.com",
"UserId": "ServicePrincipal_66666666-6666-6666-6666-666666666666",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "AdministrativeUnit",
"Value": "33333333-3333-3333-3333-333333333333"
},
{
"Name": "additionalDetails",
"Value": "{}"
},
{
"Name": "extendedAuditEventCategory",
"Value": "User"
}
],
"ModifiedProperties": [
{
"Name": "Password",
"NewValue": "",
"OldValue": ""
},
{
"Name": "ActorId.ServicePrincipalNames",
"NewValue": "https://passwordreset.microsoftonline.com;https://passwordreset.microsoftonline.com/;55555555-5555-5555-5555-555555555555;SelfServicePasswordReset",
"OldValue": ""
},
{
"Name": "SPN",
"NewValue": "https://passwordreset.microsoftonline.com;https://passwordreset.microsoftonline.com/;55555555-5555-5555-5555-555555555555;SelfServicePasswordReset",
"OldValue": ""
}
],
"Actor": [
{
"ID": "Microsoft password reset service",
"Type": 1
},
{
"ID": "55555555-5555-5555-5555-555555555555",
"Type": 2
},
{
"ID": "ServicePrincipal_66666666-6666-6666-6666-666666666666",
"Type": 2
},
{
"ID": "66666666-6666-6666-6666-666666666666",
"Type": 2
},
{
"ID": "ServicePrincipal",
"Type": 2
}
],
"ActorContextId": "22222222-2222-2222-2222-222222222222",
"InterSystemsId": "11111111-1111-1111-1111-111111111111",
"IntraSystemId": "88888888-8888-8888-8888-888888888888",
"SupportTicketId": "",
"Target": [
{
"ID": "User_77777777-7777-7777-7777-777777777777",
"Type": 2
},
{
"ID": "77777777-7777-7777-7777-777777777777",
"Type": 2
},
{
"ID": "User",
"Type": 2
},
{
"ID": "jonh.doe@example.com",
"Type": 5
},
{
"ID": "55555555555555555",
"Type": 3
}
],
"TargetContextId": "22222222-2222-2222-2222-222222222222"
}
{
"CreationTime": "2024-07-10T14:25:49",
"Id": "b4f48141-a2fe-4d47-9f0d-f09f26307035",
"Operation": "Add member to role.",
"OrganizationId": "ANONYMIZED",
"RecordType": 8,
"ResultStatus": "Success",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ObjectId": "john.doe@example.com",
"UserId": "user1",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "additionalDetails",
"Value": "{}"
},
{
"Name": "extendedAuditEventCategory",
"Value": "Role"
}
],
"ModifiedProperties": [
{
"Name": "Role.ObjectID",
"NewValue": "54fc7176-29ef-4b41-808f-3cdeb8010649",
"OldValue": ""
},
{
"Name": "Role.DisplayName",
"NewValue": "Global Administrator",
"OldValue": ""
},
{
"Name": "Role.TemplateId",
"NewValue": "ad1cbca4-efcc-4149-b4a2-aeb40412fe48",
"OldValue": ""
},
{
"Name": "Role.WellKnownObjectName",
"NewValue": "TenantAdmins",
"OldValue": ""
}
],
"Actor": [
{
"ID": "user1",
"Type": 5
},
{
"ID": "100320029D963D0D",
"Type": 3
},
{
"ID": "User_576409b5-84f3-4791-8e3c-c9677e3bd898",
"Type": 2
},
{
"ID": "576409b5-84f3-4791-8e3c-c9677e3bd898",
"Type": 2
},
{
"ID": "User",
"Type": 2
}
],
"ActorContextId": "ANONYMIZED",
"InterSystemsId": "5a0910e4-c125-4b46-9616-0232d14915dc",
"IntraSystemId": "fb6cd132-f8e8-4ec5-9a0b-4ec8397e1405",
"SupportTicketId": "",
"Target": [
{
"ID": "User_46522b15-1bf5-4bed-8a6c-4edc58c05b23",
"Type": 2
},
{
"ID": "46522b15-1bf5-4bed-8a6c-4edc58c05b23",
"Type": 2
},
{
"ID": "User",
"Type": 2
},
{
"ID": "john.doe@example.com",
"Type": 5
},
{
"ID": "100320029D9D1C86",
"Type": 3
}
],
"TargetContextId": "ANONYMIZED"
}
{
"CreationTime": "2023-04-17T14:27:09",
"Id": "60eaf0aa-edc3-4f8d-8275-bc82d9500e59",
"Operation": "AirInvestigationData",
"OrganizationId": "ANONYMIZED",
"RecordType": 64,
"UserKey": "user1",
"UserType": 4,
"Version": 1,
"Workload": "user1",
"ObjectId": "60eaf0aa-edc3-4f8d-8275-bc82d9500e59",
"UserId": "user1",
"DeepLinkUrl": "https://security.microsoft.com/mtp-investigation/urn:ZappedUrlInvestigation:a10a976",
"EndTimeUtc": "2023-04-17T14:27:07",
"InvestigationId": "urn:ZappedUrlInvestigation:a10a976d-6e3e-4d10-be50-4907183b6f86",
"InvestigationName": "Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:a1",
"InvestigationType": "ZappedUrlInvestigation",
"LastUpdateTimeUtc": "2023-04-17T14:21:59",
"RunningTime": 931,
"StartTimeUtc": "2023-04-17T14:11:38",
"Status": "Remediated",
"Data": "{\"Version\":\"3.0\",\"VendorName\":\"Microsoft\",\"ProviderName\":\"OATP\",\"AlertType\":\"alert_type_value\",\"Status\":\"status_value\",\"Severity\":\"severity_value\",\"IsIncident\":true,\"CorrelationKey\":\"correlation_key_value\",\"Category\":\"category_value\",\"SourceAlertType\":\"source_alert_type_value\",\"MachineName\":\"machine_name_value\"}",
"Actions": [
"{\"$id\":\"1\",\"ActionId\":\"urn:EmailZapper:8ad9417586e14790ba2afed0a7840e65\"}"
]
}
{
"CreationTime": "2024-10-31T16:24:41",
"Id": "c3ebef20-fb63-4d14-b3c1-7bfb5937903a",
"Operation": "AirInvestigationData",
"OrganizationId": "ANONYMIZED",
"RecordType": 64,
"UserKey": "user1",
"UserType": 4,
"Version": 1,
"Workload": "user1",
"ObjectId": "c3ebef20-fb63-4d14-b3c1-7bfb5937903a",
"UserId": "user1",
"Actions": [
"{\"$id\":\"1\",\"ActionId\":\"urn:EmailZapper:a17bc80a136cbf4f5d4e82f43a9a3d1d\",\"InvestigationId\":\"urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101\",\"ActionApproval\":\"None\",\"ActionType\":\"EmailRemediation\",\"ActionStatus\":\"Pending\",\"Entities\":[{\"$id\":\"2\",\"NetworkMessageIds\":[\"24b8430c-484d-4ee0-e12b-08dcee99416a\",\"2e99f39a-c998-4d94-2085-08dce9cd0b7d\",\"0ac4ee3c-7c79-408e-76c2-08dcf4106b65\",\"fd400540-8a8d-42ae-d1f9-08dced20c42f\",\"31cfca73-f309-4e21-cbc4-08dceed074cf\",\"0491b33a-15fc-4503-9dd1-08dced818f57\",\"4b620244-917b-4a04-7416-08dcf50af378\",\"1abed68d-3b03-46bd-45e2-08dcf43fb625\",\"abb4c4a5-7049-4047-5a68-08dcec201c1f\",\"92bba720-15bc-4f09-49f2-08dcf8d738a4\",\"3d511617-b717-416c-89cf-08dcf90a51c7\",\"c3ad4b6b-0fd9-4510-4481-08dcf9043502\",\"37b236bd-ad39-41c0-3984-08dcf85e6b44\",\"a1d9684c-9982-4f80-880c-08dcf775c1a9\"],\"CountByThreatType\":{\"HighConfPhish\":5,\"Phish\":0,\"Malware\":0,\"Spam\":0,\"MaliciousUrl\":15},\"CountByProtectionStatus\":{\"Delivered\":10,\"Blocked\":4,\"DeliveredAsSpam\":1},\"CountByDeliveryLocation\":{\"Inbox\":10,\"Quarantine\":4,\"DeletedFolder\":1},\"Query\":\"( ((NormalizedUrl:\\\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en\\\") AND (ContentType: 1)) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\",\"QueryTime\":\"2024-10-31T13:31:54.2957192Z\",\"MailCount\":15,\"IsVolumeAnamoly\":false,\"ClusterSourceIdentifier\":\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en\",\"ClusterSourceType\":\"UrlThreatIndicator\",\"ClusterQueryStartTime\":\"2024-10-11T00:00:00Z\",\"ClusterQueryEndTime\":\"2024-10-31T13:31:54.2957192Z\",\"ClusterGroup\":\"UrlThreatIdentifier\",\"Type\":\"mailCluster\",\"ClusterBy\":\"NormalizedUrl;ContentType\",\"ClusterByValue\":\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en;1\",\"QueryStartTime\":\"10/11/2024 12:00:00 AM\",\"QueryTime\":\"10/31/2024 1:31:54 PM\",\"Urn\":\"urn:MailClusterEntity:cae0ce4483385c4ff176b00a0cd18f8e\",\"Source\":\"TestProvider\",\"FirstSeen\":\"2024-10-31T13:31:56\"}],\"RelatedAlertIds\":[\"fff21c13-c681-7398-1200-08dcf8958252\"],\"StartTimeUtc\":\"2024-10-31T13:33:19\",\"LastUpdateTimeUtc\":\"2024-10-31T15:28:45.1030022Z\",\"TimestampUtc\":\"2024-10-31T13:33:19\",\"BulkName\":\"Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101\",\"ResourceIdentifiers\":[{\"$id\":\"3\",\"AadTenantId\":\"xxxxxx-xxxxx-xxxxxxx-xxxxxxx-xxxxxxx\",\"Type\":\"AAD\"}],\"PendingType\":\"User\",\"LogCreationTime\":\"2024-10-31T15:28:45.1030022Z\",\"MachineName\":\"MachineNameTest\",\"Description\":\"For malicious emails, you can move to junk, soft or hard delete from user's mailbox.\"}"
],
"Data": "{\"Version\":\"3.0\",\"VendorName\":\"Microsoft\",\"ProviderName\":\"TestProvider\",\"AlertType\":\"8e6ba277-ef39-404e-aaf1-294f6d9a2b88\",\"StartTimeUtc\":\"2024-10-30T03:47:24Z\",\"EndTimeUtc\":\"2024-10-30T03:47:24Z\",\"TimeGenerated\":\"2024-10-30T03:52:49.16Z\",\"ProcessingEndTime\":\"2024-10-31T15:28:45.1030022Z\",\"Status\":\"InProgress\",\"DetectionTechnology\":\"UrlReputation\",\"Severity\":\"Informational\",\"ConfidenceLevel\":\"Unknown\",\"ConfidenceScore\":1.0,\"IsIncident\":false,\"ProviderAlertId\":\"fff21c13-c681-7398-1200-08dcf8958252\",\"SystemAlertId\":null,\"CorrelationKey\":\"bb0ac18c-5081-41e0-8656-f256ba9298d0\",\"Investigations\":[{\"$id\":\"1\",\"Id\":\"urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101\",\"InvestigationStatus\":\"Running\"}],\"InvestigationIds\":[\"urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101\"],\"Intent\":\"Probing\",\"ResourceIdentifiers\":[{\"$id\":\"2\",\"AadTenantId\":\"xxxxxx-xxxxx-xxxxxxx-xxxxxxx-xxxxxxx\",\"Type\":\"AAD\"}],\"AzureResourceId\":null,\"WorkspaceId\":null,\"WorkspaceSubscriptionId\":null,\"WorkspaceResourceGroup\":null,\"AgentId\":null,\"AlertDisplayName\":\"Email messages containing malicious URL removed after delivery\u200b\",\"Description\":\"Emails with malicious URL that were delivered and later removed -V1.0.0.3\",\"ExtendedLinks\":[{\"Href\":\"https://security.microsoft.com/alerts/fafff21c13-c681-7398-1200-08dcf8958252\",\"Category\":null,\"Label\":\"alert\",\"Type\":\"webLink\"}],\"Metadata\":{\"CustomApps\":null,\"GenericInfo\":null},\"Entities\":[{\"$id\":\"3\",\"Url\":\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en\",\"Type\":\"url\",\"ClickCount\":0,\"EmailCount\":2,\"Urn\":\"urn:UrlEntity:289101bb3aa22cd0464dcd3ffa7116a8\",\"Source\":\"TestProvider\",\"FirstSeen\":\"2024-10-31T12:58:53\"},{\"$id\":\"4\",\"Files\":[{\"$id\":\"5\",\"Name\":\"returnLabel_314378736750.pdf\",\"FileHashes\":[{\"$id\":\"6\",\"Algorithm\":\"SHA256\",\"Value\":\"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b\",\"Type\":\"filehash\"}],\"Type\":\"file\",\"MalwareFamily\":null}],\"Recipient\":\"test.to@example.com\",\"Urls\":[\"https://subexample.example.net/?REDACTED\",\"https://u25492214.ct.example.net/ls/click?upn=u001.Ni9F2bUzMGygU7I6927xz-2B7I3RFKjR2LTj-2FCdqvCgUA-3De-zv_r5YCKD565fWzehHx-2FViuB8oHOL1DYwg-2Bfx4BUmzkfTPes7sa-2BVi-2BqS9kcdV08lhzTrs-2B4Lvsupi32g3cG4FINnNbknV9eEzYIqgaa4YfaZHEEHRVUWDqycf8mgAbrzvtnOX7pQHdt3iR6DHP-2BxR3PfnH-2BDzIJZkv1MK0yzBmp6otxpVGSalyLT-2BMyMS7yEfvbLbY9v9Wjn3hkHG29S-2FBOFjoVX-2FSwv2kZeymJW-2FlgRvHCB20rH0kwYqIdOsdO-2FvuCq-2BU49-2FNEo4S2gaZRd0h3zn5MFhXxj-2F-2FbW3X5gOaGP7-2FpGN-2BX-2BHRi1Xt1JzFgCpA\",\"https://u25492214.ct.example.net/ls/click?upn=u001.Ni9F2bUzMGygU7I6927xz49R6-2B-2FASLo-2BUtlyP-2F4iSjQlm-2F4HWFki90oq-2Bc29Sr-2BJAxlu_r5YCKD565fWzehHx-2FViuB8oHOL1DYwg-2Bfx4BUmzkfTPes7sa-2BVi-2BqS9kcdV08lhzTrs-2B4Lvsupi32g3cG4FINnNbknV9eEzYIqgaa4YfaZHEEHRVUWDqycf8mgAbrzvtnOX7pQHdt3iR6DHP-2BxR3PfnH-2BDzIJZkv1MK0yzBmp6qR2GRWjTyLjKHBwmcXgTV-2BMq0R5qnuDMHYAbrFxAmtHiepp1aU8L-2FOCt-2BiboZksoqBfuo-2FcqBrfi9un8ILJByRUOZM3T6alRzsB1jmdLOKOZwr3m8kymuz3dFvNya6aYPmSZG4l57ycCGBya5xMMqf\",\"https://u25492214.ct.example.net/ls/click?upn=u001.Ni9F2bUzMGygU7I6927xz1dNl4cyoCqQhbWGcqggHJW8SDLFVls-2FdSGWRn2n26uXgiSb-2FLZ3Oc-2F6taFyBHXTJv-2BdvE0YkDtEsaWUVnnpz7Lus9fp2MjvsYOqibyuC9Sjzgm4flo2XfvY4y5mBWuQF-2F7nM55pZ5S6S-2BSuNa5j-2BID5HJzdZOlXc2nyvbxmDFrTDuau_r5YCKD565fWzehHx-2FViuB8oHOL1DYwg-2Bfx4BUmzkfTPes7sa-2BVi-2BqS9kcdV08lhzTrs-2B4Lvsupi32g3cG4FINnNbknV9eEzYIqgaa4YfaZHEEHRVUWDqycf8mgAbrzvtnOX7pQHdt3iR6DHP-2BxR3PfnH-2BDzIJZkv1MK0yzBmp6oCyme2zPY6GKJBwI7FWZYrXhePHLdzV5WL-2F5EJubwqlYflj1CI9yL7Xfb24ks7WDE2wa8hQ-2BQ3h8K7-2FNpWkzEtiEQPiPEF3zOMzaOlqjkbPLg0UzpEmObjky1BycKoXMMwtfEuHLB9VnhNmDV3aIW2\",\"https://u25492214.ct.example.net/ls/click?upn=u001.Ni9F2bUzMGygU7I6927xzwS57HzRFV06M2bzMBaRY-2BtdD2HhGOqR6HD9j7eU3woqib3lW0qFsRIYtEfnDRINtIJErjGpQG2ad3jjAbAIacwJ4Le0eScR4TY1ExyusbvGQU5p_r5YCKD565fWzehHx-2FViuB8oHOL1DYwg-2Bfx4BUmzkfTPes7sa-2BVi-2BqS9kcdV08lhzTrs-2B4Lvsupi32g3cG4FINnNbknV9eEzYIqgaa4YfaZHEEHRVUWDqycf8mgAbrzvtnOX7pQHdt3iR6DHP-2BxR3PfnH-2BDzIJZkv1MK0yzBmp6psejQMn2EzritsHjoZX3rBM6GN1Gt7OeDjl2fzK-2BAK5-2FzHIjoTmyFKIkBvxn4mrKqstgF5tkhF6rc-2BIL2TqH7FTpqHdxk6lMOLfZVS4DrhiP-2FvyHZwSo2RzY-2BDmTRvcBEOqOwutpZKgr0m7fArTF-2Fv\",\"http://shein.ltwebstatic.com/advertise/shein/www/images_sheIn/SheIn_logo1_1.png\",\"https://romwe.ltwebstatic.com/advertise/romwe/www/images_Romwe/edm3_09_2.jpg\",\"https://romwe.ltwebstatic.com/advertise/romwe/www/images_Romwe/edm3_11_1.jpg\",\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en\",\"https://fr.shein.com/\",\"https://fr.shein.com/robot\",\"https://fr.shein.com/user/order_return/order_return_label/GSONEQ62U001GKT?country=France&refund_bill_id=&return_order_id=NE91E0E8C1\",\"https://itunes.apple.com/us/app/yub-streetwear-fashion-shopping/id878577184?mt=8\"],\"Threats\":[\"ZapPhish\",\"HighConfPhish\"],\"Sender\":\"test.sender@example.com\",\"P1Sender\":\"test.sender@example.com\",\"P1SenderDomain\":\"gmail.com\",\"SenderIP\":\"1.2.3.4\",\"P2Sender\":\"test.sender@example.com\",\"P2SenderDisplayName\":\"Fanny Barriol\",\"P2SenderDomain\":\"gmail.com\",\"ReceivedDate\":\"2024-10-29T21:12:56\",\"NetworkMessageId\":\"37b236bd-ad39-41c0-3984-08dcf85e6b44\",\"InternetMessageId\":\"<CAH2_hrsct2KwUBwRFXNs9sXxZyTJMnV2f7FxaPj2eX=7y5a2Hw@mail.gmail.com>\",\"Subject\":\"Fwd: Votre \u00e9tiquette de retour de SHEIN\",\"AntispamDirection\":\"Inbound\",\"DeliveryAction\":\"Blocked\",\"ThreatDetectionMethods\":[\"UrlReputation\"],\"Language\":\"fr\",\"DeliveryLocation\":\"Quarantine\",\"OriginalDeliveryLocation\":\"Inbox\",\"PhishConfidenceLevel\":\"High\",\"AdditionalActionsAndResults\":[\"OriginalDelivery: [N/A]\",\"Zap: [Success: Message moved to quarantine]\"],\"AuthDetails\":[{\"Name\":\"SPF\",\"Value\":\"Pass\"},{\"Name\":\"DKIM\",\"Value\":\"Pass\"},{\"Name\":\"DMARC\",\"Value\":\"Pass\"},{\"Name\":\"Comp Auth\",\"Value\":\"pass\"}],\"SystemOverrides\":[],\"Type\":\"mailMessage\",\"Urn\":\"urn:MailEntity:79be71f3203d9db81f0076352eca662e\",\"Source\":\"TestProvider\",\"FirstSeen\":\"2024-10-31T12:58:53\"},{\"$id\":\"7\",\"MailboxPrimaryAddress\":\"test.to@example.com\",\"Upn\":\"test.to@example.com\",\"AadId\":\"2011d28b-3a87-4359-b2a0-7d14f0a83828\",\"RiskLevel\":\"None\",\"Type\":\"mailbox\",\"Urn\":\"urn:UserEntity:f182c190672d0194477f316c5f0367e5\",\"Source\":\"TestProvider\",\"FirstSeen\":\"2024-10-31T12:58:53\"},{\"$id\":\"8\",\"NetworkMessageIds\":[\"37b236bd-ad39-41c0-3984-08dcf85e6b44\"],\"CountByThreatType\":{\"HighConfPhish\":1,\"Phish\":0,\"Malware\":0,\"Spam\":0},\"CountByProtectionStatus\":{\"Blocked\":1},\"CountByDeliveryLocation\":{\"Quarantine\":1},\"Query\":\"( (( (BodyFingerprintBin1:\\\"2929356879\\\") ) AND ( (SenderIp:\\\"1.2.3.4\\\") ) AND ( (ContentType: 1) )) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\",\"QueryTime\":\"2024-10-31T13:31:45.0302157Z\",\"MailCount\":1,\"IsVolumeAnamoly\":false,\"ClusterSourceIdentifier\":\"37b236bd-ad39-41c0-3984-08dcf85e6b44\",\"ClusterSourceType\":\"Similarity\",\"ClusterQueryStartTime\":\"2024-10-11T00:00:00Z\",\"ClusterQueryEndTime\":\"2024-10-31T13:31:45.0302157Z\",\"ClusterGroup\":\"BodyFingerprintBin1,SenderIp\",\"Type\":\"mailCluster\",\"ClusterBy\":\"BodyFingerprintBin1;SenderIp;ContentType\",\"ClusterByValue\":\"2929356879;1.2.3.4;1\",\"QueryStartTime\":\"10/11/2024 12:00:00 AM\",\"QueryTime\":\"10/31/2024 1:31:45 PM\",\"Urn\":\"urn:MailClusterEntity:0b159e7db54d59b4165e81fb02f6c656\",\"Source\":\"TestProvider\",\"FirstSeen\":\"2024-10-31T13:31:52\"},{\"$id\":\"9\",\"NetworkMessageIds\":[\"37b236bd-ad39-41c0-3984-08dcf85e6b44\"],\"CountByThreatType\":{\"HighConfPhish\":1,\"Phish\":0,\"Malware\":0,\"Spam\":0},\"CountByProtectionStatus\":{\"Blocked\":1},\"CountByDeliveryLocation\":{\"Quarantine\":1},\"Query\":\"( (( (Subject:\\\"Fwd: Votre \u00e9tiquette de retour de SHEIN\\\") ) AND ( (P2SenderDomain:\\\"gmail.com\\\") ) AND ( (AntispamDirection:\\\"1\\\") ) AND ( (ContentType: 1) )) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\",\"QueryTime\":\"2024-10-31T13:31:45.0302157Z\",\"MailCount\":1,\"IsVolumeAnamoly\":false,\"ClusterSourceIdentifier\":\"37b236bd-ad39-41c0-3984-08dcf85e6b44\",\"ClusterSourceType\":\"Similarity\",\"ClusterQueryStartTime\":\"2024-10-11T00:00:00Z\",\"ClusterQueryEndTime\":\"2024-10-31T13:31:45.0302157Z\",\"ClusterGroup\":\"Subject,P2SenderDomain,AntispamDirection\",\"Type\":\"mailCluster\",\"ClusterBy\":\"Subject;P2SenderDomain;AntispamDirection;ContentType\",\"ClusterByValue\":\"Fwd: Votre \u00e9tiquette de retour de SHEIN;gmail.com;1;1\",\"QueryStartTime\":\"10/11/2024 12:00:00 AM\",\"QueryTime\":\"10/31/2024 1:31:45 PM\",\"Urn\":\"urn:MailClusterEntity:5e820543f7cce922d13fcc25a0ca2204\",\"Source\":\"TestProvider\",\"FirstSeen\":\"2024-10-31T13:31:52\"},{\"$id\":\"10\",\"NetworkMessageIds\":[\"37b236bd-ad39-41c0-3984-08dcf85e6b44\"],\"CountByThreatType\":{\"HighConfPhish\":1,\"Phish\":0,\"Malware\":0,\"Spam\":0},\"CountByProtectionStatus\":{\"Blocked\":1},\"CountByDeliveryLocation\":{\"Quarantine\":1},\"Query\":\"( (( (Subject:\\\"Fwd: Votre \u00e9tiquette de retour de SHEIN\\\") ) AND ( (SenderIp:\\\"1.2.3.4\\\") ) AND ( (AntispamDirection:\\\"1\\\") ) AND ( (ContentType: 1) )) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\",\"QueryTime\":\"2024-10-31T13:31:45.0302157Z\",\"MailCount\":1,\"IsVolumeAnamoly\":false,\"ClusterSourceIdentifier\":\"37b236bd-ad39-41c0-3984-08dcf85e6b44\",\"ClusterSourceType\":\"Similarity\",\"ClusterQueryStartTime\":\"2024-10-11T00:00:00Z\",\"ClusterQueryEndTime\":\"2024-10-31T13:31:45.0302157Z\",\"ClusterGroup\":\"Subject,SenderIp,AntispamDirection\",\"Type\":\"mailCluster\",\"ClusterBy\":\"Subject;SenderIp;AntispamDirection;ContentType\",\"ClusterByValue\":\"Fwd: Votre \u00e9tiquette de retour de SHEIN;1.2.3.4;1;1\",\"QueryStartTime\":\"10/11/2024 12:00:00 AM\",\"QueryTime\":\"10/31/2024 1:31:45 PM\",\"Urn\":\"urn:MailClusterEntity:a42bb73f2f36d917364f11fe67f0c39b\",\"Source\":\"TestProvider\",\"FirstSeen\":\"2024-10-31T13:31:52\"},{\"$id\":\"11\",\"NetworkMessageIds\":[\"37b236bd-ad39-41c0-3984-08dcf85e6b44\"],\"CountByThreatType\":{\"HighConfPhish\":1,\"Phish\":0,\"Malware\":0,\"Spam\":0},\"CountByProtectionStatus\":{\"Blocked\":1},\"CountByDeliveryLocation\":{\"Quarantine\":1},\"Query\":\"( (( (BodyFingerprintBin1:\\\"2929356879\\\") ) AND ( (P2SenderDomain:\\\"gmail.com\\\") ) AND ( (ContentType: 1) )) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\",\"QueryTime\":\"2024-10-31T13:31:45.0302157Z\",\"MailCount\":1,\"IsVolumeAnamoly\":false,\"ClusterSourceIdentifier\":\"37b236bd-ad39-41c0-3984-08dcf85e6b44\",\"ClusterSourceType\":\"Similarity\",\"ClusterQueryStartTime\":\"2024-10-11T00:00:00Z\",\"ClusterQueryEndTime\":\"2024-10-31T13:31:45.0302157Z\",\"ClusterGroup\":\"BodyFingerprintBin1,P2SenderDomain\",\"Type\":\"mailCluster\",\"ClusterBy\":\"BodyFingerprintBin1;P2SenderDomain;ContentType\",\"ClusterByValue\":\"2929356879;gmail.com;1\",\"QueryStartTime\":\"10/11/2024 12:00:00 AM\",\"QueryTime\":\"10/31/2024 1:31:45 PM\",\"Urn\":\"urn:MailClusterEntity:a5f65badbcbc2e3c6409625436363a29\",\"Source\":\"TestProvider\",\"FirstSeen\":\"2024-10-31T13:31:52\"},{\"$id\":\"12\",\"NetworkMessageIds\":[\"24b8430c-484d-4ee0-e12b-08dcee99416a\",\"2e99f39a-c998-4d94-2085-08dce9cd0b7d\",\"0ac4ee3c-7c79-408e-76c2-08dcf4106b65\",\"fd400540-8a8d-42ae-d1f9-08dced20c42f\",\"31cfca73-f309-4e21-cbc4-08dceed074cf\",\"0491b33a-15fc-4503-9dd1-08dced818f57\",\"4b620244-917b-4a04-7416-08dcf50af378\",\"1abed68d-3b03-46bd-45e2-08dcf43fb625\",\"abb4c4a5-7049-4047-5a68-08dcec201c1f\",\"92bba720-15bc-4f09-49f2-08dcf8d738a4\",\"3d511617-b717-416c-89cf-08dcf90a51c7\",\"c3ad4b6b-0fd9-4510-4481-08dcf9043502\",\"37b236bd-ad39-41c0-3984-08dcf85e6b44\",\"a1d9684c-9982-4f80-880c-08dcf775c1a9\"],\"CountByThreatType\":{\"HighConfPhish\":5,\"Phish\":0,\"Malware\":0,\"Spam\":0,\"MaliciousUrl\":15},\"CountByProtectionStatus\":{\"Delivered\":10,\"Blocked\":4,\"DeliveredAsSpam\":1},\"CountByDeliveryLocation\":{\"Inbox\":10,\"Quarantine\":4,\"DeletedFolder\":1},\"Query\":\"( ((NormalizedUrl:\\\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en\\\") AND (ContentType: 1)) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\",\"QueryTime\":\"2024-10-31T13:31:54.2957192Z\",\"MailCount\":15,\"IsVolumeAnamoly\":false,\"ClusterSourceIdentifier\":\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en\",\"ClusterSourceType\":\"UrlThreatIndicator\",\"ClusterQueryStartTime\":\"2024-10-11T00:00:00Z\",\"ClusterQueryEndTime\":\"2024-10-31T13:31:54.2957192Z\",\"ClusterGroup\":\"UrlThreatIdentifier\",\"Type\":\"mailCluster\",\"ClusterBy\":\"NormalizedUrl;ContentType\",\"ClusterByValue\":\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en;1\",\"QueryStartTime\":\"10/11/2024 12:00:00 AM\",\"QueryTime\":\"10/31/2024 1:31:54 PM\",\"Urn\":\"urn:MailClusterEntity:cae0ce4483385c4ff176b00a0cd18f8e\",\"Source\":\"TestProvider\",\"FirstSeen\":\"2024-10-31T13:31:56\"}],\"LogCreationTime\":\"2024-10-31T15:28:45.1030022Z\",\"MachineName\":\"MachineNameTest\",\"SourceTemplateType\":\"Threat_Single\",\"Category\":\"ThreatManagement\",\"SourceAlertType\":\"System\"}",
"DeepLinkUrl": "https://security.microsoft.com/mtp-investigation/urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101",
"EndTimeUtc": "2024-10-31T15:26:49",
"InvestigationId": "urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101",
"InvestigationName": "Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101",
"InvestigationType": "ZappedUrlInvestigation",
"LastUpdateTimeUtc": "2024-10-31T12:59:19",
"RunningTime": 9022,
"StartTimeUtc": "2024-10-31T12:58:22",
"Status": "Pending Action"
}
{
"CreationTime": "2025-02-04T09:15:18",
"Id": "11111111-1111-1111-1111-111111111111",
"Operation": "AirInvestigationData",
"OrganizationId": "ANONYMIZED",
"RecordType": 64,
"UserKey": "user1",
"UserType": 4,
"Version": 1,
"Workload": "user1",
"ObjectId": "11111111-1111-1111-1111-111111111111",
"UserId": "user1",
"Actions": [
"{\"$id\":\"1\",\"ActionId\":\"urn:EmailZapper:06ba299975c56e191a2d4b8bf98c921a\",\"InvestigationId\":\"urn:UrlVerdictChangeInvestig:ef7ff0b054c22025f22f6f4416f75cc0\",\"ActionApproval\":\"None\",\"ActionType\":\"EmailRemediation\",\"ActionStatus\":\"Pending\",\"Entities\":[{\"$id\":\"2\",\"NetworkMessageIds\":[\"33333333-3333-3333-3333-333333333333\"],\"CountByThreatType\":{\"HighConfPhish\":0,\"Phish\":0,\"Malware\":0,\"Spam\":1,\"MaliciousUrl\":1},\"CountByProtectionStatus\":{\"Delivered\":1},\"CountByDeliveryLocation\":{\"Inbox\":1},\"Query\":\"( ((NormalizedUrl:\\\"https://www.test.com.tr/2025%20inquiry.js\\\") AND (ContentType: 1)) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\",\"QueryTime\":\"2025-02-04T08:36:24.0457384Z\",\"MailCount\":1,\"IsVolumeAnamoly\":false,\"ClusterSourceIdentifier\":\"https://www.test.com.tr/2025%20inquiry.js\",\"ClusterSourceType\":\"UrlThreatIndicator\",\"ClusterQueryStartTime\":\"2025-01-15T00:00:00Z\",\"ClusterQueryEndTime\":\"2025-02-04T08:36:24.0457384Z\",\"ClusterGroup\":\"UrlThreatIdentifier\",\"Type\":\"mailCluster\",\"ClusterBy\":\"NormalizedUrl;ContentType\",\"ClusterByValue\":\"https://www.test.com.tr/2025%20inquiry.js;1\",\"QueryStartTime\":\"1/15/2025 12:00:00 AM\",\"QueryTime\":\"2/4/2025 8:36:24 AM\",\"Urn\":\"urn:MailClusterEntity:7e75296cf6667565c1af6a8d4239c5e5\",\"Source\":\"OATP\",\"FirstSeen\":\"2025-02-04T08:36:27\"}],\"RelatedAlertIds\":[\"44444444-4444-4444-4444-444444444444\"],\"StartTimeUtc\":\"2025-02-04T08:37:47\",\"LastUpdateTimeUtc\":\"2025-02-04T09:15:17.5752228Z\",\"TimestampUtc\":\"2025-02-04T08:37:47\",\"BulkName\":\"Clicked url Verdict changed to malicious - https://www.test.com.tr/2025%20inquiry.js\",\"ResourceIdentifiers\":[{\"$id\":\"3\",\"AadTenantId\":\"22222222-2222-2222-2222-222222222222\",\"Type\":\"AAD\"}],\"PendingType\":\"User\",\"LogCreationTime\":\"2025-02-04T09:15:17.5752228Z\",\"MachineName\":\"PC01\",\"Description\":\"For malicious emails, you can move to junk, soft or hard delete from user's mailbox.\"}"
],
"Data": "{\"Version\":\"3.0\",\"VendorName\":\"Microsoft\",\"ProviderName\":\"OATP\",\"AlertType\":\"55555555-5555-5555-5555-555555555555\",\"StartTimeUtc\":\"2025-02-04T08:28:33.4393685Z\",\"EndTimeUtc\":\"2025-02-04T08:28:33.4393685Z\",\"TimeGenerated\":\"2025-02-04T08:29:16.4466667Z\",\"ProcessingEndTime\":\"2025-02-04T09:15:17.5752228Z\",\"Status\":\"InProgress\",\"Severity\":\"High\",\"ConfidenceLevel\":\"Unknown\",\"ConfidenceScore\":1.0,\"IsIncident\":false,\"ProviderAlertId\":\"44444444-4444-4444-4444-444444444444\",\"SystemAlertId\":null,\"CorrelationKey\":\"66666666-6666-6666-6666-666666666666\",\"Investigations\":[{\"$id\":\"1\",\"Id\":\"urn:UrlVerdictChangeInvestig:ef7ff0b054c22025f22f6f4416f75cc0\",\"InvestigationStatus\":\"Pending\"}],\"InvestigationIds\":[\"urn:UrlVerdictChangeInvestig:ef7ff0b054c22025f22f6f4416f75cc0\"],\"Intent\":\"Probing\",\"ResourceIdentifiers\":[{\"$id\":\"2\",\"AadTenantId\":\"22222222-2222-2222-2222-222222222222\",\"Type\":\"AAD\"}],\"AzureResourceId\":null,\"WorkspaceId\":null,\"WorkspaceSubscriptionId\":null,\"WorkspaceResourceGroup\":null,\"AgentId\":null,\"AlertDisplayName\":\"A potentially malicious URL click was detected\",\"Description\":\"We have detected that one of your users has recently clicked on a link that was found to be malicious. -V1.0.0.5\",\"ExtendedLinks\":[{\"Href\":\"https://security.microsoft.com/alerts/fa44444444-4444-4444-4444-444444444444\",\"Category\":null,\"Label\":\"alert\",\"Type\":\"webLink\"}],\"Metadata\":{\"CustomApps\":null,\"GenericInfo\":null},\"Entities\":[{\"$id\":\"3\",\"MailboxPrimaryAddress\":\"john.doe@company.eu\",\"Upn\":\"John.DOE@company.eu\",\"AadId\":\"77777777-7777-7777-7777-777777777777\",\"RiskLevel\":\"Low\",\"Type\":\"mailbox\",\"Urn\":\"urn:UserEntity:c15ba52dfdd0d0b80095eb906ee7c9d6\",\"Source\":\"OATP\",\"FirstSeen\":\"2025-02-04T08:33:58\"},{\"$id\":\"4\",\"Url\":\"https://www.test.com.tr/2025%20inquiry.js\",\"Type\":\"url\",\"Urn\":\"urn:UrlEntity:b1fbd9f06eb20489f88f83ac7cea7867\",\"Source\":\"OATP\",\"FirstSeen\":\"2025-02-04T08:33:58\"},{\"$id\":\"5\",\"NetworkMessageIds\":[\"33333333-3333-3333-3333-333333333333\"],\"CountByThreatType\":{\"HighConfPhish\":0,\"Phish\":0,\"Malware\":0,\"Spam\":1,\"MaliciousUrl\":1},\"CountByProtectionStatus\":{\"Delivered\":1},\"CountByDeliveryLocation\":{\"Inbox\":1},\"Query\":\"( ((NormalizedUrl:\\\"https://www.test.com.tr/2025%20inquiry.js\\\") AND (ContentType: 1)) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\",\"QueryTime\":\"2025-02-04T08:36:24.0457384Z\",\"MailCount\":1,\"IsVolumeAnamoly\":false,\"ClusterSourceIdentifier\":\"https://www.test.com.tr/2025%20inquiry.js\",\"ClusterSourceType\":\"UrlThreatIndicator\",\"ClusterQueryStartTime\":\"2025-01-15T00:00:00Z\",\"ClusterQueryEndTime\":\"2025-02-04T08:36:24.0457384Z\",\"ClusterGroup\":\"UrlThreatIdentifier\",\"Type\":\"mailCluster\",\"ClusterBy\":\"NormalizedUrl;ContentType\",\"ClusterByValue\":\"https://www.test.com.tr/2025%20inquiry.js;1\",\"QueryStartTime\":\"1/15/2025 12:00:00 AM\",\"QueryTime\":\"2/4/2025 8:36:24 AM\",\"Urn\":\"urn:MailClusterEntity:7e75296cf6667565c1af6a8d4239c5e5\",\"Source\":\"OATP\",\"FirstSeen\":\"2025-02-04T08:36:27\"}],\"LogCreationTime\":\"2025-02-04T09:15:17.5752228Z\",\"MachineName\":\"PC01\",\"SourceTemplateType\":\"MaliciousUrlClick_Single\",\"Category\":\"ThreatManagement\",\"SourceAlertType\":\"System\"}",
"DeepLinkUrl": "https://security.microsoft.com/mtp-investigation/urn:UrlVerdictChangeInvestig:ef7ff0b054c22025f22f6f4416f75cc0",
"EndTimeUtc": "2025-02-04T09:15:17",
"InvestigationId": "urn:UrlVerdictChangeInvestig:ef7ff0b054c22025f22f6f4416f75cc0",
"InvestigationName": "Clicked url Verdict changed to malicious - https://www.test.com.tr/2025%20inquiry.js",
"InvestigationType": "UrlVerdictChangeInvestigation",
"LastUpdateTimeUtc": "2025-02-04T09:04:57",
"RunningTime": 2478,
"StartTimeUtc": "2025-02-04T08:33:58",
"Status": "Pending Action"
}
{
"InvestigationId": "urn:UrlVerdictChangeInvestig:11111111111111111111111111111111",
"InvestigationName": "URL verdict changed to malicious - urn:UrlVerdictChangeInvestig:11111111111111111111111111111111.",
"InvestigationType": "UrlVerdictChangeInvestigation",
"Status": "Remediated",
"StartTimeUtc": "2026-04-14T09:28:21",
"EndTimeUtc": "2026-04-14T11:28:37",
"LastUpdateTimeUtc": "2026-04-14T11:28:37",
"RunningTime": 7215,
"DeepLinkUrl": "https://security.microsoft.com/mtp-investigation/urn:UrlVerdictChangeInvestig:11111111111111111111111111111111",
"Data": "{\"$id\":\"1\",\"Version\":\"3.0\",\"VendorName\":\"Microsoft\",\"ProviderName\":\"OATP\",\"AlertType\":\"11111111-1111-1111-1111-111111111111\",\"StartTimeUtc\":\"2026-04-14T09:18:25Z\",\"EndTimeUtc\":\"2026-04-14T09:18:25Z\",\"TimeGenerated\":\"2026-04-14T09:25:03.39Z\",\"ProcessingEndTime\":\"2026-04-14T09:28:20.3493656Z\",\"Status\":\"New\",\"Severity\":\"High\",\"ConfidenceScore\":1.0,\"IsIncident\":false,\"ProviderAlertId\":\"22222222-2222-2222-2222-222222222222\",\"SystemAlertId\":null,\"CorrelationKey\":\"33333333-3333-3333-3333-333333333333\",\"Intent\":\"Probing\",\"ResourceIdentifiers\":[{\"$id\":\"2\",\"AadTenantId\":\"44444444-4444-4444-4444-444444444444\",\"Type\":\"AAD\"}],\"AlertDisplayName\":\"A potentially malicious URL click was detected\",\"Description\":\"We have detected that one of your users has recently clicked on a link that was found to be malicious. -V1.0.0.5\",\"ExtendedLinks\":[{\"Href\":\"https://security.microsoft.com/alerts/fa22222222-2222-2222-2222-222222222222\",\"Category\":null,\"Label\":\"alert\",\"Type\":\"webLink\"}],\"AlertMetadata\":{\"CustomApps\":null,\"GenericInfo\":null},\"Entities\":[{\"$id\":\"3\",\"Recipient\":\"usermail@company.fr\",\"SenderIP\":\"1.2.3.4\",\"ReceivedDate\":\"2026-04-14T07:15:45Z\",\"NetworkMessageId\":\"55555555-5555-5555-5555-555555555555\",\"StartTimeUtc\":\"2026-04-14T09:18:25Z\",\"EndTimeUtc\":\"2026-04-14T09:18:25Z\",\"Type\":\"mailMessage\",\"Urn\":null,\"Source\":\"OATP\",\"FirstSeen\":\"0001-01-01T00:00:00\",\"SourceEntityType\":\"MaliciousUrl\",\"SourceEntityId\":\"https://test.integration.com/?context=1111111111111111111111111\"},{\"$id\":\"4\",\"Address\":\"1.2.3.4\",\"StartTimeUtc\":\"2026-04-14T09:18:25Z\",\"EndTimeUtc\":\"2026-04-14T09:18:25Z\",\"Type\":\"ip\",\"Urn\":null,\"Source\":\"OATP\",\"FirstSeen\":\"0001-01-01T00:00:00\",\"SourceEntityType\":\"MaliciousUrl\",\"SourceEntityId\":\"https://test.integration.com/?context=1111111111111111111111111\"}],\"LogCreationTime\":\"2026-04-14T09:28:20.3493656Z\",\"MachineName\":\"PC01\",\"SourceTemplateType\":\"MaliciousUrlClick_Single\",\"Category\":\"ThreatManagement\",\"SourceAlertType\":\"System\",\"EventDateTime\":\"2026-04-14T09:18:25Z\",\"Operation\":\"MaliciousUrlClick\",\"Forest\":\"eur02\"}",
"Actions": [
"{\"Facts\":[{\"TagName\":\"ModernAirObject\",\"TagValue\":\"1\",\"FactStatus\":\"None\",\"id\":\"urn:ModernAirObject:1:22222222222222222222222222222222\",\"TenantId\":\"44444444-4444-4444-4444-444444444444\",\"InvestigationId\":\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"ParentObjectId\":\"urn:MailClusterAnalyzer:33333333333333333333333333333333\",\"RelatedObjectId\":\"urn:MailClusterAnalyzer:33333333333333333333333333333333\",\"ObjectCreationTime\":\"0001-01-01T00:00:00\",\"ObjectChangedTime\":\"0001-01-01T00:00:00\",\"ExecutionCount\":0,\"ProcessingStartTime\":\"0001-01-01T00:00:00\",\"ProcessingEndTime\":\"0001-01-01T00:00:00\",\"DisplayName\":null,\"MalScore\":0,\"SubPartitionKey1\":null,\"SubPartitionKey2\":null,\"TimeToLiveInSeconds\":null,\"ContainerName\":null,\"PartitionKeyPaths\":[\"/partitionKey\"],\"PartitionKey\":null,\"Type\":null,\"ETag\":null,\"IsGCed\":false,\"ExtensionData\":null}],\"EntityUrn\":\"urn:MailEntityModel:44444444444444444444444444444444\",\"Disposition\":\"Analyzer\",\"ActionType\":\"MailClusterAnalyzer\",\"TimeoutForAction\":\"2026-04-14T09:33:25.3460101+00:00\",\"IsRecurringAction\":false,\"ActionStatus\":\"Complete\",\"PartitionKey\":\"44444444-4444-4444-4444-444444444444\",\"SubPartitionKey1\":\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"id\":\"urn:MailClusterAnalyzer:33333333333333333333333333333333\",\"TenantId\":\"44444444-4444-4444-4444-444444444444\",\"InvestigationId\":\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"ParentObjectId\":\"urn:MailEntityModel:44444444444444444444444444444444\",\"RelatedObjectId\":\"\",\"ObjectCreationTime\":\"2026-04-14T09:28:24.9626945Z\",\"ObjectChangedTime\":\"2026-04-14T09:28:26.3121569Z\",\"ExecutionCount\":0,\"ProcessingStartTime\":\"2026-04-14T09:28:25.4001066Z\",\"ProcessingEndTime\":\"2026-04-14T09:28:26.2465844Z\",\"DisplayName\":null,\"MalScore\":0,\"SubPartitionKey2\":null,\"TimeToLiveInSeconds\":null,\"Type\":null,\"ETag\":null,\"IsGCed\":false,\"ExtensionData\":null}",
"{\"Facts\":[{\"TagName\":\"ModernAirObject\",\"TagValue\":\"1\",\"FactStatus\":\"None\",\"id\":\"urn:ModernAirObject:1:55555555555555555555555555555555\",\"TenantId\":\"44444444-4444-4444-4444-444444444444\",\"InvestigationId\":\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"ParentObjectId\":\"urn:MailClusterAnalyzer:66666666666666666666666666666666\",\"RelatedObjectId\":\"urn:MailClusterAnalyzer:66666666666666666666666666666666\",\"ObjectCreationTime\":\"0001-01-01T00:00:00\",\"ObjectChangedTime\":\"0001-01-01T00:00:00\",\"ExecutionCount\":0,\"ProcessingStartTime\":\"0001-01-01T00:00:00\",\"ProcessingEndTime\":\"0001-01-01T00:00:00\",\"DisplayName\":null,\"MalScore\":0,\"SubPartitionKey1\":null,\"SubPartitionKey2\":null,\"TimeToLiveInSeconds\":null,\"ContainerName\":null,\"PartitionKeyPaths\":[\"/partitionKey\"],\"PartitionKey\":null,\"Type\":null,\"ETag\":null,\"IsGCed\":false,\"ExtensionData\":null}],\"EntityUrn\":\"urn:UrlEntityModel:77777777777777777777777777777777\",\"Disposition\":\"Analyzer\",\"ActionType\":\"MailClusterAnalyzer\",\"TimeoutForAction\":\"2026-04-14T09:33:25.1548139+00:00\",\"IsRecurringAction\":false,\"ActionStatus\":\"Complete\",\"PartitionKey\":\"44444444-4444-4444-4444-444444444444\",\"SubPartitionKey1\":\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"id\":\"urn:MailClusterAnalyzer:66666666666666666666666666666666\",\"TenantId\":\"44444444-4444-4444-4444-444444444444\",\"InvestigationId\":\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"ParentObjectId\":\"urn:UrlEntityModel:77777777777777777777777777777777\",\"RelatedObjectId\":\"\",\"ObjectCreationTime\":\"2026-04-14T09:28:25.0068659Z\",\"ObjectChangedTime\":\"2026-04-14T09:28:26.1005485Z\",\"ExecutionCount\":0,\"ProcessingStartTime\":\"2026-04-14T09:28:25.1979172Z\",\"ProcessingEndTime\":\"2026-04-14T09:28:26.0299557Z\",\"DisplayName\":null,\"MalScore\":0,\"SubPartitionKey2\":null,\"TimeToLiveInSeconds\":null,\"Type\":null,\"ETag\":null,\"IsGCed\":false,\"ExtensionData\":null}",
"{\"TiInvestigationId\":\"\",\"TiRemediationId\":\"\",\"TiInvestigationName\":\"\",\"KqlString\":\"\",\"Facts\":[{\"TagName\":\"ModernAirObject\",\"TagValue\":\"1\",\"FactStatus\":\"None\",\"id\":\"urn:ModernAirObject:1:88888888888888888888888888888888\",\"TenantId\":\"44444444-4444-4444-4444-444444444444\",\"InvestigationId\":\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"ParentObjectId\":\"urn:EmailZapperRemediation:33333333333333333333333333333333\",\"RelatedObjectId\":\"urn:EmailZapperRemediation:33333333333333333333333333333333\",\"ObjectCreationTime\":\"0001-01-01T00:00:00\",\"ObjectChangedTime\":\"0001-01-01T00:00:00\",\"ExecutionCount\":0,\"ProcessingStartTime\":\"0001-01-01T00:00:00\",\"ProcessingEndTime\":\"0001-01-01T00:00:00\",\"DisplayName\":null,\"MalScore\":0,\"SubPartitionKey1\":null,\"SubPartitionKey2\":null,\"TimeToLiveInSeconds\":null,\"ContainerName\":null,\"PartitionKeyPaths\":[\"/partitionKey\"],\"PartitionKey\":null,\"Type\":null,\"ETag\":null,\"IsGCed\":false,\"ExtensionData\":null}],\"EntityUrn\":\"urn:MailEntityModel:44444444444444444444444444444444\",\"Disposition\":\"Remediator\",\"ActionType\":\"EmailZapperRemediation\",\"TimeoutForAction\":\"2026-04-14T09:33:26.3168632+00:00\",\"IsRecurringAction\":false,\"ActionStatus\":\"Cancelled\",\"PartitionKey\":\"44444444-4444-4444-4444-444444444444\",\"SubPartitionKey1\":\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"id\":\"urn:EmailZapperRemediation:33333333333333333333333333333333\",\"TenantId\":\"44444444-4444-4444-4444-444444444444\",\"InvestigationId\":\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"ParentObjectId\":\"urn:MailEntityModel:44444444444444444444444444444444\",\"RelatedObjectId\":\"\",\"ObjectCreationTime\":\"2026-04-14T09:28:24.9626945Z\",\"ObjectChangedTime\":\"2026-04-14T09:28:26.3121569Z\",\"ExecutionCount\":0,\"ProcessingStartTime\":\"0001-01-01T00:00:00\",\"ProcessingEndTime\":\"2026-04-14T11:28:36.8201365Z\",\"DisplayName\":null,\"MalScore\":0,\"SubPartitionKey2\":null,\"TimeToLiveInSeconds\":null,\"Type\":null,\"ETag\":null,\"IsGCed\":false,\"ExtensionData\":null}",
"{\"Facts\":[{\"TagName\":\"ModernAirObject\",\"TagValue\":\"1\",\"FactStatus\":\"None\",\"id\":\"urn:ModernAirObject:1:99999999999999999999999999999999\",\"TenantId\":\"44444444-4444-4444-4444-444444444444\",\"InvestigationId\":\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"ParentObjectId\":\"urn:MailRefreshAnalyzer:33333333333333333333333333333333\",\"RelatedObjectId\":\"urn:MailRefreshAnalyzer:33333333333333333333333333333333\",\"ObjectCreationTime\":\"0001-01-01T00:00:00\",\"ObjectChangedTime\":\"0001-01-01T00:00:00\",\"ExecutionCount\":0,\"ProcessingStartTime\":\"0001-01-01T00:00:00\",\"ProcessingEndTime\":\"0001-01-01T00:00:00\",\"DisplayName\":null,\"MalScore\":0,\"SubPartitionKey1\":null,\"SubPartitionKey2\":null,\"TimeToLiveInSeconds\":null,\"ContainerName\":null,\"PartitionKeyPaths\":[\"/partitionKey\"],\"PartitionKey\":null,\"Type\":null,\"ETag\":null,\"IsGCed\":false,\"ExtensionData\":null}],\"EntityUrn\":\"urn:MailEntityModel:44444444444444444444444444444444\",\"Disposition\":\"Analyzer\",\"ActionType\":\"MailRefreshAnalyzer\",\"TimeoutForAction\":\"2026-04-14T09:33:27.4181556+00:00\",\"IsRecurringAction\":true,\"ActionStatus\":\"Complete\",\"PartitionKey\":\"44444444-4444-4444-4444-444444444444\",\"SubPartitionKey1\":\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"id\":\"urn:MailRefreshAnalyzer:33333333333333333333333333333333\",\"TenantId\":\"44444444-4444-4444-4444-444444444444\",\"InvestigationId\":\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"ParentObjectId\":\"urn:MailEntityModel:44444444444444444444444444444444\",\"RelatedObjectId\":\"\",\"ObjectCreationTime\":\"2026-04-14T09:28:24.9626945Z\",\"ObjectChangedTime\":\"2026-04-14T09:28:26.3121569Z\",\"ExecutionCount\":0,\"ProcessingStartTime\":\"2026-04-14T11:28:31.8407962Z\",\"ProcessingEndTime\":\"2026-04-14T11:28:32.4217177Z\",\"DisplayName\":null,\"MalScore\":0,\"SubPartitionKey2\":null,\"TimeToLiveInSeconds\":null,\"Type\":null,\"ETag\":null,\"IsGCed\":false,\"ExtensionData\":null}"
],
"ObjectId": "aaaaaaaa-aaaa-aaaa-aaaaaaaaaaaa",
"UserId": "AirInvestigation",
"ClientIP": null,
"Id": "bbbbbbbb-bbbb-bbbb-bbbb-bbbbbbbbbbbb",
"RecordType": 64,
"CreationTime": "2026-04-14T11:28:39",
"Operation": "AirInvestigationData",
"OrganizationId": "44444444-4444-4444-4444-444444444444",
"UserType": 4,
"UserKey": "AirInvestigation",
"Workload": "AirInvestigation",
"ResultStatus": null,
"AppAccessContext": null,
"AppIdentity": null,
"AgentId": null,
"AgentName": null,
"CorrelationIdentity": null,
"Version": 1,
"Scope": 0,
"Purpose": 0,
"RequiresCustomerKeyEncryption": null,
"AssociatedAdminUnits": null,
"ScopingEntityType": 0,
"ScopingEntityIds": null
}
{
"CreationTime": "2023-04-17T14:27:09",
"Id": "60eaf0aa-edc3-4f8d-8275-bc82d9500e59",
"Operation": "AirInvestigationData",
"OrganizationId": "ANONYMIZED",
"RecordType": 64,
"UserKey": "user1",
"UserType": 4,
"Version": 1,
"Workload": "user1",
"ObjectId": "60eaf0aa-edc3-4f8d-8275-bc82d9500e59",
"UserId": "user1",
"DeepLinkUrl": "https://security.microsoft.com/mtp-investigation/urn:ZappedUrlInvestigation:a10a976",
"EndTimeUtc": "2023-04-17T14:27:07",
"InvestigationId": "urn:ZappedUrlInvestigation:a10a976d-6e3e-4d10-be50-4907183b6f86",
"InvestigationName": "Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:a1",
"InvestigationType": "ZappedUrlInvestigation",
"LastUpdateTimeUtc": "2023-04-17T14:21:59",
"RunningTime": 931,
"StartTimeUtc": "2023-04-17T14:11:38",
"Status": "Remediated",
"Data": "{\"Version\":\"3.0\",\"VendorName\":\"Microsoft\",\"ProviderName\":\"OATP\",\"AlertType\":\"alert_type_value\",\"Status\":\"status_value\",\"Severity\":\"severity_value\",\"IsIncident\":true,\"CorrelationKey\":\"correlation_key_value\",\"Category\":\"category_value\",\"SourceAlertType\":\"source_alert_type_value\",\"MachineName\":\"machine_name_value\",\"Entities\": [{\"Urls\":[\"http://example.com\",\"http://1.2.3.5\"],\"SenderIP\":\"1.2.3.4\",\"Subject\":\"subject_value\",\"P1SenderDomain\":\"http://example.com\",\"Threats\":1,\"Sender\":\"test@test.test\",\"Recipient\":\"user1@example.com\"},{\"Urls\":[\"http://1.2.3.6\",\"http://1.2.3.7\"],\"SenderIP\":\"1.2.3.8\",\"Subject\":\"subject_value_1\",\"P1SenderDomain\":\"http://1.2.3.9\",\"Threats\":2,\"Sender\":\"user3@example.com\",\"Recipient\":\"user4@example.com\"}]}",
"Actions": [
"{\"$id\":\"1\",\"ActionId\":\"urn:EmailZapper:8ad9417586e14790ba2afed0a7840e65\"}"
]
}
{
"CreationTime": "2024-09-02T03:33:37",
"Id": "1234ab56-7890-1234-c5de-678fabcd9012",
"Operation": "AirInvestigationData",
"OrganizationId": "ANONYMIZED",
"RecordType": 64,
"UserKey": "user1",
"UserType": 4,
"Version": 1,
"Workload": "user1",
"ObjectId": "1234ab56-7890-1234-c5de-678fabcd9012",
"UserId": "user1",
"Actions": [
"{\"$id\":\"1\",\"ActionId\":\"urn:EmailZapper:12345a6789bc01de23456f789ab0\",\"InvestigationId\":\"urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\",\"ActionApproval\":\"None\",\"ActionType\":\"EmailRemediation\",\"ActionStatus\":\"Pending\",\"Entities\":[{\"$id\":\"2\",\"Recipient\":\"user@example.net\",\"Urls\":[\"https://example.net/TUZAu6VrAvQT\",\"https://website.net/up/24/35/image.png\"],\"Threats\":[\"ZapPhish\",\"NormalPhish\"],\"Sender\":\"user1@test.example.com\",\"P1Sender\":\"p1user1@test.example.com\",\"P1SenderDomain\":\"test.integration.com\",\"SenderIP\":\"1.2.3.4\",\"P2Sender\":\"user1@test.example.com\",\"P2SenderDisplayName\":\"P2 name\",\"P2SenderDomain\":\"test.integration.com\",\"ReceivedDate\":\"2024-09-02T02:43:12\",\"NetworkMessageId\":\"ab12cde3-f456-789a-01bc-23defa4bc5d\",\"InternetMessageId\":\"<message.id.test@0123456789.userabc.mail.com>\",\"Subject\":\"Subject of the mail\",\"AntispamDirection\":\"Inbound\",\"DeliveryAction\":\"DeliveredAsSpam\",\"ThreatDetectionMethods\":[\"FingerPrintMatch\"],\"Language\":\"en\",\"DeliveryLocation\":\"JunkFolder\",\"OriginalDeliveryLocation\":\"Inbox\",\"AdditionalActionsAndResults\":[\"OriginalDelivery: [N/A]\",\"Zap: [Success: Message moved]\"],\"AuthDetails\":[{\"Name\":\"SPF\",\"Value\":\"Pass\"},{\"Name\":\"DKIM\",\"Value\":\"None\"},{\"Name\":\"DMARC\",\"Value\":\"Best guess pass\"},{\"Name\":\"Comp Auth\",\"Value\":\"pass\"}],\"SystemOverrides\":[],\"Type\":\"mailMessage\",\"Urn\":\"urn:MailEntity:01abc23d456efa7bc8901234d5efa67b\",\"Source\":\"OATP\",\"FirstSeen\":\"2024-09-02T03:20:40\"}],\"RelatedAlertIds\":[\"01234567-89a0-1234-5b67-89cdefa0b12\"],\"StartTimeUtc\":\"2024-09-02T03:27:33\",\"LastUpdateTimeUtc\":\"2024-09-02T03:33:31.8137435Z\",\"TimestampUtc\":\"2024-09-02T03:27:33\",\"BulkName\":\"Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\",\"ResourceIdentifiers\":[{\"$id\":\"3\",\"AadTenantId\":\"123abc456-d789-0e1f-2a34-b56789c01234\",\"Type\":\"AAD\"}],\"PendingType\":\"User\",\"LogCreationTime\":\"2024-09-02T03:33:31.8137435Z\",\"MachineName\":\"MACHINE01\",\"Description\":\"For malicious emails, you can move to junk, soft or hard delete from user's mailbox.\"}",
"{\"$id\":\"1\",\"ActionId\":\"urn:EmailZapper:012345a6789bcd0e1f23a4b5cd678ef9\",\"InvestigationId\":\"urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\",\"ActionApproval\":\"None\",\"ActionType\":\"EmailRemediation\",\"ActionStatus\":\"Pending\",\"Entities\":[{\"$id\":\"2\",\"NetworkMessageIds\":[\"01a2bcd3-efab-4c56-7890-12defa3bc4d\",\"0123a456-b789-0cd1-e23f-45abcd6ef78\",\"ab12cde3-f456-789a-01bc-23defa4bc5d\",\"01a2b345-67c8-9012-345d-67efabc8d90e\",\"01a234b5-6789-012c-3d4e-56fabcd7ef8\",\"a0bcd12e-3456-7f89-0a1b-23cdefa4b5c6\",\"0a1b23c4-567d-8901-2345-67efabc8d90a\",\"0123a4b5-678c-9d0e-1f23-45abcde6fa78\",\"0a1b234c-5678-90d1-2efa-34bcdef5a6b7\",\"0123a4bc-5d6e-78f9-0123-45abcde67890\"],\"CountByThreatType\":{\"HighConfPhish\":0,\"Phish\":6,\"Malware\":0,\"Spam\":6,\"MaliciousUrl\":12},\"CountByProtectionStatus\":{\"DeliveredAsSpam\":6,\"Delivered\":4,\"Blocked\":2},\"CountByDeliveryLocation\":{\"JunkFolder\":6,\"External\":3,\"Failed\":2,\"Forwarded\":1},\"Query\":\"( ((NormalizedUrl:\\\"https://example.net/TUZAu6VrAvQT\\\") AND (ContentType: 1)) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\",\"QueryTime\":\"2024-09-02T03:24:59.7851632Z\",\"MailCount\":12,\"IsVolumeAnamoly\":true,\"ClusterSourceIdentifier\":\"https://example.net/TUZAu6VrAvQT\",\"ClusterSourceType\":\"UrlThreatIndicator\",\"ClusterQueryStartTime\":\"2024-08-13T00:00:00Z\",\"ClusterQueryEndTime\":\"2024-09-02T03:24:59.7851632Z\",\"ClusterGroup\":\"UrlThreatIdentifier\",\"Type\":\"mailCluster\",\"ClusterBy\":\"NormalizedUrl;ContentType\",\"ClusterByValue\":\"https://example.net/TUZAu6VrAvQT;1\",\"QueryStartTime\":\"8/13/2024 12:00:00 AM\",\"QueryTime\":\"9/2/2024 3:24:59 AM\",\"Urn\":\"urn:MailClusterEntity:a0123b4c5678def901234a5b67cde890\",\"Source\":\"OATP\",\"FirstSeen\":\"2024-09-02T03:25:01\"}],\"RelatedAlertIds\":[\"01234567-89a0-1234-5b67-89cdefa0b12\"],\"StartTimeUtc\":\"2024-09-02T03:27:33\",\"LastUpdateTimeUtc\":\"2024-09-02T03:33:31.8137435Z\",\"TimestampUtc\":\"2024-09-02T03:27:33\",\"BulkName\":\"Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\",\"ResourceIdentifiers\":[{\"$id\":\"3\",\"AadTenantId\":\"123abc456-d789-0e1f-2a34-b56789c01234\",\"Type\":\"AAD\"}],\"PendingType\":\"User\",\"LogCreationTime\":\"2024-09-02T03:33:31.8137435Z\",\"MachineName\":\"MACHINE01\",\"Description\":\"For malicious emails, you can move to junk, soft or hard delete from user's mailbox.\"}"
],
"Data": "{\"Version\":\"3.0\",\"VendorName\":\"Microsoft\",\"ProviderName\":\"OATP\",\"AlertType\":\"8e6ba277-ef39-404e-aaf1-294f6d9a2b88\",\"StartTimeUtc\":\"2024-09-02T03:14:37.3349438Z\",\"EndTimeUtc\":\"2024-09-02T03:14:37.3349438Z\",\"TimeGenerated\":\"2024-09-02T03:16:43.91Z\",\"ProcessingEndTime\":\"2024-09-02T03:33:31.8137435Z\",\"Status\":\"InProgress\",\"DetectionTechnology\":\"URLList\",\"Severity\":\"Informational\",\"ConfidenceLevel\":\"Unknown\",\"ConfidenceScore\":1.0,\"IsIncident\":false,\"ProviderAlertId\":\"01234567-89a0-1234-5b67-89cdefa0b12\",\"SystemAlertId\":null,\"CorrelationKey\":\"8a5bf71a-d9e4-422e-8bdb-33272de66983\",\"Investigations\":[{\"$id\":\"1\",\"Id\":\"urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\",\"InvestigationStatus\":\"Pending\"}],\"InvestigationIds\":[\"urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\"],\"Intent\":\"Probing\",\"ResourceIdentifiers\":[{\"$id\":\"2\",\"AadTenantId\":\"123abc456-d789-0e1f-2a34-b56789c01234\",\"Type\":\"AAD\"}],\"AzureResourceId\":null,\"WorkspaceId\":null,\"WorkspaceSubscriptionId\":null,\"WorkspaceResourceGroup\":null,\"AgentId\":null,\"AlertDisplayName\":\"Email messages containing malicious URL removed after delivery\u200b\",\"Description\":\"Emails with malicious URL that were delivered and later removed -V1.0.0.3\",\"ExtendedLinks\":[{\"Href\":\"https://security.microsoft.com/alerts/fa01234567-89a0-1234-5b67-89cdefa0b12\",\"Category\":null,\"Label\":\"alert\",\"Type\":\"webLink\"}],\"Metadata\":{\"CustomApps\":null,\"GenericInfo\":null},\"Entities\":[{\"$id\":\"3\",\"Recipient\":\"user@example.net\",\"Urls\":[\"https://example.net/TUZAu6VrAvQT\",\"https://website.net/up/24/35/image.png\"],\"Threats\":[\"ZapPhish\",\"NormalPhish\"],\"Sender\":\"user1@test.example.com\",\"P1Sender\":\"p1user1@test.example.com\",\"P1SenderDomain\":\"test.integration.com\",\"SenderIP\":\"1.2.3.4\",\"P2Sender\":\"user1@test.example.com\",\"P2SenderDisplayName\":\"P2 name\",\"P2SenderDomain\":\"test.integration.com\",\"ReceivedDate\":\"2024-09-02T02:43:12\",\"NetworkMessageId\":\"ab12cde3-f456-789a-01bc-23defa4bc5d\",\"InternetMessageId\":\"<message.id.test@0123456789.userabc.mail.com>\",\"Subject\":\"Subject of the mail\",\"AntispamDirection\":\"Inbound\",\"DeliveryAction\":\"DeliveredAsSpam\",\"ThreatDetectionMethods\":[\"FingerPrintMatch\"],\"Language\":\"en\",\"DeliveryLocation\":\"JunkFolder\",\"OriginalDeliveryLocation\":\"Inbox\",\"AdditionalActionsAndResults\":[\"OriginalDelivery: [N/A]\",\"Zap: [Success: Message moved]\"],\"AuthDetails\":[{\"Name\":\"SPF\",\"Value\":\"Pass\"},{\"Name\":\"DKIM\",\"Value\":\"None\"},{\"Name\":\"DMARC\",\"Value\":\"Best guess pass\"},{\"Name\":\"Comp Auth\",\"Value\":\"pass\"}],\"SystemOverrides\":[],\"Type\":\"mailMessage\",\"Urn\":\"urn:MailEntity:01abc23d456efa7bc8901234d5efa67b\",\"Source\":\"OATP\",\"FirstSeen\":\"2024-09-02T03:20:40\"},{\"$id\":\"4\",\"MailboxPrimaryAddress\":\"user@example.net\",\"Upn\":\"user@example.net\",\"AadId\":\"0123ac45-6c7d-e89f-a0123b45c6d7\",\"RiskLevel\":\"None\",\"Type\":\"mailbox\",\"Urn\":\"urn:UserEntity:1a2b3456c7defabc8901d2e3fa456789\",\"Source\":\"OATP\",\"FirstSeen\":\"2024-09-02T03:20:40\"},{\"$id\":\"5\",\"Url\":\"https://example.net/TUZAu6VrAvQT\",\"Type\":\"url\",\"ClickCount\":0,\"EmailCount\":12,\"Urn\":\"urn:UrlEntity:0123a4567b8c9de0fa123bcde4f5a6b\",\"Source\":\"OATP\",\"FirstSeen\":\"2024-09-02T03:20:40\"},{\"$id\":\"6\",\"NetworkMessageIds\":[\"ab12cde3-f456-789a-01bc-23defa4bc5d\"],\"CountByThreatType\":{\"HighConfPhish\":0,\"Phish\":1,\"Malware\":0,\"Spam\":1},\"CountByProtectionStatus\":{\"DeliveredAsSpam\":1},\"CountByDeliveryLocation\":{\"JunkFolder\":1},\"Query\":\"( (( (Subject:\\\"Subject of the mail\\\") ) AND ( (SenderIp:\\\"1.2.3.4\\\") ) AND ( (AntispamDirection:\\\"1\\\") ) AND ( (ContentType: 1) )) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\",\"QueryTime\":\"2024-09-02T03:24:59.8007877Z\",\"MailCount\":1,\"IsVolumeAnamoly\":false,\"ClusterSourceIdentifier\":\"ab12cde3-f456-789a-01bc-23defa4bc5d\",\"ClusterSourceType\":\"Similarity\",\"ClusterQueryStartTime\":\"2024-08-13T00:00:00Z\",\"ClusterQueryEndTime\":\"2024-09-02T03:24:59.8007877Z\",\"ClusterGroup\":\"Subject,SenderIp,AntispamDirection\",\"Type\":\"mailCluster\",\"ClusterBy\":\"Subject;SenderIp;AntispamDirection;ContentType\",\"ClusterByValue\":\"Subject of the mail;1.2.3.4;1;1\",\"QueryStartTime\":\"8/13/2024 12:00:00 AM\",\"QueryTime\":\"9/2/2024 3:24:59 AM\",\"Urn\":\"urn:MailClusterEntity:01a2bc345678de901f2a34b567cdef89\",\"Source\":\"OATP\",\"FirstSeen\":\"2024-09-02T03:25:01\"},{\"$id\":\"7\",\"NetworkMessageIds\":[\"01a2bcd3-efab-4c56-7890-12defa3bc4d\",\"0123a456-b789-0cd1-e23f-45abcd6ef78\",\"ab12cde3-f456-789a-01bc-23defa4bc5d\",\"01a2b345-67c8-9012-345d-67efabc8d90e\",\"01a234b5-6789-012c-3d4e-56fabcd7ef8\",\"a0bcd12e-3456-7f89-0a1b-23cdefa4b5c6\",\"0a1b23c4-567d-8901-2345-67efabc8d90a\",\"0123a4b5-678c-9d0e-1f23-45abcde6fa78\",\"0a1b234c-5678-90d1-2efa-34bcdef5a6b7\",\"0123a4bc-5d6e-78f9-0123-45abcde67890\"],\"CountByThreatType\":{\"HighConfPhish\":0,\"Phish\":6,\"Malware\":0,\"Spam\":6,\"MaliciousUrl\":12},\"CountByProtectionStatus\":{\"DeliveredAsSpam\":6,\"Delivered\":4,\"Blocked\":2},\"CountByDeliveryLocation\":{\"JunkFolder\":6,\"External\":3,\"Failed\":2,\"Forwarded\":1},\"Query\":\"( ((NormalizedUrl:\\\"https://example.net/TUZAu6VrAvQT\\\") AND (ContentType: 1)) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\",\"QueryTime\":\"2024-09-02T03:24:59.7851632Z\",\"MailCount\":12,\"IsVolumeAnamoly\":true,\"ClusterSourceIdentifier\":\"https://example.net/TUZAu6VrAvQT\",\"ClusterSourceType\":\"UrlThreatIndicator\",\"ClusterQueryStartTime\":\"2024-08-13T00:00:00Z\",\"ClusterQueryEndTime\":\"2024-09-02T03:24:59.7851632Z\",\"ClusterGroup\":\"UrlThreatIdentifier\",\"Type\":\"mailCluster\",\"ClusterBy\":\"NormalizedUrl;ContentType\",\"ClusterByValue\":\"https://example.net/TUZAu6VrAvQT;1\",\"QueryStartTime\":\"8/13/2024 12:00:00 AM\",\"QueryTime\":\"9/2/2024 3:24:59 AM\",\"Urn\":\"urn:MailClusterEntity:a0123b4c5678def901234a5b67cde890\",\"Source\":\"OATP\",\"FirstSeen\":\"2024-09-02T03:25:01\"},{\"$id\":\"8\",\"NetworkMessageIds\":[\"ab12cde3-f456-789a-01bc-23defa4bc5d\"],\"CountByThreatType\":{\"HighConfPhish\":0,\"Phish\":1,\"Malware\":0,\"Spam\":1},\"CountByProtectionStatus\":{\"DeliveredAsSpam\":1},\"CountByDeliveryLocation\":{\"JunkFolder\":1},\"Query\":\"( (( (Subject:\\\"Subject of the mail\\\") ) AND ( (P2SenderDomain:\\\"test.integration.com\\\") ) AND ( (AntispamDirection:\\\"1\\\") ) AND ( (ContentType: 1) )) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\",\"QueryTime\":\"2024-09-02T03:24:59.8007877Z\",\"MailCount\":1,\"IsVolumeAnamoly\":false,\"ClusterSourceIdentifier\":\"ab12cde3-f456-789a-01bc-23defa4bc5d\",\"ClusterSourceType\":\"Similarity\",\"ClusterQueryStartTime\":\"2024-08-13T00:00:00Z\",\"ClusterQueryEndTime\":\"2024-09-02T03:24:59.8007877Z\",\"ClusterGroup\":\"Subject,P2SenderDomain,AntispamDirection\",\"Type\":\"mailCluster\",\"ClusterBy\":\"Subject;P2SenderDomain;AntispamDirection;ContentType\",\"ClusterByValue\":\"Subject of the mail;test.integration.com;1;1\",\"QueryStartTime\":\"8/13/2024 12:00:00 AM\",\"QueryTime\":\"9/2/2024 3:24:59 AM\",\"Urn\":\"urn:MailClusterEntity:7350e5b982beaa3846d327a005dd57d6\",\"Source\":\"OATP\",\"FirstSeen\":\"2024-09-02T03:25:01\"}],\"LogCreationTime\":\"2024-09-02T03:33:31.8137435Z\",\"MachineName\":\"MACHINE01\",\"SourceTemplateType\":\"Threat_Single\",\"Category\":\"ThreatManagement\",\"SourceAlertType\":\"System\"}",
"DeepLinkUrl": "https://security.microsoft.com/mtp-investigation/urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9",
"EndTimeUtc": "2024-09-02T03:33:31",
"InvestigationId": "urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9",
"InvestigationName": "Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9",
"InvestigationType": "ZappedUrlInvestigation",
"LastUpdateTimeUtc": "2024-09-02T03:28:24",
"RunningTime": 771,
"StartTimeUtc": "2024-09-02T03:20:40",
"Status": "Pending Action"
}
{
"CreationTime": "2023-11-21T12:24:04",
"Id": "d32b02fd-f97e-47a1-9407-f5cb2dcca772",
"Operation": "AirInvestigationData",
"OrganizationId": "ANONYMIZED",
"RecordType": 64,
"UserKey": "user1",
"UserType": 4,
"Version": 1,
"Workload": "user1",
"ObjectId": "d32b02fd-f97e-47a1-9407-f5cb2dcca772",
"UserId": "user1",
"Data": "{\"Version\":\"3.0\",\"VendorName\":\"Microsoft\",\"ProviderName\":\"OATP\",\"AlertType\":\"4b1820ec-39dc-45f3-abf6-5ee80df51fd2\",\"StartTimeUtc\":\"2023-11-21T12:13:21.3426718Z\",\"EndTimeUtc\":\"2023-11-21T12:13:21.3426718Z\",\"TimeGenerated\":\"2023-11-21T12:21:01.367Z\",\"ProcessingEndTime\":\"2023-11-21T12:24:02.9479392Z\",\"Status\":\"InProgress\",\"Severity\":\"Informational\",\"ConfidenceLevel\":\"Unknown\",\"ConfidenceScore\":1.0,\"IsIncident\":false,\"ProviderAlertId\":\"2187a396-5337-1901-6e00-08dbea8b3430\",\"SystemAlertId\":null,\"CorrelationKey\":\"955b1f53-3bcf-45cf-9e1d-b071d0518b01\",\"Investigations\":[{\"$id\":\"1\",\"Id\":\"urn:ZappedFileInvestigation:adffaf6ed0f17079cf14e9dc2adf9c1d\",\"InvestigationStatus\":\"Running\"}],\"InvestigationIds\":[\"urn:ZappedFileInvestigation:adffaf6ed0f17079cf14e9dc2adf9c1d\"],\"Intent\":\"Probing\",\"ResourceIdentifiers\":[{\"$id\":\"2\",\"AadTenantId\":\"62e8c4be-8433-4768-82bb-4c97eaf05a19\",\"Type\":\"AAD\"}],\"AzureResourceId\":null,\"WorkspaceId\":null,\"WorkspaceSubscriptionId\":null,\"WorkspaceResourceGroup\":null,\"AgentId\":null,\"AlertDisplayName\":\"Email messages containing malicious file removed after delivery\",\"Description\":\"Emails with malicious file that were delivered and later removed -V1.0.0.3\",\"ExtendedLinks\":[{\"Href\":\"https://security.microsoft.com/viewalerts?id=2187a396-5337-1901-6e00-08dbea8b3430\",\"Category\":null,\"Label\":\"alert\",\"Type\":\"webLink\"}],\"Metadata\":{\"CustomApps\":null,\"GenericInfo\":null},\"Entities\":[{\"$id\":\"3\",\"MailboxPrimaryAddress\":\"john.doe@example.com\",\"Upn\":\"john.doe@example.com\",\"AadId\":\"70999cb4-e7db-47c8-a3ba-99381283152d\",\"RiskLevel\":\"None\",\"Type\":\"mailbox\",\"Urn\":\"urn:UserEntity:11111111111111111111111111111111\",\"Source\":\"OATP\",\"FirstSeen\":\"0001-01-01T00:00:00\"},{\"$id\":\"4\",\"Files\":[{\"$id\":\"5\",\"Name\":\"pix.jpg\",\"FileHashes\":[{\"$id\":\"6\",\"Algorithm\":\"SHA256\",\"Value\":\"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b\",\"Type\":\"filehash\"}],\"Type\":\"file\",\"MalwareFamily\":\"Malicious Payload\"}],\"Recipient\":\"john.doe@example.com\",\"Urls\":[\"https://example.org\"],\"Sender\":\"jane.doe@example.org\",\"P1Sender\":\"jane.doe@example.org\",\"P1SenderDomain\":\"example.org\",\"SenderIP\":\"1.2.3.4\",\"P2Sender\":\"jane.doe@example.org\",\"P2SenderDisplayName\":\"jane.doe\",\"P2SenderDomain\":\"example.org\",\"ReceivedDate\":\"2023-11-21T12:00:46\",\"NetworkMessageId\":\"3fe5777d-1fb7-4f34-bb1e-035e4df1f96f\",\"InternetMessageId\":\"<88f57442-338a-4e6b-8925-73d62527809b@example.org>\",\"Subject\":\"Pending and Review\",\"AntispamDirection\":\"Inbound\",\"DeliveryAction\":\"Blocked\",\"ThreatDetectionMethods\":[\"FileHashList\"],\"Language\":\"en\",\"DeliveryLocation\":\"Quarantine\",\"OriginalDeliveryLocation\":\"Inbox\",\"PhishConfidenceLevel\":\"High\",\"AdditionalActionsAndResults\":[\"OriginalDelivery: [N/A]\",\"Zap: [Success: Message moved to quarantine]\"],\"AuthDetails\":[{\"Name\":\"SPF\",\"Value\":\"Pass\"},{\"Name\":\"DKIM\",\"Value\":\"Pass\"},{\"Name\":\"DMARC\",\"Value\":\"Best guess pass\"},{\"Name\":\"Comp Auth\",\"Value\":\"pass\"}],\"SystemOverrides\":[],\"Type\":\"mailMessage\",\"Urn\":\"urn:MailEntity:93d7f11156b7dc03c36d7ef108389605\",\"Source\":\"OATP\",\"FirstSeen\":\"0001-01-01T00:00:00\"},{\"$id\":\"7\",\"Name\":\"pix.jpg\",\"FileHashes\":[{\"$id\":\"8\",\"Algorithm\":\"SHA256\",\"Value\":\"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b\",\"Type\":\"filehash\"}],\"Type\":\"file\",\"MalwareFamily\":\"\",\"Urn\":\"urn:FileEntity:6cfb0a0866370a891ce96e9c83fb4fed\",\"Source\":\"OATP\",\"FirstSeen\":\"0001-01-01T00:00:00\"}],\"LogCreationTime\":\"2023-11-21T12:24:02.9479392Z\",\"MachineName\":\"DBAEUR03BG405\",\"SourceTemplateType\":\"Threat_Single\",\"Category\":\"ThreatManagement\",\"SourceAlertType\":\"System\"}",
"DeepLinkUrl": "https://security.microsoft.com/mtp-investigation/urn:ZappedFileInvestigation:adffaf6ed0f17079cf14e9dc2adf9c1d",
"EndTimeUtc": "0001-01-01T00:00:00",
"InvestigationId": "urn:ZappedFileInvestigation:adffaf6ed0f17079cf14e9dc2adf9c1d",
"InvestigationName": "Mail with malicious file is zapped - urn:ZappedFileInvestigation:adffaf6ed0f17079cf14e9dc2adf9c1d",
"InvestigationType": "ZappedFileInvestigation",
"LastUpdateTimeUtc": "2023-11-21T12:21:48",
"StartTimeUtc": "2023-11-21T12:24:03",
"Status": "Investigation Started"
}
{
"AppAccessContext": {
"AADSessionId": "ANONYMIZED",
"CorrelationId": "ANONYMIZED",
"UniqueTokenId": "ANONYMIZED"
},
"CreationTime": "2023-12-13T10:08:25",
"Id": "ANONYMIZED",
"Operation": "ListViewed",
"OrganizationId": "ANONYMIZED",
"RecordType": 36,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "SharePoint",
"ClientIP": "0.0.0.0",
"UserId": "user1",
"AuthenticationType": "FormsCookieAuth",
"BrowserName": "Chrome",
"BrowserVersion": "102.0.5005.197",
"CorrelationId": "ANONYMIZED",
"EventSource": "SharePoint",
"IsManagedDevice": false,
"ItemType": "List",
"ListId": "xxxxxx",
"Platform": "WinDesktop",
"Site": "xxxxxx",
"UserAgent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Teams/1.6.00.29964 Chrome/102.0.5005.197 Electron/19.1.8 Safari/537.36",
"WebId": "xxxxxx",
"DeviceDisplayName": "xxxxxx",
"CustomizedDoclib": false,
"FromApp": true,
"ItemCount": 102,
"ListBaseTemplateType": "101",
"ListBaseType": "DocumentLibrary",
"ListColor": "",
"ListIcon": "",
"Source": "Unknown",
"TemplateTypeId": "",
"ListTitle": "xxxxxx",
"ObjectId": "https://domain.com/subdomain/xxxxxx"
}
{
"CreationTime": "2024-06-26T06:29:14",
"Id": "ANONYMIZED",
"Operation": "MailItemsAccessed",
"OrganizationId": "ANONYMIZED",
"RecordType": 50,
"ResultStatus": "Succeeded",
"UserKey": "ANONYMIZED",
"UserType": 5,
"Version": 1,
"Workload": "Exchange",
"UserId": "ANONYMIZED",
"AppId": "ANONYMIZED",
"ClientAppId": "clientappidxxxx-xxx-xxx-xxxx",
"ClientIPAddress": "FE80::",
"ClientInfoString": "Client=Exemple1;Client=Exemple2;;",
"ExternalAccess": "False",
"InternalLogonType": 0,
"LogonType": 0,
"LogonUserSid": "S-1-2-3",
"MailboxGuid": "ANONYMIZED",
"MailboxOwnerSid": "S-1-2-3",
"MailboxOwnerUPN": "ANONYMIZED",
"OperationProperties": [
{
"Name": "MailAccessType",
"Value": "Bind"
},
{
"Name": "IsThrottled",
"Value": "False"
}
],
"OrganizationName": "organization.microsoft.com",
"OriginatingServer": "server (0.0.0000.000)\r\n",
"Folders": [
{
"FolderItems": [
{
"ClientRequestId": "ANONYMIZED",
"Id": "aaaaaaaaaaaaa",
"InternetMessageId": "xxxxx@exemple.com",
"SizeInBytes": 127625
},
{
"ClientRequestId": "ANONYMIZED",
"Id": "aaaaaaaaaaaaaaaaaa",
"InternetMessageId": "xxxx-xxx-xxx-xxxx@enterprise.net",
"SizeInBytes": 147360
}
],
"Id": "aaaaaaaaaaaaaaaaaaaa",
"Path": "Boite de reception"
}
],
"OperationCount": 2
}
{
"ActionId": "a81edede-be03-41f4-aae2-b6b25186adc6",
"ActionName": "Enable self-service password reset",
"ActionProducts": [],
"ActionScore": 26.0,
"ActionScoreChange": -1.0,
"ActionActivity": "COMPLIANCEMANAGER-SCORECHANGE",
"Assessments": [],
"Templates": [],
"Solutions": [],
"ManagedBy": "User",
"ActionScope": "Tenant",
"UserId": "",
"Id": "aa9367e4-9fa3-4709-8326-b35c04f784d2",
"RecordType": 155,
"CreationTime": "2022-10-05T10:12:57",
"Operation": "COMPLIANCEMANAGER-SCORECHANGE",
"OrganizationId": "ANONYMIZED",
"UserType": 2,
"UserKey": "user1",
"Workload": "ComplianceManager",
"ResultStatus": "Successful",
"Version": 1
}
{
"CreationTime": "2024-05-24T06:29:22",
"Id": "03604c8d-ed69-466b-a9f4-80467c958739",
"Operation": "AlertUpdated",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "f54a9b97-a432-471b-a84a-ddcba13f5f35",
"UserId": "SecurityComplianceAlerts",
"AlertId": "2c7f6c46-33d7-4101-b2fc-0af27eaf308a",
"AlertLinks": [],
"AlertType": "System",
"Category": "ThreatManagement",
"Comments": "New alert",
"Data": "{\"f3u\":\"john.doe@example.com\",\"ts\":\"2024-05-24T05:44:00Z\",\"te\":\"2024-05-24T05:45:00Z\",\"op\":\"UserSubmission\",\"wl\":\"SecurityComplianceCenter\",\"tid\":\"8a1a1157-0272-492d-ab10-3f9853ac8183\",\"tdc\":\"1\",\"reid\":\"a04c1571-7271-445e-82e3-c39f848aceb8\",\"wsrt\":\"2024-05-24T05:45:22\",\"mdt\":\"Audit\",\"rid\":\"9a36861c-cc4d-4818-be4a-a20555480a00\",\"cid\":\"2b6fda52-8386-4213-b6fb-2fcb078571c4\",\"ad\":\"This alert is triggered when any email message is reported as malware or phish by users -V1.0.0.3\",\"lon\":\"UserSubmission\",\"an\":\"Email reported by user as malware or phish\",\"sev\":\"Low\",\"ail\":\"https://security.microsoft.com/mtp-investigation/urn:SubmissionInvestigation:260a29b9cf8a4358857b82aa9f086c48\"}",
"Name": "Email reported by user as malware or phish",
"PolicyId": "5b31bd58-7d6e-4f97-aa6b-5135fb1b1e52",
"Severity": "Low",
"Source": "Office 365 Security & Compliance",
"Status": "Resolved"
}
{
"CreationTime": "2025-08-13T14:02:32",
"Id": "id-1",
"Operation": "MipLabel",
"OrganizationId": "ANONYMIZED",
"RecordType": 43,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"ObjectId": "objectid-1",
"UserId": "user1",
"ApplicationMode": "Standard",
"ItemName": "ANONYMIZED",
"LabelAction": "None",
"LabelAppliedDateTime": "2025-06-25T12:40:11",
"LabelId": "labelid-1",
"LabelName": "Internal",
"Receivers": [
"user-2@example.com",
"user-3@example.com",
"user-4@example.com",
"user-5@example.com",
"user-6@example.com",
"user-7@example.com",
"user-8@example.com",
"user-9@example.com",
"user-10@example.com",
"user-11@example.com",
"user-12@example.com",
"user-13@example.com",
"user-14@example.com",
"user-15@example.com",
"user-16@example.com",
"user-17@example.com",
"user-18@example.com",
"user-19@example.com",
"user-20@example.com"
],
"Sender": "user1"
}
{
"CreationTime": "2025-11-25T10:41:35",
"Id": "TEST_RECORD_ID",
"Operation": "Add application.",
"OrganizationId": "ANONYMIZED",
"RecordType": 8,
"ResultStatus": "Success",
"UserKey": "user1",
"UserType": 4,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ObjectId": "Application_123123123123213",
"UserId": "user1",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "additionalDetails",
"Value": "{\"AppId\":\"TEST_APP_Id\",\"Source\":\"{\\\"TYPE\\\":\\\"USER\\\",\\\"OBJECT ID\\\":\\\"22222222-2222-2222-2222-222222222222\\\"}\"}"
},
{
"Name": "extendedAuditEventCategory",
"Value": "Application"
}
],
"ModifiedProperties": [
{
"Name": "AppAddress",
"NewValue": "[\r\n {\r\n \"AddressType\": 0,\r\n \"Address\": \"https://*.services.adobe.com/federated/saml/SSO/alias/*\",\r\n \"ReplyAddressClientType\": 0,\r\n \"ReplyAddressIndex\": null,\r\n \"IsReplyAddressDefault\": false\r\n }\r\n]",
"OldValue": "[]"
},
{
"Name": "AppId",
"NewValue": "[\r\n \"TEST_APP_Id\"\r\n]",
"OldValue": "[]"
},
{
"Name": "AvailableToOtherTenants",
"NewValue": "[\r\n false\r\n]",
"OldValue": "[]"
},
{
"Name": "DisplayName",
"NewValue": "[\r\n \"Adobe Identity Management (SAML)\"\r\n]",
"OldValue": "[]"
},
{
"Name": "Entitlement",
"NewValue": "[\r\n {\r\n \"EntitlementEncodingVersion\": 2,\r\n \"EntitlementId\": \"33333333-3333-3333-3333-333333333333\",\r\n \"IsDisabled\": false,\r\n \"Origin\": 0,\r\n \"Name\": \"Access Adobe Identity Management (SAML)\",\r\n \"Description\": \"Allow the application to access Adobe Identity Management (SAML) on behalf of the signed-in user.\",\r\n \"Definition\": null,\r\n \"ClaimValue\": \"user_impersonation\",\r\n \"ResourceScopeType\": 1,\r\n \"IsPrivate\": false,\r\n \"UserConsentDisplayName\": \"Access Adobe Identity Management (SAML)\",\r\n \"UserConsentDescription\": \"Allow the application to access Adobe Identity Management (SAML) on your behalf.\",\r\n \"DirectAccessGrantTypes\": [],\r\n \"ImpersonationAccessGrantTypes\": [\r\n {\r\n \"Impersonator\": 29,\r\n \"Impersonated\": 20\r\n }\r\n ],\r\n \"EntitlementCategory\": 0,\r\n \"DependentMicrosoftGraphPermissions\": [],\r\n \"IsPreauthzOnlyDirectAccessGrant\": false,\r\n \"IsPreauthzOnlyImpersonationGrant\": false\r\n }\r\n]",
"OldValue": "[]"
},
{
"Name": "PublicClient",
"NewValue": "[\r\n false\r\n]",
"OldValue": "[]"
},
{
"Name": "WwwHomepage",
"NewValue": "[\r\n \"https://*.services.adobe.com/federated/saml/SSO/alias/*?metadata=adobeidentitymanagement|ISV9.1|primary|z\"\r\n]",
"OldValue": "[]"
},
{
"Name": "PublisherDomain",
"NewValue": "[\r\n \"ocd-testing.com\"\r\n]",
"OldValue": "[]"
},
{
"Name": "SignInAudience",
"NewValue": "[\r\n \"AzureADMyOrg\"\r\n]",
"OldValue": "[]"
},
{
"Name": "Included Updated Properties",
"NewValue": "AppAddress, AppId, AvailableToOtherTenants, DisplayName, Entitlement, PublicClient, WwwHomepage, PublisherDomain, SignInAudience",
"OldValue": ""
}
],
"Actor": [
{
"ID": "AAD App Management",
"Type": 1
},
{
"ID": "55555555-5555-5555-5555-555555555555",
"Type": 2
},
{
"ID": "user1",
"Type": 2
},
{
"ID": "44444444-4444-4444-4444-444444444444",
"Type": 2
},
{
"ID": "ServicePrincipal",
"Type": 2
}
],
"ActorContextId": "ANONYMIZED",
"InterSystemsId": "TEST_CORRELATION_ID",
"IntraSystemId": "11111111-1111-1111-1111-111111111111",
"SupportTicketId": "",
"Target": [
{
"ID": "Application_123123123123213",
"Type": 2
},
{
"ID": "123123123123213",
"Type": 2
},
{
"ID": "Application",
"Type": 2
},
{
"ID": "Adobe Identity Management (SAML)",
"Type": 1
},
{
"ID": "TEST_APP_Id",
"Type": 2
}
],
"TargetContextId": "ANONYMIZED"
}
{
"AppAccessContext": {
"AADSessionId": "44444444-4444-4444-4444-444444444444",
"IssuedAtTime": "2026-04-16T13:01:17",
"UniqueTokenId": "REDACTED"
},
"CreationTime": "2026-04-16T13:07:07",
"Id": "55555555-5555-5555-5555-555555555555",
"Operation": "Set-Mailbox",
"OrganizationId": "33333333-3333-3333-3333-333333333333",
"RecordType": 1,
"ResultStatus": "True",
"UserKey": "john.doe@example.com",
"UserType": 2,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "1.1.1.1:26061",
"ObjectId": "Jane DOE",
"UserId": "john.doe@example.com",
"AppId": "",
"AppPoolName": "MSExchangeOWAAppPool",
"ClientAppId": "",
"CorrelationID": "",
"DeviceId": "22222222-2222-2222-2222-222222222222",
"ExternalAccess": false,
"OrganizationName": "example.onmicrosoft.com",
"OriginatingServer": "HOSTNAME (15.20.9818.014)",
"Parameters": [
{
"Name": "Identity",
"Value": "ABC123456.PROD.OUTLOOK.COM/Microsoft Exchange Hosted Organizations/example.onmicrosoft.com/Jane DOE"
},
{
"Name": "ForwardingSmtpAddress",
"Value": "smtp:jane.doe@example.org"
},
{
"Name": "DeliverToMailboxAndForward",
"Value": "True"
}
],
"RequestId": "66666666-6666-6666-6666-666666666666",
"SessionId": "44444444-4444-4444-4444-444444444444",
"TokenObjectId": "11111111-1111-1111-1111-111111111111",
"TokenTenantId": "33333333-3333-3333-3333-333333333333"
}
{
"CreationTime": "2022-04-05T20:35:01",
"Id": "5615b32d-4c18-4ada-cc88-08da1743c258",
"Operation": "Create",
"OrganizationId": "ANONYMIZED",
"RecordType": 2,
"ResultStatus": "Succeeded",
"UserKey": "10033FFF80D15ECF",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "192.0.2.1",
"UserId": "user1",
"AppId": "27922004-5251-4030-b22d-91ecd9a37ea4",
"ClientIPAddress": "192.0.2.1",
"ClientInfoString": "Client=OutlookService;Outlook-iOS/2.0;",
"ClientRequestId": "1725",
"ExternalAccess": false,
"InternalLogonType": 0,
"LogonType": 0,
"LogonUserSid": "user1",
"MailboxGuid": "24683bc8-fab1-48b3-b834-cb11b95bb911",
"MailboxOwnerSid": "user1",
"MailboxOwnerUPN": "user1",
"OrganizationName": "xxxx.onmicrosoft.com",
"OriginatingServer": "PR3PR03MB6601 (15.20.4200.000)\r\n",
"SessionId": "8ad3822b-1cfd-40e7-aeaa-6d0708691ad8",
"Item": {
"Id": "LgAAAAAdhAMRqmYRzZvIAKoAL8RaDQCB1ldAzYsRRItL+noffZbOAATJxTeHAAAJ",
"InternetMessageId": "<11111111111111111111111111@example.com>",
"IsRecord": false,
"ParentFolder": {
"Id": "LgAAAAAbOnSFmOkITaMliEZRj+Z3AQAPzmaC0nx3Qo/JWqclreA/AAAEUskDAAAB",
"Path": "\\Drafts1"
},
"SizeInBytes": 34785,
"Subject": "ANONYMIZED"
}
}
{
"CreationTime": "2023-09-15T18:16:53",
"Id": "461a38ce-fc36-4a4d-b73e-643262cc063f",
"Operation": "MailItemsAccessed",
"OrganizationId": "ANONYMIZED",
"RecordType": 50,
"ResultStatus": "Succeeded",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"UserId": "user1",
"AppId": "00000002-0000-0ff1-ce00-000000000000",
"ClientIPAddress": "192.0.2.1",
"ClientInfoString": "Client=OWA;Action=ViaProxy",
"ExternalAccess": false,
"InternalLogonType": 0,
"LogonType": 0,
"LogonUserSid": "S-1-2-3",
"MailboxGuid": "03d9e949-cbc1-4dd2-b7ba-8a1d1e0207b5",
"MailboxOwnerSid": "S-1-2-3",
"MailboxOwnerUPN": "user1",
"OperationProperties": [
{
"Name": "MailAccessType",
"Value": "Bind"
},
{
"Name": "IsThrottled",
"Value": "False"
}
],
"OrganizationName": "example.onmicrosoft.com",
"OriginatingServer": "AM0PR07MB5763 (15.20.4200.000)\r\n",
"SessionId": "dcdad6b2-f279-48c6-9ed8-3df0ffde4ece",
"Folders": [
{
"FolderItems": [
{
"InternetMessageId": "<AM0PR07MB576312B164491AF0F9214C738DF6A@AM0PR07MB5763.eurprd07.prod.outlook.com>",
"Sensitivity": "defa4170-0d19-0005-0004-bc88714345d2",
"SizeInBytes": 3476
},
{
"InternetMessageId": "<AM0PR07MB5763A95F7E4A5BA512692F698DF6A@AM0PR07MB5763.eurprd07.prod.outlook.com>",
"SizeInBytes": 4871
},
{
"InternetMessageId": "<AM0PR07MB57633CFE8EE2ACB8CEF184AC8DF6A@AM0PR07MB5763.eurprd07.prod.outlook.com>",
"SizeInBytes": 4873
}
],
"Id": "LgAAAABxSjbeIoBUT6MlFIM9cqcFAQCxmw0Q8U/kQIyFE2Uk+mwoAAAAAAEPAAAB",
"Path": "\\Brouillons"
}
],
"OperationCount": 3
}
{
"CreationTime": "2023-09-15T18:11:42",
"Id": "d0d7820c-cdbe-4524-bf75-08dbb61736bf",
"Operation": "HardDelete",
"OrganizationId": "ANONYMIZED",
"RecordType": 3,
"ResultStatus": "Succeeded",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "192.0.2.1",
"UserId": "user1",
"AppId": "00000002-0000-0ff1-ce00-000000000000",
"ClientIPAddress": "192.0.2.1",
"ClientInfoString": "Client=OWA;Action=ViaProxy",
"ExternalAccess": false,
"InternalLogonType": 0,
"LogonType": 0,
"LogonUserSid": "S-1-2-3",
"MailboxGuid": "03d9e949-cbc1-4dd2-b7ba-8a1d1e0207b5",
"MailboxOwnerSid": "S-1-2-3",
"MailboxOwnerUPN": "user1",
"OrganizationName": "example.onmicrosoft.com",
"OriginatingServer": "AM0PR07MB5763 (15.20.4200.000)\r\n",
"SessionId": "dcdad6b2-f279-48c6-9ed8-3df0ffde4ece",
"AffectedItems": [
{
"Id": "RgAAAABxSjbeIoBUT6MlFIM9cqcFBwCxmw0Q8U/kQIyFE2Uk+mwoAAAAAAEbAACxmw0Q8U/kQIyFE2Uk+mwoAABVzgKRAAAJ",
"InternetMessageId": "<AM0PR07MB57631C0B52D097386841A4998D37A@AM0PR07MB5763.eurprd07.prod.outlook.com>",
"ParentFolder": {
"Id": "LgAAAABxSjbeIoBUT6MlFIM9cqcFAQCxmw0Q8U/kQIyFE2Uk+mwoAAAAAAEbAAAB",
"Path": "\\Recoverable Items\\Deletions"
},
"Subject": ""
}
],
"CrossMailboxOperation": false,
"Folder": {
"Id": "LgAAAABxSjbeIoBUT6MlFIM9cqcFAQCxmw0Q8U/kQIyFE2Uk+mwoAAAAAAEbAAAB",
"Path": "\\Recoverable Items\\Deletions"
}
}
{
"CreationTime": "2023-08-22T13:51:02",
"Id": "5f24aa82-f874-44d1-b6df-857cd9e1decf",
"Operation": "SoftDelete",
"OrganizationId": "ANONYMIZED",
"RecordType": 3,
"ResultStatus": "Succeeded",
"UserKey": "11111111111111",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "1.2.3.4",
"UserId": "user1",
"ClientIPAddress": "1.2.3.4",
"ClientInfoString": "Client=MSExchangeRPC",
"ClientProcessName": "OUTLOOK.EXE",
"ClientRequestId": "{037FD006-A72B-49AE-4BB0-08DBA30C8729}",
"ClientVersion": "16.0.15601.20364",
"ExternalAccess": false,
"InternalLogonType": 0,
"LogonType": 0,
"LogonUserSid": "S-1-2-3",
"MailboxGuid": "8208550a-4001-439d-a9f6-e95d76767507",
"MailboxOwnerSid": "S-1-2-3",
"MailboxOwnerUPN": "user1",
"OrganizationName": "example.onmicrosoft.com",
"OriginatingServer": "MYSERVER (15.20.4200.000)\r\n",
"SessionId": "77f6d9ce-da8f-46bf-a651-4bec3c189770",
"AffectedItems": [
{
"Attachments": "image006.png (6438b); image007.png (449b); image008.png (448b); image009.png (449b); image010.jpg (2443b); image011.png (6444b); image012.png (447b); image013.png (448b)",
"Id": "333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333",
"InternetMessageId": "<44444444444444444444444444444444444444@EXAMPLE.COM>",
"ParentFolder": {
"Id": "1111111111111111111111111111111111111111111111111111111111111111",
"Path": "\\Draft"
},
"Subject": "Re: HI"
}
],
"CrossMailboxOperation": false,
"Folder": {
"Id": "2222222222222222222222222222222222222222222222222222222222222222",
"Path": "\\Draft"
}
}
{
"AppAccessContext": {
"APIId": ""
},
"CreationTime": "2025-09-16T14:46:55",
"Id": "135ddd32-fee4-4f54-8606-7f203190b25f",
"Operation": "SoftDelete",
"OrganizationId": "ANONYMIZED",
"RecordType": 3,
"ResultStatus": "Succeeded",
"UserKey": "11111111111111",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "1.2.3.4",
"UserId": "user1",
"ActorInfoString": "OUTLOOK.EXE/16.0.10417.20051",
"ClientIPAddress": "1.2.3.4",
"ClientInfoString": "Client=MSExchangeRPC",
"ClientProcessName": "OUTLOOK.EXE",
"ClientRequestId": "{D10D3A8A-BCFF-481B-B609-2AE0B1DE9B14}",
"ClientVersion": "16.0.10417.20051",
"ExternalAccess": false,
"InternalLogonType": 0,
"LogonType": 0,
"LogonUserSid": "S-1-2-3",
"MailboxGuid": "9f63ab44-248d-43a2-8565-63589e5232db",
"MailboxOwnerSid": "S-1-2-3",
"MailboxOwnerUPN": "user1",
"OrganizationName": "example.onmicrosoft.com",
"OriginatingServer": "MYSERVER (15.20.4200.000)\r\n",
"SessionId": "70d4272c-db05-4e17-90a6-5c475bab04b7",
"AffectedItems": [
{
"Attachments": "tps (report) 1.docx (1024b); image001.jpg (2048b); image002.jpg (4096b); image003.jpg (8192b)",
"Id": "ABCDEF0123456",
"InternetMessageId": "<message.id.test@0123456789.userabc.prod.outlook.com>",
"ParentFolder": {
"Id": "908eca3617c16126164465a986b6a2610f84efdcf91c46dc37a34f68954e2a3c",
"Path": "\\Test"
},
"Subject": "Report"
}
],
"CrossMailboxOperation": false,
"Folder": {
"Id": "908eca3617c16126164465a986b6a2610f84efdcf91c46dc37a34f68954e2a3c",
"Path": "\\Test"
},
"AssociatedAdminUnits": [
"4aef334f-5097-4b40-9286-d7b2efcd57bf"
]
}
{
"AppAccessContext": {
"AADSessionId": "98fb5d83-9a00-4efc-816e-22f61c2d7733",
"APIId": "3CF2EC34-D27B-4E15-9D67-1D77873D8FCC",
"ClientAppId": "3a278062-7639-4075-8973-bd650d7bf415",
"IssuedAtTime": "2025-09-23T09:13:33",
"UniqueTokenId": "0000000000000000000000"
},
"CreationTime": "2025-09-23T09:43:13",
"Id": "79971dfe-b09d-4caa-99f1-b86cd51bdbbe",
"Operation": "SoftDelete",
"OrganizationId": "ANONYMIZED",
"RecordType": 3,
"ResultStatus": "Succeeded",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "1.2.3.4",
"UserId": "user1",
"AuthType": "Bearer",
"ClientAppId": "3a278062-7639-4075-8973-bd650d7bf415",
"ClientIPAddress": "1.2.3.4",
"ClientInfoString": "Client=OWA;Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/1.2.3.4 Safari/537.36;",
"ExternalAccess": false,
"InternalLogonType": 0,
"LogonType": 0,
"LogonUserSid": "S-1-2-3",
"MailboxGuid": "10842c9e-1cd8-40cf-828f-412a3e28a70f",
"MailboxOwnerSid": "S-1-2-3",
"MailboxOwnerUPN": "user1",
"OrganizationName": "example.onmicrosoft.com",
"OriginatingServer": "SERVER (15.20.4200.000)\r\n",
"TokenObjectId": "cd57fb1a-c318-4941-bb6e-e81ee7a18350",
"TokenTenantId": "ANONYMIZED",
"TokenType": "V1AppActAs",
"AffectedItems": [
{
"Attachments": "C:\\Users\\USERDIR\\AppData\\Local\\Microsoft\\Windows\\Temporary Internet Files\\Content.Outlook\\ABCDEF\\1.pdf (9731941b)",
"Id": "111111111111111111111111/222222222222U/A",
"InternetMessageId": "<message.id.test@0123456789.userabc.mail.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
},
"Subject": "SUBJECT"
},
{
"Attachments": "C:\\Users\\USERDIR\\AppData\\Local\\Microsoft\\Windows\\Temporary Internet Files\\Content.Outlook\\ABCDEF\\1.pdf (9731941b)",
"Id": "111111111111111111111111/222222222222VAA",
"InternetMessageId": "<message.id.test2@0123456789.userabc.mail.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
},
"Subject": "SUBJECT2"
},
{
"Attachments": "2.jpg (3440100b)",
"Id": "111111111111111111111111/222222222222VBA",
"InternetMessageId": "<1@email.android.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
}
},
{
"Attachments": "3.jpg (3405444b)",
"Id": "111111111111111111111111/222222222222VCA",
"InternetMessageId": "<2@email.android.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
}
},
{
"Attachments": "4.jpg (3184493b)",
"Id": "111111111111111111111111/222222222222VDA",
"InternetMessageId": "<3@email.android.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
}
}
],
"CrossMailboxOperation": false,
"Folder": {
"Id": "33333333333",
"Path": "\\Drafts"
}
}
{
"AppAccessContext": {
"AADSessionId": "98fb5d83-9a00-4efc-816e-22f61c2d7733",
"APIId": "3CF2EC34-D27B-4E15-9D67-1D77873D8FCC",
"ClientAppId": "3a278062-7639-4075-8973-bd650d7bf415",
"IssuedAtTime": "2025-09-23T09:13:33",
"UniqueTokenId": "0000000000000000000000"
},
"CreationTime": "2025-09-23T09:43:13",
"Id": "79971dfe-b09d-4caa-99f1-b86cd51bdbbe",
"Operation": "SoftDelete",
"OrganizationId": "ANONYMIZED",
"RecordType": 3,
"ResultStatus": "Succeeded",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "1.2.3.4",
"UserId": "user1",
"AuthType": "Bearer",
"ClientAppId": "3a278062-7639-4075-8973-bd650d7bf415",
"ClientIPAddress": "1.2.3.4",
"ClientInfoString": "Client=OWA;Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/1.2.3.4 Safari/537.36;",
"ExternalAccess": false,
"InternalLogonType": 0,
"LogonType": 0,
"LogonUserSid": "S-1-2-3",
"MailboxGuid": "10842c9e-1cd8-40cf-828f-412a3e28a70f",
"MailboxOwnerSid": "S-1-2-3",
"MailboxOwnerUPN": "user1",
"OrganizationName": "example.onmicrosoft.com",
"OriginatingServer": "SERVER (15.20.4200.000)\r\n",
"TokenObjectId": "cd57fb1a-c318-4941-bb6e-e81ee7a18350",
"TokenTenantId": "ANONYMIZED",
"TokenType": "V1AppActAs",
"AffectedItems": [
{
"Attachments": "C:\\Users\\USERDIR\\AppData\\Local\\Microsoft\\Windows\\Temporary Internet Files\\Content.Outlook\\ABCDEF\\1.pdf (9731941b)",
"Id": "111111111111111111111111/222222222222U/A",
"InternetMessageId": "<message.id.test@0123456789.userabc.mail.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
},
"Subject": "SUBJECT"
},
{
"Attachments": "C:\\Users\\USERDIR\\AppData\\Local\\Microsoft\\Windows\\Temporary Internet Files\\Content.Outlook\\ABCDEF\\1.pdf (9731941b)",
"Id": "111111111111111111111111/222222222222VAA",
"InternetMessageId": "<message.id.test2@0123456789.userabc.mail.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
},
"Subject": "SUBJECT2"
},
{
"Attachments": "2.jpg (3440100b)",
"Id": "111111111111111111111111/222222222222VBA",
"InternetMessageId": "<1@email.android.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
}
},
{
"Attachments": "3\n .jpg (3405444b)",
"Id": "111111111111111111111111/222222222222VCA",
"InternetMessageId": "<2@email.android.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
}
},
{
"Attachments": "4.jpg (3184493b)",
"Id": "111111111111111111111111/222222222222VDA",
"InternetMessageId": "<3@email.android.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
}
}
],
"CrossMailboxOperation": false,
"Folder": {
"Id": "33333333333",
"Path": "\\Drafts"
}
}
{
"AppAccessContext": {
"AADSessionId": "98fb5d83-9a00-4efc-816e-22f61c2d7733",
"APIId": "3CF2EC34-D27B-4E15-9D67-1D77873D8FCC",
"ClientAppId": "3a278062-7639-4075-8973-bd650d7bf415",
"IssuedAtTime": "2025-09-23T09:13:33",
"UniqueTokenId": "0000000000000000000000"
},
"CreationTime": "2025-09-23T09:43:13",
"Id": "79971dfe-b09d-4caa-99f1-b86cd51bdbbe",
"Operation": "SoftDelete",
"OrganizationId": "ANONYMIZED",
"RecordType": 3,
"ResultStatus": "Succeeded",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "1.2.3.4",
"UserId": "user1",
"AuthType": "Bearer",
"ClientAppId": "3a278062-7639-4075-8973-bd650d7bf415",
"ClientIPAddress": "1.2.3.4",
"ClientInfoString": "Client=OWA;Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/1.2.3.4 Safari/537.36;",
"ExternalAccess": false,
"InternalLogonType": 0,
"LogonType": 0,
"LogonUserSid": "S-1-2-3",
"MailboxGuid": "10842c9e-1cd8-40cf-828f-412a3e28a70f",
"MailboxOwnerSid": "S-1-2-3",
"MailboxOwnerUPN": "user1",
"OrganizationName": "example.onmicrosoft.com",
"OriginatingServer": "SERVER (15.20.4200.000)\r\n",
"TokenObjectId": "cd57fb1a-c318-4941-bb6e-e81ee7a18350",
"TokenTenantId": "ANONYMIZED",
"TokenType": "V1AppActAs",
"AffectedItems": [
{
"Attachments": "C:\\Users\\USERDIR\\AppData\\Local\\Microsoft\\Windows\\Temporary Internet Files\\Content.Outlook\\ABCDEF\\1.pdf (9731941b)",
"Id": "111111111111111111111111/222222222222U/A",
"InternetMessageId": "<message.id.test@0123456789.userabc.mail.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
},
"Subject": "SUBJECT"
},
{
"Attachments": "C:\\Users\\USERDIR\\AppData\\Local\\Microsoft\\Windows\\Temporary Internet Files\\Content.Outlook\\ABCDEF\\1.pdf (9731941b)",
"Id": "111111111111111111111111/222222222222VAA",
"InternetMessageId": "<message.id.test2@0123456789.userabc.mail.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
},
"Subject": "SUBJECT2"
},
{
"Attachments": "2.jpg (3440100b)",
"Id": "111111111111111111111111/222222222222VBA",
"InternetMessageId": "<1@email.android.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
}
},
{
"Attachments": "3 \"test\".jpg (3405444b)",
"Id": "111111111111111111111111/222222222222VCA",
"InternetMessageId": "<2@email.android.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
}
},
{
"Attachments": "4.jpg (3184493b)",
"Id": "111111111111111111111111/222222222222VDA",
"InternetMessageId": "<3@email.android.com>",
"ParentFolder": {
"Id": "33333333333",
"Path": "\\Drafts"
}
}
],
"CrossMailboxOperation": false,
"Folder": {
"Id": "33333333333",
"Path": "\\Drafts"
}
}
{
"AppAccessContext": {
"AADSessionId": "ANONYMIZED",
"APIId": "ANONYMIZED",
"ClientAppId": "ANONYMIZED",
"IssuedAtTime": "2025-10-26T13:12:18",
"UniqueTokenId": "AAAAAAAAAAAAAAAAAAAAAA"
},
"CreationTime": "2025-10-27T07:09:33",
"Id": "ANONYMIZED",
"Operation": "MailItemsAccessed",
"OrganizationId": "ANONYMIZED",
"RecordType": 50,
"ResultStatus": "Succeeded",
"UserKey": "0000000000000000",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"UserId": "user1",
"AppId": "ANONYMIZED",
"ClientAppId": "ANONYMIZED",
"ClientIPAddress": "1.2.3.4",
"ClientInfoString": "Client=OWA;Action=ViaProxy",
"DeviceId": "ANONYMIZED",
"ExternalAccess": false,
"InternalLogonType": 0,
"LogonType": 0,
"LogonUserSid": "S-1-2-3",
"MailboxGuid": "ANONYMIZED",
"MailboxOwnerSid": "S-1-2-3",
"MailboxOwnerUPN": "user1",
"OperationProperties": [
{
"Name": "MailAccessType",
"Value": "Bind"
}
],
"OrganizationName": "example.onmicrosoft.com",
"OriginatingServer": "EXCH01 (15.20.4200.000)\r\n",
"TokenObjectId": "ANONYMIZED",
"TokenTenantId": "ANONYMIZED",
"Folders": [
{
"FolderItems": [
{
"Id": "AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA",
"ImmutableId": "AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA",
"InternetMessageId": "<abcdef@mail.example.com>",
"SizeInBytes": 123456
}
],
"Id": "AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA",
"Path": "\\Inbox"
}
],
"OperationCount": 1
}
{
"AppAccessContext": {
"APIId": ""
},
"CreationTime": "2026-01-19T14:44:15",
"Id": "66666666-6666-6666-6666-666666666666",
"Operation": "SendAs",
"OrganizationId": "77777777-7777-7777-7777-777777777777",
"RecordType": 2,
"ResultStatus": "Succeeded",
"UserKey": "ANONYMIZED",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "1.1.1.1",
"UserId": "johndoe@example.net",
"ActorInfoString": "OUTLOOK.EXE/16.0.19328.20266",
"ClientIPAddress": "1.1.1.1",
"ClientInfoString": "Client=MSExchangeRPC",
"ClientProcessName": "OUTLOOK.EXE",
"ClientRequestId": "{11111111-1111-1111-1111-111111111111}",
"ClientVersion": "16.0.19328.20266",
"ExternalAccess": false,
"HostAppId": "44444444-4444-4444-4444-444444444444",
"InternalLogonType": 0,
"LogonType": 2,
"LogonUserSid": "S-1-2-3",
"MailboxGuid": "55555555-5555-5555-5555-555555555555",
"MailboxOwnerSid": "S-1-2-3",
"MailboxOwnerUPN": "johndoe@example.com",
"OrganizationName": "example.org",
"OriginatingServer": "HOSTNAME (15.20.4200.000)\r\n",
"SessionId": "33333333-3333-3333-3333-333333333333",
"Item": {
"Id": "REDACTED",
"ImmutableId": "REDACTED",
"InternetMessageId": "<1111111111111111111111111111111111111111111111111@HOSTNAME.example.com>",
"ParentFolder": {
"Id": "REDACTED",
"Path": "REDACTED"
},
"SizeInBytes": 21219,
"Subject": "Security alert: Fraudulent messages"
},
"SaveToSentItems": true,
"SendAsUserMailboxGuid": "22222222-2222-2222-2222-222222222222",
"SendAsUserSmtp": "janedoe@example.com"
}
{
"CreationTime": "2023-08-22T13:49:36",
"Id": "5f24aa82-f874-44d1-b6df-857cd9e1decf",
"Operation": "Update",
"OrganizationId": "ANONYMIZED",
"RecordType": 2,
"ResultStatus": "Succeeded",
"UserKey": "1111111111111111",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "192.0.2.1",
"UserId": "user1",
"AppId": "037fd006-a72b-49ae-4bb0-08dba30c8729",
"ClientAppId": "037fd006-a72b-49ae-4bb0-08dba30c8729",
"ClientIPAddress": "2603:1026:c09:834::5",
"ClientInfoString": "Client=REST;Client=RESTSystem;;",
"ClientRequestId": "037fd006-a72b-49ae-4bb0-08dba30c8729",
"ExternalAccess": false,
"InternalLogonType": 0,
"LogonType": 0,
"LogonUserSid": "user1",
"MailboxGuid": "8208550a-4001-439d-a9f6-e95d76767507",
"MailboxOwnerSid": "user1",
"MailboxOwnerUPN": "user1",
"OrganizationName": "example.onmicrosoft.com",
"OriginatingServer": "MYSERVER (15.20.4200.000)\r\n",
"Item": {
"Id": "333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333",
"InternetMessageId": "<44444444444444444444444444444444444444@EXAMPLE.COM>",
"ParentFolder": {
"Id": "1111111111111111111111111111111111111111111111111111111111111111",
"Path": "\\Draft"
},
"SizeInBytes": 70806,
"Subject": "ANONYMIZED"
},
"ModifiedProperties": [
"MapiEndTime",
"MapiPREndDate",
"TimeZone",
"TimeZoneBlob",
"TimeZoneDefinitionStart",
"TimeZoneDefinitionEnd",
"MapiStartTime",
"MapiPRStartDate",
"MapiIsAllDayEvent",
"TimeZoneDefinitionRecurring",
"AppointmentRecurring",
"AttendeeCriticalChangeTime",
"Location",
"SendRichInfo",
"PartnerNetworkUserId",
"PartnerNetworkId",
"SentRepresentingDisplayName",
"SentRepresentingEmailAddress",
"SentRepresentingType",
"SentRepresentingEntryId",
"SentRepresentingSmtpAddress",
"SipUri",
"SentRepresentingSID",
"When",
"BirthdayContactAttributionDisplayName",
"BirthdayLocal",
"ReceivedByName",
"ReceivedByEmailAddress",
"ReceivedByAddrType",
"ReceivedByEntryId",
"ReceivedBySmtpAddress",
"AllAttachmentsHidden",
"SenderDisplayName",
"SenderEmailAddress",
"SenderAddressType",
"SenderEntryId",
"SenderSmtpAddress",
"SenderSID",
"SentTime",
"HtmlBody",
"RtfBody",
"TextBody",
"DisplayName",
"CreationTime",
"MapiSubject",
"NormalizedSubjectInternal",
"SubjectPrefixInternal",
"ItemClass",
"ReplyForwardStatus",
"ReceivedTime",
"RecipientCollection"
]
}
{
"AppAccessContext": {
"ClientAppName": "MeTA",
"CorrelationId": "27de65c0-1c43-4d70-9a4d-45a66418dbd6"
},
"CreationTime": "2024-11-29T12:31:12",
"Id": "609745a8-8ec0-4305-8607-fa95f45cf370",
"Operation": "FileDownloaded",
"OrganizationId": "ANONYMIZED",
"RecordType": 6,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "OneDrive",
"ClientIP": "1.2.3.4",
"UserId": "urn:spo:guest#john.doe@example.com",
"AuthenticationType": "OAuth",
"BrowserName": "",
"BrowserVersion": "",
"CorrelationId": "27de65c0-1c43-4d70-9a4d-45a66418dbd6",
"DoNotDistributeEvent": true,
"EventSource": "SharePoint",
"GeoLocation": "EUR",
"IsManagedDevice": false,
"ItemType": "File",
"ListId": "56391ee5-91aa-44f9-810e-a5dc47abbb02",
"ListItemUniqueId": "1d91eda8-2918-42f0-8f2b-88dd9aaffcdf",
"Platform": "Service",
"Site": "582d798a-ba87-4a78-8792-87db9262b0a3",
"UserAgent": "OneDriveMpc-Transform_Zip/1.0",
"UserSessionId": "b332294a-fad5-45a0-8761-63922a2544bf",
"WebId": "ead1e78b-1d0c-4251-920a-f4fb48fce5e2",
"DeviceDisplayName": "5.6.7.8",
"EventSignature": "SOME_SIGNATURE",
"FileSizeBytes": 26860827,
"HighPriorityMediaProcessing": false,
"ListBaseType": 1,
"ListServerTemplate": 700,
"SourceFileExtension": "zip",
"ZipFileName": "1.zip",
"SiteUrl": "https://example.com/",
"SourceRelativeUrl": "Documents/IMT MBA",
"SourceFileName": "1.zip",
"ApplicationDisplayName": "MeTA",
"ObjectId": "https://example.com/1.zip"
}
{
"CreationTime": "2025-08-08T10:12:51",
"Id": "123123213-a9a8-123-885c-123123123",
"Operation": "AlertTriggered",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "31f138b3-da55-13123123-9200-08ddd663dfb8",
"UserId": "SecurityComplianceAlerts",
"AlertId": "31f138b3-da55-d6c2-123123123213-08ddd663dfb8",
"AlertLinks": [
{
"AlertLinkHref": ""
}
],
"AlertType": "Custom",
"Category": "DataLossPrevention",
"Comments": "New alert",
"Data": "{\"f3u\":\"john.doe@example.com\",\"ts\":\"2025-08-08T10:10:00.0000000Z\",\"te\":\"2025-08-08T10:11:00.0000000Z\",\"op\":\"DlpRuleMatch\",\"wl\":\"Endpoint\",\"tid\":\"123123123-62b5-46fa-adc3-117eedef841e\",\"tdc\":\"1\",\"reid\":\"87778fde-76c9-123123123-a42b-45a6af122292\",\"dpn\":\"Endpoint DLP Web - Low & High\",\"dpid\":\"2a236c69-8cea-123123312-a393-45f6e7ab87f3\",\"drn\":\"Low volume of content detected National ID Web\",\"drid\":\"83736f8f-428a-41dc-dqwerqerqwe-ae4e272ac590\",\"dact\":\"\",\"von\":\"REDACTED\",\"sitmi\":\"7f0e921c-9677-435b-aba2-123123123213:Malaysia Identity Card Number:1:123;12312312-c42e-47a0-9d85-bebed1c237d4:Germany Identity Card Number:1:123;123123123123-6d9d-4be1-a154-b531f7a91b41:EU National Identification Number:3:93123\",\"sict\":\"None;None;None\",\"dprm\":\"Enable\",\"eop\":\"FileUploadedToCloud\",\"enmd\":\"Audit\",\"tdmn\":\"web.whatsapp.com\",\"app\":\"chrome.exe\",\"ofph\":\"C:\\\\Users\\\\TestUser\\\\Downloads\\\\urururururutyrtyrty123-vaf.pdf\",\"dn\":\"lt-pf463p9n\",\"mddid\":\"123123123123123\",\"rmse\":\"False\",\"efs\":\"138307\",\"ecip\":\"1.2.3.4\",\"rtp\":108,\"wsrt\":\"2025-08-08T10:12:35\",\"mdt\":\"Audit\",\"rid\":\"9292992929292-0402-4b20-8faa-93efc2dd5672\",\"cid\":\"9ac45ff2-5c21-4e73-bf4a-1i1i1188181\",\"ad\":\"\",\"lon\":\"DlpRuleMatch\",\"an\":\"DLP-Low volume of content detected National ID Web\",\"sev\":\"Low\"}",
"Name": "DLP-Low volume of content detected National ID Web",
"PolicyId": "812812812812-123123-4e73-bf4a-fdcc40cbe8e0",
"Severity": "Low",
"Source": "Office 365 Security & Compliance",
"Status": "Active"
}
{
"CreationTime": "2025-08-08T09:55:45",
"Id": "uuid-1",
"Operation": "AlertTriggered",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "uuid-3",
"UserId": "SecurityComplianceAlerts",
"AlertId": "uuid-3",
"AlertLinks": [
{
"AlertLinkHref": ""
}
],
"AlertType": "Custom",
"Category": "DataLossPrevention",
"Comments": "New alert",
"Data": "{\"f3u\":\"user1@example.com\",\"ts\":\"2025-08-08T09:53:00.0000000Z\",\"te\":\"2025-08-08T09:54:00.0000000Z\",\"op\":\"DlpRuleMatch\",\"wl\":\"Endpoint\",\"tid\":\"uuid-2\",\"tdc\":\"1\",\"reid\":\"uuid-4\",\"dpn\":\"Endpoint DLP Web - Low & High\",\"dpid\":\"uuid-5\",\"drn\":\"HIGH: C3 File Web\",\"drid\":\"uuid-6\",\"dact\":\"\",\"von\":\"REDACTED\",\"dprm\":\"Enable\",\"eop\":\"FileUploadedToCloud\",\"enmd\":\"Warn\",\"tdmn\":\"example.gov\",\"app\":\"chrome.exe\",\"ofph\":\"C:\\\\Users\\\\UserName\\\\OneDrive - Example\\\\Admin\\\\Visa\\\\document.pdf\",\"dn\":\"device-1\",\"mddid\":\"hash-1\",\"rmse\":\"False\",\"efs\":\"232103\",\"ecip\":\"192.0.2.1\",\"rtp\":108,\"wsrt\":\"2025-08-08T09:55:29\",\"mdt\":\"Audit\",\"rid\":\"uuid-7\",\"cid\":\"uuid-8\",\"ad\":\"\",\"lon\":\"DlpRuleMatch\",\"an\":\"DLP-HIGH: C3 File Web\",\"sev\":\"Medium\"}",
"Name": "DLP-HIGH: C3 File Web",
"PolicyId": "uuid-8",
"Severity": "Medium",
"Source": "Office 365 Security & Compliance",
"Status": "Active"
}
{
"CreationTime": "2025-08-08T02:03:24",
"Id": "uuid-9",
"Operation": "AlertTriggered",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "uuid-10",
"UserId": "SecurityComplianceAlerts",
"AlertId": "uuid-10",
"AlertLinks": [
{
"AlertLinkHref": ""
}
],
"AlertType": "Custom",
"Category": "DataLossPrevention",
"Comments": "New alert",
"Data": "{\"f3u\":\"user2@example.com\",\"ts\":\"2025-08-08T01:59:00.0000000Z\",\"te\":\"2025-08-08T02:00:00.0000000Z\",\"op\":\"DlpRuleMatch\",\"wl\":\"Endpoint\",\"tid\":\"uuid-2\",\"tdc\":\"1\",\"reid\":\"uuid-11\",\"dpn\":\"Endpoint DLP Network Share - Low & High\",\"dpid\":\"uuid-12\",\"drn\":\"HIGH: C3 File Network Share\",\"drid\":\"uuid-13\",\"dact\":\"\",\"von\":\"REDACTED\",\"dprm\":\"Enable\",\"eop\":\"FileCopiedToNetworkShare\",\"enmd\":\"Warn\",\"app\":\"explorer.exe\",\"ofph\":\"C:\\\\Users\\\\UserName2\\\\OneDrive - Example\\\\FolderA\\\\REDACTED\",\"tfph\":\"\\\\\\\\fileserver\\\\InternalAudit\\\\FolderB\\\\REDACTED\",\"dn\":\"device-2\",\"mddid\":\"hash-2\",\"rmse\":\"False\",\"efs\":\"3362127\",\"ecip\":\"192.0.2.2\",\"rtp\":108,\"wsrt\":\"2025-08-08T02:02:45\",\"mdt\":\"Audit\",\"rid\":\"uuid-14\",\"cid\":\"uuid-15\",\"ad\":\"\",\"lon\":\"DlpRuleMatch\",\"an\":\"DLP-HIGH: C3 File Network Share\",\"sev\":\"Medium\"}",
"Name": "DLP-HIGH: C3 File Network Share",
"PolicyId": "uuid-15",
"Severity": "Medium",
"Source": "Office 365 Security & Compliance",
"Status": "Active"
}
{
"AppAccessContext": {
"ClientAppId": "f482d5ab-3acd-4c27-9721-30b09a03a648",
"ClientAppName": "f482d5ab-3acd-4c27-9721-30b09a03a648",
"CorrelationId": "75b4c463-190b-46e9-b38e-00b45b967900"
},
"CreationTime": "2025-03-08T19:21:47",
"Id": "955b44a7-49a5-4b9a-af2e-f26f949a7063",
"Operation": "FileMalwareDetected",
"OrganizationId": "ANONYMIZED",
"RecordType": 6,
"UserKey": "user1",
"UserType": 5,
"Version": 1,
"Workload": "SharePoint",
"ClientIP": "1.2.3.4",
"UserId": "user1",
"ApplicationId": "f482d5ab-3acd-4c27-9721-30b09a03a648",
"AuthenticationType": "OAuth",
"BrowserName": "",
"BrowserVersion": "",
"CorrelationId": "1b9688a1-5010-b000-c8c4-efdddefc18",
"EventSource": "SharePoint",
"GeoLocation": "FRA",
"IsManagedDevice": false,
"ItemType": "File",
"ListId": "b407ecfb-3392-415b-a860-836ff8f783a3",
"ListItemUniqueId": "79ace9be-1ee0-4107-a1e8-7fdd80710545",
"Platform": "Service",
"Site": "ead0c6a8-2b8b-4af8-84d8-8787c7660219",
"UserAgent": "MS Scanner ATP",
"WebId": "76d24e2e-9ad6-46a1-8107-68d8853b872b",
"DeviceDisplayName": "1.2.3.4",
"EventSignature": "SOME_SIGNATURE",
"HighPriorityMediaProcessing": false,
"ListBaseType": 0,
"ListServerTemplate": 0,
"SourceFileExtension": "zip",
"VirusInfo": "Trojan_Win32_MysticBlocker_Gen#",
"VirusVendor": "Advanced Threat Protection",
"SiteUrl": "https://example.com/",
"SourceRelativeUrl": "files",
"SourceFileName": "AdobePhotoshop20-cs_CZ_x64.zip",
"ApplicationDisplayName": "f482d5ab-3acd-4c27-9721-30b09a03a648",
"ObjectId": "https://example.com/files/AdobePhotoshop20-cs_CZ_x64.zip"
}
{
"AppAccessContext": {
"ClientAppName": "AntiVirusScanningHighVolumeWriteJob",
"CorrelationId": "c697b5ce-a4ec-4cac-8c97-620a6f1467ea"
},
"CreationTime": "2025-07-25T09:29:37",
"Id": "fa212399-9900-402b-9866-cedb12e31a96",
"Operation": "FileMalwareDetected",
"OrganizationId": "ANONYMIZED",
"RecordType": 6,
"UserKey": "S-1-2-3",
"UserType": 4,
"Version": 1,
"Workload": "OneDrive",
"ClientIP": "",
"UserId": "user1",
"CorrelationId": "c697b5ce-a4ec-4cac-8c97-620a6f1467ea",
"EventSource": "SharePoint",
"GeoLocation": "EUR",
"ItemType": "File",
"ListId": "159928cf-7b9f-4294-838e-f92dae5d6e90",
"ListItemUniqueId": "761b15b1-9342-4f0f-938e-a4e019b49876",
"Site": "3e355ece-4c7f-4204-8aca-f6044e642c2f",
"UserAgent": "",
"WebId": "9b3d42e0-4310-4970-a893-cc81ac577ea1",
"EventSignature": "SOME_SIGNATURE",
"HighPriorityMediaProcessing": false,
"ListBaseType": 0,
"ListServerTemplate": 0,
"VirusInfo": "Win32/KeyLogger.RDI!MTB",
"VirusVendor": "Default",
"SourceRelativeUrl": "Documents/Desktop",
"SourceFileName": "Test1.exe",
"SourceFileExtension": "exe",
"MD5Hash": "68b329da9893e34099c7d8ad5cb9c940",
"SHA256Hash": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b",
"ApplicationDisplayName": "AntiVirusScanningHighVolumeWriteJob",
"SiteUrl": "https://example.sharepoint.com/personal/hostname/",
"ObjectId": "https://example.com/"
}
{
"CreationTime": "2020-09-29T07:32:51",
"Id": "4e597c8c-e185-4ea5-3413-08d86449df74",
"Operation": "FilePreviewed",
"OrganizationId": "ANONYMIZED",
"RecordType": 6,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "OneDrive",
"ClientIP": "1.2.3.4",
"ObjectId": "https://example.com/",
"UserId": "user1",
"ApplicationId": "4345a7b9-9a63-4910-a426-35363201d503",
"CorrelationId": "41af7e9f-30a8-9000-8f78-756aca9a7474",
"DoNotDistributeEvent": "True",
"EventSource": "SharePoint",
"ItemType": "File",
"ListId": "2db6ee74-6bd7-4d9b-a63f-26ae6eef9fb3",
"ListItemUniqueId": "0e3f3538-8a03-4728-b431-225bc10687b6",
"Site": "2d3c44c1-d225-499d-a47f-bda2751a00b9",
"UserAgent": "OneDriveMpc-Transform_Thumbnail/1.0",
"WebId": "c4b81f7e-4f91-4b3a-97a7-660709edef15",
"HighPriorityMediaProcessing": "False",
"SourceFileExtension": "xlsx",
"SiteUrl": "https://company-my.sharepoint.com/personal/jane_doe_company_onmicrosoft_com/",
"SourceFileName": "MyDocument.docx",
"SourceRelativeUrl": "Documents"
}
{
"AppAccessContext": {
"AADSessionId": "xxxx-xxx-xxx-xxx",
"ClientAppName": "WebExcel",
"CorrelationId": "ANONYMIZED"
},
"CreationTime": "2024-02-22T16:06:53",
"Id": "ANONYMIZED",
"Operation": "FileModifiedExtended",
"OrganizationId": "ANONYMIZED",
"RecordType": 6,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "SharePoint",
"ClientIP": "0.0.0.0",
"UserId": "user1",
"AuthenticationType": "OAuth",
"BrowserName": "",
"BrowserVersion": "",
"CorrelationId": "ANONYMIZED",
"EventSource": "SharePoint",
"IsManagedDevice": false,
"ItemType": "File",
"ListId": "ANONYMIZED",
"ListItemUniqueId": "ANONYMIZED",
"Platform": "OfficeCollaborationService",
"Site": "xx-xxx-xx-xx",
"UserAgent": "Useragentname",
"WebId": "xxx-xx-xxx-xxx",
"DeviceDisplayName": "0.0.0.0",
"FileSizeBytes": 906087,
"HighPriorityMediaProcessing": false,
"ListBaseType": 1,
"ListServerTemplate": 101,
"SourceFileExtension": "xlsx",
"SiteUrl": "https://sharepoint.com/sites/filepath/",
"SourceRelativeUrl": "Folder/Path",
"SourceFileName": "FILENAME.xlsx",
"ApplicationDisplayName": "WebExcel",
"ObjectId": "https://example.com/"
}
{
"AppAccessContext": {
"AADSessionId": "0e042318-7c78-4acb-ae00-5ee74465bca3",
"CorrelationId": "c299a0a0-14da-428a-b08d-481d562298cb",
"UniqueTokenId": "0000000000000000000000"
},
"CreationTime": "2022-06-10T12:00:14",
"Id": "7c13b5d5-aa8d-48d1-b3d1-5f4b657136ba",
"Operation": "FileSyncDownloadedFull",
"OrganizationId": "ANONYMIZED",
"RecordType": 6,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "SharePoint",
"ClientIP": "1.2.3.4",
"ObjectId": "https://example.com/",
"UserId": "user1",
"CorrelationId": "4b25e3d9-1e4f-4c62-a544-da747449f144",
"EventSource": "SharePoint",
"ItemType": "File",
"ListId": "ca07dda5-0cdc-4399-94a6-303a7aa8ac00",
"ListItemUniqueId": "ab5a159c-c8fd-409c-a48f-524c29df0341",
"Site": "1a53ae0f-8405-42ec-8c43-724101fd34a2",
"UserAgent": "Microsoft SkyDriveSync 22.099.0508.0001 ship; Windows NT 10.0 (19043)",
"WebId": "ba71b4fe-22e8-41cf-9eaf-48b1787bad16",
"MachineDomainInfo": "f059d209-e819-402b-a391-4941ff3860c6",
"MachineId": "884ecccb-1e44-4dd4-a2b5-b60517893ce0",
"FileSyncBytesCommitted": "1344200",
"HighPriorityMediaProcessing": false,
"SourceFileExtension": "png",
"SiteUrl": "https://company.sharepoint.com/sites/shared",
"SourceFileName": "logo.png",
"SourceRelativeUrl": "public/assets/website"
}
{
"Id": "40094389-7baf-a3ba-5acc-2773c002cfbe",
"RecordType": 22,
"CreationTime": "2022-09-07T12:22:07",
"Operation": "FileVisited",
"OrganizationId": "ANONYMIZED",
"UserType": 0,
"UserKey": "user1",
"Workload": "Yammer",
"ResultStatus": "TRUE",
"ObjectId": "Pix_C'est la rentre!.png",
"ClientIP": "192.0.2.1",
"UserId": "user1",
"ActorYammerUserId": 1315924230144,
"ActorUserId": "user1",
"YammerNetworkId": 6358000,
"Version": 1,
"FileId": 1439262310400,
"FileName": "Pix_C'est la rentre!.png",
"VersionId": 1460243079168
}
{
"CreationTime": "2023-12-13T10:08:21",
"Id": "ANONYMIZED",
"Operation": "EditForm",
"OrganizationId": "ANONYMIZED",
"RecordType": 66,
"ResultStatus": "Succeeded",
"UserKey": "ANONYMIZED",
"UserType": 0,
"Version": 1,
"Workload": "MicrosoftForms",
"ClientIP": "0.0.0.0",
"ObjectId": "xxxxxxx",
"UserId": "ANONYMIZED",
"ActivityParameters": "{\"EditOperation\":\"QuestionUpdated\"}",
"FormId": "xxxxxxx",
"FormName": "FormNameValue\n\n",
"FormType": 1,
"FormsUserType": 1,
"SourceApp": "ms-formweb"
}
{
"CreationTime": "2023-05-24T15:10:53",
"Id": "9cf2a1f7-90bc-494b-2784-08db5c691133",
"Operation": "New-InboxRule",
"OrganizationId": "ANONYMIZED",
"RecordType": 1,
"ResultStatus": "True",
"UserKey": "user1",
"UserType": 2,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "1.2.3.4:63070",
"ObjectId": "EURPR07A010.PROD.OUTLOOK.COM/Microsoft Exchange Hosted Organizations/example.onmicrosoft.com/bc1b1df3-f861-4aec-bf7c-40ce5b5566c1\\RULE_NAME",
"UserId": "user1",
"AppId": "00000002-0000-0ff1-ce00-000000000000",
"ClientAppId": "",
"ExternalAccess": false,
"OrganizationName": "example.onmicrosoft.com",
"OriginatingServer": "AM0PR07MB5763 (15.20.6411.029)",
"Parameters": [
{
"Name": "ForwardTo",
"Value": "bob@example.org"
},
{
"Name": "Force",
"Value": "False"
},
{
"Name": "AlwaysDeleteOutlookRulesBlob",
"Value": "False"
},
{
"Name": "RedirectTo",
"Value": "joe@example.org"
},
{
"Name": "From",
"Value": "alice@example.org"
},
{
"Name": "Name",
"Value": "RULE_NAME"
},
{
"Name": "DeleteMessage",
"Value": "True"
},
{
"Name": "FromAddressContainsWords",
"Value": "@example.org"
},
{
"Name": "MarkAsRead",
"Value": "True"
},
{
"Name": "StopProcessingRules",
"Value": "True"
},
{
"Name": "SubjectOrBodyContainsWords",
"Value": "keyword"
},
{
"Name": "MoveToFolder",
"Value": "Historique des conversations"
}
],
"SessionId": "984c0958-0631-4b90-b116-15094fc36847"
}
{
"AppAccessContext": {
"AADSessionId": "fbe7d318-3d7f-4645-9e03-caa46e2a8f01",
"CorrelationId": "5f24aa82-f874-44d1-b6df-857cd9e1decf",
"UniqueTokenId": "2222222222222222222222"
},
"CreationTime": "2023-08-22T12:37:20",
"Id": "037fd006-a72b-49ae-4bb0-08dba30c8729",
"Operation": "ManagedSyncClientAllowed",
"OrganizationId": "ANONYMIZED",
"RecordType": 4,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "SharePoint",
"ClientIP": "1.2.3.4",
"UserId": "user1",
"AuthenticationType": "FormsCookieAuth",
"BrowserName": "Edge",
"BrowserVersion": "114.0.1823.79",
"CorrelationId": "ec84154f-db9d-47cd-b1be-56d75cb8840e",
"EventSource": "SharePoint",
"IsManagedDevice": false,
"ItemType": "DocumentLibrary",
"Platform": "WinDesktop",
"Site": "1435321e-2bbb-417d-b21c-533e3ec15f5f",
"UserAgent": "Microsoft SkyDriveSync 23.101.0514.0004 ship; Windows NT 10.0 (19045)",
"WebId": "50ad5578-0fa1-4285-9cde-1e4f067fb892",
"DeviceDisplayName": "3deb:3c5e:59d0:53ad:1115:d3d7:58da:47d6",
"MachineDomainInfo": "8208550a-4001-439d-a9f6-e95d76767507",
"MachineId": "77f6d9ce-da8f-46bf-a651-4bec3c189770"
}
{
"CreationTime": "2024-02-22T09:56:48",
"Id": "0e042318-7c78-4acb-ae00-5ee74465bca3",
"Operation": "AlertUpdated",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "c299a0a0-14da-428a-b08d-481d562298cb",
"UserId": "SecurityComplianceAlerts",
"AlertId": "c299a0a0-14da-428a-b08d-481d562298cb",
"AlertLinks": [
{
"AlertLinkHref": ""
}
],
"AlertType": "Custom",
"Category": "ThreatManagement",
"Comments": "New alert",
"Data": "{\"ts\":\"2024-02-22 09:46:54Z\",\"te\":\"2024-02-22 09:46:54Z\",\"an\":\"Mass download by a single user\",\"ad\":\"Activity policy 'Mass download by a single user' was triggered by 'Anakin SKYWALKER'\",\"f3u\":\"john.doe@example.com\",\"alk\":\"https://example.com/#/alerts/79d71811t27fe160149dcd56\",\"plk\":\"https://gondor.portal.cloudappsecurity.com/#/policy/?id=eq(5f391720dd4e64e3db757c35,)\",\"mat\":\"MCAS_ALERT_CABINET_EVENT_MATCH_AUDIT\"}",
"Name": "Mass download by a single user",
"PolicyId": "8697dfdc-965d-67f7-bb37-b2551b296c04",
"Severity": "High",
"Source": "Cloud App Security",
"Status": "Active"
}
{
"Applications": [
{
"Name": "Microsoft SharePoint Online"
}
],
"AlertCategory": "ANOMALY_DETECTION",
"AlertDisplayName": "Impossible travel activity",
"AlertDescription": "The user JOHN DOE (john.doe@example.org) was involved in an impossible travel\n incident. The user connected from two countries within 10 minutes, from these IP addresses: Belgium\n (3deb:3c5e:59d0:53ad:1115:d3d7:58da:47d6) and France (1.2.3.4). If any of these IP addresses are used by the\n organization for VPN connections and do not necessarily represent a physical location, we recommend categorizing them as\n VPN in the IP Address range page in Microsoft Defender for Cloud Apps portal to avoid false alerts.",
"AlertSeverity": "Medium",
"AssignedTo": null,
"LastUpdatedTime": "2023-04-19T12:24:16",
"ActivityStartTime": "2023-04-19T12:07:08",
"ItemCount": 0,
"AlertUri": "https://example.portal.cloudappsecurity.com/#/alerts/111111111111111111111111",
"ClientIPs": [
"3deb:3c5e:59d0:53ad:1115:d3d7:58da:47d6",
"1.2.3.4"
],
"ObjectId": "643fdd70e8ff3e15bba6dfd8",
"UserId": "user1",
"Id": "ANONYMIZED",
"RecordType": 98,
"CreationTime": "2023-04-19T12:24:16",
"Operation": "MCAS_ALERT_ANUBIS_DETECTION_VELOCITY",
"OrganizationId": "ANONYMIZED",
"UserType": 0,
"UserKey": "user1",
"Workload": "MCAS",
"ResultStatus": "New",
"Version": 1
}
{
"CreationTime": "2022-07-07T22:38:49",
"Id": "266f5962-ffad-4fce-a101-3197581af3d4",
"Operation": "AtpDetection",
"OrganizationId": "ANONYMIZED",
"RecordType": 47,
"UserKey": "user1",
"UserType": 4,
"Version": 1,
"Workload": "ThreatIntelligence",
"UserId": "user1",
"DetectionDate": "2022-07-07T22:38:11",
"DetectionMethod": "AntiMalware",
"EventDeepLink": "https://example.com/",
"FileData": {
"DocumentId": "03254108-f682-417d-f3e6-08da605bf091",
"FileName": "malware",
"FilePath": "https://example.com/",
"FileSize": "12345",
"FileVerdict": 1,
"MalwareFamily": "iPhoneOS/Vortex.C",
"SHA256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"LastModifiedBy": "user1",
"LastModifiedDate": "2022-01-01T13:00:53",
"SourceWorkload": 1
}
{
"CreationTime": "2022-07-08T09:10:19",
"Id": "50906475-74dd-4447-ae4d-595d225d0055",
"Operation": "TIMailData",
"OrganizationId": "ANONYMIZED",
"RecordType": 28,
"UserKey": "user1",
"UserType": 4,
"Version": 1,
"Workload": "ThreatIntelligence",
"ObjectId": "4ca2df96-4488-4f3b-a265-b4edaa3c4d8f",
"UserId": "user1",
"AdditionalActionsAndResults": [
"OriginalDelivery: [N/A]"
],
"AttachmentData": [
{
"FileName": "malicious.pdf.exe",
"FileType": "exe;zip",
"FileVerdict": 1,
"MalwareFamily": "Trojan_Gen_FileWithSpoofedExtension_A",
"SHA256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
}
],
"AuthDetails": [
{
"Name": "SPF",
"Value": "Pass"
},
{
"Name": "DKIM",
"Value": "Fail"
},
{
"Name": "DMARC",
"Value": "Best guess pass"
},
{
"Name": "Comp Auth",
"Value": "pass"
}
],
"DeliveryAction": "Blocked",
"DetectionMethod": "File detonation",
"DetectionType": "Inline",
"Directionality": "Inbound",
"EventDeepLink": "https://example.com/",
"InternetMessageId": "<11111111-1111-1111-1111-111111111111@example.com>",
"LatestDeliveryLocation": "Quarantine",
"MessageTime": "2022-07-08T09:07:47",
"NetworkMessageId": "7250ff78-fd13-45a2-bb5d-23a5d59c2699",
"OriginalDeliveryLocation": "Quarantine",
"P1Sender": "prvs=0000000000=human@sender.com",
"P2Sender": "ANONYMIZED",
"Policy": "SafeAttachements",
"PolicyAction": "Quarantine",
"Recipients": [
"human@example.com"
],
"SenderIp": "1.2.3.4",
"Subject": "ANONYMIZED",
"SystemOverrides": [
{
"Details": "Antimalware policy block by file type",
"FinalOverride": "No",
"Result": "Block",
"Source": "Tenant"
}
],
"ThreatsAndDetectionTech": [
"Malware: [File detonation]",
"Spam: [General filter]"
],
"Verdict": "Malware"
}
{
"CreationTime": "2022-07-07T10:10:52",
"Id": "47bf7844-15bf-4cf2-91a3-15b32ceb89b5",
"Operation": "TIUrlClickData",
"OrganizationId": "ANONYMIZED",
"RecordType": 41,
"UserKey": "user1",
"UserType": 4,
"Version": 1,
"Workload": "ThreatIntelligence",
"UserId": "user1",
"AppName": "Mail",
"AppVersion": "0.0.0000",
"EventDeepLink": "https://example.com/",
"SourceId": "8a8634d0-d803-4bc9-b221-2863bff6a001",
"TimeOfClick": "2022-07-07T09:33:33",
"Url": "https://example.com/",
"UserIp": "1.2.3.4"
}
{
"AppAccessContext": {},
"CreationTime": "2024-10-28T10:34:13",
"Id": "ANONYMIZED",
"Operation": "UpdateInboxRules",
"OrganizationId": "ANONYMIZED",
"RecordType": 2,
"ResultStatus": "Succeeded",
"UserKey": "ANONYMIZED",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "1.2.3.4",
"UserId": "user1",
"ClientIPAddress": "1.2.3.4",
"ClientInfoString": "Client=xxxx-xxx-xxx-xxxx",
"ClientProcessName": "PROCESS.EXE",
"ClientRequestId": "{xxxx-xxx-xxx-xxxx}",
"ClientVersion": "16.0.17328.20550",
"ExternalAccess": false,
"InternalLogonType": 0,
"LogonType": 2,
"LogonUserSid": "S-1-2-3",
"MailboxGuid": "ANONYMIZED",
"MailboxOwnerMasterAccountSid": "S-1-2-3",
"MailboxOwnerSid": "S-1-2-3",
"MailboxOwnerUPN": "owner@mail.fr",
"OperationProperties": [
{
"Name": "RuleOperation",
"Value": "ModifyMailboxRule"
},
{
"Name": "RuleId",
"Value": "-123"
},
{
"Name": "RuleState",
"Value": "Enabled"
},
{
"Name": "RuleCondition",
"Value": "{(Exists(ItemClass))}"
},
{
"Name": "RuleName"
},
{
"Name": "RuleProvider",
"Value": "RuleOrganizer"
},
{
"Name": "RuleActions",
"Value": "[{\"ActionType\":\"Forward\",\"Recipients\":[\"john.doe@mail.fr\",\"user@email.fr\",\"asmithee@mailbox.fr\",\"user.name@mail.fr\"],\"ForwardFlags\":\"None\"}]"
}
],
"OrganizationName": "organization.com",
"OriginatingServer": "Origin Server\r\n",
"SessionId": "ANONYMIZED",
"Item": {
"Id": "ID12345",
"ImmutableId": "ErrorDuringIdConversion",
"ParentFolder": {
"Id": "ID12345",
"Name": "Bo\u00eete de r\u00e9ception",
"Path": "\\Bo\u00eete de r\u00e9ception"
}
}
}
{
"AppAccessContext": {},
"CreationTime": "2024-10-23T12:26:18",
"Id": "ANONYMIZED",
"Operation": "UpdateInboxRules",
"OrganizationId": "ANONYMIZED",
"RecordType": 2,
"ResultStatus": "Succeeded",
"UserKey": "123456",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "1.2.3.4",
"UserId": "user1",
"ClientIPAddress": "1.2.3.4",
"ClientInfoString": "Client=xxxx-xxx-xxx-xxxx",
"ClientProcessName": "PROCESS.EXE",
"ClientRequestId": "{xxxx-xxx-xxx-xxxx}",
"ClientVersion": "16.0.16731.20456",
"ExternalAccess": false,
"InternalLogonType": 0,
"LogonType": 0,
"LogonUserSid": "S-1-2-3",
"MailboxGuid": "ANONYMIZED",
"MailboxOwnerSid": "S-1-2-3",
"MailboxOwnerUPN": "user1",
"OperationProperties": [
{
"Name": "RuleOperation",
"Value": "ModifyMailboxRule"
},
{
"Name": "RuleId",
"Value": "4561233110666051585"
},
{
"Name": "RuleState",
"Value": "Enabled"
},
{
"Name": "RuleCondition",
"Value": "{(&(([RssServerLockStartTime=1, =r, =noreply-wham@mail.fr, DisplayType=0], ((SenderSearchKey Equal SMTP:NOREPLY-WHAM@MAIL.FR)))(SubString IgnoreCase(SubjectProperty)=WHAM)))}"
},
{
"Name": "RuleName"
},
{
"Name": "RuleProvider",
"Value": "RuleOrganizer"
},
{
"Name": "RuleActions",
"Value": "[{\"ActionType\":\"Forward\",\"Recipients\":[\"user.name@mail.fr\"],\"ForwardFlags\":\"None\"}]"
}
],
"OrganizationName": "organization.name.com",
"OriginatingServer": "Origin Server\r\n",
"SessionId": "ANONYMIZED",
"Item": {
"Id": "ANONYMIZED",
"ImmutableId": "ErrorDuringIdConversion",
"ParentFolder": {
"Id": "ANONYMIZED",
"Name": "Bo\u00eete de r\u00e9ception",
"Path": "\\Bo\u00eete de r\u00e9ception"
}
}
}
{
"AppAccessContext": {
"APIId": ""
},
"CreationTime": "2025-02-13T09:53:51",
"Id": "2b69a1a1-5e4e-4d1d-9feb-543d61b025e7",
"Operation": "UpdateInboxRules",
"OrganizationId": "ANONYMIZED",
"RecordType": 2,
"ResultStatus": "Succeeded",
"UserKey": "1111111111111111",
"UserType": 0,
"Version": 1,
"Workload": "Exchange",
"ClientIP": "1.2.3.4",
"UserId": "user1",
"ClientIPAddress": "1.2.3.4",
"ClientInfoString": "Client=MSExchangeRPC",
"ClientProcessName": "OUTLOOK.EXE",
"ClientRequestId": "{5ED2E898-FAAF-4A39-B9C3-407176A7087A}",
"ClientVersion": "16.0.5467.1000",
"ExternalAccess": false,
"InternalLogonType": 0,
"LogonType": 0,
"LogonUserSid": "user1",
"MailboxGuid": "e24b161f-f171-4db0-9572-4945279041c2",
"MailboxOwnerSid": "user1",
"MailboxOwnerUPN": "user1",
"OperationProperties": [
{
"Name": "RuleOperation",
"Value": "ModifyMailboxRule"
},
{
"Name": "RuleId",
"Value": "-5555555555555555555"
},
{
"Name": "RuleState",
"Value": "Enabled, ExitAfterExecution"
},
{
"Name": "RuleCondition",
"Value": "{(&((&((MessageToMe Equal True)(!((SubString Default(DisplayTo)=;)))))([RssServerLockStartTime=1, =/o=EXAMPLE/ou=Administrative (AAAAAAAAAAAAAAA)/cn=Recipients/cn=11111111111111111111111111111111111111111111, =Example, DisplayType=0], ((SenderSearchKey Equal EX:/O=EXAMPLE/OU=ADMINISTRATIVE (AAAAAAAAAAAAAAAAAAAA)/CN=RECIPIENTS/CN=BBBBBBBBBBBBBBBBBBBBBBBBBBBB)))(SubString IgnoreCase(SubjectProperty)=Incident - \")))}"
},
{
"Name": "RuleName",
"Value": "MyRule"
},
{
"Name": "RuleProvider",
"Value": "MyRuleProvider"
},
{
"Name": "RuleActions",
"Value": "[{\"ActionType\":\"DeferAction\",\"LengthOfDeferData\":\"1453\"}]"
}
],
"OrganizationName": "example.onmicrosoft.com",
"OriginatingServer": "RRRRRRRRRRRRR (15.20.4200.000)\r\n",
"SessionId": "514b0ea7-73b8-4fa7-85f0-195fb3846a86",
"Item": {
"Id": "TTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTT",
"ImmutableId": "ErrorDuringIdConversion",
"ParentFolder": {
"Id": "EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE",
"Name": "Mailbox",
"Path": "\\Mailbox"
}
}
}
{
"Id": "bb6e6d49",
"RecordType": 20,
"CreationTime": "2023-08-22T13:51:33",
"Operation": "ViewReport",
"OrganizationId": "ANONYMIZED",
"UserType": 0,
"UserKey": "user1",
"Workload": "PowerBI",
"UserId": "user1",
"ClientIP": "1.2.3.4",
"UserAgent": "Mozilla/5.0",
"Activity": "ViewReport",
"ItemName": "Tdb_TI",
"WorkSpaceName": "Tableau de Bord Strat\u00e9gique",
"DatasetName": "Tdb_TI",
"ReportName": "Tdb_TI",
"CapacityId": "5A456BD6",
"CapacityName": "P1_ACOSS",
"WorkspaceId": "08d52dac",
"AppName": "Tableaux de bord de pilotage",
"ObjectId": "Tdb_TI",
"DatasetId": "6f39a3c3",
"ReportId": "213eb6fe",
"ArtifactId": "213eb6fe",
"ArtifactName": "Tdb_TI",
"IsSuccess": true,
"ReportType": "PowerBIReport",
"RequestId": "94fea00c",
"ActivityId": "147a0db5",
"AppReportId": "fe6a9f80",
"DistributionMethod": "Apps",
"ConsumptionMethod": "Power BI Web",
"AppId": "187ea3f4",
"ArtifactKind": "Report",
"RefreshEnforcementPolicy": 0
}
{
"CreationTime": "2024-07-10T14:31:24",
"Id": "d1253377-388e-4ca1-a163-32dccb867ddd",
"Operation": "Remove member from role.",
"OrganizationId": "ANONYMIZED",
"RecordType": 8,
"ResultStatus": "Success",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ObjectId": "john.doe@example.com",
"UserId": "user1",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "additionalDetails",
"Value": "{}"
},
{
"Name": "extendedAuditEventCategory",
"Value": "Role"
}
],
"ModifiedProperties": [
{
"Name": "Role.ObjectID",
"NewValue": "",
"OldValue": "62d603c4-9712-4ea9-83c6-1e253fad40a4"
},
{
"Name": "Role.DisplayName",
"NewValue": "",
"OldValue": "Global Administrator"
},
{
"Name": "Role.TemplateId",
"NewValue": "",
"OldValue": "2eb5763a-6258-4084-90d6-8f149a03132d"
},
{
"Name": "Role.WellKnownObjectName",
"NewValue": "",
"OldValue": "TenantAdmins"
}
],
"Actor": [
{
"ID": "user1",
"Type": 5
},
{
"ID": "100320029D963D0D",
"Type": 3
},
{
"ID": "User_47498f0f-242d-4ec8-8c13-9c861ce5669f",
"Type": 2
},
{
"ID": "47498f0f-242d-4ec8-8c13-9c861ce5669f",
"Type": 2
},
{
"ID": "User",
"Type": 2
}
],
"ActorContextId": "ANONYMIZED",
"InterSystemsId": "3da056e9-e6dc-4157-b991-8304c3b95eb7",
"IntraSystemId": "e7bf6e46-a61f-417a-a11d-282756b8262f",
"SupportTicketId": "",
"Target": [
{
"ID": "User_1514c9ec-882d-4beb-99a9-301209f6a05a",
"Type": 2
},
{
"ID": "1514c9ec-882d-4beb-99a9-301209f6a05a",
"Type": 2
},
{
"ID": "User",
"Type": 2
},
{
"ID": "john.doe@example.com",
"Type": 5
},
{
"ID": "100320029D9D1C86",
"Type": 3
}
],
"TargetContextId": "ANONYMIZED"
}
{
"CreationTime": "2023-08-31T07:24:24",
"Id": "ANONYMIZED",
"Operation": "AlertTriggered",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "ANONYMIZED",
"UserId": "SecurityComplianceAlerts",
"AlertId": "ANONYMIZED",
"AlertLinks": [
{
"AlertLinkHref": ""
}
],
"AlertType": "System",
"Category": "ThreatManagement",
"Comments": "New alert",
"Data": "{\"ts\": \"2023-08-31T07:23:13.0000000Z\", \"te\": \"2023-08-31T07:23:13.0000000Z\", \"tid\": \"77f6d9ce-da8f-46bf-a651-4bec3c189770\", \"tdc\": \"1\", \"af\": \"0\", \"tht\": \"Phish,\\n\\nMalicious\", \"als\": \"Protection\", \"op\": \"Protection\", \"wsrt\": \"0001-01-01T00:00:00\", \"mdt\": \"u\", \"rid\": \"77f6d9ce-da8f-46bf-a651-4bec3c189770\", \"cid\": \"77f6d9ce-da8f-46bf-a651-4bec3c189770\", \"ad\": \"This\\nalert fires when message containing phish was delivered due to an ETR override. \\n-V1.0.0.5\", \"lon\": \"Protection\", \"an\": \"Phish delivered due to an ETR override\", \"sev\": \"Informational\"}",
"Name": "Phish delivered due to an ETR override",
"PolicyId": "ANONYMIZED",
"Severity": "Informational",
"Source": "Office 365 Security & Compliance",
"Status": "Active"
}
{
"CreationTime": "2024-04-04T08:15:14",
"Id": "11c950ca-f6b6-4bbf-a0fc-bb287f9c1ef4",
"Operation": "AlertEntityGenerated",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "9ccf6a76-3106-4bad-ad80-fc515b137ba2",
"UserId": "SecurityComplianceAlerts",
"AlertEntityId": "b2358a80-85d3-488e-8285-db123ce918a4",
"AlertId": "cf0708c6-e2c5-4962-ae99-9af4799175f4",
"AlertLinks": [
{
"AlertLinkHref": ""
}
],
"AlertType": "Custom",
"Category": "DataLossPrevention",
"Comments": "New alert",
"Data": "{\"etype\":\"DlpRuleMatch\",\"eid\":\"48aa73f6-b740-438b-861d-441281310de7\",\"tid\":\"21692c1b-2bd4-464a-aa27-6658fe410b4b\",\"ts\":\"2024-04-04T07:36:48.0000000Z\",\"te\":\"2024-04-04T07:36:48.0000000Z\",\"at\":\"2024-04-04T07:36:48.0000000Z\",\"dpid\":\"2401d128-ab89-4552-a6da-b2f77c3d212c\",\"dpn\":\"Data\",\"drid\":\"70ce5ca3-1da6-45d2-8699-8d470a719ab3\",\"drn\":\"rulename\",\"dmrid\":\"793fed0d-79e2-4bf8-b057-67c77a6db003\",\"wl\":\"Exchange\",\"von\":\"REDACTED\",\"dact\":\"GenerateAlert\",\"cc\":\"suspicious@example.com,spam.enquiries@example.org\",\"to\":\"john.doe@example.org\",\"mfrm\":\"spam@example.com\",\"dpm\":\"Enable\",\"lon\":\"DlpRuleMatch\"}",
"EntityType": "DlpRuleMatch",
"Name": "description",
"PolicyId": "bef2401e-5c6c-476b-aedb-e2f521fafb1f",
"Severity": "Low",
"Source": "Office 365 Security & Compliance",
"Status": "Active"
}
{
"CreationTime": "2024-04-04T08:09:07",
"Id": "9bb5e4b2-febd-4f1a-93bb-1380f7868320",
"Operation": "AlertEntityGenerated",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "4dde17d2-635a-498b-914e-73898a280433",
"UserId": "SecurityComplianceAlerts",
"AlertEntityId": "a1bba0c6-d8d0-4710-8fc3-6085b3ac79fc",
"AlertId": "178fa649-642f-4d41-943c-451e2266f4a7",
"AlertLinks": [
{
"AlertLinkHref": ""
}
],
"AlertType": "Custom",
"Category": "MailFlow",
"Comments": "New alert",
"Data": "{\"etype\":\"MalwareFamily\",\"at\":\"2024-04-04T08:07:58.0000000Z\",\"md\":\"2024-04-04T08:07:58.0000000Z\",\"sip\":\"217.182.111.68\",\"ms\":\"REDACTED\",\"imsgid\":\"<f2231b61bc5cbb95893c5b62281e4f4c@example.com>\",\"dm\":\"CrossOrgSpoof\",\"eid\":\"58fe2050-27be-431f-a035-2cba142cb021-15828634862951700795-1\",\"aii\":\"58fe2050-27be-431f-a035-2cba142cb021\",\"thn\":\"Phish, Malicious\",\"ts\":\"2024-04-04T08:06:58.0000000Z\",\"te\":\"2024-04-04T08:08:58.0000000Z\",\"fvs\":\"Filters\",\"tpt\":\"AntiPhishPolicy\",\"tpid\":\"b3caa8a3-c6de-4d06-b2a4-8968c6d1f2d5\",\"tid\":\"7fca7e7b-11e7-48c7-b345-1145a7a3a918\",\"tht\":\"Phish, Malicious\",\"trc\":\"john.doe@example.org\",\"tsd\":\"communications@example.com\",\"tdc\":\"1\",\"cpid\":null,\"lon\":\"Protection\"}",
"EntityType": "MalwareFamily",
"Name": "Phishing detected",
"PolicyId": "40663ca5-73da-43ca-b0be-af8b54987339",
"Severity": "Low",
"Source": "Office 365 Security & Compliance",
"Status": "Active"
}
{
"CreationTime": "2024-04-04T08:22:40",
"Id": "ANONYMIZED",
"Operation": "AlertEntityGenerated",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "john.doe@example.org",
"UserId": "SecurityComplianceAlerts",
"AlertEntityId": "john.doe@example.org",
"AlertId": "ANONYMIZED",
"AlertLinks": [
{
"AlertLinkHref": ""
}
],
"AlertType": "System",
"Category": "ThreatManagement",
"Comments": "New alert",
"Data": "{\"etype\":\"User\",\"eid\":\"john.doe@example.org\",\"tid\":\"be2ee3c6-2b3c-42ae-aefe-69f185114418\",\"ts\":\"2024-04-04T08:20:21.0000000Z\",\"te\":\"2024-04-04T08:20:21.0000000Z\",\"op\":\"UserSubmission\",\"tdc\":\"1\",\"suid\":\"john.doe@example.org\",\"ut\":\"Regular\",\"ssic\":\"0\",\"tsd\":\"REDACTED\",\"sip\":\"1.2.3.4\",\"srt\":\"0\",\"trc\":\"john.doe@example.org\",\"ms\":\"REDACTED\",\"sid\":\"be2ee3c6-2b3c-42ae-aefe-69f185114418\",\"aii\":\"be2ee3c6-2b3c-42ae-aefe-69f185114418\",\"md\":\"2024-04-04T07:50:14.0000000Z\",\"etps\":\"KesMailId:1111111111111111;FingerprintData:AAAAAAAA.BBBBBBBB.CCCCCCCF.72AC895E.200F2;SubmissionCategory:Email;RescanVerdict:NotSpam;SubmissionSource:Microsoft;SubmissionId:be2ee3c6-2b3c-42ae-aefe-69f185114418;OriginalVerdict:Allow\",\"lon\":\"UserSubmission\"}",
"EntityType": "User",
"Name": "Email reported by user as junk",
"PolicyId": "ANONYMIZED",
"Severity": "Low",
"Source": "Office 365 Security & Compliance",
"Status": "Active"
}
{
"CreationTime": "2024-04-16T08:01:42",
"Id": "d7cab54f-77b1-4ad5-8f2d-b4bba61e4e93",
"Operation": "AlertEntityGenerated",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "jdoe@example.org",
"UserId": "SecurityComplianceAlerts",
"AlertEntityId": "jdoe@example.org",
"AlertId": "a3ce0859-c92c-4f57-b50b-a63dad75ec4a",
"AlertLinks": [],
"AlertType": "System",
"Category": "ThreatManagement",
"Comments": "New alert",
"Data": "",
"EntityType": "User",
"Name": "Email reported by user as malware or phish",
"PolicyId": "88d533c5-bad6-4cfb-9245-1776726b55d7",
"Severity": "Low",
"Source": "Office 365 Security & Compliance",
"Status": "Investigating"
}
{
"CreationTime": "2024-10-24T09:10:38",
"Id": "9b1762d6-2667-4c2d-ad8f-5faa9b9dbad8",
"Operation": "AlertEntityGenerated",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "32c70dd6-ce69-434d-b52a-0d876696fd8d-9402318098831178296-1",
"UserId": "SecurityComplianceAlerts",
"AlertEntityId": "32c70dd6-ce69-434d-b52a-0d876696fd8d-9402318098831178296-1",
"AlertId": "6c88ef80-67f0-4a32-b1c9-4696ba48a3e4",
"AlertLinks": [
{
"AlertLinkHref": ""
}
],
"AlertType": "System",
"Category": "ThreatManagement",
"Comments": "New alert",
"Data": "{\"etype\":\"MalwareFamily\",\"at\":\"2024-10-24T09:07:19.0000000Z\",\"md\":\"2024-10-24T07:08:32.0000000Z\",\"sip\":null,\"ms\":\"REDACTED\",\"imsgid\":\"<AFIA3GCDITNgUgIKlOF5n5oH.1.1729763630549.mail.evil@example.com>\",\"ttdt\":\"2024-10-24T09:07:19.0000000Z\",\"ttr\":\"Success_MessageQuarantined\",\"dm\":\"UrlReputation\",\"eid\":\"32c70dd6-ce69-434d-b52a-0d876696fd8d-9402318098831178296-1\",\"aii\":\"32c70dd6-ce69-434d-b52a-0d876696fd8d\",\"thn\":\"Phish, Malicious\",\"ts\":\"2024-10-24T09:06:19.0000000Z\",\"te\":\"2024-10-24T09:08:19.0000000Z\",\"fvs\":\"Filters\",\"tpt\":\"HostedContentFilterPolicy\",\"tpid\":\"f0749efa-70b1-4420-94f7-9527b4f7f677\",\"tid\":\"3995fc59-1c0e-4812-b0f1-5308a209ef5e\",\"tht\":\"Phish, Malicious\",\"trc\":\"user1@example.com\",\"tsd\":\"evil@example.com\",\"zu\":\"clickonthis.example.com/api/phishing\",\"pud\":\"clickonthis.example.com/api/phishing\",\"tdc\":\"1\",\"cpid\":null,\"lon\":\"Protection\"}",
"EntityType": "MalwareFamily",
"Name": "Email messages containing malicious URL removed after delivery\u200b",
"PolicyId": "55087523-49bd-4bbd-b269-cda496a06d05",
"Severity": "Informational",
"Source": "Office 365 Security & Compliance",
"Status": "Active"
}
{
"CreationTime": "2025-01-31T23:11:21",
"Id": "3af6fbb3-040e-4ecc-4e18-08dd424c935a",
"Operation": "AlertEntityGenerated",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "test@example.com",
"UserId": "SecurityComplianceAlerts",
"AlertEntityId": "BIURO",
"AlertId": "b69ac1d6-7546-4f1b-a15f-fca0b5a7d005",
"AlertLinks": [
{
"AlertLinkHref": ""
}
],
"AlertType": "System",
"Category": "ThreatManagement",
"Comments": "New alert",
"Data": "{\"etype\":\"User\",\"eid\":\"test@example.com\",\"tid\":\"abcdef123-ecef-4cb1-a848-794d17916b7b\",\"ts\":\"2025-01-31T23:09:52.0000000Z\",\"te\":\"2025-01-31T23:09:52.0000000Z\",\"op\":\"CompromisedAccount\",\"tdc\":\"1\",\"suid\":\"john.doe@example.com\",\"ut\":\"System\",\"ssic\":\"0\",\"lon\":\"CompromisedAccount\"}",
"EntityType": "User",
"Name": "User restricted from sending email",
"PolicyId": "5bd8e1ef-44f4-4a67-b40f-48fd576ec779",
"Severity": "High",
"Source": "Office 365 Security & Compliance",
"Status": "Active"
}
{
"CreationTime": "2024-10-07T20:29:25",
"Id": "33c6081c-a402-49a3-828e-8e6df08c5e90",
"Operation": "AlertEntityGenerated",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "https://example.com/",
"UserId": "SecurityComplianceAlerts",
"AlertEntityId": "https://example.com/",
"AlertId": "657fb16a-ee7f-4939-a218-33ba3c72805e",
"AlertLinks": [
{
"AlertLinkHref": ""
}
],
"AlertType": "System",
"Category": "ThreatManagement",
"Comments": "New alert",
"Data": "{\"etype\":\"MaliciousUrl\",\"aii\":\"d6c7276b-3a65-43c7-9e25-525f7e289543\",\"eid\":\"https://test-d7a3.evil.net/?param=SGVsbG8gV29ybGQh\",\"curlh\":\"12815939189066485645\",\"tid\":\"b76bf78d-7696-4b17-bbda-e9995c266879\",\"ts\":\"2024-10-07T20:07:11.0000000Z\",\"te\":\"2024-10-07T20:07:11.0000000Z\",\"trc\":\"user1@example.org\",\"tdc\":\"1\",\"at\":\"2024-10-07T20:07:11.0000000Z\",\"dm\":\"MDO Safe Links\",\"ot\":\"Allowed\",\"od\":\"User clicked on a URL which was identified as potentially malicious at a later time.\",\"md\":\"2024-10-07T20:29:25.5945545Z\",\"lon\":\"MaliciousUrlClick\"}",
"EntityType": "MaliciousUrl",
"Name": "A potentially malicious URL click was detected",
"PolicyId": "471d921d-e417-41c4-be33-ad67040f3ece",
"Severity": "High",
"Source": "Office 365 Security & Compliance",
"Status": "Active"
}
{
"AppAccessContext": {
"AADSessionId": "ANONYMIZED",
"CorrelationId": "ANONYMIZED",
"UniqueTokenId": "ANONYMIZED"
},
"CreationTime": "2023-12-13T09:43:17",
"Id": "ANONYMIZED",
"Operation": "AccessRequestCreated",
"OrganizationId": "ANONYMIZED",
"RecordType": 14,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "SharePoint",
"ClientIP": "0.0.0.0",
"UserId": "user1",
"AuthenticationType": "FormsCookieAuth",
"BrowserName": "Chrome",
"BrowserVersion": "120.0.0.0",
"CorrelationId": "ANONYMIZED",
"EventSource": "SharePoint",
"IsManagedDevice": false,
"ItemType": "File",
"ListId": "xxxxx",
"ListItemUniqueId": "xxxxx",
"Platform": "WinDesktop",
"Site": "xxxxxxxxx",
"UserAgent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36",
"WebId": "xxxxxxxxx",
"DeviceDisplayName": "xxxxxxxxx",
"EventData": "<SharingLevel>Lecture</SharingLevel><ExpirationDate>12/03/2024 09:43:15</ExpirationDate>",
"SourceFileExtension": "xlsx",
"TargetUserOrGroupType": "Member",
"TargetUserOrGroupName": "user1",
"SiteUrl": "https://maindomain.com/subdomain/endvalue",
"SourceRelativeUrl": "Documents partages/xxxxx.xlsx",
"SourceFileName": "https://example.com/",
"ObjectId": "https://example.com/"
}
{
"AppAccessContext": {
"AADSessionId": "ANONYMIZED",
"ClientAppId": "ANONYMIZED",
"ClientAppName": "Microsoft Teams",
"CorrelationId": "ANONYMIZED",
"UniqueTokenId": "xxxxxx"
},
"CreationTime": "2024-10-29T07:41:53",
"Id": "ANONYMIZED",
"Operation": "AddedToSecureLink",
"OrganizationId": "ANONYMIZED",
"RecordType": 14,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "OneDrive",
"ClientIP": "1.2.3.4",
"UserId": "user1",
"ApplicationId": "ANONYMIZED",
"AuthenticationType": "OAuth",
"BrowserName": "Edge",
"BrowserVersion": "130.0.0.0",
"CorrelationId": "ANONYMIZED",
"EventSource": "SharePoint",
"GeoLocation": "EUR",
"IsManagedDevice": true,
"ItemType": "File",
"ListId": "ANONYMIZED",
"ListItemUniqueId": "ANONYMIZED",
"Platform": "WinDesktop",
"Site": "ANONYMIZED",
"UserAgent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36 Edg/130.0.0.0 Teams/24257.205.3165.2029/49",
"WebId": "ANONYMIZED",
"DeviceDisplayName": "ANONYMIZED",
"EventData": "<Type>Edit</Type><MembersCanShareApplied>False</MembersCanShareApplied>",
"SourceFileExtension": "pdf",
"TargetUserOrGroupType": "Member",
"UniqueSharingId": "ANONYMIZED",
"TargetUserOrGroupName": "user1",
"SiteUrl": "https://compagny-my.sharepoint.com/personal/usrename",
"SourceRelativeUrl": "Documents/filename.pdf",
"SourceFileName": "filename.pdf",
"ApplicationDisplayName": "Microsoft Teams",
"ObjectId": "https://example.com/",
"AssociatedAdminUnits": [
"ANONYMIZED"
]
}
{
"CreationTime": "2022-04-05T19:51:35",
"Id": "1324e3d2-f29c-5c15-9f44-1ca64e42250f",
"Operation": "MessageCreatedHasLink",
"OrganizationId": "ANONYMIZED",
"RecordType": 25,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "MicrosoftTeams",
"ClientIP": "::ffff:1.2.3.4",
"UserId": "user1",
"ChatThreadId": "19:11dbae04-5d5d-4bc7-9766-16793ed91233_4fdb1e07-a7e9-475c-a5e2-8d042a6c8102@unq.gbl.spaces",
"CommunicationType": "OneOnOne",
"ExtraProperties": [
{
"Key": "TimeZone",
"Value": "Europe/Paris"
},
{
"Key": "OsName",
"Value": "windows"
},
{
"Key": "OsVersion",
"Value": "10"
},
{
"Key": "Country",
"Value": "fr"
},
{
"Key": "ClientName",
"Value": "skypeteams"
},
{
"Key": "ClientVersion",
"Value": "27/1.0.0.2022031814"
},
{
"Key": "ClientUtcOffsetSeconds",
"Value": "7200"
}
],
"MessageId": "1649188295480",
"MessageVersion": "1649188295480",
"ItemName": "19:11dbae04-5d5d-4bc7-9766-16793ed91233_4fdb1e07-a7e9-475c-a5e2-8d042a6c8102@unq.gbl.spaces",
"MessageURLs": [
"https://example.com/"
],
"Members": [
{
"UPN": "admin@example.org",
"Role": 1
},
{
"UPN": "user1@example.org",
"Role": 0
}
]
}
{
"AppAccessContext": {
"IssuedAtTime": "2024-06-10T06:51:28",
"UniqueTokenId": "mYyWp_-UrEa4Z_pZM7FlAA"
},
"CreationTime": "2024-06-10T11:50:24",
"Id": "4e3612b5-9cf5-4c6d-8213-2ba12af15334",
"Operation": "ChatCreated",
"OrganizationId": "ANONYMIZED",
"RecordType": 25,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "MicrosoftTeams",
"ClientIP": "192.0.2.1",
"UserId": "user1",
"ChatThreadId": "19:2546ebff-72fd-4fda-b537-bc31bf5e1d4c_ba359007-06c1-497f-bc4a-41ea45df4cbd@unq.gbl.spaces",
"CommunicationType": "OneOnOne",
"ExtraProperties": [
{
"Key": "TimeZone",
"Value": "Europe/Paris"
},
{
"Key": "OsName",
"Value": "windows"
},
{
"Key": "OsVersion",
"Value": "10"
},
{
"Key": "Country",
"Value": "fr"
},
{
"Key": "ClientName",
"Value": "skypeteams"
},
{
"Key": "ClientVersion",
"Value": "27/1.0.0.2024052206"
},
{
"Key": "ClientUtcOffsetSeconds",
"Value": "7200"
}
],
"Members": [
{
"OrganizationId": "6d869a66-371f-4b76-a1f6-3c115469a99d",
"DisplayName": "John Doe",
"UPN": "john.doe@example.org"
},
{
"OrganizationId": "6db03b45-27a2-4662-9121-fa5773a8e043",
"DisplayName": "Jane Doe",
"UPN": "jane.doe@example.com"
}
],
"ParticipantInfo": {
"HasForeignTenantUsers": true,
"HasGuestUsers": false,
"HasOtherGuestUsers": false,
"HasUnauthenticatedUsers": false,
"ParticipatingDomains": [
"example.org",
"example.com"
],
"ParticipatingSIPDomains": [
{
"DomainName": "example.org",
"TenantId": "6d869a66-371f-4b76-a1f6-3c115469a99d"
},
{
"DomainName": "example.com",
"TenantId": "6db03b45-27a2-4662-9121-fa5773a8e043"
}
],
"ParticipatingTenantIds": [
"6d869a66-371f-4b76-a1f6-3c115469a99d",
"6db03b45-27a2-4662-9121-fa5773a8e043"
]
},
"ResourceTenantId": "6db03b45-27a2-4662-9121-fa5773a8e043",
"ItemName": "19:2546ebff-72fd-4fda-b537-bc31bf5e1d4c_ba359007-06c1-497f-bc4a-41ea45df4cbd@unq.gbl.spaces"
}
{
"CreationTime": "2024-07-12T08:27:46",
"Id": "5964f7bd-8775-4dbe-84a8-37573510558c",
"Operation": "ChatCreated",
"OrganizationId": "ANONYMIZED",
"RecordType": 25,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "MicrosoftTeams",
"ClientIP": "1.2.3.4",
"UserId": "user1",
"ChatThreadId": "19:9ac303ea-1bf3-442c-a216-a517de868921_413e1939-c450-4d63-8226-b02a542e6a9a@unq.gbl.spaces",
"CommunicationType": "OneOnOne",
"ExtraProperties": [
{
"Key": "TimeZone",
"Value": "Europe/Berlin"
},
{
"Key": "OsName",
"Value": "windows"
},
{
"Key": "OsVersion",
"Value": "NT 10.0"
},
{
"Key": "Country",
"Value": "de"
},
{
"Key": "ClientName",
"Value": "skypeteams"
},
{
"Key": "ClientVersion",
"Value": "49/24061318408"
},
{
"Key": "ClientUtcOffsetSeconds",
"Value": "7200"
}
],
"Members": [
{
"OrganizationId": "ANONYMIZED",
"DisplayName": "John Doe",
"UPN": "user1"
},
{
"OrganizationId": "f35fe983-e797-44ce-bd0b-cf4da93a8043",
"DisplayName": "Jane Doe",
"UPN": "jane.doe@example2.com"
}
],
"ParticipantInfo": {
"HasForeignTenantUsers": true,
"HasGuestUsers": false,
"HasOtherGuestUsers": false,
"HasUnauthenticatedUsers": false,
"ParticipatingDomains": [
"example1.com",
"example2.com"
],
"ParticipatingSIPDomains": [
{
"DomainName": "example1.com",
"TenantId": "ANONYMIZED"
},
{
"DomainName": "example2.com",
"TenantId": "f35fe983-e797-44ce-bd0b-cf4da93a8043"
}
],
"ParticipatingTenantIds": [
"f35fe983-e797-44ce-bd0b-cf4da93a8043",
"ANONYMIZED"
]
},
"ResourceTenantId": "ANONYMIZED",
"ItemName": "19:9ac303ea-1bf3-442c-a216-a517de868921_413e1939-c450-4d63-8226-b02a542e6a9a@unq.gbl.spaces"
}
{
"CreationTime": "2024-07-12T08:27:37",
"Id": "db1cd437-5417-4cd3-ae6b-19a980f9bcfc",
"Operation": "ChatCreated",
"OrganizationId": "ANONYMIZED",
"RecordType": 25,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "MicrosoftTeams",
"ClientIP": "1.2.3.4",
"UserId": "user1",
"ChatThreadId": "19:d473ae3c-906c-4a72-8b3f-18e6c9bfdcd7_4daf1829-8823-454f-b4e0-1cd22342d5f3@unq.gbl.spaces",
"CommunicationType": "OneOnOne",
"ExtraProperties": [
{
"Key": "TimeZone",
"Value": "Europe/Berlin"
},
{
"Key": "OsName",
"Value": "windows"
},
{
"Key": "OsVersion",
"Value": "NT 10.0"
},
{
"Key": "Country",
"Value": "de"
},
{
"Key": "ClientName",
"Value": "skypeteams"
},
{
"Key": "ClientVersion",
"Value": "49/24061318408"
},
{
"Key": "ClientUtcOffsetSeconds",
"Value": "7200"
}
],
"Members": [
{
"OrganizationId": "ANONYMIZED",
"DisplayName": "John Doe",
"UPN": "user1"
},
{
"OrganizationId": "1d36ca61-5509-4ac7-983d-91dfdeb5f492",
"DisplayName": "Jane Doe",
"UPN": "jane.doe@example2.com"
}
],
"ParticipantInfo": {
"HasForeignTenantUsers": true,
"HasGuestUsers": false,
"HasOtherGuestUsers": false,
"HasUnauthenticatedUsers": false,
"ParticipatingDomains": [
"example1.com",
"example2.com"
],
"ParticipatingSIPDomains": [
{
"DomainName": "example1.com",
"TenantId": "ANONYMIZED"
},
{
"DomainName": "example2.com",
"TenantId": "1d36ca61-5509-4ac7-983d-91dfdeb5f492"
}
],
"ParticipatingTenantIds": [
"1d36ca61-5509-4ac7-983d-91dfdeb5f492",
"ANONYMIZED"
]
},
"ResourceTenantId": "ANONYMIZED",
"ItemName": "19:d473ae3c-906c-4a72-8b3f-18e6c9bfdcd7_4daf1829-8823-454f-b4e0-1cd22342d5f3@unq.gbl.spaces"
}
{
"CreationTime": "2024-06-10T12:14:57",
"Id": "f47118c3-edcf-43a9-b505-c7c904231ac2",
"Operation": "ChatCreated",
"OrganizationId": "ANONYMIZED",
"RecordType": 25,
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "MicrosoftTeams",
"ClientIP": "192.0.2.1",
"UserId": "user1",
"ChatThreadId": "19:0f738a46-74e0-45cf-a5e7-ff31eb2d9cdb_e574a199-c965-4fe2-8c02-0a98a1e8f597@unq.gbl.spaces",
"CommunicationType": "OneOnOne",
"ExtraProperties": [
{
"Key": "TimeZone",
"Value": "Europe/Paris"
},
{
"Key": "OsName",
"Value": "windows"
},
{
"Key": "OsVersion",
"Value": "NT 10.0"
},
{
"Key": "Country",
"Value": "fr"
},
{
"Key": "ClientName",
"Value": "skypeteams"
},
{
"Key": "ClientVersion",
"Value": "49/24051622207"
},
{
"Key": "ClientUtcOffsetSeconds",
"Value": "7200"
}
],
"Members": [
{
"OrganizationId": "ANONYMIZED",
"DisplayName": "John Doe",
"UPN": "user1"
},
{
"OrganizationId": "ANONYMIZED",
"DisplayName": "Jane Doe",
"UPN": "jane.doe@example.org"
}
],
"ParticipantInfo": {
"HasForeignTenantUsers": false,
"HasGuestUsers": true,
"HasOtherGuestUsers": false,
"HasUnauthenticatedUsers": false,
"ParticipatingDomains": [],
"ParticipatingSIPDomains": [],
"ParticipatingTenantIds": [
"ANONYMIZED"
]
},
"ResourceTenantId": "ANONYMIZED",
"ItemName": "19:0f738a46-74e0-45cf-a5e7-ff31eb2d9cdb_e574a199-c965-4fe2-8c02-0a98a1e8f597@unq.gbl.spaces"
}
{
"CreationTime": "2025-01-02T08:01:41",
"Id": "f96dedc3-0e53-4444-bbbb-ef0000000000000",
"Operation": "UserLoggedIn",
"OrganizationId": "ANONYMIZED",
"RecordType": 15,
"ResultStatus": "Success",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ClientIP": "192.0.2.1",
"ObjectId": "0000000a-0000-0000-c000-000000000000",
"UserId": "user1",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "ResultStatusDetail",
"Value": "Redirect"
},
{
"Name": "UserAgent",
"Value": "Mozilla/5.0 (Linux; Android 14; FFF-N49 Build/Test-N49; wv) AppleWebKit/537.36 (KHTML, like Gecko) Version/4.0 Chrome/131.0.6778.200 Mobile Safari/537.36 PKeyAuth/1.0"
},
{
"Name": "RequestType",
"Value": "OrgIdWsFederation:federation"
}
],
"ModifiedProperties": [],
"Actor": [
{
"ID": "37fc2dfc-cccc-4888-8fff-00000000000000003",
"Type": 0
},
{
"ID": "user1",
"Type": 5
}
],
"ActorContextId": "3e49b082-6666-4444-aaaa-8777777777d2",
"ActorIpAddress": "2000:4444:1111:5555:3333:1111:bbbb:555",
"InterSystemsId": "a282e7bb-2eea-4773-b296-00000000000000",
"IntraSystemId": "f96dedc3-0e53-4724-ba85-000000000000800",
"SupportTicketId": "",
"Target": [
{
"ID": "0000000a-0000-0000-c000-000000000000",
"Type": 0
}
],
"TargetContextId": "ANONYMIZED",
"ApplicationId": "9ba1a5c7-f17a-4de9-a1f1-6178c8d51223",
"DeviceProperties": [
{
"Name": "OS",
"Value": "Android"
},
{
"Name": "BrowserType",
"Value": "AndroidWebViewLollipopAndAbove"
},
{
"Name": "SessionId",
"Value": "1584fd84-0508-419e-b678-ac60c80000000000"
}
],
"ErrorNumber": "0"
}
{
"CreationTime": "2025-10-15T06:50:14Z",
"Id": "aaaaaaaa-bbbb-4ccc-8ddd-eeeeeeee0001",
"Operation": "AlertTriggered",
"OrganizationId": "ANONYMIZED",
"RecordType": 40,
"ResultStatus": "Succeeded",
"UserKey": "SecurityComplianceAlerts",
"UserType": 4,
"Version": 1,
"Workload": "SecurityComplianceCenter",
"ObjectId": "aaaaaaaa-bbbb-4ccc-8ddd-eeeeeeee0002",
"UserId": "SecurityComplianceAlerts",
"AlertId": "aaaaaaaa-bbbb-4ccc-8ddd-eeeeeeee0002",
"AlertLinks": [
{
"AlertLinkHref": "https://example.security/alert/0002"
}
],
"AlertType": "Custom",
"Category": "DataLossPrevention",
"Comments": "New alert",
"Data": "{\"ts\":\"2025-10-15 06:50:08Z\",\"te\":\"2025-10-15 06:50:08Z\",\"an\":\"Quarantine File\",\"ad\":\"File policy 'Quarantine File Policy' was matched by 'document.xlsx'\",\"f3u\":\"user1@example.com\",\"alk\":\"https://security.example.net/alerts/0002\",\"plk\":\"https://example.security/policy/123456\",\"mat\":\"MCAS_ALERT_FILE_MATCH\"}",
"Name": "Quarantine File",
"PolicyId": "22222222-3333-4444-8555-666666666666",
"Severity": "Medium",
"Source": "Cloud App Security",
"Status": "Active"
}
{
"CreationTime": "2023-08-30T20:49:04",
"Id": "f872f447-2417-492a-d462-08dba99a7777",
"Operation": "AtpDetection",
"OrganizationId": "ANONYMIZED",
"RecordType": 47,
"UserKey": "user1",
"UserType": 4,
"Version": 1,
"Workload": "ThreatIntelligence",
"UserId": "user1",
"DetectionDate": "2023-08-30T20:48:08",
"DetectionMethod": "AntiMalware",
"EventDeepLink": "https://example.com/",
"FileData": {
"DocumentId": "f773238b-ef02-41f4-94db-bbd7d5167777",
"FileName": "file.exe",
"FilePath": "https://example.com/",
"FileSize": "9670017",
"FileVerdict": 1,
"MalwareFamily": "Malicious Payload",
"SHA256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
}
}
{
"CreationTime": "2019-11-18T13:40:24",
"Id": "038ae875-ffd8-45e4-9dcf-6e385cfad349",
"Operation": "Update group.",
"OrganizationId": "ANONYMIZED",
"RecordType": 8,
"ResultStatus": "Success",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ClientIP": "<null>",
"ObjectId": "Not Available",
"UserId": "user1",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "resultType",
"Value": "Success"
}
]
}
{
"CreationTime": "2019-12-09T14:18:19",
"Id": "359154c4-72c5-4ba0-bbf9-7eb1dff88af7",
"Operation": "Update user.",
"OrganizationId": "ANONYMIZED",
"RecordType": 8,
"ResultStatus": "Success",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ClientIP": "<null>",
"ObjectId": "bob.smith@acme.org",
"UserId": "user1",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "resultType",
"Value": "Success"
},
{
"Name": "auditEventCategory",
"Value": "UserManagement"
},
{
"Name": "nCloud",
"Value": "<null>"
}
]
}
{
"CreationTime": "2021-03-05T14:43:17",
"Id": "21a107c2-2071-4ce3-8330-cf82f3caa79f",
"Operation": "Update user.",
"OrganizationId": "ANONYMIZED",
"RecordType": 8,
"ResultStatus": "Success",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ClientIP": "",
"ObjectId": "aaaa.bbbb@example.org",
"UserId": "user1",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "additionalDetails",
"Value": "{\"UserType\":\"Member\"}"
},
{
"Name": "extendedAuditEventCategory",
"Value": "User"
}
],
"ModifiedProperties": [
{
"Name": "LastDirSyncTime",
"NewValue": "[\r\n \"2021-03-05T14:43:17Z\"\r\n]",
"OldValue": "[\r\n \"2021-03-03T12:30:50Z\"\r\n]"
},
{
"Name": "Included Updated Properties",
"NewValue": "LastDirSyncTime",
"OldValue": ""
},
{
"Name": "Action Client Name",
"NewValue": "DirectorySync",
"OldValue": ""
},
{
"Name": "TargetId.UserType",
"NewValue": "Member",
"OldValue": ""
}
],
"Actor": [
{
"ID": "user1",
"Type": 5
},
{
"ID": "10030000A96EA230",
"Type": 3
},
{
"ID": "User_c96cf894-cca6-438b-b6f2-c2744c1680f5",
"Type": 2
},
{
"ID": "c96cf894-cca6-438b-b6f2-c2744c1680f5",
"Type": 2
},
{
"ID": "User",
"Type": 2
}
],
"ActorContextId": "ANONYMIZED",
"ActorIpAddress": "",
"InterSystemsId": "92d46438-1e67-43e3-91ca-039ff39d7217",
"IntraSystemId": "bd8cc421-efe8-4a44-b61d-44670fc6f56e",
"SupportTicketId": "",
"Target": [
{
"ID": "User_de76d2a9-d8bf-47d4-8f74-2ba2b560f55e",
"Type": 2
},
{
"ID": "de76d2a9-d8bf-47d4-8f74-2ba2b560f55e",
"Type": 2
},
{
"ID": "User",
"Type": 2
},
{
"ID": "aaaa.bbbb@example.org",
"Type": 5
},
{
"ID": "1003200119762B26",
"Type": 3
}
],
"TargetContextId": "ANONYMIZED"
}
{
"CreationTime": "2019-11-18T10:15:52",
"Id": "405f795f-8bff-45d2-98c9-ef675d7d2db6",
"Operation": "UserLoggedIn",
"OrganizationId": "ANONYMIZED",
"RecordType": 15,
"ResultStatus": "Succeeded",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ClientIP": "1.2.3.4:8085",
"ObjectId": "5f09333a-842c-47da-a157-57da27fcbca5",
"UserId": "user1",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "UserAgent",
"Value": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/64.0.3282.140 Safari/537.36 Edge/18.17763"
},
{
"Name": "UserAuthenticationMethod",
"Value": "1"
},
{
"Name": "RequestType",
"Value": "OAuth2:Authorize"
},
{
"Name": "ResultStatusDetail",
"Value": "Redirect"
},
{
"Name": "KeepMeSignedIn",
"Value": "True"
}
],
"ModifiedProperties": [],
"Actor": [
{
"ID": "3d0e7ff9-261e-440f-a2f8-9e1ec4072f3e",
"Type": 0
},
{
"ID": "user1",
"Type": 5
},
{
"ID": "10037FFEA0A22006",
"Type": 3
}
],
"ActorContextId": "ANONYMIZED",
"ActorIpAddress": "1.2.3.4",
"InterSystemsId": "794c9504-66fe-441c-831a-5fc2badfcdc8",
"IntraSystemId": "99f54f6a-ddfe-4916-b89b-edd9fcac4500",
"SupportTicketId": "",
"Target": [
{
"ID": "5f09333a-842c-47da-a157-57da27fcbca5",
"Type": 0
}
],
"TargetContextId": "ANONYMIZED",
"ApplicationId": "89bee1f7-5e6e-4d8a-9f3d-ecd601259da7"
}
{
"CreationTime": "2023-05-02T18:02:13",
"Id": "5f24aa82-f874-44d1-b6df-857cd9e1decf",
"Operation": "UserLoggedIn",
"OrganizationId": "ANONYMIZED",
"RecordType": 15,
"ResultStatus": "Success",
"UserKey": "1111111111111111",
"UserType": 0,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ClientIP": "1.2.3.4",
"ObjectId": "77f6d9ce-da8f-46bf-a651-4bec3c189770",
"UserId": "user1",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "ResultStatusDetail",
"Value": "Redirect"
},
{
"Name": "UserAgent",
"Value": "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:102.0) Gecko/20100101 Firefox/102.0"
},
{
"Name": "RequestType",
"Value": "OAuth2:Authorize"
}
],
"ModifiedProperties": [],
"Actor": [
{
"ID": "77f6d9ce-da8f-46bf-a651-4bec3c189770",
"Type": 0
},
{
"ID": "user1",
"Type": 5
}
],
"ActorContextId": "77f6d9ce-da8f-46bf-a651-4bec3c189770",
"ActorIpAddress": "1.2.3.4",
"InterSystemsId": "77f6d9ce-da8f-46bf-a651-4bec3c189770",
"IntraSystemId": "77f6d9ce-da8f-46bf-a651-4bec3c189770",
"SupportTicketId": "",
"Target": [
{
"ID": "00000003-0000-0ff1-ce00-000000000000",
"Type": 0
}
],
"TargetContextId": "77f6d9ce-da8f-46bf-a651-4bec3c189770",
"ApplicationId": "77f6d9ce-da8f-46bf-a651-4bec3c189770",
"DeviceProperties": [
{
"Name": "Id",
"Value": "77f6d9ce-da8f-46bf-a651-4bec3c189770"
},
{
"Name": "DisplayName",
"Value": "example.com"
},
{
"Name": "OS",
"Value": "Windows 10"
},
{
"Name": "BrowserType",
"Value": "Firefox"
},
{
"Name": "IsCompliant",
"Value": "True"
},
{
"Name": "IsCompliantAndManaged",
"Value": "True"
},
{
"Name": "TrustType",
"Value": "2"
},
{
"Name": "SessionId",
"Value": "77f6d9ce-da8f-46bf-a651-4bec3c189770"
}
],
"ErrorNumber": "0"
}
{
"CreationTime": "2022-10-14T13:48:03",
"Id": "4af0b443-42dd-4dc6-9bd1-751a55441000",
"Operation": "UserLoginFailed",
"OrganizationId": "ANONYMIZED",
"RecordType": 15,
"ResultStatus": "Success",
"UserKey": "user1",
"UserType": 0,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ClientIP": "192.0.2.1",
"ObjectId": "00000003-0000-0ff1-ce00-000000000000",
"UserId": "user1",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "ResultStatusDetail",
"Value": "Success"
},
{
"Name": "UserAgent",
"Value": "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:105.0) Gecko/20100101 Firefox/105.0"
},
{
"Name": "UserAuthenticationMethod",
"Value": "1"
},
{
"Name": "RequestType",
"Value": "SAS:EndAuth"
}
],
"ModifiedProperties": [],
"Actor": [
{
"ID": "user1",
"Type": 0
},
{
"ID": "user1",
"Type": 5
}
],
"ActorContextId": "ANONYMIZED",
"ActorIpAddress": "192.0.2.1",
"InterSystemsId": "d48e6ea0-40c1-5000-5eba-0ee33d13b1ca",
"IntraSystemId": "4af0b443-42dd-4dc6-9bd1-751a55441000",
"SupportTicketId": "",
"Target": [
{
"ID": "00000003-0000-0ff1-ce00-000000000000",
"Type": 0
}
],
"TargetContextId": "ANONYMIZED",
"ApplicationId": "00000003-0000-0ff1-ce00-000000000000",
"DeviceProperties": [
{
"Name": "OS",
"Value": "Windows 10"
},
{
"Name": "BrowserType",
"Value": "Firefox"
},
{
"Name": "IsCompliantAndManaged",
"Value": "False"
},
{
"Name": "SessionId",
"Value": "b3a9b2b4-57c9-406b-9a2d-106b7f612248"
}
],
"ErrorNumber": "500121",
"LogonError": "AuthenticationFailedSasError"
}
{
"CreationTime": "2026-03-12T11:05:51",
"Id": "11111111-1111-1111-1111-111111111111",
"Operation": "UserLoginFailed",
"OrganizationId": "22222222-2222-2222-2222-222222222222",
"RecordType": 15,
"ResultStatus": "Success",
"UserKey": "00000000-0000-0000-0000-000000000000",
"UserType": 6,
"Version": 1,
"Workload": "AzureActiveDirectory",
"ClientIP": "",
"ObjectId": "44444444-4444-4444-4444-444444444444",
"UserId": "55555555-5555-5555-5555-555555555555||66666666-6666-6666-6666-666666666666",
"AzureActiveDirectoryEventType": 1,
"ExtendedProperties": [
{
"Name": "ResultStatusDetail",
"Value": "Success"
},
{
"Name": "UserAgent",
"Value": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/145.0.0.0 Safari/537.36"
},
{
"Name": "RequestType",
"Value": "PrivacyConsent:guestconsentset"
}
],
"ModifiedProperties": [],
"Actor": [
{
"ID": "Unknown",
"Type": 2
}
],
"ActorContextId": "77777777-7777-7777-7777-777777777777",
"ActorIpAddress": "",
"InterSystemsId": "88888888-8888-8888-8888-888888888888",
"IntraSystemId": "11111111-1111-1111-1111-111111111111",
"SupportTicketId": "",
"Target": [
{
"ID": "44444444-4444-4444-4444-444444444444",
"Type": 0
}
],
"TargetContextId": "22222222-2222-2222-2222-222222222222",
"ApplicationId": "44444444-4444-4444-4444-444444444444",
"ErrorNumber": "500142"
}
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake Microsoft 365 / Office 365. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x Microsoft 365 / Office 365 on ATT&CK Navigator
ACLight Discovering Privileged Accounts
Detects use of ACLight tool. This tool aims to discover privileged accounts by scanning the network.
- Effort: advanced
Account Added To A Security Enabled Group
Detection in order to investigate who has added a specific Domain User in Domain Admins or Group Policy Creator Owners (Security event 4728)
- Effort: master
Account Removed From A Security Enabled Group
Detection in order to investigate who has removed a specific Domain User in Domain Admins or Group Policy Creator Owners (Security event 4729)
- Effort: master
Active Directory Data Export Using Csvde
Detects the use of Csvde, a command-line tool from Windows Server that can be used to export Active Directory data to CSV files. This export doesn't include password hashes, but can be used as a discovery tool to enumerate users, machines and group memberships.
- Effort: elementary
AdFind Usage
Detects the usage of the AdFind tool. AdFind.exe is a free tool that extracts information from Active Directory. Wizard Spider (Bazar, TrickBot, Ryuk), FIN6 and MAZE operators have used AdFind.exe to collect information about Active Directory organizational units and trust objects
- Effort: elementary
Adexplorer Usage
Detects the usage of Adexplorer, a legitimate tool from the Sysinternals suite that could be abused by attackers as it can saves snapshots of the Active Directory Database.
- Effort: advanced
Advanced IP Scanner
Detects the use of Advanced IP Scanner. Seems to be a popular tool for ransomware groups.
- Effort: master
Aspnet Compiler
Detects the starts of aspnet compiler.
- Effort: advanced
Bloodhound and Sharphound Tools Usage
Detects default process names and default command line parameters used by Bloodhound and Sharphound tools.
- Effort: intermediate
Burp Suite Tool Detected
Burp Suite is a cybersecurity tool. When used as a proxy service, its purpose is to intercept packets and modify them to send them to the server. Burp Collaborator is a network service that Burp Suite uses to help discover many kinds of vulnerabilities (vulnerabilities scanner).
- Effort: intermediate
CVE-2017-11882 Microsoft Office Equation Editor Vulnerability
Detects the exploitation of CVE-2017-11882 vulnerability. The Microsoft Office Equation Editor has no reason to do a network request or drop an executable file. This requires a sysmon configuration with file and network events.
- Effort: master
CVE-2020-0688 Microsoft Exchange Server Exploit
Detects the exploitation of CVE-2020-0688. The POC exploit a .NET serialization vulnerability in the Exchange Control Panel (ECP) web page. The vulnerability is due to Microsoft Exchange Server not randomizing the keys on a per-installation basis resulting in them using the same validationKey and decryptionKey values. With knowledge of these, values an attacker can craft a special viewstate to use an OS command to be executed by NT_AUTHORITY\SYSTEM using .NET deserialization. To exploit this vulnerability, an attacker needs to leverage the credentials of an account it had already compromised to authenticate to OWA.
- Effort: elementary
CVE-2020-17530 Apache Struts RCE
Detects the exploitation of the Apache Struts RCE vulnerability (CVE-2020-17530).
- Effort: intermediate
CVE-2021-20021 SonicWall Unauthenticated Administrator Access
Detects the exploitation of SonicWall Unauthenticated Admin Access.
- Effort: advanced
CVE-2021-20023 SonicWall Arbitrary File Read
Detects Arbitrary File Read, which can be used with other vulnerabilities as a mean to obtain outputs generated by attackers, or sensitive data.
- Effort: advanced
CVE-2021-22893 Pulse Connect Secure RCE Vulnerability
Detects potential exploitation of the authentication by-pass vulnerability that can allow an unauthenticated user to perform remote arbitrary file execution on the Pulse Connect Secure gateway. It is highly recommended to apply the Pulse Secure mitigations and seach for indicators of compromise on affected servers if you are in doubt over the integrity of your Pulse Connect Secure product.
- Effort: intermediate
Certificate Authority Modification
Installation of new certificate(s) in the Certificate Authority can be used to trick user when spoofing website or to add trusted destinations.
- Effort: master
Certify Or Certipy
Detects the use of certify and certipy which are two different tools used to enumerate and abuse Active Directory Certificate Services.
- Effort: advanced
Cobalt Strike Default Beacons Names
Detects the default names of Cobalt Strike beacons / payloads.
- Effort: intermediate
Computer Account Deleted
Detects computer account deletion.
- Effort: master
Covenant Default HTTP Beaconing
Detects potential Covenant communications through the user-agent and specific urls
- Effort: intermediate
Credential Dump Tools Related Files
Detects processes or file names related to credential dumping tools and the dropped files they generate by default.
- Effort: advanced
Cryptomining
Detection of domain names potentially related to cryptomining activities.
- Effort: master
DNS Query For Iplookup
Detects dns query of observables tagged as iplookup.
- Effort: master
Detect requests to Konni C2 servers
This rule detects requests to Konni C2 servers. These patterns come from an analysis done in 2022, September.
- Effort: elementary
Discord Suspicious Download
Discord is a messaging application. It allows users to create their own communities to share messages and attachments. Those attachments have little to no overview and can be downloaded by almost anyone, which has been abused by attackers to host malicious payloads.
- Effort: advanced
Discovery Commands Correlation
Detects some frequent discovery commands used by some ransomware operators.
- Effort: intermediate
Domain Trust Created Or Removed
A trust was created or removed to a domain. An attacker could perform that in order to do lateral movement easily between domains or shutdown the ability of two domains to communicate.
- Effort: advanced
Dynamic DNS Contacted
Detect communication with dynamic dns domain. This kind of domain is often used by attackers. This rule can trigger false positive in non-controlled environment because dynamic dns is not always malicious.
- Effort: master
Elevated Shell Launched By Browser
Detects when openwith.exe is launched with privileges followed by a browser launching an elevated shell. Related to the CVE-2024-38014.
- Effort: master
Enable Root Account With Dsenableroot
Detects when root is enabled. Attackers can use this as a mean of persistence since root is disabled by default.
- Effort: elementary
Entra ID Consent Attempt to Suspicious OAuth Application
Detects an attempt to authorize account access to an OAuth application commonly used in business email compromise (BEC) attacks. Investigate the source IP address: unusual countries, RDP hosts and VPN providers are likely indicators of malicious activity.
- Effort: elementary
Entra ID Password Compromised By Known Credential Testing Tool
Detects a sign-in that has a correlation ID known to be used by malicious credential testing scripts. Note that even if the sign-in was blocked by MFA (error 50074) or device authentication (error 50097), these verifications only occur after the correct password was submitted. The account's password must still be considered compromised, and be changed.
- Effort: elementary
Entra ID Password Compromised Via Seamless SSO Credential Testing
Detects a sign-in using the Entra ID Seamless SSO usernamemixed endpoint. This endpoint is rarely used legitimately, and often abused by credential testing tools. Note that even if the sign-in was blocked by MFA (error 50074) or device authentication (error 50097), these verifications only occur after the correct password was submitted. The account's password must still be considered compromised, and be changed.
- Effort: elementary
Entra ID Sign-In Via Known AiTM Phishing Kit (CEPHAS 2FA)
Detects a sign-in attempt with known characteristics of the adversary-in-the-middle phishing kit CEPHAS 2FA.
- Effort: elementary
Entra ID Sign-In Via Known AiTM Phishing Kit (Gabagool)
Detects a sign-in attempt with known characteristics of the adversary-in-the-middle phishing kit Gabagool. The filter_password_spraying exclusion corresponds to a password spraying tool which is already detected by the rule Entra ID Password Compromised By Known Credential Testing Tool.
- Effort: elementary
Entra ID Sign-In Via Known AiTM Phishing Kit (Greatness)
Detects a sign-in attempt with known characteristics of the adversary-in-the-middle phishing kit Greatness.
- Effort: elementary
Entra ID Sign-In Via Known AiTM Phishing Kit (HoneySecurity / HoneyStorm)
Detects a sign-in attempt with known characteristics of the adversary-in-the-middle phishing kit HoneySecurity / HoneyStorm.
- Effort: elementary
Entra ID Sign-In Via Known AiTM Phishing Kit (Mamba 2FA)
Detects a sign-in attempt with known characteristics of the adversary-in-the-middle phishing kit tracked by Sekoia.io as Mamba 2FA.
- Effort: elementary
Entra ID Sign-In Via Known AiTM Phishing Kit (Rockstar 2FA)
Detects a sign-in attempt with known characteristics of the adversary-in-the-middle phishing kit Rockstar 2FA.
- Effort: elementary
Entra ID Sign-In Via Known AiTM Phishing Kit (Sneaky 2FA)
Detects a sign-in attempt with an impossible device shift characteristic of the adversary-in-the-middle phishing kit Sneaky 2FA.
- Effort: elementary
Entra ID Sign-In Via Known AiTM Phishing Kit (Tycoon 2FA)
Detects a sign-in attempt with known characteristics of the adversary-in-the-middle phishing kit Tycoon 2FA.
- Effort: elementary
Exfiltration And Tunneling Tools Execution
Execution of well known tools for data exfiltration and tunneling
- Effort: advanced
Exfiltration Domain
Detects traffic toward a domain flagged as a possible exfiltration vector.
- Effort: master
HTA Infection Chains
Detect the creation of a ZIP file and an HTA file as it is often used in infection chains. Furthermore it also detects the use of suspicious processes launched by explorer.exe combined with the creation of an HTA file, since it is also often used in infection chains (LNK - HTA for instance).
- Effort: advanced
HTML Smuggling Suspicious Usage
Based on several samples from different botnets, this rule aims at detecting HTML infection chain by looking for HTML created files followed by suspicious files being executed.
- Effort: advanced
HackTools Suspicious Names
Quick-win rule to detect the default process names or file names of several HackTools.
- Effort: advanced
ISO LNK Infection Chain
Detection of an ISO (or any other similar archive file) downloaded file, followed by a child-process of explorer, which is characteristic of an infection using an ISO containing an LNK file. For events with host.name.
- Effort: master
Impacket Addcomputer
Detects suspicious computer account creation based on impacket default pattern
- Effort: intermediate
Kernel Module Alteration
Kernel module installation can be used to configure system settings to automatically execute a program during system boot or logon to maintain persistence or gain higher-level privileges on compromised systems. The prerequisites are to enable monitoring of the finit_module, init_module, delete_module syscalls using Auditbeat.
- Effort: advanced
Koadic MSHTML Command
Detects Koadic payload using MSHTML module
- Effort: intermediate
Microsoft 365 (Office 365) Anti-Phishing Policy Deletion
Detects when the anti-phishing policy is removed from Microsoft 365 (Office 365). By default, Microsoft 365 (Office 365) includes built-in features that help protect users from phishing attacks. This policy specifies the phishing protections to enable or disable, and the actions to apply options.
- Effort: master
Microsoft 365 (Office 365) Anti-Phishing Rule Deletion
Detects the deactivation of the anti-phishing rule from Microsoft 365 (Office 365). The anti-phishing rule specifies the priority and recipient filters (who the policy applies to) for an anti-phish policy.
- Effort: master
Microsoft 365 (Office 365) AtpDetection
Detects when an AtpDetection (Advanced Threat Protection) event from the Office365 ThreatIntelligence service is raised. AtpDetection is a service which secures emails, attachments, and files by scanning them for threats.
- Effort: intermediate
Microsoft 365 (Office 365) DLP Policy Removed
Detects when a DLP (Data Loss Prevention) policy is removed in Microsoft 365 (Office 365). DLP policies defines which resources can be shared and with whom, preventing sensitive information from being leaked.
- Effort: master
Microsoft 365 (Office 365) MCAS Detection Velocity
Detects when Microsoft Cloud App Security identifies two user activities (a single or multiple sessions) originating from geographically distant locations within a time period shorter than the time it would have taken the user to travel from the first location to the second. To use this feature, you must have an Microsoft 365 (Office 365) E5 license (https://docs.microsoft.com/en-us/defender-cloud-apps/get-started?culture=fr-fr&country=FR).
- Effort: master
Microsoft 365 (Office 365) MCAS Inbox Hiding
Detects when Microsoft Cloud App Security identifies that a suspicious inbox rule was set on a user’s inbox. This may indicate that the user account is compromised, and that the mailbox is being used to distribute spam and malware in your organization. To use this feature, you must have an Microsoft 365 (Office 365) E5 license (https://docs.microsoft.com/en-us/defender-cloud-apps/get-started?culture=fr-fr&country=FR).
- Effort: master
Microsoft 365 (Office 365) MCAS New Country
Detects when Microsoft Cloud App Security identifies a sign-in from a country where it has never connected. To use this feature, you must have an Microsoft 365 (Office 365) E5 license (https://docs.microsoft.com/en-us/defender-cloud-apps/get-started?culture=fr-fr&country=FR).
- Effort: master
Microsoft 365 (Office 365) MCAS Repeated Delete
Detects when Microsoft Cloud App Security identifies that a user has deleted an unusually large volume of files. To use this feature, you must have an Microsoft 365 (Office 365) E5 license (https://docs.microsoft.com/en-us/defender-cloud-apps/get-started?culture=fr-fr&country=FR).
- Effort: master
Microsoft 365 (Office 365) MCAS Repeated Failed Login
Detects when Microsoft Cloud App Security identifies a large number of failed login attempts which may indicate a brute-force attempt. To use this feature, you must have an Microsoft 365 (Office 365) E5 license (https://docs.microsoft.com/en-us/defender-cloud-apps/get-started?culture=fr-fr&country=FR).
- Effort: master
Microsoft 365 (Office 365) MCAS Risky IP
Detects when Microsoft Cloud App Security identifies sign-ins from a risky IP address, for example, using an anonymous browser or VPN. To use this feature, you must have an Microsoft 365 (Office 365) E5 license (https://docs.microsoft.com/en-us/defender-cloud-apps/get-started?culture=fr-fr&country=FR).
- Effort: master
Microsoft 365 (Office 365) MailBoxAuditBypassAssociation Option Implementation
Detects the implementation of a MailBoxAuditBypassAssociation option in Microsoft 365 (Office 365). This option is used when you configure a user or computer account to bypass mailbox audit logging, access or actions taken by the user or computer account to any mailbox isn't logged.
- Effort: master
Microsoft 365 (Office 365) Malware Filter Policy Removed
Detects when a malware policy has been deleted in Microsoft 365 (Office 365). A malware filter policy is used to alert administrators that an internal user sent a message that contained malware.
- Effort: master
Microsoft 365 (Office 365) Malware Filter Rule Deletion
Detects when a malware filter rule has been deleted in Microsoft 365 (Office 365). The malware filter rule specifies the priority and recipient filters (who the policy applies to) for a malware filter policy.
- Effort: master
Microsoft 365 (Office 365) Malware Uploaded On OneDrive
Detects when Microsoft 365 (Office 365) identifies a malicious file uploaded to OneDrive. Attackers can use this method to propagate through the network.
- Effort: intermediate
Microsoft 365 (Office 365) Malware Uploaded On SharePoint
Detects when Microsoft 365 (Office 365) identifies a malicious file uploaded to SharePoint. Attackers can use this method to propagate through the network.
- Effort: intermediate
Microsoft 365 (Office 365) Mass Download By A Single User
Identifies when Microsoft Cloud App Security reports that a single user performs more than 50 downloads within 1 minute.
- Effort: master
Microsoft 365 (Office 365) Potential Ransomware Activity Detected
Detects when Microsoft Cloud App Security reports that a user has uploaded files to the cloud that might be infected with ransomware.
- Effort: master
Microsoft 365 (Office 365) Safe Attachment Rule Disabled
Detects when the safe attachment rule has been deleted in Microsoft 365 (Office 365). Safe Attachments is a feature in Microsoft Defender for Microsoft 365 (Office 365) that opens email attachments in a special hypervisor environment to detect malicious activity.
- Effort: master
Microsoft 365 (Office 365) Safelinks Disabled
Detects when a safelink rule has been deleted in Microsoft 365 (Office 365). Safe Links is a feature in Defender for Microsoft 365 (Office 365) that provides URL scanning and rewriting of inbound email messages in mail flow, and time-of-click verification of URLs and links in email messages and other locations.
- Effort: master
Microsoft 365 (Office 365) Unusual Volume Of File Deletion
Detects when Microsoft Cloud App Security identifies that a user has deleted an unusually large volume of files.
- Effort: master
Microsoft 365 Authenticated Activity From Tor IP Address
Detects authenticated Microsoft 365 activity from an IP address associated with Tor.
- Effort: advanced
Microsoft 365 Device Code Authentication
Authentication via a device code is designed for use with input constrained devices. This method can however be abused, particularly in social engineering attacks. Whitelisting based on the organisation's practices is likely required to make this rule useful (e.g. excluding the public IP ranges of the organisation, excluding authentications attempt from managed devices, etc.). Note: if you collect Entra ID SignInLogs, the rule "Microsoft Entra ID (Azure AD) Device Code Authentication" is a better equivalent to this rule.
- Effort: master
Microsoft 365 Email Forwarding To Consumer Email Address
An email forwarding rule was created, that automatically forwards incoming emails to an address outside of the organization (most common consumer email services).
- Effort: intermediate
Microsoft 365 Email Forwarding To Email Address With Rare TLD
An email forwarding rule was created, that automatically forwards incoming emails to an address outside of the organization (less common top-level domain).
- Effort: intermediate
Microsoft 365 Email Forwarding To Privacy Email Address
An email forwarding rule was created, that automatically forwards incoming emails to an address outside of the organization (most common privacy email services).
- Effort: elementary
Microsoft 365 Security and Compliance Center High Severity Alert
A security or compliance-related alert of high severity was raised, based on the policies of the tenant. This rule can be very noisy depending on the configuration of the tenant. Alert filters are likely required. In addition, most alerts don't include any context, and are only useful if the analysts have access to the Microsoft portals to investigate.
- Effort: master
Microsoft 365 Security and Compliance Center Medium Severity Alert
A security or compliance-related alert of medium severity was raised, based on the policies of the tenant. This rule can be very noisy depending on the configuration of the tenant. Alert filters are likely required. In addition, most alerts don't include any context, and are only useful if the analysts have access to the Microsoft portals to investigate.
- Effort: master
Microsoft 365 Sign-in With No User Agent
Detects a sign-in without any User-Agent header. This may indicate that the sign-in originated from an adversary-in-the-middle phishing page or a password spraying tool. Sign-ins happening through a regular web browser always have a User-Agent header. Investigate the source IP address. If it is unknown, assume that the account's password is compromised.
- Effort: elementary
Microsoft 365 Suspicious Inbox Rule
Business Email Compromise threat actors often create inbox rules to forward, hide, or delete emails containing sensitive information. This rule detects common caracteristics of malicious inbox rules.
- Effort: elementary
Microsoft Defender for Office 365 High Severity AIR Alert
Microsoft Defender for Office 365 includes the capability to run Automated investigation and response (AIR) actions. This rule detects when a High severity alert triggers an automated investigation, such as when a potentially malicious URL click was detected, or when a user is restricted from sending email.
- Effort: master
Microsoft Defender for Office 365 Low Severity AIR Alert Handled Automatically
Microsoft Defender for Office 365 includes the capability to run Automated investigation and response (AIR) actions. This rule detects when a Low or Informational severity alert triggered an automated investigation, and remediation was conducted automatically. Low and Informational alerts include when an email is reported by a user, or when a malicious email is removed after delivery.
- Effort: master
Microsoft Defender for Office 365 Low Severity AIR Alert Requires Action
Microsoft Defender for Office 365 includes the capability to run Automated investigation and response (AIR) actions. This rule detects when a Low or Informational severity alert triggered an automated investigation, and remediation actions need to be approved or conducted. Low and Informational alerts include when an email is reported by a user, or when a malicious email is removed after delivery.
- Effort: master
Microsoft Defender for Office 365 Medium Severity AIR Alert
Microsoft Defender for Office 365 includes the capability to run Automated investigation and response (AIR) actions. This rule detects when a Medium severity alert triggers an automated investigation, such as when suspicious email sending patterns are detected from an account.
- Effort: master
Microsoft Entra ID (Azure AD) Domain Trust Modification
Adversaries may add new domain trusts or modify the properties of existing domain trusts to evade defenses and/or elevate privileges. Confirm the added or modified target domain/URL is legitimate administrator behavior.
- Effort: elementary
Microsoft Exchange Server Creating Unusual Files
Look for Microsoft Exchange Server’s Unified Messaging service creating non-standard content on disk, which could indicate web shells or other malicious content, suggesting exploitation of CVE-2021-26858 vulnerability
- Effort: intermediate
Multiple Authentication On Microsoft 365 (Office 365) Portal From Two IP Addresses
Detection of login events from two IP addresses within 3mn, as it could happen if someone got phished with a tool like Evilginx2.
- Effort: intermediate
Network Scanning and Discovery
Tools and command lines used for network discovery from current system
- Effort: advanced
Network Sniffing
List of common tools used for network packages sniffing
- Effort: advanced
Network Sniffing Windows
Network sniffing refers to using the network interface on a system to monitor or capture information sent over a wired or wireless connection. An adversary may place a network interface into promiscuous mode to passively access data in transit over the network, or use span ports to capture a larger amount of data.
- Effort: intermediate
Nimbo-C2 User Agent
Nimbo-C2 Uses an unusual User-Agent format in its implants.
- Effort: intermediate
NlTest Usage
Detects attempts to gather information on domain trust relationships that may be used to identify lateral movement opportunities. These command lines were observed in numerous attacks, but also sometimes from legitimate administrators for debugging purposes. The rule does not cover very basics commands but rather the ones that are interesting for attackers to gather information on a domain.
- Effort: advanced
Password Change On Directory Service Restore Mode (DSRM) Account
The Directory Service Restore Mode (DSRM) account is a local administrator account on Domain Controllers. Attackers may change the password to gain persistence.
- Effort: intermediate
PasswordDump SecurityXploded Tool
Detects the execution of the PasswordDump SecurityXploded Tool
- Effort: elementary
Possible Malicious File Double Extension
Detects request to potential malicious file with double extension
- Effort: elementary
Possible Replay Attack
This event can be a sign of Kerberos replay attack or, among other things, network device configuration or routing problems.
- Effort: master
Potential Bazar Loader User-Agents
Detects potential Bazar loader communications through the user-agent
- Effort: elementary
Potential Lemon Duck User-Agent
Detects LemonDuck user agent. The format used two sets of alphabetical characters separated by dashes, for example "User-Agent: Lemon-Duck-[A-Z]-[A-Z]".
- Effort: elementary
ProxyShell Microsoft Exchange Suspicious Paths
Detects suspicious calls to Microsoft Exchange resources, in locations related to webshells observed in campaigns using this vulnerability.
- Effort: elementary
PsExec Process
Detects PsExec execution, command line which contains pstools or installation of the PsExec service. PsExec is a SysInternals which can be used to execute a program on another computer. The tool is as much used by attackers as by administrators.
- Effort: advanced
RDP Configuration File From Mail Process
Detects RDP configuration file being created or executed by a Mail-related process like Outlook. RDP configuration file will allow, when opened, an user to connect to the configured server easily. Attackers use this to trick victims in order to get a shared drive and potentially retrieve the data from that drive, but also drop a malicious file on the drive to establish persistence. Using RDP can also expose the victim's credential and clipboard data on some cases.
- Effort: advanced
RDP Session Discovery
Detects use of RDP session discovery via qwinsta or quser. Used by some threat actors to know if someone is working via RDP on a server.
- Effort: advanced
RTLO Character
Detects RTLO (Right-To-Left character) in file and process names.
- Effort: elementary
Raccoon Stealer 2.0 Legitimate Third-Party DLL Download URL
Detects Raccoon Stealer 2.0 malware downloading legitimate third-party DLLs from its C2 server. These legitimate DLLs are used by the information stealer to collect data on the compromised hosts.
- Effort: elementary
Remote Access Tool Domain
Detects traffic toward a domain flagged as a Remote Administration Tool (RAT).
- Effort: master
Remote Monitoring and Management Software - AnyDesk
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool AnyDesk.
- Effort: master
Remote Monitoring and Management Software - Atera
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool Atera.
- Effort: master
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
Sekoia.io EICAR Detection
Detects observables in Sekoia.io CTI tagged as EICAR, which are fake samples meant to test detection.
- Effort: master
Sign-In Via Known AiTM Phishing Kit
Detects a sign-in attempt from an IP address belonging to a known adversary-in-the-middle phishing kit.
- Effort: elementary
SolarWinds Suspicious File Creation
Detects SolarWinds process creating a file with a suspicious extension. The process solarwinds.businesslayerhost.exe created an unexpected file whose extension is ".exe", ".ps1", ".jpg", ".png" or ".dll".
- Effort: intermediate
Suspicious Double Extension
Detects suspicious use of an .exe extension after a non-executable file extension like .pdf.exe, a set of spaces or underlines to cloak the executable file in spearphishing campaigns
- Effort: advanced
Suspicious Download Links From Legitimate Services
Detects users clicking on Google docs links to download suspicious files. This technique was used a lot by Bazar Loader in the past.
- Effort: intermediate
Suspicious Email Attachment Received
Detects email containing a suspicious file as an attachment, based on its extension.
- Effort: advanced
Suspicious File Name
Detects suspicious file name possibly linked to malicious tool.
- Effort: advanced
Suspicious PROCEXP152.sys File Created In Tmp
Detects the creation of the PROCEXP152.sys file in the application-data local temporary folder. This driver is used by Sysinternals Process Explorer but also by KDU (https://github.com/hfiref0x/KDU) or Ghost-In-The-Logs (https://github.com/bats3c/Ghost-In-The-Logs), which uses KDU. Note - Clever attackers may easily bypass this detection by just renaming the driver filename. Therefore just Medium-level and don't rely on it.
- Effort: advanced
Suspicious TOR Gateway
Detects suspicious TOR gateways. Gateways are often used by the victim to pay and decrypt the encrypted files without installing TOR. Tor intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: advanced
Suspicious URI Used In A Lazarus Campaign
Detects suspicious requests to a specific URI, usually on an .asp page. The website is often compromised.
- Effort: intermediate
System Info Discovery
System info discovery, attempt to detects basic command use to fingerprint a host.
- Effort: master
TOR Usage Generic Rule
Detects TOR usage globally, whether the IP is a destination or source. TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
TrevorC2 HTTP Communication
Detects TrevorC2 HTTP communication based on the HTTP request URI and the user-agent.
- Effort: elementary
User Account Created
Detects user creation on windows servers, which shouldn't happen in an Active Directory environment. Apply this on your windows server logs and not on your DC logs. One default account defaultuser0 is excluded as only used during Windows set-up. This detection use Security Event ID 4720.
- Effort: master
User Account Deleted
Detects local user deletion
- Effort: master
WCE wceaux.dll Creation
Detects wceaux.dll creation while Windows Credentials Editor (WCE) is executed.
- Effort: intermediate
ZIP LNK Infection Chain
Detection of an ZIP download followed by a child-process of explorer, followed by multiple Windows processes.This is widely used as an infection chain mechanism.
- Effort: advanced
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Office 365 account logs |
Authentication events |
Office 365 audit logs |
Some user actions are parsed (e.g. file access) |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | alert |
| Category | authentication, email, file, iam, intrusion_detection, network |
| Type | access, change, info, start |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "{\"CreationTime\":\"2020-09-29T08:59:26\",\"Id\":\"e1717ca5-c13e-4382-ad7e-4864faa11e85\",\"Operation\":\"UserLoggedIn\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":15,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ClientIP\":\"1.2.3.4\",\"ObjectId\":\"cc15fd57-2c6c-4117-a88c-83b1d56b4bbe\",\"UserId\":\"user1\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"UserAgent\",\"Value\":\"Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.121 Safari/537.36\"},{\"Name\":\"UserAuthenticationMethod\",\"Value\":\"1\"},{\"Name\":\"RequestType\",\"Value\":\"OAuth2:Authorize\"},{\"Name\":\"ResultStatusDetail\",\"Value\":\"Redirect\"},{\"Name\":\"KeepMeSignedIn\",\"Value\":\"True\"}],\"ModifiedProperties\":[],\"Actor\":[{\"ID\":\"cb42ef6c-989f-49d0-86cd-7706b8d14528\",\"Type\":0},{\"ID\":\"user1\",\"Type\":5},{\"ID\":\"10030000A9F382C6\",\"Type\":3}],\"ActorContextId\":\"ANONYMIZED\",\"ActorIpAddress\":\"1.2.3.4\",\"InterSystemsId\":\"d23dd5d2-ccc8-4928-b7a0-f446a2ca4a90\",\"IntraSystemId\":\"a196489a-9a7c-4824-b35a-5bfdec600c00\",\"SupportTicketId\":\"\",\"Target\":[{\"ID\":\"cc15fd57-2c6c-4117-a88c-83b1d56b4bbe\",\"Type\":0}],\"TargetContextId\":\"ANONYMIZED\",\"ApplicationId\":\"5e3ce6c0-2b1f-4285-8d4b-75ee78787346\"}",
"event": {
"action": "UserLoggedIn",
"category": [
"authentication"
],
"code": "15",
"outcome": "success",
"type": [
"start"
]
},
"@timestamp": "2020-09-29T08:59:26Z",
"action": {
"id": 15,
"name": "UserLoggedIn",
"outcome": "success",
"target": "network-traffic"
},
"office365": {
"audit": {
"object_id": "cc15fd57-2c6c-4117-a88c-83b1d56b4bbe"
},
"auth": {
"keep_me_signed_in": true,
"request_type": "OAuth2:Authorize",
"result_status_detail": "Redirect",
"user_authentication_method": 1
},
"context": {
"client": {
"id": "5e3ce6c0-2b1f-4285-8d4b-75ee78787346"
},
"correlation": {
"id": "d23dd5d2-ccc8-4928-b7a0-f446a2ca4a90"
}
},
"record_id": "e1717ca5-c13e-4382-ad7e-4864faa11e85",
"record_type": 15,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "user1",
"name": "user1"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Chrome",
"original": "Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.121 Safari/537.36",
"os": {
"name": "Linux"
},
"version": "85.0.4183"
}
}
{
"message": "{\"CreationTime\":\"2023-08-22T13:51:38\",\"Id\":\"3e4f9ff8\",\"Operation\":\"UserLoggedIn\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":15,\"ResultStatus\":\"Success\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ClientIP\":\"1.2.3.4\",\"ObjectId\":\"16aeb910\",\"UserId\":\"user1\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"ResultStatusDetail\",\"Value\":\"Success\"},{\"Name\":\"UserAgent\",\"Value\":\"Mozilla/5.0\"},{\"Name\":\"RequestType\",\"Value\":\"OAuth2:Token\"}],\"ModifiedProperties\":[],\"Actor\":[{\"ID\":\"user1\",\"Type\":0},{\"ID\":\"joe.doe@user.fr\",\"Type\":5}],\"ActorContextId\":\"ANONYMIZED\",\"ActorIpAddress\":\"1.2.3.4\",\"InterSystemsId\":\"d8254b84\",\"IntraSystemId\":\"3e4f9ff8\",\"SupportTicketId\":\"\",\"Target\":[{\"ID\":\"16aeb910\",\"Type\":0}],\"TargetContextId\":\"ANONYMIZED\",\"ApplicationId\":\"1b3c667f\",\"DeviceProperties\":[{\"Name\":\"OS\",\"Value\":\"Windows10\"},{\"Name\":\"BrowserType\",\"Value\":\"Edge\"},{\"Name\":\"IsCompliantAndManaged\",\"Value\":\"False\"},{\"Name\":\"SessionId\",\"Value\":\"8e2cdebf\"}],\"ErrorNumber\":\"0\"}",
"event": {
"action": "UserLoggedIn",
"category": [
"authentication"
],
"code": "15",
"outcome": "success",
"type": [
"start"
]
},
"@timestamp": "2023-08-22T13:51:38Z",
"action": {
"id": 15,
"name": "UserLoggedIn",
"outcome": "success",
"target": "network-traffic"
},
"host": {
"os": {
"full": "Windows10"
}
},
"office365": {
"audit": {
"object_id": "16aeb910"
},
"auth": {
"request_type": "OAuth2:Token",
"result_status_detail": "Success"
},
"context": {
"aad_session_id": "8e2cdebf",
"client": {
"id": "1b3c667f"
},
"correlation": {
"id": "d8254b84"
}
},
"device": {
"browser_type": "Edge",
"is_compliant_and_managed": false
},
"error_number": 0,
"record_id": "3e4f9ff8",
"record_type": 15,
"result_status": "Success",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "user1",
"name": "user1"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Other",
"original": "Mozilla/5.0",
"os": {
"name": "Other"
}
}
}
{
"message": "{\"CreationTime\":\"2025-11-18T19:56:44\",\"Id\":\"99999999-9999-9999-9999-999999999999\",\"Operation\":\"Consent to application.\",\"OrganizationId\":\"redacted\",\"RecordType\":8,\"ResultStatus\":\"Success\",\"UserKey\":\"1234567890@example.com\",\"UserType\":0,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ObjectId\":\"11111111-1111-1111-1111-111111111111\",\"UserId\":\"john.doe@example.com\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"additionalDetails\",\"Value\":\"{\\\"User-Agent\\\":\\\"EvoSTS\\\",\\\"AppId\\\":\\\"11111111-1111-1111-1111-111111111111\\\"}\"},{\"Name\":\"extendedAuditEventCategory\",\"Value\":\"ServicePrincipal\"}],\"ModifiedProperties\":[{\"Name\":\"ConsentContext.IsAdminConsent\",\"NewValue\":\"False\",\"OldValue\":\"\"},{\"Name\":\"ConsentContext.IsAppOnly\",\"NewValue\":\"False\",\"OldValue\":\"\"},{\"Name\":\"ConsentContext.OnBehalfOfAll\",\"NewValue\":\"False\",\"OldValue\":\"\"},{\"Name\":\"ConsentContext.Tags\",\"NewValue\":\"WindowsAzureActiveDirectoryIntegratedApp\",\"OldValue\":\"\"},{\"Name\":\"ConsentAction.Permissions\",\"NewValue\":\"[] => [[Id: REDACTED, ClientId: 33333333-3333-3333-3333-333333333333, PrincipalId: 55555555-5555-5555-5555-555555555555, ResourceId: 22222222-1111-1111-1111-222222222222, ConsentType: Principal, Scope: openid profile email offline_access, CreatedDateTime: , LastModifiedDateTime ]]; \",\"OldValue\":\"\"},{\"Name\":\"TargetId.ServicePrincipalNames\",\"NewValue\":\"11111111-1111-1111-1111-111111111111\",\"OldValue\":\"\"}],\"Actor\":[{\"ID\":\"john.doe@example.com\",\"Type\":5},{\"ID\":\"1234567890\",\"Type\":3},{\"ID\":\"Azure ESTS Service\",\"Type\":1},{\"ID\":\"44444444-4444-4444-4444-444444444444\",\"Type\":2},{\"ID\":\"User_55555555-5555-5555-5555-555555555555\",\"Type\":2},{\"ID\":\"55555555-5555-5555-5555-555555555555\",\"Type\":2},{\"ID\":\"User\",\"Type\":2}],\"ActorContextId\":\"redacted\",\"InterSystemsId\":\"77777777-7777-7777-7777-777777777777\",\"IntraSystemId\":\"66666666-6666-6666-6666-666666666666\",\"SupportTicketId\":\"\",\"Target\":[{\"ID\":\"ServicePrincipal_33333333-3333-3333-3333-333333333333\",\"Type\":2},{\"ID\":\"33333333-3333-3333-3333-333333333333\",\"Type\":2},{\"ID\":\"ServicePrincipal\",\"Type\":2},{\"ID\":\"APPNAME\",\"Type\":1},{\"ID\":\"11111111-1111-1111-1111-111111111111\",\"Type\":2},{\"ID\":\"11111111-1111-1111-1111-111111111111\",\"Type\":4}],\"TargetContextId\":\"redacted\",\"AssociatedAdminUnits\":[\"88888888-8888-8888-8888-888888888888\"]}",
"event": {
"action": "Consent to application",
"category": [
"iam"
],
"code": "8",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2025-11-18T19:56:44Z",
"action": {
"id": 8,
"name": "Consent to application",
"outcome": "success",
"target": "user"
},
"office365": {
"audit": {
"object_id": "11111111-1111-1111-1111-111111111111"
},
"context": {
"correlation": {
"id": "77777777-7777-7777-7777-777777777777"
},
"modified_properties": [
{
"Name": "ConsentContext.IsAdminConsent",
"NewValue": "False",
"OldValue": ""
},
{
"Name": "ConsentContext.IsAppOnly",
"NewValue": "False",
"OldValue": ""
},
{
"Name": "ConsentContext.OnBehalfOfAll",
"NewValue": "False",
"OldValue": ""
},
{
"Name": "ConsentContext.Tags",
"NewValue": "WindowsAzureActiveDirectoryIntegratedApp",
"OldValue": ""
},
{
"Name": "ConsentAction.Permissions",
"NewValue": "[] => [[Id: REDACTED, ClientId: 33333333-3333-3333-3333-333333333333, PrincipalId: 55555555-5555-5555-5555-555555555555, ResourceId: 22222222-1111-1111-1111-222222222222, ConsentType: Principal, Scope: openid profile email offline_access, CreatedDateTime: , LastModifiedDateTime ]]; ",
"OldValue": ""
},
{
"Name": "TargetId.ServicePrincipalNames",
"NewValue": "11111111-1111-1111-1111-111111111111",
"OldValue": ""
}
]
},
"record_id": "99999999-9999-9999-9999-999999999999",
"record_type": 8,
"result_status": "Success",
"target": {
"displayName": "APPNAME"
},
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "redacted"
},
"related": {
"user": [
"john.doe@example.com"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"user": {
"email": "john.doe@example.com",
"id": "1234567890@example.com",
"name": "john.doe@example.com"
}
}
{
"message": "{\"CreationTime\": \"2026-01-27T20:11:38\", \"Id\": \"44444444-4444-4444-4444-444444444444\", \"Operation\": \"Update PasswordProfile.\", \"OrganizationId\": \"22222222-2222-2222-2222-222222222222\", \"RecordType\": 8, \"ResultStatus\": \"Success\", \"UserKey\": \"Not Available\", \"UserType\": 4, \"Version\": 1, \"Workload\": \"AzureActiveDirectory\", \"ObjectId\": \"jonh.doe@example.com\", \"UserId\": \"ServicePrincipal_66666666-6666-6666-6666-666666666666\", \"AzureActiveDirectoryEventType\": 1, \"ExtendedProperties\": [{\"Name\": \"AdministrativeUnit\", \"Value\": \"33333333-3333-3333-3333-333333333333\"}, {\"Name\": \"additionalDetails\", \"Value\": \"{}\"}, {\"Name\": \"extendedAuditEventCategory\", \"Value\": \"User\"}], \"ModifiedProperties\": [{\"Name\": \"Password\", \"NewValue\": \"\", \"OldValue\": \"\"}, {\"Name\": \"ActorId.ServicePrincipalNames\", \"NewValue\": \"https://passwordreset.microsoftonline.com;https://passwordreset.microsoftonline.com/;55555555-5555-5555-5555-555555555555;SelfServicePasswordReset\", \"OldValue\": \"\"}, {\"Name\": \"SPN\", \"NewValue\": \"https://passwordreset.microsoftonline.com;https://passwordreset.microsoftonline.com/;55555555-5555-5555-5555-555555555555;SelfServicePasswordReset\", \"OldValue\": \"\"}], \"Actor\": [{\"ID\": \"Microsoft password reset service\", \"Type\": 1}, {\"ID\": \"55555555-5555-5555-5555-555555555555\", \"Type\": 2}, {\"ID\": \"ServicePrincipal_66666666-6666-6666-6666-666666666666\", \"Type\": 2}, {\"ID\": \"66666666-6666-6666-6666-666666666666\", \"Type\": 2}, {\"ID\": \"ServicePrincipal\", \"Type\": 2}], \"ActorContextId\": \"22222222-2222-2222-2222-222222222222\", \"InterSystemsId\": \"11111111-1111-1111-1111-111111111111\", \"IntraSystemId\": \"88888888-8888-8888-8888-888888888888\", \"SupportTicketId\": \"\", \"Target\": [{\"ID\": \"User_77777777-7777-7777-7777-777777777777\", \"Type\": 2}, {\"ID\": \"77777777-7777-7777-7777-777777777777\", \"Type\": 2}, {\"ID\": \"User\", \"Type\": 2}, {\"ID\": \"jonh.doe@example.com\", \"Type\": 5}, {\"ID\": \"55555555555555555\", \"Type\": 3}], \"TargetContextId\": \"22222222-2222-2222-2222-222222222222\"}",
"event": {
"action": "Update PasswordProfile",
"category": [
"iam"
],
"code": "8",
"outcome": "success",
"type": [
"change"
]
},
"@timestamp": "2026-01-27T20:11:38Z",
"action": {
"id": 8,
"name": "Update PasswordProfile",
"outcome": "success",
"target": "user"
},
"office365": {
"audit": {
"object_id": "jonh.doe@example.com"
},
"context": {
"correlation": {
"id": "11111111-1111-1111-1111-111111111111"
},
"modified_properties": [
{
"Name": "Password",
"NewValue": "",
"OldValue": ""
},
{
"Name": "ActorId.ServicePrincipalNames",
"NewValue": "https://passwordreset.microsoftonline.com;https://passwordreset.microsoftonline.com/;55555555-5555-5555-5555-555555555555;SelfServicePasswordReset",
"OldValue": ""
},
{
"Name": "SPN",
"NewValue": "https://passwordreset.microsoftonline.com;https://passwordreset.microsoftonline.com/;55555555-5555-5555-5555-555555555555;SelfServicePasswordReset",
"OldValue": ""
}
]
},
"record_id": "44444444-4444-4444-4444-444444444444",
"record_type": 8,
"result_status": "Success",
"target": {
"upn": "jonh.doe@example.com"
},
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "22222222-2222-2222-2222-222222222222"
},
"related": {
"user": [
"ServicePrincipal_66666666-6666-6666-6666-666666666666",
"jonh.doe@example.com"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"user": {
"id": "Not Available",
"name": "ServicePrincipal_66666666-6666-6666-6666-666666666666",
"target": {
"name": "jonh.doe@example.com"
}
}
}
{
"message": "{\"CreationTime\":\"2024-07-10T14:25:49\",\"Id\":\"b4f48141-a2fe-4d47-9f0d-f09f26307035\",\"Operation\":\"Add member to role.\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":8,\"ResultStatus\":\"Success\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ObjectId\":\"john.doe@example.com\",\"UserId\":\"user1\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"additionalDetails\",\"Value\":\"{}\"},{\"Name\":\"extendedAuditEventCategory\",\"Value\":\"Role\"}],\"ModifiedProperties\":[{\"Name\":\"Role.ObjectID\",\"NewValue\":\"54fc7176-29ef-4b41-808f-3cdeb8010649\",\"OldValue\":\"\"},{\"Name\":\"Role.DisplayName\",\"NewValue\":\"Global Administrator\",\"OldValue\":\"\"},{\"Name\":\"Role.TemplateId\",\"NewValue\":\"ad1cbca4-efcc-4149-b4a2-aeb40412fe48\",\"OldValue\":\"\"},{\"Name\":\"Role.WellKnownObjectName\",\"NewValue\":\"TenantAdmins\",\"OldValue\":\"\"}],\"Actor\":[{\"ID\":\"user1\",\"Type\":5},{\"ID\":\"100320029D963D0D\",\"Type\":3},{\"ID\":\"User_576409b5-84f3-4791-8e3c-c9677e3bd898\",\"Type\":2},{\"ID\":\"576409b5-84f3-4791-8e3c-c9677e3bd898\",\"Type\":2},{\"ID\":\"User\",\"Type\":2}],\"ActorContextId\":\"ANONYMIZED\",\"InterSystemsId\":\"5a0910e4-c125-4b46-9616-0232d14915dc\",\"IntraSystemId\":\"fb6cd132-f8e8-4ec5-9a0b-4ec8397e1405\",\"SupportTicketId\":\"\",\"Target\":[{\"ID\":\"User_46522b15-1bf5-4bed-8a6c-4edc58c05b23\",\"Type\":2},{\"ID\":\"46522b15-1bf5-4bed-8a6c-4edc58c05b23\",\"Type\":2},{\"ID\":\"User\",\"Type\":2},{\"ID\":\"john.doe@example.com\",\"Type\":5},{\"ID\":\"100320029D9D1C86\",\"Type\":3}],\"TargetContextId\":\"ANONYMIZED\"}",
"event": {
"action": "Add member to role",
"category": [
"iam"
],
"code": "8",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-07-10T14:25:49Z",
"action": {
"id": 8,
"name": "Add member to role",
"outcome": "success",
"target": "user"
},
"office365": {
"audit": {
"object_id": "john.doe@example.com"
},
"context": {
"correlation": {
"id": "5a0910e4-c125-4b46-9616-0232d14915dc"
},
"modified_properties": [
{
"Name": "Role.ObjectID",
"NewValue": "54fc7176-29ef-4b41-808f-3cdeb8010649",
"OldValue": ""
},
{
"Name": "Role.DisplayName",
"NewValue": "Global Administrator",
"OldValue": ""
},
{
"Name": "Role.TemplateId",
"NewValue": "ad1cbca4-efcc-4149-b4a2-aeb40412fe48",
"OldValue": ""
},
{
"Name": "Role.WellKnownObjectName",
"NewValue": "TenantAdmins",
"OldValue": ""
}
]
},
"record_id": "b4f48141-a2fe-4d47-9f0d-f09f26307035",
"record_type": 8,
"result_status": "Success",
"target": {
"upn": "john.doe@example.com"
},
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"john.doe@example.com",
"user1"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"user": {
"id": "user1",
"name": "user1",
"target": {
"name": "john.doe@example.com"
}
}
}
{
"message": "{\"CreationTime\":\"2023-04-17T14:27:09\",\"Id\":\"60eaf0aa-edc3-4f8d-8275-bc82d9500e59\",\"Operation\":\"AirInvestigationData\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":64,\"UserKey\":\"user1\",\"UserType\":4,\"Version\":1,\"Workload\":\"user1\",\"ObjectId\":\"60eaf0aa-edc3-4f8d-8275-bc82d9500e59\",\"UserId\":\"user1\",\"DeepLinkUrl\":\"https://security.microsoft.com/mtp-investigation/urn:ZappedUrlInvestigation:a10a976\",\"EndTimeUtc\":\"2023-04-17T14:27:07\",\"InvestigationId\":\"urn:ZappedUrlInvestigation:a10a976d-6e3e-4d10-be50-4907183b6f86\",\"InvestigationName\":\"Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:a1\",\"InvestigationType\":\"ZappedUrlInvestigation\",\"LastUpdateTimeUtc\":\"2023-04-17T14:21:59\",\"RunningTime\":931,\"StartTimeUtc\":\"2023-04-17T14:11:38\",\"Status\":\"Remediated\",\"Data\":\"{\\\"Version\\\":\\\"3.0\\\",\\\"VendorName\\\":\\\"Microsoft\\\",\\\"ProviderName\\\":\\\"OATP\\\",\\\"AlertType\\\":\\\"alert_type_value\\\",\\\"Status\\\":\\\"status_value\\\",\\\"Severity\\\":\\\"severity_value\\\",\\\"IsIncident\\\":true,\\\"CorrelationKey\\\":\\\"correlation_key_value\\\",\\\"Category\\\":\\\"category_value\\\",\\\"SourceAlertType\\\":\\\"source_alert_type_value\\\",\\\"MachineName\\\":\\\"machine_name_value\\\"}\",\"Actions\":[\"{\\\"$id\\\":\\\"1\\\",\\\"ActionId\\\":\\\"urn:EmailZapper:8ad9417586e14790ba2afed0a7840e65\\\"}\"]}",
"event": {
"action": "AirInvestigationData",
"code": "64",
"end": "2023-04-17T14:27:07Z",
"kind": "alert",
"outcome": "success",
"start": "2023-04-17T14:11:38Z"
},
"@timestamp": "2023-04-17T14:27:09Z",
"action": {
"id": 64,
"name": "AirInvestigationData",
"outcome": "success",
"target": "user"
},
"log": {
"level": "severity_value"
},
"office365": {
"audit": {
"object_id": "60eaf0aa-edc3-4f8d-8275-bc82d9500e59"
},
"investigation": {
"alert": {
"category": "category_value",
"correlation_key": "correlation_key_value",
"is_incident": true,
"provider": {
"name": "OATP",
"status": "status_value"
},
"severity": "severity_value",
"source_type": "source_alert_type_value",
"type": "alert_type_value"
},
"id": "urn:ZappedUrlInvestigation:a10a976d-6e3e-4d10-be50-4907183b6f86",
"name": "Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:a1",
"status": "Remediated",
"type": "ZappedUrlInvestigation"
},
"machine_name": "machine_name_value",
"record_id": "60eaf0aa-edc3-4f8d-8275-bc82d9500e59",
"record_type": 64,
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"service": {
"name": "user1"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2024-10-31T16:24:41\",\"Id\":\"c3ebef20-fb63-4d14-b3c1-7bfb5937903a\",\"Operation\":\"AirInvestigationData\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":64,\"UserKey\":\"user1\",\"UserType\":4,\"Version\":1,\"Workload\":\"user1\",\"ObjectId\":\"c3ebef20-fb63-4d14-b3c1-7bfb5937903a\",\"UserId\":\"user1\",\"Actions\":[\"{\\\"$id\\\":\\\"1\\\",\\\"ActionId\\\":\\\"urn:EmailZapper:a17bc80a136cbf4f5d4e82f43a9a3d1d\\\",\\\"InvestigationId\\\":\\\"urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101\\\",\\\"ActionApproval\\\":\\\"None\\\",\\\"ActionType\\\":\\\"EmailRemediation\\\",\\\"ActionStatus\\\":\\\"Pending\\\",\\\"Entities\\\":[{\\\"$id\\\":\\\"2\\\",\\\"NetworkMessageIds\\\":[\\\"24b8430c-484d-4ee0-e12b-08dcee99416a\\\",\\\"2e99f39a-c998-4d94-2085-08dce9cd0b7d\\\",\\\"0ac4ee3c-7c79-408e-76c2-08dcf4106b65\\\",\\\"fd400540-8a8d-42ae-d1f9-08dced20c42f\\\",\\\"31cfca73-f309-4e21-cbc4-08dceed074cf\\\",\\\"0491b33a-15fc-4503-9dd1-08dced818f57\\\",\\\"4b620244-917b-4a04-7416-08dcf50af378\\\",\\\"1abed68d-3b03-46bd-45e2-08dcf43fb625\\\",\\\"abb4c4a5-7049-4047-5a68-08dcec201c1f\\\",\\\"92bba720-15bc-4f09-49f2-08dcf8d738a4\\\",\\\"3d511617-b717-416c-89cf-08dcf90a51c7\\\",\\\"c3ad4b6b-0fd9-4510-4481-08dcf9043502\\\",\\\"37b236bd-ad39-41c0-3984-08dcf85e6b44\\\",\\\"a1d9684c-9982-4f80-880c-08dcf775c1a9\\\"],\\\"CountByThreatType\\\":{\\\"HighConfPhish\\\":5,\\\"Phish\\\":0,\\\"Malware\\\":0,\\\"Spam\\\":0,\\\"MaliciousUrl\\\":15},\\\"CountByProtectionStatus\\\":{\\\"Delivered\\\":10,\\\"Blocked\\\":4,\\\"DeliveredAsSpam\\\":1},\\\"CountByDeliveryLocation\\\":{\\\"Inbox\\\":10,\\\"Quarantine\\\":4,\\\"DeletedFolder\\\":1},\\\"Query\\\":\\\"( ((NormalizedUrl:\\\\\\\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en\\\\\\\") AND (ContentType: 1)) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\\\",\\\"QueryTime\\\":\\\"2024-10-31T13:31:54.2957192Z\\\",\\\"MailCount\\\":15,\\\"IsVolumeAnamoly\\\":false,\\\"ClusterSourceIdentifier\\\":\\\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en\\\",\\\"ClusterSourceType\\\":\\\"UrlThreatIndicator\\\",\\\"ClusterQueryStartTime\\\":\\\"2024-10-11T00:00:00Z\\\",\\\"ClusterQueryEndTime\\\":\\\"2024-10-31T13:31:54.2957192Z\\\",\\\"ClusterGroup\\\":\\\"UrlThreatIdentifier\\\",\\\"Type\\\":\\\"mailCluster\\\",\\\"ClusterBy\\\":\\\"NormalizedUrl;ContentType\\\",\\\"ClusterByValue\\\":\\\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en;1\\\",\\\"QueryStartTime\\\":\\\"10/11/2024 12:00:00 AM\\\",\\\"QueryTime\\\":\\\"10/31/2024 1:31:54 PM\\\",\\\"Urn\\\":\\\"urn:MailClusterEntity:cae0ce4483385c4ff176b00a0cd18f8e\\\",\\\"Source\\\":\\\"TestProvider\\\",\\\"FirstSeen\\\":\\\"2024-10-31T13:31:56\\\"}],\\\"RelatedAlertIds\\\":[\\\"fff21c13-c681-7398-1200-08dcf8958252\\\"],\\\"StartTimeUtc\\\":\\\"2024-10-31T13:33:19\\\",\\\"LastUpdateTimeUtc\\\":\\\"2024-10-31T15:28:45.1030022Z\\\",\\\"TimestampUtc\\\":\\\"2024-10-31T13:33:19\\\",\\\"BulkName\\\":\\\"Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101\\\",\\\"ResourceIdentifiers\\\":[{\\\"$id\\\":\\\"3\\\",\\\"AadTenantId\\\":\\\"xxxxxx-xxxxx-xxxxxxx-xxxxxxx-xxxxxxx\\\",\\\"Type\\\":\\\"AAD\\\"}],\\\"PendingType\\\":\\\"User\\\",\\\"LogCreationTime\\\":\\\"2024-10-31T15:28:45.1030022Z\\\",\\\"MachineName\\\":\\\"MachineNameTest\\\",\\\"Description\\\":\\\"For malicious emails, you can move to junk, soft or hard delete from user's mailbox.\\\"}\"],\"Data\":\"{\\\"Version\\\":\\\"3.0\\\",\\\"VendorName\\\":\\\"Microsoft\\\",\\\"ProviderName\\\":\\\"TestProvider\\\",\\\"AlertType\\\":\\\"8e6ba277-ef39-404e-aaf1-294f6d9a2b88\\\",\\\"StartTimeUtc\\\":\\\"2024-10-30T03:47:24Z\\\",\\\"EndTimeUtc\\\":\\\"2024-10-30T03:47:24Z\\\",\\\"TimeGenerated\\\":\\\"2024-10-30T03:52:49.16Z\\\",\\\"ProcessingEndTime\\\":\\\"2024-10-31T15:28:45.1030022Z\\\",\\\"Status\\\":\\\"InProgress\\\",\\\"DetectionTechnology\\\":\\\"UrlReputation\\\",\\\"Severity\\\":\\\"Informational\\\",\\\"ConfidenceLevel\\\":\\\"Unknown\\\",\\\"ConfidenceScore\\\":1.0,\\\"IsIncident\\\":false,\\\"ProviderAlertId\\\":\\\"fff21c13-c681-7398-1200-08dcf8958252\\\",\\\"SystemAlertId\\\":null,\\\"CorrelationKey\\\":\\\"bb0ac18c-5081-41e0-8656-f256ba9298d0\\\",\\\"Investigations\\\":[{\\\"$id\\\":\\\"1\\\",\\\"Id\\\":\\\"urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101\\\",\\\"InvestigationStatus\\\":\\\"Running\\\"}],\\\"InvestigationIds\\\":[\\\"urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101\\\"],\\\"Intent\\\":\\\"Probing\\\",\\\"ResourceIdentifiers\\\":[{\\\"$id\\\":\\\"2\\\",\\\"AadTenantId\\\":\\\"xxxxxx-xxxxx-xxxxxxx-xxxxxxx-xxxxxxx\\\",\\\"Type\\\":\\\"AAD\\\"}],\\\"AzureResourceId\\\":null,\\\"WorkspaceId\\\":null,\\\"WorkspaceSubscriptionId\\\":null,\\\"WorkspaceResourceGroup\\\":null,\\\"AgentId\\\":null,\\\"AlertDisplayName\\\":\\\"Email messages containing malicious URL removed after delivery\\u200b\\\",\\\"Description\\\":\\\"Emails with malicious URL that were delivered and later removed -V1.0.0.3\\\",\\\"ExtendedLinks\\\":[{\\\"Href\\\":\\\"https://security.microsoft.com/alerts/fafff21c13-c681-7398-1200-08dcf8958252\\\",\\\"Category\\\":null,\\\"Label\\\":\\\"alert\\\",\\\"Type\\\":\\\"webLink\\\"}],\\\"Metadata\\\":{\\\"CustomApps\\\":null,\\\"GenericInfo\\\":null},\\\"Entities\\\":[{\\\"$id\\\":\\\"3\\\",\\\"Url\\\":\\\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en\\\",\\\"Type\\\":\\\"url\\\",\\\"ClickCount\\\":0,\\\"EmailCount\\\":2,\\\"Urn\\\":\\\"urn:UrlEntity:289101bb3aa22cd0464dcd3ffa7116a8\\\",\\\"Source\\\":\\\"TestProvider\\\",\\\"FirstSeen\\\":\\\"2024-10-31T12:58:53\\\"},{\\\"$id\\\":\\\"4\\\",\\\"Files\\\":[{\\\"$id\\\":\\\"5\\\",\\\"Name\\\":\\\"returnLabel_314378736750.pdf\\\",\\\"FileHashes\\\":[{\\\"$id\\\":\\\"6\\\",\\\"Algorithm\\\":\\\"SHA256\\\",\\\"Value\\\":\\\"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b\\\",\\\"Type\\\":\\\"filehash\\\"}],\\\"Type\\\":\\\"file\\\",\\\"MalwareFamily\\\":null}],\\\"Recipient\\\":\\\"test.to@example.com\\\",\\\"Urls\\\":[\\\"https://subexample.example.net/?REDACTED\\\",\\\"https://u25492214.ct.example.net/ls/click?upn=u001.Ni9F2bUzMGygU7I6927xz-2B7I3RFKjR2LTj-2FCdqvCgUA-3De-zv_r5YCKD565fWzehHx-2FViuB8oHOL1DYwg-2Bfx4BUmzkfTPes7sa-2BVi-2BqS9kcdV08lhzTrs-2B4Lvsupi32g3cG4FINnNbknV9eEzYIqgaa4YfaZHEEHRVUWDqycf8mgAbrzvtnOX7pQHdt3iR6DHP-2BxR3PfnH-2BDzIJZkv1MK0yzBmp6otxpVGSalyLT-2BMyMS7yEfvbLbY9v9Wjn3hkHG29S-2FBOFjoVX-2FSwv2kZeymJW-2FlgRvHCB20rH0kwYqIdOsdO-2FvuCq-2BU49-2FNEo4S2gaZRd0h3zn5MFhXxj-2F-2FbW3X5gOaGP7-2FpGN-2BX-2BHRi1Xt1JzFgCpA\\\",\\\"https://u25492214.ct.example.net/ls/click?upn=u001.Ni9F2bUzMGygU7I6927xz49R6-2B-2FASLo-2BUtlyP-2F4iSjQlm-2F4HWFki90oq-2Bc29Sr-2BJAxlu_r5YCKD565fWzehHx-2FViuB8oHOL1DYwg-2Bfx4BUmzkfTPes7sa-2BVi-2BqS9kcdV08lhzTrs-2B4Lvsupi32g3cG4FINnNbknV9eEzYIqgaa4YfaZHEEHRVUWDqycf8mgAbrzvtnOX7pQHdt3iR6DHP-2BxR3PfnH-2BDzIJZkv1MK0yzBmp6qR2GRWjTyLjKHBwmcXgTV-2BMq0R5qnuDMHYAbrFxAmtHiepp1aU8L-2FOCt-2BiboZksoqBfuo-2FcqBrfi9un8ILJByRUOZM3T6alRzsB1jmdLOKOZwr3m8kymuz3dFvNya6aYPmSZG4l57ycCGBya5xMMqf\\\",\\\"https://u25492214.ct.example.net/ls/click?upn=u001.Ni9F2bUzMGygU7I6927xz1dNl4cyoCqQhbWGcqggHJW8SDLFVls-2FdSGWRn2n26uXgiSb-2FLZ3Oc-2F6taFyBHXTJv-2BdvE0YkDtEsaWUVnnpz7Lus9fp2MjvsYOqibyuC9Sjzgm4flo2XfvY4y5mBWuQF-2F7nM55pZ5S6S-2BSuNa5j-2BID5HJzdZOlXc2nyvbxmDFrTDuau_r5YCKD565fWzehHx-2FViuB8oHOL1DYwg-2Bfx4BUmzkfTPes7sa-2BVi-2BqS9kcdV08lhzTrs-2B4Lvsupi32g3cG4FINnNbknV9eEzYIqgaa4YfaZHEEHRVUWDqycf8mgAbrzvtnOX7pQHdt3iR6DHP-2BxR3PfnH-2BDzIJZkv1MK0yzBmp6oCyme2zPY6GKJBwI7FWZYrXhePHLdzV5WL-2F5EJubwqlYflj1CI9yL7Xfb24ks7WDE2wa8hQ-2BQ3h8K7-2FNpWkzEtiEQPiPEF3zOMzaOlqjkbPLg0UzpEmObjky1BycKoXMMwtfEuHLB9VnhNmDV3aIW2\\\",\\\"https://u25492214.ct.example.net/ls/click?upn=u001.Ni9F2bUzMGygU7I6927xzwS57HzRFV06M2bzMBaRY-2BtdD2HhGOqR6HD9j7eU3woqib3lW0qFsRIYtEfnDRINtIJErjGpQG2ad3jjAbAIacwJ4Le0eScR4TY1ExyusbvGQU5p_r5YCKD565fWzehHx-2FViuB8oHOL1DYwg-2Bfx4BUmzkfTPes7sa-2BVi-2BqS9kcdV08lhzTrs-2B4Lvsupi32g3cG4FINnNbknV9eEzYIqgaa4YfaZHEEHRVUWDqycf8mgAbrzvtnOX7pQHdt3iR6DHP-2BxR3PfnH-2BDzIJZkv1MK0yzBmp6psejQMn2EzritsHjoZX3rBM6GN1Gt7OeDjl2fzK-2BAK5-2FzHIjoTmyFKIkBvxn4mrKqstgF5tkhF6rc-2BIL2TqH7FTpqHdxk6lMOLfZVS4DrhiP-2FvyHZwSo2RzY-2BDmTRvcBEOqOwutpZKgr0m7fArTF-2Fv\\\",\\\"http://shein.ltwebstatic.com/advertise/shein/www/images_sheIn/SheIn_logo1_1.png\\\",\\\"https://romwe.ltwebstatic.com/advertise/romwe/www/images_Romwe/edm3_09_2.jpg\\\",\\\"https://romwe.ltwebstatic.com/advertise/romwe/www/images_Romwe/edm3_11_1.jpg\\\",\\\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en\\\",\\\"https://fr.shein.com/\\\",\\\"https://fr.shein.com/robot\\\",\\\"https://fr.shein.com/user/order_return/order_return_label/GSONEQ62U001GKT?country=France&refund_bill_id=&return_order_id=NE91E0E8C1\\\",\\\"https://itunes.apple.com/us/app/yub-streetwear-fashion-shopping/id878577184?mt=8\\\"],\\\"Threats\\\":[\\\"ZapPhish\\\",\\\"HighConfPhish\\\"],\\\"Sender\\\":\\\"test.sender@example.com\\\",\\\"P1Sender\\\":\\\"test.sender@example.com\\\",\\\"P1SenderDomain\\\":\\\"gmail.com\\\",\\\"SenderIP\\\":\\\"1.2.3.4\\\",\\\"P2Sender\\\":\\\"test.sender@example.com\\\",\\\"P2SenderDisplayName\\\":\\\"Fanny Barriol\\\",\\\"P2SenderDomain\\\":\\\"gmail.com\\\",\\\"ReceivedDate\\\":\\\"2024-10-29T21:12:56\\\",\\\"NetworkMessageId\\\":\\\"37b236bd-ad39-41c0-3984-08dcf85e6b44\\\",\\\"InternetMessageId\\\":\\\"<CAH2_hrsct2KwUBwRFXNs9sXxZyTJMnV2f7FxaPj2eX=7y5a2Hw@mail.gmail.com>\\\",\\\"Subject\\\":\\\"Fwd: Votre \\u00e9tiquette de retour de SHEIN\\\",\\\"AntispamDirection\\\":\\\"Inbound\\\",\\\"DeliveryAction\\\":\\\"Blocked\\\",\\\"ThreatDetectionMethods\\\":[\\\"UrlReputation\\\"],\\\"Language\\\":\\\"fr\\\",\\\"DeliveryLocation\\\":\\\"Quarantine\\\",\\\"OriginalDeliveryLocation\\\":\\\"Inbox\\\",\\\"PhishConfidenceLevel\\\":\\\"High\\\",\\\"AdditionalActionsAndResults\\\":[\\\"OriginalDelivery: [N/A]\\\",\\\"Zap: [Success: Message moved to quarantine]\\\"],\\\"AuthDetails\\\":[{\\\"Name\\\":\\\"SPF\\\",\\\"Value\\\":\\\"Pass\\\"},{\\\"Name\\\":\\\"DKIM\\\",\\\"Value\\\":\\\"Pass\\\"},{\\\"Name\\\":\\\"DMARC\\\",\\\"Value\\\":\\\"Pass\\\"},{\\\"Name\\\":\\\"Comp Auth\\\",\\\"Value\\\":\\\"pass\\\"}],\\\"SystemOverrides\\\":[],\\\"Type\\\":\\\"mailMessage\\\",\\\"Urn\\\":\\\"urn:MailEntity:79be71f3203d9db81f0076352eca662e\\\",\\\"Source\\\":\\\"TestProvider\\\",\\\"FirstSeen\\\":\\\"2024-10-31T12:58:53\\\"},{\\\"$id\\\":\\\"7\\\",\\\"MailboxPrimaryAddress\\\":\\\"test.to@example.com\\\",\\\"Upn\\\":\\\"test.to@example.com\\\",\\\"AadId\\\":\\\"2011d28b-3a87-4359-b2a0-7d14f0a83828\\\",\\\"RiskLevel\\\":\\\"None\\\",\\\"Type\\\":\\\"mailbox\\\",\\\"Urn\\\":\\\"urn:UserEntity:f182c190672d0194477f316c5f0367e5\\\",\\\"Source\\\":\\\"TestProvider\\\",\\\"FirstSeen\\\":\\\"2024-10-31T12:58:53\\\"},{\\\"$id\\\":\\\"8\\\",\\\"NetworkMessageIds\\\":[\\\"37b236bd-ad39-41c0-3984-08dcf85e6b44\\\"],\\\"CountByThreatType\\\":{\\\"HighConfPhish\\\":1,\\\"Phish\\\":0,\\\"Malware\\\":0,\\\"Spam\\\":0},\\\"CountByProtectionStatus\\\":{\\\"Blocked\\\":1},\\\"CountByDeliveryLocation\\\":{\\\"Quarantine\\\":1},\\\"Query\\\":\\\"( (( (BodyFingerprintBin1:\\\\\\\"2929356879\\\\\\\") ) AND ( (SenderIp:\\\\\\\"1.2.3.4\\\\\\\") ) AND ( (ContentType: 1) )) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\\\",\\\"QueryTime\\\":\\\"2024-10-31T13:31:45.0302157Z\\\",\\\"MailCount\\\":1,\\\"IsVolumeAnamoly\\\":false,\\\"ClusterSourceIdentifier\\\":\\\"37b236bd-ad39-41c0-3984-08dcf85e6b44\\\",\\\"ClusterSourceType\\\":\\\"Similarity\\\",\\\"ClusterQueryStartTime\\\":\\\"2024-10-11T00:00:00Z\\\",\\\"ClusterQueryEndTime\\\":\\\"2024-10-31T13:31:45.0302157Z\\\",\\\"ClusterGroup\\\":\\\"BodyFingerprintBin1,SenderIp\\\",\\\"Type\\\":\\\"mailCluster\\\",\\\"ClusterBy\\\":\\\"BodyFingerprintBin1;SenderIp;ContentType\\\",\\\"ClusterByValue\\\":\\\"2929356879;1.2.3.4;1\\\",\\\"QueryStartTime\\\":\\\"10/11/2024 12:00:00 AM\\\",\\\"QueryTime\\\":\\\"10/31/2024 1:31:45 PM\\\",\\\"Urn\\\":\\\"urn:MailClusterEntity:0b159e7db54d59b4165e81fb02f6c656\\\",\\\"Source\\\":\\\"TestProvider\\\",\\\"FirstSeen\\\":\\\"2024-10-31T13:31:52\\\"},{\\\"$id\\\":\\\"9\\\",\\\"NetworkMessageIds\\\":[\\\"37b236bd-ad39-41c0-3984-08dcf85e6b44\\\"],\\\"CountByThreatType\\\":{\\\"HighConfPhish\\\":1,\\\"Phish\\\":0,\\\"Malware\\\":0,\\\"Spam\\\":0},\\\"CountByProtectionStatus\\\":{\\\"Blocked\\\":1},\\\"CountByDeliveryLocation\\\":{\\\"Quarantine\\\":1},\\\"Query\\\":\\\"( (( (Subject:\\\\\\\"Fwd: Votre \\u00e9tiquette de retour de SHEIN\\\\\\\") ) AND ( (P2SenderDomain:\\\\\\\"gmail.com\\\\\\\") ) AND ( (AntispamDirection:\\\\\\\"1\\\\\\\") ) AND ( (ContentType: 1) )) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\\\",\\\"QueryTime\\\":\\\"2024-10-31T13:31:45.0302157Z\\\",\\\"MailCount\\\":1,\\\"IsVolumeAnamoly\\\":false,\\\"ClusterSourceIdentifier\\\":\\\"37b236bd-ad39-41c0-3984-08dcf85e6b44\\\",\\\"ClusterSourceType\\\":\\\"Similarity\\\",\\\"ClusterQueryStartTime\\\":\\\"2024-10-11T00:00:00Z\\\",\\\"ClusterQueryEndTime\\\":\\\"2024-10-31T13:31:45.0302157Z\\\",\\\"ClusterGroup\\\":\\\"Subject,P2SenderDomain,AntispamDirection\\\",\\\"Type\\\":\\\"mailCluster\\\",\\\"ClusterBy\\\":\\\"Subject;P2SenderDomain;AntispamDirection;ContentType\\\",\\\"ClusterByValue\\\":\\\"Fwd: Votre \\u00e9tiquette de retour de SHEIN;gmail.com;1;1\\\",\\\"QueryStartTime\\\":\\\"10/11/2024 12:00:00 AM\\\",\\\"QueryTime\\\":\\\"10/31/2024 1:31:45 PM\\\",\\\"Urn\\\":\\\"urn:MailClusterEntity:5e820543f7cce922d13fcc25a0ca2204\\\",\\\"Source\\\":\\\"TestProvider\\\",\\\"FirstSeen\\\":\\\"2024-10-31T13:31:52\\\"},{\\\"$id\\\":\\\"10\\\",\\\"NetworkMessageIds\\\":[\\\"37b236bd-ad39-41c0-3984-08dcf85e6b44\\\"],\\\"CountByThreatType\\\":{\\\"HighConfPhish\\\":1,\\\"Phish\\\":0,\\\"Malware\\\":0,\\\"Spam\\\":0},\\\"CountByProtectionStatus\\\":{\\\"Blocked\\\":1},\\\"CountByDeliveryLocation\\\":{\\\"Quarantine\\\":1},\\\"Query\\\":\\\"( (( (Subject:\\\\\\\"Fwd: Votre \\u00e9tiquette de retour de SHEIN\\\\\\\") ) AND ( (SenderIp:\\\\\\\"1.2.3.4\\\\\\\") ) AND ( (AntispamDirection:\\\\\\\"1\\\\\\\") ) AND ( (ContentType: 1) )) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\\\",\\\"QueryTime\\\":\\\"2024-10-31T13:31:45.0302157Z\\\",\\\"MailCount\\\":1,\\\"IsVolumeAnamoly\\\":false,\\\"ClusterSourceIdentifier\\\":\\\"37b236bd-ad39-41c0-3984-08dcf85e6b44\\\",\\\"ClusterSourceType\\\":\\\"Similarity\\\",\\\"ClusterQueryStartTime\\\":\\\"2024-10-11T00:00:00Z\\\",\\\"ClusterQueryEndTime\\\":\\\"2024-10-31T13:31:45.0302157Z\\\",\\\"ClusterGroup\\\":\\\"Subject,SenderIp,AntispamDirection\\\",\\\"Type\\\":\\\"mailCluster\\\",\\\"ClusterBy\\\":\\\"Subject;SenderIp;AntispamDirection;ContentType\\\",\\\"ClusterByValue\\\":\\\"Fwd: Votre \\u00e9tiquette de retour de SHEIN;1.2.3.4;1;1\\\",\\\"QueryStartTime\\\":\\\"10/11/2024 12:00:00 AM\\\",\\\"QueryTime\\\":\\\"10/31/2024 1:31:45 PM\\\",\\\"Urn\\\":\\\"urn:MailClusterEntity:a42bb73f2f36d917364f11fe67f0c39b\\\",\\\"Source\\\":\\\"TestProvider\\\",\\\"FirstSeen\\\":\\\"2024-10-31T13:31:52\\\"},{\\\"$id\\\":\\\"11\\\",\\\"NetworkMessageIds\\\":[\\\"37b236bd-ad39-41c0-3984-08dcf85e6b44\\\"],\\\"CountByThreatType\\\":{\\\"HighConfPhish\\\":1,\\\"Phish\\\":0,\\\"Malware\\\":0,\\\"Spam\\\":0},\\\"CountByProtectionStatus\\\":{\\\"Blocked\\\":1},\\\"CountByDeliveryLocation\\\":{\\\"Quarantine\\\":1},\\\"Query\\\":\\\"( (( (BodyFingerprintBin1:\\\\\\\"2929356879\\\\\\\") ) AND ( (P2SenderDomain:\\\\\\\"gmail.com\\\\\\\") ) AND ( (ContentType: 1) )) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\\\",\\\"QueryTime\\\":\\\"2024-10-31T13:31:45.0302157Z\\\",\\\"MailCount\\\":1,\\\"IsVolumeAnamoly\\\":false,\\\"ClusterSourceIdentifier\\\":\\\"37b236bd-ad39-41c0-3984-08dcf85e6b44\\\",\\\"ClusterSourceType\\\":\\\"Similarity\\\",\\\"ClusterQueryStartTime\\\":\\\"2024-10-11T00:00:00Z\\\",\\\"ClusterQueryEndTime\\\":\\\"2024-10-31T13:31:45.0302157Z\\\",\\\"ClusterGroup\\\":\\\"BodyFingerprintBin1,P2SenderDomain\\\",\\\"Type\\\":\\\"mailCluster\\\",\\\"ClusterBy\\\":\\\"BodyFingerprintBin1;P2SenderDomain;ContentType\\\",\\\"ClusterByValue\\\":\\\"2929356879;gmail.com;1\\\",\\\"QueryStartTime\\\":\\\"10/11/2024 12:00:00 AM\\\",\\\"QueryTime\\\":\\\"10/31/2024 1:31:45 PM\\\",\\\"Urn\\\":\\\"urn:MailClusterEntity:a5f65badbcbc2e3c6409625436363a29\\\",\\\"Source\\\":\\\"TestProvider\\\",\\\"FirstSeen\\\":\\\"2024-10-31T13:31:52\\\"},{\\\"$id\\\":\\\"12\\\",\\\"NetworkMessageIds\\\":[\\\"24b8430c-484d-4ee0-e12b-08dcee99416a\\\",\\\"2e99f39a-c998-4d94-2085-08dce9cd0b7d\\\",\\\"0ac4ee3c-7c79-408e-76c2-08dcf4106b65\\\",\\\"fd400540-8a8d-42ae-d1f9-08dced20c42f\\\",\\\"31cfca73-f309-4e21-cbc4-08dceed074cf\\\",\\\"0491b33a-15fc-4503-9dd1-08dced818f57\\\",\\\"4b620244-917b-4a04-7416-08dcf50af378\\\",\\\"1abed68d-3b03-46bd-45e2-08dcf43fb625\\\",\\\"abb4c4a5-7049-4047-5a68-08dcec201c1f\\\",\\\"92bba720-15bc-4f09-49f2-08dcf8d738a4\\\",\\\"3d511617-b717-416c-89cf-08dcf90a51c7\\\",\\\"c3ad4b6b-0fd9-4510-4481-08dcf9043502\\\",\\\"37b236bd-ad39-41c0-3984-08dcf85e6b44\\\",\\\"a1d9684c-9982-4f80-880c-08dcf775c1a9\\\"],\\\"CountByThreatType\\\":{\\\"HighConfPhish\\\":5,\\\"Phish\\\":0,\\\"Malware\\\":0,\\\"Spam\\\":0,\\\"MaliciousUrl\\\":15},\\\"CountByProtectionStatus\\\":{\\\"Delivered\\\":10,\\\"Blocked\\\":4,\\\"DeliveredAsSpam\\\":1},\\\"CountByDeliveryLocation\\\":{\\\"Inbox\\\":10,\\\"Quarantine\\\":4,\\\"DeletedFolder\\\":1},\\\"Query\\\":\\\"( ((NormalizedUrl:\\\\\\\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en\\\\\\\") AND (ContentType: 1)) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\\\",\\\"QueryTime\\\":\\\"2024-10-31T13:31:54.2957192Z\\\",\\\"MailCount\\\":15,\\\"IsVolumeAnamoly\\\":false,\\\"ClusterSourceIdentifier\\\":\\\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en\\\",\\\"ClusterSourceType\\\":\\\"UrlThreatIndicator\\\",\\\"ClusterQueryStartTime\\\":\\\"2024-10-11T00:00:00Z\\\",\\\"ClusterQueryEndTime\\\":\\\"2024-10-31T13:31:54.2957192Z\\\",\\\"ClusterGroup\\\":\\\"UrlThreatIdentifier\\\",\\\"Type\\\":\\\"mailCluster\\\",\\\"ClusterBy\\\":\\\"NormalizedUrl;ContentType\\\",\\\"ClusterByValue\\\":\\\"https://play.google.com/store/apps/details?id=com.zzkko&hl=en;1\\\",\\\"QueryStartTime\\\":\\\"10/11/2024 12:00:00 AM\\\",\\\"QueryTime\\\":\\\"10/31/2024 1:31:54 PM\\\",\\\"Urn\\\":\\\"urn:MailClusterEntity:cae0ce4483385c4ff176b00a0cd18f8e\\\",\\\"Source\\\":\\\"TestProvider\\\",\\\"FirstSeen\\\":\\\"2024-10-31T13:31:56\\\"}],\\\"LogCreationTime\\\":\\\"2024-10-31T15:28:45.1030022Z\\\",\\\"MachineName\\\":\\\"MachineNameTest\\\",\\\"SourceTemplateType\\\":\\\"Threat_Single\\\",\\\"Category\\\":\\\"ThreatManagement\\\",\\\"SourceAlertType\\\":\\\"System\\\"}\",\"DeepLinkUrl\":\"https://security.microsoft.com/mtp-investigation/urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101\",\"EndTimeUtc\":\"2024-10-31T15:26:49\",\"InvestigationId\":\"urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101\",\"InvestigationName\":\"Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101\",\"InvestigationType\":\"ZappedUrlInvestigation\",\"LastUpdateTimeUtc\":\"2024-10-31T12:59:19\",\"RunningTime\":9022,\"StartTimeUtc\":\"2024-10-31T12:58:22\",\"Status\":\"Pending Action\"}",
"event": {
"action": "AirInvestigationData",
"code": "64",
"end": "2024-10-31T15:26:49Z",
"kind": "event",
"outcome": "success",
"start": "2024-10-31T12:58:22Z"
},
"@timestamp": "2024-10-31T16:24:41Z",
"action": {
"id": 64,
"name": "AirInvestigationData",
"outcome": "success",
"target": "user"
},
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "returnLabel_314378736750.pdf"
}
}
],
"from": {
"address": [
"test.sender@example.com"
]
},
"to": {
"address": [
"test.to@example.com"
]
}
},
"log": {
"level": "Informational"
},
"office365": {
"audit": {
"object_id": "c3ebef20-fb63-4d14-b3c1-7bfb5937903a"
},
"investigation": {
"alert": {
"category": "ThreatManagement",
"correlation_key": "bb0ac18c-5081-41e0-8656-f256ba9298d0",
"is_incident": false,
"provider": {
"name": "TestProvider",
"status": "InProgress"
},
"severity": "Informational",
"source_type": "System",
"type": "8e6ba277-ef39-404e-aaf1-294f6d9a2b88",
"urls": [
"https://security.microsoft.com/alerts/fafff21c13-c681-7398-1200-08dcf8958252"
]
},
"delivery": {
"action": [
"Blocked"
]
},
"email": {
"sender": {
"domains": [
"gmail.com"
],
"ip": [
"1.2.3.4"
]
},
"subjects": [
"Fwd: Votre \u00e9tiquette de retour de SHEIN"
],
"urls": [
"http://shein.ltwebstatic.com/advertise/shein/www/images_sheIn/SheIn_logo1_1.png",
"https://fr.shein.com/",
"https://fr.shein.com/robot",
"https://fr.shein.com/user/order_return/order_return_label/GSONEQ62U001GKT?country=France&refund_bill_id=&return_order_id=NE91E0E8C1",
"https://itunes.apple.com/us/app/yub-streetwear-fashion-shopping/id878577184?mt=8",
"https://play.google.com/store/apps/details?id=com.zzkko&hl=en",
"https://romwe.ltwebstatic.com/advertise/romwe/www/images_Romwe/edm3_09_2.jpg",
"https://romwe.ltwebstatic.com/advertise/romwe/www/images_Romwe/edm3_11_1.jpg",
"https://subexample.example.net/?REDACTED",
"https://u25492214.ct.example.net/ls/click?upn=u001.Ni9F2bUzMGygU7I6927xz-2B7I3RFKjR2LTj-2FCdqvCgUA-3De-zv_r5YCKD565fWzehHx-2FViuB8oHOL1DYwg-2Bfx4BUmzkfTPes7sa-2BVi-2BqS9kcdV08lhzTrs-2B4Lvsupi32g3cG4FINnNbknV9eEzYIqgaa4YfaZHEEHRVUWDqycf8mgAbrzvtnOX7pQHdt3iR6DHP-2BxR3PfnH-2BDzIJZkv1MK0yzBmp6otxpVGSalyLT-2BMyMS7yEfvbLbY9v9Wjn3hkHG29S-2FBOFjoVX-2FSwv2kZeymJW-2FlgRvHCB20rH0kwYqIdOsdO-2FvuCq-2BU49-2FNEo4S2gaZRd0h3zn5MFhXxj-2F-2FbW3X5gOaGP7-2FpGN-2BX-2BHRi1Xt1JzFgCpA",
"https://u25492214.ct.example.net/ls/click?upn=u001.Ni9F2bUzMGygU7I6927xz1dNl4cyoCqQhbWGcqggHJW8SDLFVls-2FdSGWRn2n26uXgiSb-2FLZ3Oc-2F6taFyBHXTJv-2BdvE0YkDtEsaWUVnnpz7Lus9fp2MjvsYOqibyuC9Sjzgm4flo2XfvY4y5mBWuQF-2F7nM55pZ5S6S-2BSuNa5j-2BID5HJzdZOlXc2nyvbxmDFrTDuau_r5YCKD565fWzehHx-2FViuB8oHOL1DYwg-2Bfx4BUmzkfTPes7sa-2BVi-2BqS9kcdV08lhzTrs-2B4Lvsupi32g3cG4FINnNbknV9eEzYIqgaa4YfaZHEEHRVUWDqycf8mgAbrzvtnOX7pQHdt3iR6DHP-2BxR3PfnH-2BDzIJZkv1MK0yzBmp6oCyme2zPY6GKJBwI7FWZYrXhePHLdzV5WL-2F5EJubwqlYflj1CI9yL7Xfb24ks7WDE2wa8hQ-2BQ3h8K7-2FNpWkzEtiEQPiPEF3zOMzaOlqjkbPLg0UzpEmObjky1BycKoXMMwtfEuHLB9VnhNmDV3aIW2",
"https://u25492214.ct.example.net/ls/click?upn=u001.Ni9F2bUzMGygU7I6927xz49R6-2B-2FASLo-2BUtlyP-2F4iSjQlm-2F4HWFki90oq-2Bc29Sr-2BJAxlu_r5YCKD565fWzehHx-2FViuB8oHOL1DYwg-2Bfx4BUmzkfTPes7sa-2BVi-2BqS9kcdV08lhzTrs-2B4Lvsupi32g3cG4FINnNbknV9eEzYIqgaa4YfaZHEEHRVUWDqycf8mgAbrzvtnOX7pQHdt3iR6DHP-2BxR3PfnH-2BDzIJZkv1MK0yzBmp6qR2GRWjTyLjKHBwmcXgTV-2BMq0R5qnuDMHYAbrFxAmtHiepp1aU8L-2FOCt-2BiboZksoqBfuo-2FcqBrfi9un8ILJByRUOZM3T6alRzsB1jmdLOKOZwr3m8kymuz3dFvNya6aYPmSZG4l57ycCGBya5xMMqf",
"https://u25492214.ct.example.net/ls/click?upn=u001.Ni9F2bUzMGygU7I6927xzwS57HzRFV06M2bzMBaRY-2BtdD2HhGOqR6HD9j7eU3woqib3lW0qFsRIYtEfnDRINtIJErjGpQG2ad3jjAbAIacwJ4Le0eScR4TY1ExyusbvGQU5p_r5YCKD565fWzehHx-2FViuB8oHOL1DYwg-2Bfx4BUmzkfTPes7sa-2BVi-2BqS9kcdV08lhzTrs-2B4Lvsupi32g3cG4FINnNbknV9eEzYIqgaa4YfaZHEEHRVUWDqycf8mgAbrzvtnOX7pQHdt3iR6DHP-2BxR3PfnH-2BDzIJZkv1MK0yzBmp6psejQMn2EzritsHjoZX3rBM6GN1Gt7OeDjl2fzK-2BAK5-2FzHIjoTmyFKIkBvxn4mrKqstgF5tkhF6rc-2BIL2TqH7FTpqHdxk6lMOLfZVS4DrhiP-2FvyHZwSo2RzY-2BDmTRvcBEOqOwutpZKgr0m7fArTF-2Fv"
]
},
"emails": [
{
"message_ids": [
"24b8430c-484d-4ee0-e12b-08dcee99416a",
"2e99f39a-c998-4d94-2085-08dce9cd0b7d",
"0ac4ee3c-7c79-408e-76c2-08dcf4106b65",
"fd400540-8a8d-42ae-d1f9-08dced20c42f",
"31cfca73-f309-4e21-cbc4-08dceed074cf",
"0491b33a-15fc-4503-9dd1-08dced818f57",
"4b620244-917b-4a04-7416-08dcf50af378",
"1abed68d-3b03-46bd-45e2-08dcf43fb625",
"abb4c4a5-7049-4047-5a68-08dcec201c1f",
"92bba720-15bc-4f09-49f2-08dcf8d738a4",
"3d511617-b717-416c-89cf-08dcf90a51c7",
"c3ad4b6b-0fd9-4510-4481-08dcf9043502",
"37b236bd-ad39-41c0-3984-08dcf85e6b44",
"a1d9684c-9982-4f80-880c-08dcf775c1a9"
]
},
{
"message_ids": [
"37b236bd-ad39-41c0-3984-08dcf85e6b44"
]
},
{
"delivery": {
"action": "Blocked",
"location": "Quarantine",
"original_location": "Inbox"
},
"direction": "Inbound",
"language": "fr",
"message_ids": [
"37b236bd-ad39-41c0-3984-08dcf85e6b44"
]
}
],
"id": "urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101",
"name": "Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:611e72a0f8dc10fecbf6fc017c51d101",
"status": "Pending Action",
"threats": [
"HighConfPhish",
"ZapPhish"
],
"type": "ZappedUrlInvestigation"
},
"machine_name": "MachineNameTest",
"record_id": "c3ebef20-fb63-4d14-b3c1-7bfb5937903a",
"record_type": 64,
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"rule": {
"name": "Email messages containing malicious URL removed after delivery\u200b"
},
"service": {
"name": "user1"
},
"threat": {
"enrichments": [
{
"indicator": {
"first_seen": "2024-10-31T12:58:53Z",
"provider": "TestProvider",
"url": {
"full": "https://play.google.com/store/apps/details?id=com.zzkko&hl=en"
}
}
},
{
"indicator": {
"email": {
"address": "test.to@example.com"
},
"first_seen": "2024-10-31T12:58:53Z",
"ip": "1.2.3.4",
"provider": "TestProvider"
}
}
]
},
"url": {
"domain": "subexample.example.net",
"full": "https://subexample.example.net/?REDACTED",
"original": "https://subexample.example.net/?REDACTED",
"path": "/",
"port": 443,
"query": "REDACTED",
"registered_domain": "example.net",
"scheme": "https",
"subdomain": "subexample",
"top_level_domain": "net"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2025-02-04T09:15:18\",\"Id\":\"11111111-1111-1111-1111-111111111111\",\"Operation\":\"AirInvestigationData\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":64,\"UserKey\":\"user1\",\"UserType\":4,\"Version\":1,\"Workload\":\"user1\",\"ObjectId\":\"11111111-1111-1111-1111-111111111111\",\"UserId\":\"user1\",\"Actions\":[\"{\\\"$id\\\":\\\"1\\\",\\\"ActionId\\\":\\\"urn:EmailZapper:06ba299975c56e191a2d4b8bf98c921a\\\",\\\"InvestigationId\\\":\\\"urn:UrlVerdictChangeInvestig:ef7ff0b054c22025f22f6f4416f75cc0\\\",\\\"ActionApproval\\\":\\\"None\\\",\\\"ActionType\\\":\\\"EmailRemediation\\\",\\\"ActionStatus\\\":\\\"Pending\\\",\\\"Entities\\\":[{\\\"$id\\\":\\\"2\\\",\\\"NetworkMessageIds\\\":[\\\"33333333-3333-3333-3333-333333333333\\\"],\\\"CountByThreatType\\\":{\\\"HighConfPhish\\\":0,\\\"Phish\\\":0,\\\"Malware\\\":0,\\\"Spam\\\":1,\\\"MaliciousUrl\\\":1},\\\"CountByProtectionStatus\\\":{\\\"Delivered\\\":1},\\\"CountByDeliveryLocation\\\":{\\\"Inbox\\\":1},\\\"Query\\\":\\\"( ((NormalizedUrl:\\\\\\\"https://www.test.com.tr/2025%20inquiry.js\\\\\\\") AND (ContentType: 1)) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\\\",\\\"QueryTime\\\":\\\"2025-02-04T08:36:24.0457384Z\\\",\\\"MailCount\\\":1,\\\"IsVolumeAnamoly\\\":false,\\\"ClusterSourceIdentifier\\\":\\\"https://www.test.com.tr/2025%20inquiry.js\\\",\\\"ClusterSourceType\\\":\\\"UrlThreatIndicator\\\",\\\"ClusterQueryStartTime\\\":\\\"2025-01-15T00:00:00Z\\\",\\\"ClusterQueryEndTime\\\":\\\"2025-02-04T08:36:24.0457384Z\\\",\\\"ClusterGroup\\\":\\\"UrlThreatIdentifier\\\",\\\"Type\\\":\\\"mailCluster\\\",\\\"ClusterBy\\\":\\\"NormalizedUrl;ContentType\\\",\\\"ClusterByValue\\\":\\\"https://www.test.com.tr/2025%20inquiry.js;1\\\",\\\"QueryStartTime\\\":\\\"1/15/2025 12:00:00 AM\\\",\\\"QueryTime\\\":\\\"2/4/2025 8:36:24 AM\\\",\\\"Urn\\\":\\\"urn:MailClusterEntity:7e75296cf6667565c1af6a8d4239c5e5\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"2025-02-04T08:36:27\\\"}],\\\"RelatedAlertIds\\\":[\\\"44444444-4444-4444-4444-444444444444\\\"],\\\"StartTimeUtc\\\":\\\"2025-02-04T08:37:47\\\",\\\"LastUpdateTimeUtc\\\":\\\"2025-02-04T09:15:17.5752228Z\\\",\\\"TimestampUtc\\\":\\\"2025-02-04T08:37:47\\\",\\\"BulkName\\\":\\\"Clicked url Verdict changed to malicious - https://www.test.com.tr/2025%20inquiry.js\\\",\\\"ResourceIdentifiers\\\":[{\\\"$id\\\":\\\"3\\\",\\\"AadTenantId\\\":\\\"22222222-2222-2222-2222-222222222222\\\",\\\"Type\\\":\\\"AAD\\\"}],\\\"PendingType\\\":\\\"User\\\",\\\"LogCreationTime\\\":\\\"2025-02-04T09:15:17.5752228Z\\\",\\\"MachineName\\\":\\\"PC01\\\",\\\"Description\\\":\\\"For malicious emails, you can move to junk, soft or hard delete from user's mailbox.\\\"}\"],\"Data\":\"{\\\"Version\\\":\\\"3.0\\\",\\\"VendorName\\\":\\\"Microsoft\\\",\\\"ProviderName\\\":\\\"OATP\\\",\\\"AlertType\\\":\\\"55555555-5555-5555-5555-555555555555\\\",\\\"StartTimeUtc\\\":\\\"2025-02-04T08:28:33.4393685Z\\\",\\\"EndTimeUtc\\\":\\\"2025-02-04T08:28:33.4393685Z\\\",\\\"TimeGenerated\\\":\\\"2025-02-04T08:29:16.4466667Z\\\",\\\"ProcessingEndTime\\\":\\\"2025-02-04T09:15:17.5752228Z\\\",\\\"Status\\\":\\\"InProgress\\\",\\\"Severity\\\":\\\"High\\\",\\\"ConfidenceLevel\\\":\\\"Unknown\\\",\\\"ConfidenceScore\\\":1.0,\\\"IsIncident\\\":false,\\\"ProviderAlertId\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"SystemAlertId\\\":null,\\\"CorrelationKey\\\":\\\"66666666-6666-6666-6666-666666666666\\\",\\\"Investigations\\\":[{\\\"$id\\\":\\\"1\\\",\\\"Id\\\":\\\"urn:UrlVerdictChangeInvestig:ef7ff0b054c22025f22f6f4416f75cc0\\\",\\\"InvestigationStatus\\\":\\\"Pending\\\"}],\\\"InvestigationIds\\\":[\\\"urn:UrlVerdictChangeInvestig:ef7ff0b054c22025f22f6f4416f75cc0\\\"],\\\"Intent\\\":\\\"Probing\\\",\\\"ResourceIdentifiers\\\":[{\\\"$id\\\":\\\"2\\\",\\\"AadTenantId\\\":\\\"22222222-2222-2222-2222-222222222222\\\",\\\"Type\\\":\\\"AAD\\\"}],\\\"AzureResourceId\\\":null,\\\"WorkspaceId\\\":null,\\\"WorkspaceSubscriptionId\\\":null,\\\"WorkspaceResourceGroup\\\":null,\\\"AgentId\\\":null,\\\"AlertDisplayName\\\":\\\"A potentially malicious URL click was detected\\\",\\\"Description\\\":\\\"We have detected that one of your users has recently clicked on a link that was found to be malicious. -V1.0.0.5\\\",\\\"ExtendedLinks\\\":[{\\\"Href\\\":\\\"https://security.microsoft.com/alerts/fa44444444-4444-4444-4444-444444444444\\\",\\\"Category\\\":null,\\\"Label\\\":\\\"alert\\\",\\\"Type\\\":\\\"webLink\\\"}],\\\"Metadata\\\":{\\\"CustomApps\\\":null,\\\"GenericInfo\\\":null},\\\"Entities\\\":[{\\\"$id\\\":\\\"3\\\",\\\"MailboxPrimaryAddress\\\":\\\"john.doe@company.eu\\\",\\\"Upn\\\":\\\"John.DOE@company.eu\\\",\\\"AadId\\\":\\\"77777777-7777-7777-7777-777777777777\\\",\\\"RiskLevel\\\":\\\"Low\\\",\\\"Type\\\":\\\"mailbox\\\",\\\"Urn\\\":\\\"urn:UserEntity:c15ba52dfdd0d0b80095eb906ee7c9d6\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"2025-02-04T08:33:58\\\"},{\\\"$id\\\":\\\"4\\\",\\\"Url\\\":\\\"https://www.test.com.tr/2025%20inquiry.js\\\",\\\"Type\\\":\\\"url\\\",\\\"Urn\\\":\\\"urn:UrlEntity:b1fbd9f06eb20489f88f83ac7cea7867\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"2025-02-04T08:33:58\\\"},{\\\"$id\\\":\\\"5\\\",\\\"NetworkMessageIds\\\":[\\\"33333333-3333-3333-3333-333333333333\\\"],\\\"CountByThreatType\\\":{\\\"HighConfPhish\\\":0,\\\"Phish\\\":0,\\\"Malware\\\":0,\\\"Spam\\\":1,\\\"MaliciousUrl\\\":1},\\\"CountByProtectionStatus\\\":{\\\"Delivered\\\":1},\\\"CountByDeliveryLocation\\\":{\\\"Inbox\\\":1},\\\"Query\\\":\\\"( ((NormalizedUrl:\\\\\\\"https://www.test.com.tr/2025%20inquiry.js\\\\\\\") AND (ContentType: 1)) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\\\",\\\"QueryTime\\\":\\\"2025-02-04T08:36:24.0457384Z\\\",\\\"MailCount\\\":1,\\\"IsVolumeAnamoly\\\":false,\\\"ClusterSourceIdentifier\\\":\\\"https://www.test.com.tr/2025%20inquiry.js\\\",\\\"ClusterSourceType\\\":\\\"UrlThreatIndicator\\\",\\\"ClusterQueryStartTime\\\":\\\"2025-01-15T00:00:00Z\\\",\\\"ClusterQueryEndTime\\\":\\\"2025-02-04T08:36:24.0457384Z\\\",\\\"ClusterGroup\\\":\\\"UrlThreatIdentifier\\\",\\\"Type\\\":\\\"mailCluster\\\",\\\"ClusterBy\\\":\\\"NormalizedUrl;ContentType\\\",\\\"ClusterByValue\\\":\\\"https://www.test.com.tr/2025%20inquiry.js;1\\\",\\\"QueryStartTime\\\":\\\"1/15/2025 12:00:00 AM\\\",\\\"QueryTime\\\":\\\"2/4/2025 8:36:24 AM\\\",\\\"Urn\\\":\\\"urn:MailClusterEntity:7e75296cf6667565c1af6a8d4239c5e5\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"2025-02-04T08:36:27\\\"}],\\\"LogCreationTime\\\":\\\"2025-02-04T09:15:17.5752228Z\\\",\\\"MachineName\\\":\\\"PC01\\\",\\\"SourceTemplateType\\\":\\\"MaliciousUrlClick_Single\\\",\\\"Category\\\":\\\"ThreatManagement\\\",\\\"SourceAlertType\\\":\\\"System\\\"}\",\"DeepLinkUrl\":\"https://security.microsoft.com/mtp-investigation/urn:UrlVerdictChangeInvestig:ef7ff0b054c22025f22f6f4416f75cc0\",\"EndTimeUtc\":\"2025-02-04T09:15:17\",\"InvestigationId\":\"urn:UrlVerdictChangeInvestig:ef7ff0b054c22025f22f6f4416f75cc0\",\"InvestigationName\":\"Clicked url Verdict changed to malicious - https://www.test.com.tr/2025%20inquiry.js\",\"InvestigationType\":\"UrlVerdictChangeInvestigation\",\"LastUpdateTimeUtc\":\"2025-02-04T09:04:57\",\"RunningTime\":2478,\"StartTimeUtc\":\"2025-02-04T08:33:58\",\"Status\":\"Pending Action\"}",
"event": {
"action": "AirInvestigationData",
"code": "64",
"end": "2025-02-04T09:15:17Z",
"kind": "event",
"outcome": "success",
"start": "2025-02-04T08:33:58Z"
},
"@timestamp": "2025-02-04T09:15:18Z",
"action": {
"id": 64,
"name": "AirInvestigationData",
"outcome": "success",
"target": "user"
},
"email": {
"to": {
"address": [
"john.doe@company.eu"
]
}
},
"log": {
"level": "High"
},
"office365": {
"audit": {
"object_id": "11111111-1111-1111-1111-111111111111"
},
"investigation": {
"alert": {
"category": "ThreatManagement",
"correlation_key": "66666666-6666-6666-6666-666666666666",
"is_incident": false,
"provider": {
"name": "OATP",
"status": "InProgress"
},
"severity": "High",
"source_type": "System",
"type": "55555555-5555-5555-5555-555555555555",
"urls": [
"https://security.microsoft.com/alerts/fa44444444-4444-4444-4444-444444444444"
]
},
"emails": [
{
"message_ids": [
"33333333-3333-3333-3333-333333333333"
]
}
],
"id": "urn:UrlVerdictChangeInvestig:ef7ff0b054c22025f22f6f4416f75cc0",
"name": "Clicked url Verdict changed to malicious - https://www.test.com.tr/2025%20inquiry.js",
"status": "Pending Action",
"type": "UrlVerdictChangeInvestigation"
},
"machine_name": "PC01",
"record_id": "11111111-1111-1111-1111-111111111111",
"record_type": 64,
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"rule": {
"name": "A potentially malicious URL click was detected"
},
"service": {
"name": "user1"
},
"threat": {
"enrichments": [
{
"indicator": {
"first_seen": "2025-02-04T08:33:58Z",
"provider": "OATP",
"url": {
"full": "https://www.test.com.tr/2025%20inquiry.js"
}
}
}
]
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"InvestigationId\":\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"InvestigationName\":\"URL verdict changed to malicious - urn:UrlVerdictChangeInvestig:11111111111111111111111111111111.\",\"InvestigationType\":\"UrlVerdictChangeInvestigation\",\"Status\":\"Remediated\",\"StartTimeUtc\":\"2026-04-14T09:28:21\",\"EndTimeUtc\":\"2026-04-14T11:28:37\",\"LastUpdateTimeUtc\":\"2026-04-14T11:28:37\",\"RunningTime\":7215,\"DeepLinkUrl\":\"https://security.microsoft.com/mtp-investigation/urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\",\"Data\":\"{\\\"$id\\\":\\\"1\\\",\\\"Version\\\":\\\"3.0\\\",\\\"VendorName\\\":\\\"Microsoft\\\",\\\"ProviderName\\\":\\\"OATP\\\",\\\"AlertType\\\":\\\"11111111-1111-1111-1111-111111111111\\\",\\\"StartTimeUtc\\\":\\\"2026-04-14T09:18:25Z\\\",\\\"EndTimeUtc\\\":\\\"2026-04-14T09:18:25Z\\\",\\\"TimeGenerated\\\":\\\"2026-04-14T09:25:03.39Z\\\",\\\"ProcessingEndTime\\\":\\\"2026-04-14T09:28:20.3493656Z\\\",\\\"Status\\\":\\\"New\\\",\\\"Severity\\\":\\\"High\\\",\\\"ConfidenceScore\\\":1.0,\\\"IsIncident\\\":false,\\\"ProviderAlertId\\\":\\\"22222222-2222-2222-2222-222222222222\\\",\\\"SystemAlertId\\\":null,\\\"CorrelationKey\\\":\\\"33333333-3333-3333-3333-333333333333\\\",\\\"Intent\\\":\\\"Probing\\\",\\\"ResourceIdentifiers\\\":[{\\\"$id\\\":\\\"2\\\",\\\"AadTenantId\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"Type\\\":\\\"AAD\\\"}],\\\"AlertDisplayName\\\":\\\"A potentially malicious URL click was detected\\\",\\\"Description\\\":\\\"We have detected that one of your users has recently clicked on a link that was found to be malicious. -V1.0.0.5\\\",\\\"ExtendedLinks\\\":[{\\\"Href\\\":\\\"https://security.microsoft.com/alerts/fa22222222-2222-2222-2222-222222222222\\\",\\\"Category\\\":null,\\\"Label\\\":\\\"alert\\\",\\\"Type\\\":\\\"webLink\\\"}],\\\"AlertMetadata\\\":{\\\"CustomApps\\\":null,\\\"GenericInfo\\\":null},\\\"Entities\\\":[{\\\"$id\\\":\\\"3\\\",\\\"Recipient\\\":\\\"usermail@company.fr\\\",\\\"SenderIP\\\":\\\"1.2.3.4\\\",\\\"ReceivedDate\\\":\\\"2026-04-14T07:15:45Z\\\",\\\"NetworkMessageId\\\":\\\"55555555-5555-5555-5555-555555555555\\\",\\\"StartTimeUtc\\\":\\\"2026-04-14T09:18:25Z\\\",\\\"EndTimeUtc\\\":\\\"2026-04-14T09:18:25Z\\\",\\\"Type\\\":\\\"mailMessage\\\",\\\"Urn\\\":null,\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"0001-01-01T00:00:00\\\",\\\"SourceEntityType\\\":\\\"MaliciousUrl\\\",\\\"SourceEntityId\\\":\\\"https://test.integration.com/?context=1111111111111111111111111\\\"},{\\\"$id\\\":\\\"4\\\",\\\"Address\\\":\\\"1.2.3.4\\\",\\\"StartTimeUtc\\\":\\\"2026-04-14T09:18:25Z\\\",\\\"EndTimeUtc\\\":\\\"2026-04-14T09:18:25Z\\\",\\\"Type\\\":\\\"ip\\\",\\\"Urn\\\":null,\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"0001-01-01T00:00:00\\\",\\\"SourceEntityType\\\":\\\"MaliciousUrl\\\",\\\"SourceEntityId\\\":\\\"https://test.integration.com/?context=1111111111111111111111111\\\"}],\\\"LogCreationTime\\\":\\\"2026-04-14T09:28:20.3493656Z\\\",\\\"MachineName\\\":\\\"PC01\\\",\\\"SourceTemplateType\\\":\\\"MaliciousUrlClick_Single\\\",\\\"Category\\\":\\\"ThreatManagement\\\",\\\"SourceAlertType\\\":\\\"System\\\",\\\"EventDateTime\\\":\\\"2026-04-14T09:18:25Z\\\",\\\"Operation\\\":\\\"MaliciousUrlClick\\\",\\\"Forest\\\":\\\"eur02\\\"}\",\"Actions\":[\"{\\\"Facts\\\":[{\\\"TagName\\\":\\\"ModernAirObject\\\",\\\"TagValue\\\":\\\"1\\\",\\\"FactStatus\\\":\\\"None\\\",\\\"id\\\":\\\"urn:ModernAirObject:1:22222222222222222222222222222222\\\",\\\"TenantId\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"InvestigationId\\\":\\\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\\\",\\\"ParentObjectId\\\":\\\"urn:MailClusterAnalyzer:33333333333333333333333333333333\\\",\\\"RelatedObjectId\\\":\\\"urn:MailClusterAnalyzer:33333333333333333333333333333333\\\",\\\"ObjectCreationTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"ObjectChangedTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"ExecutionCount\\\":0,\\\"ProcessingStartTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"ProcessingEndTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"DisplayName\\\":null,\\\"MalScore\\\":0,\\\"SubPartitionKey1\\\":null,\\\"SubPartitionKey2\\\":null,\\\"TimeToLiveInSeconds\\\":null,\\\"ContainerName\\\":null,\\\"PartitionKeyPaths\\\":[\\\"/partitionKey\\\"],\\\"PartitionKey\\\":null,\\\"Type\\\":null,\\\"ETag\\\":null,\\\"IsGCed\\\":false,\\\"ExtensionData\\\":null}],\\\"EntityUrn\\\":\\\"urn:MailEntityModel:44444444444444444444444444444444\\\",\\\"Disposition\\\":\\\"Analyzer\\\",\\\"ActionType\\\":\\\"MailClusterAnalyzer\\\",\\\"TimeoutForAction\\\":\\\"2026-04-14T09:33:25.3460101+00:00\\\",\\\"IsRecurringAction\\\":false,\\\"ActionStatus\\\":\\\"Complete\\\",\\\"PartitionKey\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"SubPartitionKey1\\\":\\\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\\\",\\\"id\\\":\\\"urn:MailClusterAnalyzer:33333333333333333333333333333333\\\",\\\"TenantId\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"InvestigationId\\\":\\\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\\\",\\\"ParentObjectId\\\":\\\"urn:MailEntityModel:44444444444444444444444444444444\\\",\\\"RelatedObjectId\\\":\\\"\\\",\\\"ObjectCreationTime\\\":\\\"2026-04-14T09:28:24.9626945Z\\\",\\\"ObjectChangedTime\\\":\\\"2026-04-14T09:28:26.3121569Z\\\",\\\"ExecutionCount\\\":0,\\\"ProcessingStartTime\\\":\\\"2026-04-14T09:28:25.4001066Z\\\",\\\"ProcessingEndTime\\\":\\\"2026-04-14T09:28:26.2465844Z\\\",\\\"DisplayName\\\":null,\\\"MalScore\\\":0,\\\"SubPartitionKey2\\\":null,\\\"TimeToLiveInSeconds\\\":null,\\\"Type\\\":null,\\\"ETag\\\":null,\\\"IsGCed\\\":false,\\\"ExtensionData\\\":null}\",\"{\\\"Facts\\\":[{\\\"TagName\\\":\\\"ModernAirObject\\\",\\\"TagValue\\\":\\\"1\\\",\\\"FactStatus\\\":\\\"None\\\",\\\"id\\\":\\\"urn:ModernAirObject:1:55555555555555555555555555555555\\\",\\\"TenantId\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"InvestigationId\\\":\\\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\\\",\\\"ParentObjectId\\\":\\\"urn:MailClusterAnalyzer:66666666666666666666666666666666\\\",\\\"RelatedObjectId\\\":\\\"urn:MailClusterAnalyzer:66666666666666666666666666666666\\\",\\\"ObjectCreationTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"ObjectChangedTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"ExecutionCount\\\":0,\\\"ProcessingStartTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"ProcessingEndTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"DisplayName\\\":null,\\\"MalScore\\\":0,\\\"SubPartitionKey1\\\":null,\\\"SubPartitionKey2\\\":null,\\\"TimeToLiveInSeconds\\\":null,\\\"ContainerName\\\":null,\\\"PartitionKeyPaths\\\":[\\\"/partitionKey\\\"],\\\"PartitionKey\\\":null,\\\"Type\\\":null,\\\"ETag\\\":null,\\\"IsGCed\\\":false,\\\"ExtensionData\\\":null}],\\\"EntityUrn\\\":\\\"urn:UrlEntityModel:77777777777777777777777777777777\\\",\\\"Disposition\\\":\\\"Analyzer\\\",\\\"ActionType\\\":\\\"MailClusterAnalyzer\\\",\\\"TimeoutForAction\\\":\\\"2026-04-14T09:33:25.1548139+00:00\\\",\\\"IsRecurringAction\\\":false,\\\"ActionStatus\\\":\\\"Complete\\\",\\\"PartitionKey\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"SubPartitionKey1\\\":\\\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\\\",\\\"id\\\":\\\"urn:MailClusterAnalyzer:66666666666666666666666666666666\\\",\\\"TenantId\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"InvestigationId\\\":\\\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\\\",\\\"ParentObjectId\\\":\\\"urn:UrlEntityModel:77777777777777777777777777777777\\\",\\\"RelatedObjectId\\\":\\\"\\\",\\\"ObjectCreationTime\\\":\\\"2026-04-14T09:28:25.0068659Z\\\",\\\"ObjectChangedTime\\\":\\\"2026-04-14T09:28:26.1005485Z\\\",\\\"ExecutionCount\\\":0,\\\"ProcessingStartTime\\\":\\\"2026-04-14T09:28:25.1979172Z\\\",\\\"ProcessingEndTime\\\":\\\"2026-04-14T09:28:26.0299557Z\\\",\\\"DisplayName\\\":null,\\\"MalScore\\\":0,\\\"SubPartitionKey2\\\":null,\\\"TimeToLiveInSeconds\\\":null,\\\"Type\\\":null,\\\"ETag\\\":null,\\\"IsGCed\\\":false,\\\"ExtensionData\\\":null}\",\"{\\\"TiInvestigationId\\\":\\\"\\\",\\\"TiRemediationId\\\":\\\"\\\",\\\"TiInvestigationName\\\":\\\"\\\",\\\"KqlString\\\":\\\"\\\",\\\"Facts\\\":[{\\\"TagName\\\":\\\"ModernAirObject\\\",\\\"TagValue\\\":\\\"1\\\",\\\"FactStatus\\\":\\\"None\\\",\\\"id\\\":\\\"urn:ModernAirObject:1:88888888888888888888888888888888\\\",\\\"TenantId\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"InvestigationId\\\":\\\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\\\",\\\"ParentObjectId\\\":\\\"urn:EmailZapperRemediation:33333333333333333333333333333333\\\",\\\"RelatedObjectId\\\":\\\"urn:EmailZapperRemediation:33333333333333333333333333333333\\\",\\\"ObjectCreationTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"ObjectChangedTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"ExecutionCount\\\":0,\\\"ProcessingStartTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"ProcessingEndTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"DisplayName\\\":null,\\\"MalScore\\\":0,\\\"SubPartitionKey1\\\":null,\\\"SubPartitionKey2\\\":null,\\\"TimeToLiveInSeconds\\\":null,\\\"ContainerName\\\":null,\\\"PartitionKeyPaths\\\":[\\\"/partitionKey\\\"],\\\"PartitionKey\\\":null,\\\"Type\\\":null,\\\"ETag\\\":null,\\\"IsGCed\\\":false,\\\"ExtensionData\\\":null}],\\\"EntityUrn\\\":\\\"urn:MailEntityModel:44444444444444444444444444444444\\\",\\\"Disposition\\\":\\\"Remediator\\\",\\\"ActionType\\\":\\\"EmailZapperRemediation\\\",\\\"TimeoutForAction\\\":\\\"2026-04-14T09:33:26.3168632+00:00\\\",\\\"IsRecurringAction\\\":false,\\\"ActionStatus\\\":\\\"Cancelled\\\",\\\"PartitionKey\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"SubPartitionKey1\\\":\\\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\\\",\\\"id\\\":\\\"urn:EmailZapperRemediation:33333333333333333333333333333333\\\",\\\"TenantId\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"InvestigationId\\\":\\\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\\\",\\\"ParentObjectId\\\":\\\"urn:MailEntityModel:44444444444444444444444444444444\\\",\\\"RelatedObjectId\\\":\\\"\\\",\\\"ObjectCreationTime\\\":\\\"2026-04-14T09:28:24.9626945Z\\\",\\\"ObjectChangedTime\\\":\\\"2026-04-14T09:28:26.3121569Z\\\",\\\"ExecutionCount\\\":0,\\\"ProcessingStartTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"ProcessingEndTime\\\":\\\"2026-04-14T11:28:36.8201365Z\\\",\\\"DisplayName\\\":null,\\\"MalScore\\\":0,\\\"SubPartitionKey2\\\":null,\\\"TimeToLiveInSeconds\\\":null,\\\"Type\\\":null,\\\"ETag\\\":null,\\\"IsGCed\\\":false,\\\"ExtensionData\\\":null}\",\"{\\\"Facts\\\":[{\\\"TagName\\\":\\\"ModernAirObject\\\",\\\"TagValue\\\":\\\"1\\\",\\\"FactStatus\\\":\\\"None\\\",\\\"id\\\":\\\"urn:ModernAirObject:1:99999999999999999999999999999999\\\",\\\"TenantId\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"InvestigationId\\\":\\\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\\\",\\\"ParentObjectId\\\":\\\"urn:MailRefreshAnalyzer:33333333333333333333333333333333\\\",\\\"RelatedObjectId\\\":\\\"urn:MailRefreshAnalyzer:33333333333333333333333333333333\\\",\\\"ObjectCreationTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"ObjectChangedTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"ExecutionCount\\\":0,\\\"ProcessingStartTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"ProcessingEndTime\\\":\\\"0001-01-01T00:00:00\\\",\\\"DisplayName\\\":null,\\\"MalScore\\\":0,\\\"SubPartitionKey1\\\":null,\\\"SubPartitionKey2\\\":null,\\\"TimeToLiveInSeconds\\\":null,\\\"ContainerName\\\":null,\\\"PartitionKeyPaths\\\":[\\\"/partitionKey\\\"],\\\"PartitionKey\\\":null,\\\"Type\\\":null,\\\"ETag\\\":null,\\\"IsGCed\\\":false,\\\"ExtensionData\\\":null}],\\\"EntityUrn\\\":\\\"urn:MailEntityModel:44444444444444444444444444444444\\\",\\\"Disposition\\\":\\\"Analyzer\\\",\\\"ActionType\\\":\\\"MailRefreshAnalyzer\\\",\\\"TimeoutForAction\\\":\\\"2026-04-14T09:33:27.4181556+00:00\\\",\\\"IsRecurringAction\\\":true,\\\"ActionStatus\\\":\\\"Complete\\\",\\\"PartitionKey\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"SubPartitionKey1\\\":\\\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\\\",\\\"id\\\":\\\"urn:MailRefreshAnalyzer:33333333333333333333333333333333\\\",\\\"TenantId\\\":\\\"44444444-4444-4444-4444-444444444444\\\",\\\"InvestigationId\\\":\\\"urn:UrlVerdictChangeInvestig:11111111111111111111111111111111\\\",\\\"ParentObjectId\\\":\\\"urn:MailEntityModel:44444444444444444444444444444444\\\",\\\"RelatedObjectId\\\":\\\"\\\",\\\"ObjectCreationTime\\\":\\\"2026-04-14T09:28:24.9626945Z\\\",\\\"ObjectChangedTime\\\":\\\"2026-04-14T09:28:26.3121569Z\\\",\\\"ExecutionCount\\\":0,\\\"ProcessingStartTime\\\":\\\"2026-04-14T11:28:31.8407962Z\\\",\\\"ProcessingEndTime\\\":\\\"2026-04-14T11:28:32.4217177Z\\\",\\\"DisplayName\\\":null,\\\"MalScore\\\":0,\\\"SubPartitionKey2\\\":null,\\\"TimeToLiveInSeconds\\\":null,\\\"Type\\\":null,\\\"ETag\\\":null,\\\"IsGCed\\\":false,\\\"ExtensionData\\\":null}\"],\"ObjectId\":\"aaaaaaaa-aaaa-aaaa-aaaaaaaaaaaa\",\"UserId\":\"AirInvestigation\",\"ClientIP\":null,\"Id\":\"bbbbbbbb-bbbb-bbbb-bbbb-bbbbbbbbbbbb\",\"RecordType\":64,\"CreationTime\":\"2026-04-14T11:28:39\",\"Operation\":\"AirInvestigationData\",\"OrganizationId\":\"44444444-4444-4444-4444-444444444444\",\"UserType\":4,\"UserKey\":\"AirInvestigation\",\"Workload\":\"AirInvestigation\",\"ResultStatus\":null,\"AppAccessContext\":null,\"AppIdentity\":null,\"AgentId\":null,\"AgentName\":null,\"CorrelationIdentity\":null,\"Version\":1,\"Scope\":0,\"Purpose\":0,\"RequiresCustomerKeyEncryption\":null,\"AssociatedAdminUnits\":null,\"ScopingEntityType\":0,\"ScopingEntityIds\":null}",
"event": {
"action": "AirInvestigationData",
"code": "64",
"end": "2026-04-14T11:28:37Z",
"kind": "event",
"outcome": "success",
"start": "2026-04-14T09:28:21Z"
},
"@timestamp": "2026-04-14T11:28:39Z",
"action": {
"id": 64,
"name": "AirInvestigationData",
"outcome": "success",
"target": "user"
},
"email": {
"to": {
"address": [
"usermail@company.fr"
]
}
},
"log": {
"level": "High"
},
"office365": {
"audit": {
"object_id": "aaaaaaaa-aaaa-aaaa-aaaaaaaaaaaa"
},
"investigation": {
"alert": {
"category": "ThreatManagement",
"correlation_key": "33333333-3333-3333-3333-333333333333",
"is_incident": false,
"provider": {
"name": "OATP",
"status": "New"
},
"severity": "High",
"source_type": "System",
"type": "11111111-1111-1111-1111-111111111111",
"urls": [
"https://security.microsoft.com/alerts/fa22222222-2222-2222-2222-222222222222"
]
},
"email": {
"sender": {
"ip": [
"1.2.3.4"
]
}
},
"emails": [
{
"message_ids": [
"55555555-5555-5555-5555-555555555555"
]
}
],
"id": "urn:UrlVerdictChangeInvestig:11111111111111111111111111111111",
"name": "URL verdict changed to malicious - urn:UrlVerdictChangeInvestig:11111111111111111111111111111111.",
"status": "Remediated",
"type": "UrlVerdictChangeInvestigation"
},
"machine_name": "PC01",
"record_id": "bbbbbbbb-bbbb-bbbb-bbbb-bbbbbbbbbbbb",
"record_type": 64,
"scope": {
"code": 0,
"name": "Online"
},
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "44444444-4444-4444-4444-444444444444"
},
"related": {
"user": [
"AirInvestigation"
]
},
"rule": {
"name": "A potentially malicious URL click was detected"
},
"service": {
"name": "AirInvestigation"
},
"threat": {
"enrichments": [
{
"indicator": {
"email": {
"address": "usermail@company.fr"
},
"first_seen": "0001-01-01T00:00:00Z",
"ip": "1.2.3.4",
"provider": "OATP",
"url": {
"full": "https://test.integration.com/?context=1111111111111111111111111"
}
}
},
{
"indicator": {
"first_seen": "0001-01-01T00:00:00Z",
"provider": "OATP",
"url": {
"full": "https://test.integration.com/?context=1111111111111111111111111"
}
}
}
]
},
"user": {
"id": "AirInvestigation",
"name": "AirInvestigation"
}
}
{
"message": "{\"CreationTime\":\"2023-04-17T14:27:09\",\"Id\":\"60eaf0aa-edc3-4f8d-8275-bc82d9500e59\",\"Operation\":\"AirInvestigationData\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":64,\"UserKey\":\"user1\",\"UserType\":4,\"Version\":1,\"Workload\":\"user1\",\"ObjectId\":\"60eaf0aa-edc3-4f8d-8275-bc82d9500e59\",\"UserId\":\"user1\",\"DeepLinkUrl\":\"https://security.microsoft.com/mtp-investigation/urn:ZappedUrlInvestigation:a10a976\",\"EndTimeUtc\":\"2023-04-17T14:27:07\",\"InvestigationId\":\"urn:ZappedUrlInvestigation:a10a976d-6e3e-4d10-be50-4907183b6f86\",\"InvestigationName\":\"Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:a1\",\"InvestigationType\":\"ZappedUrlInvestigation\",\"LastUpdateTimeUtc\":\"2023-04-17T14:21:59\",\"RunningTime\":931,\"StartTimeUtc\":\"2023-04-17T14:11:38\",\"Status\":\"Remediated\",\"Data\":\"{\\\"Version\\\":\\\"3.0\\\",\\\"VendorName\\\":\\\"Microsoft\\\",\\\"ProviderName\\\":\\\"OATP\\\",\\\"AlertType\\\":\\\"alert_type_value\\\",\\\"Status\\\":\\\"status_value\\\",\\\"Severity\\\":\\\"severity_value\\\",\\\"IsIncident\\\":true,\\\"CorrelationKey\\\":\\\"correlation_key_value\\\",\\\"Category\\\":\\\"category_value\\\",\\\"SourceAlertType\\\":\\\"source_alert_type_value\\\",\\\"MachineName\\\":\\\"machine_name_value\\\",\\\"Entities\\\": [{\\\"Urls\\\":[\\\"http://example.com\\\",\\\"http://1.2.3.5\\\"],\\\"SenderIP\\\":\\\"1.2.3.4\\\",\\\"Subject\\\":\\\"subject_value\\\",\\\"P1SenderDomain\\\":\\\"http://example.com\\\",\\\"Threats\\\":1,\\\"Sender\\\":\\\"test@test.test\\\",\\\"Recipient\\\":\\\"user1@example.com\\\"},{\\\"Urls\\\":[\\\"http://1.2.3.6\\\",\\\"http://1.2.3.7\\\"],\\\"SenderIP\\\":\\\"1.2.3.8\\\",\\\"Subject\\\":\\\"subject_value_1\\\",\\\"P1SenderDomain\\\":\\\"http://1.2.3.9\\\",\\\"Threats\\\":2,\\\"Sender\\\":\\\"user3@example.com\\\",\\\"Recipient\\\":\\\"user4@example.com\\\"}]}\",\"Actions\":[\"{\\\"$id\\\":\\\"1\\\",\\\"ActionId\\\":\\\"urn:EmailZapper:8ad9417586e14790ba2afed0a7840e65\\\"}\"]}",
"event": {
"action": "AirInvestigationData",
"code": "64",
"end": "2023-04-17T14:27:07Z",
"kind": "alert",
"outcome": "success",
"start": "2023-04-17T14:11:38Z"
},
"@timestamp": "2023-04-17T14:27:09Z",
"action": {
"id": 64,
"name": "AirInvestigationData",
"outcome": "success",
"target": "user"
},
"email": {
"from": {
"address": [
"test@test.test",
"user3@example.com"
]
},
"to": {
"address": [
"user1@example.com",
"user4@example.com"
]
}
},
"log": {
"level": "severity_value"
},
"office365": {
"audit": {
"object_id": "60eaf0aa-edc3-4f8d-8275-bc82d9500e59"
},
"investigation": {
"alert": {
"category": "category_value",
"correlation_key": "correlation_key_value",
"is_incident": true,
"provider": {
"name": "OATP",
"status": "status_value"
},
"severity": "severity_value",
"source_type": "source_alert_type_value",
"type": "alert_type_value"
},
"email": {
"sender": {
"domains": [
"http://1.2.3.9",
"http://example.com"
],
"ip": [
"1.2.3.4",
"1.2.3.8"
]
},
"subjects": [
"subject_value",
"subject_value_1"
],
"urls": [
"http://1.2.3.5",
"http://1.2.3.6",
"http://1.2.3.7",
"http://example.com"
]
},
"emails": [],
"id": "urn:ZappedUrlInvestigation:a10a976d-6e3e-4d10-be50-4907183b6f86",
"name": "Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:a1",
"status": "Remediated",
"threats": [
"1",
"2"
],
"type": "ZappedUrlInvestigation"
},
"machine_name": "machine_name_value",
"record_id": "60eaf0aa-edc3-4f8d-8275-bc82d9500e59",
"record_type": 64,
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"service": {
"name": "user1"
},
"url": {
"domain": "example.com",
"full": "http://example.com",
"original": "http://example.com",
"port": 80,
"registered_domain": "example.com",
"scheme": "http",
"top_level_domain": "com"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2024-09-02T03:33:37\",\"Id\":\"1234ab56-7890-1234-c5de-678fabcd9012\",\"Operation\":\"AirInvestigationData\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":64,\"UserKey\":\"user1\",\"UserType\":4,\"Version\":1,\"Workload\":\"user1\",\"ObjectId\":\"1234ab56-7890-1234-c5de-678fabcd9012\",\"UserId\":\"user1\",\"Actions\":[\"{\\\"$id\\\":\\\"1\\\",\\\"ActionId\\\":\\\"urn:EmailZapper:12345a6789bc01de23456f789ab0\\\",\\\"InvestigationId\\\":\\\"urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\\\",\\\"ActionApproval\\\":\\\"None\\\",\\\"ActionType\\\":\\\"EmailRemediation\\\",\\\"ActionStatus\\\":\\\"Pending\\\",\\\"Entities\\\":[{\\\"$id\\\":\\\"2\\\",\\\"Recipient\\\":\\\"user@example.net\\\",\\\"Urls\\\":[\\\"https://example.net/TUZAu6VrAvQT\\\",\\\"https://website.net/up/24/35/image.png\\\"],\\\"Threats\\\":[\\\"ZapPhish\\\",\\\"NormalPhish\\\"],\\\"Sender\\\":\\\"user1@test.example.com\\\",\\\"P1Sender\\\":\\\"p1user1@test.example.com\\\",\\\"P1SenderDomain\\\":\\\"test.integration.com\\\",\\\"SenderIP\\\":\\\"1.2.3.4\\\",\\\"P2Sender\\\":\\\"user1@test.example.com\\\",\\\"P2SenderDisplayName\\\":\\\"P2 name\\\",\\\"P2SenderDomain\\\":\\\"test.integration.com\\\",\\\"ReceivedDate\\\":\\\"2024-09-02T02:43:12\\\",\\\"NetworkMessageId\\\":\\\"ab12cde3-f456-789a-01bc-23defa4bc5d\\\",\\\"InternetMessageId\\\":\\\"<message.id.test@0123456789.userabc.mail.com>\\\",\\\"Subject\\\":\\\"Subject of the mail\\\",\\\"AntispamDirection\\\":\\\"Inbound\\\",\\\"DeliveryAction\\\":\\\"DeliveredAsSpam\\\",\\\"ThreatDetectionMethods\\\":[\\\"FingerPrintMatch\\\"],\\\"Language\\\":\\\"en\\\",\\\"DeliveryLocation\\\":\\\"JunkFolder\\\",\\\"OriginalDeliveryLocation\\\":\\\"Inbox\\\",\\\"AdditionalActionsAndResults\\\":[\\\"OriginalDelivery: [N/A]\\\",\\\"Zap: [Success: Message moved]\\\"],\\\"AuthDetails\\\":[{\\\"Name\\\":\\\"SPF\\\",\\\"Value\\\":\\\"Pass\\\"},{\\\"Name\\\":\\\"DKIM\\\",\\\"Value\\\":\\\"None\\\"},{\\\"Name\\\":\\\"DMARC\\\",\\\"Value\\\":\\\"Best guess pass\\\"},{\\\"Name\\\":\\\"Comp Auth\\\",\\\"Value\\\":\\\"pass\\\"}],\\\"SystemOverrides\\\":[],\\\"Type\\\":\\\"mailMessage\\\",\\\"Urn\\\":\\\"urn:MailEntity:01abc23d456efa7bc8901234d5efa67b\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"2024-09-02T03:20:40\\\"}],\\\"RelatedAlertIds\\\":[\\\"01234567-89a0-1234-5b67-89cdefa0b12\\\"],\\\"StartTimeUtc\\\":\\\"2024-09-02T03:27:33\\\",\\\"LastUpdateTimeUtc\\\":\\\"2024-09-02T03:33:31.8137435Z\\\",\\\"TimestampUtc\\\":\\\"2024-09-02T03:27:33\\\",\\\"BulkName\\\":\\\"Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\\\",\\\"ResourceIdentifiers\\\":[{\\\"$id\\\":\\\"3\\\",\\\"AadTenantId\\\":\\\"123abc456-d789-0e1f-2a34-b56789c01234\\\",\\\"Type\\\":\\\"AAD\\\"}],\\\"PendingType\\\":\\\"User\\\",\\\"LogCreationTime\\\":\\\"2024-09-02T03:33:31.8137435Z\\\",\\\"MachineName\\\":\\\"MACHINE01\\\",\\\"Description\\\":\\\"For malicious emails, you can move to junk, soft or hard delete from user's mailbox.\\\"}\",\"{\\\"$id\\\":\\\"1\\\",\\\"ActionId\\\":\\\"urn:EmailZapper:012345a6789bcd0e1f23a4b5cd678ef9\\\",\\\"InvestigationId\\\":\\\"urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\\\",\\\"ActionApproval\\\":\\\"None\\\",\\\"ActionType\\\":\\\"EmailRemediation\\\",\\\"ActionStatus\\\":\\\"Pending\\\",\\\"Entities\\\":[{\\\"$id\\\":\\\"2\\\",\\\"NetworkMessageIds\\\":[\\\"01a2bcd3-efab-4c56-7890-12defa3bc4d\\\",\\\"0123a456-b789-0cd1-e23f-45abcd6ef78\\\",\\\"ab12cde3-f456-789a-01bc-23defa4bc5d\\\",\\\"01a2b345-67c8-9012-345d-67efabc8d90e\\\",\\\"01a234b5-6789-012c-3d4e-56fabcd7ef8\\\",\\\"a0bcd12e-3456-7f89-0a1b-23cdefa4b5c6\\\",\\\"0a1b23c4-567d-8901-2345-67efabc8d90a\\\",\\\"0123a4b5-678c-9d0e-1f23-45abcde6fa78\\\",\\\"0a1b234c-5678-90d1-2efa-34bcdef5a6b7\\\",\\\"0123a4bc-5d6e-78f9-0123-45abcde67890\\\"],\\\"CountByThreatType\\\":{\\\"HighConfPhish\\\":0,\\\"Phish\\\":6,\\\"Malware\\\":0,\\\"Spam\\\":6,\\\"MaliciousUrl\\\":12},\\\"CountByProtectionStatus\\\":{\\\"DeliveredAsSpam\\\":6,\\\"Delivered\\\":4,\\\"Blocked\\\":2},\\\"CountByDeliveryLocation\\\":{\\\"JunkFolder\\\":6,\\\"External\\\":3,\\\"Failed\\\":2,\\\"Forwarded\\\":1},\\\"Query\\\":\\\"( ((NormalizedUrl:\\\\\\\"https://example.net/TUZAu6VrAvQT\\\\\\\") AND (ContentType: 1)) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\\\",\\\"QueryTime\\\":\\\"2024-09-02T03:24:59.7851632Z\\\",\\\"MailCount\\\":12,\\\"IsVolumeAnamoly\\\":true,\\\"ClusterSourceIdentifier\\\":\\\"https://example.net/TUZAu6VrAvQT\\\",\\\"ClusterSourceType\\\":\\\"UrlThreatIndicator\\\",\\\"ClusterQueryStartTime\\\":\\\"2024-08-13T00:00:00Z\\\",\\\"ClusterQueryEndTime\\\":\\\"2024-09-02T03:24:59.7851632Z\\\",\\\"ClusterGroup\\\":\\\"UrlThreatIdentifier\\\",\\\"Type\\\":\\\"mailCluster\\\",\\\"ClusterBy\\\":\\\"NormalizedUrl;ContentType\\\",\\\"ClusterByValue\\\":\\\"https://example.net/TUZAu6VrAvQT;1\\\",\\\"QueryStartTime\\\":\\\"8/13/2024 12:00:00 AM\\\",\\\"QueryTime\\\":\\\"9/2/2024 3:24:59 AM\\\",\\\"Urn\\\":\\\"urn:MailClusterEntity:a0123b4c5678def901234a5b67cde890\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"2024-09-02T03:25:01\\\"}],\\\"RelatedAlertIds\\\":[\\\"01234567-89a0-1234-5b67-89cdefa0b12\\\"],\\\"StartTimeUtc\\\":\\\"2024-09-02T03:27:33\\\",\\\"LastUpdateTimeUtc\\\":\\\"2024-09-02T03:33:31.8137435Z\\\",\\\"TimestampUtc\\\":\\\"2024-09-02T03:27:33\\\",\\\"BulkName\\\":\\\"Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\\\",\\\"ResourceIdentifiers\\\":[{\\\"$id\\\":\\\"3\\\",\\\"AadTenantId\\\":\\\"123abc456-d789-0e1f-2a34-b56789c01234\\\",\\\"Type\\\":\\\"AAD\\\"}],\\\"PendingType\\\":\\\"User\\\",\\\"LogCreationTime\\\":\\\"2024-09-02T03:33:31.8137435Z\\\",\\\"MachineName\\\":\\\"MACHINE01\\\",\\\"Description\\\":\\\"For malicious emails, you can move to junk, soft or hard delete from user's mailbox.\\\"}\"],\"Data\":\"{\\\"Version\\\":\\\"3.0\\\",\\\"VendorName\\\":\\\"Microsoft\\\",\\\"ProviderName\\\":\\\"OATP\\\",\\\"AlertType\\\":\\\"8e6ba277-ef39-404e-aaf1-294f6d9a2b88\\\",\\\"StartTimeUtc\\\":\\\"2024-09-02T03:14:37.3349438Z\\\",\\\"EndTimeUtc\\\":\\\"2024-09-02T03:14:37.3349438Z\\\",\\\"TimeGenerated\\\":\\\"2024-09-02T03:16:43.91Z\\\",\\\"ProcessingEndTime\\\":\\\"2024-09-02T03:33:31.8137435Z\\\",\\\"Status\\\":\\\"InProgress\\\",\\\"DetectionTechnology\\\":\\\"URLList\\\",\\\"Severity\\\":\\\"Informational\\\",\\\"ConfidenceLevel\\\":\\\"Unknown\\\",\\\"ConfidenceScore\\\":1.0,\\\"IsIncident\\\":false,\\\"ProviderAlertId\\\":\\\"01234567-89a0-1234-5b67-89cdefa0b12\\\",\\\"SystemAlertId\\\":null,\\\"CorrelationKey\\\":\\\"8a5bf71a-d9e4-422e-8bdb-33272de66983\\\",\\\"Investigations\\\":[{\\\"$id\\\":\\\"1\\\",\\\"Id\\\":\\\"urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\\\",\\\"InvestigationStatus\\\":\\\"Pending\\\"}],\\\"InvestigationIds\\\":[\\\"urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\\\"],\\\"Intent\\\":\\\"Probing\\\",\\\"ResourceIdentifiers\\\":[{\\\"$id\\\":\\\"2\\\",\\\"AadTenantId\\\":\\\"123abc456-d789-0e1f-2a34-b56789c01234\\\",\\\"Type\\\":\\\"AAD\\\"}],\\\"AzureResourceId\\\":null,\\\"WorkspaceId\\\":null,\\\"WorkspaceSubscriptionId\\\":null,\\\"WorkspaceResourceGroup\\\":null,\\\"AgentId\\\":null,\\\"AlertDisplayName\\\":\\\"Email messages containing malicious URL removed after delivery\\u200b\\\",\\\"Description\\\":\\\"Emails with malicious URL that were delivered and later removed -V1.0.0.3\\\",\\\"ExtendedLinks\\\":[{\\\"Href\\\":\\\"https://security.microsoft.com/alerts/fa01234567-89a0-1234-5b67-89cdefa0b12\\\",\\\"Category\\\":null,\\\"Label\\\":\\\"alert\\\",\\\"Type\\\":\\\"webLink\\\"}],\\\"Metadata\\\":{\\\"CustomApps\\\":null,\\\"GenericInfo\\\":null},\\\"Entities\\\":[{\\\"$id\\\":\\\"3\\\",\\\"Recipient\\\":\\\"user@example.net\\\",\\\"Urls\\\":[\\\"https://example.net/TUZAu6VrAvQT\\\",\\\"https://website.net/up/24/35/image.png\\\"],\\\"Threats\\\":[\\\"ZapPhish\\\",\\\"NormalPhish\\\"],\\\"Sender\\\":\\\"user1@test.example.com\\\",\\\"P1Sender\\\":\\\"p1user1@test.example.com\\\",\\\"P1SenderDomain\\\":\\\"test.integration.com\\\",\\\"SenderIP\\\":\\\"1.2.3.4\\\",\\\"P2Sender\\\":\\\"user1@test.example.com\\\",\\\"P2SenderDisplayName\\\":\\\"P2 name\\\",\\\"P2SenderDomain\\\":\\\"test.integration.com\\\",\\\"ReceivedDate\\\":\\\"2024-09-02T02:43:12\\\",\\\"NetworkMessageId\\\":\\\"ab12cde3-f456-789a-01bc-23defa4bc5d\\\",\\\"InternetMessageId\\\":\\\"<message.id.test@0123456789.userabc.mail.com>\\\",\\\"Subject\\\":\\\"Subject of the mail\\\",\\\"AntispamDirection\\\":\\\"Inbound\\\",\\\"DeliveryAction\\\":\\\"DeliveredAsSpam\\\",\\\"ThreatDetectionMethods\\\":[\\\"FingerPrintMatch\\\"],\\\"Language\\\":\\\"en\\\",\\\"DeliveryLocation\\\":\\\"JunkFolder\\\",\\\"OriginalDeliveryLocation\\\":\\\"Inbox\\\",\\\"AdditionalActionsAndResults\\\":[\\\"OriginalDelivery: [N/A]\\\",\\\"Zap: [Success: Message moved]\\\"],\\\"AuthDetails\\\":[{\\\"Name\\\":\\\"SPF\\\",\\\"Value\\\":\\\"Pass\\\"},{\\\"Name\\\":\\\"DKIM\\\",\\\"Value\\\":\\\"None\\\"},{\\\"Name\\\":\\\"DMARC\\\",\\\"Value\\\":\\\"Best guess pass\\\"},{\\\"Name\\\":\\\"Comp Auth\\\",\\\"Value\\\":\\\"pass\\\"}],\\\"SystemOverrides\\\":[],\\\"Type\\\":\\\"mailMessage\\\",\\\"Urn\\\":\\\"urn:MailEntity:01abc23d456efa7bc8901234d5efa67b\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"2024-09-02T03:20:40\\\"},{\\\"$id\\\":\\\"4\\\",\\\"MailboxPrimaryAddress\\\":\\\"user@example.net\\\",\\\"Upn\\\":\\\"user@example.net\\\",\\\"AadId\\\":\\\"0123ac45-6c7d-e89f-a0123b45c6d7\\\",\\\"RiskLevel\\\":\\\"None\\\",\\\"Type\\\":\\\"mailbox\\\",\\\"Urn\\\":\\\"urn:UserEntity:1a2b3456c7defabc8901d2e3fa456789\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"2024-09-02T03:20:40\\\"},{\\\"$id\\\":\\\"5\\\",\\\"Url\\\":\\\"https://example.net/TUZAu6VrAvQT\\\",\\\"Type\\\":\\\"url\\\",\\\"ClickCount\\\":0,\\\"EmailCount\\\":12,\\\"Urn\\\":\\\"urn:UrlEntity:0123a4567b8c9de0fa123bcde4f5a6b\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"2024-09-02T03:20:40\\\"},{\\\"$id\\\":\\\"6\\\",\\\"NetworkMessageIds\\\":[\\\"ab12cde3-f456-789a-01bc-23defa4bc5d\\\"],\\\"CountByThreatType\\\":{\\\"HighConfPhish\\\":0,\\\"Phish\\\":1,\\\"Malware\\\":0,\\\"Spam\\\":1},\\\"CountByProtectionStatus\\\":{\\\"DeliveredAsSpam\\\":1},\\\"CountByDeliveryLocation\\\":{\\\"JunkFolder\\\":1},\\\"Query\\\":\\\"( (( (Subject:\\\\\\\"Subject of the mail\\\\\\\") ) AND ( (SenderIp:\\\\\\\"1.2.3.4\\\\\\\") ) AND ( (AntispamDirection:\\\\\\\"1\\\\\\\") ) AND ( (ContentType: 1) )) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\\\",\\\"QueryTime\\\":\\\"2024-09-02T03:24:59.8007877Z\\\",\\\"MailCount\\\":1,\\\"IsVolumeAnamoly\\\":false,\\\"ClusterSourceIdentifier\\\":\\\"ab12cde3-f456-789a-01bc-23defa4bc5d\\\",\\\"ClusterSourceType\\\":\\\"Similarity\\\",\\\"ClusterQueryStartTime\\\":\\\"2024-08-13T00:00:00Z\\\",\\\"ClusterQueryEndTime\\\":\\\"2024-09-02T03:24:59.8007877Z\\\",\\\"ClusterGroup\\\":\\\"Subject,SenderIp,AntispamDirection\\\",\\\"Type\\\":\\\"mailCluster\\\",\\\"ClusterBy\\\":\\\"Subject;SenderIp;AntispamDirection;ContentType\\\",\\\"ClusterByValue\\\":\\\"Subject of the mail;1.2.3.4;1;1\\\",\\\"QueryStartTime\\\":\\\"8/13/2024 12:00:00 AM\\\",\\\"QueryTime\\\":\\\"9/2/2024 3:24:59 AM\\\",\\\"Urn\\\":\\\"urn:MailClusterEntity:01a2bc345678de901f2a34b567cdef89\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"2024-09-02T03:25:01\\\"},{\\\"$id\\\":\\\"7\\\",\\\"NetworkMessageIds\\\":[\\\"01a2bcd3-efab-4c56-7890-12defa3bc4d\\\",\\\"0123a456-b789-0cd1-e23f-45abcd6ef78\\\",\\\"ab12cde3-f456-789a-01bc-23defa4bc5d\\\",\\\"01a2b345-67c8-9012-345d-67efabc8d90e\\\",\\\"01a234b5-6789-012c-3d4e-56fabcd7ef8\\\",\\\"a0bcd12e-3456-7f89-0a1b-23cdefa4b5c6\\\",\\\"0a1b23c4-567d-8901-2345-67efabc8d90a\\\",\\\"0123a4b5-678c-9d0e-1f23-45abcde6fa78\\\",\\\"0a1b234c-5678-90d1-2efa-34bcdef5a6b7\\\",\\\"0123a4bc-5d6e-78f9-0123-45abcde67890\\\"],\\\"CountByThreatType\\\":{\\\"HighConfPhish\\\":0,\\\"Phish\\\":6,\\\"Malware\\\":0,\\\"Spam\\\":6,\\\"MaliciousUrl\\\":12},\\\"CountByProtectionStatus\\\":{\\\"DeliveredAsSpam\\\":6,\\\"Delivered\\\":4,\\\"Blocked\\\":2},\\\"CountByDeliveryLocation\\\":{\\\"JunkFolder\\\":6,\\\"External\\\":3,\\\"Failed\\\":2,\\\"Forwarded\\\":1},\\\"Query\\\":\\\"( ((NormalizedUrl:\\\\\\\"https://example.net/TUZAu6VrAvQT\\\\\\\") AND (ContentType: 1)) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\\\",\\\"QueryTime\\\":\\\"2024-09-02T03:24:59.7851632Z\\\",\\\"MailCount\\\":12,\\\"IsVolumeAnamoly\\\":true,\\\"ClusterSourceIdentifier\\\":\\\"https://example.net/TUZAu6VrAvQT\\\",\\\"ClusterSourceType\\\":\\\"UrlThreatIndicator\\\",\\\"ClusterQueryStartTime\\\":\\\"2024-08-13T00:00:00Z\\\",\\\"ClusterQueryEndTime\\\":\\\"2024-09-02T03:24:59.7851632Z\\\",\\\"ClusterGroup\\\":\\\"UrlThreatIdentifier\\\",\\\"Type\\\":\\\"mailCluster\\\",\\\"ClusterBy\\\":\\\"NormalizedUrl;ContentType\\\",\\\"ClusterByValue\\\":\\\"https://example.net/TUZAu6VrAvQT;1\\\",\\\"QueryStartTime\\\":\\\"8/13/2024 12:00:00 AM\\\",\\\"QueryTime\\\":\\\"9/2/2024 3:24:59 AM\\\",\\\"Urn\\\":\\\"urn:MailClusterEntity:a0123b4c5678def901234a5b67cde890\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"2024-09-02T03:25:01\\\"},{\\\"$id\\\":\\\"8\\\",\\\"NetworkMessageIds\\\":[\\\"ab12cde3-f456-789a-01bc-23defa4bc5d\\\"],\\\"CountByThreatType\\\":{\\\"HighConfPhish\\\":0,\\\"Phish\\\":1,\\\"Malware\\\":0,\\\"Spam\\\":1},\\\"CountByProtectionStatus\\\":{\\\"DeliveredAsSpam\\\":1},\\\"CountByDeliveryLocation\\\":{\\\"JunkFolder\\\":1},\\\"Query\\\":\\\"( (( (Subject:\\\\\\\"Subject of the mail\\\\\\\") ) AND ( (P2SenderDomain:\\\\\\\"test.integration.com\\\\\\\") ) AND ( (AntispamDirection:\\\\\\\"1\\\\\\\") ) AND ( (ContentType: 1) )) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:PhishEdu) AND NOT(XmiInfoTenantPolicyFinalVerdictSource:SecOps))\\\",\\\"QueryTime\\\":\\\"2024-09-02T03:24:59.8007877Z\\\",\\\"MailCount\\\":1,\\\"IsVolumeAnamoly\\\":false,\\\"ClusterSourceIdentifier\\\":\\\"ab12cde3-f456-789a-01bc-23defa4bc5d\\\",\\\"ClusterSourceType\\\":\\\"Similarity\\\",\\\"ClusterQueryStartTime\\\":\\\"2024-08-13T00:00:00Z\\\",\\\"ClusterQueryEndTime\\\":\\\"2024-09-02T03:24:59.8007877Z\\\",\\\"ClusterGroup\\\":\\\"Subject,P2SenderDomain,AntispamDirection\\\",\\\"Type\\\":\\\"mailCluster\\\",\\\"ClusterBy\\\":\\\"Subject;P2SenderDomain;AntispamDirection;ContentType\\\",\\\"ClusterByValue\\\":\\\"Subject of the mail;test.integration.com;1;1\\\",\\\"QueryStartTime\\\":\\\"8/13/2024 12:00:00 AM\\\",\\\"QueryTime\\\":\\\"9/2/2024 3:24:59 AM\\\",\\\"Urn\\\":\\\"urn:MailClusterEntity:7350e5b982beaa3846d327a005dd57d6\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"2024-09-02T03:25:01\\\"}],\\\"LogCreationTime\\\":\\\"2024-09-02T03:33:31.8137435Z\\\",\\\"MachineName\\\":\\\"MACHINE01\\\",\\\"SourceTemplateType\\\":\\\"Threat_Single\\\",\\\"Category\\\":\\\"ThreatManagement\\\",\\\"SourceAlertType\\\":\\\"System\\\"}\",\"DeepLinkUrl\":\"https://security.microsoft.com/mtp-investigation/urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\",\"EndTimeUtc\":\"2024-09-02T03:33:31\",\"InvestigationId\":\"urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\",\"InvestigationName\":\"Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9\",\"InvestigationType\":\"ZappedUrlInvestigation\",\"LastUpdateTimeUtc\":\"2024-09-02T03:28:24\",\"RunningTime\":771,\"StartTimeUtc\":\"2024-09-02T03:20:40\",\"Status\":\"Pending Action\"}",
"event": {
"action": "AirInvestigationData",
"code": "64",
"end": "2024-09-02T03:33:31Z",
"kind": "event",
"outcome": "success",
"start": "2024-09-02T03:20:40Z"
},
"@timestamp": "2024-09-02T03:33:37Z",
"action": {
"id": 64,
"name": "AirInvestigationData",
"outcome": "success",
"target": "user"
},
"email": {
"from": {
"address": [
"user1@test.example.com"
]
},
"to": {
"address": [
"user@example.net"
]
}
},
"log": {
"level": "Informational"
},
"office365": {
"audit": {
"object_id": "1234ab56-7890-1234-c5de-678fabcd9012"
},
"investigation": {
"alert": {
"category": "ThreatManagement",
"correlation_key": "8a5bf71a-d9e4-422e-8bdb-33272de66983",
"is_incident": false,
"provider": {
"name": "OATP",
"status": "InProgress"
},
"severity": "Informational",
"source_type": "System",
"type": "8e6ba277-ef39-404e-aaf1-294f6d9a2b88",
"urls": [
"https://security.microsoft.com/alerts/fa01234567-89a0-1234-5b67-89cdefa0b12"
]
},
"delivery": {
"action": [
"DeliveredAsSpam"
]
},
"email": {
"sender": {
"domains": [
"test.integration.com"
],
"ip": [
"1.2.3.4"
]
},
"subjects": [
"Subject of the mail"
],
"urls": [
"https://example.net/TUZAu6VrAvQT",
"https://website.net/up/24/35/image.png"
]
},
"emails": [
{
"message_ids": [
"01a2bcd3-efab-4c56-7890-12defa3bc4d",
"0123a456-b789-0cd1-e23f-45abcd6ef78",
"ab12cde3-f456-789a-01bc-23defa4bc5d",
"01a2b345-67c8-9012-345d-67efabc8d90e",
"01a234b5-6789-012c-3d4e-56fabcd7ef8",
"a0bcd12e-3456-7f89-0a1b-23cdefa4b5c6",
"0a1b23c4-567d-8901-2345-67efabc8d90a",
"0123a4b5-678c-9d0e-1f23-45abcde6fa78",
"0a1b234c-5678-90d1-2efa-34bcdef5a6b7",
"0123a4bc-5d6e-78f9-0123-45abcde67890"
]
},
{
"message_ids": [
"ab12cde3-f456-789a-01bc-23defa4bc5d"
]
},
{
"delivery": {
"action": "DeliveredAsSpam",
"location": "JunkFolder",
"original_location": "Inbox"
},
"direction": "Inbound",
"language": "en",
"message_ids": [
"ab12cde3-f456-789a-01bc-23defa4bc5d"
]
}
],
"id": "urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9",
"name": "Mail with malicious urls is zapped - urn:ZappedUrlInvestigation:a01b23c4de5f678901a234bc5678d9",
"status": "Pending Action",
"threats": [
"NormalPhish",
"ZapPhish"
],
"type": "ZappedUrlInvestigation"
},
"machine_name": "MACHINE01",
"record_id": "1234ab56-7890-1234-c5de-678fabcd9012",
"record_type": 64,
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"rule": {
"name": "Email messages containing malicious URL removed after delivery\u200b"
},
"service": {
"name": "user1"
},
"threat": {
"enrichments": [
{
"indicator": {
"email": {
"address": "user@example.net"
},
"first_seen": "2024-09-02T03:20:40Z",
"ip": "1.2.3.4",
"provider": "OATP"
}
},
{
"indicator": {
"first_seen": "2024-09-02T03:20:40Z",
"provider": "OATP",
"url": {
"full": "https://example.net/TUZAu6VrAvQT"
}
}
}
]
},
"url": {
"domain": "example.net",
"full": "https://example.net/TUZAu6VrAvQT",
"original": "https://example.net/TUZAu6VrAvQT",
"path": "/TUZAu6VrAvQT",
"port": 443,
"registered_domain": "example.net",
"scheme": "https",
"top_level_domain": "net"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2023-11-21T12:24:04\",\"Id\":\"d32b02fd-f97e-47a1-9407-f5cb2dcca772\",\"Operation\":\"AirInvestigationData\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":64,\"UserKey\":\"user1\",\"UserType\":4,\"Version\":1,\"Workload\":\"user1\",\"ObjectId\":\"d32b02fd-f97e-47a1-9407-f5cb2dcca772\",\"UserId\":\"user1\",\"Data\":\"{\\\"Version\\\":\\\"3.0\\\",\\\"VendorName\\\":\\\"Microsoft\\\",\\\"ProviderName\\\":\\\"OATP\\\",\\\"AlertType\\\":\\\"4b1820ec-39dc-45f3-abf6-5ee80df51fd2\\\",\\\"StartTimeUtc\\\":\\\"2023-11-21T12:13:21.3426718Z\\\",\\\"EndTimeUtc\\\":\\\"2023-11-21T12:13:21.3426718Z\\\",\\\"TimeGenerated\\\":\\\"2023-11-21T12:21:01.367Z\\\",\\\"ProcessingEndTime\\\":\\\"2023-11-21T12:24:02.9479392Z\\\",\\\"Status\\\":\\\"InProgress\\\",\\\"Severity\\\":\\\"Informational\\\",\\\"ConfidenceLevel\\\":\\\"Unknown\\\",\\\"ConfidenceScore\\\":1.0,\\\"IsIncident\\\":false,\\\"ProviderAlertId\\\":\\\"2187a396-5337-1901-6e00-08dbea8b3430\\\",\\\"SystemAlertId\\\":null,\\\"CorrelationKey\\\":\\\"955b1f53-3bcf-45cf-9e1d-b071d0518b01\\\",\\\"Investigations\\\":[{\\\"$id\\\":\\\"1\\\",\\\"Id\\\":\\\"urn:ZappedFileInvestigation:adffaf6ed0f17079cf14e9dc2adf9c1d\\\",\\\"InvestigationStatus\\\":\\\"Running\\\"}],\\\"InvestigationIds\\\":[\\\"urn:ZappedFileInvestigation:adffaf6ed0f17079cf14e9dc2adf9c1d\\\"],\\\"Intent\\\":\\\"Probing\\\",\\\"ResourceIdentifiers\\\":[{\\\"$id\\\":\\\"2\\\",\\\"AadTenantId\\\":\\\"62e8c4be-8433-4768-82bb-4c97eaf05a19\\\",\\\"Type\\\":\\\"AAD\\\"}],\\\"AzureResourceId\\\":null,\\\"WorkspaceId\\\":null,\\\"WorkspaceSubscriptionId\\\":null,\\\"WorkspaceResourceGroup\\\":null,\\\"AgentId\\\":null,\\\"AlertDisplayName\\\":\\\"Email messages containing malicious file removed after delivery\\\",\\\"Description\\\":\\\"Emails with malicious file that were delivered and later removed -V1.0.0.3\\\",\\\"ExtendedLinks\\\":[{\\\"Href\\\":\\\"https://security.microsoft.com/viewalerts?id=2187a396-5337-1901-6e00-08dbea8b3430\\\",\\\"Category\\\":null,\\\"Label\\\":\\\"alert\\\",\\\"Type\\\":\\\"webLink\\\"}],\\\"Metadata\\\":{\\\"CustomApps\\\":null,\\\"GenericInfo\\\":null},\\\"Entities\\\":[{\\\"$id\\\":\\\"3\\\",\\\"MailboxPrimaryAddress\\\":\\\"john.doe@example.com\\\",\\\"Upn\\\":\\\"john.doe@example.com\\\",\\\"AadId\\\":\\\"70999cb4-e7db-47c8-a3ba-99381283152d\\\",\\\"RiskLevel\\\":\\\"None\\\",\\\"Type\\\":\\\"mailbox\\\",\\\"Urn\\\":\\\"urn:UserEntity:11111111111111111111111111111111\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"0001-01-01T00:00:00\\\"},{\\\"$id\\\":\\\"4\\\",\\\"Files\\\":[{\\\"$id\\\":\\\"5\\\",\\\"Name\\\":\\\"pix.jpg\\\",\\\"FileHashes\\\":[{\\\"$id\\\":\\\"6\\\",\\\"Algorithm\\\":\\\"SHA256\\\",\\\"Value\\\":\\\"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b\\\",\\\"Type\\\":\\\"filehash\\\"}],\\\"Type\\\":\\\"file\\\",\\\"MalwareFamily\\\":\\\"Malicious Payload\\\"}],\\\"Recipient\\\":\\\"john.doe@example.com\\\",\\\"Urls\\\":[\\\"https://example.org\\\"],\\\"Sender\\\":\\\"jane.doe@example.org\\\",\\\"P1Sender\\\":\\\"jane.doe@example.org\\\",\\\"P1SenderDomain\\\":\\\"example.org\\\",\\\"SenderIP\\\":\\\"1.2.3.4\\\",\\\"P2Sender\\\":\\\"jane.doe@example.org\\\",\\\"P2SenderDisplayName\\\":\\\"jane.doe\\\",\\\"P2SenderDomain\\\":\\\"example.org\\\",\\\"ReceivedDate\\\":\\\"2023-11-21T12:00:46\\\",\\\"NetworkMessageId\\\":\\\"3fe5777d-1fb7-4f34-bb1e-035e4df1f96f\\\",\\\"InternetMessageId\\\":\\\"<88f57442-338a-4e6b-8925-73d62527809b@example.org>\\\",\\\"Subject\\\":\\\"Pending and Review\\\",\\\"AntispamDirection\\\":\\\"Inbound\\\",\\\"DeliveryAction\\\":\\\"Blocked\\\",\\\"ThreatDetectionMethods\\\":[\\\"FileHashList\\\"],\\\"Language\\\":\\\"en\\\",\\\"DeliveryLocation\\\":\\\"Quarantine\\\",\\\"OriginalDeliveryLocation\\\":\\\"Inbox\\\",\\\"PhishConfidenceLevel\\\":\\\"High\\\",\\\"AdditionalActionsAndResults\\\":[\\\"OriginalDelivery: [N/A]\\\",\\\"Zap: [Success: Message moved to quarantine]\\\"],\\\"AuthDetails\\\":[{\\\"Name\\\":\\\"SPF\\\",\\\"Value\\\":\\\"Pass\\\"},{\\\"Name\\\":\\\"DKIM\\\",\\\"Value\\\":\\\"Pass\\\"},{\\\"Name\\\":\\\"DMARC\\\",\\\"Value\\\":\\\"Best guess pass\\\"},{\\\"Name\\\":\\\"Comp Auth\\\",\\\"Value\\\":\\\"pass\\\"}],\\\"SystemOverrides\\\":[],\\\"Type\\\":\\\"mailMessage\\\",\\\"Urn\\\":\\\"urn:MailEntity:93d7f11156b7dc03c36d7ef108389605\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"0001-01-01T00:00:00\\\"},{\\\"$id\\\":\\\"7\\\",\\\"Name\\\":\\\"pix.jpg\\\",\\\"FileHashes\\\":[{\\\"$id\\\":\\\"8\\\",\\\"Algorithm\\\":\\\"SHA256\\\",\\\"Value\\\":\\\"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b\\\",\\\"Type\\\":\\\"filehash\\\"}],\\\"Type\\\":\\\"file\\\",\\\"MalwareFamily\\\":\\\"\\\",\\\"Urn\\\":\\\"urn:FileEntity:6cfb0a0866370a891ce96e9c83fb4fed\\\",\\\"Source\\\":\\\"OATP\\\",\\\"FirstSeen\\\":\\\"0001-01-01T00:00:00\\\"}],\\\"LogCreationTime\\\":\\\"2023-11-21T12:24:02.9479392Z\\\",\\\"MachineName\\\":\\\"DBAEUR03BG405\\\",\\\"SourceTemplateType\\\":\\\"Threat_Single\\\",\\\"Category\\\":\\\"ThreatManagement\\\",\\\"SourceAlertType\\\":\\\"System\\\"}\",\"DeepLinkUrl\":\"https://security.microsoft.com/mtp-investigation/urn:ZappedFileInvestigation:adffaf6ed0f17079cf14e9dc2adf9c1d\",\"EndTimeUtc\":\"0001-01-01T00:00:00\",\"InvestigationId\":\"urn:ZappedFileInvestigation:adffaf6ed0f17079cf14e9dc2adf9c1d\",\"InvestigationName\":\"Mail with malicious file is zapped - urn:ZappedFileInvestigation:adffaf6ed0f17079cf14e9dc2adf9c1d\",\"InvestigationType\":\"ZappedFileInvestigation\",\"LastUpdateTimeUtc\":\"2023-11-21T12:21:48\",\"StartTimeUtc\":\"2023-11-21T12:24:03\",\"Status\":\"Investigation Started\"}",
"event": {
"action": "AirInvestigationData",
"code": "64",
"end": "0001-01-01T00:00:00Z",
"kind": "event",
"outcome": "success",
"start": "2023-11-21T12:24:03Z"
},
"@timestamp": "2023-11-21T12:24:04Z",
"action": {
"id": 64,
"name": "AirInvestigationData",
"outcome": "success",
"target": "user"
},
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "pix.jpg"
}
}
],
"from": {
"address": [
"jane.doe@example.org"
]
},
"to": {
"address": [
"john.doe@example.com"
]
}
},
"log": {
"level": "Informational"
},
"office365": {
"audit": {
"object_id": "d32b02fd-f97e-47a1-9407-f5cb2dcca772"
},
"investigation": {
"alert": {
"category": "ThreatManagement",
"correlation_key": "955b1f53-3bcf-45cf-9e1d-b071d0518b01",
"is_incident": false,
"provider": {
"name": "OATP",
"status": "InProgress"
},
"severity": "Informational",
"source_type": "System",
"type": "4b1820ec-39dc-45f3-abf6-5ee80df51fd2",
"urls": [
"https://security.microsoft.com/viewalerts?id=2187a396-5337-1901-6e00-08dbea8b3430"
]
},
"delivery": {
"action": [
"Blocked"
]
},
"email": {
"sender": {
"domains": [
"example.org"
],
"ip": [
"1.2.3.4"
]
},
"subjects": [
"Pending and Review"
],
"urls": [
"https://example.org"
]
},
"emails": [
{
"delivery": {
"action": "Blocked",
"location": "Quarantine",
"original_location": "Inbox"
},
"direction": "Inbound",
"language": "en",
"message_ids": [
"3fe5777d-1fb7-4f34-bb1e-035e4df1f96f"
]
}
],
"id": "urn:ZappedFileInvestigation:adffaf6ed0f17079cf14e9dc2adf9c1d",
"name": "Mail with malicious file is zapped - urn:ZappedFileInvestigation:adffaf6ed0f17079cf14e9dc2adf9c1d",
"status": "Investigation Started",
"type": "ZappedFileInvestigation"
},
"machine_name": "DBAEUR03BG405",
"record_id": "d32b02fd-f97e-47a1-9407-f5cb2dcca772",
"record_type": 64,
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"rule": {
"name": "Email messages containing malicious file removed after delivery"
},
"service": {
"name": "user1"
},
"threat": {
"enrichments": [
{
"indicator": {
"email": {
"address": "john.doe@example.com"
},
"first_seen": "0001-01-01T00:00:00Z",
"ip": "1.2.3.4",
"provider": "OATP"
}
}
]
},
"url": {
"domain": "example.org",
"full": "https://example.org",
"original": "https://example.org",
"port": 443,
"registered_domain": "example.org",
"scheme": "https",
"top_level_domain": "org"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\":{\"AADSessionId\":\"ANONYMIZED\",\"CorrelationId\":\"ANONYMIZED\",\"UniqueTokenId\":\"ANONYMIZED\"},\"CreationTime\":\"2023-12-13T10:08:25\",\"Id\":\"ANONYMIZED\",\"Operation\":\"ListViewed\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":36,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"SharePoint\",\"ClientIP\":\"0.0.0.0\",\"UserId\":\"user1\",\"AuthenticationType\":\"FormsCookieAuth\",\"BrowserName\":\"Chrome\",\"BrowserVersion\":\"102.0.5005.197\",\"CorrelationId\":\"ANONYMIZED\",\"EventSource\":\"SharePoint\",\"IsManagedDevice\":false,\"ItemType\":\"List\",\"ListId\":\"xxxxxx\",\"Platform\":\"WinDesktop\",\"Site\":\"xxxxxx\",\"UserAgent\":\"Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Teams/1.6.00.29964 Chrome/102.0.5005.197 Electron/19.1.8 Safari/537.36\",\"WebId\":\"xxxxxx\",\"DeviceDisplayName\":\"xxxxxx\",\"CustomizedDoclib\":false,\"FromApp\":true,\"ItemCount\":102,\"ListBaseTemplateType\":\"101\",\"ListBaseType\":\"DocumentLibrary\",\"ListColor\":\"\",\"ListIcon\":\"\",\"Source\":\"Unknown\",\"TemplateTypeId\":\"\",\"ListTitle\":\"xxxxxx\",\"ObjectId\":\"https://domain.com/subdomain/xxxxxx\"}",
"event": {
"action": "ListViewed",
"code": "36",
"outcome": "success"
},
"@timestamp": "2023-12-13T10:08:25Z",
"action": {
"id": 36,
"name": "ListViewed",
"outcome": "success",
"target": "user"
},
"azuread": {
"properties": {
"uniqueTokenIdentifier": "ANONYMIZED"
}
},
"office365": {
"audit": {
"object_id": "https://domain.com/subdomain/xxxxxx"
},
"context": {
"aad_session_id": "ANONYMIZED",
"authentication_type": "FormsCookieAuth",
"correlation": {
"id": "ANONYMIZED"
}
},
"device": {
"is_managed": false
},
"record_id": "ANONYMIZED",
"record_type": 36,
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"0.0.0.0"
],
"user": [
"user1"
]
},
"service": {
"name": "SharePoint"
},
"source": {
"address": "0.0.0.0",
"ip": "0.0.0.0"
},
"user": {
"id": "user1",
"name": "user1"
},
"user_agent": {
"name": "Chrome",
"version": "102.0.5005.197"
}
}
{
"message": "{\"CreationTime\":\"2024-06-26T06:29:14\",\"Id\":\"ANONYMIZED\",\"Operation\":\"MailItemsAccessed\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":50,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"ANONYMIZED\",\"UserType\":5,\"Version\":1,\"Workload\":\"Exchange\",\"UserId\":\"ANONYMIZED\",\"AppId\":\"ANONYMIZED\",\"ClientAppId\":\"clientappidxxxx-xxx-xxx-xxxx\",\"ClientIPAddress\":\"FE80::\",\"ClientInfoString\":\"Client=Exemple1;Client=Exemple2;;\",\"ExternalAccess\":\"False\",\"InternalLogonType\":0,\"LogonType\":0,\"LogonUserSid\":\"S-1-2-3\",\"MailboxGuid\":\"ANONYMIZED\",\"MailboxOwnerSid\":\"S-1-2-3\",\"MailboxOwnerUPN\":\"ANONYMIZED\",\"OperationProperties\":[{\"Name\":\"MailAccessType\",\"Value\":\"Bind\"},{\"Name\":\"IsThrottled\",\"Value\":\"False\"}],\"OrganizationName\":\"organization.microsoft.com\",\"OriginatingServer\":\"server (0.0.0000.000)\\r\\n\",\"Folders\":[{\"FolderItems\":[{\"ClientRequestId\":\"ANONYMIZED\",\"Id\":\"aaaaaaaaaaaaa\",\"InternetMessageId\":\"xxxxx@exemple.com\",\"SizeInBytes\":127625},{\"ClientRequestId\":\"ANONYMIZED\",\"Id\":\"aaaaaaaaaaaaaaaaaa\",\"InternetMessageId\":\"xxxx-xxx-xxx-xxxx@enterprise.net\",\"SizeInBytes\":147360}],\"Id\":\"aaaaaaaaaaaaaaaaaaaa\",\"Path\":\"Boite de reception\"}],\"OperationCount\":2}",
"event": {
"action": "MailItemsAccessed",
"code": "50",
"outcome": "success"
},
"@timestamp": "2024-06-26T06:29:14Z",
"action": {
"id": 50,
"name": "MailItemsAccessed",
"outcome": "success",
"target": "user"
},
"office365": {
"context": {
"client": {
"id": "clientappidxxxx-xxx-xxx-xxxx"
}
},
"exchange": {
"mailbox_owner": {
"sid": "S-1-2-3",
"upn": "ANONYMIZED"
}
},
"folders": {
"paths": [
"Boite de reception"
]
},
"operation": {
"properties": {
"IsThrottled": "False",
"MailAccessType": "Bind"
}
},
"record_id": "ANONYMIZED",
"record_type": 50,
"result_status": "Succeeded",
"user_type": {
"code": 5,
"name": "Application"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"fe80::"
],
"user": [
"ANONYMIZED"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "fe80::",
"ip": "fe80::"
},
"user": {
"id": "S-1-2-3",
"name": "ANONYMIZED"
}
}
{
"message": "{\"ActionId\":\"a81edede-be03-41f4-aae2-b6b25186adc6\",\"ActionName\":\"Enable self-service password reset\",\"ActionProducts\":[],\"ActionScore\":26.0,\"ActionScoreChange\":-1.0,\"ActionActivity\":\"COMPLIANCEMANAGER-SCORECHANGE\",\"Assessments\":[],\"Templates\":[],\"Solutions\":[],\"ManagedBy\":\"User\",\"ActionScope\":\"Tenant\",\"UserId\":\"\",\"Id\":\"aa9367e4-9fa3-4709-8326-b35c04f784d2\",\"RecordType\":155,\"CreationTime\":\"2022-10-05T10:12:57\",\"Operation\":\"COMPLIANCEMANAGER-SCORECHANGE\",\"OrganizationId\":\"ANONYMIZED\",\"UserType\":2,\"UserKey\":\"user1\",\"Workload\":\"ComplianceManager\",\"ResultStatus\":\"Successful\",\"Version\":1}",
"event": {
"action": "COMPLIANCEMANAGER-SCORECHANGE",
"code": "155",
"outcome": "success",
"reason": "Enable self-service password reset"
},
"@timestamp": "2022-10-05T10:12:57Z",
"action": {
"id": 155,
"name": "COMPLIANCEMANAGER-SCORECHANGE",
"outcome": "success",
"target": "user"
},
"office365": {
"record_id": "aa9367e4-9fa3-4709-8326-b35c04f784d2",
"record_type": 155,
"result_status": "Successful",
"user_type": {
"code": 2,
"name": "Admin"
}
},
"organization": {
"id": "ANONYMIZED"
},
"service": {
"name": "ComplianceManager"
},
"user": {
"id": "user1"
}
}
{
"message": "{\"CreationTime\":\"2024-05-24T06:29:22\",\"Id\":\"03604c8d-ed69-466b-a9f4-80467c958739\",\"Operation\":\"AlertUpdated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"f54a9b97-a432-471b-a84a-ddcba13f5f35\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertId\":\"2c7f6c46-33d7-4101-b2fc-0af27eaf308a\",\"AlertLinks\":[],\"AlertType\":\"System\",\"Category\":\"ThreatManagement\",\"Comments\":\"New alert\",\"Data\":\"{\\\"f3u\\\":\\\"john.doe@example.com\\\",\\\"ts\\\":\\\"2024-05-24T05:44:00Z\\\",\\\"te\\\":\\\"2024-05-24T05:45:00Z\\\",\\\"op\\\":\\\"UserSubmission\\\",\\\"wl\\\":\\\"SecurityComplianceCenter\\\",\\\"tid\\\":\\\"8a1a1157-0272-492d-ab10-3f9853ac8183\\\",\\\"tdc\\\":\\\"1\\\",\\\"reid\\\":\\\"a04c1571-7271-445e-82e3-c39f848aceb8\\\",\\\"wsrt\\\":\\\"2024-05-24T05:45:22\\\",\\\"mdt\\\":\\\"Audit\\\",\\\"rid\\\":\\\"9a36861c-cc4d-4818-be4a-a20555480a00\\\",\\\"cid\\\":\\\"2b6fda52-8386-4213-b6fb-2fcb078571c4\\\",\\\"ad\\\":\\\"This alert is triggered when any email message is reported as malware or phish by users -V1.0.0.3\\\",\\\"lon\\\":\\\"UserSubmission\\\",\\\"an\\\":\\\"Email reported by user as malware or phish\\\",\\\"sev\\\":\\\"Low\\\",\\\"ail\\\":\\\"https://security.microsoft.com/mtp-investigation/urn:SubmissionInvestigation:260a29b9cf8a4358857b82aa9f086c48\\\"}\",\"Name\":\"Email reported by user as malware or phish\",\"PolicyId\":\"5b31bd58-7d6e-4f97-aa6b-5135fb1b1e52\",\"Severity\":\"Low\",\"Source\":\"Office 365 Security & Compliance\",\"Status\":\"Resolved\"}",
"event": {
"action": "AlertUpdated",
"category": [
"intrusion_detection"
],
"code": "40",
"kind": "alert",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-05-24T06:29:22Z",
"action": {
"id": 40,
"name": "AlertUpdated",
"outcome": "success",
"target": "user"
},
"office365": {
"alert": {
"category": "ThreatManagement",
"display_name": "Email reported by user as malware or phish",
"id": "2c7f6c46-33d7-4101-b2fc-0af27eaf308a",
"severity": "Low",
"source": "Office 365 Security & Compliance",
"status": "Resolved"
},
"audit": {
"object_id": "f54a9b97-a432-471b-a84a-ddcba13f5f35"
},
"record_id": "03604c8d-ed69-466b-a9f4-80467c958739",
"record_type": 40,
"result_status": "Succeeded",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"john.doe"
]
},
"rule": {
"id": "5b31bd58-7d6e-4f97-aa6b-5135fb1b1e52"
},
"service": {
"name": "SecurityComplianceCenter"
},
"user": {
"domain": "example.com",
"email": "john.doe@example.com",
"name": "john.doe"
}
}
{
"message": "{\"CreationTime\":\"2025-08-13T14:02:32\",\"Id\":\"id-1\",\"Operation\":\"MipLabel\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":43,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"ObjectId\":\"objectid-1\",\"UserId\":\"user1\",\"ApplicationMode\":\"Standard\",\"ItemName\":\"ANONYMIZED\",\"LabelAction\":\"None\",\"LabelAppliedDateTime\":\"2025-06-25T12:40:11\",\"LabelId\":\"labelid-1\",\"LabelName\":\"Internal\",\"Receivers\":[\"user-2@example.com\",\"user-3@example.com\",\"user-4@example.com\",\"user-5@example.com\",\"user-6@example.com\",\"user-7@example.com\",\"user-8@example.com\",\"user-9@example.com\",\"user-10@example.com\",\"user-11@example.com\",\"user-12@example.com\",\"user-13@example.com\",\"user-14@example.com\",\"user-15@example.com\",\"user-16@example.com\",\"user-17@example.com\",\"user-18@example.com\",\"user-19@example.com\",\"user-20@example.com\"],\"Sender\":\"user1\"}",
"event": {
"action": "MipLabel",
"code": "43",
"outcome": "success"
},
"@timestamp": "2025-08-13T14:02:32Z",
"action": {
"id": 43,
"name": "MipLabel",
"outcome": "success",
"target": "user"
},
"email": {
"sender": {
"address": "user1"
},
"subject": "ANONYMIZED",
"to": {
"address": [
"user-10@example.com",
"user-11@example.com",
"user-12@example.com",
"user-13@example.com",
"user-14@example.com",
"user-15@example.com",
"user-16@example.com",
"user-17@example.com",
"user-18@example.com",
"user-19@example.com",
"user-20@example.com",
"user-2@example.com",
"user-3@example.com",
"user-4@example.com",
"user-5@example.com",
"user-6@example.com",
"user-7@example.com",
"user-8@example.com",
"user-9@example.com"
]
}
},
"office365": {
"audit": {
"object_id": "objectid-1"
},
"mip": {
"label_name": "Internal"
},
"record_id": "id-1",
"record_type": 43,
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2025-11-25T10:41:35\",\"Id\":\"TEST_RECORD_ID\",\"Operation\":\"Add application.\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":8,\"ResultStatus\":\"Success\",\"UserKey\":\"user1\",\"UserType\":4,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ObjectId\":\"Application_123123123123213\",\"UserId\":\"user1\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"additionalDetails\",\"Value\":\"{\\\"AppId\\\":\\\"TEST_APP_Id\\\",\\\"Source\\\":\\\"{\\\\\\\"TYPE\\\\\\\":\\\\\\\"USER\\\\\\\",\\\\\\\"OBJECT ID\\\\\\\":\\\\\\\"22222222-2222-2222-2222-222222222222\\\\\\\"}\\\"}\"},{\"Name\":\"extendedAuditEventCategory\",\"Value\":\"Application\"}],\"ModifiedProperties\":[{\"Name\":\"AppAddress\",\"NewValue\":\"[\\r\\n {\\r\\n \\\"AddressType\\\": 0,\\r\\n \\\"Address\\\": \\\"https://*.services.adobe.com/federated/saml/SSO/alias/*\\\",\\r\\n \\\"ReplyAddressClientType\\\": 0,\\r\\n \\\"ReplyAddressIndex\\\": null,\\r\\n \\\"IsReplyAddressDefault\\\": false\\r\\n }\\r\\n]\",\"OldValue\":\"[]\"},{\"Name\":\"AppId\",\"NewValue\":\"[\\r\\n \\\"TEST_APP_Id\\\"\\r\\n]\",\"OldValue\":\"[]\"},{\"Name\":\"AvailableToOtherTenants\",\"NewValue\":\"[\\r\\n false\\r\\n]\",\"OldValue\":\"[]\"},{\"Name\":\"DisplayName\",\"NewValue\":\"[\\r\\n \\\"Adobe Identity Management (SAML)\\\"\\r\\n]\",\"OldValue\":\"[]\"},{\"Name\":\"Entitlement\",\"NewValue\":\"[\\r\\n {\\r\\n \\\"EntitlementEncodingVersion\\\": 2,\\r\\n \\\"EntitlementId\\\": \\\"33333333-3333-3333-3333-333333333333\\\",\\r\\n \\\"IsDisabled\\\": false,\\r\\n \\\"Origin\\\": 0,\\r\\n \\\"Name\\\": \\\"Access Adobe Identity Management (SAML)\\\",\\r\\n \\\"Description\\\": \\\"Allow the application to access Adobe Identity Management (SAML) on behalf of the signed-in user.\\\",\\r\\n \\\"Definition\\\": null,\\r\\n \\\"ClaimValue\\\": \\\"user_impersonation\\\",\\r\\n \\\"ResourceScopeType\\\": 1,\\r\\n \\\"IsPrivate\\\": false,\\r\\n \\\"UserConsentDisplayName\\\": \\\"Access Adobe Identity Management (SAML)\\\",\\r\\n \\\"UserConsentDescription\\\": \\\"Allow the application to access Adobe Identity Management (SAML) on your behalf.\\\",\\r\\n \\\"DirectAccessGrantTypes\\\": [],\\r\\n \\\"ImpersonationAccessGrantTypes\\\": [\\r\\n {\\r\\n \\\"Impersonator\\\": 29,\\r\\n \\\"Impersonated\\\": 20\\r\\n }\\r\\n ],\\r\\n \\\"EntitlementCategory\\\": 0,\\r\\n \\\"DependentMicrosoftGraphPermissions\\\": [],\\r\\n \\\"IsPreauthzOnlyDirectAccessGrant\\\": false,\\r\\n \\\"IsPreauthzOnlyImpersonationGrant\\\": false\\r\\n }\\r\\n]\",\"OldValue\":\"[]\"},{\"Name\":\"PublicClient\",\"NewValue\":\"[\\r\\n false\\r\\n]\",\"OldValue\":\"[]\"},{\"Name\":\"WwwHomepage\",\"NewValue\":\"[\\r\\n \\\"https://*.services.adobe.com/federated/saml/SSO/alias/*?metadata=adobeidentitymanagement|ISV9.1|primary|z\\\"\\r\\n]\",\"OldValue\":\"[]\"},{\"Name\":\"PublisherDomain\",\"NewValue\":\"[\\r\\n \\\"ocd-testing.com\\\"\\r\\n]\",\"OldValue\":\"[]\"},{\"Name\":\"SignInAudience\",\"NewValue\":\"[\\r\\n \\\"AzureADMyOrg\\\"\\r\\n]\",\"OldValue\":\"[]\"},{\"Name\":\"Included Updated Properties\",\"NewValue\":\"AppAddress, AppId, AvailableToOtherTenants, DisplayName, Entitlement, PublicClient, WwwHomepage, PublisherDomain, SignInAudience\",\"OldValue\":\"\"}],\"Actor\":[{\"ID\":\"AAD App Management\",\"Type\":1},{\"ID\":\"55555555-5555-5555-5555-555555555555\",\"Type\":2},{\"ID\":\"user1\",\"Type\":2},{\"ID\":\"44444444-4444-4444-4444-444444444444\",\"Type\":2},{\"ID\":\"ServicePrincipal\",\"Type\":2}],\"ActorContextId\":\"ANONYMIZED\",\"InterSystemsId\":\"TEST_CORRELATION_ID\",\"IntraSystemId\":\"11111111-1111-1111-1111-111111111111\",\"SupportTicketId\":\"\",\"Target\":[{\"ID\":\"Application_123123123123213\",\"Type\":2},{\"ID\":\"123123123123213\",\"Type\":2},{\"ID\":\"Application\",\"Type\":2},{\"ID\":\"Adobe Identity Management (SAML)\",\"Type\":1},{\"ID\":\"TEST_APP_Id\",\"Type\":2}],\"TargetContextId\":\"ANONYMIZED\"}",
"event": {
"action": "Add application",
"category": [
"iam"
],
"code": "8",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2025-11-25T10:41:35Z",
"action": {
"id": 8,
"name": "Add application",
"outcome": "success",
"target": "user"
},
"office365": {
"application": {
"id": "TEST_APP_Id",
"name": "Adobe Identity Management (SAML)"
},
"audit": {
"object_id": "Application_123123123123213"
},
"context": {
"correlation": {
"id": "TEST_CORRELATION_ID"
},
"modified_properties": [
{
"Name": "AppAddress",
"NewValue": "[\r\n {\r\n \"AddressType\": 0,\r\n \"Address\": \"https://*.services.adobe.com/federated/saml/SSO/alias/*\",\r\n \"ReplyAddressClientType\": 0,\r\n \"ReplyAddressIndex\": null,\r\n \"IsReplyAddressDefault\": false\r\n }\r\n]",
"OldValue": "[]"
},
{
"Name": "AppId",
"NewValue": "[\r\n \"TEST_APP_Id\"\r\n]",
"OldValue": "[]"
},
{
"Name": "AvailableToOtherTenants",
"NewValue": "[\r\n false\r\n]",
"OldValue": "[]"
},
{
"Name": "DisplayName",
"NewValue": "[\r\n \"Adobe Identity Management (SAML)\"\r\n]",
"OldValue": "[]"
},
{
"Name": "Entitlement",
"NewValue": "[\r\n {\r\n \"EntitlementEncodingVersion\": 2,\r\n \"EntitlementId\": \"33333333-3333-3333-3333-333333333333\",\r\n \"IsDisabled\": false,\r\n \"Origin\": 0,\r\n \"Name\": \"Access Adobe Identity Management (SAML)\",\r\n \"Description\": \"Allow the application to access Adobe Identity Management (SAML) on behalf of the signed-in user.\",\r\n \"Definition\": null,\r\n \"ClaimValue\": \"user_impersonation\",\r\n \"ResourceScopeType\": 1,\r\n \"IsPrivate\": false,\r\n \"UserConsentDisplayName\": \"Access Adobe Identity Management (SAML)\",\r\n \"UserConsentDescription\": \"Allow the application to access Adobe Identity Management (SAML) on your behalf.\",\r\n \"DirectAccessGrantTypes\": [],\r\n \"ImpersonationAccessGrantTypes\": [\r\n {\r\n \"Impersonator\": 29,\r\n \"Impersonated\": 20\r\n }\r\n ],\r\n \"EntitlementCategory\": 0,\r\n \"DependentMicrosoftGraphPermissions\": [],\r\n \"IsPreauthzOnlyDirectAccessGrant\": false,\r\n \"IsPreauthzOnlyImpersonationGrant\": false\r\n }\r\n]",
"OldValue": "[]"
},
{
"Name": "PublicClient",
"NewValue": "[\r\n false\r\n]",
"OldValue": "[]"
},
{
"Name": "WwwHomepage",
"NewValue": "[\r\n \"https://*.services.adobe.com/federated/saml/SSO/alias/*?metadata=adobeidentitymanagement|ISV9.1|primary|z\"\r\n]",
"OldValue": "[]"
},
{
"Name": "PublisherDomain",
"NewValue": "[\r\n \"ocd-testing.com\"\r\n]",
"OldValue": "[]"
},
{
"Name": "SignInAudience",
"NewValue": "[\r\n \"AzureADMyOrg\"\r\n]",
"OldValue": "[]"
},
{
"Name": "Included Updated Properties",
"NewValue": "AppAddress, AppId, AvailableToOtherTenants, DisplayName, Entitlement, PublicClient, WwwHomepage, PublisherDomain, SignInAudience",
"OldValue": ""
}
]
},
"record_id": "TEST_RECORD_ID",
"record_type": 8,
"result_status": "Success",
"target": {
"displayName": "Adobe Identity Management (SAML)"
},
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\": {\"AADSessionId\": \"44444444-4444-4444-4444-444444444444\", \"IssuedAtTime\": \"2026-04-16T13:01:17\", \"UniqueTokenId\": \"REDACTED\"}, \"CreationTime\": \"2026-04-16T13:07:07\", \"Id\": \"55555555-5555-5555-5555-555555555555\", \"Operation\": \"Set-Mailbox\", \"OrganizationId\": \"33333333-3333-3333-3333-333333333333\", \"RecordType\": 1, \"ResultStatus\": \"True\", \"UserKey\": \"john.doe@example.com\", \"UserType\": 2, \"Version\": 1, \"Workload\": \"Exchange\", \"ClientIP\": \"1.1.1.1:26061\", \"ObjectId\": \"Jane DOE\", \"UserId\": \"john.doe@example.com\", \"AppId\": \"\", \"AppPoolName\": \"MSExchangeOWAAppPool\", \"ClientAppId\": \"\", \"CorrelationID\": \"\", \"DeviceId\": \"22222222-2222-2222-2222-222222222222\", \"ExternalAccess\": false, \"OrganizationName\": \"example.onmicrosoft.com\", \"OriginatingServer\": \"HOSTNAME (15.20.9818.014)\", \"Parameters\": [{\"Name\": \"Identity\", \"Value\": \"ABC123456.PROD.OUTLOOK.COM/Microsoft Exchange Hosted Organizations/example.onmicrosoft.com/Jane DOE\"}, {\"Name\": \"ForwardingSmtpAddress\", \"Value\": \"smtp:jane.doe@example.org\"}, {\"Name\": \"DeliverToMailboxAndForward\", \"Value\": \"True\"}], \"RequestId\": \"66666666-6666-6666-6666-666666666666\", \"SessionId\": \"44444444-4444-4444-4444-444444444444\", \"TokenObjectId\": \"11111111-1111-1111-1111-111111111111\", \"TokenTenantId\": \"33333333-3333-3333-3333-333333333333\"}",
"event": {
"action": "Set-Mailbox",
"code": "1",
"outcome": "success"
},
"@timestamp": "2026-04-16T13:07:07Z",
"action": {
"id": 1,
"name": "Set-Mailbox",
"outcome": "success",
"target": "user"
},
"azuread": {
"properties": {
"uniqueTokenIdentifier": "REDACTED"
}
},
"email": {
"to": {
"address": [
"jane.doe@example.org"
]
}
},
"office365": {
"audit": {
"object_id": "Jane DOE"
},
"context": {
"aad_session_id": "44444444-4444-4444-4444-444444444444"
},
"device": {
"id": "22222222-2222-2222-2222-222222222222"
},
"exchange_admin": {
"parameters": [
"DeliverToMailboxAndForward:True",
"ForwardingSmtpAddress:smtp:jane.doe@example.org",
"Identity:ABC123456.PROD.OUTLOOK.COM/Microsoft Exchange Hosted Organizations/example.onmicrosoft.com/Jane DOE"
]
},
"record_id": "55555555-5555-5555-5555-555555555555",
"record_type": 1,
"result_status": "True",
"user_type": {
"code": 2,
"name": "Admin"
}
},
"organization": {
"id": "33333333-3333-3333-3333-333333333333"
},
"related": {
"ip": [
"1.1.1.1"
],
"user": [
"john.doe@example.com"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"port": 26061
},
"user": {
"email": "john.doe@example.com",
"id": "john.doe@example.com",
"name": "john.doe@example.com"
}
}
{
"message": "{\"CreationTime\":\"2022-04-05T20:35:01\",\"Id\":\"5615b32d-4c18-4ada-cc88-08da1743c258\",\"Operation\":\"Create\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":2,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"10033FFF80D15ECF\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"ClientIP\":\"192.0.2.1\",\"UserId\":\"user1\",\"AppId\":\"27922004-5251-4030-b22d-91ecd9a37ea4\",\"ClientIPAddress\":\"192.0.2.1\",\"ClientInfoString\":\"Client=OutlookService;Outlook-iOS/2.0;\",\"ClientRequestId\":\"1725\",\"ExternalAccess\":false,\"InternalLogonType\":0,\"LogonType\":0,\"LogonUserSid\":\"user1\",\"MailboxGuid\":\"24683bc8-fab1-48b3-b834-cb11b95bb911\",\"MailboxOwnerSid\":\"user1\",\"MailboxOwnerUPN\":\"user1\",\"OrganizationName\":\"xxxx.onmicrosoft.com\",\"OriginatingServer\":\"PR3PR03MB6601 (15.20.4200.000)\\r\\n\",\"SessionId\":\"8ad3822b-1cfd-40e7-aeaa-6d0708691ad8\",\"Item\":{\"Id\":\"LgAAAAAdhAMRqmYRzZvIAKoAL8RaDQCB1ldAzYsRRItL+noffZbOAATJxTeHAAAJ\",\"InternetMessageId\":\"<11111111111111111111111111@example.com>\",\"IsRecord\":false,\"ParentFolder\":{\"Id\":\"LgAAAAAbOnSFmOkITaMliEZRj+Z3AQAPzmaC0nx3Qo/JWqclreA/AAAEUskDAAAB\",\"Path\":\"\\\\Drafts1\"},\"SizeInBytes\":34785,\"Subject\":\"ANONYMIZED\"}}",
"event": {
"action": "Create",
"category": [
"email",
"file"
],
"code": "2",
"outcome": "success",
"type": [
"creation",
"info"
]
},
"@timestamp": "2022-04-05T20:35:01Z",
"action": {
"id": 2,
"name": "Create",
"outcome": "success",
"target": "user"
},
"email": {
"message_id": "11111111111111111111111111@example.com",
"subject": "ANONYMIZED"
},
"office365": {
"context": {
"aad_session_id": "8ad3822b-1cfd-40e7-aeaa-6d0708691ad8"
},
"exchange": {
"mailbox_guid": "24683bc8-fab1-48b3-b834-cb11b95bb911",
"mailbox_owner": {
"sid": "user1",
"upn": "user1"
}
},
"record_id": "5615b32d-4c18-4ada-cc88-08da1743c258",
"record_type": 2,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2023-09-15T18:16:53\",\"Id\":\"461a38ce-fc36-4a4d-b73e-643262cc063f\",\"Operation\":\"MailItemsAccessed\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":50,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"UserId\":\"user1\",\"AppId\":\"00000002-0000-0ff1-ce00-000000000000\",\"ClientIPAddress\":\"192.0.2.1\",\"ClientInfoString\":\"Client=OWA;Action=ViaProxy\",\"ExternalAccess\":false,\"InternalLogonType\":0,\"LogonType\":0,\"LogonUserSid\":\"S-1-2-3\",\"MailboxGuid\":\"03d9e949-cbc1-4dd2-b7ba-8a1d1e0207b5\",\"MailboxOwnerSid\":\"S-1-2-3\",\"MailboxOwnerUPN\":\"user1\",\"OperationProperties\":[{\"Name\":\"MailAccessType\",\"Value\":\"Bind\"},{\"Name\":\"IsThrottled\",\"Value\":\"False\"}],\"OrganizationName\":\"example.onmicrosoft.com\",\"OriginatingServer\":\"AM0PR07MB5763 (15.20.4200.000)\\r\\n\",\"SessionId\":\"dcdad6b2-f279-48c6-9ed8-3df0ffde4ece\",\"Folders\":[{\"FolderItems\":[{\"InternetMessageId\":\"<AM0PR07MB576312B164491AF0F9214C738DF6A@AM0PR07MB5763.eurprd07.prod.outlook.com>\",\"Sensitivity\":\"defa4170-0d19-0005-0004-bc88714345d2\",\"SizeInBytes\":3476},{\"InternetMessageId\":\"<AM0PR07MB5763A95F7E4A5BA512692F698DF6A@AM0PR07MB5763.eurprd07.prod.outlook.com>\",\"SizeInBytes\":4871},{\"InternetMessageId\":\"<AM0PR07MB57633CFE8EE2ACB8CEF184AC8DF6A@AM0PR07MB5763.eurprd07.prod.outlook.com>\",\"SizeInBytes\":4873}],\"Id\":\"LgAAAABxSjbeIoBUT6MlFIM9cqcFAQCxmw0Q8U/kQIyFE2Uk+mwoAAAAAAEPAAAB\",\"Path\":\"\\\\Brouillons\"}],\"OperationCount\":3}",
"event": {
"action": "MailItemsAccessed",
"code": "50",
"outcome": "success"
},
"@timestamp": "2023-09-15T18:16:53Z",
"action": {
"id": 50,
"name": "MailItemsAccessed",
"outcome": "success",
"target": "user"
},
"office365": {
"context": {
"aad_session_id": "dcdad6b2-f279-48c6-9ed8-3df0ffde4ece"
},
"exchange": {
"mailbox_owner": {
"sid": "S-1-2-3",
"upn": "user1"
}
},
"folders": {
"paths": [
"\\Brouillons"
]
},
"operation": {
"properties": {
"IsThrottled": "False",
"MailAccessType": "Bind"
}
},
"record_id": "461a38ce-fc36-4a4d-b73e-643262cc063f",
"record_type": 50,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"user": {
"id": "S-1-2-3",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2023-09-15T18:11:42\",\"Id\":\"d0d7820c-cdbe-4524-bf75-08dbb61736bf\",\"Operation\":\"HardDelete\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":3,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"ClientIP\":\"192.0.2.1\",\"UserId\":\"user1\",\"AppId\":\"00000002-0000-0ff1-ce00-000000000000\",\"ClientIPAddress\":\"192.0.2.1\",\"ClientInfoString\":\"Client=OWA;Action=ViaProxy\",\"ExternalAccess\":false,\"InternalLogonType\":0,\"LogonType\":0,\"LogonUserSid\":\"S-1-2-3\",\"MailboxGuid\":\"03d9e949-cbc1-4dd2-b7ba-8a1d1e0207b5\",\"MailboxOwnerSid\":\"S-1-2-3\",\"MailboxOwnerUPN\":\"user1\",\"OrganizationName\":\"example.onmicrosoft.com\",\"OriginatingServer\":\"AM0PR07MB5763 (15.20.4200.000)\\r\\n\",\"SessionId\":\"dcdad6b2-f279-48c6-9ed8-3df0ffde4ece\",\"AffectedItems\":[{\"Id\":\"RgAAAABxSjbeIoBUT6MlFIM9cqcFBwCxmw0Q8U/kQIyFE2Uk+mwoAAAAAAEbAACxmw0Q8U/kQIyFE2Uk+mwoAABVzgKRAAAJ\",\"InternetMessageId\":\"<AM0PR07MB57631C0B52D097386841A4998D37A@AM0PR07MB5763.eurprd07.prod.outlook.com>\",\"ParentFolder\":{\"Id\":\"LgAAAABxSjbeIoBUT6MlFIM9cqcFAQCxmw0Q8U/kQIyFE2Uk+mwoAAAAAAEbAAAB\",\"Path\":\"\\\\Recoverable Items\\\\Deletions\"},\"Subject\":\"\"}],\"CrossMailboxOperation\":false,\"Folder\":{\"Id\":\"LgAAAABxSjbeIoBUT6MlFIM9cqcFAQCxmw0Q8U/kQIyFE2Uk+mwoAAAAAAEbAAAB\",\"Path\":\"\\\\Recoverable Items\\\\Deletions\"}}",
"event": {
"action": "HardDelete",
"category": [
"email"
],
"code": "3",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2023-09-15T18:11:42Z",
"action": {
"id": 3,
"name": "HardDelete",
"outcome": "success",
"target": "user"
},
"office365": {
"context": {
"aad_session_id": "dcdad6b2-f279-48c6-9ed8-3df0ffde4ece"
},
"exchange": {
"email": {
"paths": [
"\\Recoverable Items\\Deletions"
],
"subjects": [
""
]
},
"mailbox_owner": {
"sid": "S-1-2-3",
"upn": "user1"
}
},
"record_id": "d0d7820c-cdbe-4524-bf75-08dbb61736bf",
"record_type": 3,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2023-08-22T13:51:02\",\"Id\":\"5f24aa82-f874-44d1-b6df-857cd9e1decf\",\"Operation\":\"SoftDelete\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":3,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"11111111111111\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"user1\",\"ClientIPAddress\":\"1.2.3.4\",\"ClientInfoString\":\"Client=MSExchangeRPC\",\"ClientProcessName\":\"OUTLOOK.EXE\",\"ClientRequestId\":\"{037FD006-A72B-49AE-4BB0-08DBA30C8729}\",\"ClientVersion\":\"16.0.15601.20364\",\"ExternalAccess\":false,\"InternalLogonType\":0,\"LogonType\":0,\"LogonUserSid\":\"S-1-2-3\",\"MailboxGuid\":\"8208550a-4001-439d-a9f6-e95d76767507\",\"MailboxOwnerSid\":\"S-1-2-3\",\"MailboxOwnerUPN\":\"user1\",\"OrganizationName\":\"example.onmicrosoft.com\",\"OriginatingServer\":\"MYSERVER (15.20.4200.000)\\r\\n\",\"SessionId\":\"77f6d9ce-da8f-46bf-a651-4bec3c189770\",\"AffectedItems\":[{\"Attachments\":\"image006.png (6438b); image007.png (449b); image008.png (448b); image009.png (449b); image010.jpg (2443b); image011.png (6444b); image012.png (447b); image013.png (448b)\",\"Id\":\"333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333\",\"InternetMessageId\":\"<44444444444444444444444444444444444444@EXAMPLE.COM>\",\"ParentFolder\":{\"Id\":\"1111111111111111111111111111111111111111111111111111111111111111\",\"Path\":\"\\\\Draft\"},\"Subject\":\"Re: HI\"}],\"CrossMailboxOperation\":false,\"Folder\":{\"Id\":\"2222222222222222222222222222222222222222222222222222222222222222\",\"Path\":\"\\\\Draft\"}}",
"event": {
"action": "SoftDelete",
"category": [
"email"
],
"code": "3",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2023-08-22T13:51:02Z",
"action": {
"id": 3,
"name": "SoftDelete",
"outcome": "success",
"target": "user"
},
"email": {
"attachments": [
{
"file": {
"name": "image006.png",
"size": 6438
}
},
{
"file": {
"name": "image007.png",
"size": 449
}
},
{
"file": {
"name": "image008.png",
"size": 448
}
},
{
"file": {
"name": "image009.png",
"size": 449
}
},
{
"file": {
"name": "image010.jpg",
"size": 2443
}
},
{
"file": {
"name": "image011.png",
"size": 6444
}
},
{
"file": {
"name": "image012.png",
"size": 447
}
},
{
"file": {
"name": "image013.png",
"size": 448
}
}
]
},
"office365": {
"context": {
"aad_session_id": "77f6d9ce-da8f-46bf-a651-4bec3c189770"
},
"exchange": {
"client_version": "16.0.15601.20364",
"email": {
"paths": [
"\\Draft"
],
"subjects": [
"Re: HI"
]
},
"mailbox_owner": {
"sid": "S-1-2-3",
"upn": "user1"
}
},
"record_id": "5f24aa82-f874-44d1-b6df-857cd9e1decf",
"record_type": 3,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"process": {
"name": "OUTLOOK.EXE"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "11111111111111",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\":{\"APIId\":\"\"},\"CreationTime\":\"2025-09-16T14:46:55\",\"Id\":\"135ddd32-fee4-4f54-8606-7f203190b25f\",\"Operation\":\"SoftDelete\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":3,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"11111111111111\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"user1\",\"ActorInfoString\":\"OUTLOOK.EXE/16.0.10417.20051\",\"ClientIPAddress\":\"1.2.3.4\",\"ClientInfoString\":\"Client=MSExchangeRPC\",\"ClientProcessName\":\"OUTLOOK.EXE\",\"ClientRequestId\":\"{D10D3A8A-BCFF-481B-B609-2AE0B1DE9B14}\",\"ClientVersion\":\"16.0.10417.20051\",\"ExternalAccess\":false,\"InternalLogonType\":0,\"LogonType\":0,\"LogonUserSid\":\"S-1-2-3\",\"MailboxGuid\":\"9f63ab44-248d-43a2-8565-63589e5232db\",\"MailboxOwnerSid\":\"S-1-2-3\",\"MailboxOwnerUPN\":\"user1\",\"OrganizationName\":\"example.onmicrosoft.com\",\"OriginatingServer\":\"MYSERVER (15.20.4200.000)\\r\\n\",\"SessionId\":\"70d4272c-db05-4e17-90a6-5c475bab04b7\",\"AffectedItems\":[{\"Attachments\":\"tps (report) 1.docx (1024b); image001.jpg (2048b); image002.jpg (4096b); image003.jpg (8192b)\",\"Id\":\"ABCDEF0123456\",\"InternetMessageId\":\"<message.id.test@0123456789.userabc.prod.outlook.com>\",\"ParentFolder\":{\"Id\":\"908eca3617c16126164465a986b6a2610f84efdcf91c46dc37a34f68954e2a3c\",\"Path\":\"\\\\Test\"},\"Subject\":\"Report\"}],\"CrossMailboxOperation\":false,\"Folder\":{\"Id\":\"908eca3617c16126164465a986b6a2610f84efdcf91c46dc37a34f68954e2a3c\",\"Path\":\"\\\\Test\"},\"AssociatedAdminUnits\":[\"4aef334f-5097-4b40-9286-d7b2efcd57bf\"]}",
"event": {
"action": "SoftDelete",
"category": [
"email"
],
"code": "3",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2025-09-16T14:46:55Z",
"action": {
"id": 3,
"name": "SoftDelete",
"outcome": "success",
"target": "user"
},
"email": {
"attachments": [
{
"file": {
"name": "tps (report) 1.docx",
"size": 1024
}
},
{
"file": {
"name": "image001.jpg",
"size": 2048
}
},
{
"file": {
"name": "image002.jpg",
"size": 4096
}
},
{
"file": {
"name": "image003.jpg",
"size": 8192
}
}
]
},
"office365": {
"context": {
"aad_session_id": "70d4272c-db05-4e17-90a6-5c475bab04b7"
},
"exchange": {
"client_version": "16.0.10417.20051",
"email": {
"paths": [
"\\Test"
],
"subjects": [
"Report"
]
},
"mailbox_owner": {
"sid": "S-1-2-3",
"upn": "user1"
}
},
"record_id": "135ddd32-fee4-4f54-8606-7f203190b25f",
"record_type": 3,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"process": {
"name": "OUTLOOK.EXE"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "11111111111111",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\":{\"AADSessionId\":\"98fb5d83-9a00-4efc-816e-22f61c2d7733\",\"APIId\":\"3CF2EC34-D27B-4E15-9D67-1D77873D8FCC\",\"ClientAppId\":\"3a278062-7639-4075-8973-bd650d7bf415\",\"IssuedAtTime\":\"2025-09-23T09:13:33\",\"UniqueTokenId\":\"0000000000000000000000\"},\"CreationTime\":\"2025-09-23T09:43:13\",\"Id\":\"79971dfe-b09d-4caa-99f1-b86cd51bdbbe\",\"Operation\":\"SoftDelete\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":3,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"user1\",\"AuthType\":\"Bearer\",\"ClientAppId\":\"3a278062-7639-4075-8973-bd650d7bf415\",\"ClientIPAddress\":\"1.2.3.4\",\"ClientInfoString\":\"Client=OWA;Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/1.2.3.4 Safari/537.36;\",\"ExternalAccess\":false,\"InternalLogonType\":0,\"LogonType\":0,\"LogonUserSid\":\"S-1-2-3\",\"MailboxGuid\":\"10842c9e-1cd8-40cf-828f-412a3e28a70f\",\"MailboxOwnerSid\":\"S-1-2-3\",\"MailboxOwnerUPN\":\"user1\",\"OrganizationName\":\"example.onmicrosoft.com\",\"OriginatingServer\":\"SERVER (15.20.4200.000)\\r\\n\",\"TokenObjectId\":\"cd57fb1a-c318-4941-bb6e-e81ee7a18350\",\"TokenTenantId\":\"ANONYMIZED\",\"TokenType\":\"V1AppActAs\",\"AffectedItems\":[{\"Attachments\":\"C:\\\\Users\\\\USERDIR\\\\AppData\\\\Local\\\\Microsoft\\\\Windows\\\\Temporary Internet Files\\\\Content.Outlook\\\\ABCDEF\\\\1.pdf (9731941b)\",\"Id\":\"111111111111111111111111/222222222222U/A\",\"InternetMessageId\":\"<message.id.test@0123456789.userabc.mail.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"},\"Subject\":\"SUBJECT\"},{\"Attachments\":\"C:\\\\Users\\\\USERDIR\\\\AppData\\\\Local\\\\Microsoft\\\\Windows\\\\Temporary Internet Files\\\\Content.Outlook\\\\ABCDEF\\\\1.pdf (9731941b)\",\"Id\":\"111111111111111111111111/222222222222VAA\",\"InternetMessageId\":\"<message.id.test2@0123456789.userabc.mail.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"},\"Subject\":\"SUBJECT2\"},{\"Attachments\":\"2.jpg (3440100b)\",\"Id\":\"111111111111111111111111/222222222222VBA\",\"InternetMessageId\":\"<1@email.android.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"}},{\"Attachments\":\"3.jpg (3405444b)\",\"Id\":\"111111111111111111111111/222222222222VCA\",\"InternetMessageId\":\"<2@email.android.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"}},{\"Attachments\":\"4.jpg (3184493b)\",\"Id\":\"111111111111111111111111/222222222222VDA\",\"InternetMessageId\":\"<3@email.android.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"}}],\"CrossMailboxOperation\":false,\"Folder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"}}",
"event": {
"action": "SoftDelete",
"category": [
"email"
],
"code": "3",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2025-09-23T09:43:13Z",
"action": {
"id": 3,
"name": "SoftDelete",
"outcome": "success",
"target": "user"
},
"azuread": {
"properties": {
"uniqueTokenIdentifier": "0000000000000000000000"
}
},
"email": {
"attachments": [
{
"file": {
"name": "1.pdf",
"size": 9731941
}
},
{
"file": {
"name": "1.pdf",
"size": 9731941
}
},
{
"file": {
"name": "2.jpg",
"size": 3440100
}
},
{
"file": {
"name": "3.jpg",
"size": 3405444
}
},
{
"file": {
"name": "4.jpg",
"size": 3184493
}
}
]
},
"office365": {
"context": {
"aad_session_id": "98fb5d83-9a00-4efc-816e-22f61c2d7733",
"api_id": "3CF2EC34-D27B-4E15-9D67-1D77873D8FCC",
"client": {
"id": "3a278062-7639-4075-8973-bd650d7bf415"
}
},
"exchange": {
"email": {
"paths": [
"\\Drafts",
"\\Drafts",
"\\Drafts",
"\\Drafts",
"\\Drafts"
],
"subjects": [
"",
"",
"",
"SUBJECT",
"SUBJECT2"
]
},
"mailbox_owner": {
"sid": "S-1-2-3",
"upn": "user1"
}
},
"record_id": "79971dfe-b09d-4caa-99f1-b86cd51bdbbe",
"record_type": 3,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\":{\"AADSessionId\":\"98fb5d83-9a00-4efc-816e-22f61c2d7733\",\"APIId\":\"3CF2EC34-D27B-4E15-9D67-1D77873D8FCC\",\"ClientAppId\":\"3a278062-7639-4075-8973-bd650d7bf415\",\"IssuedAtTime\":\"2025-09-23T09:13:33\",\"UniqueTokenId\":\"0000000000000000000000\"},\"CreationTime\":\"2025-09-23T09:43:13\",\"Id\":\"79971dfe-b09d-4caa-99f1-b86cd51bdbbe\",\"Operation\":\"SoftDelete\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":3,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"user1\",\"AuthType\":\"Bearer\",\"ClientAppId\":\"3a278062-7639-4075-8973-bd650d7bf415\",\"ClientIPAddress\":\"1.2.3.4\",\"ClientInfoString\":\"Client=OWA;Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/1.2.3.4 Safari/537.36;\",\"ExternalAccess\":false,\"InternalLogonType\":0,\"LogonType\":0,\"LogonUserSid\":\"S-1-2-3\",\"MailboxGuid\":\"10842c9e-1cd8-40cf-828f-412a3e28a70f\",\"MailboxOwnerSid\":\"S-1-2-3\",\"MailboxOwnerUPN\":\"user1\",\"OrganizationName\":\"example.onmicrosoft.com\",\"OriginatingServer\":\"SERVER (15.20.4200.000)\\r\\n\",\"TokenObjectId\":\"cd57fb1a-c318-4941-bb6e-e81ee7a18350\",\"TokenTenantId\":\"ANONYMIZED\",\"TokenType\":\"V1AppActAs\",\"AffectedItems\":[{\"Attachments\":\"C:\\\\Users\\\\USERDIR\\\\AppData\\\\Local\\\\Microsoft\\\\Windows\\\\Temporary Internet Files\\\\Content.Outlook\\\\ABCDEF\\\\1.pdf (9731941b)\",\"Id\":\"111111111111111111111111/222222222222U/A\",\"InternetMessageId\":\"<message.id.test@0123456789.userabc.mail.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"},\"Subject\":\"SUBJECT\"},{\"Attachments\":\"C:\\\\Users\\\\USERDIR\\\\AppData\\\\Local\\\\Microsoft\\\\Windows\\\\Temporary Internet Files\\\\Content.Outlook\\\\ABCDEF\\\\1.pdf (9731941b)\",\"Id\":\"111111111111111111111111/222222222222VAA\",\"InternetMessageId\":\"<message.id.test2@0123456789.userabc.mail.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"},\"Subject\":\"SUBJECT2\"},{\"Attachments\":\"2.jpg (3440100b)\",\"Id\":\"111111111111111111111111/222222222222VBA\",\"InternetMessageId\":\"<1@email.android.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"}},{\"Attachments\":\"3\\n .jpg (3405444b)\",\"Id\":\"111111111111111111111111/222222222222VCA\",\"InternetMessageId\":\"<2@email.android.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"}},{\"Attachments\":\"4.jpg (3184493b)\",\"Id\":\"111111111111111111111111/222222222222VDA\",\"InternetMessageId\":\"<3@email.android.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"}}],\"CrossMailboxOperation\":false,\"Folder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"}}",
"event": {
"action": "SoftDelete",
"category": [
"email"
],
"code": "3",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2025-09-23T09:43:13Z",
"action": {
"id": 3,
"name": "SoftDelete",
"outcome": "success",
"target": "user"
},
"azuread": {
"properties": {
"uniqueTokenIdentifier": "0000000000000000000000"
}
},
"email": {
"attachments": [
{
"file": {
"name": "1.pdf",
"size": 9731941
}
},
{
"file": {
"name": "1.pdf",
"size": 9731941
}
},
{
"file": {
"name": "2.jpg",
"size": 3440100
}
},
{
"file": {
"name": "3\n .jpg",
"size": 3405444
}
},
{
"file": {
"name": "4.jpg",
"size": 3184493
}
}
]
},
"office365": {
"context": {
"aad_session_id": "98fb5d83-9a00-4efc-816e-22f61c2d7733",
"api_id": "3CF2EC34-D27B-4E15-9D67-1D77873D8FCC",
"client": {
"id": "3a278062-7639-4075-8973-bd650d7bf415"
}
},
"exchange": {
"email": {
"paths": [
"\\Drafts",
"\\Drafts",
"\\Drafts",
"\\Drafts",
"\\Drafts"
],
"subjects": [
"",
"",
"",
"SUBJECT",
"SUBJECT2"
]
},
"mailbox_owner": {
"sid": "S-1-2-3",
"upn": "user1"
}
},
"record_id": "79971dfe-b09d-4caa-99f1-b86cd51bdbbe",
"record_type": 3,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\":{\"AADSessionId\":\"98fb5d83-9a00-4efc-816e-22f61c2d7733\",\"APIId\":\"3CF2EC34-D27B-4E15-9D67-1D77873D8FCC\",\"ClientAppId\":\"3a278062-7639-4075-8973-bd650d7bf415\",\"IssuedAtTime\":\"2025-09-23T09:13:33\",\"UniqueTokenId\":\"0000000000000000000000\"},\"CreationTime\":\"2025-09-23T09:43:13\",\"Id\":\"79971dfe-b09d-4caa-99f1-b86cd51bdbbe\",\"Operation\":\"SoftDelete\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":3,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"user1\",\"AuthType\":\"Bearer\",\"ClientAppId\":\"3a278062-7639-4075-8973-bd650d7bf415\",\"ClientIPAddress\":\"1.2.3.4\",\"ClientInfoString\":\"Client=OWA;Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/1.2.3.4 Safari/537.36;\",\"ExternalAccess\":false,\"InternalLogonType\":0,\"LogonType\":0,\"LogonUserSid\":\"S-1-2-3\",\"MailboxGuid\":\"10842c9e-1cd8-40cf-828f-412a3e28a70f\",\"MailboxOwnerSid\":\"S-1-2-3\",\"MailboxOwnerUPN\":\"user1\",\"OrganizationName\":\"example.onmicrosoft.com\",\"OriginatingServer\":\"SERVER (15.20.4200.000)\\r\\n\",\"TokenObjectId\":\"cd57fb1a-c318-4941-bb6e-e81ee7a18350\",\"TokenTenantId\":\"ANONYMIZED\",\"TokenType\":\"V1AppActAs\",\"AffectedItems\":[{\"Attachments\":\"C:\\\\Users\\\\USERDIR\\\\AppData\\\\Local\\\\Microsoft\\\\Windows\\\\Temporary Internet Files\\\\Content.Outlook\\\\ABCDEF\\\\1.pdf (9731941b)\",\"Id\":\"111111111111111111111111/222222222222U/A\",\"InternetMessageId\":\"<message.id.test@0123456789.userabc.mail.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"},\"Subject\":\"SUBJECT\"},{\"Attachments\":\"C:\\\\Users\\\\USERDIR\\\\AppData\\\\Local\\\\Microsoft\\\\Windows\\\\Temporary Internet Files\\\\Content.Outlook\\\\ABCDEF\\\\1.pdf (9731941b)\",\"Id\":\"111111111111111111111111/222222222222VAA\",\"InternetMessageId\":\"<message.id.test2@0123456789.userabc.mail.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"},\"Subject\":\"SUBJECT2\"},{\"Attachments\":\"2.jpg (3440100b)\",\"Id\":\"111111111111111111111111/222222222222VBA\",\"InternetMessageId\":\"<1@email.android.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"}},{\"Attachments\":\"3 \\\"test\\\".jpg (3405444b)\",\"Id\":\"111111111111111111111111/222222222222VCA\",\"InternetMessageId\":\"<2@email.android.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"}},{\"Attachments\":\"4.jpg (3184493b)\",\"Id\":\"111111111111111111111111/222222222222VDA\",\"InternetMessageId\":\"<3@email.android.com>\",\"ParentFolder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"}}],\"CrossMailboxOperation\":false,\"Folder\":{\"Id\":\"33333333333\",\"Path\":\"\\\\Drafts\"}}",
"event": {
"action": "SoftDelete",
"category": [
"email"
],
"code": "3",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2025-09-23T09:43:13Z",
"action": {
"id": 3,
"name": "SoftDelete",
"outcome": "success",
"target": "user"
},
"azuread": {
"properties": {
"uniqueTokenIdentifier": "0000000000000000000000"
}
},
"email": {
"attachments": [
{
"file": {
"name": "1.pdf",
"size": 9731941
}
},
{
"file": {
"name": "1.pdf",
"size": 9731941
}
},
{
"file": {
"name": "2.jpg",
"size": 3440100
}
},
{
"file": {
"name": "3 \"test\".jpg",
"size": 3405444
}
},
{
"file": {
"name": "4.jpg",
"size": 3184493
}
}
]
},
"office365": {
"context": {
"aad_session_id": "98fb5d83-9a00-4efc-816e-22f61c2d7733",
"api_id": "3CF2EC34-D27B-4E15-9D67-1D77873D8FCC",
"client": {
"id": "3a278062-7639-4075-8973-bd650d7bf415"
}
},
"exchange": {
"email": {
"paths": [
"\\Drafts",
"\\Drafts",
"\\Drafts",
"\\Drafts",
"\\Drafts"
],
"subjects": [
"",
"",
"",
"SUBJECT",
"SUBJECT2"
]
},
"mailbox_owner": {
"sid": "S-1-2-3",
"upn": "user1"
}
},
"record_id": "79971dfe-b09d-4caa-99f1-b86cd51bdbbe",
"record_type": 3,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\":{\"AADSessionId\":\"ANONYMIZED\",\"APIId\":\"ANONYMIZED\",\"ClientAppId\":\"ANONYMIZED\",\"IssuedAtTime\":\"2025-10-26T13:12:18\",\"UniqueTokenId\":\"AAAAAAAAAAAAAAAAAAAAAA\"},\"CreationTime\":\"2025-10-27T07:09:33\",\"Id\":\"ANONYMIZED\",\"Operation\":\"MailItemsAccessed\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":50,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"0000000000000000\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"UserId\":\"user1\",\"AppId\":\"ANONYMIZED\",\"ClientAppId\":\"ANONYMIZED\",\"ClientIPAddress\":\"1.2.3.4\",\"ClientInfoString\":\"Client=OWA;Action=ViaProxy\",\"DeviceId\":\"ANONYMIZED\",\"ExternalAccess\":false,\"InternalLogonType\":0,\"LogonType\":0,\"LogonUserSid\":\"S-1-2-3\",\"MailboxGuid\":\"ANONYMIZED\",\"MailboxOwnerSid\":\"S-1-2-3\",\"MailboxOwnerUPN\":\"user1\",\"OperationProperties\":[{\"Name\":\"MailAccessType\",\"Value\":\"Bind\"}],\"OrganizationName\":\"example.onmicrosoft.com\",\"OriginatingServer\":\"EXCH01 (15.20.4200.000)\\r\\n\",\"TokenObjectId\":\"ANONYMIZED\",\"TokenTenantId\":\"ANONYMIZED\",\"Folders\":[{\"FolderItems\":[{\"Id\":\"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA\",\"ImmutableId\":\"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA\",\"InternetMessageId\":\"<abcdef@mail.example.com>\",\"SizeInBytes\":123456}],\"Id\":\"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA\",\"Path\":\"\\\\Inbox\"}],\"OperationCount\":1}",
"event": {
"action": "MailItemsAccessed",
"code": "50",
"outcome": "success"
},
"@timestamp": "2025-10-27T07:09:33Z",
"action": {
"id": 50,
"name": "MailItemsAccessed",
"outcome": "success",
"target": "user"
},
"azuread": {
"properties": {
"uniqueTokenIdentifier": "AAAAAAAAAAAAAAAAAAAAAA"
}
},
"office365": {
"context": {
"aad_session_id": "ANONYMIZED",
"api_id": "ANONYMIZED",
"client": {
"id": "ANONYMIZED"
}
},
"device": {
"id": "ANONYMIZED"
},
"exchange": {
"mailbox_owner": {
"sid": "S-1-2-3",
"upn": "user1"
}
},
"folders": {
"paths": [
"\\Inbox"
]
},
"operation": {
"properties": {
"MailAccessType": "Bind"
}
},
"record_id": "ANONYMIZED",
"record_type": 50,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "S-1-2-3",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\": {\"APIId\": \"\"}, \"CreationTime\": \"2026-01-19T14:44:15\", \"Id\": \"66666666-6666-6666-6666-666666666666\", \"Operation\": \"SendAs\", \"OrganizationId\": \"77777777-7777-7777-7777-777777777777\", \"RecordType\": 2, \"ResultStatus\": \"Succeeded\", \"UserKey\": \"ANONYMIZED\", \"UserType\": 0, \"Version\": 1, \"Workload\": \"Exchange\", \"ClientIP\": \"1.1.1.1\", \"UserId\": \"johndoe@example.net\", \"ActorInfoString\": \"OUTLOOK.EXE/16.0.19328.20266\", \"ClientIPAddress\": \"1.1.1.1\", \"ClientInfoString\": \"Client=MSExchangeRPC\", \"ClientProcessName\": \"OUTLOOK.EXE\", \"ClientRequestId\": \"{11111111-1111-1111-1111-111111111111}\", \"ClientVersion\": \"16.0.19328.20266\", \"ExternalAccess\": false, \"HostAppId\": \"44444444-4444-4444-4444-444444444444\", \"InternalLogonType\": 0, \"LogonType\": 2, \"LogonUserSid\": \"S-1-2-3\", \"MailboxGuid\": \"55555555-5555-5555-5555-555555555555\", \"MailboxOwnerSid\": \"S-1-2-3\", \"MailboxOwnerUPN\": \"johndoe@example.com\", \"OrganizationName\": \"example.org\", \"OriginatingServer\": \"HOSTNAME (15.20.4200.000)\\r\\n\", \"SessionId\": \"33333333-3333-3333-3333-333333333333\", \"Item\": {\"Id\": \"REDACTED\", \"ImmutableId\": \"REDACTED\", \"InternetMessageId\": \"<1111111111111111111111111111111111111111111111111@HOSTNAME.example.com>\", \"ParentFolder\": {\"Id\": \"REDACTED\", \"Path\": \"REDACTED\"}, \"SizeInBytes\": 21219, \"Subject\": \"Security alert: Fraudulent messages\"}, \"SaveToSentItems\": true, \"SendAsUserMailboxGuid\": \"22222222-2222-2222-2222-222222222222\", \"SendAsUserSmtp\": \"janedoe@example.com\"}",
"event": {
"action": "SendAs",
"category": [
"email",
"file"
],
"code": "2",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2026-01-19T14:44:15Z",
"action": {
"id": 2,
"name": "SendAs",
"outcome": "success",
"target": "user"
},
"email": {
"message_id": "1111111111111111111111111111111111111111111111111@HOSTNAME.example.com",
"subject": "Security alert: Fraudulent messages"
},
"office365": {
"context": {
"aad_session_id": "33333333-3333-3333-3333-333333333333"
},
"exchange": {
"mailbox_guid": "55555555-5555-5555-5555-555555555555",
"mailbox_owner": {
"sid": "S-1-2-3",
"upn": "johndoe@example.com"
},
"send_as_user": {
"mailbox_guid": "22222222-2222-2222-2222-222222222222",
"smtp": "janedoe@example.com"
}
},
"record_id": "66666666-6666-6666-6666-666666666666",
"record_type": 2,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "77777777-7777-7777-7777-777777777777"
},
"related": {
"ip": [
"1.1.1.1"
],
"user": [
"johndoe@example.net"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"user": {
"email": "johndoe@example.net",
"id": "S-1-2-3",
"name": "johndoe@example.net"
}
}
{
"message": "{\"CreationTime\":\"2023-08-22T13:49:36\",\"Id\":\"5f24aa82-f874-44d1-b6df-857cd9e1decf\",\"Operation\":\"Update\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":2,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"1111111111111111\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"ClientIP\":\"192.0.2.1\",\"UserId\":\"user1\",\"AppId\":\"037fd006-a72b-49ae-4bb0-08dba30c8729\",\"ClientAppId\":\"037fd006-a72b-49ae-4bb0-08dba30c8729\",\"ClientIPAddress\":\"2603:1026:c09:834::5\",\"ClientInfoString\":\"Client=REST;Client=RESTSystem;;\",\"ClientRequestId\":\"037fd006-a72b-49ae-4bb0-08dba30c8729\",\"ExternalAccess\":false,\"InternalLogonType\":0,\"LogonType\":0,\"LogonUserSid\":\"user1\",\"MailboxGuid\":\"8208550a-4001-439d-a9f6-e95d76767507\",\"MailboxOwnerSid\":\"user1\",\"MailboxOwnerUPN\":\"user1\",\"OrganizationName\":\"example.onmicrosoft.com\",\"OriginatingServer\":\"MYSERVER (15.20.4200.000)\\r\\n\",\"Item\":{\"Id\":\"333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333333\",\"InternetMessageId\":\"<44444444444444444444444444444444444444@EXAMPLE.COM>\",\"ParentFolder\":{\"Id\":\"1111111111111111111111111111111111111111111111111111111111111111\",\"Path\":\"\\\\Draft\"},\"SizeInBytes\":70806,\"Subject\":\"ANONYMIZED\"},\"ModifiedProperties\":[\"MapiEndTime\",\"MapiPREndDate\",\"TimeZone\",\"TimeZoneBlob\",\"TimeZoneDefinitionStart\",\"TimeZoneDefinitionEnd\",\"MapiStartTime\",\"MapiPRStartDate\",\"MapiIsAllDayEvent\",\"TimeZoneDefinitionRecurring\",\"AppointmentRecurring\",\"AttendeeCriticalChangeTime\",\"Location\",\"SendRichInfo\",\"PartnerNetworkUserId\",\"PartnerNetworkId\",\"SentRepresentingDisplayName\",\"SentRepresentingEmailAddress\",\"SentRepresentingType\",\"SentRepresentingEntryId\",\"SentRepresentingSmtpAddress\",\"SipUri\",\"SentRepresentingSID\",\"When\",\"BirthdayContactAttributionDisplayName\",\"BirthdayLocal\",\"ReceivedByName\",\"ReceivedByEmailAddress\",\"ReceivedByAddrType\",\"ReceivedByEntryId\",\"ReceivedBySmtpAddress\",\"AllAttachmentsHidden\",\"SenderDisplayName\",\"SenderEmailAddress\",\"SenderAddressType\",\"SenderEntryId\",\"SenderSmtpAddress\",\"SenderSID\",\"SentTime\",\"HtmlBody\",\"RtfBody\",\"TextBody\",\"DisplayName\",\"CreationTime\",\"MapiSubject\",\"NormalizedSubjectInternal\",\"SubjectPrefixInternal\",\"ItemClass\",\"ReplyForwardStatus\",\"ReceivedTime\",\"RecipientCollection\"]}",
"event": {
"action": "Update",
"category": [
"email",
"file"
],
"code": "2",
"outcome": "success",
"type": [
"change",
"info"
]
},
"@timestamp": "2023-08-22T13:49:36Z",
"action": {
"id": 2,
"name": "Update",
"outcome": "success",
"target": "user"
},
"email": {
"message_id": "44444444444444444444444444444444444444@EXAMPLE.COM",
"subject": "ANONYMIZED"
},
"office365": {
"context": {
"client": {
"id": "037fd006-a72b-49ae-4bb0-08dba30c8729"
}
},
"exchange": {
"mailbox_guid": "8208550a-4001-439d-a9f6-e95d76767507",
"mailbox_owner": {
"sid": "user1",
"upn": "user1"
}
},
"record_id": "5f24aa82-f874-44d1-b6df-857cd9e1decf",
"record_type": 2,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\":{\"ClientAppName\":\"MeTA\",\"CorrelationId\":\"27de65c0-1c43-4d70-9a4d-45a66418dbd6\"},\"CreationTime\":\"2024-11-29T12:31:12\",\"Id\":\"609745a8-8ec0-4305-8607-fa95f45cf370\",\"Operation\":\"FileDownloaded\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":6,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"OneDrive\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"urn:spo:guest#john.doe@example.com\",\"AuthenticationType\":\"OAuth\",\"BrowserName\":\"\",\"BrowserVersion\":\"\",\"CorrelationId\":\"27de65c0-1c43-4d70-9a4d-45a66418dbd6\",\"DoNotDistributeEvent\":true,\"EventSource\":\"SharePoint\",\"GeoLocation\":\"EUR\",\"IsManagedDevice\":false,\"ItemType\":\"File\",\"ListId\":\"56391ee5-91aa-44f9-810e-a5dc47abbb02\",\"ListItemUniqueId\":\"1d91eda8-2918-42f0-8f2b-88dd9aaffcdf\",\"Platform\":\"Service\",\"Site\":\"582d798a-ba87-4a78-8792-87db9262b0a3\",\"UserAgent\":\"OneDriveMpc-Transform_Zip/1.0\",\"UserSessionId\":\"b332294a-fad5-45a0-8761-63922a2544bf\",\"WebId\":\"ead1e78b-1d0c-4251-920a-f4fb48fce5e2\",\"DeviceDisplayName\":\"5.6.7.8\",\"EventSignature\":\"SOME_SIGNATURE\",\"FileSizeBytes\":26860827,\"HighPriorityMediaProcessing\":false,\"ListBaseType\":1,\"ListServerTemplate\":700,\"SourceFileExtension\":\"zip\",\"ZipFileName\":\"1.zip\",\"SiteUrl\":\"https://example.com/\",\"SourceRelativeUrl\":\"Documents/IMT MBA\",\"SourceFileName\":\"1.zip\",\"ApplicationDisplayName\":\"MeTA\",\"ObjectId\":\"https://example.com/1.zip\"}",
"event": {
"action": "FileDownloaded",
"category": [
"file"
],
"code": "6",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-11-29T12:31:12Z",
"action": {
"id": 6,
"name": "FileDownloaded",
"outcome": "success",
"properties": [
{
"SiteUrl": "https://example.com/",
"SourceFileName": "1.zip",
"SourceRelativeUrl": "Documents/IMT MBA",
"UserAgent": "OneDriveMpc-Transform_Zip/1.0"
}
],
"target": "user"
},
"file": {
"directory": "Documents/IMT MBA",
"extension": "zip",
"name": "1.zip",
"size": 26860827
},
"office365": {
"audit": {
"item_type": "File",
"object_id": "https://example.com/1.zip",
"platform": "Service"
},
"context": {
"authentication_type": "OAuth",
"client": {
"name": "MeTA"
},
"correlation": {
"id": "27de65c0-1c43-4d70-9a4d-45a66418dbd6"
}
},
"device": {
"is_managed": false
},
"record_id": "609745a8-8ec0-4305-8607-fa95f45cf370",
"record_type": 6,
"user_type": {
"code": 0,
"is_external": true,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"john.doe@example.com"
]
},
"service": {
"name": "OneDrive"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"url": {
"domain": "example.com",
"full": "https://example.com/1.zip",
"original": "https://example.com/1.zip",
"path": "/1.zip",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"email": "john.doe@example.com",
"id": "user1",
"name": "john.doe@example.com"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Other",
"original": "OneDriveMpc-Transform_Zip/1.0",
"os": {
"name": "Other"
}
}
}
{
"message": "{\"CreationTime\":\"2025-08-08T10:12:51\",\"Id\":\"123123213-a9a8-123-885c-123123123\",\"Operation\":\"AlertTriggered\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"31f138b3-da55-13123123-9200-08ddd663dfb8\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertId\":\"31f138b3-da55-d6c2-123123123213-08ddd663dfb8\",\"AlertLinks\":[{\"AlertLinkHref\":\"\"}],\"AlertType\":\"Custom\",\"Category\":\"DataLossPrevention\",\"Comments\":\"New alert\",\"Data\":\"{\\\"f3u\\\":\\\"john.doe@example.com\\\",\\\"ts\\\":\\\"2025-08-08T10:10:00.0000000Z\\\",\\\"te\\\":\\\"2025-08-08T10:11:00.0000000Z\\\",\\\"op\\\":\\\"DlpRuleMatch\\\",\\\"wl\\\":\\\"Endpoint\\\",\\\"tid\\\":\\\"123123123-62b5-46fa-adc3-117eedef841e\\\",\\\"tdc\\\":\\\"1\\\",\\\"reid\\\":\\\"87778fde-76c9-123123123-a42b-45a6af122292\\\",\\\"dpn\\\":\\\"Endpoint DLP Web - Low & High\\\",\\\"dpid\\\":\\\"2a236c69-8cea-123123312-a393-45f6e7ab87f3\\\",\\\"drn\\\":\\\"Low volume of content detected National ID Web\\\",\\\"drid\\\":\\\"83736f8f-428a-41dc-dqwerqerqwe-ae4e272ac590\\\",\\\"dact\\\":\\\"\\\",\\\"von\\\":\\\"REDACTED\\\",\\\"sitmi\\\":\\\"7f0e921c-9677-435b-aba2-123123123213:Malaysia Identity Card Number:1:123;12312312-c42e-47a0-9d85-bebed1c237d4:Germany Identity Card Number:1:123;123123123123-6d9d-4be1-a154-b531f7a91b41:EU National Identification Number:3:93123\\\",\\\"sict\\\":\\\"None;None;None\\\",\\\"dprm\\\":\\\"Enable\\\",\\\"eop\\\":\\\"FileUploadedToCloud\\\",\\\"enmd\\\":\\\"Audit\\\",\\\"tdmn\\\":\\\"web.whatsapp.com\\\",\\\"app\\\":\\\"chrome.exe\\\",\\\"ofph\\\":\\\"C:\\\\\\\\Users\\\\\\\\TestUser\\\\\\\\Downloads\\\\\\\\urururururutyrtyrty123-vaf.pdf\\\",\\\"dn\\\":\\\"lt-pf463p9n\\\",\\\"mddid\\\":\\\"123123123123123\\\",\\\"rmse\\\":\\\"False\\\",\\\"efs\\\":\\\"138307\\\",\\\"ecip\\\":\\\"1.2.3.4\\\",\\\"rtp\\\":108,\\\"wsrt\\\":\\\"2025-08-08T10:12:35\\\",\\\"mdt\\\":\\\"Audit\\\",\\\"rid\\\":\\\"9292992929292-0402-4b20-8faa-93efc2dd5672\\\",\\\"cid\\\":\\\"9ac45ff2-5c21-4e73-bf4a-1i1i1188181\\\",\\\"ad\\\":\\\"\\\",\\\"lon\\\":\\\"DlpRuleMatch\\\",\\\"an\\\":\\\"DLP-Low volume of content detected National ID Web\\\",\\\"sev\\\":\\\"Low\\\"}\",\"Name\":\"DLP-Low volume of content detected National ID Web\",\"PolicyId\":\"812812812812-123123-4e73-bf4a-fdcc40cbe8e0\",\"Severity\":\"Low\",\"Source\":\"Office 365 Security & Compliance\",\"Status\":\"Active\"}",
"event": {
"action": "AlertTriggered",
"category": [
"intrusion_detection"
],
"code": "40",
"kind": "alert",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2025-08-08T10:12:51Z",
"action": {
"id": 40,
"name": "AlertTriggered",
"outcome": "success",
"target": "user"
},
"email": {
"subject": "REDACTED"
},
"office365": {
"alert": {
"category": "DataLossPrevention",
"display_name": "DLP-Low volume of content detected National ID Web",
"id": "31f138b3-da55-d6c2-123123123213-08ddd663dfb8",
"severity": "Low",
"source": "Office 365 Security & Compliance",
"status": "Active"
},
"app": "chrome.exe",
"audit": {
"object_id": "31f138b3-da55-13123123-9200-08ddd663dfb8"
},
"dn": "lt-pf463p9n",
"dprm": "Enable",
"enmd": "Audit",
"eop": "FileUploadedToCloud",
"ofph": "C:\\Users\\TestUser\\Downloads\\urururururutyrtyrty123-vaf.pdf",
"record_id": "123123213-a9a8-123-885c-123123123",
"record_type": 40,
"result_status": "Succeeded",
"tdmn": "web.whatsapp.com",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"john.doe"
]
},
"rule": {
"id": "812812812812-123123-4e73-bf4a-fdcc40cbe8e0"
},
"service": {
"name": "SecurityComplianceCenter"
},
"user": {
"domain": "example.com",
"email": "john.doe@example.com",
"name": "john.doe"
}
}
{
"message": "{\"CreationTime\":\"2025-08-08T09:55:45\",\"Id\":\"uuid-1\",\"Operation\":\"AlertTriggered\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"uuid-3\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertId\":\"uuid-3\",\"AlertLinks\":[{\"AlertLinkHref\":\"\"}],\"AlertType\":\"Custom\",\"Category\":\"DataLossPrevention\",\"Comments\":\"New alert\",\"Data\":\"{\\\"f3u\\\":\\\"user1@example.com\\\",\\\"ts\\\":\\\"2025-08-08T09:53:00.0000000Z\\\",\\\"te\\\":\\\"2025-08-08T09:54:00.0000000Z\\\",\\\"op\\\":\\\"DlpRuleMatch\\\",\\\"wl\\\":\\\"Endpoint\\\",\\\"tid\\\":\\\"uuid-2\\\",\\\"tdc\\\":\\\"1\\\",\\\"reid\\\":\\\"uuid-4\\\",\\\"dpn\\\":\\\"Endpoint DLP Web - Low & High\\\",\\\"dpid\\\":\\\"uuid-5\\\",\\\"drn\\\":\\\"HIGH: C3 File Web\\\",\\\"drid\\\":\\\"uuid-6\\\",\\\"dact\\\":\\\"\\\",\\\"von\\\":\\\"REDACTED\\\",\\\"dprm\\\":\\\"Enable\\\",\\\"eop\\\":\\\"FileUploadedToCloud\\\",\\\"enmd\\\":\\\"Warn\\\",\\\"tdmn\\\":\\\"example.gov\\\",\\\"app\\\":\\\"chrome.exe\\\",\\\"ofph\\\":\\\"C:\\\\\\\\Users\\\\\\\\UserName\\\\\\\\OneDrive - Example\\\\\\\\Admin\\\\\\\\Visa\\\\\\\\document.pdf\\\",\\\"dn\\\":\\\"device-1\\\",\\\"mddid\\\":\\\"hash-1\\\",\\\"rmse\\\":\\\"False\\\",\\\"efs\\\":\\\"232103\\\",\\\"ecip\\\":\\\"192.0.2.1\\\",\\\"rtp\\\":108,\\\"wsrt\\\":\\\"2025-08-08T09:55:29\\\",\\\"mdt\\\":\\\"Audit\\\",\\\"rid\\\":\\\"uuid-7\\\",\\\"cid\\\":\\\"uuid-8\\\",\\\"ad\\\":\\\"\\\",\\\"lon\\\":\\\"DlpRuleMatch\\\",\\\"an\\\":\\\"DLP-HIGH: C3 File Web\\\",\\\"sev\\\":\\\"Medium\\\"}\",\"Name\":\"DLP-HIGH: C3 File Web\",\"PolicyId\":\"uuid-8\",\"Severity\":\"Medium\",\"Source\":\"Office 365 Security & Compliance\",\"Status\":\"Active\"}",
"event": {
"action": "AlertTriggered",
"category": [
"intrusion_detection"
],
"code": "40",
"kind": "alert",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2025-08-08T09:55:45Z",
"action": {
"id": 40,
"name": "AlertTriggered",
"outcome": "success",
"target": "user"
},
"email": {
"subject": "REDACTED"
},
"office365": {
"alert": {
"category": "DataLossPrevention",
"display_name": "DLP-HIGH: C3 File Web",
"id": "uuid-3",
"severity": "Medium",
"source": "Office 365 Security & Compliance",
"status": "Active"
},
"app": "chrome.exe",
"audit": {
"object_id": "uuid-3"
},
"dn": "device-1",
"dprm": "Enable",
"enmd": "Warn",
"eop": "FileUploadedToCloud",
"ofph": "C:\\Users\\UserName\\OneDrive - Example\\Admin\\Visa\\document.pdf",
"record_id": "uuid-1",
"record_type": 40,
"result_status": "Succeeded",
"tdmn": "example.gov",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"rule": {
"id": "uuid-8"
},
"service": {
"name": "SecurityComplianceCenter"
},
"user": {
"domain": "example.com",
"email": "user1@example.com",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2025-08-08T02:03:24\",\"Id\":\"uuid-9\",\"Operation\":\"AlertTriggered\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"uuid-10\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertId\":\"uuid-10\",\"AlertLinks\":[{\"AlertLinkHref\":\"\"}],\"AlertType\":\"Custom\",\"Category\":\"DataLossPrevention\",\"Comments\":\"New alert\",\"Data\":\"{\\\"f3u\\\":\\\"user2@example.com\\\",\\\"ts\\\":\\\"2025-08-08T01:59:00.0000000Z\\\",\\\"te\\\":\\\"2025-08-08T02:00:00.0000000Z\\\",\\\"op\\\":\\\"DlpRuleMatch\\\",\\\"wl\\\":\\\"Endpoint\\\",\\\"tid\\\":\\\"uuid-2\\\",\\\"tdc\\\":\\\"1\\\",\\\"reid\\\":\\\"uuid-11\\\",\\\"dpn\\\":\\\"Endpoint DLP Network Share - Low & High\\\",\\\"dpid\\\":\\\"uuid-12\\\",\\\"drn\\\":\\\"HIGH: C3 File Network Share\\\",\\\"drid\\\":\\\"uuid-13\\\",\\\"dact\\\":\\\"\\\",\\\"von\\\":\\\"REDACTED\\\",\\\"dprm\\\":\\\"Enable\\\",\\\"eop\\\":\\\"FileCopiedToNetworkShare\\\",\\\"enmd\\\":\\\"Warn\\\",\\\"app\\\":\\\"explorer.exe\\\",\\\"ofph\\\":\\\"C:\\\\\\\\Users\\\\\\\\UserName2\\\\\\\\OneDrive - Example\\\\\\\\FolderA\\\\\\\\REDACTED\\\",\\\"tfph\\\":\\\"\\\\\\\\\\\\\\\\fileserver\\\\\\\\InternalAudit\\\\\\\\FolderB\\\\\\\\REDACTED\\\",\\\"dn\\\":\\\"device-2\\\",\\\"mddid\\\":\\\"hash-2\\\",\\\"rmse\\\":\\\"False\\\",\\\"efs\\\":\\\"3362127\\\",\\\"ecip\\\":\\\"192.0.2.2\\\",\\\"rtp\\\":108,\\\"wsrt\\\":\\\"2025-08-08T02:02:45\\\",\\\"mdt\\\":\\\"Audit\\\",\\\"rid\\\":\\\"uuid-14\\\",\\\"cid\\\":\\\"uuid-15\\\",\\\"ad\\\":\\\"\\\",\\\"lon\\\":\\\"DlpRuleMatch\\\",\\\"an\\\":\\\"DLP-HIGH: C3 File Network Share\\\",\\\"sev\\\":\\\"Medium\\\"}\",\"Name\":\"DLP-HIGH: C3 File Network Share\",\"PolicyId\":\"uuid-15\",\"Severity\":\"Medium\",\"Source\":\"Office 365 Security & Compliance\",\"Status\":\"Active\"}",
"event": {
"action": "AlertTriggered",
"category": [
"intrusion_detection"
],
"code": "40",
"kind": "alert",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2025-08-08T02:03:24Z",
"action": {
"id": 40,
"name": "AlertTriggered",
"outcome": "success",
"target": "user"
},
"email": {
"subject": "REDACTED"
},
"office365": {
"alert": {
"category": "DataLossPrevention",
"display_name": "DLP-HIGH: C3 File Network Share",
"id": "uuid-10",
"severity": "Medium",
"source": "Office 365 Security & Compliance",
"status": "Active"
},
"app": "explorer.exe",
"audit": {
"object_id": "uuid-10"
},
"dn": "device-2",
"dprm": "Enable",
"enmd": "Warn",
"eop": "FileCopiedToNetworkShare",
"ofph": "C:\\Users\\UserName2\\OneDrive - Example\\FolderA\\REDACTED",
"record_id": "uuid-9",
"record_type": 40,
"result_status": "Succeeded",
"tfph": "\\\\fileserver\\InternalAudit\\FolderB\\REDACTED",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user2"
]
},
"rule": {
"id": "uuid-15"
},
"service": {
"name": "SecurityComplianceCenter"
},
"user": {
"domain": "example.com",
"email": "user2@example.com",
"name": "user2"
}
}
{
"message": "{\"AppAccessContext\":{\"ClientAppId\":\"f482d5ab-3acd-4c27-9721-30b09a03a648\",\"ClientAppName\":\"f482d5ab-3acd-4c27-9721-30b09a03a648\",\"CorrelationId\":\"75b4c463-190b-46e9-b38e-00b45b967900\"},\"CreationTime\":\"2025-03-08T19:21:47\",\"Id\":\"955b44a7-49a5-4b9a-af2e-f26f949a7063\",\"Operation\":\"FileMalwareDetected\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":6,\"UserKey\":\"user1\",\"UserType\":5,\"Version\":1,\"Workload\":\"SharePoint\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"user1\",\"ApplicationId\":\"f482d5ab-3acd-4c27-9721-30b09a03a648\",\"AuthenticationType\":\"OAuth\",\"BrowserName\":\"\",\"BrowserVersion\":\"\",\"CorrelationId\":\"1b9688a1-5010-b000-c8c4-efdddefc18\",\"EventSource\":\"SharePoint\",\"GeoLocation\":\"FRA\",\"IsManagedDevice\":false,\"ItemType\":\"File\",\"ListId\":\"b407ecfb-3392-415b-a860-836ff8f783a3\",\"ListItemUniqueId\":\"79ace9be-1ee0-4107-a1e8-7fdd80710545\",\"Platform\":\"Service\",\"Site\":\"ead0c6a8-2b8b-4af8-84d8-8787c7660219\",\"UserAgent\":\"MS Scanner ATP\",\"WebId\":\"76d24e2e-9ad6-46a1-8107-68d8853b872b\",\"DeviceDisplayName\":\"1.2.3.4\",\"EventSignature\":\"SOME_SIGNATURE\",\"HighPriorityMediaProcessing\":false,\"ListBaseType\":0,\"ListServerTemplate\":0,\"SourceFileExtension\":\"zip\",\"VirusInfo\":\"Trojan_Win32_MysticBlocker_Gen#\",\"VirusVendor\":\"Advanced Threat Protection\",\"SiteUrl\":\"https://example.com/\",\"SourceRelativeUrl\":\"files\",\"SourceFileName\":\"AdobePhotoshop20-cs_CZ_x64.zip\",\"ApplicationDisplayName\":\"f482d5ab-3acd-4c27-9721-30b09a03a648\",\"ObjectId\":\"https://example.com/files/AdobePhotoshop20-cs_CZ_x64.zip\"}",
"event": {
"action": "FileMalwareDetected",
"category": [
"file"
],
"code": "6",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2025-03-08T19:21:47Z",
"action": {
"id": 6,
"name": "FileMalwareDetected",
"outcome": "success",
"properties": [
{
"SiteUrl": "https://example.com/",
"SourceFileName": "AdobePhotoshop20-cs_CZ_x64.zip",
"SourceRelativeUrl": "files",
"UserAgent": "MS Scanner ATP"
}
],
"target": "user"
},
"file": {
"directory": "files",
"extension": "zip",
"name": "AdobePhotoshop20-cs_CZ_x64.zip"
},
"office365": {
"audit": {
"item_type": "File",
"object_id": "https://example.com/files/AdobePhotoshop20-cs_CZ_x64.zip",
"platform": "Service"
},
"context": {
"authentication_type": "OAuth",
"client": {
"id": "f482d5ab-3acd-4c27-9721-30b09a03a648",
"name": "f482d5ab-3acd-4c27-9721-30b09a03a648"
},
"correlation": {
"id": "75b4c463-190b-46e9-b38e-00b45b967900"
}
},
"device": {
"is_managed": false
},
"record_id": "955b44a7-49a5-4b9a-af2e-f26f949a7063",
"record_type": 6,
"user_type": {
"code": 5,
"name": "Application"
},
"virus_info": "Trojan_Win32_MysticBlocker_Gen#",
"virus_vendor": "Advanced Threat Protection"
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "SharePoint"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"url": {
"domain": "example.com",
"full": "https://example.com/files/AdobePhotoshop20-cs_CZ_x64.zip",
"original": "https://example.com/files/AdobePhotoshop20-cs_CZ_x64.zip",
"path": "/files/AdobePhotoshop20-cs_CZ_x64.zip",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"id": "user1",
"name": "user1"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Other",
"original": "MS Scanner ATP",
"os": {
"name": "Other"
}
}
}
{
"message": "{\"AppAccessContext\":{\"ClientAppName\":\"AntiVirusScanningHighVolumeWriteJob\",\"CorrelationId\":\"c697b5ce-a4ec-4cac-8c97-620a6f1467ea\"},\"CreationTime\":\"2025-07-25T09:29:37\",\"Id\":\"fa212399-9900-402b-9866-cedb12e31a96\",\"Operation\":\"FileMalwareDetected\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":6,\"UserKey\":\"S-1-2-3\",\"UserType\":4,\"Version\":1,\"Workload\":\"OneDrive\",\"ClientIP\":\"\",\"UserId\":\"user1\",\"CorrelationId\":\"c697b5ce-a4ec-4cac-8c97-620a6f1467ea\",\"EventSource\":\"SharePoint\",\"GeoLocation\":\"EUR\",\"ItemType\":\"File\",\"ListId\":\"159928cf-7b9f-4294-838e-f92dae5d6e90\",\"ListItemUniqueId\":\"761b15b1-9342-4f0f-938e-a4e019b49876\",\"Site\":\"3e355ece-4c7f-4204-8aca-f6044e642c2f\",\"UserAgent\":\"\",\"WebId\":\"9b3d42e0-4310-4970-a893-cc81ac577ea1\",\"EventSignature\":\"SOME_SIGNATURE\",\"HighPriorityMediaProcessing\":false,\"ListBaseType\":0,\"ListServerTemplate\":0,\"VirusInfo\":\"Win32/KeyLogger.RDI!MTB\",\"VirusVendor\":\"Default\",\"SourceRelativeUrl\":\"Documents/Desktop\",\"SourceFileName\":\"Test1.exe\",\"SourceFileExtension\":\"exe\",\"MD5Hash\":\"68b329da9893e34099c7d8ad5cb9c940\",\"SHA256Hash\":\"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b\",\"ApplicationDisplayName\":\"AntiVirusScanningHighVolumeWriteJob\",\"SiteUrl\":\"https://example.sharepoint.com/personal/hostname/\",\"ObjectId\":\"https://example.com/\"}",
"event": {
"action": "FileMalwareDetected",
"category": [
"file"
],
"code": "6",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2025-07-25T09:29:37Z",
"action": {
"id": 6,
"name": "FileMalwareDetected",
"outcome": "success",
"properties": [
{
"SiteUrl": "https://example.sharepoint.com/personal/hostname/",
"SourceFileName": "Test1.exe",
"SourceRelativeUrl": "Documents/Desktop",
"UserAgent": ""
}
],
"target": "user"
},
"file": {
"directory": "Documents/Desktop",
"extension": "exe",
"hash": {
"md5": "68b329da9893e34099c7d8ad5cb9c940",
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "Test1.exe"
},
"office365": {
"audit": {
"item_type": "File",
"object_id": "https://example.com/"
},
"context": {
"client": {
"name": "AntiVirusScanningHighVolumeWriteJob"
},
"correlation": {
"id": "c697b5ce-a4ec-4cac-8c97-620a6f1467ea"
}
},
"record_id": "fa212399-9900-402b-9866-cedb12e31a96",
"record_type": 6,
"user_type": {
"code": 4,
"name": "System"
},
"virus_info": "Win32/KeyLogger.RDI!MTB",
"virus_vendor": "Default"
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"hash": [
"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b",
"68b329da9893e34099c7d8ad5cb9c940"
],
"user": [
"user1"
]
},
"service": {
"name": "OneDrive"
},
"url": {
"domain": "example.com",
"full": "https://example.com/",
"original": "https://example.com/",
"path": "/",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"id": "S-1-2-3",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2020-09-29T07:32:51\",\"Id\":\"4e597c8c-e185-4ea5-3413-08d86449df74\",\"Operation\":\"FilePreviewed\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":6,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"OneDrive\",\"ClientIP\":\"1.2.3.4\",\"ObjectId\":\"https://example.com/\",\"UserId\":\"user1\",\"ApplicationId\":\"4345a7b9-9a63-4910-a426-35363201d503\",\"CorrelationId\":\"41af7e9f-30a8-9000-8f78-756aca9a7474\",\"DoNotDistributeEvent\":\"True\",\"EventSource\":\"SharePoint\",\"ItemType\":\"File\",\"ListId\":\"2db6ee74-6bd7-4d9b-a63f-26ae6eef9fb3\",\"ListItemUniqueId\":\"0e3f3538-8a03-4728-b431-225bc10687b6\",\"Site\":\"2d3c44c1-d225-499d-a47f-bda2751a00b9\",\"UserAgent\":\"OneDriveMpc-Transform_Thumbnail/1.0\",\"WebId\":\"c4b81f7e-4f91-4b3a-97a7-660709edef15\",\"HighPriorityMediaProcessing\":\"False\",\"SourceFileExtension\":\"xlsx\",\"SiteUrl\":\"https://company-my.sharepoint.com/personal/jane_doe_company_onmicrosoft_com/\",\"SourceFileName\":\"MyDocument.docx\",\"SourceRelativeUrl\":\"Documents\"}",
"event": {
"action": "FilePreviewed",
"category": [
"file"
],
"code": "6",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2020-09-29T07:32:51Z",
"action": {
"id": 6,
"name": "FilePreviewed",
"outcome": "success",
"properties": [
{
"SiteUrl": "https://company-my.sharepoint.com/personal/jane_doe_company_onmicrosoft_com/",
"SourceFileName": "MyDocument.docx",
"SourceRelativeUrl": "Documents",
"UserAgent": "OneDriveMpc-Transform_Thumbnail/1.0"
}
],
"target": "user"
},
"file": {
"directory": "Documents",
"extension": "xlsx",
"name": "MyDocument.docx"
},
"office365": {
"audit": {
"item_type": "File",
"object_id": "https://example.com/"
},
"record_id": "4e597c8c-e185-4ea5-3413-08d86449df74",
"record_type": 6,
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "OneDrive"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"url": {
"domain": "example.com",
"full": "https://example.com/",
"original": "https://example.com/",
"path": "/",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"id": "user1",
"name": "user1"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Other",
"original": "OneDriveMpc-Transform_Thumbnail/1.0",
"os": {
"name": "Other"
}
}
}
{
"message": "{\"AppAccessContext\":{\"AADSessionId\":\"xxxx-xxx-xxx-xxx\",\"ClientAppName\":\"WebExcel\",\"CorrelationId\":\"ANONYMIZED\"},\"CreationTime\":\"2024-02-22T16:06:53\",\"Id\":\"ANONYMIZED\",\"Operation\":\"FileModifiedExtended\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":6,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"SharePoint\",\"ClientIP\":\"0.0.0.0\",\"UserId\":\"user1\",\"AuthenticationType\":\"OAuth\",\"BrowserName\":\"\",\"BrowserVersion\":\"\",\"CorrelationId\":\"ANONYMIZED\",\"EventSource\":\"SharePoint\",\"IsManagedDevice\":false,\"ItemType\":\"File\",\"ListId\":\"ANONYMIZED\",\"ListItemUniqueId\":\"ANONYMIZED\",\"Platform\":\"OfficeCollaborationService\",\"Site\":\"xx-xxx-xx-xx\",\"UserAgent\":\"Useragentname\",\"WebId\":\"xxx-xx-xxx-xxx\",\"DeviceDisplayName\":\"0.0.0.0\",\"FileSizeBytes\":906087,\"HighPriorityMediaProcessing\":false,\"ListBaseType\":1,\"ListServerTemplate\":101,\"SourceFileExtension\":\"xlsx\",\"SiteUrl\":\"https://sharepoint.com/sites/filepath/\",\"SourceRelativeUrl\":\"Folder/Path\",\"SourceFileName\":\"FILENAME.xlsx\",\"ApplicationDisplayName\":\"WebExcel\",\"ObjectId\":\"https://example.com/\"}",
"event": {
"action": "FileModifiedExtended",
"category": [
"file"
],
"code": "6",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-02-22T16:06:53Z",
"action": {
"id": 6,
"name": "FileModifiedExtended",
"outcome": "success",
"properties": [
{
"SiteUrl": "https://sharepoint.com/sites/filepath/",
"SourceFileName": "FILENAME.xlsx",
"SourceRelativeUrl": "Folder/Path",
"UserAgent": "Useragentname"
}
],
"target": "user"
},
"file": {
"directory": "Folder/Path",
"extension": "xlsx",
"name": "FILENAME.xlsx",
"size": 906087
},
"office365": {
"audit": {
"item_type": "File",
"object_id": "https://example.com/",
"platform": "OfficeCollaborationService"
},
"context": {
"aad_session_id": "xxxx-xxx-xxx-xxx",
"authentication_type": "OAuth",
"client": {
"name": "WebExcel"
},
"correlation": {
"id": "ANONYMIZED"
}
},
"device": {
"is_managed": false
},
"record_id": "ANONYMIZED",
"record_type": 6,
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"0.0.0.0"
],
"user": [
"user1"
]
},
"service": {
"name": "SharePoint"
},
"source": {
"address": "0.0.0.0",
"ip": "0.0.0.0"
},
"url": {
"domain": "example.com",
"full": "https://example.com/",
"original": "https://example.com/",
"path": "/",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"id": "user1",
"name": "user1"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Other",
"original": "Useragentname",
"os": {
"name": "Other"
}
}
}
{
"message": "{\"AppAccessContext\":{\"AADSessionId\":\"0e042318-7c78-4acb-ae00-5ee74465bca3\",\"CorrelationId\":\"c299a0a0-14da-428a-b08d-481d562298cb\",\"UniqueTokenId\":\"0000000000000000000000\"},\"CreationTime\":\"2022-06-10T12:00:14\",\"Id\":\"7c13b5d5-aa8d-48d1-b3d1-5f4b657136ba\",\"Operation\":\"FileSyncDownloadedFull\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":6,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"SharePoint\",\"ClientIP\":\"1.2.3.4\",\"ObjectId\":\"https://example.com/\",\"UserId\":\"user1\",\"CorrelationId\":\"4b25e3d9-1e4f-4c62-a544-da747449f144\",\"EventSource\":\"SharePoint\",\"ItemType\":\"File\",\"ListId\":\"ca07dda5-0cdc-4399-94a6-303a7aa8ac00\",\"ListItemUniqueId\":\"ab5a159c-c8fd-409c-a48f-524c29df0341\",\"Site\":\"1a53ae0f-8405-42ec-8c43-724101fd34a2\",\"UserAgent\":\"Microsoft SkyDriveSync 22.099.0508.0001 ship; Windows NT 10.0 (19043)\",\"WebId\":\"ba71b4fe-22e8-41cf-9eaf-48b1787bad16\",\"MachineDomainInfo\":\"f059d209-e819-402b-a391-4941ff3860c6\",\"MachineId\":\"884ecccb-1e44-4dd4-a2b5-b60517893ce0\",\"FileSyncBytesCommitted\":\"1344200\",\"HighPriorityMediaProcessing\":false,\"SourceFileExtension\":\"png\",\"SiteUrl\":\"https://company.sharepoint.com/sites/shared\",\"SourceFileName\":\"logo.png\",\"SourceRelativeUrl\":\"public/assets/website\"}",
"event": {
"action": "FileSyncDownloadedFull",
"category": [
"file"
],
"code": "6",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2022-06-10T12:00:14Z",
"action": {
"id": 6,
"name": "FileSyncDownloadedFull",
"outcome": "success",
"properties": [
{
"SiteUrl": "https://company.sharepoint.com/sites/shared",
"SourceFileName": "logo.png",
"SourceRelativeUrl": "public/assets/website",
"UserAgent": "Microsoft SkyDriveSync 22.099.0508.0001 ship; Windows NT 10.0 (19043)"
}
],
"target": "user"
},
"azuread": {
"properties": {
"uniqueTokenIdentifier": "0000000000000000000000"
}
},
"file": {
"directory": "public/assets/website",
"extension": "png",
"name": "logo.png"
},
"office365": {
"audit": {
"item_type": "File",
"object_id": "https://example.com/"
},
"context": {
"aad_session_id": "0e042318-7c78-4acb-ae00-5ee74465bca3",
"correlation": {
"id": "c299a0a0-14da-428a-b08d-481d562298cb"
}
},
"record_id": "7c13b5d5-aa8d-48d1-b3d1-5f4b657136ba",
"record_type": 6,
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "SharePoint"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"url": {
"domain": "example.com",
"full": "https://example.com/",
"original": "https://example.com/",
"path": "/",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"id": "user1",
"name": "user1"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Microsoft SkyDriveSync",
"original": "Microsoft SkyDriveSync 22.099.0508.0001 ship; Windows NT 10.0 (19043)",
"os": {
"name": "Windows",
"version": "10"
},
"version": "22.099.0508"
}
}
{
"message": "{\"Id\":\"40094389-7baf-a3ba-5acc-2773c002cfbe\",\"RecordType\":22,\"CreationTime\":\"2022-09-07T12:22:07\",\"Operation\":\"FileVisited\",\"OrganizationId\":\"ANONYMIZED\",\"UserType\":0,\"UserKey\":\"user1\",\"Workload\":\"Yammer\",\"ResultStatus\":\"TRUE\",\"ObjectId\":\"Pix_C'est la rentre!.png\",\"ClientIP\":\"192.0.2.1\",\"UserId\":\"user1\",\"ActorYammerUserId\":1315924230144,\"ActorUserId\":\"user1\",\"YammerNetworkId\":6358000,\"Version\":1,\"FileId\":1439262310400,\"FileName\":\"Pix_C'est la rentre!.png\",\"VersionId\":1460243079168}",
"event": {
"action": "FileVisited",
"category": [
"file"
],
"code": "22",
"outcome": "success"
},
"@timestamp": "2022-09-07T12:22:07Z",
"action": {
"id": 22,
"name": "FileVisited",
"outcome": "success",
"target": "user"
},
"file": {
"name": "Pix_C'est la rentre!.png"
},
"office365": {
"audit": {
"object_id": "Pix_C'est la rentre!.png"
},
"record_id": "40094389-7baf-a3ba-5acc-2773c002cfbe",
"record_type": 22,
"result_status": "TRUE",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"service": {
"name": "Yammer"
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2023-12-13T10:08:21\",\"Id\":\"ANONYMIZED\",\"Operation\":\"EditForm\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":66,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"ANONYMIZED\",\"UserType\":0,\"Version\":1,\"Workload\":\"MicrosoftForms\",\"ClientIP\":\"0.0.0.0\",\"ObjectId\":\"xxxxxxx\",\"UserId\":\"ANONYMIZED\",\"ActivityParameters\":\"{\\\"EditOperation\\\":\\\"QuestionUpdated\\\"}\",\"FormId\":\"xxxxxxx\",\"FormName\":\"FormNameValue\\n\\n\",\"FormType\":1,\"FormsUserType\":1,\"SourceApp\":\"ms-formweb\"}",
"event": {
"action": "EditForm",
"code": "66",
"outcome": "success"
},
"@timestamp": "2023-12-13T10:08:21Z",
"action": {
"id": 66,
"name": "EditForm",
"outcome": "success",
"target": "user"
},
"office365": {
"audit": {
"object_id": "xxxxxxx"
},
"form_name": "FormNameValue\n\n",
"record_id": "ANONYMIZED",
"record_type": 66,
"result_status": "Succeeded",
"source": {
"application": "ms-formweb"
},
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"0.0.0.0"
],
"user": [
"ANONYMIZED"
]
},
"service": {
"name": "MicrosoftForms"
},
"source": {
"address": "0.0.0.0",
"ip": "0.0.0.0"
},
"user": {
"id": "ANONYMIZED",
"name": "ANONYMIZED"
}
}
{
"message": "{\"CreationTime\":\"2023-05-24T15:10:53\",\"Id\":\"9cf2a1f7-90bc-494b-2784-08db5c691133\",\"Operation\":\"New-InboxRule\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":1,\"ResultStatus\":\"True\",\"UserKey\":\"user1\",\"UserType\":2,\"Version\":1,\"Workload\":\"Exchange\",\"ClientIP\":\"1.2.3.4:63070\",\"ObjectId\":\"EURPR07A010.PROD.OUTLOOK.COM/Microsoft Exchange Hosted Organizations/example.onmicrosoft.com/bc1b1df3-f861-4aec-bf7c-40ce5b5566c1\\\\RULE_NAME\",\"UserId\":\"user1\",\"AppId\":\"00000002-0000-0ff1-ce00-000000000000\",\"ClientAppId\":\"\",\"ExternalAccess\":false,\"OrganizationName\":\"example.onmicrosoft.com\",\"OriginatingServer\":\"AM0PR07MB5763 (15.20.6411.029)\",\"Parameters\":[{\"Name\":\"ForwardTo\",\"Value\":\"bob@example.org\"},{\"Name\":\"Force\",\"Value\":\"False\"},{\"Name\":\"AlwaysDeleteOutlookRulesBlob\",\"Value\":\"False\"},{\"Name\":\"RedirectTo\",\"Value\":\"joe@example.org\"},{\"Name\":\"From\",\"Value\":\"alice@example.org\"},{\"Name\":\"Name\",\"Value\":\"RULE_NAME\"},{\"Name\":\"DeleteMessage\",\"Value\":\"True\"},{\"Name\":\"FromAddressContainsWords\",\"Value\":\"@example.org\"},{\"Name\":\"MarkAsRead\",\"Value\":\"True\"},{\"Name\":\"StopProcessingRules\",\"Value\":\"True\"},{\"Name\":\"SubjectOrBodyContainsWords\",\"Value\":\"keyword\"},{\"Name\":\"MoveToFolder\",\"Value\":\"Historique des conversations\"}],\"SessionId\":\"984c0958-0631-4b90-b116-15094fc36847\"}",
"event": {
"action": "New-InboxRule",
"code": "1",
"outcome": "success"
},
"@timestamp": "2023-05-24T15:10:53Z",
"action": {
"id": 1,
"name": "New-InboxRule",
"outcome": "success",
"target": "user"
},
"office365": {
"audit": {
"object_id": "EURPR07A010.PROD.OUTLOOK.COM/Microsoft Exchange Hosted Organizations/example.onmicrosoft.com/bc1b1df3-f861-4aec-bf7c-40ce5b5566c1\\RULE_NAME"
},
"context": {
"aad_session_id": "984c0958-0631-4b90-b116-15094fc36847",
"client": {
"id": "00000002-0000-0ff1-ce00-000000000000"
}
},
"exchange_admin": {
"parameters": [
"AlwaysDeleteOutlookRulesBlob:False",
"DeleteMessage:True",
"Force:False",
"ForwardTo:bob@example.org",
"From:alice@example.org",
"FromAddressContainsWords:@example.org",
"MarkAsRead:True",
"MoveToFolder:Historique des conversations",
"Name:RULE_NAME",
"RedirectTo:joe@example.org",
"StopProcessingRules:True",
"SubjectOrBodyContainsWords:keyword"
]
},
"record_id": "9cf2a1f7-90bc-494b-2784-08db5c691133",
"record_type": 1,
"result_status": "True",
"user_type": {
"code": 2,
"name": "Admin"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 63070
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\":{\"AADSessionId\":\"fbe7d318-3d7f-4645-9e03-caa46e2a8f01\",\"CorrelationId\":\"5f24aa82-f874-44d1-b6df-857cd9e1decf\",\"UniqueTokenId\":\"2222222222222222222222\"},\"CreationTime\":\"2023-08-22T12:37:20\",\"Id\":\"037fd006-a72b-49ae-4bb0-08dba30c8729\",\"Operation\":\"ManagedSyncClientAllowed\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":4,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"SharePoint\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"user1\",\"AuthenticationType\":\"FormsCookieAuth\",\"BrowserName\":\"Edge\",\"BrowserVersion\":\"114.0.1823.79\",\"CorrelationId\":\"ec84154f-db9d-47cd-b1be-56d75cb8840e\",\"EventSource\":\"SharePoint\",\"IsManagedDevice\":false,\"ItemType\":\"DocumentLibrary\",\"Platform\":\"WinDesktop\",\"Site\":\"1435321e-2bbb-417d-b21c-533e3ec15f5f\",\"UserAgent\":\"Microsoft SkyDriveSync 23.101.0514.0004 ship; Windows NT 10.0 (19045)\",\"WebId\":\"50ad5578-0fa1-4285-9cde-1e4f067fb892\",\"DeviceDisplayName\":\"3deb:3c5e:59d0:53ad:1115:d3d7:58da:47d6\",\"MachineDomainInfo\":\"8208550a-4001-439d-a9f6-e95d76767507\",\"MachineId\":\"77f6d9ce-da8f-46bf-a651-4bec3c189770\"}",
"event": {
"action": "ManagedSyncClientAllowed",
"category": [
"file"
],
"code": "4",
"outcome": "success",
"type": [
"access"
]
},
"@timestamp": "2023-08-22T12:37:20Z",
"action": {
"id": 4,
"name": "ManagedSyncClientAllowed",
"outcome": "success",
"target": "user"
},
"azuread": {
"properties": {
"uniqueTokenIdentifier": "2222222222222222222222"
}
},
"office365": {
"audit": {
"event_source": "SharePoint",
"item_type": "DocumentLibrary",
"platform": "WinDesktop",
"site": "1435321e-2bbb-417d-b21c-533e3ec15f5f"
},
"context": {
"aad_session_id": "fbe7d318-3d7f-4645-9e03-caa46e2a8f01",
"authentication_type": "FormsCookieAuth",
"correlation": {
"id": "5f24aa82-f874-44d1-b6df-857cd9e1decf"
}
},
"device": {
"is_managed": false
},
"record_id": "037fd006-a72b-49ae-4bb0-08dba30c8729",
"record_type": 4,
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "SharePoint"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "user1",
"name": "user1"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Microsoft SkyDriveSync",
"original": "Microsoft SkyDriveSync 23.101.0514.0004 ship; Windows NT 10.0 (19045)",
"os": {
"name": "Windows",
"version": "10"
},
"version": "23.101.0514"
}
}
{
"message": "{\"CreationTime\":\"2024-02-22T09:56:48\",\"Id\":\"0e042318-7c78-4acb-ae00-5ee74465bca3\",\"Operation\":\"AlertUpdated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"c299a0a0-14da-428a-b08d-481d562298cb\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertId\":\"c299a0a0-14da-428a-b08d-481d562298cb\",\"AlertLinks\":[{\"AlertLinkHref\":\"\"}],\"AlertType\":\"Custom\",\"Category\":\"ThreatManagement\",\"Comments\":\"New alert\",\"Data\":\"{\\\"ts\\\":\\\"2024-02-22 09:46:54Z\\\",\\\"te\\\":\\\"2024-02-22 09:46:54Z\\\",\\\"an\\\":\\\"Mass download by a single user\\\",\\\"ad\\\":\\\"Activity policy 'Mass download by a single user' was triggered by 'Anakin SKYWALKER'\\\",\\\"f3u\\\":\\\"john.doe@example.com\\\",\\\"alk\\\":\\\"https://example.com/#/alerts/79d71811t27fe160149dcd56\\\",\\\"plk\\\":\\\"https://gondor.portal.cloudappsecurity.com/#/policy/?id=eq(5f391720dd4e64e3db757c35,)\\\",\\\"mat\\\":\\\"MCAS_ALERT_CABINET_EVENT_MATCH_AUDIT\\\"}\",\"Name\":\"Mass download by a single user\",\"PolicyId\":\"8697dfdc-965d-67f7-bb37-b2551b296c04\",\"Severity\":\"High\",\"Source\":\"Cloud App Security\",\"Status\":\"Active\"}",
"event": {
"action": "AlertUpdated",
"category": [
"intrusion_detection"
],
"code": "40",
"end": "2024-02-22T09:46:54Z",
"kind": "alert",
"outcome": "success",
"reason": "Activity policy 'Mass download by a single user' was triggered by 'Anakin SKYWALKER'",
"start": "2024-02-22T09:46:54Z",
"type": [
"info"
],
"url": "https://example.com/#/alerts/79d71811t27fe160149dcd56"
},
"@timestamp": "2024-02-22T09:56:48Z",
"action": {
"id": 40,
"name": "AlertUpdated",
"outcome": "success",
"target": "user"
},
"office365": {
"alert": {
"category": "ThreatManagement",
"display_name": "Mass download by a single user",
"id": "c299a0a0-14da-428a-b08d-481d562298cb",
"severity": "High",
"source": "Cloud App Security",
"status": "Active"
},
"audit": {
"object_id": "c299a0a0-14da-428a-b08d-481d562298cb"
},
"record_id": "0e042318-7c78-4acb-ae00-5ee74465bca3",
"record_type": 40,
"result_status": "Succeeded",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"john.doe"
]
},
"rule": {
"category": "MCAS_ALERT_CABINET_EVENT_MATCH_AUDIT",
"id": "8697dfdc-965d-67f7-bb37-b2551b296c04",
"reference": "https://gondor.portal.cloudappsecurity.com/#/policy/?id=eq(5f391720dd4e64e3db757c35,)"
},
"service": {
"name": "SecurityComplianceCenter"
},
"source": {
"user": {
"email": "john.doe@example.com"
}
},
"user": {
"domain": "example.com",
"email": "john.doe@example.com",
"name": "john.doe"
}
}
{
"message": "{\"Applications\":[{\"Name\":\"Microsoft SharePoint Online\"}],\"AlertCategory\":\"ANOMALY_DETECTION\",\"AlertDisplayName\":\"Impossible travel activity\",\"AlertDescription\":\"The user JOHN DOE (john.doe@example.org) was involved in an impossible travel\\n incident. The user connected from two countries within 10 minutes, from these IP addresses: Belgium\\n (3deb:3c5e:59d0:53ad:1115:d3d7:58da:47d6) and France (1.2.3.4). If any of these IP addresses are used by the\\n organization for VPN connections and do not necessarily represent a physical location, we recommend categorizing them as\\n VPN in the IP Address range page in Microsoft Defender for Cloud Apps portal to avoid false alerts.\",\"AlertSeverity\":\"Medium\",\"AssignedTo\":null,\"LastUpdatedTime\":\"2023-04-19T12:24:16\",\"ActivityStartTime\":\"2023-04-19T12:07:08\",\"ItemCount\":0,\"AlertUri\":\"https://example.portal.cloudappsecurity.com/#/alerts/111111111111111111111111\",\"ClientIPs\":[\"3deb:3c5e:59d0:53ad:1115:d3d7:58da:47d6\",\"1.2.3.4\"],\"ObjectId\":\"643fdd70e8ff3e15bba6dfd8\",\"UserId\":\"user1\",\"Id\":\"ANONYMIZED\",\"RecordType\":98,\"CreationTime\":\"2023-04-19T12:24:16\",\"Operation\":\"MCAS_ALERT_ANUBIS_DETECTION_VELOCITY\",\"OrganizationId\":\"ANONYMIZED\",\"UserType\":0,\"UserKey\":\"user1\",\"Workload\":\"MCAS\",\"ResultStatus\":\"New\",\"Version\":1}",
"event": {
"action": "MCAS_ALERT_ANUBIS_DETECTION_VELOCITY",
"category": [
"intrusion_detection"
],
"code": "98",
"kind": "alert",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2023-04-19T12:24:16Z",
"action": {
"id": 98,
"name": "MCAS_ALERT_ANUBIS_DETECTION_VELOCITY",
"outcome": "success",
"target": "user"
},
"office365": {
"alert": {
"category": "ANOMALY_DETECTION",
"client_ips": [
"1.2.3.4",
"3deb:3c5e:59d0:53ad:1115:d3d7:58da:47d6"
],
"description": "The user JOHN DOE (john.doe@example.org) was involved in an impossible travel\n incident. The user connected from two countries within 10 minutes, from these IP addresses: Belgium\n (3deb:3c5e:59d0:53ad:1115:d3d7:58da:47d6) and France (1.2.3.4). If any of these IP addresses are used by the\n organization for VPN connections and do not necessarily represent a physical location, we recommend categorizing them as\n VPN in the IP Address range page in Microsoft Defender for Cloud Apps portal to avoid false alerts.",
"display_name": "Impossible travel activity",
"severity": "Medium"
},
"audit": {
"object_id": "643fdd70e8ff3e15bba6dfd8"
},
"record_id": "ANONYMIZED",
"record_type": 98,
"result_status": "New",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"service": {
"name": "MCAS"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2022-07-07T22:38:49\",\"Id\":\"266f5962-ffad-4fce-a101-3197581af3d4\",\"Operation\":\"AtpDetection\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":47,\"UserKey\":\"user1\",\"UserType\":4,\"Version\":1,\"Workload\":\"ThreatIntelligence\",\"UserId\":\"user1\",\"DetectionDate\":\"2022-07-07T22:38:11\",\"DetectionMethod\":\"AntiMalware\",\"EventDeepLink\":\"https://example.com/\",\"FileData\":{\"DocumentId\":\"03254108-f682-417d-f3e6-08da605bf091\",\"FileName\":\"malware\",\"FilePath\":\"https://example.com/\",\"FileSize\":\"12345\",\"FileVerdict\":1,\"MalwareFamily\":\"iPhoneOS/Vortex.C\",\"SHA256\":\"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b\"},\"LastModifiedBy\":\"user1\",\"LastModifiedDate\":\"2022-01-01T13:00:53\",\"SourceWorkload\":1}",
"event": {
"action": "AtpDetection",
"code": "47",
"outcome": "success",
"url": "https://example.com/"
},
"@timestamp": "2022-07-07T22:38:49Z",
"action": {
"id": 47,
"name": "AtpDetection",
"outcome": "success",
"target": "user"
},
"file": {
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "malware"
},
"office365": {
"defender": {
"detection": {
"method": "AntiMalware"
},
"malware_family": "iPhoneOS/Vortex.C"
},
"record_id": "266f5962-ffad-4fce-a101-3197581af3d4",
"record_type": 47,
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"hash": [
"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
],
"user": [
"user1"
]
},
"service": {
"name": "ThreatIntelligence"
},
"url": {
"domain": "example.com",
"full": "https://example.com/",
"original": "https://example.com/",
"path": "/",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2022-07-08T09:10:19\",\"Id\":\"50906475-74dd-4447-ae4d-595d225d0055\",\"Operation\":\"TIMailData\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":28,\"UserKey\":\"user1\",\"UserType\":4,\"Version\":1,\"Workload\":\"ThreatIntelligence\",\"ObjectId\":\"4ca2df96-4488-4f3b-a265-b4edaa3c4d8f\",\"UserId\":\"user1\",\"AdditionalActionsAndResults\":[\"OriginalDelivery: [N/A]\"],\"AttachmentData\":[{\"FileName\":\"malicious.pdf.exe\",\"FileType\":\"exe;zip\",\"FileVerdict\":1,\"MalwareFamily\":\"Trojan_Gen_FileWithSpoofedExtension_A\",\"SHA256\":\"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b\"}],\"AuthDetails\":[{\"Name\":\"SPF\",\"Value\":\"Pass\"},{\"Name\":\"DKIM\",\"Value\":\"Fail\"},{\"Name\":\"DMARC\",\"Value\":\"Best guess pass\"},{\"Name\":\"Comp Auth\",\"Value\":\"pass\"}],\"DeliveryAction\":\"Blocked\",\"DetectionMethod\":\"File detonation\",\"DetectionType\":\"Inline\",\"Directionality\":\"Inbound\",\"EventDeepLink\":\"https://example.com/\",\"InternetMessageId\":\"<11111111-1111-1111-1111-111111111111@example.com>\",\"LatestDeliveryLocation\":\"Quarantine\",\"MessageTime\":\"2022-07-08T09:07:47\",\"NetworkMessageId\":\"7250ff78-fd13-45a2-bb5d-23a5d59c2699\",\"OriginalDeliveryLocation\":\"Quarantine\",\"P1Sender\":\"prvs=0000000000=human@sender.com\",\"P2Sender\":\"ANONYMIZED\",\"Policy\":\"SafeAttachements\",\"PolicyAction\":\"Quarantine\",\"Recipients\":[\"human@example.com\"],\"SenderIp\":\"1.2.3.4\",\"Subject\":\"ANONYMIZED\",\"SystemOverrides\":[{\"Details\":\"Antimalware policy block by file type\",\"FinalOverride\":\"No\",\"Result\":\"Block\",\"Source\":\"Tenant\"}],\"ThreatsAndDetectionTech\":[\"Malware: [File detonation]\",\"Spam: [General filter]\"],\"Verdict\":\"Malware\"}",
"event": {
"action": "Blocked",
"code": "28",
"outcome": "success",
"url": "https://example.com/"
},
"@timestamp": "2022-07-08T09:10:19Z",
"action": {
"id": 28,
"name": "Blocked",
"outcome": "success",
"target": "user"
},
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"mime_type": "exe;zip",
"name": "malicious.pdf.exe"
}
}
],
"delivery_timestamp": "2022-07-08T09:07:47Z",
"from": {
"address": [
"ANONYMIZED"
]
},
"local_id": "7250ff78-fd13-45a2-bb5d-23a5d59c2699",
"message_id": "11111111-1111-1111-1111-111111111111@example.com",
"reply_to": {
"address": [
"prvs=0000000000=human@sender.com"
]
},
"subject": "ANONYMIZED",
"to": {
"address": [
"human@example.com"
]
}
},
"office365": {
"audit": {
"object_id": "4ca2df96-4488-4f3b-a265-b4edaa3c4d8f"
},
"defender": {
"additional_actions": [
"OriginalDelivery: [N/A]"
],
"auth_details": [
{
"Name": "SPF",
"Value": "Pass"
},
{
"Name": "DKIM",
"Value": "Fail"
},
{
"Name": "DMARC",
"Value": "Best guess pass"
},
{
"Name": "Comp Auth",
"Value": "pass"
}
],
"detection": {
"method": "File detonation",
"technology": [
"Malware: [File detonation]",
"Spam: [General filter]"
],
"type": "Inline"
},
"email": {
"attachments": [
{
"name": "Trojan_Gen_FileWithSpoofedExtension_A",
"verdict": {
"code": "1",
"name": "bad"
}
}
],
"delivery": {
"action": "Blocked",
"latest_location": "Quarantine",
"original_location": "Quarantine"
},
"verdict": {
"reason": "Malware"
}
},
"system_overrides": [
{
"Details": "Antimalware policy block by file type",
"FinalOverride": "No",
"Result": "Block",
"Source": "Tenant"
}
]
},
"record_id": "50906475-74dd-4447-ae4d-595d225d0055",
"record_type": 28,
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "ThreatIntelligence"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2022-07-07T10:10:52\",\"Id\":\"47bf7844-15bf-4cf2-91a3-15b32ceb89b5\",\"Operation\":\"TIUrlClickData\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":41,\"UserKey\":\"user1\",\"UserType\":4,\"Version\":1,\"Workload\":\"ThreatIntelligence\",\"UserId\":\"user1\",\"AppName\":\"Mail\",\"AppVersion\":\"0.0.0000\",\"EventDeepLink\":\"https://example.com/\",\"SourceId\":\"8a8634d0-d803-4bc9-b221-2863bff6a001\",\"TimeOfClick\":\"2022-07-07T09:33:33\",\"Url\":\"https://example.com/\",\"UserIp\":\"1.2.3.4\"}",
"event": {
"action": "TIUrlClickData",
"code": "41",
"outcome": "success",
"url": "https://example.com/"
},
"@timestamp": "2022-07-07T10:10:52Z",
"action": {
"id": 41,
"name": "TIUrlClickData",
"outcome": "success",
"target": "user"
},
"office365": {
"record_id": "47bf7844-15bf-4cf2-91a3-15b32ceb89b5",
"record_type": 41,
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"service": {
"name": "ThreatIntelligence"
},
"url": {
"domain": "example.com",
"full": "https://example.com/",
"original": "https://example.com/",
"path": "/",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\":{},\"CreationTime\":\"2024-10-28T10:34:13\",\"Id\":\"ANONYMIZED\",\"Operation\":\"UpdateInboxRules\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":2,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"ANONYMIZED\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"user1\",\"ClientIPAddress\":\"1.2.3.4\",\"ClientInfoString\":\"Client=xxxx-xxx-xxx-xxxx\",\"ClientProcessName\":\"PROCESS.EXE\",\"ClientRequestId\":\"{xxxx-xxx-xxx-xxxx}\",\"ClientVersion\":\"16.0.17328.20550\",\"ExternalAccess\":false,\"InternalLogonType\":0,\"LogonType\":2,\"LogonUserSid\":\"S-1-2-3\",\"MailboxGuid\":\"ANONYMIZED\",\"MailboxOwnerMasterAccountSid\":\"S-1-2-3\",\"MailboxOwnerSid\":\"S-1-2-3\",\"MailboxOwnerUPN\":\"owner@mail.fr\",\"OperationProperties\":[{\"Name\":\"RuleOperation\",\"Value\":\"ModifyMailboxRule\"},{\"Name\":\"RuleId\",\"Value\":\"-123\"},{\"Name\":\"RuleState\",\"Value\":\"Enabled\"},{\"Name\":\"RuleCondition\",\"Value\":\"{(Exists(ItemClass))}\"},{\"Name\":\"RuleName\"},{\"Name\":\"RuleProvider\",\"Value\":\"RuleOrganizer\"},{\"Name\":\"RuleActions\",\"Value\":\"[{\\\"ActionType\\\":\\\"Forward\\\",\\\"Recipients\\\":[\\\"john.doe@mail.fr\\\",\\\"user@email.fr\\\",\\\"asmithee@mailbox.fr\\\",\\\"user.name@mail.fr\\\"],\\\"ForwardFlags\\\":\\\"None\\\"}]\"}],\"OrganizationName\":\"organization.com\",\"OriginatingServer\":\"Origin Server\\r\\n\",\"SessionId\":\"ANONYMIZED\",\"Item\":{\"Id\":\"ID12345\",\"ImmutableId\":\"ErrorDuringIdConversion\",\"ParentFolder\":{\"Id\":\"ID12345\",\"Name\":\"Bo\\u00eete de r\\u00e9ception\",\"Path\":\"\\\\Bo\\u00eete de r\\u00e9ception\"}}}",
"event": {
"action": "UpdateInboxRules",
"category": [
"email",
"file"
],
"code": "2",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-10-28T10:34:13Z",
"action": {
"id": 2,
"name": "UpdateInboxRules",
"outcome": "success",
"target": "user"
},
"office365": {
"context": {
"aad_session_id": "ANONYMIZED"
},
"exchange": {
"mailbox_guid": "ANONYMIZED",
"mailbox_owner": {
"sid": "S-1-2-3",
"upn": "owner@mail.fr"
}
},
"operation": {
"properties": {
"RuleActions": [
{
"ActionType": "Forward",
"ForwardFlags": "None",
"Recipients": [
"john.doe@mail.fr",
"user@email.fr",
"asmithee@mailbox.fr",
"user.name@mail.fr"
]
}
],
"RuleCondition": "{(Exists(ItemClass))}",
"RuleId": -123,
"RuleOperation": "ModifyMailboxRule",
"RuleProvider": "RuleOrganizer",
"RuleState": "Enabled"
}
},
"record_id": "ANONYMIZED",
"record_type": 2,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "S-1-2-3",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\":{},\"CreationTime\":\"2024-10-23T12:26:18\",\"Id\":\"ANONYMIZED\",\"Operation\":\"UpdateInboxRules\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":2,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"123456\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"user1\",\"ClientIPAddress\":\"1.2.3.4\",\"ClientInfoString\":\"Client=xxxx-xxx-xxx-xxxx\",\"ClientProcessName\":\"PROCESS.EXE\",\"ClientRequestId\":\"{xxxx-xxx-xxx-xxxx}\",\"ClientVersion\":\"16.0.16731.20456\",\"ExternalAccess\":false,\"InternalLogonType\":0,\"LogonType\":0,\"LogonUserSid\":\"S-1-2-3\",\"MailboxGuid\":\"ANONYMIZED\",\"MailboxOwnerSid\":\"S-1-2-3\",\"MailboxOwnerUPN\":\"user1\",\"OperationProperties\":[{\"Name\":\"RuleOperation\",\"Value\":\"ModifyMailboxRule\"},{\"Name\":\"RuleId\",\"Value\":\"4561233110666051585\"},{\"Name\":\"RuleState\",\"Value\":\"Enabled\"},{\"Name\":\"RuleCondition\",\"Value\":\"{(&(([RssServerLockStartTime=1, =r, =noreply-wham@mail.fr, DisplayType=0], ((SenderSearchKey Equal SMTP:NOREPLY-WHAM@MAIL.FR)))(SubString IgnoreCase(SubjectProperty)=WHAM)))}\"},{\"Name\":\"RuleName\"},{\"Name\":\"RuleProvider\",\"Value\":\"RuleOrganizer\"},{\"Name\":\"RuleActions\",\"Value\":\"[{\\\"ActionType\\\":\\\"Forward\\\",\\\"Recipients\\\":[\\\"user.name@mail.fr\\\"],\\\"ForwardFlags\\\":\\\"None\\\"}]\"}],\"OrganizationName\":\"organization.name.com\",\"OriginatingServer\":\"Origin Server\\r\\n\",\"SessionId\":\"ANONYMIZED\",\"Item\":{\"Id\":\"ANONYMIZED\",\"ImmutableId\":\"ErrorDuringIdConversion\",\"ParentFolder\":{\"Id\":\"ANONYMIZED\",\"Name\":\"Bo\\u00eete de r\\u00e9ception\",\"Path\":\"\\\\Bo\\u00eete de r\\u00e9ception\"}}}",
"event": {
"action": "UpdateInboxRules",
"category": [
"email",
"file"
],
"code": "2",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-10-23T12:26:18Z",
"action": {
"id": 2,
"name": "UpdateInboxRules",
"outcome": "success",
"target": "user"
},
"office365": {
"context": {
"aad_session_id": "ANONYMIZED"
},
"exchange": {
"mailbox_guid": "ANONYMIZED",
"mailbox_owner": {
"sid": "S-1-2-3",
"upn": "user1"
}
},
"operation": {
"properties": {
"RuleActions": [
{
"ActionType": "Forward",
"ForwardFlags": "None",
"Recipients": [
"user.name@mail.fr"
]
}
],
"RuleCondition": "{(&(([RssServerLockStartTime=1, =r, =noreply-wham@mail.fr, DisplayType=0], ((SenderSearchKey Equal SMTP:NOREPLY-WHAM@MAIL.FR)))(SubString IgnoreCase(SubjectProperty)=WHAM)))}",
"RuleId": 4561233110666051585,
"RuleOperation": "ModifyMailboxRule",
"RuleProvider": "RuleOrganizer",
"RuleState": "Enabled"
}
},
"record_id": "ANONYMIZED",
"record_type": 2,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "S-1-2-3",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\":{\"APIId\":\"\"},\"CreationTime\":\"2025-02-13T09:53:51\",\"Id\":\"2b69a1a1-5e4e-4d1d-9feb-543d61b025e7\",\"Operation\":\"UpdateInboxRules\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":2,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"1111111111111111\",\"UserType\":0,\"Version\":1,\"Workload\":\"Exchange\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"user1\",\"ClientIPAddress\":\"1.2.3.4\",\"ClientInfoString\":\"Client=MSExchangeRPC\",\"ClientProcessName\":\"OUTLOOK.EXE\",\"ClientRequestId\":\"{5ED2E898-FAAF-4A39-B9C3-407176A7087A}\",\"ClientVersion\":\"16.0.5467.1000\",\"ExternalAccess\":false,\"InternalLogonType\":0,\"LogonType\":0,\"LogonUserSid\":\"user1\",\"MailboxGuid\":\"e24b161f-f171-4db0-9572-4945279041c2\",\"MailboxOwnerSid\":\"user1\",\"MailboxOwnerUPN\":\"user1\",\"OperationProperties\":[{\"Name\":\"RuleOperation\",\"Value\":\"ModifyMailboxRule\"},{\"Name\":\"RuleId\",\"Value\":\"-5555555555555555555\"},{\"Name\":\"RuleState\",\"Value\":\"Enabled, ExitAfterExecution\"},{\"Name\":\"RuleCondition\",\"Value\":\"{(&((&((MessageToMe Equal True)(!((SubString Default(DisplayTo)=;)))))([RssServerLockStartTime=1, =/o=EXAMPLE/ou=Administrative (AAAAAAAAAAAAAAA)/cn=Recipients/cn=11111111111111111111111111111111111111111111, =Example, DisplayType=0], ((SenderSearchKey Equal EX:/O=EXAMPLE/OU=ADMINISTRATIVE (AAAAAAAAAAAAAAAAAAAA)/CN=RECIPIENTS/CN=BBBBBBBBBBBBBBBBBBBBBBBBBBBB)))(SubString IgnoreCase(SubjectProperty)=Incident - \\\")))}\"},{\"Name\":\"RuleName\",\"Value\":\"MyRule\"},{\"Name\":\"RuleProvider\",\"Value\":\"MyRuleProvider\"},{\"Name\":\"RuleActions\",\"Value\":\"[{\\\"ActionType\\\":\\\"DeferAction\\\",\\\"LengthOfDeferData\\\":\\\"1453\\\"}]\"}],\"OrganizationName\":\"example.onmicrosoft.com\",\"OriginatingServer\":\"RRRRRRRRRRRRR (15.20.4200.000)\\r\\n\",\"SessionId\":\"514b0ea7-73b8-4fa7-85f0-195fb3846a86\",\"Item\":{\"Id\":\"TTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTTT\",\"ImmutableId\":\"ErrorDuringIdConversion\",\"ParentFolder\":{\"Id\":\"EEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE\",\"Name\":\"Mailbox\",\"Path\":\"\\\\Mailbox\"}}}",
"event": {
"action": "UpdateInboxRules",
"category": [
"email",
"file"
],
"code": "2",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2025-02-13T09:53:51Z",
"action": {
"id": 2,
"name": "UpdateInboxRules",
"outcome": "success",
"target": "user"
},
"office365": {
"context": {
"aad_session_id": "514b0ea7-73b8-4fa7-85f0-195fb3846a86"
},
"exchange": {
"mailbox_guid": "e24b161f-f171-4db0-9572-4945279041c2",
"mailbox_owner": {
"sid": "user1",
"upn": "user1"
}
},
"operation": {
"properties": {
"RuleActions": [
{
"ActionType": "DeferAction",
"LengthOfDeferData": "1453"
}
],
"RuleCondition": "{(&((&((MessageToMe Equal True)(!((SubString Default(DisplayTo)=;)))))([RssServerLockStartTime=1, =/o=EXAMPLE/ou=Administrative (AAAAAAAAAAAAAAA)/cn=Recipients/cn=11111111111111111111111111111111111111111111, =Example, DisplayType=0], ((SenderSearchKey Equal EX:/O=EXAMPLE/OU=ADMINISTRATIVE (AAAAAAAAAAAAAAAAAAAA)/CN=RECIPIENTS/CN=BBBBBBBBBBBBBBBBBBBBBBBBBBBB)))(SubString IgnoreCase(SubjectProperty)=Incident - ")))}",
"RuleId": -5555555555555555555,
"RuleName": "MyRule",
"RuleOperation": "ModifyMailboxRule",
"RuleProvider": "MyRuleProvider",
"RuleState": "Enabled, ExitAfterExecution"
}
},
"record_id": "2b69a1a1-5e4e-4d1d-9feb-543d61b025e7",
"record_type": 2,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "Exchange"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"Id\":\"bb6e6d49\",\"RecordType\":20,\"CreationTime\":\"2023-08-22T13:51:33\",\"Operation\":\"ViewReport\",\"OrganizationId\":\"ANONYMIZED\",\"UserType\":0,\"UserKey\":\"user1\",\"Workload\":\"PowerBI\",\"UserId\":\"user1\",\"ClientIP\":\"1.2.3.4\",\"UserAgent\":\"Mozilla/5.0\",\"Activity\":\"ViewReport\",\"ItemName\":\"Tdb_TI\",\"WorkSpaceName\":\"Tableau de Bord Strat\\u00e9gique\",\"DatasetName\":\"Tdb_TI\",\"ReportName\":\"Tdb_TI\",\"CapacityId\":\"5A456BD6\",\"CapacityName\":\"P1_ACOSS\",\"WorkspaceId\":\"08d52dac\",\"AppName\":\"Tableaux de bord de pilotage\",\"ObjectId\":\"Tdb_TI\",\"DatasetId\":\"6f39a3c3\",\"ReportId\":\"213eb6fe\",\"ArtifactId\":\"213eb6fe\",\"ArtifactName\":\"Tdb_TI\",\"IsSuccess\":true,\"ReportType\":\"PowerBIReport\",\"RequestId\":\"94fea00c\",\"ActivityId\":\"147a0db5\",\"AppReportId\":\"fe6a9f80\",\"DistributionMethod\":\"Apps\",\"ConsumptionMethod\":\"Power BI Web\",\"AppId\":\"187ea3f4\",\"ArtifactKind\":\"Report\",\"RefreshEnforcementPolicy\":0}",
"event": {
"action": "ViewReport",
"code": "20",
"outcome": "success"
},
"@timestamp": "2023-08-22T13:51:33Z",
"action": {
"id": 20,
"name": "ViewReport",
"outcome": "success",
"target": "user"
},
"office365": {
"audit": {
"object_id": "Tdb_TI"
},
"record_id": "bb6e6d49",
"record_type": 20,
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "PowerBI"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "user1",
"name": "user1"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Other",
"original": "Mozilla/5.0",
"os": {
"name": "Other"
}
}
}
{
"message": "{\"CreationTime\":\"2024-07-10T14:31:24\",\"Id\":\"d1253377-388e-4ca1-a163-32dccb867ddd\",\"Operation\":\"Remove member from role.\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":8,\"ResultStatus\":\"Success\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ObjectId\":\"john.doe@example.com\",\"UserId\":\"user1\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"additionalDetails\",\"Value\":\"{}\"},{\"Name\":\"extendedAuditEventCategory\",\"Value\":\"Role\"}],\"ModifiedProperties\":[{\"Name\":\"Role.ObjectID\",\"NewValue\":\"\",\"OldValue\":\"62d603c4-9712-4ea9-83c6-1e253fad40a4\"},{\"Name\":\"Role.DisplayName\",\"NewValue\":\"\",\"OldValue\":\"Global Administrator\"},{\"Name\":\"Role.TemplateId\",\"NewValue\":\"\",\"OldValue\":\"2eb5763a-6258-4084-90d6-8f149a03132d\"},{\"Name\":\"Role.WellKnownObjectName\",\"NewValue\":\"\",\"OldValue\":\"TenantAdmins\"}],\"Actor\":[{\"ID\":\"user1\",\"Type\":5},{\"ID\":\"100320029D963D0D\",\"Type\":3},{\"ID\":\"User_47498f0f-242d-4ec8-8c13-9c861ce5669f\",\"Type\":2},{\"ID\":\"47498f0f-242d-4ec8-8c13-9c861ce5669f\",\"Type\":2},{\"ID\":\"User\",\"Type\":2}],\"ActorContextId\":\"ANONYMIZED\",\"InterSystemsId\":\"3da056e9-e6dc-4157-b991-8304c3b95eb7\",\"IntraSystemId\":\"e7bf6e46-a61f-417a-a11d-282756b8262f\",\"SupportTicketId\":\"\",\"Target\":[{\"ID\":\"User_1514c9ec-882d-4beb-99a9-301209f6a05a\",\"Type\":2},{\"ID\":\"1514c9ec-882d-4beb-99a9-301209f6a05a\",\"Type\":2},{\"ID\":\"User\",\"Type\":2},{\"ID\":\"john.doe@example.com\",\"Type\":5},{\"ID\":\"100320029D9D1C86\",\"Type\":3}],\"TargetContextId\":\"ANONYMIZED\"}",
"event": {
"action": "Remove member from role",
"category": [
"iam"
],
"code": "8",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-07-10T14:31:24Z",
"action": {
"id": 8,
"name": "Remove member from role",
"outcome": "success",
"target": "user"
},
"office365": {
"audit": {
"object_id": "john.doe@example.com"
},
"context": {
"correlation": {
"id": "3da056e9-e6dc-4157-b991-8304c3b95eb7"
},
"modified_properties": [
{
"Name": "Role.ObjectID",
"NewValue": "",
"OldValue": "62d603c4-9712-4ea9-83c6-1e253fad40a4"
},
{
"Name": "Role.DisplayName",
"NewValue": "",
"OldValue": "Global Administrator"
},
{
"Name": "Role.TemplateId",
"NewValue": "",
"OldValue": "2eb5763a-6258-4084-90d6-8f149a03132d"
},
{
"Name": "Role.WellKnownObjectName",
"NewValue": "",
"OldValue": "TenantAdmins"
}
]
},
"record_id": "d1253377-388e-4ca1-a163-32dccb867ddd",
"record_type": 8,
"result_status": "Success",
"target": {
"upn": "john.doe@example.com"
},
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"john.doe@example.com",
"user1"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"user": {
"id": "user1",
"name": "user1",
"target": {
"name": "john.doe@example.com"
}
}
}
{
"message": "{\"CreationTime\":\"2023-08-31T07:24:24\",\"Id\":\"ANONYMIZED\",\"Operation\":\"AlertTriggered\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"ANONYMIZED\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertId\":\"ANONYMIZED\",\"AlertLinks\":[{\"AlertLinkHref\":\"\"}],\"AlertType\":\"System\",\"Category\":\"ThreatManagement\",\"Comments\":\"New alert\",\"Data\":\"{\\\"ts\\\": \\\"2023-08-31T07:23:13.0000000Z\\\", \\\"te\\\": \\\"2023-08-31T07:23:13.0000000Z\\\", \\\"tid\\\": \\\"77f6d9ce-da8f-46bf-a651-4bec3c189770\\\", \\\"tdc\\\": \\\"1\\\", \\\"af\\\": \\\"0\\\", \\\"tht\\\": \\\"Phish,\\\\n\\\\nMalicious\\\", \\\"als\\\": \\\"Protection\\\", \\\"op\\\": \\\"Protection\\\", \\\"wsrt\\\": \\\"0001-01-01T00:00:00\\\", \\\"mdt\\\": \\\"u\\\", \\\"rid\\\": \\\"77f6d9ce-da8f-46bf-a651-4bec3c189770\\\", \\\"cid\\\": \\\"77f6d9ce-da8f-46bf-a651-4bec3c189770\\\", \\\"ad\\\": \\\"This\\\\nalert fires when message containing phish was delivered due to an ETR override. \\\\n-V1.0.0.5\\\", \\\"lon\\\": \\\"Protection\\\", \\\"an\\\": \\\"Phish delivered due to an ETR override\\\", \\\"sev\\\": \\\"Informational\\\"}\",\"Name\":\"Phish delivered due to an ETR override\",\"PolicyId\":\"ANONYMIZED\",\"Severity\":\"Informational\",\"Source\":\"Office 365 Security & Compliance\",\"Status\":\"Active\"}",
"event": {
"action": "AlertTriggered",
"category": [
"intrusion_detection"
],
"code": "40",
"kind": "alert",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2023-08-31T07:24:24Z",
"action": {
"id": 40,
"name": "AlertTriggered",
"outcome": "success",
"target": "user"
},
"office365": {
"alert": {
"category": "ThreatManagement",
"display_name": "Phish delivered due to an ETR override",
"id": "ANONYMIZED",
"severity": "Informational",
"source": "Office 365 Security & Compliance",
"status": "Active"
},
"audit": {
"object_id": "ANONYMIZED"
},
"record_id": "ANONYMIZED",
"record_type": 40,
"result_status": "Succeeded",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"rule": {
"id": "ANONYMIZED"
},
"service": {
"name": "SecurityComplianceCenter"
}
}
{
"message": "{\"CreationTime\":\"2024-04-04T08:15:14\",\"Id\":\"11c950ca-f6b6-4bbf-a0fc-bb287f9c1ef4\",\"Operation\":\"AlertEntityGenerated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"9ccf6a76-3106-4bad-ad80-fc515b137ba2\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertEntityId\":\"b2358a80-85d3-488e-8285-db123ce918a4\",\"AlertId\":\"cf0708c6-e2c5-4962-ae99-9af4799175f4\",\"AlertLinks\":[{\"AlertLinkHref\":\"\"}],\"AlertType\":\"Custom\",\"Category\":\"DataLossPrevention\",\"Comments\":\"New alert\",\"Data\":\"{\\\"etype\\\":\\\"DlpRuleMatch\\\",\\\"eid\\\":\\\"48aa73f6-b740-438b-861d-441281310de7\\\",\\\"tid\\\":\\\"21692c1b-2bd4-464a-aa27-6658fe410b4b\\\",\\\"ts\\\":\\\"2024-04-04T07:36:48.0000000Z\\\",\\\"te\\\":\\\"2024-04-04T07:36:48.0000000Z\\\",\\\"at\\\":\\\"2024-04-04T07:36:48.0000000Z\\\",\\\"dpid\\\":\\\"2401d128-ab89-4552-a6da-b2f77c3d212c\\\",\\\"dpn\\\":\\\"Data\\\",\\\"drid\\\":\\\"70ce5ca3-1da6-45d2-8699-8d470a719ab3\\\",\\\"drn\\\":\\\"rulename\\\",\\\"dmrid\\\":\\\"793fed0d-79e2-4bf8-b057-67c77a6db003\\\",\\\"wl\\\":\\\"Exchange\\\",\\\"von\\\":\\\"REDACTED\\\",\\\"dact\\\":\\\"GenerateAlert\\\",\\\"cc\\\":\\\"suspicious@example.com,spam.enquiries@example.org\\\",\\\"to\\\":\\\"john.doe@example.org\\\",\\\"mfrm\\\":\\\"spam@example.com\\\",\\\"dpm\\\":\\\"Enable\\\",\\\"lon\\\":\\\"DlpRuleMatch\\\"}\",\"EntityType\":\"DlpRuleMatch\",\"Name\":\"description\",\"PolicyId\":\"bef2401e-5c6c-476b-aedb-e2f521fafb1f\",\"Severity\":\"Low\",\"Source\":\"Office 365 Security & Compliance\",\"Status\":\"Active\"}",
"event": {
"action": "AlertEntityGenerated",
"category": [
"intrusion_detection"
],
"code": "40",
"kind": "alert",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-04-04T08:15:14Z",
"action": {
"id": 40,
"name": "AlertEntityGenerated",
"outcome": "success",
"target": "user"
},
"email": {
"cc": {
"address": [
"spam.enquiries@example.org",
"suspicious@example.com"
]
},
"from": {
"address": [
"spam@example.com"
]
},
"subject": "REDACTED",
"to": {
"address": [
"john.doe@example.org"
]
}
},
"office365": {
"alert": {
"category": "DataLossPrevention",
"display_name": "description",
"entity_type": "DlpRuleMatch",
"id": "cf0708c6-e2c5-4962-ae99-9af4799175f4",
"severity": "Low",
"source": "Office 365 Security & Compliance",
"status": "Active"
},
"audit": {
"object_id": "9ccf6a76-3106-4bad-ad80-fc515b137ba2"
},
"record_id": "11c950ca-f6b6-4bbf-a0fc-bb287f9c1ef4",
"record_type": 40,
"result_status": "Succeeded",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"rule": {
"id": "bef2401e-5c6c-476b-aedb-e2f521fafb1f"
},
"service": {
"name": "SecurityComplianceCenter"
}
}
{
"message": "{\"CreationTime\":\"2024-04-04T08:09:07\",\"Id\":\"9bb5e4b2-febd-4f1a-93bb-1380f7868320\",\"Operation\":\"AlertEntityGenerated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"4dde17d2-635a-498b-914e-73898a280433\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertEntityId\":\"a1bba0c6-d8d0-4710-8fc3-6085b3ac79fc\",\"AlertId\":\"178fa649-642f-4d41-943c-451e2266f4a7\",\"AlertLinks\":[{\"AlertLinkHref\":\"\"}],\"AlertType\":\"Custom\",\"Category\":\"MailFlow\",\"Comments\":\"New alert\",\"Data\":\"{\\\"etype\\\":\\\"MalwareFamily\\\",\\\"at\\\":\\\"2024-04-04T08:07:58.0000000Z\\\",\\\"md\\\":\\\"2024-04-04T08:07:58.0000000Z\\\",\\\"sip\\\":\\\"217.182.111.68\\\",\\\"ms\\\":\\\"REDACTED\\\",\\\"imsgid\\\":\\\"<f2231b61bc5cbb95893c5b62281e4f4c@example.com>\\\",\\\"dm\\\":\\\"CrossOrgSpoof\\\",\\\"eid\\\":\\\"58fe2050-27be-431f-a035-2cba142cb021-15828634862951700795-1\\\",\\\"aii\\\":\\\"58fe2050-27be-431f-a035-2cba142cb021\\\",\\\"thn\\\":\\\"Phish, Malicious\\\",\\\"ts\\\":\\\"2024-04-04T08:06:58.0000000Z\\\",\\\"te\\\":\\\"2024-04-04T08:08:58.0000000Z\\\",\\\"fvs\\\":\\\"Filters\\\",\\\"tpt\\\":\\\"AntiPhishPolicy\\\",\\\"tpid\\\":\\\"b3caa8a3-c6de-4d06-b2a4-8968c6d1f2d5\\\",\\\"tid\\\":\\\"7fca7e7b-11e7-48c7-b345-1145a7a3a918\\\",\\\"tht\\\":\\\"Phish, Malicious\\\",\\\"trc\\\":\\\"john.doe@example.org\\\",\\\"tsd\\\":\\\"communications@example.com\\\",\\\"tdc\\\":\\\"1\\\",\\\"cpid\\\":null,\\\"lon\\\":\\\"Protection\\\"}\",\"EntityType\":\"MalwareFamily\",\"Name\":\"Phishing detected\",\"PolicyId\":\"40663ca5-73da-43ca-b0be-af8b54987339\",\"Severity\":\"Low\",\"Source\":\"Office 365 Security & Compliance\",\"Status\":\"Active\"}",
"event": {
"action": "AlertEntityGenerated",
"category": [
"intrusion_detection"
],
"code": "40",
"kind": "alert",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-04-04T08:09:07Z",
"action": {
"id": 40,
"name": "AlertEntityGenerated",
"outcome": "success",
"target": "user"
},
"email": {
"from": {
"address": [
"communications@example.com"
]
},
"message_id": "f2231b61bc5cbb95893c5b62281e4f4c@example.com",
"subject": "REDACTED",
"to": {
"address": [
"john.doe@example.org"
]
}
},
"office365": {
"alert": {
"category": "MailFlow",
"display_name": "Phishing detected",
"entity_type": "MalwareFamily",
"id": "178fa649-642f-4d41-943c-451e2266f4a7",
"severity": "Low",
"source": "Office 365 Security & Compliance",
"status": "Active"
},
"audit": {
"object_id": "4dde17d2-635a-498b-914e-73898a280433"
},
"record_id": "9bb5e4b2-febd-4f1a-93bb-1380f7868320",
"record_type": 40,
"result_status": "Succeeded",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"john.doe"
]
},
"rule": {
"id": "40663ca5-73da-43ca-b0be-af8b54987339"
},
"service": {
"name": "SecurityComplianceCenter"
},
"user": {
"domain": "example.org",
"email": "john.doe@example.org",
"name": "john.doe"
}
}
{
"message": "{\"CreationTime\":\"2024-04-04T08:22:40\",\"Id\":\"ANONYMIZED\",\"Operation\":\"AlertEntityGenerated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"john.doe@example.org\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertEntityId\":\"john.doe@example.org\",\"AlertId\":\"ANONYMIZED\",\"AlertLinks\":[{\"AlertLinkHref\":\"\"}],\"AlertType\":\"System\",\"Category\":\"ThreatManagement\",\"Comments\":\"New alert\",\"Data\":\"{\\\"etype\\\":\\\"User\\\",\\\"eid\\\":\\\"john.doe@example.org\\\",\\\"tid\\\":\\\"be2ee3c6-2b3c-42ae-aefe-69f185114418\\\",\\\"ts\\\":\\\"2024-04-04T08:20:21.0000000Z\\\",\\\"te\\\":\\\"2024-04-04T08:20:21.0000000Z\\\",\\\"op\\\":\\\"UserSubmission\\\",\\\"tdc\\\":\\\"1\\\",\\\"suid\\\":\\\"john.doe@example.org\\\",\\\"ut\\\":\\\"Regular\\\",\\\"ssic\\\":\\\"0\\\",\\\"tsd\\\":\\\"REDACTED\\\",\\\"sip\\\":\\\"1.2.3.4\\\",\\\"srt\\\":\\\"0\\\",\\\"trc\\\":\\\"john.doe@example.org\\\",\\\"ms\\\":\\\"REDACTED\\\",\\\"sid\\\":\\\"be2ee3c6-2b3c-42ae-aefe-69f185114418\\\",\\\"aii\\\":\\\"be2ee3c6-2b3c-42ae-aefe-69f185114418\\\",\\\"md\\\":\\\"2024-04-04T07:50:14.0000000Z\\\",\\\"etps\\\":\\\"KesMailId:1111111111111111;FingerprintData:AAAAAAAA.BBBBBBBB.CCCCCCCF.72AC895E.200F2;SubmissionCategory:Email;RescanVerdict:NotSpam;SubmissionSource:Microsoft;SubmissionId:be2ee3c6-2b3c-42ae-aefe-69f185114418;OriginalVerdict:Allow\\\",\\\"lon\\\":\\\"UserSubmission\\\"}\",\"EntityType\":\"User\",\"Name\":\"Email reported by user as junk\",\"PolicyId\":\"ANONYMIZED\",\"Severity\":\"Low\",\"Source\":\"Office 365 Security & Compliance\",\"Status\":\"Active\"}",
"event": {
"action": "AlertEntityGenerated",
"category": [
"intrusion_detection"
],
"code": "40",
"kind": "alert",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-04-04T08:22:40Z",
"action": {
"id": 40,
"name": "AlertEntityGenerated",
"outcome": "success",
"target": "user"
},
"email": {
"from": {
"address": [
"REDACTED"
]
},
"subject": "REDACTED",
"to": {
"address": [
"john.doe@example.org"
]
}
},
"office365": {
"alert": {
"category": "ThreatManagement",
"display_name": "Email reported by user as junk",
"entity_type": "User",
"id": "ANONYMIZED",
"severity": "Low",
"source": "Office 365 Security & Compliance",
"status": "Active"
},
"audit": {
"object_id": "john.doe@example.org"
},
"record_id": "ANONYMIZED",
"record_type": 40,
"result_status": "Succeeded",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"john.doe"
]
},
"rule": {
"id": "ANONYMIZED"
},
"service": {
"name": "SecurityComplianceCenter"
},
"user": {
"domain": "example.org",
"email": "john.doe@example.org",
"name": "john.doe"
}
}
{
"message": "{\"CreationTime\":\"2024-04-16T08:01:42\",\"Id\":\"d7cab54f-77b1-4ad5-8f2d-b4bba61e4e93\",\"Operation\":\"AlertEntityGenerated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"jdoe@example.org\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertEntityId\":\"jdoe@example.org\",\"AlertId\":\"a3ce0859-c92c-4f57-b50b-a63dad75ec4a\",\"AlertLinks\":[],\"AlertType\":\"System\",\"Category\":\"ThreatManagement\",\"Comments\":\"New alert\",\"Data\":\"\",\"EntityType\":\"User\",\"Name\":\"Email reported by user as malware or phish\",\"PolicyId\":\"88d533c5-bad6-4cfb-9245-1776726b55d7\",\"Severity\":\"Low\",\"Source\":\"Office 365 Security & Compliance\",\"Status\":\"Investigating\"}",
"event": {
"action": "AlertEntityGenerated",
"category": [
"intrusion_detection"
],
"code": "40",
"kind": "alert",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-04-16T08:01:42Z",
"action": {
"id": 40,
"name": "AlertEntityGenerated",
"outcome": "success",
"target": "user"
},
"office365": {
"alert": {
"category": "ThreatManagement",
"display_name": "Email reported by user as malware or phish",
"id": "a3ce0859-c92c-4f57-b50b-a63dad75ec4a",
"severity": "Low",
"source": "Office 365 Security & Compliance",
"status": "Investigating"
},
"audit": {
"object_id": "jdoe@example.org"
},
"record_id": "d7cab54f-77b1-4ad5-8f2d-b4bba61e4e93",
"record_type": 40,
"result_status": "Succeeded",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"rule": {
"id": "88d533c5-bad6-4cfb-9245-1776726b55d7"
},
"service": {
"name": "SecurityComplianceCenter"
}
}
{
"message": "{\"CreationTime\":\"2024-10-24T09:10:38\",\"Id\":\"9b1762d6-2667-4c2d-ad8f-5faa9b9dbad8\",\"Operation\":\"AlertEntityGenerated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"32c70dd6-ce69-434d-b52a-0d876696fd8d-9402318098831178296-1\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertEntityId\":\"32c70dd6-ce69-434d-b52a-0d876696fd8d-9402318098831178296-1\",\"AlertId\":\"6c88ef80-67f0-4a32-b1c9-4696ba48a3e4\",\"AlertLinks\":[{\"AlertLinkHref\":\"\"}],\"AlertType\":\"System\",\"Category\":\"ThreatManagement\",\"Comments\":\"New alert\",\"Data\":\"{\\\"etype\\\":\\\"MalwareFamily\\\",\\\"at\\\":\\\"2024-10-24T09:07:19.0000000Z\\\",\\\"md\\\":\\\"2024-10-24T07:08:32.0000000Z\\\",\\\"sip\\\":null,\\\"ms\\\":\\\"REDACTED\\\",\\\"imsgid\\\":\\\"<AFIA3GCDITNgUgIKlOF5n5oH.1.1729763630549.mail.evil@example.com>\\\",\\\"ttdt\\\":\\\"2024-10-24T09:07:19.0000000Z\\\",\\\"ttr\\\":\\\"Success_MessageQuarantined\\\",\\\"dm\\\":\\\"UrlReputation\\\",\\\"eid\\\":\\\"32c70dd6-ce69-434d-b52a-0d876696fd8d-9402318098831178296-1\\\",\\\"aii\\\":\\\"32c70dd6-ce69-434d-b52a-0d876696fd8d\\\",\\\"thn\\\":\\\"Phish, Malicious\\\",\\\"ts\\\":\\\"2024-10-24T09:06:19.0000000Z\\\",\\\"te\\\":\\\"2024-10-24T09:08:19.0000000Z\\\",\\\"fvs\\\":\\\"Filters\\\",\\\"tpt\\\":\\\"HostedContentFilterPolicy\\\",\\\"tpid\\\":\\\"f0749efa-70b1-4420-94f7-9527b4f7f677\\\",\\\"tid\\\":\\\"3995fc59-1c0e-4812-b0f1-5308a209ef5e\\\",\\\"tht\\\":\\\"Phish, Malicious\\\",\\\"trc\\\":\\\"user1@example.com\\\",\\\"tsd\\\":\\\"evil@example.com\\\",\\\"zu\\\":\\\"clickonthis.example.com/api/phishing\\\",\\\"pud\\\":\\\"clickonthis.example.com/api/phishing\\\",\\\"tdc\\\":\\\"1\\\",\\\"cpid\\\":null,\\\"lon\\\":\\\"Protection\\\"}\",\"EntityType\":\"MalwareFamily\",\"Name\":\"Email messages containing malicious URL removed after delivery\\u200b\",\"PolicyId\":\"55087523-49bd-4bbd-b269-cda496a06d05\",\"Severity\":\"Informational\",\"Source\":\"Office 365 Security & Compliance\",\"Status\":\"Active\"}",
"event": {
"action": "AlertEntityGenerated",
"category": [
"intrusion_detection"
],
"code": "40",
"kind": "alert",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-10-24T09:10:38Z",
"action": {
"id": 40,
"name": "AlertEntityGenerated",
"outcome": "success",
"target": "user"
},
"email": {
"from": {
"address": [
"evil@example.com"
]
},
"message_id": "AFIA3GCDITNgUgIKlOF5n5oH.1.1729763630549.mail.evil@example.com",
"subject": "REDACTED",
"to": {
"address": [
"user1@example.com"
]
}
},
"office365": {
"alert": {
"category": "ThreatManagement",
"display_name": "Email messages containing malicious URL removed after delivery\u200b",
"entity_type": "MalwareFamily",
"id": "6c88ef80-67f0-4a32-b1c9-4696ba48a3e4",
"severity": "Informational",
"source": "Office 365 Security & Compliance",
"status": "Active"
},
"audit": {
"object_id": "32c70dd6-ce69-434d-b52a-0d876696fd8d-9402318098831178296-1"
},
"record_id": "9b1762d6-2667-4c2d-ad8f-5faa9b9dbad8",
"record_type": 40,
"result_status": "Succeeded",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"rule": {
"id": "55087523-49bd-4bbd-b269-cda496a06d05"
},
"service": {
"name": "SecurityComplianceCenter"
},
"url": {
"domain": "clickonthis.example.com",
"original": "//clickonthis.example.com/api/phishing",
"path": "/api/phishing",
"registered_domain": "example.com",
"subdomain": "clickonthis",
"top_level_domain": "com"
},
"user": {
"domain": "example.com",
"email": "user1@example.com",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2025-01-31T23:11:21\",\"Id\":\"3af6fbb3-040e-4ecc-4e18-08dd424c935a\",\"Operation\":\"AlertEntityGenerated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"test@example.com\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertEntityId\":\"BIURO\",\"AlertId\":\"b69ac1d6-7546-4f1b-a15f-fca0b5a7d005\",\"AlertLinks\":[{\"AlertLinkHref\":\"\"}],\"AlertType\":\"System\",\"Category\":\"ThreatManagement\",\"Comments\":\"New alert\",\"Data\":\"{\\\"etype\\\":\\\"User\\\",\\\"eid\\\":\\\"test@example.com\\\",\\\"tid\\\":\\\"abcdef123-ecef-4cb1-a848-794d17916b7b\\\",\\\"ts\\\":\\\"2025-01-31T23:09:52.0000000Z\\\",\\\"te\\\":\\\"2025-01-31T23:09:52.0000000Z\\\",\\\"op\\\":\\\"CompromisedAccount\\\",\\\"tdc\\\":\\\"1\\\",\\\"suid\\\":\\\"john.doe@example.com\\\",\\\"ut\\\":\\\"System\\\",\\\"ssic\\\":\\\"0\\\",\\\"lon\\\":\\\"CompromisedAccount\\\"}\",\"EntityType\":\"User\",\"Name\":\"User restricted from sending email\",\"PolicyId\":\"5bd8e1ef-44f4-4a67-b40f-48fd576ec779\",\"Severity\":\"High\",\"Source\":\"Office 365 Security & Compliance\",\"Status\":\"Active\"}",
"event": {
"action": "AlertEntityGenerated",
"category": [
"intrusion_detection"
],
"code": "40",
"kind": "alert",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2025-01-31T23:11:21Z",
"action": {
"id": 40,
"name": "AlertEntityGenerated",
"outcome": "success",
"target": "user"
},
"office365": {
"alert": {
"category": "ThreatManagement",
"display_name": "User restricted from sending email",
"entity_type": "User",
"id": "b69ac1d6-7546-4f1b-a15f-fca0b5a7d005",
"severity": "High",
"source": "Office 365 Security & Compliance",
"status": "Active"
},
"audit": {
"object_id": "test@example.com"
},
"record_id": "3af6fbb3-040e-4ecc-4e18-08dd424c935a",
"record_type": 40,
"result_status": "Succeeded",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"john.doe"
]
},
"rule": {
"id": "5bd8e1ef-44f4-4a67-b40f-48fd576ec779"
},
"service": {
"name": "SecurityComplianceCenter"
},
"user": {
"domain": "example.com",
"email": "john.doe@example.com",
"name": "john.doe"
}
}
{
"message": "{\"CreationTime\":\"2024-10-07T20:29:25\",\"Id\":\"33c6081c-a402-49a3-828e-8e6df08c5e90\",\"Operation\":\"AlertEntityGenerated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"https://example.com/\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertEntityId\":\"https://example.com/\",\"AlertId\":\"657fb16a-ee7f-4939-a218-33ba3c72805e\",\"AlertLinks\":[{\"AlertLinkHref\":\"\"}],\"AlertType\":\"System\",\"Category\":\"ThreatManagement\",\"Comments\":\"New alert\",\"Data\":\"{\\\"etype\\\":\\\"MaliciousUrl\\\",\\\"aii\\\":\\\"d6c7276b-3a65-43c7-9e25-525f7e289543\\\",\\\"eid\\\":\\\"https://test-d7a3.evil.net/?param=SGVsbG8gV29ybGQh\\\",\\\"curlh\\\":\\\"12815939189066485645\\\",\\\"tid\\\":\\\"b76bf78d-7696-4b17-bbda-e9995c266879\\\",\\\"ts\\\":\\\"2024-10-07T20:07:11.0000000Z\\\",\\\"te\\\":\\\"2024-10-07T20:07:11.0000000Z\\\",\\\"trc\\\":\\\"user1@example.org\\\",\\\"tdc\\\":\\\"1\\\",\\\"at\\\":\\\"2024-10-07T20:07:11.0000000Z\\\",\\\"dm\\\":\\\"MDO Safe Links\\\",\\\"ot\\\":\\\"Allowed\\\",\\\"od\\\":\\\"User clicked on a URL which was identified as potentially malicious at a later time.\\\",\\\"md\\\":\\\"2024-10-07T20:29:25.5945545Z\\\",\\\"lon\\\":\\\"MaliciousUrlClick\\\"}\",\"EntityType\":\"MaliciousUrl\",\"Name\":\"A potentially malicious URL click was detected\",\"PolicyId\":\"471d921d-e417-41c4-be33-ad67040f3ece\",\"Severity\":\"High\",\"Source\":\"Office 365 Security & Compliance\",\"Status\":\"Active\"}",
"event": {
"action": "AlertEntityGenerated",
"category": [
"intrusion_detection"
],
"code": "40",
"kind": "alert",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-10-07T20:29:25Z",
"action": {
"id": 40,
"name": "AlertEntityGenerated",
"outcome": "success",
"target": "user"
},
"email": {
"to": {
"address": [
"user1@example.org"
]
}
},
"office365": {
"alert": {
"category": "ThreatManagement",
"display_name": "A potentially malicious URL click was detected",
"entity_type": "MaliciousUrl",
"id": "657fb16a-ee7f-4939-a218-33ba3c72805e",
"severity": "High",
"source": "Office 365 Security & Compliance",
"status": "Active"
},
"audit": {
"object_id": "https://example.com/"
},
"record_id": "33c6081c-a402-49a3-828e-8e6df08c5e90",
"record_type": 40,
"result_status": "Succeeded",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"rule": {
"id": "471d921d-e417-41c4-be33-ad67040f3ece"
},
"service": {
"name": "SecurityComplianceCenter"
},
"url": {
"domain": "example.com",
"full": "https://example.com/",
"original": "https://example.com/",
"path": "/",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"domain": "example.org",
"email": "user1@example.org",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\":{\"AADSessionId\":\"ANONYMIZED\",\"CorrelationId\":\"ANONYMIZED\",\"UniqueTokenId\":\"ANONYMIZED\"},\"CreationTime\":\"2023-12-13T09:43:17\",\"Id\":\"ANONYMIZED\",\"Operation\":\"AccessRequestCreated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":14,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"SharePoint\",\"ClientIP\":\"0.0.0.0\",\"UserId\":\"user1\",\"AuthenticationType\":\"FormsCookieAuth\",\"BrowserName\":\"Chrome\",\"BrowserVersion\":\"120.0.0.0\",\"CorrelationId\":\"ANONYMIZED\",\"EventSource\":\"SharePoint\",\"IsManagedDevice\":false,\"ItemType\":\"File\",\"ListId\":\"xxxxx\",\"ListItemUniqueId\":\"xxxxx\",\"Platform\":\"WinDesktop\",\"Site\":\"xxxxxxxxx\",\"UserAgent\":\"Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36\",\"WebId\":\"xxxxxxxxx\",\"DeviceDisplayName\":\"xxxxxxxxx\",\"EventData\":\"<SharingLevel>Lecture</SharingLevel><ExpirationDate>12/03/2024 09:43:15</ExpirationDate>\",\"SourceFileExtension\":\"xlsx\",\"TargetUserOrGroupType\":\"Member\",\"TargetUserOrGroupName\":\"user1\",\"SiteUrl\":\"https://maindomain.com/subdomain/endvalue\",\"SourceRelativeUrl\":\"Documents partages/xxxxx.xlsx\",\"SourceFileName\":\"https://example.com/\",\"ObjectId\":\"https://example.com/\"}",
"event": {
"action": "AccessRequestCreated",
"category": [
"file"
],
"code": "14",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2023-12-13T09:43:17Z",
"action": {
"id": 14,
"name": "AccessRequestCreated",
"outcome": "success",
"properties": [
{
"SiteUrl": "https://maindomain.com/subdomain/endvalue",
"SourceFileName": "https://example.com/",
"SourceRelativeUrl": "Documents partages/xxxxx.xlsx",
"UserAgent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36"
}
],
"target": "user"
},
"azuread": {
"properties": {
"uniqueTokenIdentifier": "ANONYMIZED"
}
},
"file": {
"directory": "Documents partages/xxxxx.xlsx",
"extension": "xlsx",
"name": "https://example.com/"
},
"office365": {
"audit": {
"item_type": "File",
"object_id": "https://example.com/",
"platform": "WinDesktop"
},
"context": {
"aad_session_id": "ANONYMIZED",
"authentication_type": "FormsCookieAuth",
"correlation": {
"id": "ANONYMIZED"
}
},
"device": {
"is_managed": false
},
"record_id": "ANONYMIZED",
"record_type": 14,
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"0.0.0.0"
],
"user": [
"user1"
]
},
"service": {
"name": "SharePoint"
},
"source": {
"address": "0.0.0.0",
"ip": "0.0.0.0"
},
"url": {
"domain": "example.com",
"full": "https://example.com/",
"original": "https://example.com/",
"path": "/",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"id": "user1",
"name": "user1",
"target": {
"name": "user1"
}
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Chrome",
"original": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36",
"os": {
"name": "Windows",
"version": "10"
},
"version": "120.0.0"
}
}
{
"message": "{\"AppAccessContext\":{\"AADSessionId\":\"ANONYMIZED\",\"ClientAppId\":\"ANONYMIZED\",\"ClientAppName\":\"Microsoft Teams\",\"CorrelationId\":\"ANONYMIZED\",\"UniqueTokenId\":\"xxxxxx\"},\"CreationTime\":\"2024-10-29T07:41:53\",\"Id\":\"ANONYMIZED\",\"Operation\":\"AddedToSecureLink\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":14,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"OneDrive\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"user1\",\"ApplicationId\":\"ANONYMIZED\",\"AuthenticationType\":\"OAuth\",\"BrowserName\":\"Edge\",\"BrowserVersion\":\"130.0.0.0\",\"CorrelationId\":\"ANONYMIZED\",\"EventSource\":\"SharePoint\",\"GeoLocation\":\"EUR\",\"IsManagedDevice\":true,\"ItemType\":\"File\",\"ListId\":\"ANONYMIZED\",\"ListItemUniqueId\":\"ANONYMIZED\",\"Platform\":\"WinDesktop\",\"Site\":\"ANONYMIZED\",\"UserAgent\":\"Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36 Edg/130.0.0.0 Teams/24257.205.3165.2029/49\",\"WebId\":\"ANONYMIZED\",\"DeviceDisplayName\":\"ANONYMIZED\",\"EventData\":\"<Type>Edit</Type><MembersCanShareApplied>False</MembersCanShareApplied>\",\"SourceFileExtension\":\"pdf\",\"TargetUserOrGroupType\":\"Member\",\"UniqueSharingId\":\"ANONYMIZED\",\"TargetUserOrGroupName\":\"user1\",\"SiteUrl\":\"https://compagny-my.sharepoint.com/personal/usrename\",\"SourceRelativeUrl\":\"Documents/filename.pdf\",\"SourceFileName\":\"filename.pdf\",\"ApplicationDisplayName\":\"Microsoft Teams\",\"ObjectId\":\"https://example.com/\",\"AssociatedAdminUnits\":[\"ANONYMIZED\"]}",
"event": {
"action": "AddedToSecureLink",
"category": [
"file"
],
"code": "14",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-10-29T07:41:53Z",
"action": {
"id": 14,
"name": "AddedToSecureLink",
"outcome": "success",
"properties": [
{
"SiteUrl": "https://compagny-my.sharepoint.com/personal/usrename",
"SourceFileName": "filename.pdf",
"SourceRelativeUrl": "Documents/filename.pdf",
"UserAgent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36 Edg/130.0.0.0 Teams/24257.205.3165.2029/49"
}
],
"target": "user"
},
"azuread": {
"properties": {
"uniqueTokenIdentifier": "xxxxxx"
}
},
"file": {
"directory": "Documents/filename.pdf",
"extension": "pdf",
"name": "filename.pdf"
},
"office365": {
"audit": {
"item_type": "File",
"object_id": "https://example.com/",
"platform": "WinDesktop"
},
"context": {
"aad_session_id": "ANONYMIZED",
"authentication_type": "OAuth",
"client": {
"id": "ANONYMIZED",
"name": "Microsoft Teams"
},
"correlation": {
"id": "ANONYMIZED"
}
},
"device": {
"is_managed": true
},
"record_id": "ANONYMIZED",
"record_type": 14,
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "OneDrive"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"url": {
"domain": "example.com",
"full": "https://example.com/",
"original": "https://example.com/",
"path": "/",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"id": "user1",
"name": "user1",
"target": {
"name": "user1"
}
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Edge",
"original": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.0.0 Safari/537.36 Edg/130.0.0.0 Teams/24257.205.3165.2029/49",
"os": {
"name": "Windows",
"version": "10"
},
"version": "130.0.0"
}
}
{
"message": "{\"CreationTime\":\"2022-04-05T19:51:35\",\"Id\":\"1324e3d2-f29c-5c15-9f44-1ca64e42250f\",\"Operation\":\"MessageCreatedHasLink\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":25,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"MicrosoftTeams\",\"ClientIP\":\"::ffff:1.2.3.4\",\"UserId\":\"user1\",\"ChatThreadId\":\"19:11dbae04-5d5d-4bc7-9766-16793ed91233_4fdb1e07-a7e9-475c-a5e2-8d042a6c8102@unq.gbl.spaces\",\"CommunicationType\":\"OneOnOne\",\"ExtraProperties\":[{\"Key\":\"TimeZone\",\"Value\":\"Europe/Paris\"},{\"Key\":\"OsName\",\"Value\":\"windows\"},{\"Key\":\"OsVersion\",\"Value\":\"10\"},{\"Key\":\"Country\",\"Value\":\"fr\"},{\"Key\":\"ClientName\",\"Value\":\"skypeteams\"},{\"Key\":\"ClientVersion\",\"Value\":\"27/1.0.0.2022031814\"},{\"Key\":\"ClientUtcOffsetSeconds\",\"Value\":\"7200\"}],\"MessageId\":\"1649188295480\",\"MessageVersion\":\"1649188295480\",\"ItemName\":\"19:11dbae04-5d5d-4bc7-9766-16793ed91233_4fdb1e07-a7e9-475c-a5e2-8d042a6c8102@unq.gbl.spaces\",\"MessageURLs\":[\"https://example.com/\"],\"Members\":[{\"UPN\":\"admin@example.org\",\"Role\":1},{\"UPN\":\"user1@example.org\",\"Role\":0}]}",
"event": {
"action": "MessageCreatedHasLink",
"category": [
"network"
],
"code": "25",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2022-04-05T19:51:35Z",
"action": {
"id": 25,
"name": "MessageCreatedHasLink",
"outcome": "success",
"target": "network-traffic"
},
"office365": {
"record_id": "1324e3d2-f29c-5c15-9f44-1ca64e42250f",
"record_type": 25,
"teams": {
"communication": {
"type": "OneOnOne"
},
"message": {
"id": "1649188295480",
"urls": [
"https://example.com/"
],
"version": "1649188295480"
},
"team": {
"members": [
{
"id": "admin@example.org",
"role": "Owner"
},
{
"id": "user1@example.org",
"role": "Member"
}
]
}
},
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "MicrosoftTeams"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"url": {
"domain": "example.com",
"full": "https://example.com/",
"original": "https://example.com/",
"path": "/",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"AppAccessContext\":{\"IssuedAtTime\":\"2024-06-10T06:51:28\",\"UniqueTokenId\":\"mYyWp_-UrEa4Z_pZM7FlAA\"},\"CreationTime\":\"2024-06-10T11:50:24\",\"Id\":\"4e3612b5-9cf5-4c6d-8213-2ba12af15334\",\"Operation\":\"ChatCreated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":25,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"MicrosoftTeams\",\"ClientIP\":\"192.0.2.1\",\"UserId\":\"user1\",\"ChatThreadId\":\"19:2546ebff-72fd-4fda-b537-bc31bf5e1d4c_ba359007-06c1-497f-bc4a-41ea45df4cbd@unq.gbl.spaces\",\"CommunicationType\":\"OneOnOne\",\"ExtraProperties\":[{\"Key\":\"TimeZone\",\"Value\":\"Europe/Paris\"},{\"Key\":\"OsName\",\"Value\":\"windows\"},{\"Key\":\"OsVersion\",\"Value\":\"10\"},{\"Key\":\"Country\",\"Value\":\"fr\"},{\"Key\":\"ClientName\",\"Value\":\"skypeteams\"},{\"Key\":\"ClientVersion\",\"Value\":\"27/1.0.0.2024052206\"},{\"Key\":\"ClientUtcOffsetSeconds\",\"Value\":\"7200\"}],\"Members\":[{\"OrganizationId\":\"6d869a66-371f-4b76-a1f6-3c115469a99d\",\"DisplayName\":\"John Doe\",\"UPN\":\"john.doe@example.org\"},{\"OrganizationId\":\"6db03b45-27a2-4662-9121-fa5773a8e043\",\"DisplayName\":\"Jane Doe\",\"UPN\":\"jane.doe@example.com\"}],\"ParticipantInfo\":{\"HasForeignTenantUsers\":true,\"HasGuestUsers\":false,\"HasOtherGuestUsers\":false,\"HasUnauthenticatedUsers\":false,\"ParticipatingDomains\":[\"example.org\",\"example.com\"],\"ParticipatingSIPDomains\":[{\"DomainName\":\"example.org\",\"TenantId\":\"6d869a66-371f-4b76-a1f6-3c115469a99d\"},{\"DomainName\":\"example.com\",\"TenantId\":\"6db03b45-27a2-4662-9121-fa5773a8e043\"}],\"ParticipatingTenantIds\":[\"6d869a66-371f-4b76-a1f6-3c115469a99d\",\"6db03b45-27a2-4662-9121-fa5773a8e043\"]},\"ResourceTenantId\":\"6db03b45-27a2-4662-9121-fa5773a8e043\",\"ItemName\":\"19:2546ebff-72fd-4fda-b537-bc31bf5e1d4c_ba359007-06c1-497f-bc4a-41ea45df4cbd@unq.gbl.spaces\"}",
"event": {
"action": "ChatCreated",
"category": [
"network"
],
"code": "25",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-06-10T11:50:24Z",
"action": {
"id": 25,
"name": "ChatCreated",
"outcome": "success",
"target": "network-traffic"
},
"azuread": {
"properties": {
"uniqueTokenIdentifier": "mYyWp_-UrEa4Z_pZM7FlAA"
}
},
"office365": {
"record_id": "4e3612b5-9cf5-4c6d-8213-2ba12af15334",
"record_type": 25,
"teams": {
"communication": {
"type": "OneOnOne"
},
"has_foreign_tenant_users": true,
"team": {
"members": [
{
"id": "john.doe@example.org",
"name": "John Doe"
},
{
"id": "jane.doe@example.com",
"name": "Jane Doe"
}
]
}
},
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"service": {
"name": "MicrosoftTeams"
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2024-07-12T08:27:46\",\"Id\":\"5964f7bd-8775-4dbe-84a8-37573510558c\",\"Operation\":\"ChatCreated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":25,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"MicrosoftTeams\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"user1\",\"ChatThreadId\":\"19:9ac303ea-1bf3-442c-a216-a517de868921_413e1939-c450-4d63-8226-b02a542e6a9a@unq.gbl.spaces\",\"CommunicationType\":\"OneOnOne\",\"ExtraProperties\":[{\"Key\":\"TimeZone\",\"Value\":\"Europe/Berlin\"},{\"Key\":\"OsName\",\"Value\":\"windows\"},{\"Key\":\"OsVersion\",\"Value\":\"NT 10.0\"},{\"Key\":\"Country\",\"Value\":\"de\"},{\"Key\":\"ClientName\",\"Value\":\"skypeteams\"},{\"Key\":\"ClientVersion\",\"Value\":\"49/24061318408\"},{\"Key\":\"ClientUtcOffsetSeconds\",\"Value\":\"7200\"}],\"Members\":[{\"OrganizationId\":\"ANONYMIZED\",\"DisplayName\":\"John Doe\",\"UPN\":\"user1\"},{\"OrganizationId\":\"f35fe983-e797-44ce-bd0b-cf4da93a8043\",\"DisplayName\":\"Jane Doe\",\"UPN\":\"jane.doe@example2.com\"}],\"ParticipantInfo\":{\"HasForeignTenantUsers\":true,\"HasGuestUsers\":false,\"HasOtherGuestUsers\":false,\"HasUnauthenticatedUsers\":false,\"ParticipatingDomains\":[\"example1.com\",\"example2.com\"],\"ParticipatingSIPDomains\":[{\"DomainName\":\"example1.com\",\"TenantId\":\"ANONYMIZED\"},{\"DomainName\":\"example2.com\",\"TenantId\":\"f35fe983-e797-44ce-bd0b-cf4da93a8043\"}],\"ParticipatingTenantIds\":[\"f35fe983-e797-44ce-bd0b-cf4da93a8043\",\"ANONYMIZED\"]},\"ResourceTenantId\":\"ANONYMIZED\",\"ItemName\":\"19:9ac303ea-1bf3-442c-a216-a517de868921_413e1939-c450-4d63-8226-b02a542e6a9a@unq.gbl.spaces\"}",
"event": {
"action": "ChatCreated",
"category": [
"network"
],
"code": "25",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-07-12T08:27:46Z",
"action": {
"id": 25,
"name": "ChatCreated",
"outcome": "success",
"target": "network-traffic"
},
"office365": {
"record_id": "5964f7bd-8775-4dbe-84a8-37573510558c",
"record_type": 25,
"teams": {
"communication": {
"type": "OneOnOne"
},
"has_foreign_tenant_users": true,
"team": {
"members": [
{
"id": "user1",
"name": "John Doe"
},
{
"id": "jane.doe@example2.com",
"name": "Jane Doe"
}
]
}
},
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "MicrosoftTeams"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2024-07-12T08:27:37\",\"Id\":\"db1cd437-5417-4cd3-ae6b-19a980f9bcfc\",\"Operation\":\"ChatCreated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":25,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"MicrosoftTeams\",\"ClientIP\":\"1.2.3.4\",\"UserId\":\"user1\",\"ChatThreadId\":\"19:d473ae3c-906c-4a72-8b3f-18e6c9bfdcd7_4daf1829-8823-454f-b4e0-1cd22342d5f3@unq.gbl.spaces\",\"CommunicationType\":\"OneOnOne\",\"ExtraProperties\":[{\"Key\":\"TimeZone\",\"Value\":\"Europe/Berlin\"},{\"Key\":\"OsName\",\"Value\":\"windows\"},{\"Key\":\"OsVersion\",\"Value\":\"NT 10.0\"},{\"Key\":\"Country\",\"Value\":\"de\"},{\"Key\":\"ClientName\",\"Value\":\"skypeteams\"},{\"Key\":\"ClientVersion\",\"Value\":\"49/24061318408\"},{\"Key\":\"ClientUtcOffsetSeconds\",\"Value\":\"7200\"}],\"Members\":[{\"OrganizationId\":\"ANONYMIZED\",\"DisplayName\":\"John Doe\",\"UPN\":\"user1\"},{\"OrganizationId\":\"1d36ca61-5509-4ac7-983d-91dfdeb5f492\",\"DisplayName\":\"Jane Doe\",\"UPN\":\"jane.doe@example2.com\"}],\"ParticipantInfo\":{\"HasForeignTenantUsers\":true,\"HasGuestUsers\":false,\"HasOtherGuestUsers\":false,\"HasUnauthenticatedUsers\":false,\"ParticipatingDomains\":[\"example1.com\",\"example2.com\"],\"ParticipatingSIPDomains\":[{\"DomainName\":\"example1.com\",\"TenantId\":\"ANONYMIZED\"},{\"DomainName\":\"example2.com\",\"TenantId\":\"1d36ca61-5509-4ac7-983d-91dfdeb5f492\"}],\"ParticipatingTenantIds\":[\"1d36ca61-5509-4ac7-983d-91dfdeb5f492\",\"ANONYMIZED\"]},\"ResourceTenantId\":\"ANONYMIZED\",\"ItemName\":\"19:d473ae3c-906c-4a72-8b3f-18e6c9bfdcd7_4daf1829-8823-454f-b4e0-1cd22342d5f3@unq.gbl.spaces\"}",
"event": {
"action": "ChatCreated",
"category": [
"network"
],
"code": "25",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-07-12T08:27:37Z",
"action": {
"id": 25,
"name": "ChatCreated",
"outcome": "success",
"target": "network-traffic"
},
"office365": {
"record_id": "db1cd437-5417-4cd3-ae6b-19a980f9bcfc",
"record_type": 25,
"teams": {
"communication": {
"type": "OneOnOne"
},
"has_foreign_tenant_users": true,
"team": {
"members": [
{
"id": "user1",
"name": "John Doe"
},
{
"id": "jane.doe@example2.com",
"name": "Jane Doe"
}
]
}
},
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "MicrosoftTeams"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2024-06-10T12:14:57\",\"Id\":\"f47118c3-edcf-43a9-b505-c7c904231ac2\",\"Operation\":\"ChatCreated\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":25,\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"MicrosoftTeams\",\"ClientIP\":\"192.0.2.1\",\"UserId\":\"user1\",\"ChatThreadId\":\"19:0f738a46-74e0-45cf-a5e7-ff31eb2d9cdb_e574a199-c965-4fe2-8c02-0a98a1e8f597@unq.gbl.spaces\",\"CommunicationType\":\"OneOnOne\",\"ExtraProperties\":[{\"Key\":\"TimeZone\",\"Value\":\"Europe/Paris\"},{\"Key\":\"OsName\",\"Value\":\"windows\"},{\"Key\":\"OsVersion\",\"Value\":\"NT 10.0\"},{\"Key\":\"Country\",\"Value\":\"fr\"},{\"Key\":\"ClientName\",\"Value\":\"skypeteams\"},{\"Key\":\"ClientVersion\",\"Value\":\"49/24051622207\"},{\"Key\":\"ClientUtcOffsetSeconds\",\"Value\":\"7200\"}],\"Members\":[{\"OrganizationId\":\"ANONYMIZED\",\"DisplayName\":\"John Doe\",\"UPN\":\"user1\"},{\"OrganizationId\":\"ANONYMIZED\",\"DisplayName\":\"Jane Doe\",\"UPN\":\"jane.doe@example.org\"}],\"ParticipantInfo\":{\"HasForeignTenantUsers\":false,\"HasGuestUsers\":true,\"HasOtherGuestUsers\":false,\"HasUnauthenticatedUsers\":false,\"ParticipatingDomains\":[],\"ParticipatingSIPDomains\":[],\"ParticipatingTenantIds\":[\"ANONYMIZED\"]},\"ResourceTenantId\":\"ANONYMIZED\",\"ItemName\":\"19:0f738a46-74e0-45cf-a5e7-ff31eb2d9cdb_e574a199-c965-4fe2-8c02-0a98a1e8f597@unq.gbl.spaces\"}",
"event": {
"action": "ChatCreated",
"category": [
"network"
],
"code": "25",
"outcome": "success",
"type": [
"info"
]
},
"@timestamp": "2024-06-10T12:14:57Z",
"action": {
"id": 25,
"name": "ChatCreated",
"outcome": "success",
"target": "network-traffic"
},
"office365": {
"record_id": "f47118c3-edcf-43a9-b505-c7c904231ac2",
"record_type": 25,
"teams": {
"communication": {
"type": "OneOnOne"
},
"has_foreign_tenant_users": false,
"team": {
"members": [
{
"id": "user1",
"name": "John Doe"
},
{
"id": "jane.doe@example.org",
"name": "Jane Doe"
}
]
}
},
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"service": {
"name": "MicrosoftTeams"
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2025-01-02T08:01:41\",\"Id\":\"f96dedc3-0e53-4444-bbbb-ef0000000000000\",\"Operation\":\"UserLoggedIn\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":15,\"ResultStatus\":\"Success\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ClientIP\":\"192.0.2.1\",\"ObjectId\":\"0000000a-0000-0000-c000-000000000000\",\"UserId\":\"user1\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"ResultStatusDetail\",\"Value\":\"Redirect\"},{\"Name\":\"UserAgent\",\"Value\":\"Mozilla/5.0 (Linux; Android 14; FFF-N49 Build/Test-N49; wv) AppleWebKit/537.36 (KHTML, like Gecko) Version/4.0 Chrome/131.0.6778.200 Mobile Safari/537.36 PKeyAuth/1.0\"},{\"Name\":\"RequestType\",\"Value\":\"OrgIdWsFederation:federation\"}],\"ModifiedProperties\":[],\"Actor\":[{\"ID\":\"37fc2dfc-cccc-4888-8fff-00000000000000003\",\"Type\":0},{\"ID\":\"user1\",\"Type\":5}],\"ActorContextId\":\"3e49b082-6666-4444-aaaa-8777777777d2\",\"ActorIpAddress\":\"2000:4444:1111:5555:3333:1111:bbbb:555\",\"InterSystemsId\":\"a282e7bb-2eea-4773-b296-00000000000000\",\"IntraSystemId\":\"f96dedc3-0e53-4724-ba85-000000000000800\",\"SupportTicketId\":\"\",\"Target\":[{\"ID\":\"0000000a-0000-0000-c000-000000000000\",\"Type\":0}],\"TargetContextId\":\"ANONYMIZED\",\"ApplicationId\":\"9ba1a5c7-f17a-4de9-a1f1-6178c8d51223\",\"DeviceProperties\":[{\"Name\":\"OS\",\"Value\":\"Android\"},{\"Name\":\"BrowserType\",\"Value\":\"AndroidWebViewLollipopAndAbove\"},{\"Name\":\"SessionId\",\"Value\":\"1584fd84-0508-419e-b678-ac60c80000000000\"}],\"ErrorNumber\":\"0\"}",
"event": {
"action": "UserLoggedIn",
"category": [
"authentication"
],
"code": "15",
"outcome": "success",
"type": [
"start"
]
},
"@timestamp": "2025-01-02T08:01:41Z",
"action": {
"id": 15,
"name": "UserLoggedIn",
"outcome": "success",
"target": "network-traffic"
},
"host": {
"os": {
"full": "Android"
}
},
"office365": {
"audit": {
"object_id": "0000000a-0000-0000-c000-000000000000"
},
"auth": {
"request_type": "OrgIdWsFederation:federation",
"result_status_detail": "Redirect"
},
"context": {
"aad_session_id": "1584fd84-0508-419e-b678-ac60c80000000000",
"client": {
"id": "9ba1a5c7-f17a-4de9-a1f1-6178c8d51223",
"name": "Microsoft Intune Company Portal"
},
"correlation": {
"id": "a282e7bb-2eea-4773-b296-00000000000000"
}
},
"device": {
"browser_type": "AndroidWebViewLollipopAndAbove"
},
"error_number": 0,
"record_id": "f96dedc3-0e53-4444-bbbb-ef0000000000000",
"record_type": 15,
"result_status": "Success",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"user": {
"id": "user1",
"name": "user1"
},
"user_agent": {
"device": {
"name": "FFF-N49"
},
"name": "Chrome Mobile WebView",
"original": "Mozilla/5.0 (Linux; Android 14; FFF-N49 Build/Test-N49; wv) AppleWebKit/537.36 (KHTML, like Gecko) Version/4.0 Chrome/131.0.6778.200 Mobile Safari/537.36 PKeyAuth/1.0",
"os": {
"name": "Android",
"version": "14"
},
"version": "131.0.6778"
}
}
{
"message": "{\"CreationTime\":\"2025-10-15T06:50:14Z\",\"Id\":\"aaaaaaaa-bbbb-4ccc-8ddd-eeeeeeee0001\",\"Operation\":\"AlertTriggered\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":40,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"SecurityComplianceAlerts\",\"UserType\":4,\"Version\":1,\"Workload\":\"SecurityComplianceCenter\",\"ObjectId\":\"aaaaaaaa-bbbb-4ccc-8ddd-eeeeeeee0002\",\"UserId\":\"SecurityComplianceAlerts\",\"AlertId\":\"aaaaaaaa-bbbb-4ccc-8ddd-eeeeeeee0002\",\"AlertLinks\":[{\"AlertLinkHref\":\"https://example.security/alert/0002\"}],\"AlertType\":\"Custom\",\"Category\":\"DataLossPrevention\",\"Comments\":\"New alert\",\"Data\":\"{\\\"ts\\\":\\\"2025-10-15 06:50:08Z\\\",\\\"te\\\":\\\"2025-10-15 06:50:08Z\\\",\\\"an\\\":\\\"Quarantine File\\\",\\\"ad\\\":\\\"File policy 'Quarantine File Policy' was matched by 'document.xlsx'\\\",\\\"f3u\\\":\\\"user1@example.com\\\",\\\"alk\\\":\\\"https://security.example.net/alerts/0002\\\",\\\"plk\\\":\\\"https://example.security/policy/123456\\\",\\\"mat\\\":\\\"MCAS_ALERT_FILE_MATCH\\\"}\",\"Name\":\"Quarantine File\",\"PolicyId\":\"22222222-3333-4444-8555-666666666666\",\"Severity\":\"Medium\",\"Source\":\"Cloud App Security\",\"Status\":\"Active\"}",
"event": {
"action": "AlertTriggered",
"category": [
"intrusion_detection"
],
"code": "40",
"end": "2025-10-15T06:50:08Z",
"kind": "alert",
"outcome": "success",
"reason": "File policy 'Quarantine File Policy' was matched by 'document.xlsx'",
"start": "2025-10-15T06:50:08Z",
"type": [
"info"
],
"url": "https://security.example.net/alerts/0002"
},
"@timestamp": "2025-10-15T06:50:14Z",
"action": {
"id": 40,
"name": "AlertTriggered",
"outcome": "success",
"target": "user"
},
"office365": {
"alert": {
"category": "DataLossPrevention",
"display_name": "Quarantine File",
"id": "aaaaaaaa-bbbb-4ccc-8ddd-eeeeeeee0002",
"severity": "Medium",
"source": "Cloud App Security",
"status": "Active"
},
"audit": {
"object_id": "aaaaaaaa-bbbb-4ccc-8ddd-eeeeeeee0002"
},
"record_id": "aaaaaaaa-bbbb-4ccc-8ddd-eeeeeeee0001",
"record_type": 40,
"result_status": "Succeeded",
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"rule": {
"category": "MCAS_ALERT_FILE_MATCH",
"id": "22222222-3333-4444-8555-666666666666",
"reference": "https://example.security/policy/123456"
},
"service": {
"name": "SecurityComplianceCenter"
},
"user": {
"domain": "example.com",
"email": "user1@example.com",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2023-08-30T20:49:04\",\"Id\":\"f872f447-2417-492a-d462-08dba99a7777\",\"Operation\":\"AtpDetection\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":47,\"UserKey\":\"user1\",\"UserType\":4,\"Version\":1,\"Workload\":\"ThreatIntelligence\",\"UserId\":\"user1\",\"DetectionDate\":\"2023-08-30T20:48:08\",\"DetectionMethod\":\"AntiMalware\",\"EventDeepLink\":\"https://example.com/\",\"FileData\":{\"DocumentId\":\"f773238b-ef02-41f4-94db-bbd7d5167777\",\"FileName\":\"file.exe\",\"FilePath\":\"https://example.com/\",\"FileSize\":\"9670017\",\"FileVerdict\":1,\"MalwareFamily\":\"Malicious Payload\",\"SHA256\":\"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b\"}}",
"event": {
"action": "AtpDetection",
"code": "47",
"outcome": "success",
"url": "https://example.com/"
},
"@timestamp": "2023-08-30T20:49:04Z",
"action": {
"id": 47,
"name": "AtpDetection",
"outcome": "success",
"target": "user"
},
"file": {
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "file.exe"
},
"office365": {
"defender": {
"detection": {
"method": "AntiMalware"
},
"malware_family": "Malicious Payload"
},
"record_id": "f872f447-2417-492a-d462-08dba99a7777",
"record_type": 47,
"user_type": {
"code": 4,
"name": "System"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"hash": [
"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
],
"user": [
"user1"
]
},
"service": {
"name": "ThreatIntelligence"
},
"url": {
"domain": "example.com",
"full": "https://example.com/",
"original": "https://example.com/",
"path": "/",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2019-11-18T13:40:24\",\"Id\":\"038ae875-ffd8-45e4-9dcf-6e385cfad349\",\"Operation\":\"Update group.\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":8,\"ResultStatus\":\"Success\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ClientIP\":\"<null>\",\"ObjectId\":\"Not Available\",\"UserId\":\"user1\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"resultType\",\"Value\":\"Success\"}]}",
"event": {
"action": "Update group",
"category": [
"iam"
],
"code": "8",
"outcome": "success",
"type": [
"change"
]
},
"@timestamp": "2019-11-18T13:40:24Z",
"action": {
"id": 8,
"name": "Update group",
"outcome": "success",
"target": "user"
},
"office365": {
"audit": {
"object_id": "Not Available"
},
"record_id": "038ae875-ffd8-45e4-9dcf-6e385cfad349",
"record_type": 8,
"result_status": "Success",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2019-12-09T14:18:19\",\"Id\":\"359154c4-72c5-4ba0-bbf9-7eb1dff88af7\",\"Operation\":\"Update user.\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":8,\"ResultStatus\":\"Success\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ClientIP\":\"<null>\",\"ObjectId\":\"bob.smith@acme.org\",\"UserId\":\"user1\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"resultType\",\"Value\":\"Success\"},{\"Name\":\"auditEventCategory\",\"Value\":\"UserManagement\"},{\"Name\":\"nCloud\",\"Value\":\"<null>\"}]}",
"event": {
"action": "Update user",
"category": [
"iam"
],
"code": "8",
"outcome": "success",
"type": [
"change"
]
},
"@timestamp": "2019-12-09T14:18:19Z",
"action": {
"id": 8,
"name": "Update user",
"outcome": "success",
"target": "user"
},
"office365": {
"audit": {
"object_id": "bob.smith@acme.org"
},
"record_id": "359154c4-72c5-4ba0-bbf9-7eb1dff88af7",
"record_type": 8,
"result_status": "Success",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"user1"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"user": {
"id": "user1",
"name": "user1"
}
}
{
"message": "{\"CreationTime\":\"2021-03-05T14:43:17\",\"Id\":\"21a107c2-2071-4ce3-8330-cf82f3caa79f\",\"Operation\":\"Update user.\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":8,\"ResultStatus\":\"Success\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ClientIP\":\"\",\"ObjectId\":\"aaaa.bbbb@example.org\",\"UserId\":\"user1\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"additionalDetails\",\"Value\":\"{\\\"UserType\\\":\\\"Member\\\"}\"},{\"Name\":\"extendedAuditEventCategory\",\"Value\":\"User\"}],\"ModifiedProperties\":[{\"Name\":\"LastDirSyncTime\",\"NewValue\":\"[\\r\\n \\\"2021-03-05T14:43:17Z\\\"\\r\\n]\",\"OldValue\":\"[\\r\\n \\\"2021-03-03T12:30:50Z\\\"\\r\\n]\"},{\"Name\":\"Included Updated Properties\",\"NewValue\":\"LastDirSyncTime\",\"OldValue\":\"\"},{\"Name\":\"Action Client Name\",\"NewValue\":\"DirectorySync\",\"OldValue\":\"\"},{\"Name\":\"TargetId.UserType\",\"NewValue\":\"Member\",\"OldValue\":\"\"}],\"Actor\":[{\"ID\":\"user1\",\"Type\":5},{\"ID\":\"10030000A96EA230\",\"Type\":3},{\"ID\":\"User_c96cf894-cca6-438b-b6f2-c2744c1680f5\",\"Type\":2},{\"ID\":\"c96cf894-cca6-438b-b6f2-c2744c1680f5\",\"Type\":2},{\"ID\":\"User\",\"Type\":2}],\"ActorContextId\":\"ANONYMIZED\",\"ActorIpAddress\":\"\",\"InterSystemsId\":\"92d46438-1e67-43e3-91ca-039ff39d7217\",\"IntraSystemId\":\"bd8cc421-efe8-4a44-b61d-44670fc6f56e\",\"SupportTicketId\":\"\",\"Target\":[{\"ID\":\"User_de76d2a9-d8bf-47d4-8f74-2ba2b560f55e\",\"Type\":2},{\"ID\":\"de76d2a9-d8bf-47d4-8f74-2ba2b560f55e\",\"Type\":2},{\"ID\":\"User\",\"Type\":2},{\"ID\":\"aaaa.bbbb@example.org\",\"Type\":5},{\"ID\":\"1003200119762B26\",\"Type\":3}],\"TargetContextId\":\"ANONYMIZED\"}",
"event": {
"action": "Update user",
"category": [
"iam"
],
"code": "8",
"outcome": "success",
"type": [
"change"
]
},
"@timestamp": "2021-03-05T14:43:17Z",
"action": {
"id": 8,
"name": "Update user",
"outcome": "success",
"target": "user"
},
"office365": {
"audit": {
"object_id": "aaaa.bbbb@example.org"
},
"context": {
"correlation": {
"id": "92d46438-1e67-43e3-91ca-039ff39d7217"
},
"modified_properties": [
{
"Name": "LastDirSyncTime",
"NewValue": "[\r\n \"2021-03-05T14:43:17Z\"\r\n]",
"OldValue": "[\r\n \"2021-03-03T12:30:50Z\"\r\n]"
},
{
"Name": "Included Updated Properties",
"NewValue": "LastDirSyncTime",
"OldValue": ""
},
{
"Name": "Action Client Name",
"NewValue": "DirectorySync",
"OldValue": ""
},
{
"Name": "TargetId.UserType",
"NewValue": "Member",
"OldValue": ""
}
]
},
"record_id": "21a107c2-2071-4ce3-8330-cf82f3caa79f",
"record_type": 8,
"result_status": "Success",
"target": {
"upn": "aaaa.bbbb@example.org"
},
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"user": [
"aaaa.bbbb@example.org",
"user1"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"user": {
"id": "user1",
"name": "user1",
"target": {
"name": "aaaa.bbbb@example.org"
}
}
}
{
"message": "{\"CreationTime\":\"2019-11-18T10:15:52\",\"Id\":\"405f795f-8bff-45d2-98c9-ef675d7d2db6\",\"Operation\":\"UserLoggedIn\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":15,\"ResultStatus\":\"Succeeded\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ClientIP\":\"1.2.3.4:8085\",\"ObjectId\":\"5f09333a-842c-47da-a157-57da27fcbca5\",\"UserId\":\"user1\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"UserAgent\",\"Value\":\"Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/64.0.3282.140 Safari/537.36 Edge/18.17763\"},{\"Name\":\"UserAuthenticationMethod\",\"Value\":\"1\"},{\"Name\":\"RequestType\",\"Value\":\"OAuth2:Authorize\"},{\"Name\":\"ResultStatusDetail\",\"Value\":\"Redirect\"},{\"Name\":\"KeepMeSignedIn\",\"Value\":\"True\"}],\"ModifiedProperties\":[],\"Actor\":[{\"ID\":\"3d0e7ff9-261e-440f-a2f8-9e1ec4072f3e\",\"Type\":0},{\"ID\":\"user1\",\"Type\":5},{\"ID\":\"10037FFEA0A22006\",\"Type\":3}],\"ActorContextId\":\"ANONYMIZED\",\"ActorIpAddress\":\"1.2.3.4\",\"InterSystemsId\":\"794c9504-66fe-441c-831a-5fc2badfcdc8\",\"IntraSystemId\":\"99f54f6a-ddfe-4916-b89b-edd9fcac4500\",\"SupportTicketId\":\"\",\"Target\":[{\"ID\":\"5f09333a-842c-47da-a157-57da27fcbca5\",\"Type\":0}],\"TargetContextId\":\"ANONYMIZED\",\"ApplicationId\":\"89bee1f7-5e6e-4d8a-9f3d-ecd601259da7\"}",
"event": {
"action": "UserLoggedIn",
"category": [
"authentication"
],
"code": "15",
"outcome": "success",
"type": [
"start"
]
},
"@timestamp": "2019-11-18T10:15:52Z",
"action": {
"id": 15,
"name": "UserLoggedIn",
"outcome": "success",
"target": "network-traffic"
},
"office365": {
"audit": {
"object_id": "5f09333a-842c-47da-a157-57da27fcbca5"
},
"auth": {
"keep_me_signed_in": true,
"request_type": "OAuth2:Authorize",
"result_status_detail": "Redirect",
"user_authentication_method": 1
},
"context": {
"client": {
"id": "89bee1f7-5e6e-4d8a-9f3d-ecd601259da7"
},
"correlation": {
"id": "794c9504-66fe-441c-831a-5fc2badfcdc8"
}
},
"record_id": "405f795f-8bff-45d2-98c9-ef675d7d2db6",
"record_type": 15,
"result_status": "Succeeded",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 8085
},
"user": {
"id": "user1",
"name": "user1"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Edge",
"original": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/64.0.3282.140 Safari/537.36 Edge/18.17763",
"os": {
"name": "Windows",
"version": "10"
},
"version": "18.17763"
}
}
{
"message": "{\"CreationTime\":\"2023-05-02T18:02:13\",\"Id\":\"5f24aa82-f874-44d1-b6df-857cd9e1decf\",\"Operation\":\"UserLoggedIn\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":15,\"ResultStatus\":\"Success\",\"UserKey\":\"1111111111111111\",\"UserType\":0,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ClientIP\":\"1.2.3.4\",\"ObjectId\":\"77f6d9ce-da8f-46bf-a651-4bec3c189770\",\"UserId\":\"user1\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"ResultStatusDetail\",\"Value\":\"Redirect\"},{\"Name\":\"UserAgent\",\"Value\":\"Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:102.0) Gecko/20100101 Firefox/102.0\"},{\"Name\":\"RequestType\",\"Value\":\"OAuth2:Authorize\"}],\"ModifiedProperties\":[],\"Actor\":[{\"ID\":\"77f6d9ce-da8f-46bf-a651-4bec3c189770\",\"Type\":0},{\"ID\":\"user1\",\"Type\":5}],\"ActorContextId\":\"77f6d9ce-da8f-46bf-a651-4bec3c189770\",\"ActorIpAddress\":\"1.2.3.4\",\"InterSystemsId\":\"77f6d9ce-da8f-46bf-a651-4bec3c189770\",\"IntraSystemId\":\"77f6d9ce-da8f-46bf-a651-4bec3c189770\",\"SupportTicketId\":\"\",\"Target\":[{\"ID\":\"00000003-0000-0ff1-ce00-000000000000\",\"Type\":0}],\"TargetContextId\":\"77f6d9ce-da8f-46bf-a651-4bec3c189770\",\"ApplicationId\":\"77f6d9ce-da8f-46bf-a651-4bec3c189770\",\"DeviceProperties\":[{\"Name\":\"Id\",\"Value\":\"77f6d9ce-da8f-46bf-a651-4bec3c189770\"},{\"Name\":\"DisplayName\",\"Value\":\"example.com\"},{\"Name\":\"OS\",\"Value\":\"Windows 10\"},{\"Name\":\"BrowserType\",\"Value\":\"Firefox\"},{\"Name\":\"IsCompliant\",\"Value\":\"True\"},{\"Name\":\"IsCompliantAndManaged\",\"Value\":\"True\"},{\"Name\":\"TrustType\",\"Value\":\"2\"},{\"Name\":\"SessionId\",\"Value\":\"77f6d9ce-da8f-46bf-a651-4bec3c189770\"}],\"ErrorNumber\":\"0\"}",
"event": {
"action": "UserLoggedIn",
"category": [
"authentication"
],
"code": "15",
"outcome": "success",
"type": [
"start"
]
},
"@timestamp": "2023-05-02T18:02:13Z",
"action": {
"id": 15,
"name": "UserLoggedIn",
"outcome": "success",
"target": "network-traffic"
},
"host": {
"name": "example.com",
"os": {
"full": "Windows 10"
}
},
"office365": {
"audit": {
"object_id": "77f6d9ce-da8f-46bf-a651-4bec3c189770"
},
"auth": {
"request_type": "OAuth2:Authorize",
"result_status_detail": "Redirect"
},
"context": {
"aad_session_id": "77f6d9ce-da8f-46bf-a651-4bec3c189770",
"client": {
"id": "77f6d9ce-da8f-46bf-a651-4bec3c189770"
},
"correlation": {
"id": "77f6d9ce-da8f-46bf-a651-4bec3c189770"
}
},
"device": {
"browser_type": "Firefox",
"id": "77f6d9ce-da8f-46bf-a651-4bec3c189770",
"is_compliant": true,
"is_compliant_and_managed": true,
"trust_type": 2
},
"error_number": 0,
"record_id": "5f24aa82-f874-44d1-b6df-857cd9e1decf",
"record_type": 15,
"result_status": "Success",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"id": "1111111111111111",
"name": "user1"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Firefox",
"original": "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:102.0) Gecko/20100101 Firefox/102.0",
"os": {
"name": "Windows",
"version": "10"
},
"version": "102.0"
}
}
{
"message": "{\"CreationTime\":\"2022-10-14T13:48:03\",\"Id\":\"4af0b443-42dd-4dc6-9bd1-751a55441000\",\"Operation\":\"UserLoginFailed\",\"OrganizationId\":\"ANONYMIZED\",\"RecordType\":15,\"ResultStatus\":\"Success\",\"UserKey\":\"user1\",\"UserType\":0,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ClientIP\":\"192.0.2.1\",\"ObjectId\":\"00000003-0000-0ff1-ce00-000000000000\",\"UserId\":\"user1\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"ResultStatusDetail\",\"Value\":\"Success\"},{\"Name\":\"UserAgent\",\"Value\":\"Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:105.0) Gecko/20100101 Firefox/105.0\"},{\"Name\":\"UserAuthenticationMethod\",\"Value\":\"1\"},{\"Name\":\"RequestType\",\"Value\":\"SAS:EndAuth\"}],\"ModifiedProperties\":[],\"Actor\":[{\"ID\":\"user1\",\"Type\":0},{\"ID\":\"user1\",\"Type\":5}],\"ActorContextId\":\"ANONYMIZED\",\"ActorIpAddress\":\"192.0.2.1\",\"InterSystemsId\":\"d48e6ea0-40c1-5000-5eba-0ee33d13b1ca\",\"IntraSystemId\":\"4af0b443-42dd-4dc6-9bd1-751a55441000\",\"SupportTicketId\":\"\",\"Target\":[{\"ID\":\"00000003-0000-0ff1-ce00-000000000000\",\"Type\":0}],\"TargetContextId\":\"ANONYMIZED\",\"ApplicationId\":\"00000003-0000-0ff1-ce00-000000000000\",\"DeviceProperties\":[{\"Name\":\"OS\",\"Value\":\"Windows 10\"},{\"Name\":\"BrowserType\",\"Value\":\"Firefox\"},{\"Name\":\"IsCompliantAndManaged\",\"Value\":\"False\"},{\"Name\":\"SessionId\",\"Value\":\"b3a9b2b4-57c9-406b-9a2d-106b7f612248\"}],\"ErrorNumber\":\"500121\",\"LogonError\":\"AuthenticationFailedSasError\"}",
"event": {
"action": "UserLoginFailed",
"category": [
"authentication"
],
"code": "15",
"outcome": "failure",
"type": [
"start"
]
},
"@timestamp": "2022-10-14T13:48:03Z",
"action": {
"id": 15,
"name": "UserLoginFailed",
"outcome": "failure",
"target": "network-traffic"
},
"host": {
"os": {
"full": "Windows 10"
}
},
"office365": {
"audit": {
"object_id": "00000003-0000-0ff1-ce00-000000000000"
},
"auth": {
"request_type": "SAS:EndAuth",
"result_status_detail": "Success",
"user_authentication_method": 1
},
"context": {
"aad_session_id": "b3a9b2b4-57c9-406b-9a2d-106b7f612248",
"client": {
"id": "00000003-0000-0ff1-ce00-000000000000"
},
"correlation": {
"id": "d48e6ea0-40c1-5000-5eba-0ee33d13b1ca"
}
},
"device": {
"browser_type": "Firefox",
"is_compliant_and_managed": false
},
"error_number": 500121,
"logon_error": "AuthenticationFailedSasError",
"record_id": "4af0b443-42dd-4dc6-9bd1-751a55441000",
"record_type": 15,
"result_status": "Success",
"user_type": {
"code": 0,
"name": "Regular"
}
},
"organization": {
"id": "ANONYMIZED"
},
"related": {
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"user": {
"id": "user1",
"name": "user1"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Firefox",
"original": "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:105.0) Gecko/20100101 Firefox/105.0",
"os": {
"name": "Windows",
"version": "10"
},
"version": "105.0"
}
}
{
"message": "{\"CreationTime\":\"2026-03-12T11:05:51\",\"Id\":\"11111111-1111-1111-1111-111111111111\",\"Operation\":\"UserLoginFailed\",\"OrganizationId\":\"22222222-2222-2222-2222-222222222222\",\"RecordType\":15,\"ResultStatus\":\"Success\",\"UserKey\":\"00000000-0000-0000-0000-000000000000\",\"UserType\":6,\"Version\":1,\"Workload\":\"AzureActiveDirectory\",\"ClientIP\":\"\",\"ObjectId\":\"44444444-4444-4444-4444-444444444444\",\"UserId\":\"55555555-5555-5555-5555-555555555555||66666666-6666-6666-6666-666666666666\",\"AzureActiveDirectoryEventType\":1,\"ExtendedProperties\":[{\"Name\":\"ResultStatusDetail\",\"Value\":\"Success\"},{\"Name\":\"UserAgent\",\"Value\":\"Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/145.0.0.0 Safari/537.36\"},{\"Name\":\"RequestType\",\"Value\":\"PrivacyConsent:guestconsentset\"}],\"ModifiedProperties\":[],\"Actor\":[{\"ID\":\"Unknown\",\"Type\":2}],\"ActorContextId\":\"77777777-7777-7777-7777-777777777777\",\"ActorIpAddress\":\"\",\"InterSystemsId\":\"88888888-8888-8888-8888-888888888888\",\"IntraSystemId\":\"11111111-1111-1111-1111-111111111111\",\"SupportTicketId\":\"\",\"Target\":[{\"ID\":\"44444444-4444-4444-4444-444444444444\",\"Type\":0}],\"TargetContextId\":\"22222222-2222-2222-2222-222222222222\",\"ApplicationId\":\"44444444-4444-4444-4444-444444444444\",\"ErrorNumber\":\"500142\"}",
"event": {
"action": "UserLoginFailed",
"category": [
"authentication"
],
"code": "15",
"outcome": "failure",
"type": [
"start"
]
},
"@timestamp": "2026-03-12T11:05:51Z",
"action": {
"id": 15,
"name": "UserLoginFailed",
"outcome": "failure",
"target": "network-traffic"
},
"office365": {
"audit": {
"object_id": "44444444-4444-4444-4444-444444444444"
},
"auth": {
"request_type": "PrivacyConsent:guestconsentset",
"result_status_detail": "Success"
},
"context": {
"client": {
"id": "44444444-4444-4444-4444-444444444444"
},
"correlation": {
"id": "88888888-8888-8888-8888-888888888888"
}
},
"error_number": 500142,
"record_id": "11111111-1111-1111-1111-111111111111",
"record_type": 15,
"result_status": "Success",
"user_type": {
"code": 6,
"name": "ServicePrincipal"
}
},
"organization": {
"id": "22222222-2222-2222-2222-222222222222"
},
"related": {
"user": [
"55555555-5555-5555-5555-555555555555||66666666-6666-6666-6666-666666666666"
]
},
"service": {
"name": "AzureActiveDirectory"
},
"user": {
"id": "55555555-5555-5555-5555-555555555555||66666666-6666-6666-6666-666666666666",
"name": "55555555-5555-5555-5555-555555555555||66666666-6666-6666-6666-666666666666"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Chrome",
"original": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/145.0.0.0 Safari/537.36",
"os": {
"name": "Windows",
"version": "10"
},
"version": "145.0.0"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
action.properties |
object |
A list of objects describing the action |
action.target |
keyword |
The target of the action |
azuread.properties.uniqueTokenIdentifier |
keyword |
|
email.attachments |
nested |
List of objects describing the attachments. |
email.cc.address |
keyword |
Email address of CC recipient |
email.delivery_timestamp |
date |
Date and time when message was delivered. |
email.from.address |
keyword |
The sender's email address. |
email.local_id |
keyword |
Unique identifier given by the source. |
email.message_id |
wildcard |
Value from the Message-ID header. |
email.reply_to.address |
keyword |
Address replies should be delivered to. |
email.sender.address |
keyword |
Address of the message sender. |
email.subject |
keyword |
The subject of the email message. |
email.to.address |
keyword |
Email address of recipient |
event.action |
keyword |
The action captured by the event. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.code |
keyword |
Identification code for this event. |
event.end |
date |
event.end contains the date when the event ended or when the activity was last observed. |
event.kind |
keyword |
The kind of the event. The highest categorization field in the hierarchy. |
event.reason |
keyword |
Reason why this event happened, according to the source |
event.start |
date |
event.start contains the date when the event started or when the activity was first observed. |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
event.url |
keyword |
Event investigation URL |
file.directory |
keyword |
Directory where the file is located. |
file.extension |
keyword |
File extension, excluding the leading dot. |
file.hash.md5 |
keyword |
MD5 hash. |
file.hash.sha256 |
keyword |
SHA256 hash. |
file.name |
keyword |
Name of the file including the extension, without the directory. |
file.size |
long |
File size in bytes. |
host.name |
keyword |
Name of the host. |
host.os.full |
keyword |
Operating system name, including the version or code name. |
log.level |
keyword |
Log level of the log event. |
office365.alert.category |
keyword |
|
office365.alert.client_ips |
array |
|
office365.alert.description |
keyword |
|
office365.alert.display_name |
keyword |
|
office365.alert.entity_type |
keyword |
|
office365.alert.id |
keyword |
|
office365.alert.severity |
keyword |
|
office365.alert.source |
keyword |
|
office365.alert.status |
keyword |
|
office365.app |
keyword |
|
office365.application.id |
keyword |
Identifier of the application |
office365.application.name |
keyword |
Name of the application |
office365.audit.event_source |
keyword |
|
office365.audit.item_type |
keyword |
|
office365.audit.object_id |
keyword |
For Exchange admin audit logging, the name of the object that was modified by the cmdlet. For SharePoint activity, the full URL path name of the file or folder accessed by a user. For Azure AD activity, the name of the user account that was modified. |
office365.audit.platform |
keyword |
|
office365.audit.site |
keyword |
|
office365.auth.keep_me_signed_in |
boolean |
User KeepMeSignedIn choice |
office365.auth.request_type |
keyword |
Authentication type |
office365.auth.result_status_detail |
keyword |
Authentication result detail |
office365.auth.user_authentication_method |
long |
User authentication method |
office365.context.aad_session_id |
keyword |
The identifier of an Azure Active Directory session |
office365.context.api_id |
keyword |
The identifier of the API pathway |
office365.context.authentication_type |
keyword |
|
office365.context.client.id |
keyword |
The identifier of Azure Active Directory application |
office365.context.client.name |
keyword |
The name of Azure Active Directory application |
office365.context.correlation.id |
keyword |
The identifier to correlate user's action across Microsoft 365 services |
office365.context.modified_properties |
array |
|
office365.defender.additional_actions |
array |
The additional actions taken on the email |
office365.defender.auth_details |
array |
The authentication checks that are done for the email |
office365.defender.connectors |
keyword |
Identifiers of connectors associated with the email |
office365.defender.detection.method |
keyword |
The method or the technology used for the detection |
office365.defender.detection.technology |
keyword |
The threats and technologies applied on the email |
office365.defender.detection.type |
keyword |
The type of detection |
office365.defender.email.attachments |
array |
The attachements of the email |
office365.defender.email.delivery.action |
keyword |
The original action delivery on the email |
office365.defender.email.delivery.latest_location |
keyword |
The latest location delivery of the email |
office365.defender.email.delivery.original_location |
keyword |
The original location delivery of the email |
office365.defender.email.verdict.confidence |
keyword |
The confidence in the verdict |
office365.defender.email.verdict.reason |
keyword |
The verdict about the messahe |
office365.defender.malware_family |
keyword |
|
office365.defender.system_overrides |
array |
Overrides that are applicable to the email |
office365.device.browser_type |
keyword |
|
office365.device.id |
keyword |
|
office365.device.is_compliant |
boolean |
|
office365.device.is_compliant_and_managed |
boolean |
|
office365.device.is_managed |
boolean |
|
office365.device.trust_type |
long |
|
office365.dn |
keyword |
|
office365.dprm |
keyword |
|
office365.enmd |
keyword |
|
office365.eop |
keyword |
|
office365.error_number |
long |
Error number |
office365.exchange.client_version |
keyword |
|
office365.exchange.email.paths |
array |
|
office365.exchange.email.subjects |
array |
A list of email subjects |
office365.exchange.mailbox_guid |
keyword |
The Exchange GUID of the mailbox that was accessed |
office365.exchange.mailbox_owner.sid |
keyword |
Mailbox owner security identifier (SID) |
office365.exchange.mailbox_owner.upn |
keyword |
Mailbox owner user principal name (UPN) |
office365.exchange.send_as_user.mailbox_guid |
keyword |
The Exchange GUID of the mailbox that was accessed to send email as |
office365.exchange.send_as_user.smtp |
keyword |
SMTP address of the user who is being impersonated |
office365.exchange_admin.parameters |
array |
The parameters that were used with the cmdlet that is identified in the event.action field |
office365.folders.paths |
array |
|
office365.form_name |
keyword |
|
office365.investigation.alert.category |
keyword |
Investigation alert category |
office365.investigation.alert.correlation_key |
keyword |
Investigation alert correlation key |
office365.investigation.alert.is_incident |
boolean |
Investigation alert severity |
office365.investigation.alert.provider.name |
keyword |
Investigation alert provider name |
office365.investigation.alert.provider.status |
keyword |
Investigation alert provider status |
office365.investigation.alert.severity |
keyword |
Investigation alert severity |
office365.investigation.alert.source_type |
keyword |
Investigation alert source type |
office365.investigation.alert.type |
keyword |
Investigation alert type |
office365.investigation.alert.urls |
array |
|
office365.investigation.delivery.action |
keyword |
Investigation delivery action |
office365.investigation.email.sender.domains |
keyword |
The domain of the sender. Might be an array |
office365.investigation.email.sender.ip |
array |
Email sender IP`s |
office365.investigation.email.subjects |
array |
A list of email subjects |
office365.investigation.email.urls |
array |
Email urls |
office365.investigation.emails |
array |
Several infos about emails |
office365.investigation.id |
keyword |
Investigation id |
office365.investigation.name |
keyword |
Investigation name |
office365.investigation.status |
keyword |
Investigation status |
office365.investigation.threats |
array |
A list of threats |
office365.investigation.type |
keyword |
Investigation type |
office365.logon_error |
keyword |
Logon error detailed reason |
office365.machine_name |
keyword |
Machine name |
office365.mip.label_name |
keyword |
The name of the sensitivity label applied to the email message |
office365.ofph |
keyword |
|
office365.operation.properties |
object |
A list of objects describing the operation |
office365.record_id |
keyword |
Unique identifier of an audit record |
office365.record_type |
long |
The type of the operation |
office365.result_status |
keyword |
Indicates whether the action was successful or not |
office365.scope.code |
long |
The origin (saas or on-premise) of the event |
office365.source.application |
keyword |
|
office365.target.displayName |
keyword |
The target identity display name |
office365.target.upn |
keyword |
The target user principal name |
office365.tdmn |
keyword |
|
office365.teams.action |
keyword |
The action taken by an invitee or the channel owner |
office365.teams.channel.id |
keyword |
The identifier of the channel |
office365.teams.channel.name |
keyword |
The name of the channel |
office365.teams.channel.type |
keyword |
The type of the channel |
office365.teams.communication.type |
keyword |
The type of communication |
office365.teams.has_foreign_tenant_users |
boolean |
|
office365.teams.invitee |
keyword |
The identifier of an invitee |
office365.teams.message.id |
keyword |
The identifier of the message |
office365.teams.message.size |
long |
The size of the message in bytes with UTF-16 encoding |
office365.teams.message.urls |
keyword |
A list of urls present in the message |
office365.teams.message.version |
keyword |
The version of the message |
office365.teams.team.id |
keyword |
The identifier of the team |
office365.teams.team.members |
object |
The list of users in a team |
office365.teams.team.name |
keyword |
The name of the team |
office365.tfph |
keyword |
|
office365.user_type.code |
long |
The type of user that performed the operation |
office365.user_type.is_external |
boolean |
Whether user is external |
office365.virus_info |
keyword |
VirusInfo |
office365.virus_vendor |
keyword |
VirusVendor |
organization.id |
keyword |
Unique identifier for the organization. |
process.name |
keyword |
Process name. |
rule.category |
keyword |
Rule category |
rule.id |
keyword |
Rule ID |
rule.name |
keyword |
Rule name |
rule.reference |
keyword |
Rule reference URL |
service.name |
keyword |
Name of the service. |
source.ip |
ip |
IP address of the source. |
source.port |
long |
Port of the source. |
source.user.email |
keyword |
User email address. |
threat.enrichments |
nested |
List of objects containing indicators enriching the event. |
url.full |
wildcard |
Full unparsed URL. |
url.original |
wildcard |
Unmodified original url as seen in the event source. |
user.domain |
keyword |
Name of the directory the user is a member of. |
user.email |
keyword |
User email address. |
user.id |
keyword |
Unique identifier of the user. |
user.name |
keyword |
Short name or login of the user. |
user.target.name |
keyword |
Short name or login of the user. |
user_agent.name |
keyword |
Name of the user agent. |
user_agent.original |
keyword |
Unparsed user_agent string. |
user_agent.version |
keyword |
Version of the user agent. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.
Troubleshooting
The permission set doesn't include the expected permission
If you receive a permission error (HTTP 401) in the log, check if policies were defined in the Data Loss Prevention section in Microsoft Purview. If yes, add the 'ActivityFeed.ReadDlp' permission to your application and grant tenant admin consent for that permission.