Trend Micro Email Security
Overview
Trend Micro Email Security is a robust email protection solution that safeguards against email-borne threats such as phishing, malware, and spam, offering advanced threat detection and content filtering to secure corporate email communications effectively.
- Vendor: Trend Micro
- Supported environment: Cloud
- Detection based on: Telemetry
- Supported application or feature: Email gateway
Configure
How to get an API key
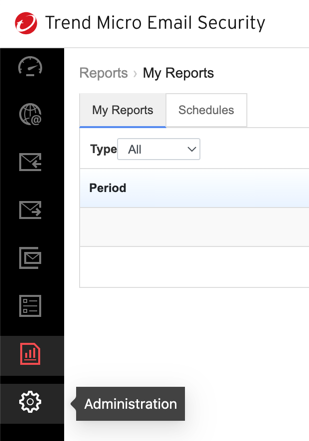
- Log on to the Trend Micro Email Security administrator console.
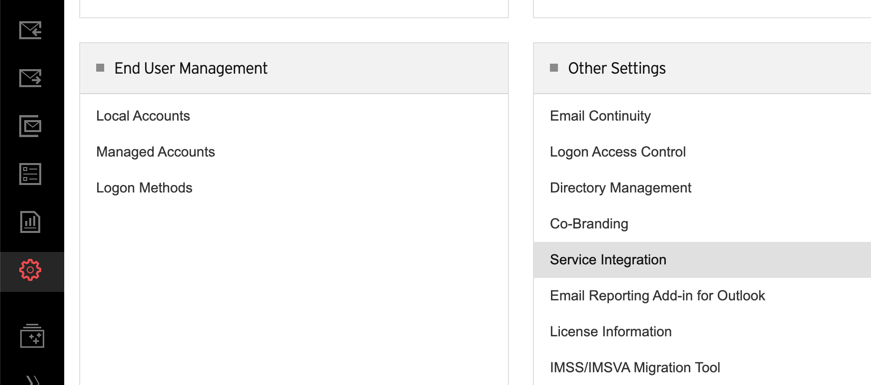
- Go to Administration
- Click on Service Integration. The API Access tab displays by default.
- Click Add to generate an API Key.
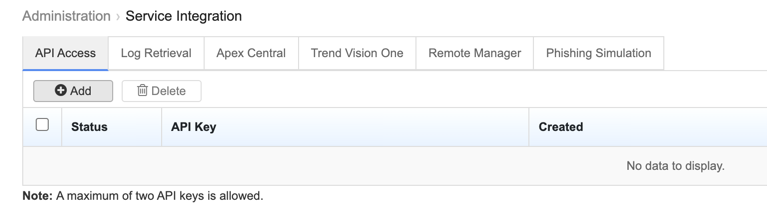
- Copy the API Key value and save the value. Keep the API Key private
Create your intake
- Go to the intake page and create a new intake from the
Trend Micro Email Security. -
Edit the intake configuration using your
Service URL,UsernameandLogin ID. All three are required. -
usernameis yourLogin IDentered during account creating - The value of
service URLvaries according to your location:
| Location | Service URL |
|---|---|
| North America, Latin America and Asia Pacific | api.tmes.trendmicro.com |
| Europe, the Middle East and Africa | api.tmes.trendmicro.eu |
| Australia and New Zealand | api.tmes-anz.trendmicro.com |
| Japan | api.tmems-jp.trendmicro.com |
| Singapore | api.tmes-sg.trendmicro.com |
| India | api.tmes-in.trendmicro.com |
Enjoy your events on the Events page
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
{
"campaignId": "22222222-2222-2222-2222-222222222222",
"classification": "MALWARE",
"clickIP": "1.1.1.1",
"clickTime": "2016-06-24T19:17:44.000Z",
"GUID": "44444444-4444-4444-4444-444444444444",
"id": "8c8b4895-a277-449f-r797-547e3c89b25a",
"messageID": "11111111-1111-1111-1111-111111111111",
"recipient": "bruce.wayne@pharmtech.zz",
"sender": "9facbf452def2d7efc5b5c48cdb837fa@badguy.zz",
"senderIP": "2.2.2.2",
"threatID": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b",
"threatTime": "2016-06-24T19:17:46.000Z",
"threatURL": "https://threatinsight.proofpoint.com/#/33333333-3333-3333-3333-333333333333/threat/u/01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b",
"threatStatus": "active",
"url": "http://badguy.zz/",
"userAgent": "Mozilla/5.0(WindowsNT6.1;WOW64;rv:27.0)Gecko/20100101Firefox/27.0",
"type": "click",
"status": "permitted"
}
{
"spamScore": 0,
"phishScore": 0,
"threatsInfoMap": [
{
"threatID": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b",
"threatStatus": "active",
"classification": "malware",
"detectionType": "COMPROMISED_WEBSITE",
"threatUrl": "https://threatinsight.proofpoint.com/11111111-1111-1111-1111-111111111111/threat/email/01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b",
"threatTime": "2025-04-28T04:27:24.000Z",
"threat": "http://some.threat.com",
"campaignID": null,
"actors": [],
"threatType": "url"
}
],
"messageTime": "2025-04-23T21:05:55.000Z",
"impostorScore": 0.0,
"malwareScore": 0,
"cluster": "example_hosted",
"subject": "TPS reports!",
"quarantineFolder": null,
"quarantineRule": null,
"policyRoutes": [
"default_inbound",
"mydomains_from_hdr"
],
"modulesRun": [
"av",
"dkimv",
"spf",
"spam",
"dmarc",
"pdr",
"urldefense"
],
"messageSize": 3002,
"headerFrom": "Danette <john.doe@example.com>",
"headerReplyTo": null,
"fromAddress": [
"john.doe@example.com"
],
"ccAddresses": [],
"replyToAddress": [],
"toAddresses": [
"jane.doe@example.com"
],
"xmailer": "WPMailSMTP/Mailer/smtp 4.3.0",
"messageParts": [
{
"disposition": "inline",
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b",
"md5": "68b329da9893e34099c7d8ad5cb9c940",
"filename": "text.txt",
"sandboxStatus": null,
"oContentType": "text/plain",
"contentType": "text/plain"
}
],
"completelyRewritten": true,
"id": "22222222-2222-2222-2222-222222222222",
"QID": "0987656",
"GUID": "123456789",
"sender": "111111111111111111111111111111111111@email.example.com",
"recipient": [
"jane.doe@example.com"
],
"senderIP": "1.1.1.1",
"messageID": "<111111111111111111111111111111111111@us-west-2.amazonses.com>",
"status": "delivered",
"type": "message"
}
{
"GUID": "11111111-1111-1111-1111-111111111111",
"status": "delivered",
"type": "message",
"QID": "r2FNwRHF004109",
"ccAddresses": [
"bruce.wayne@university-of-education.zz"
],
"clusterId": "pharmtech_hosted",
"completelyRewritten": "true",
"fromAddress": [
"badguy@evil.zz"
],
"headerCC": "\"Bruce Wayne\" <bruce.wayne@university-of-education.zz>",
"headerFrom": "\"A. Badguy\" <badguy@evil.zz>",
"headerReplyTo": null,
"headerTo": "\"Clark Kent\" <clark.kent@pharmtech.zz>; \"Diana Prince\" <diana.prince@pharmtech.zz>",
"impostorScore": 0,
"malwareScore": 100,
"messageID": "20160624211145.62086.mail@evil.zz",
"messageParts": [
{
"contentType": "text/plain",
"disposition": "inline",
"filename": "text.txt",
"md5": "68b329da9893e34099c7d8ad5cb9c940",
"oContentType": "text/plain",
"sandboxStatus": "unsupported",
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
{
"contentType": "application/pdf",
"disposition": "attached",
"filename": "Invoice for Pharmtech.pdf",
"md5": "68b329da9893e34099c7d8ad5cb9c940",
"oContentType": "application/pdf",
"sandboxStatus": "threat",
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
}
],
"messageTime": "2016-06-24T21:18:38.000Z",
"modulesRun": [
"pdr",
"sandbox",
"spam",
"urldefense"
],
"phishScore": 46,
"policyRoutes": [
"default_inbound",
"executives"
],
"quarantineFolder": "Attachment Defense",
"quarantineRule": "module.sandbox.threat",
"recipient": [
"clark.kent@pharmtech.zz",
"diana.prince@pharmtech.zz"
],
"replyToAddress": null,
"sender": "e99d7ed5580193f36a51f597bc2c0210@evil.zz",
"senderIP": "1.1.1.1",
"spamScore": 4,
"subject": "Please find a totally safe invoice attached.",
"threatsInfoMap": [
{
"campaignId": "22222222-2222-2222-2222-222222222222",
"classification": "MALWARE",
"threat": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b",
"threatId": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b",
"threatStatus": "active",
"threatTime": "2016-06-24T21:18:38.000Z",
"threatType": "ATTACHMENT",
"threatUrl": "https://threatinsight.proofpoint.com/#/33333333-3333-3333-3333-333333333333/threat/u/01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
{
"campaignId": "22222222-2222-2222-2222-222222222222",
"classification": "MALWARE",
"threat": "badsite.zz",
"threatId": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b",
"threatTime": "2016-06-24T21:18:07.000Z",
"threatType": "url",
"threatUrl": "https://threatinsight.proofpoint.com/#/33333333-3333-3333-3333-333333333333/threat/u/01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
}
],
"toAddresses": [
"clark.kent@pharmtech.zz",
"diana.prince@pharmtech.zz"
],
"xmailer": "Spambot v2.5"
}
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
No related built-in rules was found. This message is automatically generated.
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Email gateway |
Trend Micro Email Security generates mail tracking logs. |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | `` |
| Category | email |
| Type | info |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "{\"size\": 8245, \"action\": \"Bounced\", \"mailID\": \"b879ff84-55a3-4813-be99-9e0386a446f7\", \"sender\": \"noreply@example.org\", \"details\": \"mail for example.org loops back to myself\", \"genTime\": \"2023-09-28T13:55:45Z\", \"subject\": \"My subject\", \"tlsInfo\": \"upstreamTLS: TLS 1.2; downstreamTLS: None\", \"headerTo\": [\"jane.doe@example.org\"], \"senderIP\": \"1.2.3.4\", \"direction\": \"out\", \"messageID\": \"<22222222222222222222222222222222222222222222222222222222@EXAMPLE>\", \"recipient\": \"jane.doe@example.org\", \"timestamp\": \"2023-09-28T13:55:33Z\", \"headerFrom\": \"noreply@example.org\", \"deliveredTo\": \"none\", \"deliveryTime\": \"2023-09-28T13:55:33Z\"}",
"event": {
"action": "Bounced",
"category": [
"email"
],
"type": [
"info"
]
},
"@timestamp": "2023-09-28T13:55:33Z",
"email": {
"from": {
"address": "noreply@example.org"
},
"local_id": "b879ff84-55a3-4813-be99-9e0386a446f7",
"message_id": "22222222222222222222222222222222222222222222222222222222@EXAMPLE",
"sender": {
"address": "noreply@example.org"
},
"subject": "My subject",
"to": {
"address": [
"jane.doe@example.org"
]
}
}
}
{
"message": "{\"size\": 2538013, \"action\": \"Delivered\", \"mailID\": \"b879ff84-55a3-4813-be99-9e0386a446f7\", \"sender\": \"john.doe@example.org\", \"details\": \"250 2.0.0 1z3r022fdx-1 Message accepted for delivery\", \"genTime\": \"2023-09-28T13:51:23Z\", \"subject\": \"Automn is coming\", \"tlsInfo\": \"upstreamTLS: TLS 1.2; downstreamTLS: TLS 1.2\", \"headerTo\": [\"jane.doe@example.org\", \"cedric.martin@example.org\"], \"senderIP\": \"1.2.3.4\", \"direction\": \"out\", \"messageID\": \"<11111111111111111111111111111111111111@example.org>\", \"recipient\": \"jane.doe@example.org\", \"timestamp\": \"2023-09-28T13:51:13Z\", \"headerFrom\": \"john.doe@example.org\", \"attachments\": [{\"sha256\": \"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b\", \"fileName\": \"attachment.pdf\"}], \"deliveredTo\": \"antispam.example.org[5.6.7.8]:25\", \"deliveryTime\": \"2023-09-28T13:51:18Z\", \"embeddedUrls\": [\"https://aws.amazon.com\", \"https://cloud.google.com\", \"https://www.azure.com\"]}",
"event": {
"action": "Delivered",
"category": [
"email"
],
"type": [
"info"
]
},
"@timestamp": "2023-09-28T13:51:13Z",
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "attachment.pdf"
}
}
],
"from": {
"address": "john.doe@example.org"
},
"local_id": "b879ff84-55a3-4813-be99-9e0386a446f7",
"message_id": "11111111111111111111111111111111111111@example.org",
"sender": {
"address": "john.doe@example.org"
},
"subject": "Automn is coming",
"to": {
"address": [
"cedric.martin@example.org",
"jane.doe@example.org"
]
}
},
"trendmicro": {
"email": {
"embedded_urls": [
"https://aws.amazon.com",
"https://cloud.google.com",
"https://www.azure.com"
]
}
}
}
{
"message": "{\"genTime\": \"2025-08-20T13:37:22Z\", \"timestamp\": \"2025-08-20T13:37:13Z\", \"deliveryTime\": \"2025-08-20T13:37:16Z\", \"sender\": \"john.doe@example.org\", \"direction\": \"in\", \"messageID\": \"<11111111111111111111111111111111111111@example.org>\", \"subject\": \"Test subject\", \"size\": 41499, \"mailID\": \"663e0c94-1988-4de6-bbbf-a60f015fd7cd\", \"recipient\": \"jane.doe@example.org\", \"action\": \"Delivered\", \"tlsInfo\": \"upstreamTLS: TLS 1.3; downstreamTLS: TLS 1.3\", \"headerFrom\": \"john.doe@example.org\", \"headerTo\": [\"jane.doe@example.org\"], \"senderIP\": \"1.2.3.4\", \"deliveredTo\": \"antispam.example.org[5.6.7.8]:25\", \"attachments\": [{\"fileName\": \"image001.png\", \"sha256\": \"1b4f0e9851971998e732078544c96b36c3d01cedf7caa332359d6f1d83567014\"}, {\"fileName\": \"image_emb_001.png\", \"sha256\": \"60303ae22b998861bce3b28f33eec1be758a213c86c93c076dbe9f558c11c752\"}], \"embeddedUrls\": [\"https://aws.amazon.com\", \"https://cloud.google.com\", \"https://www.azure.com\"], \"details\": \"250 2.6.0 v [InternalId=123456, Hostname=EXAMPLE.PROD.OUTLOOK.COM] 57370 bytes in 0.843, 66.399 KB/sec Queued mail for delivery\"}",
"event": {
"action": "Delivered",
"category": [
"email"
],
"type": [
"info"
]
},
"@timestamp": "2025-08-20T13:37:13Z",
"email": {
"attachments": [
{
"file": {
"hash": {
"sha256": "1b4f0e9851971998e732078544c96b36c3d01cedf7caa332359d6f1d83567014"
},
"name": "image001.png"
}
},
{
"file": {
"hash": {
"sha256": "60303ae22b998861bce3b28f33eec1be758a213c86c93c076dbe9f558c11c752"
},
"name": "image_emb_001.png"
}
}
],
"from": {
"address": "john.doe@example.org"
},
"local_id": "663e0c94-1988-4de6-bbbf-a60f015fd7cd",
"message_id": "11111111111111111111111111111111111111@example.org",
"sender": {
"address": "john.doe@example.org"
},
"subject": "Test subject",
"to": {
"address": [
"jane.doe@example.org"
]
}
},
"trendmicro": {
"email": {
"embedded_urls": [
"https://aws.amazon.com",
"https://cloud.google.com",
"https://www.azure.com"
]
}
}
}
{
"message": "{\"size\": 51149, \"action\": \"Quarantined\", \"mailID\": \"b879ff84-55a3-4813-be99-9e0386a446f7\", \"sender\": \"john.doe@example.org\", \"genTime\": \"2023-09-28T13:47:18Z\", \"subject\": \"My beautiful subject\", \"headerTo\": [\"jane.doe@example.org\"], \"direction\": \"in\", \"messageID\": \"<11111111111111111111111111111111111111111111111111111111111111111@example.org>\", \"recipient\": \"jane.doe@example.org\", \"timestamp\": \"2023-09-28T13:45:59Z\", \"headerFrom\": \"john.doe@example.org\", \"embeddedUrls\": [\"https://sekoia.io\", \"https://www.nytimes.com\"]}",
"event": {
"action": "Quarantined",
"category": [
"email"
],
"type": [
"info"
]
},
"@timestamp": "2023-09-28T13:45:59Z",
"email": {
"from": {
"address": "john.doe@example.org"
},
"local_id": "b879ff84-55a3-4813-be99-9e0386a446f7",
"message_id": "11111111111111111111111111111111111111111111111111111111111111111@example.org",
"sender": {
"address": "john.doe@example.org"
},
"subject": "My beautiful subject",
"to": {
"address": [
"jane.doe@example.org"
]
}
},
"trendmicro": {
"email": {
"embedded_urls": [
"https://sekoia.io",
"https://www.nytimes.com"
]
}
}
}
{
"message": "{\"size\": 48984, \"action\": \"Scanning in sandbox\", \"mailID\": \"b879ff84-55a3-4813-be99-9e0386a446f7\", \"sender\": \"bounce@example.org\", \"genTime\": \"2023-09-28T13:55:53Z\", \"subject\": \"My beautiful subject\", \"tlsInfo\": \"upstreamTLS: TLS 1.3\", \"headerTo\": [\"jane.doe@example.org\"], \"senderIP\": \"1.2.3.4\", \"direction\": \"in\", \"messageID\": \"<11111111111111111111111111111111@example.org>\", \"recipient\": \"jane.doe@example.org\", \"timestamp\": \"2023-09-28T13:55:44Z\", \"headerFrom\": \"john.doe@example.org\", \"embeddedUrls\": [\"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd\", \"https://lemonde.fr\"]}",
"event": {
"action": "Scanning in sandbox",
"category": [
"email"
],
"type": [
"info"
]
},
"@timestamp": "2023-09-28T13:55:44Z",
"email": {
"from": {
"address": "john.doe@example.org"
},
"local_id": "b879ff84-55a3-4813-be99-9e0386a446f7",
"message_id": "11111111111111111111111111111111@example.org",
"sender": {
"address": "bounce@example.org"
},
"subject": "My beautiful subject",
"to": {
"address": [
"jane.doe@example.org"
]
}
},
"trendmicro": {
"email": {
"embedded_urls": [
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd",
"https://lemonde.fr"
]
}
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
email.attachments |
nested |
List of objects describing the attachments. |
email.from.address |
keyword |
The sender's email address. |
email.local_id |
keyword |
Unique identifier given by the source. |
email.message_id |
wildcard |
Value from the Message-ID header. |
email.sender.address |
keyword |
Address of the message sender. |
email.subject |
keyword |
The subject of the email message. |
email.to.address |
keyword |
Email address of recipient |
event.action |
keyword |
The action captured by the event. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
trendmicro.email.embedded_urls |
array |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.