Check Point Harmony Mobile
Overview
Check Point Harmony Mobile is the industry's first unified security solution for users devices and access.
- Vendor: Check Point
- Supported environment: SaaS
- Detection based on: Telemetry, Alert
- Supported application or feature:Network device logs, Network protocol analysis, Web logs
Configure
Create authentication credentials
-
Login to your Check Point Harmony account and navigate to
Profile > Global Settings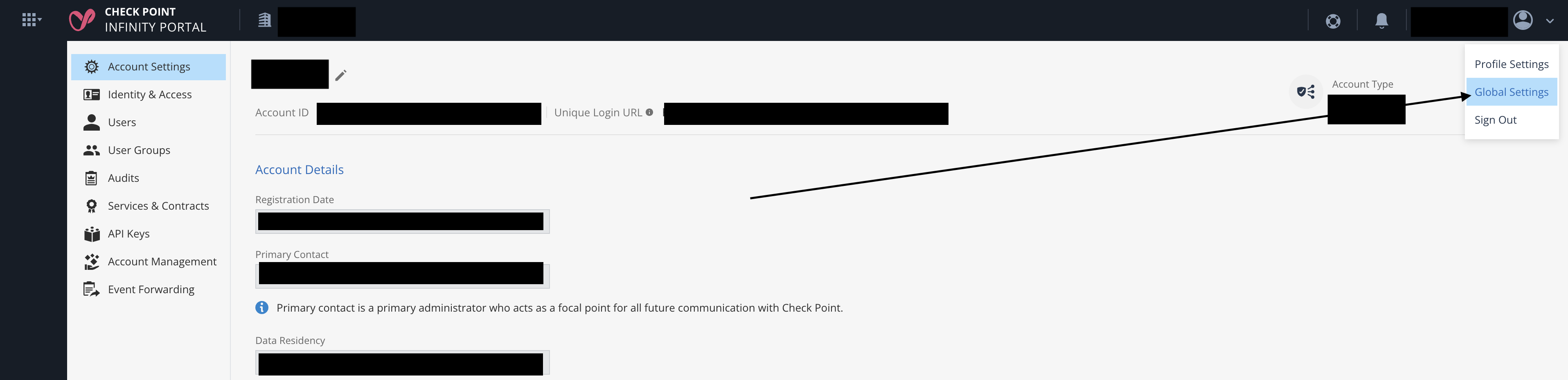
-
Go to
API Keysand click onNew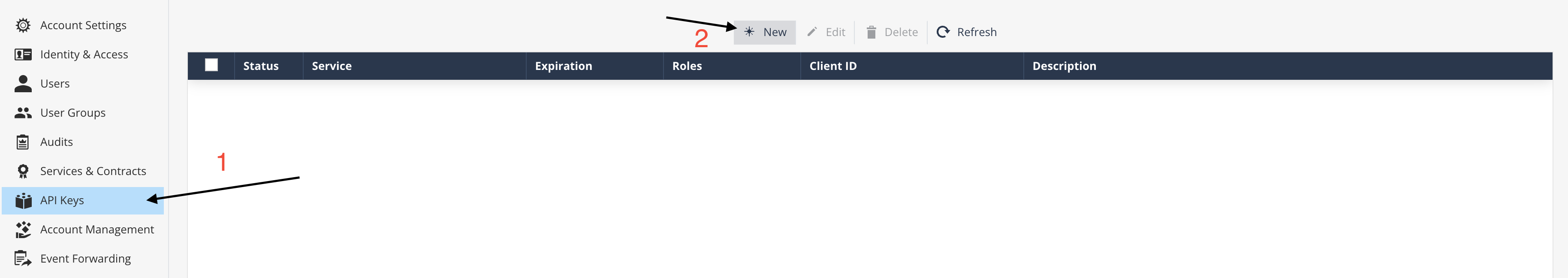
-
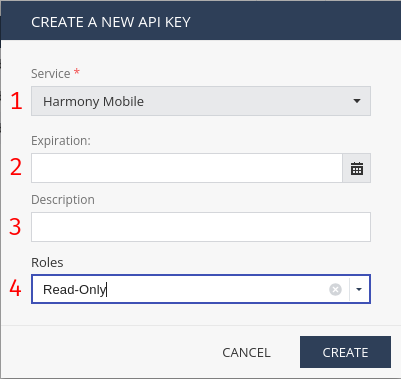
Update required fields with next information and create
API Key:- Service: Harmony Mobile (1)
- Expiration: If you pass an empty field, it means that API Key will not expire until you delete it. (2)
- Description: You can specify any description that you want. (3)
- Roles:
Read-Only
-
Copy values of
Client ID,Secret KeyandAuthentication URLand save them for the configuration of the connector.
Create the intake
- To create the intake, go to the intake page and create a new intake from the format
Check Point Harmony Mobile. - Set up the intake configuration with the Client ID, Client Secret and Authentication URL.
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
{
"attack_vector": "NetworkSecurity",
"backend_last_updated": "02/02/2025 02:22:20",
"details": "Domain:bb[.]caf\u00e9",
"device_id": "2",
"device_rooted": false,
"email": "Blocked",
"event": "Info",
"event_timestamp": "02/22/2023 02:22:20",
"id": 22,
"mdm_uuid": "00000000-0000-0000-0000-0000000000",
"name": "TestDevice",
"number": "+13045555555",
"severity": "Critical",
"threat_factors": "Phishing",
"device_model": "Android",
"client_version": "2.73-SNAPSHOT/2,089"
}
{
"attack_vector": "NetworkSecurity",
"backend_last_updated": "02/02/2025 02:22:20",
"details": "Domain:bb[.]caf\u00e9",
"device_id": "2",
"device_rooted": false,
"email": "Blocked",
"event": "Info",
"id": 22,
"mdm_uuid": "00000000-0000-0000-0000-0000000000",
"name": "TestDevice",
"number": "+13045555555",
"severity": "Critical",
"threat_factors": "Phishing",
"device_model": "Android",
"client_version": "2.73-SNAPSHOT/2,089"
}
{
"attack_vector": "NetworkSecurity",
"details": "Domain:bb[.]caf\u00e9",
"device_id": "2",
"device_rooted": false,
"email": "Blocked",
"event": "Info",
"event_timestamp": "02/22/2023 02:22:20",
"id": 22,
"mdm_uuid": "00000000-0000-0000-0000-0000000000",
"name": "TestDevice",
"number": "+13045555555",
"severity": "Critical",
"threat_factors": "Phishing",
"device_model": "Android",
"client_version": "2.73-SNAPSHOT/2,089"
}
{
"attack_vector": "NetworkSecurity",
"details": "Domain:bb[.]caf\u00e9",
"device_id": "2",
"device_rooted": false,
"email": "Blocked",
"event": "Info",
"id": 22,
"mdm_uuid": "00000000-0000-0000-0000-0000000000",
"name": "TestDevice",
"number": "+13045555555",
"severity": "Critical",
"threat_factors": "Phishing",
"device_model": "Android",
"client_version": "2.73-SNAPSHOT/2,089"
}
{
"attack_vector": "Device",
"backend_last_updated": "2025-10-02T10:53:26+00:00",
"details": "",
"device_id": 8,
"device_rooted": "False",
"email": "john.doe@example.com",
"event": "Compliant",
"event_timestamp": null,
"id": 16,
"mdm_uuid": "00000000-0000-0000-0000-0000000000",
"name": "my Iphone",
"number": "0123 4567890",
"policy_name": "Global",
"severity": "Information",
"threat_factors": "Network Protection (VPN)",
"device_model": "Apple / iPhone 15 Pro",
"client_version": "5.0.1.15281",
"os_version": "26.0.1"
}
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake Check Point Harmony Mobile. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x Check Point Harmony Mobile on ATT&CK Navigator
Check Point Harmony Mobile Application Forbidden
Detects when someone attempts to access/use a forbidden application.
- Effort: master
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Network device logs |
Check Point can record traffic events flowing through their firewall. |
Network protocol analysis |
Check Point firewall does traffic analysis at physical/data/transport layers |
Web logs |
Domain names are extracted from HTTP traffic |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | alert |
| Category | network |
| Type | info |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "{\"attack_vector\":\"NetworkSecurity\",\"backend_last_updated\":\"02/02/2025 02:22:20\",\"details\":\"Domain:bb[.]caf\u00e9\",\"device_id\":\"2\",\"device_rooted\":false,\"email\":\"Blocked\",\"event\":\"Info\",\"event_timestamp\":\"02/22/2023 02:22:20\",\"id\":22,\"mdm_uuid\":\"00000000-0000-0000-0000-0000000000\",\"name\":\"TestDevice\",\"number\":\"+13045555555\",\"severity\":\"Critical\",\"threat_factors\":\"Phishing\",\"device_model\":\"Android\",\"client_version\":\"2.73-SNAPSHOT/2,089\"}",
"event": {
"category": "network",
"kind": "alert",
"reason": "Domain:bb[.]caf\u00e9",
"type": [
"info"
]
},
"@timestamp": "2023-02-22T02:22:20Z",
"checkpoint": {
"harmony": {
"attack_vector": "NetworkSecurity",
"device_name": "TestDevice",
"mdm_uuid": "00000000-0000-0000-0000-0000000000",
"number": "+13045555555",
"threat_factors": "Phishing"
}
},
"device": {
"id": "2",
"model": {
"name": "Android"
}
},
"host": {
"os": {
"type": "Android"
}
},
"log": {
"level": "Critical"
}
}
{
"message": "{\"attack_vector\":\"NetworkSecurity\",\"backend_last_updated\":\"02/02/2025 02:22:20\",\"details\":\"Domain:bb[.]caf\u00e9\",\"device_id\":\"2\",\"device_rooted\":false,\"email\":\"Blocked\",\"event\":\"Info\",\"id\":22,\"mdm_uuid\":\"00000000-0000-0000-0000-0000000000\",\"name\":\"TestDevice\",\"number\":\"+13045555555\",\"severity\":\"Critical\",\"threat_factors\":\"Phishing\",\"device_model\":\"Android\",\"client_version\":\"2.73-SNAPSHOT/2,089\"}",
"event": {
"category": "network",
"kind": "alert",
"reason": "Domain:bb[.]caf\u00e9",
"type": [
"info"
]
},
"@timestamp": "2025-02-02T02:22:20Z",
"checkpoint": {
"harmony": {
"attack_vector": "NetworkSecurity",
"device_name": "TestDevice",
"mdm_uuid": "00000000-0000-0000-0000-0000000000",
"number": "+13045555555",
"threat_factors": "Phishing"
}
},
"device": {
"id": "2",
"model": {
"name": "Android"
}
},
"host": {
"os": {
"type": "Android"
}
},
"log": {
"level": "Critical"
}
}
{
"message": "{\"attack_vector\":\"NetworkSecurity\",\"details\":\"Domain:bb[.]caf\u00e9\",\"device_id\":\"2\",\"device_rooted\":false,\"email\":\"Blocked\",\"event\":\"Info\",\"event_timestamp\":\"02/22/2023 02:22:20\",\"id\":22,\"mdm_uuid\":\"00000000-0000-0000-0000-0000000000\",\"name\":\"TestDevice\",\"number\":\"+13045555555\",\"severity\":\"Critical\",\"threat_factors\":\"Phishing\",\"device_model\":\"Android\",\"client_version\":\"2.73-SNAPSHOT/2,089\"}",
"event": {
"category": "network",
"kind": "alert",
"reason": "Domain:bb[.]caf\u00e9",
"type": [
"info"
]
},
"@timestamp": "2023-02-22T02:22:20Z",
"checkpoint": {
"harmony": {
"attack_vector": "NetworkSecurity",
"device_name": "TestDevice",
"mdm_uuid": "00000000-0000-0000-0000-0000000000",
"number": "+13045555555",
"threat_factors": "Phishing"
}
},
"device": {
"id": "2",
"model": {
"name": "Android"
}
},
"host": {
"os": {
"type": "Android"
}
},
"log": {
"level": "Critical"
}
}
{
"message": "{\"attack_vector\":\"NetworkSecurity\",\"details\":\"Domain:bb[.]caf\u00e9\",\"device_id\":\"2\",\"device_rooted\":false,\"email\":\"Blocked\",\"event\":\"Info\",\"id\":22,\"mdm_uuid\":\"00000000-0000-0000-0000-0000000000\",\"name\":\"TestDevice\",\"number\":\"+13045555555\",\"severity\":\"Critical\",\"threat_factors\":\"Phishing\",\"device_model\":\"Android\",\"client_version\":\"2.73-SNAPSHOT/2,089\"}",
"event": {
"category": "network",
"kind": "alert",
"reason": "Domain:bb[.]caf\u00e9",
"type": [
"info"
]
},
"checkpoint": {
"harmony": {
"attack_vector": "NetworkSecurity",
"device_name": "TestDevice",
"mdm_uuid": "00000000-0000-0000-0000-0000000000",
"number": "+13045555555",
"threat_factors": "Phishing"
}
},
"device": {
"id": "2",
"model": {
"name": "Android"
}
},
"host": {
"os": {
"type": "Android"
}
},
"log": {
"level": "Critical"
}
}
{
"message": "{\"attack_vector\": \"Device\", \"backend_last_updated\": \"2025-10-02T10:53:26+00:00\", \"details\": \"\", \"device_id\": 8, \"device_rooted\": \"False\", \"email\": \"john.doe@example.com\", \"event\": \"Compliant\", \"event_timestamp\": null, \"id\": 16, \"mdm_uuid\": \"00000000-0000-0000-0000-0000000000\", \"name\": \"my Iphone\", \"number\": \"0123 4567890\", \"policy_name\": \"Global\", \"severity\": \"Information\", \"threat_factors\": \"Network Protection (VPN)\", \"device_model\": \"Apple / iPhone 15 Pro\", \"client_version\": \"5.0.1.15281\", \"os_version\": \"26.0.1\"}",
"event": {
"category": "network",
"kind": "alert",
"type": [
"info"
]
},
"@timestamp": "2025-10-02T10:53:26Z",
"checkpoint": {
"harmony": {
"attack_vector": "Device",
"device_name": "my Iphone",
"mdm_uuid": "00000000-0000-0000-0000-0000000000",
"number": "0123 4567890",
"threat_factors": "Network Protection (VPN)"
}
},
"device": {
"id": "8",
"model": {
"name": "Apple / iPhone 15 Pro"
}
},
"host": {
"os": {
"type": "Apple / iPhone 15 Pro"
}
},
"log": {
"level": "Information"
},
"user": {
"email": "john.doe@example.com"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
checkpoint.harmony.attack_vector |
keyword |
Check Point Harmony attack vector |
checkpoint.harmony.device_name |
keyword |
Check Point Harmony device name |
checkpoint.harmony.mdm_uuid |
keyword |
Check Point Harmony MDM uuid |
checkpoint.harmony.number |
keyword |
Check Point Harmony number |
checkpoint.harmony.threat_factors |
keyword |
Check Point Harmony threat factors |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.kind |
keyword |
The kind of the event. The highest categorization field in the hierarchy. |
event.reason |
keyword |
Reason why this event happened, according to the source |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
host.os.type |
keyword |
Which commercial OS family (one of: linux, macos, unix or windows). |
log.level |
keyword |
Log level of the log event. |
user.email |
keyword |
User email address. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.