Sophos EDR
Overview
Sophos EDR monitors, detects and mitigates threats on endpoints. This EDR reduces the attack surface and prevent attacks from running with an anti-exploit, an anti-ransomware and advanced control technology.
This setup guide shows how to forward events produced by Sophos EDR to Sekoia.io.
- Vendor: Sophos
- Supported environment: Cloud
- Detection based on: Telemetry
- Supported application or feature: File monitoring, Process monitoring
Configure
Create SOPHOS EDR Credentials
Warning
If you have a "Partner" or "Organization" entity, you need to do the following procedure on every tenant attached to it. Please find more information on the official documentation
In the Sophos Central Admin console:
- On the left panel, go to
Global Settingsand selectAPI Credentials Management. - Click on
Add Credentialto create a credential dedicated to Sekoia.io. - Give it a name, select the role
Service Principal ReadOnlyand click onAdd. - In the
API credential Summary, copy theClient IDand theClient Secret. It will be used later in Sekoia.io to retrieve the events.
Create the intake
- Go to the Intake page and create a new
Sophos EDRintake. -
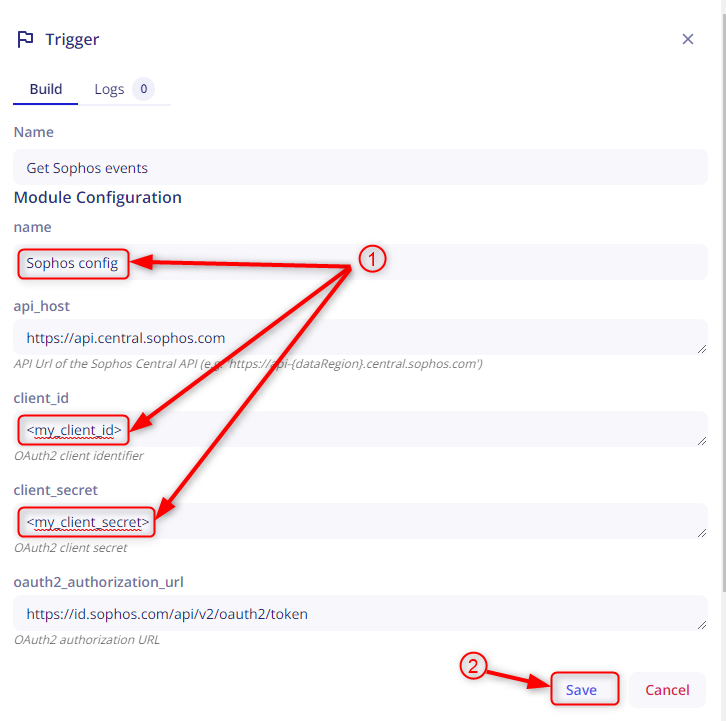
Set the intake account: Write a
nameand paste theclient_idandclient_secretfrom the Sophos console and click onSave.Info
- If you want to change the region with your own region, you can find your region via protect devices field, first click on Protect Devices, Then copy link of any download links and finally Check the region that appears as part of the URL.
- No need to change the Oauth2 Authorization Url for the moment, as this's the only endpoint to get a JWT token
-
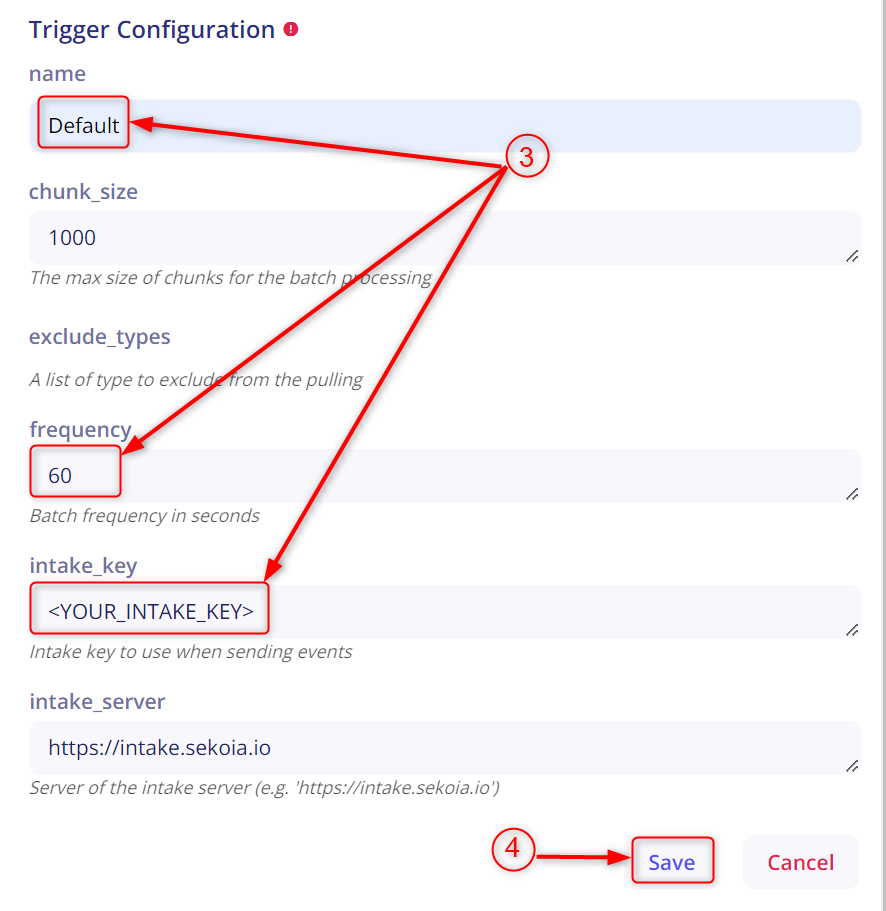
Set the intake configuration, choose a
frequency- Default is60-
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
{
"severity": "low",
"type": "Event::Endpoint::Application::Blocked",
"endpoint_type": "computer",
"endpoint_id": "11111111-1111-1111-1111-111111111111",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "33333333-3333-3333-3333-333333333333",
"name": "Controlled application blocked: Google Software Reporter Tool (Security tool)",
"id": "22222222-2222-2222-2222-222222222222",
"group": "APPLICATION_CONTROL",
"datastream": "event",
"end": "2022-04-25T03:15:31.760Z",
"suser": "n/a",
"rt": "2022-04-25T03:15:31.777Z",
"dhost": "HOSTNAME"
}
{
"severity": "medium",
"type": "Event::Endpoint::Enc::DiskNotEncryptedEvent",
"name": "Device is not encrypted.",
"id": "33333333-3333-3333-3333-333333333333",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "22222222-2222-2222-2222-222222222222",
"endpoint_id": "11111111-1111-1111-1111-111111111111",
"endpoint_type": "computer",
"group": "GROUP",
"datastream": "event",
"end": "2022-04-27T13:23:07.981Z",
"dhost": "HOSTNAME",
"rt": "2022-04-27T13:24:08.662Z",
"duid": "555555555555555555555555",
"suser": "Username2"
}
{
"severity": "low",
"type": "Event::Endpoint::DataLossPreventionAutomaticallyAllowed",
"endpoint_type": "computer",
"endpoint_id": "11111111-1111-1111-1111-111111111111",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "33333333-3333-3333-3333-333333333333",
"name": "An \u2033allow file transfer\u2033 action was taken. Username: DDDDD\\XXXXXXXXXX Rule names: \u2032Multimedia file\u2032 User action: File open Application Name: Firefox (V7 and higher) Data Control action: Allow File type: Media Container (TFT\u2215MPEG-4) File size: 559316722 Source path: C:\\XXXXXXXX\\Downloads\\YYYYYYYYYYYYYYYYY.mp4",
"id": "22222222-2222-2222-2222-222222222222",
"group": "DATA_LOSS_PREVENTION",
"datastream": "event",
"end": "2022-04-25T03:15:31.760Z",
"suser": "n/a",
"rt": "2022-04-25T03:15:31.777Z",
"dhost": "HOSTNAME"
}
{
"severity": "low",
"type": "Event::Endpoint::DataLossPreventionAutomaticallyAllowed",
"endpoint_type": "computer",
"endpoint_id": "11111111-1111-1111-1111-111111111111",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "33333333-3333-3333-3333-333333333333",
"name": "An \u2033allow file transfer\u2033 action was taken. Username: DDDDD\\XXXXXXXXXX Rule names: \u2032Multimedia file\u2032 User action: File open Application Name: Firefox (V7 and higher) Data Control action: Allow File type: Media Container (TFT\u2215MPEG-4) File size: 559316722 Source path: C:\\XXXXXXXX\\Downloads\\YYYYYYYYYYYYYYYYY.mp4 Destination path: D:\\XXXXXXXXXXXXXXX\\Documents\\Videos\\YYYYY.mp4 Destination type: Removable storage",
"id": "22222222-2222-2222-2222-222222222222",
"group": "DATA_LOSS_PREVENTION",
"datastream": "event",
"end": "2022-04-25T03:15:31.760Z",
"suser": "n/a",
"rt": "2022-04-25T03:15:31.777Z",
"dhost": "HOSTNAME"
}
{
"severity": "low",
"type": "Event::Endpoint::Enc::DiskEncryptionInformation",
"name": "Device Encryption information for volume with id: 22222222-2222-2222-2222-222222222222. Message: Encryption has been postponed.",
"id": "33333333-3333-3333-3333-333333333333",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "11111111-1111-1111-1111-111111111111",
"endpoint_id": "44444444-4444-4444-4444-444444444444",
"endpoint_type": "computer",
"group": "DENC",
"datastream": "event",
"end": "2022-04-27T08:48:48.808Z",
"dhost": "HOSTNAME",
"rt": "2022-04-27T08:48:48.809Z",
"duid": "555555555555555555555555",
"suser": "COMPANY\\Username1"
}
{
"severity": "medium",
"type": "Event::Endpoint::Denc::EncryptionSuspendedEvent",
"name": "Device Encryption is suspended",
"id": "11111111-1111-1111-1111-111111111111",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "33333333-3333-3333-3333-333333333333",
"endpoint_id": "22222222-2222-2222-2222-222222222222",
"endpoint_type": "computer",
"group": "DENC",
"datastream": "event",
"end": "2022-04-27T08:47:16.490Z",
"dhost": "HOSTNAME",
"rt": "2022-04-27T08:48:19.320Z",
"duid": "555555555555555555555555",
"suser": "COMPANY\\Username1"
}
{
"severity": "low",
"type": "Event::Endpoint::HmpaExploitPrevented",
"endpoint_type": "computer",
"endpoint_id": "11111111-1111-1111-1111-111111111111",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "33333333-3333-3333-3333-333333333333",
"name": "'CodeCave' exploit prevented in Essential Objects Worker Process",
"id": "22222222-2222-2222-2222-222222222222",
"group": "RUNTIME_DETECTIONS",
"datastream": "event",
"end": "2022-04-25T03:15:31.760Z",
"suser": "n/a",
"rt": "2022-04-25T03:15:31.777Z",
"dhost": "HOSTNAME"
}
{
"severity": "low",
"type": "Event::Endpoint::Enc::Recovery::KeyReceived",
"name": "A BitLocker recovery key has been received from: HOSTNAME.",
"id": "11111111-1111-1111-1111-111111111111",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "22222222-2222-2222-2222-222222222222",
"endpoint_id": "33333333-3333-3333-3333-333333333333",
"endpoint_type": "computer",
"group": "DENC",
"datastream": "event",
"end": "2022-04-27T13:22:08.749Z",
"dhost": "HOSTNAME",
"rt": "2022-04-27T13:22:13.565Z",
"duid": "555555555555555555555555",
"suser": "Username3"
}
{
"severity": "low",
"type": "Event::Endpoint::Denc::OutlookPluginEnabledEvent",
"name": "Outlook add-in is enabled",
"id": "33333333-3333-3333-3333-333333333333",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "22222222-2222-2222-2222-222222222222",
"endpoint_id": "11111111-1111-1111-1111-111111111111",
"endpoint_type": "computer",
"group": "DENC",
"datastream": "event",
"end": "2022-04-27T13:22:06.909Z",
"dhost": "HOSTNAME",
"rt": "2022-04-27T13:22:13.226Z",
"duid": "555555555555555555555555",
"suser": "Username3"
}
{
"severity": "low",
"type": "Event::Endpoint::CorePuaDetection",
"endpoint_type": "computer",
"endpoint_id": "11111111-1111-1111-1111-111111111111",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "33333333-3333-3333-3333-333333333333",
"name": "PUA detected: 'Rule Generic PUA' at 'C:\\XXXXXXXXXX\\AppData\\Local\\Microsoft\\SquirrelTemp\\tempc'",
"id": "22222222-2222-2222-2222-222222222222",
"group": "PUA",
"datastream": "event",
"end": "2022-04-25T03:15:31.760Z",
"suser": "n/a",
"rt": "2022-04-25T03:15:31.777Z",
"dhost": "HOSTNAME"
}
{
"appSha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "33333333-3333-3333-3333-333333333333",
"endpoint_id": "22222222-2222-2222-2222-222222222222",
"endpoint_type": "computer",
"threat": "Generic Reputation PUA",
"origin": "ML",
"type": "Event::Endpoint::CorePuaDetection",
"id": "11111111-1111-1111-1111-111111111111",
"group": "PUA",
"rt": "2023-08-07T21:55:28.843Z",
"severity": "medium",
"duid": "REDACTED",
"end": "2023-08-07T21:55:27.508Z",
"name": "PUA detected: 'Generic Reputation PUA' at 'C:\\John Doe\\Documents\\suspicious.zip'",
"dhost": "HOSTNAME",
"suser": "HOSTNAME\\John Doe"
}
{
"severity": "low",
"type": "Event::Endpoint::Registered",
"name": "New computer registered: HOSTNAME",
"id": "11111111-1111-1111-1111-111111111111",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "22222222-2222-2222-2222-222222222222",
"endpoint_id": "33333333-3333-3333-3333-333333333333",
"endpoint_type": "computer",
"group": "PROTECTION",
"datastream": "event",
"end": "2022-04-27T13:17:10.188Z",
"dhost": "HOSTNAME",
"rt": "2022-04-27T13:17:10.197Z",
"duid": "555555555555555555555555",
"suser": "Username3"
}
{
"severity": "low",
"type": "Event::Endpoint::SavScanComplete",
"name": "Scan 'Sophos Cloud Scheduled Scan' completed",
"id": "11111111-1111-1111-1111-111111111111",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "33333333-3333-3333-3333-333333333333",
"endpoint_id": "22222222-2222-2222-2222-222222222222",
"endpoint_type": "computer",
"group": "PROTECTION",
"datastream": "event",
"end": "2022-04-27T08:59:59.000Z",
"dhost": "HOSTNAME",
"rt": "2022-04-27T09:00:03.548Z",
"duid": "555555555555555555555555",
"suser": "Username2"
}
{
"severity": "low",
"type": "Event::Endpoint::UpdateFailure",
"endpoint_type": "server",
"endpoint_id": "33333333-3333-3333-3333-333333333333",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "22222222-2222-2222-2222-222222222222",
"name": "Download of WindowsCloudServer failed from server http:\u2215\u2215dci.sophosupd.com.",
"id": "11111111-1111-1111-1111-111111111111",
"group": "UPDATING",
"datastream": "event",
"end": "2022-04-25T07:41:03.101Z",
"suser": "n/a",
"rt": "2022-04-25T07:41:03.118Z",
"dhost": "HOSTNAME"
}
{
"severity": "low",
"type": "Event::Endpoint::UpdateRebootRequired",
"endpoint_type": "server",
"endpoint_id": "11111111-1111-1111-1111-111111111111",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "33333333-3333-3333-3333-333333333333",
"name": "Reboot to complete update; computer stays protected in the meantime",
"id": "22222222-2222-2222-2222-222222222222",
"group": "UPDATING",
"datastream": "event",
"end": "2022-04-25T03:15:31.760Z",
"suser": "n/a",
"rt": "2022-04-25T03:15:31.777Z",
"dhost": "HOSTNAME"
}
{
"severity": "low",
"type": "Event::Endpoint::UpdateSuccess",
"endpoint_type": "server",
"endpoint_id": "11111111-1111-1111-1111-111111111111",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "22222222-2222-2222-2222-222222222222",
"name": "Update succeeded",
"id": "33333333-3333-3333-3333-333333333333",
"group": "UPDATING",
"datastream": "event",
"end": "2022-04-25T04:57:09.886Z",
"suser": "n/a",
"rt": "2022-04-25T04:57:09.900Z",
"dhost": "HOSTNAME"
}
{
"severity": "low",
"type": "Event::Endpoint::UserAutoCreated",
"name": "New user added automatically: COMPANY\\Username1",
"id": "22222222-2222-2222-2222-222222222222",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "11111111-1111-1111-1111-111111111111",
"endpoint_id": "11111111-1111-1111-1111-111111111111",
"endpoint_type": "computer",
"group": "PROTECTION",
"datastream": "event",
"end": "2022-04-27T08:48:19.449Z",
"dhost": "HOSTNAME",
"rt": "2022-04-27T08:48:19.456Z",
"duid": "555555555555555555555555",
"suser": "COMPANY\\Username1"
}
{
"severity": "low",
"type": "Event::Endpoint::WebFilteringBlocked",
"endpoint_type": "computer",
"endpoint_id": "33333333-3333-3333-3333-333333333333",
"source_info": {
"ip": "1.1.1.1"
},
"customer_id": "22222222-2222-2222-2222-222222222222",
"name": "Access was blocked to \"www.example.com\" because of \"Rulename\".",
"id": "11111111-1111-1111-1111-111111111111",
"group": "WEB",
"datastream": "event",
"end": "2022-04-25T09:35:54.000Z",
"suser": "Username2",
"rt": "2022-04-25T09:35:55.764Z",
"duid": "555555555555555555555555",
"dhost": "HOSTNAME"
}
{
"endpoint_id": "22222222-2222-2222-2222-222222222222",
"endpoint_type": "computer",
"customer_id": "33333333-3333-3333-3333-333333333333",
"source_info": {
"ip": "1.1.1.1"
},
"id": "33333333-3333-3333-3333-333333333333",
"type": "Event::Endpoint::WebFilteringBlocked",
"group": "WEB",
"duid": "111111111111111111111111",
"rt": "2026-01-30T10:23:51.021Z",
"severity": "low",
"end": "2026-01-30T10:23:42.000Z",
"name": "Access was blocked to \"example.com\" because of \"Mal/JSInject-AC\".",
"dhost": "HOSTNAME",
"suser": "John Doe"
}
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake Sophos EDR. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x Sophos EDR on ATT&CK Navigator
Account Added To A Security Enabled Group
Detection in order to investigate who has added a specific Domain User in Domain Admins or Group Policy Creator Owners (Security event 4728)
- Effort: master
Account Removed From A Security Enabled Group
Detection in order to investigate who has removed a specific Domain User in Domain Admins or Group Policy Creator Owners (Security event 4729)
- Effort: master
CVE-2020-0688 Microsoft Exchange Server Exploit
Detects the exploitation of CVE-2020-0688. The POC exploit a .NET serialization vulnerability in the Exchange Control Panel (ECP) web page. The vulnerability is due to Microsoft Exchange Server not randomizing the keys on a per-installation basis resulting in them using the same validationKey and decryptionKey values. With knowledge of these, values an attacker can craft a special viewstate to use an OS command to be executed by NT_AUTHORITY\SYSTEM using .NET deserialization. To exploit this vulnerability, an attacker needs to leverage the credentials of an account it had already compromised to authenticate to OWA.
- Effort: elementary
CVE-2020-17530 Apache Struts RCE
Detects the exploitation of the Apache Struts RCE vulnerability (CVE-2020-17530).
- Effort: intermediate
CVE-2021-20021 SonicWall Unauthenticated Administrator Access
Detects the exploitation of SonicWall Unauthenticated Admin Access.
- Effort: advanced
CVE-2021-20023 SonicWall Arbitrary File Read
Detects Arbitrary File Read, which can be used with other vulnerabilities as a mean to obtain outputs generated by attackers, or sensitive data.
- Effort: advanced
CVE-2021-22893 Pulse Connect Secure RCE Vulnerability
Detects potential exploitation of the authentication by-pass vulnerability that can allow an unauthenticated user to perform remote arbitrary file execution on the Pulse Connect Secure gateway. It is highly recommended to apply the Pulse Secure mitigations and seach for indicators of compromise on affected servers if you are in doubt over the integrity of your Pulse Connect Secure product.
- Effort: intermediate
Computer Account Deleted
Detects computer account deletion.
- Effort: master
Correlation Admin Files Checked On Network Share
Detects requests to multiple admin files on a network share. This could be an attacker performing reconnaissance steps on the system.
- Effort: advanced
Detect requests to Konni C2 servers
This rule detects requests to Konni C2 servers. These patterns come from an analysis done in 2022, September.
- Effort: elementary
Discord Suspicious Download
Discord is a messaging application. It allows users to create their own communities to share messages and attachments. Those attachments have little to no overview and can be downloaded by almost anyone, which has been abused by attackers to host malicious payloads.
- Effort: advanced
Domain Trust Created Or Removed
A trust was created or removed to a domain. An attacker could perform that in order to do lateral movement easily between domains or shutdown the ability of two domains to communicate.
- Effort: advanced
Koadic MSHTML Command
Detects Koadic payload using MSHTML module
- Effort: intermediate
Linux Shared Lib Injection Via Ldso Preload
Detect ld.so.preload modification for shared lib injection, technique used by attackers to load arbitrary code into process
- Effort: intermediate
Password Change On Directory Service Restore Mode (DSRM) Account
The Directory Service Restore Mode (DSRM) account is a local administrator account on Domain Controllers. Attackers may change the password to gain persistence.
- Effort: intermediate
Possible Malicious File Double Extension
Detects request to potential malicious file with double extension
- Effort: elementary
Possible Replay Attack
This event can be a sign of Kerberos replay attack or, among other things, network device configuration or routing problems.
- Effort: master
Process Trace Alteration
PTrace syscall provides a means by which one process ("tracer") may observe and control the execution of another process ("tracee") and examine and change the tracee's memory and registers. Attacker might want to abuse ptrace functionnality to analyse memory process. It requires to be admin or set ptrace_scope to 0 to allow all user to trace any process.
- Effort: advanced
ProxyShell Microsoft Exchange Suspicious Paths
Detects suspicious calls to Microsoft Exchange resources, in locations related to webshells observed in campaigns using this vulnerability.
- Effort: elementary
Remote Monitoring and Management Software - AnyDesk
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool AnyDesk.
- Effort: master
Remote Monitoring and Management Software - Atera
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool Atera.
- Effort: master
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
Sophos EDR Application Blocked
Sophos EDR detected a potentially malicious application and blocked it.
- Effort: master
Sophos EDR Application Detected
Sophos EDR detected a potentially malicious application.
- Effort: master
Sophos EDR CorePUA Clean
Sophos EDR detected a potentially unwanted application and cleaned it.
- Effort: master
Sophos EDR CorePUA Detection
Sophos EDR detected a potentially unwanted application.
- Effort: master
Suspicious Download Links From Legitimate Services
Detects users clicking on Google docs links to download suspicious files. This technique was used a lot by Bazar Loader in the past.
- Effort: intermediate
Suspicious PROCEXP152.sys File Created In Tmp
Detects the creation of the PROCEXP152.sys file in the application-data local temporary folder. This driver is used by Sysinternals Process Explorer but also by KDU (https://github.com/hfiref0x/KDU) or Ghost-In-The-Logs (https://github.com/bats3c/Ghost-In-The-Logs), which uses KDU. Note - Clever attackers may easily bypass this detection by just renaming the driver filename. Therefore just Medium-level and don't rely on it.
- Effort: advanced
Suspicious TOR Gateway
Detects suspicious TOR gateways. Gateways are often used by the victim to pay and decrypt the encrypted files without installing TOR. Tor intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: advanced
Suspicious URI Used In A Lazarus Campaign
Detects suspicious requests to a specific URI, usually on an .asp page. The website is often compromised.
- Effort: intermediate
User Account Created
Detects user creation on windows servers, which shouldn't happen in an Active Directory environment. Apply this on your windows server logs and not on your DC logs. One default account defaultuser0 is excluded as only used during Windows set-up. This detection use Security Event ID 4720.
- Effort: master
User Account Deleted
Detects local user deletion
- Effort: master
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
File monitoring |
Monitor files and devices activities |
Process monitoring |
Monitor process activities |
Process use of network |
Monitor network activities |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | `` |
| Category | file, iam, network, process |
| Type | info |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::Application::Blocked\",\"endpoint_type\":\"computer\",\"endpoint_id\":\"11111111-1111-1111-1111-111111111111\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"33333333-3333-3333-3333-333333333333\",\"name\":\"Controlled application blocked: Google Software Reporter Tool (Security tool)\",\"id\":\"22222222-2222-2222-2222-222222222222\",\"group\":\"APPLICATION_CONTROL\",\"datastream\":\"event\",\"end\":\"2022-04-25T03:15:31.760Z\",\"suser\":\"n/a\",\"rt\":\"2022-04-25T03:15:31.777Z\",\"dhost\":\"HOSTNAME\"}",
"event": {
"category": [
"file"
],
"code": "Event::Endpoint::Application::Blocked",
"end": "2022-04-25T03:15:31.760000Z",
"reason": "Controlled application blocked: Google Software Reporter Tool (Security tool)",
"type": [
"denied"
]
},
"@timestamp": "2022-04-25T03:15:31.777000Z",
"agent": {
"id": "11111111-1111-1111-1111-111111111111"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"process": {
"title": "Google Software Reporter Tool (Security tool)"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
]
},
"sophos": {
"customer": {
"id": "33333333-3333-3333-3333-333333333333"
},
"endpoint": {
"id": "11111111-1111-1111-1111-111111111111",
"type": "computer"
},
"event": {
"group": "APPLICATION_CONTROL"
}
}
}
{
"message": "{\"severity\":\"medium\",\"type\":\"Event::Endpoint::Enc::DiskNotEncryptedEvent\",\"name\":\"Device is not encrypted.\",\"id\":\"33333333-3333-3333-3333-333333333333\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"22222222-2222-2222-2222-222222222222\",\"endpoint_id\":\"11111111-1111-1111-1111-111111111111\",\"endpoint_type\":\"computer\",\"group\":\"GROUP\",\"datastream\":\"event\",\"end\":\"2022-04-27T13:23:07.981Z\",\"dhost\":\"HOSTNAME\",\"rt\":\"2022-04-27T13:24:08.662Z\",\"duid\":\"555555555555555555555555\",\"suser\":\"Username2\"}",
"event": {
"category": [
"file"
],
"code": "Event::Endpoint::Enc::DiskNotEncryptedEvent",
"end": "2022-04-27T13:23:07.981000Z",
"reason": "Device is not encrypted.",
"type": [
"info"
]
},
"@timestamp": "2022-04-27T13:24:08.662000Z",
"agent": {
"id": "11111111-1111-1111-1111-111111111111"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "medium"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
],
"user": [
"Username2"
]
},
"sophos": {
"customer": {
"id": "22222222-2222-2222-2222-222222222222"
},
"endpoint": {
"id": "11111111-1111-1111-1111-111111111111",
"type": "computer"
},
"event": {
"group": "GROUP"
}
},
"user": {
"id": "555555555555555555555555",
"name": "Username2"
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::DataLossPreventionAutomaticallyAllowed\",\"endpoint_type\":\"computer\",\"endpoint_id\":\"11111111-1111-1111-1111-111111111111\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"33333333-3333-3333-3333-333333333333\",\"name\":\"An \u2033allow file transfer\u2033 action was taken. Username: DDDDD\\\\XXXXXXXXXX Rule names: \u2032Multimedia file\u2032 User action: File open Application Name: Firefox (V7 and higher) Data Control action: Allow File type: Media Container (TFT\u2215MPEG-4) File size: 559316722 Source path: C:\\\\XXXXXXXX\\\\Downloads\\\\YYYYYYYYYYYYYYYYY.mp4\",\"id\":\"22222222-2222-2222-2222-222222222222\",\"group\":\"DATA_LOSS_PREVENTION\",\"datastream\":\"event\",\"end\":\"2022-04-25T03:15:31.760Z\",\"suser\":\"n/a\",\"rt\":\"2022-04-25T03:15:31.777Z\",\"dhost\":\"HOSTNAME\"}",
"event": {
"action": "allow file transfer",
"category": [
"file"
],
"code": "Event::Endpoint::DataLossPreventionAutomaticallyAllowed",
"end": "2022-04-25T03:15:31.760000Z",
"reason": "An \u2033allow file transfer\u2033 action was taken. Username: DDDDD\\XXXXXXXXXX Rule names: \u2032Multimedia file\u2032 User action: File open Application Name: Firefox (V7 and higher) Data Control action: Allow File type: Media Container (TFT\u2215MPEG-4) File size: 559316722 Source path: C:\\XXXXXXXX\\Downloads\\YYYYYYYYYYYYYYYYY.mp4",
"type": [
"allowed"
]
},
"@timestamp": "2022-04-25T03:15:31.777000Z",
"agent": {
"id": "11111111-1111-1111-1111-111111111111"
},
"file": {
"directory": "C:\\XXXXXXXX\\Downloads",
"name": "YYYYYYYYYYYYYYYYY.mp4",
"path": "C:\\XXXXXXXX\\Downloads\\YYYYYYYYYYYYYYYYY.mp4",
"size": 559316722
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
]
},
"rule": {
"name": "Multimedia file"
},
"sophos": {
"customer": {
"id": "33333333-3333-3333-3333-333333333333"
},
"endpoint": {
"id": "11111111-1111-1111-1111-111111111111",
"type": "computer"
},
"event": {
"group": "DATA_LOSS_PREVENTION"
}
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::DataLossPreventionAutomaticallyAllowed\",\"endpoint_type\":\"computer\",\"endpoint_id\":\"11111111-1111-1111-1111-111111111111\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"33333333-3333-3333-3333-333333333333\",\"name\":\"An \u2033allow file transfer\u2033 action was taken. Username: DDDDD\\\\XXXXXXXXXX Rule names: \u2032Multimedia file\u2032 User action: File open Application Name: Firefox (V7 and higher) Data Control action: Allow File type: Media Container (TFT\u2215MPEG-4) File size: 559316722 Source path: C:\\\\XXXXXXXX\\\\Downloads\\\\YYYYYYYYYYYYYYYYY.mp4 Destination path: D:\\\\XXXXXXXXXXXXXXX\\\\Documents\\\\Videos\\\\YYYYY.mp4 Destination type: Removable storage\",\"id\":\"22222222-2222-2222-2222-222222222222\",\"group\":\"DATA_LOSS_PREVENTION\",\"datastream\":\"event\",\"end\":\"2022-04-25T03:15:31.760Z\",\"suser\":\"n/a\",\"rt\":\"2022-04-25T03:15:31.777Z\",\"dhost\":\"HOSTNAME\"}",
"event": {
"action": "allow file transfer",
"category": [
"file"
],
"code": "Event::Endpoint::DataLossPreventionAutomaticallyAllowed",
"end": "2022-04-25T03:15:31.760000Z",
"reason": "An \u2033allow file transfer\u2033 action was taken. Username: DDDDD\\XXXXXXXXXX Rule names: \u2032Multimedia file\u2032 User action: File open Application Name: Firefox (V7 and higher) Data Control action: Allow File type: Media Container (TFT\u2215MPEG-4) File size: 559316722 Source path: C:\\XXXXXXXX\\Downloads\\YYYYYYYYYYYYYYYYY.mp4 Destination path: D:\\XXXXXXXXXXXXXXX\\Documents\\Videos\\YYYYY.mp4 Destination type: Removable storage",
"type": [
"allowed"
]
},
"@timestamp": "2022-04-25T03:15:31.777000Z",
"agent": {
"id": "11111111-1111-1111-1111-111111111111"
},
"file": {
"directory": "C:\\XXXXXXXX\\Downloads",
"name": "YYYYYYYYYYYYYYYYY.mp4",
"path": "C:\\XXXXXXXX\\Downloads\\YYYYYYYYYYYYYYYYY.mp4",
"size": 559316722
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
]
},
"rule": {
"name": "Multimedia file"
},
"sophos": {
"customer": {
"id": "33333333-3333-3333-3333-333333333333"
},
"destination": {
"file": {
"path": "D:\\XXXXXXXXXXXXXXX\\Documents\\Videos\\YYYYY.mp4"
},
"type": "Removable storage"
},
"endpoint": {
"id": "11111111-1111-1111-1111-111111111111",
"type": "computer"
},
"event": {
"group": "DATA_LOSS_PREVENTION"
}
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::Enc::DiskEncryptionInformation\",\"name\":\"Device Encryption information for volume with id: 22222222-2222-2222-2222-222222222222. Message: Encryption has been postponed.\",\"id\":\"33333333-3333-3333-3333-333333333333\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"11111111-1111-1111-1111-111111111111\",\"endpoint_id\":\"44444444-4444-4444-4444-444444444444\",\"endpoint_type\":\"computer\",\"group\":\"DENC\",\"datastream\":\"event\",\"end\":\"2022-04-27T08:48:48.808Z\",\"dhost\":\"HOSTNAME\",\"rt\":\"2022-04-27T08:48:48.809Z\",\"duid\":\"555555555555555555555555\",\"suser\":\"COMPANY\\\\Username1\"}",
"event": {
"category": [
"file",
"process"
],
"code": "Event::Endpoint::Enc::DiskEncryptionInformation",
"end": "2022-04-27T08:48:48.808000Z",
"reason": "Device Encryption information for volume with id: 22222222-2222-2222-2222-222222222222. Message: Encryption has been postponed.",
"type": [
"info"
]
},
"@timestamp": "2022-04-27T08:48:48.809000Z",
"agent": {
"id": "44444444-4444-4444-4444-444444444444"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
],
"user": [
"Username1"
]
},
"sophos": {
"customer": {
"id": "11111111-1111-1111-1111-111111111111"
},
"endpoint": {
"id": "44444444-4444-4444-4444-444444444444",
"type": "computer"
},
"event": {
"group": "DENC"
}
},
"user": {
"domain": "COMPANY",
"id": "555555555555555555555555",
"name": "Username1"
}
}
{
"message": "{\"severity\":\"medium\",\"type\":\"Event::Endpoint::Denc::EncryptionSuspendedEvent\",\"name\":\"Device Encryption is suspended\",\"id\":\"11111111-1111-1111-1111-111111111111\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"33333333-3333-3333-3333-333333333333\",\"endpoint_id\":\"22222222-2222-2222-2222-222222222222\",\"endpoint_type\":\"computer\",\"group\":\"DENC\",\"datastream\":\"event\",\"end\":\"2022-04-27T08:47:16.490Z\",\"dhost\":\"HOSTNAME\",\"rt\":\"2022-04-27T08:48:19.320Z\",\"duid\":\"555555555555555555555555\",\"suser\":\"COMPANY\\\\Username1\"}",
"event": {
"category": [
"file",
"process"
],
"code": "Event::Endpoint::Denc::EncryptionSuspendedEvent",
"end": "2022-04-27T08:47:16.490000Z",
"reason": "Device Encryption is suspended",
"type": [
"info"
]
},
"@timestamp": "2022-04-27T08:48:19.320000Z",
"agent": {
"id": "22222222-2222-2222-2222-222222222222"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "medium"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
],
"user": [
"Username1"
]
},
"sophos": {
"customer": {
"id": "33333333-3333-3333-3333-333333333333"
},
"endpoint": {
"id": "22222222-2222-2222-2222-222222222222",
"type": "computer"
},
"event": {
"group": "DENC"
}
},
"user": {
"domain": "COMPANY",
"id": "555555555555555555555555",
"name": "Username1"
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::HmpaExploitPrevented\",\"endpoint_type\":\"computer\",\"endpoint_id\":\"11111111-1111-1111-1111-111111111111\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"33333333-3333-3333-3333-333333333333\",\"name\":\"'CodeCave' exploit prevented in Essential Objects Worker Process\",\"id\":\"22222222-2222-2222-2222-222222222222\",\"group\":\"RUNTIME_DETECTIONS\",\"datastream\":\"event\",\"end\":\"2022-04-25T03:15:31.760Z\",\"suser\":\"n/a\",\"rt\":\"2022-04-25T03:15:31.777Z\",\"dhost\":\"HOSTNAME\"}",
"event": {
"category": [
"file"
],
"code": "Event::Endpoint::HmpaExploitPrevented",
"end": "2022-04-25T03:15:31.760000Z",
"reason": "'CodeCave' exploit prevented in Essential Objects Worker Process",
"type": [
"info"
]
},
"@timestamp": "2022-04-25T03:15:31.777000Z",
"agent": {
"id": "11111111-1111-1111-1111-111111111111"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
]
},
"sophos": {
"customer": {
"id": "33333333-3333-3333-3333-333333333333"
},
"endpoint": {
"id": "11111111-1111-1111-1111-111111111111",
"type": "computer"
},
"event": {
"group": "RUNTIME_DETECTIONS"
},
"threat": {
"name": "CodeCave"
}
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::Enc::Recovery::KeyReceived\",\"name\":\"A BitLocker recovery key has been received from: HOSTNAME.\",\"id\":\"11111111-1111-1111-1111-111111111111\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"22222222-2222-2222-2222-222222222222\",\"endpoint_id\":\"33333333-3333-3333-3333-333333333333\",\"endpoint_type\":\"computer\",\"group\":\"DENC\",\"datastream\":\"event\",\"end\":\"2022-04-27T13:22:08.749Z\",\"dhost\":\"HOSTNAME\",\"rt\":\"2022-04-27T13:22:13.565Z\",\"duid\":\"555555555555555555555555\",\"suser\":\"Username3\"}",
"event": {
"category": [
"file",
"process"
],
"code": "Event::Endpoint::Enc::Recovery::KeyReceived",
"end": "2022-04-27T13:22:08.749000Z",
"reason": "A BitLocker recovery key has been received from: HOSTNAME.",
"type": [
"info"
]
},
"@timestamp": "2022-04-27T13:22:13.565000Z",
"agent": {
"id": "33333333-3333-3333-3333-333333333333"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
],
"user": [
"Username3"
]
},
"sophos": {
"customer": {
"id": "22222222-2222-2222-2222-222222222222"
},
"endpoint": {
"id": "33333333-3333-3333-3333-333333333333",
"type": "computer"
},
"event": {
"group": "DENC"
}
},
"user": {
"id": "555555555555555555555555",
"name": "Username3"
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::Denc::OutlookPluginEnabledEvent\",\"name\":\"Outlook add-in is enabled\",\"id\":\"33333333-3333-3333-3333-333333333333\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"22222222-2222-2222-2222-222222222222\",\"endpoint_id\":\"11111111-1111-1111-1111-111111111111\",\"endpoint_type\":\"computer\",\"group\":\"DENC\",\"datastream\":\"event\",\"end\":\"2022-04-27T13:22:06.909Z\",\"dhost\":\"HOSTNAME\",\"rt\":\"2022-04-27T13:22:13.226Z\",\"duid\":\"555555555555555555555555\",\"suser\":\"Username3\"}",
"event": {
"category": [
"file",
"process"
],
"code": "Event::Endpoint::Denc::OutlookPluginEnabledEvent",
"end": "2022-04-27T13:22:06.909000Z",
"reason": "Outlook add-in is enabled",
"type": [
"info"
]
},
"@timestamp": "2022-04-27T13:22:13.226000Z",
"agent": {
"id": "11111111-1111-1111-1111-111111111111"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
],
"user": [
"Username3"
]
},
"sophos": {
"customer": {
"id": "22222222-2222-2222-2222-222222222222"
},
"endpoint": {
"id": "11111111-1111-1111-1111-111111111111",
"type": "computer"
},
"event": {
"group": "DENC"
}
},
"user": {
"id": "555555555555555555555555",
"name": "Username3"
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::CorePuaDetection\",\"endpoint_type\":\"computer\",\"endpoint_id\":\"11111111-1111-1111-1111-111111111111\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"33333333-3333-3333-3333-333333333333\",\"name\":\"PUA detected: 'Rule Generic PUA' at 'C:\\\\XXXXXXXXXX\\\\AppData\\\\Local\\\\Microsoft\\\\SquirrelTemp\\\\tempc'\",\"id\":\"22222222-2222-2222-2222-222222222222\",\"group\":\"PUA\",\"datastream\":\"event\",\"end\":\"2022-04-25T03:15:31.760Z\",\"suser\":\"n/a\",\"rt\":\"2022-04-25T03:15:31.777Z\",\"dhost\":\"HOSTNAME\"}",
"event": {
"action": "detected",
"category": [
"file"
],
"code": "Event::Endpoint::CorePuaDetection",
"end": "2022-04-25T03:15:31.760000Z",
"reason": "PUA detected: 'Rule Generic PUA' at 'C:\\XXXXXXXXXX\\AppData\\Local\\Microsoft\\SquirrelTemp\\tempc'",
"type": [
"info"
]
},
"@timestamp": "2022-04-25T03:15:31.777000Z",
"agent": {
"id": "11111111-1111-1111-1111-111111111111"
},
"file": {
"directory": "C:\\XXXXXXXXXX\\AppData\\Local\\Microsoft\\SquirrelTemp",
"name": "tempc",
"path": "C:\\XXXXXXXXXX\\AppData\\Local\\Microsoft\\SquirrelTemp\\tempc"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
]
},
"rule": {
"name": "Rule Generic PUA"
},
"sophos": {
"customer": {
"id": "33333333-3333-3333-3333-333333333333"
},
"endpoint": {
"id": "11111111-1111-1111-1111-111111111111",
"type": "computer"
},
"event": {
"group": "PUA"
}
}
}
{
"message": "{\"appSha256\": \"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b\", \"source_info\": {\"ip\": \"1.1.1.1\"}, \"customer_id\": \"33333333-3333-3333-3333-333333333333\", \"endpoint_id\": \"22222222-2222-2222-2222-222222222222\", \"endpoint_type\": \"computer\", \"threat\": \"Generic Reputation PUA\", \"origin\": \"ML\", \"type\": \"Event::Endpoint::CorePuaDetection\", \"id\": \"11111111-1111-1111-1111-111111111111\", \"group\": \"PUA\", \"rt\": \"2023-08-07T21:55:28.843Z\", \"severity\": \"medium\", \"duid\": \"REDACTED\", \"end\": \"2023-08-07T21:55:27.508Z\", \"name\": \"PUA detected: 'Generic Reputation PUA' at 'C:\\\\John Doe\\\\Documents\\\\suspicious.zip'\", \"dhost\": \"HOSTNAME\", \"suser\": \"HOSTNAME\\\\John Doe\"}",
"event": {
"action": "detected",
"category": [
"file"
],
"code": "Event::Endpoint::CorePuaDetection",
"end": "2023-08-07T21:55:27.508000Z",
"reason": "PUA detected: 'Generic Reputation PUA' at 'C:\\John Doe\\Documents\\suspicious.zip'",
"type": [
"info"
]
},
"@timestamp": "2023-08-07T21:55:28.843000Z",
"agent": {
"id": "22222222-2222-2222-2222-222222222222"
},
"file": {
"directory": "C:\\John Doe\\Documents",
"hash": {
"sha256": "01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
},
"name": "suspicious.zip",
"path": "C:\\John Doe\\Documents\\suspicious.zip"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "medium"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hash": [
"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b"
],
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
],
"user": [
"John Doe"
]
},
"rule": {
"name": "Generic Reputation PUA"
},
"sophos": {
"customer": {
"id": "33333333-3333-3333-3333-333333333333"
},
"endpoint": {
"id": "22222222-2222-2222-2222-222222222222",
"type": "computer"
},
"event": {
"group": "PUA"
}
},
"user": {
"domain": "HOSTNAME",
"id": "REDACTED",
"name": "John Doe"
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::Registered\",\"name\":\"New computer registered: HOSTNAME\",\"id\":\"11111111-1111-1111-1111-111111111111\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"22222222-2222-2222-2222-222222222222\",\"endpoint_id\":\"33333333-3333-3333-3333-333333333333\",\"endpoint_type\":\"computer\",\"group\":\"PROTECTION\",\"datastream\":\"event\",\"end\":\"2022-04-27T13:17:10.188Z\",\"dhost\":\"HOSTNAME\",\"rt\":\"2022-04-27T13:17:10.197Z\",\"duid\":\"555555555555555555555555\",\"suser\":\"Username3\"}",
"event": {
"category": [
"iam"
],
"code": "Event::Endpoint::Registered",
"end": "2022-04-27T13:17:10.188000Z",
"reason": "New computer registered: HOSTNAME",
"type": [
"info"
]
},
"@timestamp": "2022-04-27T13:17:10.197000Z",
"agent": {
"id": "33333333-3333-3333-3333-333333333333"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
],
"user": [
"Username3"
]
},
"sophos": {
"customer": {
"id": "22222222-2222-2222-2222-222222222222"
},
"endpoint": {
"id": "33333333-3333-3333-3333-333333333333",
"type": "computer"
},
"event": {
"group": "PROTECTION"
}
},
"user": {
"id": "555555555555555555555555",
"name": "Username3"
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::SavScanComplete\",\"name\":\"Scan 'Sophos Cloud Scheduled Scan' completed\",\"id\":\"11111111-1111-1111-1111-111111111111\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"33333333-3333-3333-3333-333333333333\",\"endpoint_id\":\"22222222-2222-2222-2222-222222222222\",\"endpoint_type\":\"computer\",\"group\":\"PROTECTION\",\"datastream\":\"event\",\"end\":\"2022-04-27T08:59:59.000Z\",\"dhost\":\"HOSTNAME\",\"rt\":\"2022-04-27T09:00:03.548Z\",\"duid\":\"555555555555555555555555\",\"suser\":\"Username2\"}",
"event": {
"category": [
"iam"
],
"code": "Event::Endpoint::SavScanComplete",
"end": "2022-04-27T08:59:59Z",
"reason": "Scan 'Sophos Cloud Scheduled Scan' completed",
"type": [
"info"
]
},
"@timestamp": "2022-04-27T09:00:03.548000Z",
"agent": {
"id": "22222222-2222-2222-2222-222222222222"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
],
"user": [
"Username2"
]
},
"sophos": {
"customer": {
"id": "33333333-3333-3333-3333-333333333333"
},
"endpoint": {
"id": "22222222-2222-2222-2222-222222222222",
"type": "computer"
},
"event": {
"group": "PROTECTION"
}
},
"user": {
"id": "555555555555555555555555",
"name": "Username2"
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::UpdateFailure\",\"endpoint_type\":\"server\",\"endpoint_id\":\"33333333-3333-3333-3333-333333333333\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"22222222-2222-2222-2222-222222222222\",\"name\":\"Download of WindowsCloudServer failed from server http:\u2215\u2215dci.sophosupd.com.\",\"id\":\"11111111-1111-1111-1111-111111111111\",\"group\":\"UPDATING\",\"datastream\":\"event\",\"end\":\"2022-04-25T07:41:03.101Z\",\"suser\":\"n/a\",\"rt\":\"2022-04-25T07:41:03.118Z\",\"dhost\":\"HOSTNAME\"}",
"event": {
"category": [
"file",
"process"
],
"code": "Event::Endpoint::UpdateFailure",
"end": "2022-04-25T07:41:03.101000Z",
"reason": "Download of WindowsCloudServer failed from server http:\u2215\u2215dci.sophosupd.com.",
"type": [
"info"
]
},
"@timestamp": "2022-04-25T07:41:03.118000Z",
"agent": {
"id": "33333333-3333-3333-3333-333333333333"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
]
},
"sophos": {
"customer": {
"id": "22222222-2222-2222-2222-222222222222"
},
"endpoint": {
"id": "33333333-3333-3333-3333-333333333333",
"type": "server"
},
"event": {
"group": "UPDATING"
}
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::UpdateRebootRequired\",\"endpoint_type\":\"server\",\"endpoint_id\":\"11111111-1111-1111-1111-111111111111\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"33333333-3333-3333-3333-333333333333\",\"name\":\"Reboot to complete update; computer stays protected in the meantime\",\"id\":\"22222222-2222-2222-2222-222222222222\",\"group\":\"UPDATING\",\"datastream\":\"event\",\"end\":\"2022-04-25T03:15:31.760Z\",\"suser\":\"n/a\",\"rt\":\"2022-04-25T03:15:31.777Z\",\"dhost\":\"HOSTNAME\"}",
"event": {
"category": [
"file",
"process"
],
"code": "Event::Endpoint::UpdateRebootRequired",
"end": "2022-04-25T03:15:31.760000Z",
"reason": "Reboot to complete update; computer stays protected in the meantime",
"type": [
"info"
]
},
"@timestamp": "2022-04-25T03:15:31.777000Z",
"agent": {
"id": "11111111-1111-1111-1111-111111111111"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
]
},
"sophos": {
"customer": {
"id": "33333333-3333-3333-3333-333333333333"
},
"endpoint": {
"id": "11111111-1111-1111-1111-111111111111",
"type": "server"
},
"event": {
"group": "UPDATING"
}
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::UpdateSuccess\",\"endpoint_type\":\"server\",\"endpoint_id\":\"11111111-1111-1111-1111-111111111111\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"22222222-2222-2222-2222-222222222222\",\"name\":\"Update succeeded\",\"id\":\"33333333-3333-3333-3333-333333333333\",\"group\":\"UPDATING\",\"datastream\":\"event\",\"end\":\"2022-04-25T04:57:09.886Z\",\"suser\":\"n/a\",\"rt\":\"2022-04-25T04:57:09.900Z\",\"dhost\":\"HOSTNAME\"}",
"event": {
"category": [
"file",
"process"
],
"code": "Event::Endpoint::UpdateSuccess",
"end": "2022-04-25T04:57:09.886000Z",
"reason": "Update succeeded",
"type": [
"info"
]
},
"@timestamp": "2022-04-25T04:57:09.900000Z",
"agent": {
"id": "11111111-1111-1111-1111-111111111111"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
]
},
"sophos": {
"customer": {
"id": "22222222-2222-2222-2222-222222222222"
},
"endpoint": {
"id": "11111111-1111-1111-1111-111111111111",
"type": "server"
},
"event": {
"group": "UPDATING"
}
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::UserAutoCreated\",\"name\":\"New user added automatically: COMPANY\\\\Username1\",\"id\":\"22222222-2222-2222-2222-222222222222\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"11111111-1111-1111-1111-111111111111\",\"endpoint_id\":\"11111111-1111-1111-1111-111111111111\",\"endpoint_type\":\"computer\",\"group\":\"PROTECTION\",\"datastream\":\"event\",\"end\":\"2022-04-27T08:48:19.449Z\",\"dhost\":\"HOSTNAME\",\"rt\":\"2022-04-27T08:48:19.456Z\",\"duid\":\"555555555555555555555555\",\"suser\":\"COMPANY\\\\Username1\"}",
"event": {
"category": [
"iam"
],
"code": "Event::Endpoint::UserAutoCreated",
"end": "2022-04-27T08:48:19.449000Z",
"reason": "New user added automatically: COMPANY\\Username1",
"type": [
"creation"
]
},
"@timestamp": "2022-04-27T08:48:19.456000Z",
"agent": {
"id": "11111111-1111-1111-1111-111111111111"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
],
"user": [
"Username1"
]
},
"sophos": {
"customer": {
"id": "11111111-1111-1111-1111-111111111111"
},
"endpoint": {
"id": "11111111-1111-1111-1111-111111111111",
"type": "computer"
},
"event": {
"group": "PROTECTION"
}
},
"user": {
"domain": "COMPANY",
"id": "555555555555555555555555",
"name": "Username1"
}
}
{
"message": "{\"severity\":\"low\",\"type\":\"Event::Endpoint::WebFilteringBlocked\",\"endpoint_type\":\"computer\",\"endpoint_id\":\"33333333-3333-3333-3333-333333333333\",\"source_info\":{\"ip\":\"1.1.1.1\"},\"customer_id\":\"22222222-2222-2222-2222-222222222222\",\"name\":\"Access was blocked to \\\"www.example.com\\\" because of \\\"Rulename\\\".\",\"id\":\"11111111-1111-1111-1111-111111111111\",\"group\":\"WEB\",\"datastream\":\"event\",\"end\":\"2022-04-25T09:35:54.000Z\",\"suser\":\"Username2\",\"rt\":\"2022-04-25T09:35:55.764Z\",\"duid\":\"555555555555555555555555\",\"dhost\":\"HOSTNAME\"}",
"event": {
"category": [
"network"
],
"code": "Event::Endpoint::WebFilteringBlocked",
"end": "2022-04-25T09:35:54Z",
"reason": "Access was blocked to \"www.example.com\" because of \"Rulename\".",
"type": [
"denied"
]
},
"@timestamp": "2022-04-25T09:35:55.764000Z",
"agent": {
"id": "33333333-3333-3333-3333-333333333333"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
],
"user": [
"Username2"
]
},
"rule": {
"name": "Rulename"
},
"sophos": {
"customer": {
"id": "22222222-2222-2222-2222-222222222222"
},
"endpoint": {
"id": "33333333-3333-3333-3333-333333333333",
"type": "computer"
},
"event": {
"group": "WEB"
}
},
"url": {
"original": "www.example.com",
"path": "www.example.com"
},
"user": {
"id": "555555555555555555555555",
"name": "Username2"
}
}
{
"message": "{\"endpoint_id\": \"22222222-2222-2222-2222-222222222222\", \"endpoint_type\": \"computer\", \"customer_id\": \"33333333-3333-3333-3333-333333333333\", \"source_info\": {\"ip\": \"1.1.1.1\"}, \"id\": \"33333333-3333-3333-3333-333333333333\", \"type\": \"Event::Endpoint::WebFilteringBlocked\", \"group\": \"WEB\", \"duid\": \"111111111111111111111111\", \"rt\": \"2026-01-30T10:23:51.021Z\", \"severity\": \"low\", \"end\": \"2026-01-30T10:23:42.000Z\", \"name\": \"Access was blocked to \\\"example.com\\\" because of \\\"Mal/JSInject-AC\\\".\", \"dhost\": \"HOSTNAME\", \"suser\": \"John Doe\"}",
"event": {
"category": [
"network"
],
"code": "Event::Endpoint::WebFilteringBlocked",
"end": "2026-01-30T10:23:42Z",
"reason": "Access was blocked to \"example.com\" because of \"Mal/JSInject-AC\".",
"type": [
"denied"
]
},
"@timestamp": "2026-01-30T10:23:51.021000Z",
"agent": {
"id": "22222222-2222-2222-2222-222222222222"
},
"host": {
"hostname": "HOSTNAME",
"name": "HOSTNAME"
},
"log": {
"level": "low"
},
"observer": {
"ip": "1.1.1.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.1.1.1"
],
"user": [
"John Doe"
]
},
"rule": {
"name": "Mal/JSInject-AC"
},
"sophos": {
"customer": {
"id": "33333333-3333-3333-3333-333333333333"
},
"endpoint": {
"id": "22222222-2222-2222-2222-222222222222",
"type": "computer"
},
"event": {
"group": "WEB"
}
},
"url": {
"original": "example.com",
"path": "example.com"
},
"user": {
"id": "111111111111111111111111",
"name": "John Doe"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
agent.id |
keyword |
Unique identifier of this agent. |
event.action |
keyword |
The action captured by the event. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.code |
keyword |
Identification code for this event. |
event.end |
date |
event.end contains the date when the event ended or when the activity was last observed. |
event.reason |
keyword |
Reason why this event happened, according to the source |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
file.hash.sha256 |
keyword |
SHA256 hash. |
file.path |
keyword |
Full path to the file, including the file name. |
file.size |
long |
File size in bytes. |
host.hostname |
keyword |
Hostname of the host. |
host.name |
keyword |
Name of the host. |
log.level |
keyword |
Log level of the log event. |
observer.ip |
ip |
IP addresses of the observer. |
process.title |
keyword |
Process title. |
rule.name |
keyword |
Rule name |
sophos.customer.id |
keyword |
The identifier of the customer |
sophos.destination.file.path |
keyword |
The path of a destination transfert |
sophos.destination.type |
keyword |
The type of a destination transfert |
sophos.endpoint.id |
keyword |
The identifier of the endpoint |
sophos.endpoint.type |
keyword |
The type of the endpoint |
sophos.event.group |
keyword |
The family of the event |
sophos.threat.name |
keyword |
The name of the detected threat |
url.original |
wildcard |
Unmodified original url as seen in the event source. |
user.domain |
keyword |
Name of the directory the user is a member of. |
user.id |
keyword |
Unique identifier of the user. |
user.name |
keyword |
Short name or login of the user. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.