Symantec Endpoint Protection
Overview
Symantec Endpoint Protection is a client-server solution that protects laptops, desktops, and servers in your network against malware, risks, and vulnerabilities. This product is supported by Broadcom.
- Vendor: Broadcom
- Supported environment: On Premise
- Version compatibility: 14.3 RU3
- Detection based on: Telemetry, Alert
- Supported application or feature: Endpoint protection and threat detection
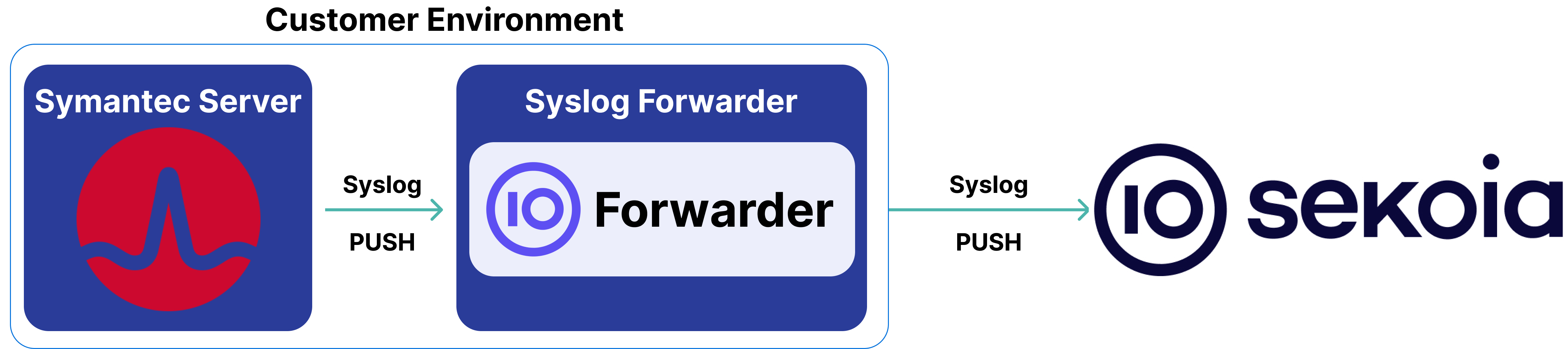
High-Level Architecture Diagram
- Type of integration: Outbound (PUSH to Sekoia.io)
- Schema
Specification
Prerequisites
- Resource:
- Self-managed syslog forwarder
- Network:
- Outbound traffic allowed
- Permissions:
- Administrator or Root access to the Symantec Endpoint Protection Manager or Symantec Endpoint Security
- Root access to the Linux server with the syslog forwarder
Transport Protocol/Method
- Indirect Syslog
Logs details
- Supported functionalities: See section Overview
- Supported type(s) of structure: Plain text
- Supported verbosity level: Alert / Informational
Note
Log levels are based on the taxonomy of RFC5424. Adapt according to the terminology used by the editor.
Step-by-Step Configuration Procedure
Instructions on the 3rd Party Solution
Forward Symantec Endpoint Protection Logs to Sekoia.io
In this guide, you will configure your Symantec Endpoint Protection Manager or your Symantec Endpoint Security to forward events through syslog.
Enable Syslog Forwarding:
- Log on the console of your management server.
- Follow this guide to enable log forwarding.
- Provide the IP address, transport protocol (we recommend TCP), and listening port (514) of the syslog concentrator.
Instruction on Sekoia
Configure Your Intake
This section will guide you through creating the intake object in Sekoia, which provides a unique identifier called the "Intake key." The Intake key is essential for later configuration, as it references the Community, Entity, and Parser (Intake Format) used when receiving raw events on Sekoia.
- Go to the Sekoia Intake page.
- Click on the
+ New Intakebutton at the top right of the page. - Search for your Intake by the product name in the search bar.
- Give it a Name and associate it with an Entity (and a Community if using multi-tenant mode).
- Click on
Create.
Note
For more details on how to use the Intake page and to find the Intake key you just created, refer to this documentation.
Configure a forwarder
To forward events using syslog to Sekoia.io, you need to update the syslog header with the intake key you previously created. Here is an example of your message before the forwarder
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG RAW_MESSAGE
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG [SEKOIA@53288 intake_key=\"YOUR_INTAKE_KEY\"] RAW_MESSAGE
To achieve this you can:
- Use the Sekoia.io forwarder which is the official supported way to collect data using the syslog protocol in Sekoia.io. In charge of centralizing data coming from many equipments/sources and forwarding them to Sekoia.io with the apporpriated format, it is a prepackaged option. You only have to provide your intake key as parameter.
- Use your own Syslog service instance. Maybe you already have an intance of one of these components on your side and want to reuse it in order to centralize data before forwarding them to Sekoia.io. When using this mode, you have to configure and maintain your component in order to respect the expected Sekoia.io format.
Warning
Only the Sekoia.io forwarder is officially supported. Other options are documented for reference purposes but do not have official support.
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
Site: OSTAM,Server Name: STR04,Domain Name: MyDomain,The client has downloaded the content package successfully,STV02,ADMIN,stv02.local
INT23456,,Blocked,C:\Program Files (x86)\Symantec\Symantec Endpoint Protection\14.3.4615.2000.105\Bin64\ccSvcHst.exe,,Begin: 2022-08-29 11:58:20,End Time: 2022-08-29 11:58:20,Rule: ,4428,C:\PROGRAM FILES\SMART-X\CONTROLUPAGENT\VERSION 8.1.5.634\CUAGENT.EXE,0,,C:\Program Files (x86)\Symantec\Symantec Endpoint Protection\14.3.4615.2000.105\Bin64\ccSvcHst.exe,User Name: Admin,Domain Name: ,Action Type: 55,File size (bytes): ,Device ID:
INT23456,1.2.3.4,Continue,Le contrôle des applications et des périphériques est prêt.,Système,Begin: 2022-10-19 06:45:39,End Time: 2022-10-19 06:45:39,Rule: Règle intégrée,0,SysPlant,0,SysPlant,Aucun(e),User Name: Aucun(e),Domain Name: DOMAIN,Action Type: ,File size (bytes): 0,Device ID:
HOSTNAME,1.2.3.4,Continue,Le contrôle des applications et des périphériques est prêt.,Système,Begin: 2022-10-19 06:45:39,End Time: 2022-10-19 06:45:39,Rule: Règle intégrée,0,SysPlant,0,SysPlant,Aucun(e),User Name: Aucun(e),Domain Name: DOMAIN,Action Type: ,File size (bytes): 0,Device ID:
INT23456,Category: 2,LiveUpdate Manager,"Event Description: L’installation d’une mise à jour de Revocation Data a échoué. Erreur : Echec de la correction de contenu (0xE0010005), DuResult: Succès (0).",Event time: 2022-10-18 18:09:26,Group Name: MyDomain\Servers
INT23456,Category: 2,LiveUpdate Manager,"Event Description: L’installation d’une mise à jour de Virus and Spyware Definitions SDS Win64 (Reduced) a échoué. Erreur : Echec de la correction de contenu (0xE0010005), DuResult: Succès (0).",Event time: 2022-10-19 07:32:25,Group Name: MyDomain\Servers
INT23456,Event Description: [SID : 32329] attaque de Audit: Malicious Scan Attempt 2 détectée mais pas bloquée. Chemin d’application : SYSTEM,Event Type: ,Local Host IP: 1.2.3.4,Local Host MAC: 000000000000,Remote Host Name: ,Remote Host IP: 5.6.7.8,Remote Host MAC: 000000000000,Outbound,TCP,,Begin: 2022-10-19 09:25:40,End Time: 2022-10-19 09:25:40,Occurrences: 1,Application: SYSTEM,Location: Par défaut,User Name: none,Domain Name: ,Local Port: 443,Remote Port: 14867,CIDS Signature ID: 32329,CIDS Signature string: Audit: Malicious Scan Attempt 2,CIDS Signature SubID: 68040,Intrusion URL: http://9.8.7.6:443/,Intrusion Payload URL: ,SHA-256: 0000000000000000000000000000000000000000000000000000000000000000,MD-5: ,Intensive Protection Level: N/A,URL Risk: N/A,URL Category: N/A
VPNP02,Event Description: [SID: 32329] Audit: Malicious Scan Attempt 2 attaque détectée mais pas bloquée. Chemin d’application : SYSTEM,Event Type: ,Local Host IP: 1.2.3.4,Local Host MAC: 000000000000,Remote Host Name: ,Remote Host IP: 5.6.7.8,Remote Host MAC: 000000000000,Outbound,TCP,,Begin: 2022-10-19 08:26:56,End Time: 2022-10-19 08:26:56,Occurrences: 1,Application: SYSTEM,Location: Par défaut,User Name: none,Domain Name: ,Local Port: 443,Remote Port: 23203,CIDS Signature ID: 32329,CIDS Signature string: Audit: Malicious Scan Attempt 2,CIDS Signature SubID: 65536,Intrusion URL: http://9.10.11.12:443/,Intrusion Payload URL: ,SHA-256: 0000000000000000000000000000000000000000000000000000000000000000,MD-5: ,Intensive Protection Level: N/A,URL Risk: N/A,URL Category: N/A
Scan ID: 1664847558,Begin: 2022-10-04 17:42:10,End Time: 2022-10-04 17:44:22,Completed,Duration (seconds): 132,User1: Système,User2: Système,Analyse lancée sur lecteurs et dossiers sélectionnés et toutes les extensions.,Analyse Installation standard : Risques : 0 Analysés : 1553 Fichiers/Dossiers/Lecteurs omis : 0 Fichiers approuvés ignorés : 844,Command: Not a command scan (),Threats: 0,Infected: 0,Total files: 1553,Omitted: 0,Computer: DNHFF3453,IP Address: 1.2.3.4,Domain Name: MyDomain,Group Name: MyDomain\Subdivision\Citrix VDI persistants,Server Name: XXXXX01,Scan Type: DefWatch
Scan ID: 1720651832,Begin: 2024-07-11 12:50:07,End Time: ,Started,Duration (seconds): 0,User1: jdoe,User2: ,Scan started on all drives and all extensions.,,Command: Not a command scan (),Threats: 0,Infected: 0,Total files: 0,Omitted: 0,Computer: DNFERO234,IP Address: 1.2.3.4,Domain Name: Par défaut,Group Name: My Domain\Region,Server Name: XXXXX001,Scan Type: Scheduled Scan
SONAR detection now allowed,IP Address: 1.2.3.4,Computer name: DNHFF3453,Source: Auto-Protect scan,Risk name: WS.Reputation.1,Occurrences: 1,File path: c:\program files (x86)\visualxxxxxxxxxx\vtomxvision.exe,Description: ,Actual action: Action invalid,Requested action: Process terminate pending restart,Secondary action: 102,Event time: 2022-07-07 17:01:05,Event Insert Time: 2022-07-07 17:24:14,End Time: 2022-07-07 17:01:05,Last update time: 2022-07-07 17:24:14,Domain Name: MyDomain,Group Name: MyDomain\Subdivision\Citrix VDI persistants,Server Name: XXXXX01,User Name: Doe,Source Computer Name: ,Source Computer IP: ,Disposition: Good,Download site: ,Web domain: ,Downloaded by: c:/windows/explorer.exe,Prevalence: This file has been seen by fewer than 50 Symantec users.,Confidence: There is some evidence that this file is trustworthy.,URL Tracking Status: On,First Seen: Symantec has known about this file approximately 2 days.,Sensitivity: ,Allowed application reason: User allow list,Application hash: E13D72DE479A65E6448C779B3B2BCE45DB7B5AE52B1BAA0FE915380A667D3C01,Hash type: SHA2,Company name: Absyss S.A.S,Application name: Visual TOM,Application version: 6.6.1 (FR),Application type: 127,File size (bytes): 67352,Category set: Malware,Category type: Insight Network Threat,Location: MyDomain,Intensive Protection Level: 0,Certificate issuer: Absyss,Certificate signer: Sectigo RSA Code Signing CA,Certificate thumbprint: D31433F4C8C0BE4846E7E90318CD0CF5046EE95C,Signing timestamp: 1649155201,Certificate serial number: 044541E287C90A879334BFD15D6A3ED3
OND345,Category: 2,REP,Event Description: Impossible d’assigner un jeton d’authentification client. Une erreur de communication générale est survenue.,Event time: 2022-08-29 11:35:29,Group Name: Company\Own
Virus found,IP Address: 1.2.3.4,Computer name: DNHFF3453,Source: Auto-Protect scan,Risk name: EICAR Test String,Occurrences: 1,File path: C:\Users\admin\Desktop\test.txt,Description: AP realtime deferred scanning,Actual action: Cleaned by deletion,Requested action: Cleaned,Secondary action: Quarantined,Event time: 2022-07-07 14:28:39,Event Insert Time: 2022-07-07 14:30:43,End Time: 2022-07-07 14:28:39,Last update time: 2022-07-07 14:30:43,Domain Name: MyDomain,Group Name: MyDomain\Subdivision\Citrix VDI persistants,Server Name: XXXXX01,User Name: ADMIN,Source Computer Name: ,Source Computer IP: ,Disposition: Bad,Download site: ,Web domain: ,Downloaded by: ,Prevalence: This file has been seen by millions of Symantec users.,Confidence: This file is untrustworthy.,URL Tracking Status: On,First Seen: Reputation was not used in this detection.,Sensitivity: ,Allowed application reason: Not on the allow list,Application hash: 275A021BBFB6489E54D471899F7DB9D1663FC695EC2FE2A2C4538AABF651FD0F,Hash type: SHA2,Company name: ,Application name: Nouveau document texte.txt,Application version: ,Application type: 127,File size (bytes): 68,Category set: Malware,Category type: Virus,Location: MyDomain,Intensive Protection Level: 0,Certificate issuer: ,Certificate signer: ,Certificate thumbprint: ,Signing timestamp: ,Certificate serial number:
Virus found,IP Address: 1.2.3.4,Computer name: MyComputer,Source: Auto-Protect scan,Risk name: EICAR Test String,Occurrences: 1,File path: /tmp/eicar.txt,Description: ,Actual action: Quarantined,Requested action: Cleaned,Secondary action: Quarantined,Event time: 2022-10-04 19:10:48,Event Insert Time: 2022-10-04 19:15:22,End Time: 2022-10-04 19:10:48,Last update time: 2022-10-04 19:15:22,Domain Name: Par défaut,Group Name: Mydomain\\Servers\\Linux,Server Name: XXXX01,User Name: user,Source Computer Name: ,Source Computer IP: ,Disposition: Reputation was not used in this detection.,Download site: ,Web domain: ,Downloaded by: ,Prevalence: Reputation was not used in this detection.,Confidence: Reputation was not used in this detection.,URL Tracking Status: N/A,First Seen: Reputation was not used in this detection.,Sensitivity: Low,Allowed application reason: Not on the allow list,Application hash: 131f95c51cc819465fa1797f6ccacf9d494aaaff46fa3eac73ae63ffbdfd8267,Hash type: SHA2,Company name: ,Application name: Unknown,Application version: ,Application type: -1,File size (bytes): 69,Category set: Malware,Category type: Virus,Location: ,Intensive Protection Level: 0,Certificate issuer: ,Certificate signer: ,Certificate thumbprint: ,Signing timestamp: 0,Certificate serial number:
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake Broadcom/Symantec Endpoint Security. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x Broadcom/Symantec Endpoint Security on ATT&CK Navigator
Active Directory Data Export Using Csvde
Detects the use of Csvde, a command-line tool from Windows Server that can be used to export Active Directory data to CSV files. This export doesn't include password hashes, but can be used as a discovery tool to enumerate users, machines and group memberships.
- Effort: elementary
AdFind Usage
Detects the usage of the AdFind tool. AdFind.exe is a free tool that extracts information from Active Directory. Wizard Spider (Bazar, TrickBot, Ryuk), FIN6 and MAZE operators have used AdFind.exe to collect information about Active Directory organizational units and trust objects
- Effort: elementary
Adexplorer Usage
Detects the usage of Adexplorer, a legitimate tool from the Sysinternals suite that could be abused by attackers as it can saves snapshots of the Active Directory Database.
- Effort: advanced
Advanced IP Scanner
Detects the use of Advanced IP Scanner. Seems to be a popular tool for ransomware groups.
- Effort: master
AutoIt3 Execution From Suspicious Folder
Detects AutoIt3 execution from an unusual/suspicious folder. Legitimate folders are "Program Files" and "AppData\Local". AutoIt3.exe is a legitimate process used to execute AutoIt program files, which are used by legitimate software, custom scripts, but also malware. Finding AutoIt3 execution from unusual/suspicious folder can help detect malware activities, such as DarkGate execution. The detection rule can be tailored to your environment and your use of AutoIt3 by filtering out folder's execution of legitimate applications or scripts.
- Effort: advanced
Bloodhound and Sharphound Tools Usage
Detects default process names and default command line parameters used by Bloodhound and Sharphound tools.
- Effort: intermediate
Broadcom/Symantec Endpoint Security Event Blocked
Broadcom/Symantec Endpoint Security blocked an action. Careful when activating this rule, it generates lots of events that are not always relevant for detection.
- Effort: master
Broadcom/Symantec Endpoint Security Event Cleaned
Broadcom/Symantec Endpoint Security had cleaned action. Careful when activating this rule, it generates lots of events that are not always relevant for detection.
- Effort: master
Broadcom/Symantec Endpoint Security Event Quarantined
Broadcom/Symantec Endpoint Security had a quarantined action. Careful when activating this rule, it generates lots of events that are not always relevant for detection.
- Effort: master
Broadcom/Symantec Endpoint Security Event Terminate
Broadcom/Symantec Endpoint Security had a process terminate action. Careful when activating this rule, it generates lots of events that are not always relevant for detection.
- Effort: master
Burp Suite Tool Detected
Burp Suite is a cybersecurity tool. When used as a proxy service, its purpose is to intercept packets and modify them to send them to the server. Burp Collaborator is a network service that Burp Suite uses to help discover many kinds of vulnerabilities (vulnerabilities scanner).
- Effort: intermediate
CVE-2020-0688 Microsoft Exchange Server Exploit
Detects the exploitation of CVE-2020-0688. The POC exploit a .NET serialization vulnerability in the Exchange Control Panel (ECP) web page. The vulnerability is due to Microsoft Exchange Server not randomizing the keys on a per-installation basis resulting in them using the same validationKey and decryptionKey values. With knowledge of these, values an attacker can craft a special viewstate to use an OS command to be executed by NT_AUTHORITY\SYSTEM using .NET deserialization. To exploit this vulnerability, an attacker needs to leverage the credentials of an account it had already compromised to authenticate to OWA.
- Effort: elementary
CVE-2020-17530 Apache Struts RCE
Detects the exploitation of the Apache Struts RCE vulnerability (CVE-2020-17530).
- Effort: intermediate
CVE-2021-20021 SonicWall Unauthenticated Administrator Access
Detects the exploitation of SonicWall Unauthenticated Admin Access.
- Effort: advanced
CVE-2021-20023 SonicWall Arbitrary File Read
Detects Arbitrary File Read, which can be used with other vulnerabilities as a mean to obtain outputs generated by attackers, or sensitive data.
- Effort: advanced
CVE-2021-22893 Pulse Connect Secure RCE Vulnerability
Detects potential exploitation of the authentication by-pass vulnerability that can allow an unauthenticated user to perform remote arbitrary file execution on the Pulse Connect Secure gateway. It is highly recommended to apply the Pulse Secure mitigations and seach for indicators of compromise on affected servers if you are in doubt over the integrity of your Pulse Connect Secure product.
- Effort: intermediate
CVE-2021-4034 Polkit's pkexec
Detection of Polkit's pkexec exploit
- Effort: intermediate
Certificate Authority Modification
Installation of new certificate(s) in the Certificate Authority can be used to trick user when spoofing website or to add trusted destinations.
- Effort: master
Certify Or Certipy
Detects the use of certify and certipy which are two different tools used to enumerate and abuse Active Directory Certificate Services.
- Effort: advanced
Cobalt Strike Default Beacons Names
Detects the default names of Cobalt Strike beacons / payloads.
- Effort: intermediate
Correlation Potential DNS Tunnel
Detects domain name which is longer than 62 characters and requested at least 50 times in a 10 minutes range time. Long domain names are distinctive of DNS tunnels.
- Effort: advanced
Correlation Priv Esc Via Remote Thread
Detect a process that obtains system privilege via a remote thread
- Effort: intermediate
Cryptomining
Detection of domain names potentially related to cryptomining activities.
- Effort: master
DNS Query For Iplookup
Detects dns query of observables tagged as iplookup.
- Effort: master
Detect requests to Konni C2 servers
This rule detects requests to Konni C2 servers. These patterns come from an analysis done in 2022, September.
- Effort: elementary
Disabled Service
Service disabling can be abused by attacker to deny security mecanisms (eg: firewall, EDR, ect) and it is also often used by cryptominer to exploit as much RAM & CPU as possible on infected host. The prerequisites are to enable monitoring of the truncate, rename and unlink syscalls using Auditbeat.
- Effort: advanced
Discord Suspicious Download
Discord is a messaging application. It allows users to create their own communities to share messages and attachments. Those attachments have little to no overview and can be downloaded by almost anyone, which has been abused by attackers to host malicious payloads.
- Effort: advanced
Discovery Commands Correlation
Detects some frequent discovery commands used by some ransomware operators.
- Effort: intermediate
Dynamic DNS Contacted
Detect communication with dynamic dns domain. This kind of domain is often used by attackers. This rule can trigger false positive in non-controlled environment because dynamic dns is not always malicious.
- Effort: master
Enable Root Account With Dsenableroot
Detects when root is enabled. Attackers can use this as a mean of persistence since root is disabled by default.
- Effort: elementary
EvilProxy Phishing Domain
Detects subdomains potentially generated by the EvilProxy adversary-in-the-middle phishing platform. Inspect the other subdomains of the domain to identify the landing page, and determine if the user submitted credentials. This rule has a small percentage of false positives on legitimate domains.
- Effort: intermediate
Exfiltration And Tunneling Tools Execution
Execution of well known tools for data exfiltration and tunneling
- Effort: advanced
Exfiltration Domain
Detects traffic toward a domain flagged as a possible exfiltration vector.
- Effort: master
HackTools Suspicious Names
Quick-win rule to detect the default process names or file names of several HackTools.
- Effort: advanced
Hijack Legit RDP Session To Move Laterally
Identifies suspicious file creations in the startup folder of a remote system. An adversary could abuse this to move laterally by dropping a malicious script or executable that will be executed after a reboot or user logon.
- Effort: intermediate
Internet Scanner
Detects known scanner IP addresses. Alert is only raised when the scan hits an opened port, on TCP or UDP. This could be a very noisy rule, so be careful to check your detection perimeter before activation.
- Effort: master
Internet Scanner Target
Detects known scanner IP addresses. Alert is only raised when the scan hits an opened port, on TCP or UDP and group by target address. This could be a very noisy rule, so be careful to check your detection perimeter before activation.
- Effort: master
Kernel Module Alteration
Kernel module installation can be used to configure system settings to automatically execute a program during system boot or logon to maintain persistence or gain higher-level privileges on compromised systems. The prerequisites are to enable monitoring of the finit_module, init_module, delete_module syscalls using Auditbeat.
- Effort: advanced
Koadic MSHTML Command
Detects Koadic payload using MSHTML module
- Effort: intermediate
Legitimate Process Execution From Unusual Folder
Detects the execution of a legitimate, windows built-in process name from an unusual / suspicious folder. Legitimate folders are c:\windows\system32\, \SystemRoot\system32\, c:\windows\syswow64\ and c:\windows\winsxs. Many malwares/attackers use legitimate names to masquerade but if they are not Administrator yet, they often can't write file into these legitimate folders.
- Effort: advanced
Linux Masquerading Space After Name
This detection rule identifies a process created from an executable with a space appended to the end of the name.
- Effort: intermediate
Network Scanning and Discovery
Tools and command lines used for network discovery from current system
- Effort: advanced
Network Sniffing
List of common tools used for network packages sniffing
- Effort: advanced
Network Sniffing Windows
Network sniffing refers to using the network interface on a system to monitor or capture information sent over a wired or wireless connection. An adversary may place a network interface into promiscuous mode to passively access data in transit over the network, or use span ports to capture a larger amount of data.
- Effort: intermediate
NlTest Usage
Detects attempts to gather information on domain trust relationships that may be used to identify lateral movement opportunities. These command lines were observed in numerous attacks, but also sometimes from legitimate administrators for debugging purposes. The rule does not cover very basics commands but rather the ones that are interesting for attackers to gather information on a domain.
- Effort: advanced
OneNote Suspicious Children Process
In January 2023, a peak of attacks using .one files was observed in the wild. This rule tries to detect the effect of such attempts using this technique.
- Effort: advanced
PasswordDump SecurityXploded Tool
Detects the execution of the PasswordDump SecurityXploded Tool
- Effort: elementary
Phorpiex Process Masquerading
Detects specific process executable path used by the Phorpiex botnet to masquerade its system process network activity. It looks for a pattern of a system process executable name that is not legitimate and running from a folder that is created via a random algorithm 13-15 numbers long.
- Effort: elementary
Possible Malicious File Double Extension
Detects request to potential malicious file with double extension
- Effort: elementary
Potential DNS Tunnel
Detects domain name which is longer than 62 characters. Long domain names are distinctive of DNS tunnels.
- Effort: advanced
Process Trace Alteration
PTrace syscall provides a means by which one process ("tracer") may observe and control the execution of another process ("tracee") and examine and change the tracee's memory and registers. Attacker might want to abuse ptrace functionnality to analyse memory process. It requires to be admin or set ptrace_scope to 0 to allow all user to trace any process.
- Effort: advanced
ProxyShell Microsoft Exchange Suspicious Paths
Detects suspicious calls to Microsoft Exchange resources, in locations related to webshells observed in campaigns using this vulnerability.
- Effort: elementary
PsExec Process
Detects PsExec execution, command line which contains pstools or installation of the PsExec service. PsExec is a SysInternals which can be used to execute a program on another computer. The tool is as much used by attackers as by administrators.
- Effort: advanced
RDP Session Discovery
Detects use of RDP session discovery via qwinsta or quser. Used by some threat actors to know if someone is working via RDP on a server.
- Effort: advanced
RTLO Character
Detects RTLO (Right-To-Left character) in file and process names.
- Effort: elementary
Raccoon Stealer 2.0 Legitimate Third-Party DLL Download URL
Detects Raccoon Stealer 2.0 malware downloading legitimate third-party DLLs from its C2 server. These legitimate DLLs are used by the information stealer to collect data on the compromised hosts.
- Effort: elementary
Remote Access Tool Domain
Detects traffic toward a domain flagged as a Remote Administration Tool (RAT).
- Effort: master
Remote Monitoring and Management Software - AnyDesk
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool AnyDesk.
- Effort: master
Remote Monitoring and Management Software - Atera
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool Atera.
- Effort: master
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
SELinux Disabling
An attacker can disable SELinux to make workstation or server compromise easier as it disables several protections.
- Effort: intermediate
Sekoia.io EICAR Detection
Detects observables in Sekoia.io CTI tagged as EICAR, which are fake samples meant to test detection.
- Effort: master
Suspicious Desktopimgdownldr Execution
Detects a suspicious Desktopimgdownldr execution. Desktopimgdownldr.exe is a Windows binary used to configure lockscreen/desktop image and can be abused to download malicious file.
- Effort: intermediate
Suspicious Double Extension
Detects suspicious use of an .exe extension after a non-executable file extension like .pdf.exe, a set of spaces or underlines to cloak the executable file in spearphishing campaigns
- Effort: advanced
Suspicious Download Links From Legitimate Services
Detects users clicking on Google docs links to download suspicious files. This technique was used a lot by Bazar Loader in the past.
- Effort: intermediate
Suspicious PROCEXP152.sys File Created In Tmp
Detects the creation of the PROCEXP152.sys file in the application-data local temporary folder. This driver is used by Sysinternals Process Explorer but also by KDU (https://github.com/hfiref0x/KDU) or Ghost-In-The-Logs (https://github.com/bats3c/Ghost-In-The-Logs), which uses KDU. Note - Clever attackers may easily bypass this detection by just renaming the driver filename. Therefore just Medium-level and don't rely on it.
- Effort: advanced
Suspicious TOR Gateway
Detects suspicious TOR gateways. Gateways are often used by the victim to pay and decrypt the encrypted files without installing TOR. Tor intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: advanced
Suspicious URI Used In A Lazarus Campaign
Detects suspicious requests to a specific URI, usually on an .asp page. The website is often compromised.
- Effort: intermediate
Suspicious Windows DNS Queries
Detects a suspicious Windows command-line process making a DNS query via known abuse text paste web services. This is based on Microsoft Windows Sysmon events (Event ID 22).
- Effort: advanced
System Info Discovery
System info discovery, attempt to detects basic command use to fingerprint a host.
- Effort: master
TOR Usage
Detects TOR usage, based on the IP address and the destination port (filtered on NTP). TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
TOR Usage Generic Rule
Detects TOR usage globally, whether the IP is a destination or source. TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
Tactical RMM Installation
Detection of common Tactical RMM installation arguments that could be abused by some attackers.
- Effort: elementary
Telegram Bot API Request
Detects suspicious DNS queries to api.telegram.org used by Telegram Bots of any kind
- Effort: advanced
Venom Multi-hop Proxy agent detection
Detects Venom Multi-hop Proxy agent.
- Effort: intermediate
WMI Persistence Script Event Consumer File Write
Detects file writes through WMI script event consumer.
- Effort: advanced
Windows Sandbox Start
Detection of Windows Sandbox started from the command line with a config file or interactively using a WSB file.
- Effort: master
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Anti-virus |
Symantec Endpoint Protection analyses processes and files to prevent malicious actions. |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | `` |
| Category | intrusion_detection, malware, network, process |
| Type | `` |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "Site: OSTAM,Server Name: STR04,Domain Name: MyDomain,The client has downloaded the content package successfully,STV02,ADMIN,stv02.local",
"event": {
"category": [
"network"
],
"reason": "The client has downloaded the content package successfully",
"type": [
"info"
]
},
"broadcom": {
"endpoint_protection": {
"server": {
"domain": "MyDomain",
"name": "STR04"
}
}
},
"host": {
"hostname": "STV02",
"name": "stv02.local"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"related": {
"hosts": [
"STV02"
],
"user": [
"ADMIN"
]
},
"user": {
"name": "ADMIN"
}
}
{
"message": "INT23456,,Blocked,C:\\Program Files (x86)\\Symantec\\Symantec Endpoint Protection\\14.3.4615.2000.105\\Bin64\\ccSvcHst.exe,,Begin: 2022-08-29 11:58:20,End Time: 2022-08-29 11:58:20,Rule: ,4428,C:\\PROGRAM FILES\\SMART-X\\CONTROLUPAGENT\\VERSION 8.1.5.634\\CUAGENT.EXE,0,,C:\\Program Files (x86)\\Symantec\\Symantec Endpoint Protection\\14.3.4615.2000.105\\Bin64\\ccSvcHst.exe,User Name: Admin,Domain Name: ,Action Type: 55,File size (bytes): ,Device ID: ",
"event": {
"action": "Blocked",
"category": [
"process"
],
"end": "2022-08-29T11:58:20Z",
"start": "2022-08-29T11:58:20Z",
"type": [
"denied"
]
},
"@timestamp": "2022-08-29T11:58:20Z",
"host": {
"hostname": "INT23456",
"name": "INT23456"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"process": {
"args": [
"C:\\Program Files (x86)\\Symantec\\Symantec Endpoint Protection\f.3.4615.2000.105\\Bin64\\ccSvcHst.exe"
],
"executable": "C:\\PROGRAM FILES\\SMART-X\\CONTROLUPAGENT\\VERSION 8.1.5.634\\CUAGENT.EXE",
"name": "CUAGENT.EXE",
"pid": 4428,
"working_directory": "C:\\PROGRAM FILES\\SMART-X\\CONTROLUPAGENT\\VERSION 8.1.5.634"
},
"related": {
"hosts": [
"INT23456"
],
"user": [
"Admin"
]
},
"user": {
"name": "Admin"
}
}
{
"message": "INT23456,1.2.3.4,Continue,Le contr\u00f4le des applications et des p\u00e9riph\u00e9riques est pr\u00eat.,Syst\u00e8me,Begin: 2022-10-19 06:45:39,End Time: 2022-10-19 06:45:39,Rule: R\u00e8gle int\u00e9gr\u00e9e,0,SysPlant,0,SysPlant,Aucun(e),User Name: Aucun(e),Domain Name: DOMAIN,Action Type: ,File size (bytes): 0,Device ID: ",
"event": {
"action": "Continue",
"category": [
"process"
],
"end": "2022-10-19T06:45:39Z",
"reason": "Le contr\u00f4le des applications et des p\u00e9riph\u00e9riques est pr\u00eat.",
"start": "2022-10-19T06:45:39Z",
"type": [
"info"
]
},
"@timestamp": "2022-10-19T06:45:39Z",
"broadcom": {
"endpoint_protection": {
"server": {
"domain": "DOMAIN"
}
}
},
"file": {
"size": 0
},
"host": {
"hostname": "INT23456",
"ip": "1.2.3.4",
"name": "INT23456"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"process": {
"executable": "SysPlant",
"name": "SysPlant",
"pid": 0
},
"related": {
"hosts": [
"INT23456"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "HOSTNAME,1.2.3.4,Continue,Le contr\u00f4le des applications et des p\u00e9riph\u00e9riques est pr\u00eat.,Syst\u00e8me,Begin: 2022-10-19 06:45:39,End Time: 2022-10-19 06:45:39,Rule: R\u00e8gle int\u00e9gr\u00e9e,0,SysPlant,0,SysPlant,Aucun(e),User Name: Aucun(e),Domain Name: DOMAIN,Action Type: ,File size (bytes): 0,Device ID:",
"event": {
"action": "Continue",
"category": [
"process"
],
"end": "2022-10-19T06:45:39Z",
"reason": "Le contr\u00f4le des applications et des p\u00e9riph\u00e9riques est pr\u00eat.",
"start": "2022-10-19T06:45:39Z",
"type": [
"info"
]
},
"@timestamp": "2022-10-19T06:45:39Z",
"broadcom": {
"endpoint_protection": {
"server": {
"domain": "DOMAIN"
}
}
},
"file": {
"size": 0
},
"host": {
"hostname": "HOSTNAME",
"ip": "1.2.3.4",
"name": "HOSTNAME"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"process": {
"executable": "SysPlant",
"name": "SysPlant",
"pid": 0
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "INT23456,Category: 2,LiveUpdate Manager,\"Event Description: L\u2019installation d\u2019une mise \u00e0 jour de Revocation Data a \u00e9chou\u00e9. Erreur : Echec de la correction de contenu (0xE0010005), DuResult: Succ\u00e8s (0).\",Event time: 2022-10-18 18:09:26,Group Name: MyDomain\\Servers",
"event": {
"category": [
"process"
],
"reason": "L\u2019installation d\u2019une mise \u00e0 jour de Revocation Data a \u00e9chou\u00e9. Erreur : Echec de la correction de contenu (0xE0010005), DuResult: Succ\u00e8s (0).",
"start": "2022-10-18T18:09:26Z",
"type": [
"info"
]
},
"@timestamp": "2022-10-18T18:09:26Z",
"broadcom": {
"endpoint_protection": {
"server": {
"group": "MyDomain\\Servers"
},
"source": "LiveUpdate Manager"
}
},
"host": {
"hostname": "INT23456",
"name": "INT23456"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"related": {
"hosts": [
"INT23456"
]
}
}
{
"message": "INT23456,Category: 2,LiveUpdate Manager,\"Event Description: L\u2019installation d\u2019une mise \u00e0 jour de Virus and Spyware Definitions SDS Win64 (Reduced) a \u00e9chou\u00e9. Erreur : Echec de la correction de contenu (0xE0010005), DuResult: Succ\u00e8s (0).\",Event time: 2022-10-19 07:32:25,Group Name: MyDomain\\Servers",
"event": {
"category": [
"malware"
],
"reason": "L\u2019installation d\u2019une mise \u00e0 jour de Virus and Spyware Definitions SDS Win64 (Reduced) a \u00e9chou\u00e9. Erreur : Echec de la correction de contenu (0xE0010005), DuResult: Succ\u00e8s (0).",
"start": "2022-10-19T07:32:25Z",
"type": [
"info"
]
},
"@timestamp": "2022-10-19T07:32:25Z",
"broadcom": {
"endpoint_protection": {
"server": {
"group": "MyDomain\\Servers"
},
"source": "LiveUpdate Manager"
}
},
"host": {
"hostname": "INT23456",
"name": "INT23456"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"related": {
"hosts": [
"INT23456"
]
}
}
{
"message": "INT23456,Event Description: [SID\u00a0: 32329] attaque de Audit: Malicious Scan Attempt 2 d\u00e9tect\u00e9e mais pas bloqu\u00e9e. Chemin d\u2019application\u00a0: SYSTEM,Event Type: ,Local Host IP: 1.2.3.4,Local Host MAC: 000000000000,Remote Host Name: ,Remote Host IP: 5.6.7.8,Remote Host MAC: 000000000000,Outbound,TCP,,Begin: 2022-10-19 09:25:40,End Time: 2022-10-19 09:25:40,Occurrences: 1,Application: SYSTEM,Location: Par d\u00e9faut,User Name: none,Domain Name: ,Local Port: 443,Remote Port: 14867,CIDS Signature ID: 32329,CIDS Signature string: Audit: Malicious Scan Attempt 2,CIDS Signature SubID: 68040,Intrusion URL: http://9.8.7.6:443/,Intrusion Payload URL: ,SHA-256: 0000000000000000000000000000000000000000000000000000000000000000,MD-5: ,Intensive Protection Level: N/A,URL Risk: N/A,URL Category: N/A",
"event": {
"category": [
"intrusion_detection"
],
"end": "2022-10-19T09:25:40Z",
"reason": "attaque de Audit: Malicious Scan Attempt 2 d\u00e9tect\u00e9e mais pas bloqu\u00e9e. Chemin d\u2019application\u00a0: SYSTEM",
"start": "2022-10-19T09:25:40Z",
"type": [
"info"
]
},
"@timestamp": "2022-10-19T09:25:40Z",
"broadcom": {
"endpoint_protection": {
"application": {
"name": "SYSTEM"
},
"cids": {
"signature": {
"id": 32329,
"label": "Audit: Malicious Scan Attempt 2",
"sub_id": 68040
}
}
}
},
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8",
"port": 14867
},
"host": {
"hostname": "INT23456",
"ip": "1.2.3.4",
"name": "INT23456"
},
"network": {
"direction": "outbound",
"transport": "tcp"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"related": {
"hosts": [
"INT23456"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 443
},
"threat": {
"enrichments": [
{
"indicator": {
"sightings": 1,
"type": "file"
}
}
]
},
"url": {
"domain": "9.8.7.6",
"full": "http://9.8.7.6:443/",
"original": "http://9.8.7.6:443/",
"path": "/",
"port": 443,
"scheme": "http"
}
}
{
"message": "VPNP02,Event Description: [SID: 32329] Audit: Malicious Scan Attempt 2 attaque d\u00e9tect\u00e9e mais pas bloqu\u00e9e. Chemin d\u2019application : SYSTEM,Event Type: ,Local Host IP: 1.2.3.4,Local Host MAC: 000000000000,Remote Host Name: ,Remote Host IP: 5.6.7.8,Remote Host MAC: 000000000000,Outbound,TCP,,Begin: 2022-10-19 08:26:56,End Time: 2022-10-19 08:26:56,Occurrences: 1,Application: SYSTEM,Location: Par d\u00e9faut,User Name: none,Domain Name: ,Local Port: 443,Remote Port: 23203,CIDS Signature ID: 32329,CIDS Signature string: Audit: Malicious Scan Attempt 2,CIDS Signature SubID: 65536,Intrusion URL: http://9.10.11.12:443/,Intrusion Payload URL: ,SHA-256: 0000000000000000000000000000000000000000000000000000000000000000,MD-5: ,Intensive Protection Level: N/A,URL Risk: N/A,URL Category: N/A",
"event": {
"category": [
"intrusion_detection"
],
"end": "2022-10-19T08:26:56Z",
"reason": "Audit: Malicious Scan Attempt 2 attaque d\u00e9tect\u00e9e mais pas bloqu\u00e9e. Chemin d\u2019application : SYSTEM",
"start": "2022-10-19T08:26:56Z",
"type": [
"info"
]
},
"@timestamp": "2022-10-19T08:26:56Z",
"broadcom": {
"endpoint_protection": {
"application": {
"name": "SYSTEM"
},
"cids": {
"signature": {
"id": 32329,
"label": "Audit: Malicious Scan Attempt 2",
"sub_id": 65536
}
}
}
},
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8",
"port": 23203
},
"host": {
"hostname": "VPNP02",
"ip": "1.2.3.4",
"name": "VPNP02"
},
"network": {
"direction": "outbound",
"transport": "tcp"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"related": {
"hosts": [
"VPNP02"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 443
},
"threat": {
"enrichments": [
{
"indicator": {
"sightings": 1,
"type": "file"
}
}
]
},
"url": {
"domain": "9.10.11.12",
"full": "http://9.10.11.12:443/",
"original": "http://9.10.11.12:443/",
"path": "/",
"port": 443,
"scheme": "http"
}
}
{
"message": "Scan ID: 1664847558,Begin: 2022-10-04 17:42:10,End Time: 2022-10-04 17:44:22,Completed,Duration (seconds): 132,User1: Syst\u00e8me,User2: Syst\u00e8me,Analyse lanc\u00e9e sur lecteurs et dossiers s\u00e9lectionn\u00e9s et toutes les extensions.,Analyse Installation standard : Risques : 0 Analys\u00e9s : 1553 Fichiers/Dossiers/Lecteurs omis : 0 Fichiers approuv\u00e9s ignor\u00e9s : 844,Command: Not a command scan (),Threats: 0,Infected: 0,Total files: 1553,Omitted: 0,Computer: DNHFF3453,IP Address: 1.2.3.4,Domain Name: MyDomain,Group Name: MyDomain\\Subdivision\\Citrix VDI persistants,Server Name: XXXXX01,Scan Type: DefWatch",
"event": {
"category": [
"malware"
],
"end": "2022-10-04T17:44:22Z",
"reason": "Analyse lanc\u00e9e sur lecteurs et dossiers s\u00e9lectionn\u00e9s et toutes les extensions.",
"start": "2022-10-04T17:42:10Z",
"type": [
"info"
]
},
"@timestamp": "2022-10-04T17:44:22Z",
"broadcom": {
"endpoint_protection": {
"scan": {
"command": "Not a command scan ()",
"duration": 132,
"id": "1664847558",
"result": {
"infections": 0,
"omitted": 0,
"threats": 0,
"total": 1553
},
"status": "completed",
"type": "DefWatch"
},
"server": {
"domain": "MyDomain",
"group": "MyDomain\\Subdivision\\Citrix VDI persistants",
"name": "XXXXX01"
}
}
},
"host": {
"hostname": "DNHFF3453",
"ip": "1.2.3.4",
"name": "DNHFF3453"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"related": {
"hosts": [
"DNHFF3453"
],
"ip": [
"1.2.3.4"
],
"user": [
"Syst\u00e8me"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"name": "Syst\u00e8me"
}
}
{
"message": "Scan ID: 1720651832,Begin: 2024-07-11 12:50:07,End Time: ,Started,Duration (seconds): 0,User1: jdoe,User2: ,Scan started on all drives and all extensions.,,Command: Not a command scan (),Threats: 0,Infected: 0,Total files: 0,Omitted: 0,Computer: DNFERO234,IP Address: 1.2.3.4,Domain Name: Par d\u00e9faut,Group Name: My Domain\\Region,Server Name: XXXXX001,Scan Type: Scheduled Scan",
"event": {
"category": [
"malware"
],
"reason": "Scan started on all drives and all extensions.",
"start": "2024-07-11T12:50:07Z",
"type": [
"info"
]
},
"@timestamp": "2024-07-11T12:50:07Z",
"broadcom": {
"endpoint_protection": {
"scan": {
"command": "Not a command scan ()",
"duration": 0,
"id": "1720651832",
"result": {
"infections": 0,
"omitted": 0,
"threats": 0,
"total": 0
},
"status": "started",
"type": "Scheduled Scan"
},
"server": {
"domain": "Par d\u00e9faut",
"group": "My Domain\\Region",
"name": "XXXXX001"
}
}
},
"host": {
"hostname": "DNFERO234",
"ip": "1.2.3.4",
"name": "DNFERO234"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"related": {
"hosts": [
"DNFERO234"
],
"ip": [
"1.2.3.4"
],
"user": [
"jdoe"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"name": "jdoe"
}
}
{
"message": "SONAR detection now allowed,IP Address: 1.2.3.4,Computer name: DNHFF3453,Source: Auto-Protect scan,Risk name: WS.Reputation.1,Occurrences: 1,File path: c:\\program files (x86)\\visualxxxxxxxxxx\\vtomxvision.exe,Description: ,Actual action: Action invalid,Requested action: Process terminate pending restart,Secondary action: 102,Event time: 2022-07-07 17:01:05,Event Insert Time: 2022-07-07 17:24:14,End Time: 2022-07-07 17:01:05,Last update time: 2022-07-07 17:24:14,Domain Name: MyDomain,Group Name: MyDomain\\Subdivision\\Citrix VDI persistants,Server Name: XXXXX01,User Name: Doe,Source Computer Name: ,Source Computer IP: ,Disposition: Good,Download site: ,Web domain: ,Downloaded by: c:/windows/explorer.exe,Prevalence: This file has been seen by fewer than 50 Symantec users.,Confidence: There is some evidence that this file is trustworthy.,URL Tracking Status: On,First Seen: Symantec has known about this file approximately 2 days.,Sensitivity: ,Allowed application reason: User allow list,Application hash: E13D72DE479A65E6448C779B3B2BCE45DB7B5AE52B1BAA0FE915380A667D3C01,Hash type: SHA2,Company name: Absyss S.A.S,Application name: Visual TOM,Application version: 6.6.1 (FR),Application type: 127,File size (bytes): 67352,Category set: Malware,Category type: Insight Network Threat,Location: MyDomain,Intensive Protection Level: 0,Certificate issuer: Absyss,Certificate signer: Sectigo RSA Code Signing CA,Certificate thumbprint: D31433F4C8C0BE4846E7E90318CD0CF5046EE95C,Signing timestamp: 1649155201,Certificate serial number: 044541E287C90A879334BFD15D6A3ED3",
"event": {
"action": "Process terminate pending restart",
"category": [
"process"
],
"reason": "SONAR detection now allowed",
"type": [
"info"
]
},
"@timestamp": "2022-07-07T17:24:14Z",
"broadcom": {
"endpoint_protection": {
"action": {
"main": "Action invalid",
"secondary": "102"
},
"application": {
"code_signature": {
"certificate": {
"serial_number": "044541E287C90A879334BFD15D6A3ED3",
"thumbprint": "D31433F4C8C0BE4846E7E90318CD0CF5046EE95C"
},
"digest_algorithm": "sha2",
"signer": "Sectigo RSA Code Signing CA",
"subject_name": "Absyss",
"timestamp": "2022-04-05T10:40:01.000000Z"
},
"hash": {
"sha2": "E13D72DE479A65E6448C779B3B2BCE45DB7B5AE52B1BAA0FE915380A667D3C01"
},
"name": "Visual TOM",
"version": "6.6.1 (FR)"
},
"confidence": "There is some evidence that this file is trustworthy.",
"downloaded_by": {
"file": {
"path": "c:/windows/explorer.exe"
}
},
"prevalence": "This file has been seen by fewer than 50 Symantec users.",
"protection": {
"level": 0
},
"server": {
"domain": "MyDomain",
"group": "MyDomain\\Subdivision\\Citrix VDI persistants",
"name": "XXXXX01"
},
"source": "Auto-Protect scan",
"threat": {
"category": "Malware",
"type": "Insight Network Threat"
}
}
},
"file": {
"directory": "c:\\program files (x86)\\visualxxxxxxxxxx",
"name": "vtomxvision.exe",
"path": "c:\\program files (x86)\\visualxxxxxxxxxx\\vtomxvision.exe",
"size": 67352
},
"host": {
"hostname": "DNHFF3453",
"ip": "1.2.3.4",
"name": "DNHFF3453"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"related": {
"hosts": [
"DNHFF3453"
],
"ip": [
"1.2.3.4"
],
"user": [
"Doe"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"threat": {
"enrichments": [
{
"indicator": {
"description": "WS.Reputation.1",
"file": {
"path": "c:\\program files (x86)\\visualxxxxxxxxxx\\vtomxvision.exe",
"size": 67352
},
"first_seen": "2022-07-07T17:01:05Z",
"last_seen": "2022-07-07T17:01:05Z",
"modified_at": "2022-07-07T17:24:14Z",
"sightings": 1,
"type": "file"
}
}
]
},
"user": {
"name": "Doe"
}
}
{
"message": "OND345,Category: 2,REP,Event Description: Impossible d\u2019assigner un jeton d\u2019authentification client. Une erreur de communication g\u00e9n\u00e9rale est survenue.,Event time: 2022-08-29 11:35:29,Group Name: Company\\Own",
"event": {
"category": [
"network"
],
"reason": "Impossible d\u2019assigner un jeton d\u2019authentification client. Une erreur de communication g\u00e9n\u00e9rale est survenue.",
"start": "2022-08-29T11:35:29Z",
"type": [
"info"
]
},
"@timestamp": "2022-08-29T11:35:29Z",
"broadcom": {
"endpoint_protection": {
"server": {
"group": "Company\\Own"
},
"source": "REP"
}
},
"host": {
"hostname": "OND345",
"name": "OND345"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"related": {
"hosts": [
"OND345"
]
}
}
{
"message": "Virus found,IP Address: 1.2.3.4,Computer name: DNHFF3453,Source: Auto-Protect scan,Risk name: EICAR Test String,Occurrences: 1,File path: C:\\Users\\admin\\Desktop\\test.txt,Description: AP realtime deferred scanning,Actual action: Cleaned by deletion,Requested action: Cleaned,Secondary action: Quarantined,Event time: 2022-07-07 14:28:39,Event Insert Time: 2022-07-07 14:30:43,End Time: 2022-07-07 14:28:39,Last update time: 2022-07-07 14:30:43,Domain Name: MyDomain,Group Name: MyDomain\\Subdivision\\Citrix VDI persistants,Server Name: XXXXX01,User Name: ADMIN,Source Computer Name: ,Source Computer IP: ,Disposition: Bad,Download site: ,Web domain: ,Downloaded by: ,Prevalence: This file has been seen by millions of Symantec users.,Confidence: This file is untrustworthy.,URL Tracking Status: On,First Seen: Reputation was not used in this detection.,Sensitivity: ,Allowed application reason: Not on the allow list,Application hash: 275A021BBFB6489E54D471899F7DB9D1663FC695EC2FE2A2C4538AABF651FD0F,Hash type: SHA2,Company name: ,Application name: Nouveau document texte.txt,Application version: ,Application type: 127,File size (bytes): 68,Category set: Malware,Category type: Virus,Location: MyDomain,Intensive Protection Level: 0,Certificate issuer: ,Certificate signer: ,Certificate thumbprint: ,Signing timestamp: ,Certificate serial number: ",
"event": {
"action": "Cleaned",
"category": [
"malware"
],
"reason": "Virus found",
"type": [
"info"
]
},
"@timestamp": "2022-07-07T14:30:43Z",
"broadcom": {
"endpoint_protection": {
"action": {
"main": "Cleaned by deletion",
"secondary": "Quarantined"
},
"application": {
"code_signature": {
"digest_algorithm": "sha2"
},
"hash": {
"sha2": "275A021BBFB6489E54D471899F7DB9D1663FC695EC2FE2A2C4538AABF651FD0F"
},
"name": "Nouveau document texte.txt"
},
"confidence": "This file is untrustworthy.",
"prevalence": "This file has been seen by millions of Symantec users.",
"protection": {
"level": 0
},
"server": {
"domain": "MyDomain",
"group": "MyDomain\\Subdivision\\Citrix VDI persistants",
"name": "XXXXX01"
},
"source": "Auto-Protect scan",
"threat": {
"category": "Malware",
"type": "Virus"
}
}
},
"file": {
"directory": "C:\\Users\\admin\\Desktop",
"name": "test.txt",
"path": "C:\\Users\\admin\\Desktop\\test.txt",
"size": 68
},
"host": {
"hostname": "DNHFF3453",
"ip": "1.2.3.4",
"name": "DNHFF3453"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"related": {
"hosts": [
"DNHFF3453"
],
"ip": [
"1.2.3.4"
],
"user": [
"ADMIN"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"threat": {
"enrichments": [
{
"indicator": {
"description": "EICAR Test String",
"file": {
"path": "C:\\Users\\admin\\Desktop\\test.txt",
"size": 68
},
"first_seen": "2022-07-07T14:28:39Z",
"last_seen": "2022-07-07T14:28:39Z",
"modified_at": "2022-07-07T14:30:43Z",
"sightings": 1,
"type": "file"
}
}
]
},
"user": {
"name": "ADMIN"
}
}
{
"message": "Virus found,IP Address: 1.2.3.4,Computer name: MyComputer,Source: Auto-Protect scan,Risk name: EICAR Test String,Occurrences: 1,File path: /tmp/eicar.txt,Description: ,Actual action: Quarantined,Requested action: Cleaned,Secondary action: Quarantined,Event time: 2022-10-04 19:10:48,Event Insert Time: 2022-10-04 19:15:22,End Time: 2022-10-04 19:10:48,Last update time: 2022-10-04 19:15:22,Domain Name: Par d\u00e9faut,Group Name: Mydomain\\\\Servers\\\\Linux,Server Name: XXXX01,User Name: user,Source Computer Name: ,Source Computer IP: ,Disposition: Reputation was not used in this detection.,Download site: ,Web domain: ,Downloaded by: ,Prevalence: Reputation was not used in this detection.,Confidence: Reputation was not used in this detection.,URL Tracking Status: N/A,First Seen: Reputation was not used in this detection.,Sensitivity: Low,Allowed application reason: Not on the allow list,Application hash: 131f95c51cc819465fa1797f6ccacf9d494aaaff46fa3eac73ae63ffbdfd8267,Hash type: SHA2,Company name: ,Application name: Unknown,Application version: ,Application type: -1,File size (bytes): 69,Category set: Malware,Category type: Virus,Location: ,Intensive Protection Level: 0,Certificate issuer: ,Certificate signer: ,Certificate thumbprint: ,Signing timestamp: 0,Certificate serial number: ",
"event": {
"action": "Cleaned",
"category": [
"malware"
],
"reason": "Virus found",
"type": [
"info"
]
},
"@timestamp": "2022-10-04T19:15:22Z",
"broadcom": {
"endpoint_protection": {
"action": {
"main": "Quarantined",
"secondary": "Quarantined"
},
"application": {
"code_signature": {
"digest_algorithm": "sha2"
},
"hash": {
"sha2": "131f95c51cc819465fa1797f6ccacf9d494aaaff46fa3eac73ae63ffbdfd8267"
},
"name": "Unknown"
},
"confidence": "Reputation was not used in this detection.",
"prevalence": "Reputation was not used in this detection.",
"protection": {
"level": 0
},
"server": {
"domain": "Par d\u00e9faut",
"group": "Mydomain\\\\Servers\\\\Linux",
"name": "XXXX01"
},
"source": "Auto-Protect scan",
"threat": {
"category": "Malware",
"type": "Virus"
}
}
},
"file": {
"directory": "/tmp",
"name": "eicar.txt",
"path": "/tmp/eicar.txt",
"size": 69
},
"host": {
"hostname": "MyComputer",
"ip": "1.2.3.4",
"name": "MyComputer"
},
"observer": {
"product": "Symantec Endpoint Protection",
"vendor": "Broadcom"
},
"related": {
"hosts": [
"MyComputer"
],
"ip": [
"1.2.3.4"
],
"user": [
"user"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"threat": {
"enrichments": [
{
"indicator": {
"description": "EICAR Test String",
"file": {
"path": "/tmp/eicar.txt",
"size": 69
},
"first_seen": "2022-10-04T19:10:48Z",
"last_seen": "2022-10-04T19:10:48Z",
"modified_at": "2022-10-04T19:15:22Z",
"sightings": 1,
"type": "file"
}
}
]
},
"user": {
"name": "user"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
broadcom.endpoint_protection.action.main |
keyword |
|
broadcom.endpoint_protection.action.secondary |
keyword |
|
broadcom.endpoint_protection.application.code_signature.certificate.serial_number |
keyword |
|
broadcom.endpoint_protection.application.code_signature.certificate.thumbprint |
keyword |
|
broadcom.endpoint_protection.application.code_signature.digest_algorithm |
keyword |
|
broadcom.endpoint_protection.application.code_signature.signer |
keyword |
|
broadcom.endpoint_protection.application.code_signature.subject_name |
keyword |
|
broadcom.endpoint_protection.application.code_signature.timestamp |
keyword |
|
broadcom.endpoint_protection.application.hash.sha2 |
keyword |
|
broadcom.endpoint_protection.application.name |
keyword |
|
broadcom.endpoint_protection.application.version |
keyword |
|
broadcom.endpoint_protection.cids.signature.id |
number |
The identifier of the CIDS sgnature |
broadcom.endpoint_protection.cids.signature.label |
string |
The label of the CIDS sgnature |
broadcom.endpoint_protection.cids.signature.sub_id |
number |
The sub-identifier of the CIDS sgnature |
broadcom.endpoint_protection.confidence |
keyword |
|
broadcom.endpoint_protection.downloaded_by.file.path |
keyword |
|
broadcom.endpoint_protection.prevalence |
keyword |
|
broadcom.endpoint_protection.protection.level |
number |
The level of intensve protection |
broadcom.endpoint_protection.scan.command |
keyword |
The command scan |
broadcom.endpoint_protection.scan.duration |
number |
The duration of the scan in seconds |
broadcom.endpoint_protection.scan.id |
keyword |
The identifier of the scan |
broadcom.endpoint_protection.scan.result.infections |
number |
The number of infected files |
broadcom.endpoint_protection.scan.result.omitted |
number |
The number of omitted files |
broadcom.endpoint_protection.scan.result.threats |
number |
The number of detected threats |
broadcom.endpoint_protection.scan.result.total |
number |
The number of total files scanned |
broadcom.endpoint_protection.scan.status |
keyword |
The status of the scan |
broadcom.endpoint_protection.scan.type |
keyword |
The type of scan |
broadcom.endpoint_protection.server.domain |
keyword |
|
broadcom.endpoint_protection.server.group |
keyword |
|
broadcom.endpoint_protection.server.name |
keyword |
|
broadcom.endpoint_protection.source |
keyword |
|
broadcom.endpoint_protection.threat.category |
keyword |
|
broadcom.endpoint_protection.threat.payload |
string |
The url of the intrusion payload |
broadcom.endpoint_protection.threat.risk |
string |
The risk associated to the intrusion url |
broadcom.endpoint_protection.threat.type |
keyword |
|
destination.domain |
keyword |
The domain name of the destination. |
destination.ip |
ip |
IP address of the destination. |
destination.mac |
keyword |
MAC address of the destination. |
destination.port |
long |
Port of the destination. |
event.action |
keyword |
The action captured by the event. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.end |
date |
event.end contains the date when the event ended or when the activity was last observed. |
event.reason |
keyword |
Reason why this event happened, according to the source |
event.start |
date |
event.start contains the date when the event started or when the activity was first observed. |
file.hash.md5 |
keyword |
MD5 hash. |
file.hash.sha256 |
keyword |
SHA256 hash. |
file.path |
keyword |
Full path to the file, including the file name. |
file.size |
long |
File size in bytes. |
host.hostname |
keyword |
Hostname of the host. |
host.ip |
ip |
Host ip addresses. |
host.mac |
keyword |
Host MAC addresses. |
host.name |
keyword |
Name of the host. |
network.direction |
keyword |
Direction of the network traffic. |
network.transport |
keyword |
Protocol Name corresponding to the field iana_number. |
observer.product |
keyword |
The product name of the observer. |
observer.vendor |
keyword |
Vendor name of the observer. |
process.args |
keyword |
Array of process arguments. |
process.executable |
keyword |
Absolute path to the process executable. |
process.name |
keyword |
Process name. |
process.pid |
long |
Process id. |
process.working_directory |
keyword |
The working directory of the process. |
source.ip |
ip |
IP address of the source. |
source.port |
long |
Port of the source. |
threat.enrichments |
nested |
List of objects containing indicators enriching the event. |
url.original |
wildcard |
Unmodified original url as seen in the event source. |
user.name |
keyword |
Short name or login of the user. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.