Cyberark Digital Vault
Overview
CyberArk Vault is a secure digital repository designed to protect and manage sensitive information, particularly privileged account credentials and secrets
- Vendor: CyberArk
- Supported environment: On Premise
- Detection based on: Telemetry
- Supported application or feature: Application logs
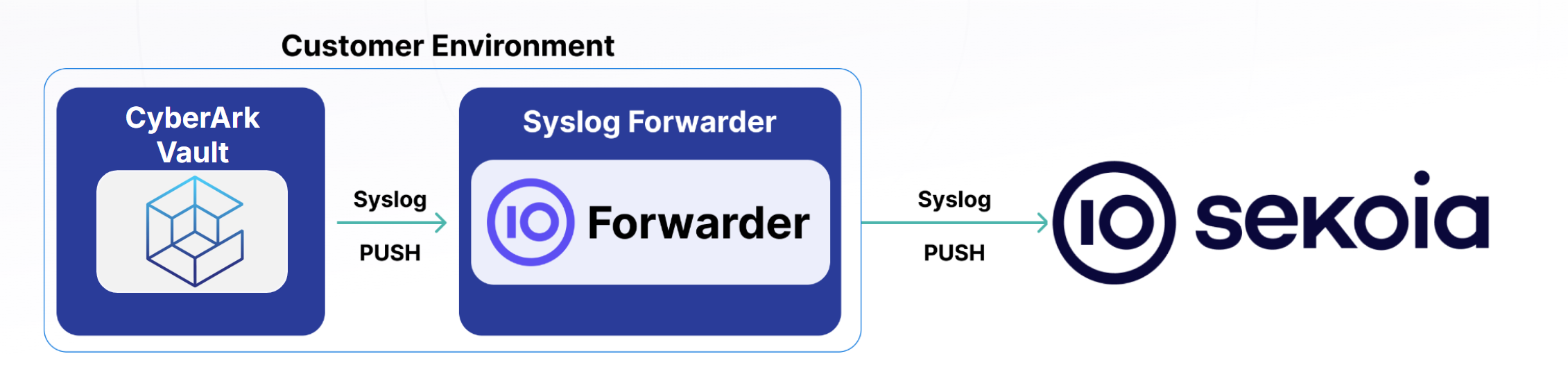
High-Level Architecture Diagram
- Type of integration: Outbound (PUSH to Sekoia.io)
- Schema
Specification
Prerequisites
- Resource:
- Self-managed syslog forwarder
- Network:
- Outbound traffic allowed
- Permissions:
- Root access to the Cyberark Vault appliance
- Root access to the Linux server with the syslog forwarder
Transport Protocol/Method
- Indirect Syslog
Logs details
- Supported functionalities: See section Overview
- Supported type(s) of structure: Syslog
- Supported verbosity level: Informational
Note
Log levels are based on the taxonomy of RFC5424. Adapt according to the terminology used by the editor.
Step-by-Step Quick Configuration Procedure
- Log in to your CyberArk Vault appliance.
-
Navigate to /Server/Conf, open the In DBParm.ini file, and configure the parameters that are relevant for syslog :
Note : if your security policy requires extra-security (ex: tls) between the application and the syslog forwarder, modify the configuration accordingly
SyslogServerIP={IP_OF_YOUR_SEKOIA_FORWARDER} SyslogServerPort={SEKOIA_FORWARDER_SPECIFIC_PORT} SyslogServerProtocol=TCP SyslogTranslatorFile=Syslog\QRadar.sample.xsl UseLegacySyslogFormat=no -
After saving DBPARM.ini file, restart the vault server
- Ensure that the Vault starts successfully and that there are no errors in the log.
Note
If you encounter any issues during the configuration specified in this section "Instructions on the 3rd Party Solution," please do not hesitate to contact your editor. We also welcome any suggestions for improving our documentation to better serve your needs.
Instruction on Sekoia
Configure Your Intake
This section will guide you through creating the intake object in Sekoia, which provides a unique identifier called the "Intake key." The Intake key is essential for later configuration, as it references the Community, Entity, and Parser (Intake Format) used when receiving raw events on Sekoia.
- Go to the Sekoia Intake page.
- Click on the
+ New Intakebutton at the top right of the page. - Search for your Intake by the product name in the search bar.
- Give it a Name and associate it with an Entity (and a Community if using multi-tenant mode).
- Click on
Create.
Note
For more details on how to use the Intake page and to find the Intake key you just created, refer to this documentation.
Configure a forwarder
To forward events using syslog to Sekoia.io, you need to update the syslog header with the intake key you previously created. Here is an example of your message before the forwarder
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG RAW_MESSAGE
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG [SEKOIA@53288 intake_key=\"YOUR_INTAKE_KEY\"] RAW_MESSAGE
To achieve this you can:
- Use the Sekoia.io forwarder which is the official supported way to collect data using the syslog protocol in Sekoia.io. In charge of centralizing data coming from many equipments/sources and forwarding them to Sekoia.io with the apporpriated format, it is a prepackaged option. You only have to provide your intake key as parameter.
- Use your own Syslog service instance. Maybe you already have an intance of one of these components on your side and want to reuse it in order to centralize data before forwarding them to Sekoia.io. When using this mode, you have to configure and maintain your component in order to respect the expected Sekoia.io format.
Warning
Only the Sekoia.io forwarder is officially supported. Other options are documented for reference purposes but do not have official support.
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
LEEF:1.0|Cyber-Ark|Vault|14.4.0002|286|sev=6 Action=Add Group Member - Synchronize from LDAP EventMessage=Add Group Member - Synchronize from LDAP OSUser= usrName=toto src=1.1.1.1 SourceUser=toto TargetUser=tata File= Safe= Location= Category= RequestId= Reason= ExtraDetails= GatewayStation=3.3.3.3 CAPolicy= shost=1.1.1.1 dhost= duser=USER externalId= app= reason=
LEEF:1.0|Cyber-Ark|Vault|14.4.0002|4|sev=3 Action=User Authentication EventMessage=User Authentication OSUser= usrName=toto src=1.1.1.1 SourceUser= TargetUser= File= Safe= Location= Category= RequestId= Reason= ExtraDetails= GatewayStation= CAPolicy= shost=1.1.1.1 dhost= duser= externalId= app= reason=
LEEF:1.0|Cyber-Ark|Vault|14.4.0001|7|sev=6 Action=Logon EventMessage=Logon OSUser= usrName=toto src=1.1.1.1 SourceUser= TargetUser= File= Safe= Location= Category= RequestId= Reason= ExtraDetails= GatewayStation= CAPolicy= shost=1.1.1.1 dhost= duser= externalId= app= reason=
LEEF:1.0|Cyber-Ark|Vault|14.4.0001|24|sev=6 Action=CPM Change Password EventMessage=CPM Change Password OSUser= usrName=toto src=1.1.1.1 SourceUser= TargetUser= File=Root/file_xxx Safe=safe_xxx Location= Category= RequestId= Reason=ExpirationPeriod ExtraDetails=address=domain.infra.client;username= USER@domain.infra.client; GatewayStation= CAPolicy= shost=1.1.1.1 dhost= duser= USER@domain.infra.client externalId= app= reason=
LEEF:1.0|Cyber-Ark|Vault|14.4.0002|2|sev=6 Action=Add External User EventMessage=Add External User OSUser= usrName=toto src=1.1.1.1 SourceUser=toto TargetUser= File= Safe= Location= Category= RequestId= Reason= ExtraDetails= GatewayStation=3.3.3.3 CAPolicy= shost=1.1.1.1 dhost= duser= externalId= app= reason=
LEEF:1.0|Cyber-Ark|Vault|14.4.0002|19|sev=6 Action=Full Gateway Connection EventMessage=Full Gateway Connection OSUser= usrName=toto src=1.1.1.1 SourceUser=toto TargetUser= File= Safe= Location= Category= RequestId= Reason= ExtraDetails= GatewayStation=3.3.3.3 CAPolicy= shost=1.1.1.1 dhost= duser= externalId= app= reason=
LEEF:1.0|Cyber-Ark|Vault|14.4.0002|361|sev=6 Action=Keystroke logging EventMessage=Keystroke logging OSUser= usrName=toto src=1.1.1.1 SourceUser= TargetUser= File=Root/file_xxx Safe=safe_xxx Location= Category= RequestId= Reason= ExtraDetails=Command=unset LANG LANGUAGE LC_CTYPE LC_COLLATE LC_MONETARY LC_NUMERIC LC_TIME LC_MESSAGES LC_ALL HUMAN_BLOCKS LS_COLORS\;cd '.'\;cd '.'\;cd '.'\;pwd\;ls -la;ConnectionComponentId=PSMP-SSH;DstHost=3.3.3.3;ManagedAccount=Yes;Protocol=SSH;PSMID=server_xxx;SessionID=c2e88cd6-21d4-4259-8456-64c8c5276c4d;SrcHost=1.1.1.1;SSHOffset=0B;User=toto;VIDOffset=0T; GatewayStation= CAPolicy= shost=1.1.1.1 dhost=3.3.3.3 duser=g_pam_demo_01 externalId=c2e88cd6-21d4-4259-8456-64c8c5276c4d app=SSH reason=unset LANG LANGUAGE LC_CTYPE LC_COLLATE LC_MONETARY LC_NUMERIC LC_TIME LC_MESSAGES LC_ALL HUMAN_BLOCKS LS_COLORS\
LEEF:1.0|Cyber-Ark|Vault|14.4.0002|300|sev=6 Action=PSM Connect EventMessage=PSM Connect OSUser= usrName=toto src=1.1.1.1 SourceUser= TargetUser= File=Root/file_xxx Safe=safe_xxx Location= Category= RequestId= Reason= ExtraDetails=ApplicationType=PSMP-SSH;DstHost=3.3.3.3;ManagedAccount=Yes;Protocol=SSH;PSMID=server_xxx;SessionID=73d7471a-cb37-4d20-914d-1c50df99114f;SrcHost=1.1.1.1;User=toto; GatewayStation= CAPolicy= shost=1.1.1.1 dhost=3.3.3.3 duser=g_pam_demo_01 externalId=73d7471a-cb37-4d20-914d-1c50df99114f app=SSH reason=
LEEF:1.0|Cyber-Ark|Vault|14.4.0002|302|sev=6 Action=PSM Disconnect EventMessage=PSM Disconnect OSUser= usrName=toto src=1.1.1.1 SourceUser= TargetUser= File=Root/file_xxx Safe=safe_xxx Location= Category= RequestId= Reason= ExtraDetails=ApplicationType=PSMP-SSH;DstHost=3.3.3.3;ManagedAccount=Yes;Protocol=SSH;PSMID=server_xxx;SessionDuration=00:00:15;SessionID=d1cde53b-28c4-48a8-9323-0db5009bf87e;SrcHost=1.1.1.1;User=toto; GatewayStation= CAPolicy= shost=1.1.1.1 dhost=3.3.3.3 duser=g_pam_demo_01 externalId=d1cde53b-28c4-48a8-9323-0db5009bf87e app=SSH reason=
LEEF:1.0|Cyber-Ark|Vault|14.4.0001|295|sev=6 Action=Retrieve password EventMessage=Retrieve password OSUser= usrName=toto src=1.1.1.1 SourceUser= TargetUser= File=Root/file_xxx Safe=safe_xxx Location= Category= RequestId= Reason=CPM ExtraDetails= GatewayStation= CAPolicy= shost=1.1.1.1 dhost=3.3.3.3 duser= USER@domain.infra.client externalId= app= reason=
LEEF:1.0|Cyber-Ark|Vault|14.4.0001|106|sev=6 Action=Update File Category EventMessage=Update File Category OSUser= usrName=toto src=1.1.1.1 SourceUser= TargetUser= File=Root/file_xxx Safe=safe_xxx Location= Category=PSMStartTime RequestId= Reason= ExtraDetails= GatewayStation= CAPolicy= shost=1.1.1.1 dhost= duser= externalId= app= reason=
LEEF:1.0|Cyber-Ark|Vault|14.4.0002|182|sev=6 Action=Update User EventMessage=Update User OSUser= usrName=toto src=1.1.1.1 SourceUser=toto TargetUser= File= Safe= Location= Category= RequestId= Reason= ExtraDetails= GatewayStation= CAPolicy= shost=1.1.1.1 dhost= duser= externalId= app= reason=
LEEF:1.0|Cyber-Ark|Vault|14.4.0002|308|sev=6 Action=Use Password EventMessage=Use Password OSUser= usrName=toto src=1.1.1.1 SourceUser= TargetUser= File=Root/file_xxx Safe=safe_xxx Location= Category= RequestId= Reason= ExtraDetails= GatewayStation=3.3.3.3 CAPolicy= shost=1.1.1.1 dhost=3.3.3.3 duser=g_pam_demo_01 externalId= app= reason=
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Authentication logs |
None |
Application logs |
None |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | event |
| Category | ['iam'] |
| Type | ['info'] |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "LEEF:1.0|Cyber-Ark|Vault|14.4.0002|286|sev=6\tAction=Add Group Member - Synchronize from LDAP\tEventMessage=Add Group Member - Synchronize from LDAP\tOSUser=\tusrName=toto\tsrc=1.1.1.1\tSourceUser=toto\tTargetUser=tata\tFile=\tSafe=\tLocation=\tCategory=\tRequestId=\tReason=\tExtraDetails=\tGatewayStation=3.3.3.3\tCAPolicy=\t shost=1.1.1.1\tdhost=\tduser=USER\texternalId=\tapp=\treason=",
"event": {
"action": "Add Group Member - Synchronize from LDAP",
"category": [
"configuration"
],
"code": "286",
"kind": "event",
"outcome": "success",
"severity": 6,
"type": [
"creation"
]
},
"cyberark": {
"vault": {
"GatewayStation": "3.3.3.3"
}
},
"destination": {
"user": {
"name": "USER"
}
},
"log": {
"description": "Add Group Member - Synchronize from LDAP",
"syslog": {
"severity": {
"code": 6,
"name": "Info"
}
}
},
"observer": {
"product": "Vault",
"vendor": "Cyber-Ark",
"version": "14.4.0002"
},
"related": {
"ip": [
"1.1.1.1"
],
"user": [
"USER",
"tata",
"toto"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"user": {
"name": "toto"
}
},
"user": {
"name": "toto",
"target": {
"name": "tata"
}
}
}
{
"message": "LEEF:1.0|Cyber-Ark|Vault|14.4.0002|4|sev=3\tAction=User Authentication\tEventMessage=User Authentication\tOSUser=\tusrName=toto\tsrc=1.1.1.1\tSourceUser=\tTargetUser=\tFile=\tSafe=\tLocation=\tCategory=\tRequestId=\tReason=\tExtraDetails=\tGatewayStation=\tCAPolicy=\t shost=1.1.1.1\tdhost=\tduser=\texternalId=\tapp=\treason=",
"event": {
"action": "User Authentication",
"category": [
"authentication"
],
"code": "4",
"kind": "event",
"outcome": "failure",
"severity": 3,
"type": [
"start"
]
},
"log": {
"description": "User Authentication",
"syslog": {
"severity": {
"code": 3,
"name": "Error"
}
}
},
"observer": {
"product": "Vault",
"vendor": "Cyber-Ark",
"version": "14.4.0002"
},
"related": {
"ip": [
"1.1.1.1"
],
"user": [
"toto"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"user": {
"name": "toto"
}
}
{
"message": "LEEF:1.0|Cyber-Ark|Vault|14.4.0001|7|sev=6\tAction=Logon\tEventMessage=Logon\tOSUser=\tusrName=toto\tsrc=1.1.1.1\tSourceUser=\tTargetUser=\tFile=\tSafe=\tLocation=\tCategory=\tRequestId=\tReason=\tExtraDetails=\tGatewayStation=\tCAPolicy=\t shost=1.1.1.1\tdhost=\tduser=\texternalId=\tapp=\treason=",
"event": {
"action": "Logon",
"category": [
"authentication"
],
"code": "7",
"kind": "event",
"outcome": "success",
"severity": 6,
"type": [
"start"
]
},
"log": {
"description": "Logon",
"syslog": {
"severity": {
"code": 6,
"name": "Info"
}
}
},
"observer": {
"product": "Vault",
"vendor": "Cyber-Ark",
"version": "14.4.0001"
},
"related": {
"ip": [
"1.1.1.1"
],
"user": [
"toto"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"user": {
"name": "toto"
}
}
{
"message": "LEEF:1.0|Cyber-Ark|Vault|14.4.0001|24|sev=6\tAction=CPM Change Password\tEventMessage=CPM Change Password\tOSUser=\tusrName=toto\tsrc=1.1.1.1\tSourceUser=\tTargetUser=\tFile=Root/file_xxx\tSafe=safe_xxx\tLocation=\tCategory=\tRequestId=\tReason=ExpirationPeriod\tExtraDetails=address=domain.infra.client;username= USER@domain.infra.client;\tGatewayStation=\tCAPolicy=\t shost=1.1.1.1\tdhost=\tduser= USER@domain.infra.client\texternalId=\tapp=\treason=",
"event": {
"action": "CPM Change Password",
"category": [
"configuration"
],
"code": "24",
"kind": "event",
"outcome": "success",
"severity": 6,
"type": [
"change"
]
},
"client": {
"user": {
"domain": "domain.infra.client",
"name": "USER@domain.infra.client"
}
},
"cyberark": {
"vault": {
"reason": "ExpirationPeriod",
"safe": "safe_xxx"
}
},
"destination": {
"user": {
"domain": "domain.infra.client",
"name": "USER@domain.infra.client"
}
},
"file": {
"name": "Root/file_xxx"
},
"log": {
"description": "CPM Change Password",
"syslog": {
"severity": {
"code": 6,
"name": "Info"
}
}
},
"observer": {
"product": "Vault",
"vendor": "Cyber-Ark",
"version": "14.4.0001"
},
"related": {
"ip": [
"1.1.1.1"
],
"user": [
"USER@domain.infra.client",
"toto"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"user": {
"name": "toto"
}
}
{
"message": "LEEF:1.0|Cyber-Ark|Vault|14.4.0002|2|sev=6\tAction=Add External User\tEventMessage=Add External User\tOSUser=\tusrName=toto\tsrc=1.1.1.1\tSourceUser=toto\tTargetUser=\tFile=\tSafe=\tLocation=\tCategory=\tRequestId=\tReason=\tExtraDetails=\tGatewayStation=3.3.3.3\tCAPolicy=\t shost=1.1.1.1\tdhost=\tduser=\texternalId=\tapp=\treason=",
"event": {
"action": "Add External User",
"category": [
"configuration"
],
"code": "2",
"kind": "event",
"outcome": "success",
"severity": 6,
"type": [
"creation"
]
},
"cyberark": {
"vault": {
"GatewayStation": "3.3.3.3"
}
},
"log": {
"description": "Add External User",
"syslog": {
"severity": {
"code": 6,
"name": "Info"
}
}
},
"observer": {
"product": "Vault",
"vendor": "Cyber-Ark",
"version": "14.4.0002"
},
"related": {
"ip": [
"1.1.1.1"
],
"user": [
"toto"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"user": {
"name": "toto"
}
},
"user": {
"name": "toto"
}
}
{
"message": "LEEF:1.0|Cyber-Ark|Vault|14.4.0002|19|sev=6\tAction=Full Gateway Connection\tEventMessage=Full Gateway Connection\tOSUser=\tusrName=toto\tsrc=1.1.1.1\tSourceUser=toto\tTargetUser=\tFile=\tSafe=\tLocation=\tCategory=\tRequestId=\tReason=\tExtraDetails=\tGatewayStation=3.3.3.3\tCAPolicy=\t shost=1.1.1.1\tdhost=\tduser=\texternalId=\tapp=\treason=",
"event": {
"action": "Full Gateway Connection",
"category": [
"network"
],
"code": "19",
"kind": "event",
"outcome": "success",
"severity": 6,
"type": [
"connection",
"start"
]
},
"cyberark": {
"vault": {
"GatewayStation": "3.3.3.3"
}
},
"log": {
"description": "Full Gateway Connection",
"syslog": {
"severity": {
"code": 6,
"name": "Info"
}
}
},
"observer": {
"product": "Vault",
"vendor": "Cyber-Ark",
"version": "14.4.0002"
},
"related": {
"ip": [
"1.1.1.1"
],
"user": [
"toto"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"user": {
"name": "toto"
}
},
"user": {
"name": "toto"
}
}
{
"message": "LEEF:1.0|Cyber-Ark|Vault|14.4.0002|361|sev=6\tAction=Keystroke logging\tEventMessage=Keystroke logging\tOSUser=\tusrName=toto\tsrc=1.1.1.1\tSourceUser=\tTargetUser=\tFile=Root/file_xxx\tSafe=safe_xxx\tLocation=\tCategory=\tRequestId=\tReason=\tExtraDetails=Command=unset LANG LANGUAGE LC_CTYPE LC_COLLATE LC_MONETARY LC_NUMERIC LC_TIME LC_MESSAGES LC_ALL HUMAN_BLOCKS LS_COLORS\\;cd '.'\\;cd '.'\\;cd '.'\\;pwd\\;ls -la;ConnectionComponentId=PSMP-SSH;DstHost=3.3.3.3;ManagedAccount=Yes;Protocol=SSH;PSMID=server_xxx;SessionID=c2e88cd6-21d4-4259-8456-64c8c5276c4d;SrcHost=1.1.1.1;SSHOffset=0B;User=toto;VIDOffset=0T;\tGatewayStation=\tCAPolicy=\t shost=1.1.1.1\tdhost=3.3.3.3\tduser=g_pam_demo_01\texternalId=c2e88cd6-21d4-4259-8456-64c8c5276c4d\tapp=SSH\treason=unset LANG LANGUAGE LC_CTYPE LC_COLLATE LC_MONETARY LC_NUMERIC LC_TIME LC_MESSAGES LC_ALL HUMAN_BLOCKS LS_COLORS\\",
"event": {
"action": "Keystroke logging",
"category": [
"iam"
],
"code": "361",
"kind": "event",
"outcome": "success",
"reason": "unset LANG LANGUAGE LC_CTYPE LC_COLLATE LC_MONETARY LC_NUMERIC LC_TIME LC_MESSAGES LC_ALL HUMAN_BLOCKS LS_COLORS\\",
"severity": 6,
"type": [
"info"
]
},
"cyberark": {
"psm": {
"application": "PSMP-SSH",
"command_line": "unset LANG LANGUAGE LC_CTYPE LC_COLLATE LC_MONETARY LC_NUMERIC LC_TIME LC_MESSAGES LC_ALL HUMAN_BLOCKS LS_COLORS\\;cd '.'\\;cd '.'\\;cd '.'\\;pwd\\;ls -la",
"server": {
"id": "server_xxx"
},
"session": {
"id": "c2e88cd6-21d4-4259-8456-64c8c5276c4d"
}
},
"vault": {
"safe": "safe_xxx"
}
},
"destination": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"user": {
"name": "g_pam_demo_01"
}
},
"file": {
"name": "Root/file_xxx"
},
"log": {
"description": "Keystroke logging",
"syslog": {
"severity": {
"code": 6,
"name": "Info"
}
}
},
"network": {
"protocol": "SSH"
},
"observer": {
"ip": "3.3.3.3",
"product": "Vault",
"vendor": "Cyber-Ark",
"version": "14.4.0002"
},
"related": {
"ip": [
"1.1.1.1",
"3.3.3.3"
],
"user": [
"g_pam_demo_01",
"toto"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"user": {
"name": "toto"
}
}
{
"message": "LEEF:1.0|Cyber-Ark|Vault|14.4.0002|300|sev=6\tAction=PSM Connect\tEventMessage=PSM Connect\tOSUser=\tusrName=toto\tsrc=1.1.1.1\tSourceUser=\tTargetUser=\tFile=Root/file_xxx\tSafe=safe_xxx\tLocation=\tCategory=\tRequestId=\tReason=\tExtraDetails=ApplicationType=PSMP-SSH;DstHost=3.3.3.3;ManagedAccount=Yes;Protocol=SSH;PSMID=server_xxx;SessionID=73d7471a-cb37-4d20-914d-1c50df99114f;SrcHost=1.1.1.1;User=toto;\tGatewayStation=\tCAPolicy=\t shost=1.1.1.1\tdhost=3.3.3.3\tduser=g_pam_demo_01\texternalId=73d7471a-cb37-4d20-914d-1c50df99114f\tapp=SSH\treason=",
"event": {
"action": "PSM Connect",
"category": [
"session"
],
"code": "300",
"kind": "event",
"outcome": "success",
"severity": 6,
"type": [
"start"
]
},
"cyberark": {
"psm": {
"application": "PSMP-SSH",
"server": {
"id": "server_xxx"
},
"session": {
"id": "73d7471a-cb37-4d20-914d-1c50df99114f"
}
},
"vault": {
"safe": "safe_xxx"
}
},
"destination": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"user": {
"name": "g_pam_demo_01"
}
},
"file": {
"name": "Root/file_xxx"
},
"log": {
"description": "PSM Connect",
"syslog": {
"severity": {
"code": 6,
"name": "Info"
}
}
},
"network": {
"protocol": "SSH"
},
"observer": {
"ip": "3.3.3.3",
"product": "Vault",
"vendor": "Cyber-Ark",
"version": "14.4.0002"
},
"related": {
"ip": [
"1.1.1.1",
"3.3.3.3"
],
"user": [
"g_pam_demo_01",
"toto"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"user": {
"name": "toto"
}
}
{
"message": "LEEF:1.0|Cyber-Ark|Vault|14.4.0002|302|sev=6\tAction=PSM Disconnect\tEventMessage=PSM Disconnect\tOSUser=\tusrName=toto\tsrc=1.1.1.1\tSourceUser=\tTargetUser=\tFile=Root/file_xxx\tSafe=safe_xxx\tLocation=\tCategory=\tRequestId=\tReason=\tExtraDetails=ApplicationType=PSMP-SSH;DstHost=3.3.3.3;ManagedAccount=Yes;Protocol=SSH;PSMID=server_xxx;SessionDuration=00:00:15;SessionID=d1cde53b-28c4-48a8-9323-0db5009bf87e;SrcHost=1.1.1.1;User=toto;\tGatewayStation=\tCAPolicy=\t shost=1.1.1.1\tdhost=3.3.3.3\tduser=g_pam_demo_01\texternalId=d1cde53b-28c4-48a8-9323-0db5009bf87e\tapp=SSH\treason=",
"event": {
"action": "PSM Disconnect",
"category": [
"session"
],
"code": "302",
"duration": 15000000000,
"kind": "event",
"outcome": "success",
"severity": 6,
"type": [
"end"
]
},
"cyberark": {
"psm": {
"application": "PSMP-SSH",
"server": {
"id": "server_xxx"
},
"session": {
"id": "d1cde53b-28c4-48a8-9323-0db5009bf87e"
}
},
"vault": {
"safe": "safe_xxx"
}
},
"destination": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"user": {
"name": "g_pam_demo_01"
}
},
"file": {
"name": "Root/file_xxx"
},
"log": {
"description": "PSM Disconnect",
"syslog": {
"severity": {
"code": 6,
"name": "Info"
}
}
},
"network": {
"protocol": "SSH"
},
"observer": {
"ip": "3.3.3.3",
"product": "Vault",
"vendor": "Cyber-Ark",
"version": "14.4.0002"
},
"related": {
"ip": [
"1.1.1.1",
"3.3.3.3"
],
"user": [
"g_pam_demo_01",
"toto"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"user": {
"name": "toto"
}
}
{
"message": "LEEF:1.0|Cyber-Ark|Vault|14.4.0001|295|sev=6\tAction=Retrieve password\tEventMessage=Retrieve password\tOSUser=\tusrName=toto\tsrc=1.1.1.1\tSourceUser=\tTargetUser=\tFile=Root/file_xxx\tSafe=safe_xxx\tLocation=\tCategory=\tRequestId=\tReason=CPM\tExtraDetails=\tGatewayStation=\tCAPolicy=\t shost=1.1.1.1\tdhost=3.3.3.3\tduser= USER@domain.infra.client\texternalId=\tapp=\treason=",
"event": {
"action": "Retrieve password",
"category": [
"iam"
],
"code": "295",
"kind": "event",
"outcome": "success",
"severity": 6,
"type": [
"info"
]
},
"cyberark": {
"vault": {
"reason": "CPM",
"safe": "safe_xxx"
}
},
"destination": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"user": {
"domain": "domain.infra.client",
"name": "USER@domain.infra.client"
}
},
"file": {
"name": "Root/file_xxx"
},
"log": {
"description": "Retrieve password",
"syslog": {
"severity": {
"code": 6,
"name": "Info"
}
}
},
"observer": {
"product": "Vault",
"vendor": "Cyber-Ark",
"version": "14.4.0001"
},
"related": {
"ip": [
"1.1.1.1",
"3.3.3.3"
],
"user": [
"USER@domain.infra.client",
"toto"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"user": {
"name": "toto"
}
}
{
"message": "LEEF:1.0|Cyber-Ark|Vault|14.4.0001|106|sev=6\tAction=Update File Category\tEventMessage=Update File Category\tOSUser=\tusrName=toto\tsrc=1.1.1.1\tSourceUser=\tTargetUser=\tFile=Root/file_xxx\tSafe=safe_xxx\tLocation=\tCategory=PSMStartTime\tRequestId=\tReason=\tExtraDetails=\tGatewayStation=\tCAPolicy=\t shost=1.1.1.1\tdhost=\tduser=\texternalId=\tapp=\treason=",
"event": {
"action": "Update File Category",
"category": [
"configuration",
"file"
],
"code": "106",
"kind": "event",
"outcome": "success",
"severity": 6,
"type": [
"change"
]
},
"cyberark": {
"vault": {
"category": "PSMStartTime",
"safe": "safe_xxx"
}
},
"file": {
"name": "Root/file_xxx"
},
"log": {
"description": "Update File Category",
"syslog": {
"severity": {
"code": 6,
"name": "Info"
}
}
},
"observer": {
"product": "Vault",
"vendor": "Cyber-Ark",
"version": "14.4.0001"
},
"related": {
"ip": [
"1.1.1.1"
],
"user": [
"toto"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"user": {
"name": "toto"
}
}
{
"message": "LEEF:1.0|Cyber-Ark|Vault|14.4.0002|182|sev=6\tAction=Update User\tEventMessage=Update User\tOSUser=\tusrName=toto\tsrc=1.1.1.1\tSourceUser=toto\tTargetUser=\tFile=\tSafe=\tLocation=\tCategory=\tRequestId=\tReason=\tExtraDetails=\tGatewayStation=\tCAPolicy=\t shost=1.1.1.1\tdhost=\tduser=\texternalId=\tapp=\treason=",
"event": {
"action": "Update User",
"category": [
"configuration"
],
"code": "182",
"kind": "event",
"outcome": "success",
"severity": 6,
"type": [
"change"
]
},
"log": {
"description": "Update User",
"syslog": {
"severity": {
"code": 6,
"name": "Info"
}
}
},
"observer": {
"product": "Vault",
"vendor": "Cyber-Ark",
"version": "14.4.0002"
},
"related": {
"ip": [
"1.1.1.1"
],
"user": [
"toto"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"user": {
"name": "toto"
}
},
"user": {
"name": "toto"
}
}
{
"message": "LEEF:1.0|Cyber-Ark|Vault|14.4.0002|308|sev=6\tAction=Use Password\tEventMessage=Use Password\tOSUser=\tusrName=toto\tsrc=1.1.1.1\tSourceUser=\tTargetUser=\tFile=Root/file_xxx\tSafe=safe_xxx\tLocation=\tCategory=\tRequestId=\tReason=\tExtraDetails=\tGatewayStation=3.3.3.3\tCAPolicy=\t shost=1.1.1.1\tdhost=3.3.3.3\tduser=g_pam_demo_01\texternalId=\tapp=\treason=",
"event": {
"action": "Use Password",
"category": [
"iam"
],
"code": "308",
"kind": "event",
"outcome": "success",
"severity": 6,
"type": [
"info"
]
},
"cyberark": {
"vault": {
"GatewayStation": "3.3.3.3",
"safe": "safe_xxx"
}
},
"destination": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"user": {
"name": "g_pam_demo_01"
}
},
"file": {
"name": "Root/file_xxx"
},
"log": {
"description": "Use Password",
"syslog": {
"severity": {
"code": 6,
"name": "Info"
}
}
},
"observer": {
"product": "Vault",
"vendor": "Cyber-Ark",
"version": "14.4.0002"
},
"related": {
"ip": [
"1.1.1.1",
"3.3.3.3"
],
"user": [
"g_pam_demo_01",
"toto"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"user": {
"name": "toto"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
client.user.domain |
keyword |
Name of the directory the user is a member of. |
client.user.name |
keyword |
Short name or login of the user. |
cyberark.psm.application |
keyword |
Name of the Privileged Session Manager application used. |
cyberark.psm.command_line |
keyword |
Command line sent through the Privileged Session Manager |
cyberark.psm.server.id |
keyword |
ID of the Privileged Session Manager Server |
cyberark.psm.session.id |
keyword |
Privileged Session Manager Session ID |
cyberark.vault.GatewayStation |
ip |
IP address of the gateway station |
cyberark.vault.category |
keyword |
The category linked to the ongoing action |
cyberark.vault.location |
keyword |
The target Location (for Location operations). |
cyberark.vault.reason |
keyword |
The reason for access to a vault |
cyberark.vault.safe |
keyword |
Name of the vault safe |
destination.domain |
keyword |
The domain name of the destination. |
destination.ip |
ip |
IP address of the destination. |
destination.user.domain |
keyword |
Name of the directory the user is a member of. |
destination.user.name |
keyword |
Short name or login of the user. |
event.action |
keyword |
The action captured by the event. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.code |
keyword |
Identification code for this event. |
event.duration |
long |
Duration of the event in nanoseconds. |
event.kind |
keyword |
The kind of the event. The highest categorization field in the hierarchy. |
event.outcome |
keyword |
The outcome of the event. The lowest level categorization field in the hierarchy. |
event.reason |
keyword |
Reason why this event happened, according to the source |
event.severity |
long |
Numeric severity of the event. |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
file.name |
keyword |
Name of the file including the extension, without the directory. |
log.syslog.severity.code |
long |
Syslog numeric severity of the event. |
network.protocol |
keyword |
Application protocol name. |
observer.ip |
ip |
IP addresses of the observer. |
observer.product |
keyword |
The product name of the observer. |
observer.vendor |
keyword |
Vendor name of the observer. |
observer.version |
keyword |
Observer version. |
source.domain |
keyword |
The domain name of the source. |
source.ip |
ip |
IP address of the source. |
source.user.domain |
keyword |
Name of the directory the user is a member of. |
source.user.name |
keyword |
Short name or login of the user. |
user.domain |
keyword |
Name of the directory the user is a member of. |
user.name |
keyword |
Short name or login of the user. |
user.target.domain |
keyword |
Name of the directory the user is a member of. |
user.target.name |
keyword |
Short name or login of the user. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.