BIND
Overview
BIND is an implementation of the Domain Name System (DNS) of the Internet. It performs both of the main DNS server roles, acting as an authoritative name server for domains, and acting as a recursive resolver in the network.
- Vendor: ISC
- Supported environment: On Premise
- Version compatibility: 9.18.8 (Latest version as of now)
- Detection based on: Telemetry
- Supported application or feature: DNS server
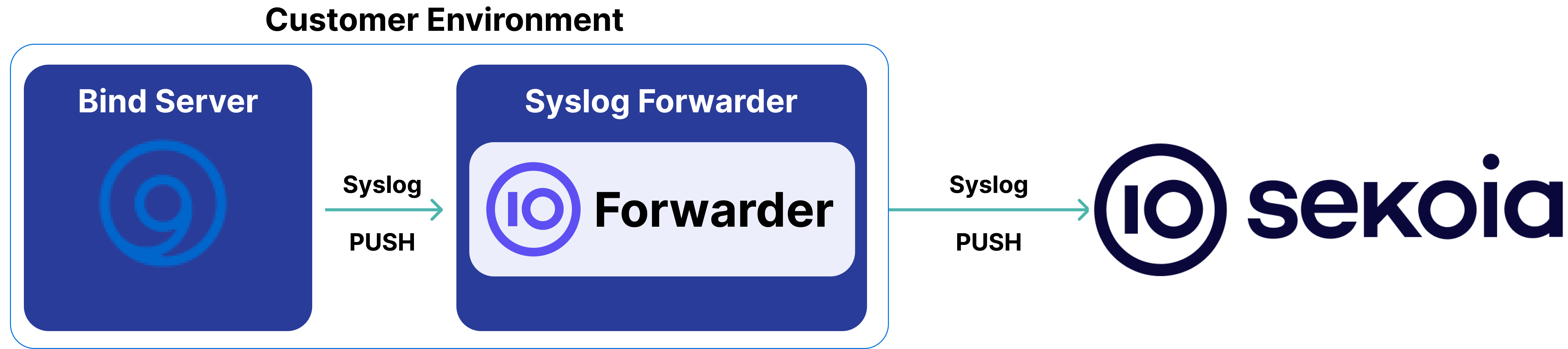
High-Level Architecture Diagram
- Type of integration: Outbound (PUSH to Sekoia.io)
- Schema
Alternative
This will not be detailed in this documentation, but logs can also be sent directly to Sekoia.io over HTTPS using the Sekoia.io Endpoint Agent and the "Collect logs in files" method. This provides an alternative to the specified syslog collection method and may be preferable in certain environments.
Specification
Prerequisites
- Resource:
- Self-managed syslog forwarder
- Network:
- Outbound traffic allowed
- Permissions:
- Administrator or Root access to the BIND server
- Root access to the Linux server with the syslog forwarder
Transport Protocol/Method
- Indirect Syslog
Logs details
- Supported functionalities: See section Overview
- Supported type(s) of structure: Plain Text
- Supported verbosity level: Informational
Note
Log levels are based on the taxonomy of RFC5424. Adapt according to the terminology used by the editor.
Step-by-Step Configuration Procedure
Instructions on the 3rd Party Solution
As of now, the main solution to collect BIND logs leverages the Rsyslog recipe. Please share your experiences with other recipes by editing this documentation.
Detailed Procedure on customer environment
- Configure BIND to Log Queries:
- First, you need to configure your BIND daemon to log queries and forward them to your rsyslog instance.
-
If rsyslog and BIND are installed on the same box, you can simply add the following statement in your BIND’s main configuration file (
named.conf):logging { channel syslog_chan { syslog daemon; severity dynamic; }; category default { syslog_chan; }; category queries { syslog_chan; }; category config { syslog_chan; }; category security { syslog_chan; }; }; -
Restart BIND Service:
-
Restart the BIND service to apply the logging configuration changes:
systemctl restart named -
Configure Rsyslog to Monitor BIND Log Files:
-
Add the following configuration to your
rsyslogconfiguration file (usually found in/etc/rsyslog.confor/etc/rsyslog.d/):# Bind log $InputFileName /var/log/bind.log $InputFileTag bind: $InputFileStateFile stat-bind $InputFileSeverity info $InputFileFacility local0 $InputFilePollInterval 10 $InputRunFileMonitor -
Forward Logs to a Concentrator:
-
Configure rsyslog to forward logs to a syslog concentrator:
*.* action(type="omfwd" target="<Concentrator_FQDN_or_IP>" port="<Remote_Port>" protocol="tcp" TCP_Framing="octet-counted" ) -
Verify Syslog Server Configuration:
- On your syslog server, verify that it is configured to accept syslog messages from the BIND server on the specified port.
For more information on how to configure your BIND instance on its official website.
Instruction on Sekoia
Configure Your Intake
This section will guide you through creating the intake object in Sekoia, which provides a unique identifier called the "Intake key." The Intake key is essential for later configuration, as it references the Community, Entity, and Parser (Intake Format) used when receiving raw events on Sekoia.
- Go to the Sekoia Intake page.
- Click on the
+ New Intakebutton at the top right of the page. - Search for your Intake by the product name in the search bar.
- Give it a Name and associate it with an Entity (and a Community if using multi-tenant mode).
- Click on
Create.
Note
For more details on how to use the Intake page and to find the Intake key you just created, refer to this documentation.
Configure a forwarder
To forward events using syslog to Sekoia.io, you need to update the syslog header with the intake key you previously created. Here is an example of your message before the forwarder
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG RAW_MESSAGE
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG [SEKOIA@53288 intake_key=\"YOUR_INTAKE_KEY\"] RAW_MESSAGE
To achieve this you can:
- Use the Sekoia.io forwarder which is the official supported way to collect data using the syslog protocol in Sekoia.io. In charge of centralizing data coming from many equipments/sources and forwarding them to Sekoia.io with the apporpriated format, it is a prepackaged option. You only have to provide your intake key as parameter.
- Use your own Syslog service instance. Maybe you already have an intance of one of these components on your side and want to reuse it in order to centralize data before forwarding them to Sekoia.io. When using this mode, you have to configure and maintain your component in order to respect the expected Sekoia.io format.
Warning
Only the Sekoia.io forwarder is officially supported. Other options are documented for reference purposes but do not have official support.
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
client @0xfc886160 10.251.201.26#54298 (geu5-onenote-eap.officeapps.live.com): answer: geu5-onenote-eap.officeapps.live.com IN HTTPS +EDC (10.0.0.2) -> NOERROR
client @0xfc886160 10.251.10.22#58925 (geu5-onenote-eap.officeapps.live.com): answer: geu5-onenote-eap.officeapps.live.com IN A +EDC (10.0.0.2) -> NOERROR x01geu5-onenote-eap.officeapps.live.com. 0 A 10.0.0.1
client @0x7fd36d364968 10.34.9.251#55892 (example.com): query failed (timed out) for assures-example.com/IN/A at query.c:7841
client @0x873f1160 10.251.201.29#58280 (10.0.0.1.in-addr.arpa): rpz NSIP/NSDNAME rewrite 10.0.0.1.in-addr.arpa via 111.0.in-addr.arpa unrecognized NS rpz_rrset_find() failed: SERVFAIL
client @0x8c331160 127.0.0.1#55475 (localhost): answer: localhost IN A + (127.0.0.1) -> NXDOMAIN
client @0x7f62b80115d0 192.168.101.70#55575 (docs.sekoia.io): query: docs.sekoia.io IN AAAA + (192.168.100.102)
client 192.168.101.70#55575 (docs.sekoia.io): query: docs.sekoia.io IN AAAA +TC (192.168.100.102)
client 192.168.103.66#42811 (ipv6.google.com): query: ipv6.google.com IN A +EDC (192.168.100.102)
client @0x7f4f8003d9e0 192.168.101.61#38251 (global.vortex.data.trafficmanager.net): query: global.vortex.data.trafficmanager.net IN AAAA +E(0) (192.168.100.102)
client 192.168.103.66#57980 (ipv6.google.com): query: ipv6.google.com IN AAAA - (192.168.100.102)
client 192.168.103.66#45041 (107.100.168.192.in-addr.arpa): query: 107.100.168.192.in-addr.arpa IN PTR +E (192.168.100.102)
client 192.168.101.70#55575 (docs.sekoia.io): query: docs.sekoia.io IN AAAA +ET (192.168.100.102)
timed out resolving 'example.org/A/IN': 5.6.7.8#53
validating api.atlassian.com/A: no valid signature found
validating cloudflare.com/SOA: got insecure response; parent indicates it should be secure
view internal: validating custhelp.com/SOA: no valid signature found
success resolving 'example.org/A' after disabling qname minimization due to 'ncache nxdomain'
lame server resolving '113.0.0.1.in-addr.arpa' (in '10.16.78.in-addr.arpa'?): 10.0.0.1#53
network unreachable resolving '113.0.0.1.in-addr.arpa/PTR/IN': 19e9:ae66:c43d:fc8:fcaf:df4a:2bd8:29ab#53
client @0x12345678 1.2.3.4#52998 (id.test.fr): rpz QNAME PASSTHRU rewrite id.test.fr/A/IN via id.test.fr.0-1.wl.rpz
client @0x12345678 1.2.3.4#49966 (test.com): rpz QNAME CNAME rewrite test.com/A/IN via test.com.badrep.host.dtq (CNAME to: badrep.host.dtq.rpz.portal.net.be.ch)
rpz: bad-nameservers.host.dtq: reload done: success
rpz: bad-nameservers.host.dtq: reload start
rpz: bad-nameservers.ip.dtq: new zone version came too soon, deferring update for 60 seconds
general: info: zone 10.in-addr.arpa/IN: Transfer started.
zone 10.in-addr.arpa/IN: Transfer started.
zone 10.in-addr.arpa/IN: sending notifies (serial 393191)
zone 10.in-addr.arpa/IN: api.atlassian.com/A: bad owner name (check-names)
zone 10.in-addr.arpa/IN: transferred serial 273966: TSIG 'bern-key'
general: info: zone 10.in-addr.arpa/IN: refresh: retry limit for master 10.0.0.1#53 exceeded (source 0.0.0.0#0)
transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: Transfer completed: 0 messages, 26 records, 0 bytes, 0.001 secs (0 bytes/sec) (serial 393191)
transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: Transfer status: IXFR failed
transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: connected using 5.6.7.8#53
transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: failed while receiving responses: not exact
transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: Transfer status: success
xfer-in: error: transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: failed to connect: host unreachable
xfer-in: info: transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: Transfer completed: 0 messages, 0 records, 0 bytes, 3.075 secs (0 bytes/sec)
xfer-in: info: transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: Transfer status: host unreachable
general: info: zone 2.0.192.in-addr.arpa/IN/internal: serial number (1771420876) received from master 192.0.2.1#53 < ours (1772690752)
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake BIND. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x BIND on ATT&CK Navigator
Bazar Loader DGA (Domain Generation Algorithm)
Detects Bazar Loader domains based on the Bazar Loader DGA
- Effort: elementary
Cobalt Strike DNS Beaconing
Detects suspicious DNS queries known from Cobalt Strike beacons. The threshold is more than 50 suspicious DNS requests to avoid false positives.
- Effort: advanced
Correlation Potential DNS Tunnel
Detects domain name which is longer than 62 characters and requested at least 50 times in a 10 minutes range time. Long domain names are distinctive of DNS tunnels.
- Effort: advanced
Cryptomining
Detection of domain names potentially related to cryptomining activities.
- Effort: master
Dynamic DNS Contacted
Detect communication with dynamic dns domain. This kind of domain is often used by attackers. This rule can trigger false positive in non-controlled environment because dynamic dns is not always malicious.
- Effort: master
EvilProxy Phishing Domain
Detects subdomains potentially generated by the EvilProxy adversary-in-the-middle phishing platform. Inspect the other subdomains of the domain to identify the landing page, and determine if the user submitted credentials. This rule has a small percentage of false positives on legitimate domains.
- Effort: intermediate
Exfiltration Domain
Detects traffic toward a domain flagged as a possible exfiltration vector.
- Effort: master
Potential DNS Tunnel
Detects domain name which is longer than 62 characters. Long domain names are distinctive of DNS tunnels.
- Effort: advanced
Remote Access Tool Domain
Detects traffic toward a domain flagged as a Remote Administration Tool (RAT).
- Effort: master
Remote Monitoring and Management Software - AnyDesk
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool AnyDesk.
- Effort: master
Remote Monitoring and Management Software - Atera
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool Atera.
- Effort: master
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
Sekoia.io EICAR Detection
Detects observables in Sekoia.io CTI tagged as EICAR, which are fake samples meant to test detection.
- Effort: master
Sliver DNS Beaconing
Detects suspicious DNS queries known from Sliver beaconing
- Effort: intermediate
Suspicious TOR Gateway
Detects suspicious TOR gateways. Gateways are often used by the victim to pay and decrypt the encrypted files without installing TOR. Tor intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: advanced
TOR Usage Generic Rule
Detects TOR usage globally, whether the IP is a destination or source. TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
Telegram Bot API Request
Detects suspicious DNS queries to api.telegram.org used by Telegram Bots of any kind
- Effort: advanced
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
DNS records |
BIND provides detailed logs on handled DNS queries |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "client @0xfc886160 10.251.201.26#54298 (geu5-onenote-eap.officeapps.live.com): answer: geu5-onenote-eap.officeapps.live.com IN HTTPS +EDC (10.0.0.2) -> NOERROR",
"dns": {
"answers": [
{
"data": "10.0.0.2",
"type": "HTTPS"
}
],
"header_flags": [
"CD",
"RD"
],
"question": {
"class": "IN",
"name": "geu5-onenote-eap.officeapps.live.com",
"registered_domain": "live.com",
"subdomain": "geu5-onenote-eap.officeapps",
"top_level_domain": "com",
"type": "HTTPS"
},
"response_code": "NOERROR",
"type": "answer"
},
"related": {
"hosts": [
"geu5-onenote-eap.officeapps.live.com"
],
"ip": [
"10.251.201.26"
]
},
"source": {
"address": "10.251.201.26",
"ip": "10.251.201.26",
"port": 54298
}
}
{
"message": "client @0xfc886160 10.251.10.22#58925 (geu5-onenote-eap.officeapps.live.com): answer: geu5-onenote-eap.officeapps.live.com IN A +EDC (10.0.0.2) -> NOERROR x01geu5-onenote-eap.officeapps.live.com. 0 A 10.0.0.1",
"dns": {
"answers": [
{
"data": "10.0.0.2",
"type": "A"
},
{
"class": "0",
"data": "10.0.0.1",
"name": "x01geu5-onenote-eap.officeapps.live.com.",
"type": "A"
}
],
"header_flags": [
"CD",
"RD"
],
"question": {
"class": "IN",
"name": "geu5-onenote-eap.officeapps.live.com",
"registered_domain": "live.com",
"subdomain": "geu5-onenote-eap.officeapps",
"top_level_domain": "com",
"type": "A"
},
"response_code": "NOERROR",
"type": "answer"
},
"related": {
"hosts": [
"geu5-onenote-eap.officeapps.live.com"
],
"ip": [
"10.251.10.22"
]
},
"source": {
"address": "10.251.10.22",
"ip": "10.251.10.22",
"port": 58925
}
}
{
"message": "client @0x7fd36d364968 10.34.9.251#55892 (example.com): query failed (timed out) for assures-example.com/IN/A at query.c:7841",
"dns": {
"question": {
"class": "IN",
"name": "assures-example.com",
"registered_domain": "assures-example.com",
"top_level_domain": "com",
"type": "A"
},
"type": "query"
},
"error": {
"message": "query failed (timed out)"
},
"related": {
"hosts": [
"assures-example.com"
],
"ip": [
"10.34.9.251"
]
},
"source": {
"address": "10.34.9.251",
"ip": "10.34.9.251",
"port": 55892
}
}
{
"message": "client @0x873f1160 10.251.201.29#58280 (10.0.0.1.in-addr.arpa): rpz NSIP/NSDNAME rewrite 10.0.0.1.in-addr.arpa via 111.0.in-addr.arpa unrecognized NS rpz_rrset_find() failed: SERVFAIL",
"dns": {
"question": {
"name": "10.0.0.1.in-addr.arpa",
"registered_domain": "1.in-addr.arpa",
"subdomain": "10.0.0",
"top_level_domain": "in-addr.arpa"
},
"response_code": "SERVFAIL",
"type": "query"
},
"error": {
"message": "rpz NSIP/NSDNAME rewrite 10.0.0.1.in-addr.arpa via 111.0.in-addr.arpa unrecognized NS rpz_rrset_find() failed"
},
"related": {
"hosts": [
"10.0.0.1.in-addr.arpa"
],
"ip": [
"10.251.201.29"
]
},
"source": {
"address": "10.251.201.29",
"ip": "10.251.201.29",
"port": 58280
}
}
{
"message": "client @0x8c331160 127.0.0.1#55475 (localhost): answer: localhost IN A + (127.0.0.1) -> NXDOMAIN",
"dns": {
"answers": [
{
"data": "127.0.0.1",
"type": "A"
}
],
"header_flags": [
"RD"
],
"question": {
"class": "IN",
"name": "localhost",
"type": "A"
},
"response_code": "NXDOMAIN",
"type": "answer"
},
"related": {
"hosts": [
"localhost"
],
"ip": [
"127.0.0.1"
]
},
"source": {
"address": "127.0.0.1",
"ip": "127.0.0.1",
"port": 55475
}
}
{
"message": "client @0x7f62b80115d0 192.168.101.70#55575 (docs.sekoia.io): query: docs.sekoia.io IN AAAA + (192.168.100.102)",
"dns": {
"header_flags": [
"RD"
],
"question": {
"class": "IN",
"name": "docs.sekoia.io",
"registered_domain": "sekoia.io",
"subdomain": "docs",
"top_level_domain": "io",
"type": "AAAA"
},
"type": "query"
},
"related": {
"hosts": [
"docs.sekoia.io"
],
"ip": [
"192.168.101.70"
]
},
"source": {
"address": "192.168.101.70",
"ip": "192.168.101.70",
"port": 55575
}
}
{
"message": "client 192.168.101.70#55575 (docs.sekoia.io): query: docs.sekoia.io IN AAAA +TC (192.168.100.102)",
"dns": {
"header_flags": [
"CD",
"RD"
],
"question": {
"class": "IN",
"name": "docs.sekoia.io",
"registered_domain": "sekoia.io",
"subdomain": "docs",
"top_level_domain": "io",
"type": "AAAA"
},
"type": "query"
},
"network": {
"transport": "tcp"
},
"related": {
"hosts": [
"docs.sekoia.io"
],
"ip": [
"192.168.101.70"
]
},
"source": {
"address": "192.168.101.70",
"ip": "192.168.101.70",
"port": 55575
}
}
{
"message": "client 192.168.103.66#42811 (ipv6.google.com): query: ipv6.google.com IN A +EDC (192.168.100.102)",
"dns": {
"header_flags": [
"CD",
"RD"
],
"question": {
"class": "IN",
"name": "ipv6.google.com",
"registered_domain": "google.com",
"subdomain": "ipv6",
"top_level_domain": "com",
"type": "A"
},
"type": "query"
},
"related": {
"hosts": [
"ipv6.google.com"
],
"ip": [
"192.168.103.66"
]
},
"source": {
"address": "192.168.103.66",
"ip": "192.168.103.66",
"port": 42811
}
}
{
"message": "client @0x7f4f8003d9e0 192.168.101.61#38251 (global.vortex.data.trafficmanager.net): query: global.vortex.data.trafficmanager.net IN AAAA +E(0) (192.168.100.102)",
"dns": {
"header_flags": [
"RD"
],
"question": {
"class": "IN",
"name": "global.vortex.data.trafficmanager.net",
"registered_domain": "trafficmanager.net",
"subdomain": "global.vortex.data",
"top_level_domain": "net",
"type": "AAAA"
},
"type": "query"
},
"related": {
"hosts": [
"global.vortex.data.trafficmanager.net"
],
"ip": [
"192.168.101.61"
]
},
"source": {
"address": "192.168.101.61",
"ip": "192.168.101.61",
"port": 38251
}
}
{
"message": "client 192.168.103.66#57980 (ipv6.google.com): query: ipv6.google.com IN AAAA - (192.168.100.102)",
"dns": {
"header_flags": [],
"question": {
"class": "IN",
"name": "ipv6.google.com",
"registered_domain": "google.com",
"subdomain": "ipv6",
"top_level_domain": "com",
"type": "AAAA"
},
"type": "query"
},
"related": {
"hosts": [
"ipv6.google.com"
],
"ip": [
"192.168.103.66"
]
},
"source": {
"address": "192.168.103.66",
"ip": "192.168.103.66",
"port": 57980
}
}
{
"message": "client 192.168.103.66#45041 (107.100.168.192.in-addr.arpa): query: 107.100.168.192.in-addr.arpa IN PTR +E (192.168.100.102)",
"dns": {
"header_flags": [
"RD"
],
"question": {
"class": "IN",
"name": "107.100.168.192.in-addr.arpa",
"registered_domain": "192.in-addr.arpa",
"subdomain": "107.100.168",
"top_level_domain": "in-addr.arpa",
"type": "PTR"
},
"type": "query"
},
"related": {
"hosts": [
"107.100.168.192.in-addr.arpa"
],
"ip": [
"192.168.103.66"
]
},
"source": {
"address": "192.168.103.66",
"ip": "192.168.103.66",
"port": 45041
}
}
{
"message": "client 192.168.101.70#55575 (docs.sekoia.io): query: docs.sekoia.io IN AAAA +ET (192.168.100.102)",
"dns": {
"header_flags": [
"RD"
],
"question": {
"class": "IN",
"name": "docs.sekoia.io",
"registered_domain": "sekoia.io",
"subdomain": "docs",
"top_level_domain": "io",
"type": "AAAA"
},
"type": "query"
},
"network": {
"transport": "tcp"
},
"related": {
"hosts": [
"docs.sekoia.io"
],
"ip": [
"192.168.101.70"
]
},
"source": {
"address": "192.168.101.70",
"ip": "192.168.101.70",
"port": 55575
}
}
{
"message": "timed out resolving 'example.org/A/IN': 5.6.7.8#53",
"bind": {
"rpz": {
"action": "resolving",
"status": "timed out"
}
},
"dns": {
"question": {
"class": "A",
"name": "example.org",
"registered_domain": "example.org",
"top_level_domain": "org",
"type": "IN"
},
"type": "query"
},
"related": {
"hosts": [
"example.org"
],
"ip": [
"5.6.7.8"
]
},
"source": {
"address": "5.6.7.8",
"ip": "5.6.7.8",
"port": 53
}
}
{
"message": "validating api.atlassian.com/A: no valid signature found",
"bind": {
"rpz": {
"action": "validating"
}
},
"dns": {
"question": {
"class": "A",
"name": "api.atlassian.com",
"registered_domain": "atlassian.com",
"subdomain": "api",
"top_level_domain": "com"
},
"type": "query"
},
"error": {
"message": "no valid signature found"
},
"related": {
"hosts": [
"api.atlassian.com"
]
}
}
{
"message": "validating cloudflare.com/SOA: got insecure response; parent indicates it should be secure",
"bind": {
"rpz": {
"action": "validating"
}
},
"dns": {
"question": {
"class": "SOA",
"name": "cloudflare.com",
"registered_domain": "cloudflare.com",
"top_level_domain": "com"
},
"type": "query"
},
"error": {
"message": "got insecure response; parent indicates it should be secure"
},
"related": {
"hosts": [
"cloudflare.com"
]
}
}
{
"message": "view internal: validating custhelp.com/SOA: no valid signature found",
"bind": {
"rpz": {
"action": "validating"
}
},
"dns": {
"question": {
"class": "SOA",
"name": "custhelp.com",
"registered_domain": "custhelp.com",
"top_level_domain": "com"
},
"type": "query"
},
"error": {
"message": "no valid signature found"
},
"related": {
"hosts": [
"custhelp.com"
]
}
}
{
"message": "success resolving 'example.org/A' after disabling qname minimization due to 'ncache nxdomain'",
"bind": {
"rpz": {
"action": "resolving",
"status": "success"
}
},
"dns": {
"question": {
"class": "A",
"name": "example.org",
"registered_domain": "example.org",
"top_level_domain": "org"
},
"type": "query"
},
"related": {
"hosts": [
"example.org"
]
}
}
{
"message": "lame server resolving '113.0.0.1.in-addr.arpa' (in '10.16.78.in-addr.arpa'?): 10.0.0.1#53",
"bind": {
"rpz": {
"action": "resolving",
"status": "lame server"
}
},
"dns": {
"question": {
"name": "113.0.0.1.in-addr.arpa",
"registered_domain": "1.in-addr.arpa",
"subdomain": "113.0.0",
"top_level_domain": "in-addr.arpa"
},
"type": "query"
},
"related": {
"hosts": [
"113.0.0.1.in-addr.arpa"
],
"ip": [
"10.0.0.1"
]
},
"source": {
"address": "10.0.0.1",
"ip": "10.0.0.1",
"port": 53
}
}
{
"message": "network unreachable resolving '113.0.0.1.in-addr.arpa/PTR/IN': 19e9:ae66:c43d:fc8:fcaf:df4a:2bd8:29ab#53",
"bind": {
"rpz": {
"action": "resolving",
"status": "network unreachable"
}
},
"dns": {
"question": {
"class": "PTR",
"name": "113.0.0.1.in-addr.arpa",
"registered_domain": "1.in-addr.arpa",
"subdomain": "113.0.0",
"top_level_domain": "in-addr.arpa",
"type": "IN"
},
"type": "query"
},
"related": {
"hosts": [
"113.0.0.1.in-addr.arpa"
],
"ip": [
"19e9:ae66:c43d:fc8:fcaf:df4a:2bd8:29ab"
]
},
"source": {
"address": "19e9:ae66:c43d:fc8:fcaf:df4a:2bd8:29ab",
"ip": "19e9:ae66:c43d:fc8:fcaf:df4a:2bd8:29ab",
"port": 53
}
}
{
"message": "client @0x12345678 1.2.3.4#52998 (id.test.fr): rpz QNAME PASSTHRU rewrite id.test.fr/A/IN via id.test.fr.0-1.wl.rpz",
"bind": {
"rpz": {
"action": "rewrite",
"policy": "QNAME PASSTHRU"
}
},
"dns": {
"question": {
"class": "A",
"name": "id.test.fr",
"registered_domain": "test.fr",
"subdomain": "id",
"top_level_domain": "fr",
"type": "IN"
},
"type": "query"
},
"related": {
"hosts": [
"id.test.fr"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 52998
}
}
{
"message": "client @0x12345678 1.2.3.4#49966 (test.com): rpz QNAME CNAME rewrite test.com/A/IN via test.com.badrep.host.dtq (CNAME to: badrep.host.dtq.rpz.portal.net.be.ch)",
"bind": {
"rpz": {
"action": "rewrite",
"policy": "QNAME CNAME"
}
},
"dns": {
"question": {
"class": "A",
"name": "test.com",
"registered_domain": "test.com",
"top_level_domain": "com",
"type": "IN"
},
"type": "query"
},
"related": {
"hosts": [
"test.com"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 49966
}
}
{
"message": "rpz: bad-nameservers.host.dtq: reload done: success",
"bind": {
"rpz": {
"action": "reload",
"name": "bad-nameservers.host.dtq",
"status": "done"
}
},
"dns": {
"type": "query"
}
}
{
"message": "rpz: bad-nameservers.host.dtq: reload start",
"bind": {
"rpz": {
"action": "reload",
"name": "bad-nameservers.host.dtq",
"status": "start"
}
},
"dns": {
"type": "query"
}
}
{
"message": "rpz: bad-nameservers.ip.dtq: new zone version came too soon, deferring update for 60 seconds",
"bind": {
"rpz": {
"name": "bad-nameservers.ip.dtq"
}
},
"dns": {
"type": "query"
},
"error": {
"message": "new zone version came too soon, deferring update for 60 seconds"
}
}
{
"message": "general: info: zone 10.in-addr.arpa/IN: Transfer started.",
"event": {
"reason": "Transfer started."
},
"bind": {
"rpz": {
"action": "transfer",
"name": "10.in-addr.arpa",
"status": "started",
"type": "IN"
}
},
"dns": {
"type": "query"
},
"log": {
"level": "info"
}
}
{
"message": "zone 10.in-addr.arpa/IN: Transfer started.",
"event": {
"reason": "Transfer started."
},
"bind": {
"rpz": {
"action": "transfer",
"name": "10.in-addr.arpa",
"status": "started",
"type": "IN"
}
},
"dns": {
"type": "query"
}
}
{
"message": "zone 10.in-addr.arpa/IN: sending notifies (serial 393191)",
"event": {
"reason": "sending notifies (serial 393191)"
},
"bind": {
"rpz": {
"name": "10.in-addr.arpa",
"type": "IN"
}
},
"dns": {
"type": "query"
}
}
{
"message": "zone 10.in-addr.arpa/IN: api.atlassian.com/A: bad owner name (check-names)",
"event": {
"reason": "bad owner name (check-names)"
},
"bind": {
"rpz": {
"name": "10.in-addr.arpa",
"type": "IN"
}
},
"dns": {
"question": {
"name": "api.atlassian.com",
"registered_domain": "atlassian.com",
"subdomain": "api",
"top_level_domain": "com",
"type": "A"
},
"type": "query"
},
"related": {
"hosts": [
"api.atlassian.com"
]
}
}
{
"message": "zone 10.in-addr.arpa/IN: transferred serial 273966: TSIG 'bern-key'",
"event": {
"reason": "transferred serial 273966: TSIG 'bern-key'"
},
"bind": {
"rpz": {
"action": "transfer",
"name": "10.in-addr.arpa",
"type": "IN"
}
},
"dns": {
"type": "query"
}
}
{
"message": "general: info: zone 10.in-addr.arpa/IN: refresh: retry limit for master 10.0.0.1#53 exceeded (source 0.0.0.0#0)",
"event": {
"reason": "retry limit for master 10.0.0.1#53 exceeded (source 0.0.0.0#0)"
},
"bind": {
"rpz": {
"action": "refresh",
"name": "10.in-addr.arpa",
"type": "IN"
}
},
"dns": {
"type": "query"
},
"log": {
"level": "info"
}
}
{
"message": "transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: Transfer completed: 0 messages, 26 records, 0 bytes, 0.001 secs (0 bytes/sec) (serial 393191)",
"bind": {
"rpz": {
"action": "transfer",
"name": "10.in-addr.arpa",
"status": "completed",
"type": "IN"
}
},
"dns": {
"type": "query"
},
"related": {
"ip": [
"10.0.0.1"
]
},
"source": {
"address": "10.0.0.1",
"ip": "10.0.0.1",
"port": 53
}
}
{
"message": "transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: Transfer status: IXFR failed",
"bind": {
"rpz": {
"action": "transfer",
"name": "10.in-addr.arpa",
"status": "IXFR failed",
"type": "IN"
}
},
"dns": {
"type": "query"
},
"related": {
"ip": [
"10.0.0.1"
]
},
"source": {
"address": "10.0.0.1",
"ip": "10.0.0.1",
"port": 53
}
}
{
"message": "transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: connected using 5.6.7.8#53",
"event": {
"reason": "connected using 5.6.7.8#53"
},
"bind": {
"rpz": {
"action": "transfer",
"name": "10.in-addr.arpa",
"type": "IN"
}
},
"dns": {
"type": "query"
},
"related": {
"ip": [
"10.0.0.1"
]
},
"source": {
"address": "10.0.0.1",
"ip": "10.0.0.1",
"port": 53
}
}
{
"message": "transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: failed while receiving responses: not exact",
"bind": {
"rpz": {
"action": "transfer",
"name": "10.in-addr.arpa",
"status": "failed",
"type": "IN"
}
},
"dns": {
"type": "query"
},
"error": {
"message": "failed while receiving responses"
},
"related": {
"ip": [
"10.0.0.1"
]
},
"source": {
"address": "10.0.0.1",
"ip": "10.0.0.1",
"port": 53
}
}
{
"message": "transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: Transfer status: success",
"bind": {
"rpz": {
"action": "transfer",
"name": "10.in-addr.arpa",
"status": "success",
"type": "IN"
}
},
"dns": {
"type": "query"
},
"related": {
"ip": [
"10.0.0.1"
]
},
"source": {
"address": "10.0.0.1",
"ip": "10.0.0.1",
"port": 53
}
}
{
"message": "xfer-in: error: transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: failed to connect: host unreachable",
"bind": {
"rpz": {
"action": "transfer",
"name": "10.in-addr.arpa",
"status": "failed",
"type": "IN"
}
},
"dns": {
"type": "query"
},
"error": {
"message": "failed to connect"
},
"log": {
"level": "error"
},
"related": {
"ip": [
"10.0.0.1"
]
},
"source": {
"address": "10.0.0.1",
"ip": "10.0.0.1",
"port": 53
}
}
{
"message": "xfer-in: info: transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: Transfer completed: 0 messages, 0 records, 0 bytes, 3.075 secs (0 bytes/sec)",
"bind": {
"rpz": {
"action": "transfer",
"name": "10.in-addr.arpa",
"status": "completed",
"type": "IN"
}
},
"dns": {
"type": "query"
},
"log": {
"level": "info"
},
"related": {
"ip": [
"10.0.0.1"
]
},
"source": {
"address": "10.0.0.1",
"ip": "10.0.0.1",
"port": 53
}
}
{
"message": "xfer-in: info: transfer of '10.in-addr.arpa/IN' from 10.0.0.1#53: Transfer status: host unreachable",
"bind": {
"rpz": {
"action": "transfer",
"name": "10.in-addr.arpa",
"status": "host unreachable",
"type": "IN"
}
},
"dns": {
"type": "query"
},
"log": {
"level": "info"
},
"related": {
"ip": [
"10.0.0.1"
]
},
"source": {
"address": "10.0.0.1",
"ip": "10.0.0.1",
"port": 53
}
}
{
"message": "general: info: zone 2.0.192.in-addr.arpa/IN/internal: serial number (1771420876) received from master 192.0.2.1#53 < ours (1772690752)",
"event": {
"reason": "serial number (1771420876) received from master 192.0.2.1#53 < ours (1772690752)"
},
"bind": {
"rpz": {
"name": "2.0.192.in-addr.arpa",
"type": "IN",
"view": "internal"
}
},
"dns": {
"type": "query"
},
"log": {
"level": "info"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
bind.rpz.action |
keyword |
The RPZ action that was applied to the DNS query. |
bind.rpz.name |
keyword |
The RPZ name that was applied to the DNS query. |
bind.rpz.policy |
keyword |
The RPZ policy that was applied to the DNS query. |
bind.rpz.status |
keyword |
The RPZ status that was applied to the DNS query. |
bind.rpz.type |
keyword |
The RPZ type that was queried. |
bind.rpz.view |
keyword |
The BIND view associated with the zone. |
dns.answers |
object |
Array of DNS answers. |
dns.header_flags |
keyword |
Array of DNS header flags. |
dns.question.class |
keyword |
The class of records being queried. |
dns.question.name |
keyword |
The name being queried. |
dns.question.type |
keyword |
The type of record being queried. |
dns.response_code |
keyword |
The DNS response code. |
dns.type |
keyword |
The type of DNS event captured, query or answer. |
error.message |
match_only_text |
Error message. |
event.reason |
keyword |
Reason why this event happened, according to the source |
log.level |
keyword |
Log level of the log event. |
network.transport |
keyword |
Protocol Name corresponding to the field iana_number. |
source.ip |
ip |
IP address of the source. |
source.port |
long |
Port of the source. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.