Citrix NetScaler / ADC
Overview
Citrix NetScaler / ADC (formerly Citrix NetScaler) is a delivery controller and load-balancing tool that offers enhanced security and application performance.
- Vendor: Citrix
- Supported environment: On Premise
- Detection based on: Telemetry, Alert, Audit
- Supported application or feature: Application Delivery and Security
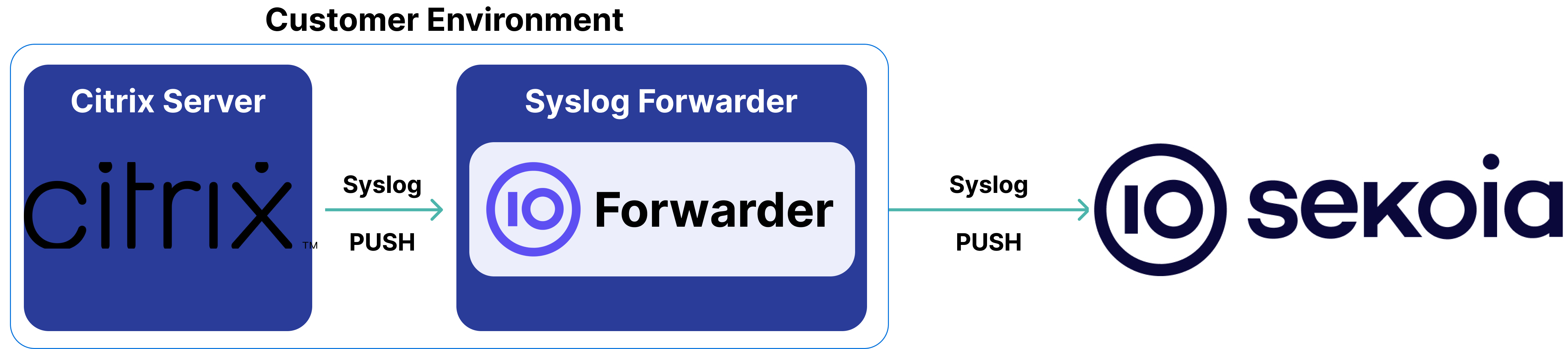
High-Level Architecture Diagram
- Type of integration: Outbound (PUSH to Sekoia.io)
- Schema
Specification
Prerequisites
- Resource:
- Self-managed syslog forwarder
- NSLog server with the syslog protocol
- Auditing module which runs on the NetScaler appliance
- Network:
- Outbound traffic allowed
- Permissions:
- Administrator or Root access to the Citrix NetScaler appliance
- Root access to the Linux server with the syslog forwarder
Transport Protocol/Method
- Indirect Syslog
Logs details
- Supported functionalities: See section Overview
- Supported type(s) of structure: CEF (traffic), Plain text (audit)
- Supported verbosity level: Alert, Warning, Informational
Note
Log levels are based on the taxonomy of RFC5424. Adapt according to the terminology used by the editor.
Step-by-Step Configuration Procedure
Instructions on the 3rd Party Solution
This setup guide will show you how to forward both your access and error logs to Sekoia.io by means of a syslog transport channel.
Forward Audit Logs
- Follow this guide to enable syslog forwarding for audit logs.
Important
Make sure -dateFormat MMDDYYYY is set and the date is present in logs.
Forward Application Firewall Logs
-
To enable application firewall logs forwarding, see this guide and apply the following command to convert Application Firewall logs into CEF events:
set appfw settings CEFLogging on
Important
Make sure to set the value of "Max Log Data Size To Hold" to 1000 to avoid logs to be truncated, as the default value is 500.
Instruction on Sekoia
Configure Your Intake
This section will guide you through creating the intake object in Sekoia, which provides a unique identifier called the "Intake key." The Intake key is essential for later configuration, as it references the Community, Entity, and Parser (Intake Format) used when receiving raw events on Sekoia.
- Go to the Sekoia Intake page.
- Click on the
+ New Intakebutton at the top right of the page. - Search for your Intake by the product name in the search bar.
- Give it a Name and associate it with an Entity (and a Community if using multi-tenant mode).
- Click on
Create.
Note
For more details on how to use the Intake page and to find the Intake key you just created, refer to this documentation.
Configure a forwarder
To forward events using syslog to Sekoia.io, you need to update the syslog header with the intake key you previously created. Here is an example of your message before the forwarder
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG RAW_MESSAGE
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG [SEKOIA@53288 intake_key=\"YOUR_INTAKE_KEY\"] RAW_MESSAGE
To achieve this you can:
- Use the Sekoia.io forwarder which is the official supported way to collect data using the syslog protocol in Sekoia.io. In charge of centralizing data coming from many equipments/sources and forwarding them to Sekoia.io with the apporpriated format, it is a prepackaged option. You only have to provide your intake key as parameter.
- Use your own Syslog service instance. Maybe you already have an intance of one of these components on your side and want to reuse it in order to centralize data before forwarding them to Sekoia.io. When using this mode, you have to configure and maintain your component in order to respect the expected Sekoia.io format.
Warning
Only the Sekoia.io forwarder is officially supported. Other options are documented for reference purposes but do not have official support.
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
01/24/2025:12:06:37 GMT NetscalerCD07_1 0-PPE-0 : default AAA LOGIN_FAILED 73912122 0 : User testUser - Client_ip 1.2.3.4 - Failure_reason "External authentication server denied access" - Browser Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/131.0.0.0 Safari/537.36
02/17/2025:07:32:36 GMT NetscalerCD07_2 0-PPE-0 : default AAA LOGIN_FAILED 14861134 0 : User john.doe - Client_ip 1.2.3.4 - Failure_reason "External authentication server denied access"
09/30/2025:11:55:37 0-PPE-0 : default AAA Message 207030 0 : "Authentication is rejected for johndoe (client ip : 1.2.3.4 , vserver ip: 5.6.7.8 ), extended error, if any : "
01/24/2025:12:19:12 GMT NetscalerCD07_1 0-PPE-0 : default AAATM Message 73920564 0 : "nFactor: SESS UPDATE: flags 40001, flags2 1f20000, flags3 40, flags4 0, message length 0, sess_req flags 40000"
08/26/2025:07:22:06 GMT ADC01 0-PPE-0 : default AAATM Message 19548406 0 : "ns_aaa_saml_parse_assertion: parsing the begg tag: AttributeValue>http://schemas.#012"
root on (null) shell_command="for pid in $PROF_PIDS; do kill -0 $pid > /dev/null 2>&1; if [ $? -ne 0 ]; then kill -9 $PROF_PIDS > /dev/null 2>&1; return; fi; done"
root on /dev/pts/0 shell_command="PATH=/netscaler:/bin:/sbin:/usr/bin:/usr/sbin:/usr/libexec:/usr/local/bin:/usr/local/sbin:."
CEF:0|Citrix|NetScaler|NS13.1|APPFW|APPFW_MULTIPLE_HEADER|6|src=1.2.3.4 geolocation=Unknown spt=61903 method=GET request=https://www.example.org/services msg=Multiple headers in request cn1=3755128 cn2=1636674 cs1=WAF_PRF_RULE1 cs2=PPE1 cs4=ALERT cs5=2023 act=blocked
01/28/2025:13:21:01 GMT DVPXLBLINT01 0-PPE-0 : default GUI CMD_EXECUTED 13034678 0 : User john-doe - ADM_User NONE - Remote_ip 1.2.3.4 - Command "show ssl profile integration_ssl_profile_frontend_test" - Status "Success"
default CMD_EXECUTED 500593 0 : User john.doe - ADM_User NONE - Remote_ip 1.2.3.4 - Command "logout" - Status "Success"
2023/07/04:09:03:46 ADC 0-PPE-2 : default TCP CONN_TERMINATE 4556618 0 : Source 1.2.3.4:443 - Destination 5.6.7.8:43566 - Start Time 2023/07/04:09:03:46 - End Time 2023/07/04:09:03:46 - Total_bytes_send 473 - Total_bytes_recv 1
2023/07/04:09:03:46 ADC 0-PPE-0 : default TCP CONN_TERMINATE 19695388 0 : Source 1.2.3.4:5557 - Destination 5.6.7.8:39654 - Start Time 2023/07/04:09:03:01 - End Time 2023/07/04:09:03:46 - Total_bytes_send 1 - Total_bytes_recv 1
2023/07/04:09:03:45 ADC 0-PPE-1 : default TCP CONN_DELINK 4356922 0 : Source 1.2.3.4:13788 - Vserver 192.168.152.11:443 - NatIP 4.3.2.1:3198 - Destination 5.6.7.8:443 - Delink Time 2023/07/04:09:03:45 - Total_bytes_send 0 - Total_bytes_recv 762
1.2.3.4 -> 5.6.7.8 "GET /test/v1/config/systemfile?REDACTED HTTP/1.1" 200 14794 "-" "Prometheus/2.30.0" "Time: 65590 microsecs"
1.2.3.4 -> 1.2.3.4 - - [10/Jun/2024:23:07:11 +0530] [1571] "GET /nitro/v1/config/route6?REDACTED HTTP/1.1" 200 1162 "-" "-" "Time: 9797 microsecs"
CEF:0|Citrix|NetScaler|NS13.1|APPFW|APPFW_POLICY_HIT|6|src=1.2.3.4 geolocation=Unknown spt=62919 method=GET request=https://www.example.org/services msg=Application Firewall profile invoked cn1=3864530 cn2=1644557 cs1=WAF_PRF_RULE1 cs2=PPE2 cs4=ALERT cs5=2023 act=not blocked
"2023/07/04:09:03:41 ADC 0-PPE-1 : default SNMP TRAP_SENT 0 0 : appfwPolicyHit (appfwLogMsg = ""CEF:0|Citrix|NetScaler|NS13.1|APPFW|APPFW_POLI..."", nsPartitionName = default)"
01/16/2025:15:22:40 NSMPXPHOENIX 0-PPE-4 : default SSLVPN Message 855350000 0 : "SSLVPN Mux Authorize result is Allow, Srcip: 1.2.3.4, Dstip: 5.6.7.8"
"2023/07/04:09:03:39 ADC 0-PPE-0 : default SSLLOG SSL_HANDSHAKE_SUCCESS 19695351 0 : SPCBId 1265452 - ClientIP 1.2.3.4 - ClientPort 50130 - VserverServiceIP 192.168.152.11 - VserverServicePort 443 - ClientVersion TLSv1.2 - CipherSuite ""TLS1.2-ECDHE-RSA-AES256-GCM-SHA384"" - Session New - HandshakeTime 27 ms"
"2023/07/04:09:03:46 ADC 0-PPE-0 : default SSLVPN Message 19695397 0 : ""SSLVPN Mux Authorize result is Deny, User <user1>, Srcip: 1.2.3.4, Dstip: 5.6.7.8, denied_by_policy: SESSPOL_VPN_Remoteadmin"""
"2023/07/04:09:03:39 ADC 0-PPE-0 : default SSLVPN NONHTTP_RESOURCEACCESS_DENIED 19695356 0 : Context user1@91.170.235.67 - SessionId: 1286 - User user1 - Client_ip 1.2.3.4 - Nat_ip 4.3.2.1 - Vserver 192.168.152.11:443 - Source 1.2.3.4:50130 - Destination 5.6.7.8:514 - Total_bytes_send 340 - Total_bytes_recv 0 - Denied_by_policy ""AUTHZ_DENY"" - Group(s) ""vpndsin,vpndsin"""
"12/07/2023:10:58:42 GMT CXA-GAT 0-PPE-0 : default SSLVPN Message 1521206 0 : "SSO ns_sslvpn_process_sso_conn: user john.doe@example.com clientip 1.2.3.4 request: /Citrix/CITRIXCGDWeb/clients/HTML5Client/resources/images/icon_clipboard.png sso_flags-0 p_flags-0 x_flags-200000 author_hdr_removed-0""
12/19/2024:10:37:23 GMT NetscalerCD07_1 0-PPE-0 : default SSLVPN LOGOUT 40895248 0 : Context testuser@1.2.3.4 - SessionId: 1096201 - User testuser - Client_ip 1.2.3.4 - Nat_ip "Mapped Ip" - Vserver 3.4.5.6:443 - Start_time "12/19/2024:10:16:43 GMT" - End_time "12/19/2024:10:37:23 GMT" - Duration 00:20:40 - Http_resources_accessed 0 - NonHttp_services_accessed 0 - Total_TCP_connections 46 - Total_UDP_flows 0 - Total_policies_allowed 46 - Total_policies_denied 0 - Total_bytes_send 0 - Total_bytes_recv 414177 - Total_compressedbytes_send 0 - Total_compressedbytes_recv 0 - Compression_ratio_send 0.00% - Compression_ratio_recv 0.00% - LogoutMethod "Explicit" - Group(s) "N/A"
12/19/2024:09:40:29 GMT NetscalerCD07_1 0-PPE-0 : default SSLVPN TCPCONNSTAT 40844824 0 : Context user1@1.2.3.4 - SessionId: 1096160 - User user1 - Client_ip 1.2.3.4 - Nat_ip 5.6.7.8 - Vserver 3.4.5.6:443 - Source 1.2.3.4:59549 - Destination 3.3.3.3:443 - Start_time "12/19/2024:09:40:29 GMT" - End_time "12/19/2024:09:40:29 GMT" - Duration 00:00:00 - Total_bytes_send 0 - Total_bytes_recv 51251 - Total_compressedbytes_send 0 - Total_compressedbytes_recv 0 - Compression_ratio_send 0.00% - Compression_ratio_recv 0.00% - Access Allowed - Group(s) "N/A"
12/19/2024:09:40:29 GMT NetscalerCD07_1 0-PPE-0 : default SSLVPN HTTPREQUEST 40844823 0 : Context user1@1.2.3.4 - SessionId: 1096160 - example.com User user1 : Group(s) N/A : Vserver 3.4.5.6:443 - 12/19/2024:09:40:29 GMT : SSO is ON : GET /ttt.jpg - -
08/13/2025:11:29:14 TEST01 0-PPE-1 : default SSLLOG SSL_HANDSHAKE_FAILURE 2037242 0 : SPCBId 55592 - ClientIP 1.2.3.4 - ClientPort 60892 - VserverServiceIP 3.4.5.6 - VserverServicePort 443 - ClientVersion TLSv1.2 - CipherSuite "TLS1-AES-256-CBC-SHA" - Session New - Reason "Fatal alert received"
13/08/2025:11:29:14 TEST01 0-PPE-1 : default SSLLOG SSL_HANDSHAKE_FAILURE 2037242 0 : SPCBId 55592 - ClientIP 1.2.3.4 - ClientPort 60892 - VserverServiceIP 2.3.4.5 - VserverServicePort 443 - ClientVersion TLSv1.2 - CipherSuite "TLS1-AES-256-CBC-SHA" - Session New - Reason "Fatal alert received"
01/28/2026:14:14:14 HOSTNAME 0-PPE-0 : default SSLVPN ICASTART 25487330 0 : [TECHSUPPORT][LAUNCH][TCP][CGP][ICAUUID=11111111111-11111-1111-1111-111111111] Source 2.2.2.2:49692 - Destination 1.1.1.1:2598 - customername - username:domainname user1:example - applicationName Application-Test $S3-56 - startTime "01/28/2026:14:14:13 " - connectionId 1111111
28/01/2026:14:14:14 HOSTNAME 0-PPE-0 : default SSLVPN ICASTART 25487330 0 : [TECHSUPPORT][LAUNCH][TCP][CGP][ICAUUID=11111111111-11111-1111-1111-111111111] Source 2.2.2.2:49692 - Destination 1.1.1.1:2598 - customername - username:domainname user1:example - applicationName Application-Test $S3-56 - startTime "28/01/2026:14:14:13 " - connectionId 1111111
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake Citrix NetScaler / ADC. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x Citrix NetScaler / ADC on ATT&CK Navigator
Account Added To A Security Enabled Group
Detection in order to investigate who has added a specific Domain User in Domain Admins or Group Policy Creator Owners (Security event 4728)
- Effort: master
Account Removed From A Security Enabled Group
Detection in order to investigate who has removed a specific Domain User in Domain Admins or Group Policy Creator Owners (Security event 4729)
- Effort: master
AdFind Usage
Detects the usage of the AdFind tool. AdFind.exe is a free tool that extracts information from Active Directory. Wizard Spider (Bazar, TrickBot, Ryuk), FIN6 and MAZE operators have used AdFind.exe to collect information about Active Directory organizational units and trust objects
- Effort: elementary
Address Space Layout Randomization (ASLR) Alteration
ASLR is a security feature used by the Operating System to mitigate memory exploit, attacker might want to disable it
- Effort: intermediate
Adexplorer Usage
Detects the usage of Adexplorer, a legitimate tool from the Sysinternals suite that could be abused by attackers as it can saves snapshots of the Active Directory Database.
- Effort: advanced
Adidnsdump Enumeration
Detects use of the tool adidnsdump for enumeration and discovering DNS records.
- Effort: advanced
Advanced IP Scanner
Detects the use of Advanced IP Scanner. Seems to be a popular tool for ransomware groups.
- Effort: master
Audio Capture via PowerShell
Detects audio capture via PowerShell Cmdlet
- Effort: intermediate
Autorun Keys Modification
Detects modification of autostart extensibility point (ASEP) in registry. Prerequisites are Logging for Registry events in the Sysmon configuration (events 12 and 13).
- Effort: master
AzureEdge in Command Line
Detects use of azureedge in the command line.
- Effort: advanced
BITSAdmin Download
Detects command to download file using BITSAdmin, a built-in tool in Windows. This technique is used by several threat actors to download scripts or payloads on infected system.
- Effort: advanced
Bazar Loader DGA (Domain Generation Algorithm)
Detects Bazar Loader domains based on the Bazar Loader DGA
- Effort: elementary
BazarLoader Persistence Using Schtasks
Detects possible BazarLoader persistence using schtasks. BazarLoader will create a Scheduled Task using a specific command line to establish its persistence.
- Effort: intermediate
Bloodhound and Sharphound Tools Usage
Detects default process names and default command line parameters used by Bloodhound and Sharphound tools.
- Effort: intermediate
Blue Mockingbird Malware
Attempts to detect system changes made by Blue Mockingbird
- Effort: elementary
Burp Suite Tool Detected
Burp Suite is a cybersecurity tool. When used as a proxy service, its purpose is to intercept packets and modify them to send them to the server. Burp Collaborator is a network service that Burp Suite uses to help discover many kinds of vulnerabilities (vulnerabilities scanner).
- Effort: intermediate
CVE-2018-11776 Apache Struts2
Apache Struts versions 2.3 to 2.3.34 and 2.5 to 2.5.16 suffer from possible Remote Code Execution when alwaysSelectFullNamespace is true (either by user or a plugin like Convention Plugin) and then: results are used with no namespace and in same time, its upper package have no or wildcard namespace and similar to results, same possibility when using url tag which doesn't have value and action set and in same time, its upper package have no or wildcard namespace.
- Effort: intermediate
CVE-2018-13379 Fortinet Exploit
Detects the successful exploitation of the Fortinet FortiOS CVE-2018-13379. This CVE is one of the most exploited CVEs since 2018. It is exploited by APT threat actors as well as cybercriminals. The exploitation of this CVE lead an unauthenticated user to get full access to FortiOS system file through SSL VPN via specially crafted HTTP resource requests. The exploit read /dev/cmdb/sslvpn_websession file, that contains login and passwords in (clear/text). An HTTP response status code = 200, means the file was successfully accessed. This vulnerability affects FortiOS 5.6.3 to 5.6.7 and FortiOS 6.0.0 to 6.0.4.
- Effort: advanced
CVE-2019-0604 SharePoint
Detects the exploitation of the SharePoint vulnerability (CVE-2019-0604).
- Effort: advanced
CVE-2019-11510 Pulse Secure Exploit
Detects the successful exploitation of the Pulse Secure vulnerability CVE-2019-11510. This CVE is one of the most exploited CVEs since 2019. It is exploited by diverse threat actors, leading sometimes in ransomware deployement among these groups: Maze, Conti, Egregor, DoppelPaymer, NetWalker and REvil. But also APT actors such as APT29. The exploitation of this CVE allows a remote, unauthenticated attacker to compromise a vulnerable VPN server. The attacker may be able to gain access to all active users and their plain-text credentials. It may also be possible for the attacker to execute arbitrary commands on each VPN client as it successfully connects to the VPN server. The exploit reads /etc/passwd file to get access to login and passwords in (clear/text). An HTTP response status code = 200, means the file was successfully accessed. This vulnerability affects 8.1R15.1, 8.2 before 8.2R12.1, 8.3 before 8.3R7.1, and 9.0 before 9.0R3.4 products.
- Effort: elementary
CVE-2019-19781 Citrix NetScaler (ADC)
Detects CVE-2019-19781 exploitation attempt against Citrix NetScaler (ADC), Application Delivery Controller and Citrix Gateway Attack.
- Effort: elementary
CVE-2019-2725 Oracle Weblogic Exploit
Detects the successful exploitation of a deserialization vulnerability in Oracle Weblogic Server, CVE-2019-2725. This vulnerability affects versions 10.X and 12.1.3 of WebLogic that have the components wls9_async_response.war and wls-wsat.war enabled. It is a remote code execution which can be exploited without authentication via HTTP. An HTTP response status code = 202, means the target is vulnerable, the analyst then has to look in depth to check if a webshell has been uploaded or something else has been done.
- Effort: elementary
CVE-2020-0688 Microsoft Exchange Server Exploit
Detects the exploitation of CVE-2020-0688. The POC exploit a .NET serialization vulnerability in the Exchange Control Panel (ECP) web page. The vulnerability is due to Microsoft Exchange Server not randomizing the keys on a per-installation basis resulting in them using the same validationKey and decryptionKey values. With knowledge of these, values an attacker can craft a special viewstate to use an OS command to be executed by NT_AUTHORITY\SYSTEM using .NET deserialization. To exploit this vulnerability, an attacker needs to leverage the credentials of an account it had already compromised to authenticate to OWA.
- Effort: elementary
CVE-2020-1147 SharePoint
Detection of SharePoint vulnerability CVE-2020-1147.
- Effort: advanced
CVE-2020-14882 Oracle WebLogic Server
Detects the exploitation of the Oracle WebLogic Server vulnerability (CVE-2020-16952).
- Effort: advanced
CVE-2020-17530 Apache Struts RCE
Detects the exploitation of the Apache Struts RCE vulnerability (CVE-2020-17530).
- Effort: intermediate
CVE-2020-5902 F5 BIG-IP Exploitation Attempts
Detects the exploitation attempt of the vulnerability found in F5 BIG-IP and described in CVE-2020-5902.
- Effort: elementary
CVE-2021-20021 SonicWall Unauthenticated Administrator Access
Detects the exploitation of SonicWall Unauthenticated Admin Access.
- Effort: advanced
CVE-2021-20023 SonicWall Arbitrary File Read
Detects Arbitrary File Read, which can be used with other vulnerabilities as a mean to obtain outputs generated by attackers, or sensitive data.
- Effort: advanced
CVE-2021-21972 VMware vCenter
The vSphere Client (HTML5) contains a remote code execution vulnerability in a vCenter Server plugin. A malicious actor with network access to port 443 may exploit this issue to execute commands with unrestricted privileges on the underlying operating system that hosts vCenter Server. This affects VMware vCenter Server (7.x before 7.0 U1c, 6.7 before 6.7 U3l and 6.5 before 6.5 U3n) and VMware Cloud Foundation (4.x before 4.2 and 3.x before 3.10.1.2). POST request on the following PATH "/ui/vropspluginui/rest/services/uploadova". If in response body (500) the words it has "uploadFile", that means the vCenter is available to accept files via POST without any restrictions.
- Effort: intermediate
CVE-2021-21985 VMware vCenter
The VMware vSphere Client (HTML5) contains a remote code execution vulnerability due to lack of input validation in the Virtual SAN Health Check plug-in which is enabled by default in vCenter Server. A malicious actor with network access to port 443 may exploit this issue to execute commands with unrestricted privileges on the underlying operating system that hosts vCenter Server. This affects VMware vCenter Server (7.0 before 7.0 U2b, 6.7 before 6.7 U3n and 6.5 before 6.5 U3p) and VMware Cloud Foundation (4.x before 4.2.1 and 3.x before 3.10.2.1).
- Effort: advanced
CVE-2021-22123 Fortinet FortiWeb OS Command Injection
Detects Fortinet FortiWeb OS Command Injection (August 2021) vulnerability exploitation attempt. A remote, authenticated attacker can execute arbitrary commands on the system hosting a vulnerable FortiWeb WAF by sending a POST request with the command in the name field. At the time of writing this rule, it would appear that the request would respond in code 500 for a successful exploitation attempt.
- Effort: advanced
CVE-2021-22893 Pulse Connect Secure RCE Vulnerability
Detects potential exploitation of the authentication by-pass vulnerability that can allow an unauthenticated user to perform remote arbitrary file execution on the Pulse Connect Secure gateway. It is highly recommended to apply the Pulse Secure mitigations and seach for indicators of compromise on affected servers if you are in doubt over the integrity of your Pulse Connect Secure product.
- Effort: intermediate
CVE-2021-26855 Exchange SSRF
Detects the exploitation of ProyxLogon vulerability on Exchange servers.
- Effort: advanced
CVE-2021-34473 ProxyShell Attempt
Detects CVE-2021-34473 ProxyShell attempt against Microsoft Exchange Server, Remote Code Execution Vulnerability.
- Effort: advanced
CVE-2021-41773 Apache 2.4.49 Path Traversal
Detects successful exploitation of the Apache Path Traversal CVE-2021-41773.
- Effort: advanced
CVE-2021-43798 Grafana Directory Traversal
Grafana version 8.x has a 0day arbitrary file read (with no fix yet) based on a directory traversal vulnerability
- Effort: intermediate
CertOC Loading Dll
Detects when a user installs certificates by using CertOC.exe to loads the target DLL file.
- Effort: intermediate
Certificate Authority Modification
Installation of new certificate(s) in the Certificate Authority can be used to trick user when spoofing website or to add trusted destinations.
- Effort: master
Certify Or Certipy
Detects the use of certify and certipy which are two different tools used to enumerate and abuse Active Directory Certificate Services.
- Effort: advanced
Change Default File Association
When a file is opened, the default program used to open the file (also called the file association or handler) is checked. File association selections are stored in the Windows Registry and can be edited by users, administrators, or programs that have Registry access or by administrators using the built-in assoc utility. Applications can modify the file association for a given file extension to call an arbitrary program when a file with the given extension is opened.
- Effort: advanced
Citrix NetScaler (ADC) Actions Blocked
This rule aims to detect a large amount of actions blocked performed from the same source.
- Effort: advanced
Clear EventLogs Through CommandLine
Detects a command that clears event logs which could indicate an attempt from an attacker to erase its previous traces.
- Effort: intermediate
Commonly Used Commands To Stop Services And Remove Backups
Detects specific commands used regularly by ransomwares to stop services or remove backups
- Effort: master
Component Object Model Hijacking
Detects component object model hijacking. An attacker can establish persistence with COM objects.
- Effort: advanced
Compression Followed By Suppression
Detects when a file is compressed and deleted.
- Effort: advanced
Computer Account Deleted
Detects computer account deletion.
- Effort: master
Container Credential Access
Adversaries could abuse containers tools to obtain credential like Kubernetes secret or Kubernetes service account access token
- Effort: intermediate
Control Panel Items
Detects the malicious use of a control panel item
- Effort: advanced
Copy Of Legitimate System32 Executable
A script has copied a System32 executable.
- Effort: intermediate
Copying Browser Files With Credentials
Detects copy of sensitive data (passwords, cookies, credit cards) included in web browsers files.
- Effort: elementary
Covenant Default HTTP Beaconing
Detects potential Covenant communications through the user-agent and specific urls
- Effort: intermediate
Cryptomining
Detection of domain names potentially related to cryptomining activities.
- Effort: master
DHCP Callout DLL Installation
Detects the installation of a Callout DLL via CalloutDlls and CalloutEnabled parameter in Registry, which can be used to execute code in context of the DHCP server (restart required).
- Effort: intermediate
DNS Exfiltration and Tunneling Tools Execution
Well-known DNS exfiltration tools execution
- Effort: intermediate
DNS Query For Iplookup
Detects dns query of observables tagged as iplookup.
- Effort: master
DNS ServerLevelPluginDll Installation
Detects the installation of a plugin DLL via ServerLevelPluginDll parameter in Windows Registry or in command line, which can be used to execute code in context of the DNS server (restart required). To fully use this rule, prerequesites are logging for Registry events in the Sysmon configuration (events 12, 13 and 14).
- Effort: master
Data Compressed With Rar With Password
An adversary may compress data in order to make it portable and minimize the amount of data sent over the network, this could be done the popular rar command line program. This is a more specific one for rar where the arguments allow to encrypt both file data and headers with a given password.
- Effort: intermediate
Debugging Software Deactivation
Deactivation of some debugging softwares using taskkill command. It was observed being used by Ransomware operators.
- Effort: elementary
Default Encoding To UTF-8 PowerShell
Detects PowerShell encoding to UTF-8, which is used by Sliver implants. The command line just sets the default encoding to UTF-8 in PowerShell.
- Effort: advanced
Detect requests to Konni C2 servers
This rule detects requests to Konni C2 servers. These patterns come from an analysis done in 2022, September.
- Effort: elementary
Disable .NET ETW Through COMPlus_ETWEnabled
Detects potential adversaries stopping ETW providers recording loaded .NET assemblies. Prerequisites are logging for Registry events or logging command line parameters (both is better). Careful for registry events, if SwiftOnSecurity's SYSMON default configuration is used, you will need to update the configuration to include the .NETFramework registry key path. Same issue with Windows 4657 EventID logging, the registry path must be specified.
- Effort: intermediate
Disable Task Manager Through Registry Key
Detects commands used to disable the Windows Task Manager by modifying the proper registry key in order to impair security tools. This technique is used by the Agent Tesla RAT, among others.
- Effort: elementary
Disabled IE Security Features
Detects from the command lines or the registry, changes that indicate unwanted modifications to registry keys that disable important Internet Explorer security features. This has been used by attackers during Operation Ke3chang.
- Effort: advanced
Discord Suspicious Download
Discord is a messaging application. It allows users to create their own communities to share messages and attachments. Those attachments have little to no overview and can be downloaded by almost anyone, which has been abused by attackers to host malicious payloads.
- Effort: advanced
Domain Trust Created Or Removed
A trust was created or removed to a domain. An attacker could perform that in order to do lateral movement easily between domains or shutdown the ability of two domains to communicate.
- Effort: advanced
Domain Trust Discovery Through LDAP
Detects attempts to gather information on domain trust relationships that may be used to identify lateral movement opportunities. "trustedDomain" which is detected here is a Microsoft Active Directory ObjectClass Type that represents a domain that is trusted by, or trusting, the local AD DOMAIN. Several tools are using LDAP queries in the end to get the information (DSQuery, sometimes ADFind as well, etc.)
- Effort: elementary
Download Files From Suspicious TLDs
Detects download of certain file types from hosts in suspicious TLDs
- Effort: master
Dynamic DNS Contacted
Detect communication with dynamic dns domain. This kind of domain is often used by attackers. This rule can trigger false positive in non-controlled environment because dynamic dns is not always malicious.
- Effort: master
Dynamic Linker Hijacking From Environment Variable
LD_PRELOAD and LD_LIBRARY_PATH are environment variables used by the Operating System at the runtime to load shared objects (library.ies) when executing a new process, attacker can overwrite this variable to attempts a privileges escalation.
- Effort: master
ETW Tampering
Detects a command that clears or disables any ETW Trace log which could indicate a logging evasion
- Effort: intermediate
Equation Group DLL_U Load
Detects a specific tool and export used by EquationGroup
- Effort: elementary
EvilProxy Phishing Domain
Detects subdomains potentially generated by the EvilProxy adversary-in-the-middle phishing platform. Inspect the other subdomains of the domain to identify the landing page, and determine if the user submitted credentials. This rule has a small percentage of false positives on legitimate domains.
- Effort: intermediate
Exfiltration Domain
Detects traffic toward a domain flagged as a possible exfiltration vector.
- Effort: master
Exfiltration Domain In Command Line
Detects commands containing a domain linked to http exfiltration.
- Effort: intermediate
FoggyWeb HTTP Default GET/POST Requests
Detects GET or POST request pattern observed within the first FoggyWeb campaign detected by Microsoft.
- Effort: advanced
FromBase64String Command Line
Detects suspicious FromBase64String expressions in command line arguments.
- Effort: master
GitLab CVE-2021-22205
Detects GitLab vulnerability CVE-2021-22205 exploitation success. It allows an attacker to do some remote code execution with user git. The HTTP return code 422 indicates a successfull exploitation.
- Effort: intermediate
HackTools Suspicious Process Names In Command Line
Detects the default process name of several HackTools and also check in command line. This rule is here for quickwins as it obviously has many blind spots.
- Effort: intermediate
High Privileges Network Share Removal
Detects high privileges shares being deleted with the net share command.
- Effort: intermediate
ICacls Granting Access To All
Detects suspicious icacls command granting access to all, used by the ransomware Ryuk to delete every access-based restrictions on files and directories. ICacls is a built-in Windows command to interact with the Discretionary Access Control Lists (DACLs) which can grand adversaries higher permissions on specific files and folders.
- Effort: elementary
Inhibit System Recovery Deleting Backups
Detects adversaries attempts to delete backups or inhibit system recovery. This rule relies on differents known techniques using Windows events logs from Sysmon (ID 1), and PowerShell (ID 4103, 4104).
- Effort: intermediate
Invoke-TheHash Commandlets
Detects suspicious Invoke-TheHash PowerShell commandlet used for performing pass the hash WMI and SMB tasks.
- Effort: elementary
KeePass Config XML In Command-Line
Detects a command-line interaction with the KeePass Config XML file. It could be used to retrieve informations or to be abused for persistence.
- Effort: intermediate
Koadic MSHTML Command
Detects Koadic payload using MSHTML module
- Effort: intermediate
Lazarus Loaders
Detects different loaders used by the Lazarus Group APT
- Effort: elementary
Leviathan Registry Key Activity
Detects registry key used by Leviathan APT in Malaysian focused campaign.
- Effort: elementary
Linux Bash Reverse Shell
To bypass some security equipement or for a sack of simplicity attackers can open raw reverse shell using shell commands
- Effort: intermediate
Linux Shared Lib Injection Via Ldso Preload
Detect ld.so.preload modification for shared lib injection, technique used by attackers to load arbitrary code into process
- Effort: intermediate
Listing Systemd Environment
Detects a listing of systemd environment variables. This command could be used to do reconnaissance on a compromised host.
- Effort: advanced
Logon Scripts (UserInitMprLogonScript)
Detects creation or execution of UserInitMprLogonScript persistence method. The rule requires to log for process command lines and registry creations or update, which can be done using Sysmon Event IDs 1, 12, 13 and 14.
- Effort: advanced
LokiBot Default C2 URL
Detects default C2 URL for trojan LokiBot
- Effort: elementary
Malicious Browser Extensions
Detects browser extensions being loaded with the --load-extension and -base-url options, which works on Chromium-based browsers. We are looking for potentially malicious browser extensions. These extensions can get access to informations.
- Effort: advanced
Malspam Execution Registering Malicious DLL
Detects the creation of a file in the C:\Datop folder, or DLL registering a file in the C:\Datop folder. Files located in the Datop folder are very characteristic of malspam execution related to Qakbot or SquirrelWaffle. Prerequisites are Logging for File Creation events, which can be done in the Sysmon configuration (events 11), for the first part of the pattern (TargetFilename).
- Effort: elementary
Malware Persistence Registry Key
Detects registry key used by several malware, especially Formbook spyware in two ways, either the Sysmon registry events, or the commands line.
- Effort: master
MalwareBytes Uninstallation
Detects command line being used by attackers to uninstall Malwarebytes.
- Effort: intermediate
MavInject Process Injection
Detects process injection using the signed Windows tool Mavinject32.exe (which is a LOLBAS)
- Effort: intermediate
Microsoft Defender Antivirus Disable Services
The rule detects attempts to deactivate/disable Windows Defender through command line and registry.
- Effort: intermediate
Microsoft Defender Antivirus Disable Using Registry
The rule detects attempts to deactivate/disable Microsoft Defender Antivirus using registry modification via command line or PowerShell scripts.
- Effort: master
Microsoft Defender Antivirus Disabled Base64 Encoded
Detects attempts to deactivate/disable Windows Defender through base64 encoded PowerShell command line or scripts.
- Effort: intermediate
Microsoft Defender Antivirus History Directory Deleted
Windows Defender history directory has been deleted. This could be an attempt by an attacker to remove its traces.
- Effort: elementary
Microsoft Defender Antivirus Restoration Abuse
The rule detects attempts to abuse Windows Defender file restoration tool. The Windows Defender process is allowed to write files in its own protected directory. This functionality can be used by a threat actor to overwrite Windows Defender files in order to prevent it from running correctly or use Windows Defender to execute a malicious DLL.
- Effort: intermediate
Microsoft Defender Antivirus Set-MpPreference Base64 Encoded
Detects changes of preferences for Windows Defender through command line or PowerShell scripts. Configure Windows Defender using base64-encoded commands is suspicious and could be related to malicious activities.
- Effort: intermediate
Microsoft Defender Antivirus Signatures Removed With MpCmdRun
Detects attempts to remove Windows Defender Signatures using MpCmdRun legitimate Windows Defender executable. No signatures mean Windows Defender will be less effective (or completely useless depending on the option used).
- Effort: elementary
Microsoft Exchange PowerShell Snap-Ins To Export Exchange Mailbox Data
Detects PowerShell SnapIn command line or PowerShell script, often used with Get-Mailbox to export Exchange mailbox data.
- Effort: intermediate
Microsoft Office Macro Security Registry Modifications
Detects registry changes allowing an attacker to make Microsoft Office products runs Macros without warning. Events are collected either from ETW/Sysmon/EDR depending of the integration.
- Effort: master
Mimikatz Basic Commands
Detects Mimikatz most popular commands.
- Effort: elementary
Msdt (Follina) File Browse Process Execution
Detects various Follina vulnerability exploitation techniques. This is based on the Compatability Troubleshooter which is abused to do code execution.
- Effort: elementary
Mustang Panda Dropper
Detects specific process parameters as used by Mustang Panda droppers
- Effort: elementary
NTDS.dit File Interaction Through Command Line
Detects interaction with the file NTDS.dit through command line. This is usually really suspicious and could indicate an attacker trying copy the file to then look for users password hashes.
- Effort: intermediate
NetSh Used To Disable Windows Firewall
Detects NetSh commands used to disable the Windows Firewall
- Effort: advanced
Netsh Allowed Python Program
Detects netsh command that performs modification on Firewall rules to allow the program python.exe. This activity is most likely related to the deployment of a Python server or an application that needs to communicate over a network. Threat actors could use it for data extraction, hosting a webshell or else.
- Effort: intermediate
Netsh Port Forwarding
Detects netsh commands that enable a port forwarding between to hosts. This can be used by attackers to tunnel RDP or SMB shares for example.
- Effort: intermediate
Netsh RDP Port Forwarding
Detects netsh commands that configure a port forwarding of port 3389 used for RDP. This is commonly used by attackers during lateralization on windows environments.
- Effort: elementary
New DLL Added To AppCertDlls Registry Key
Dynamic-link libraries (DLLs) that are specified in the AppCertDLLs value in the Registry key can be abused to obtain persistence and privilege escalation by causing a malicious DLL to be loaded and run in the context of separate processes on the computer. Logging for Registry events is needed in the Sysmon configuration (events 12 and 13).
- Effort: intermediate
Ngrok Process Execution
Detects possible Ngrok execution, which can be used by attacker for RDP tunneling.
- Effort: intermediate
Nimbo-C2 User Agent
Nimbo-C2 Uses an unusual User-Agent format in its implants.
- Effort: intermediate
NjRat Registry Changes
Detects changes for the RUN registry key which happen when a victim is infected by NjRAT. Please note that even if NjRat is well-known for the behavior the rule catches, the rule is a bit larger and could catch other malwares.
- Effort: master
Njrat Registry Values
Detects specifis registry values that are related to njRat usage.
- Effort: intermediate
NlTest Usage
Detects attempts to gather information on domain trust relationships that may be used to identify lateral movement opportunities. These command lines were observed in numerous attacks, but also sometimes from legitimate administrators for debugging purposes. The rule does not cover very basics commands but rather the ones that are interesting for attackers to gather information on a domain.
- Effort: advanced
Non-Legitimate Executable Using AcceptEula Parameter
Detects accepteula in command line with non-legitimate executable name. Some attackers are masquerading SysInternals tools with decoy names to prevent detection.
- Effort: advanced
Office Application Startup Office Test
Detects the addition of office test registry that allows a user to specify an arbitrary DLL that will be executed everytime an Office application is started. An adversaries may abuse the Microsoft Office "Office Test" Registry key to obtain persistence on a compromised system.
- Effort: elementary
Outlook Registry Access
Detection of accesses to Microsoft Outlook registry hive, which might contain sensitive information.
- Effort: master
Pandemic Windows Implant
Detects Pandemic Windows Implant through registry keys or specific command lines. Prerequisites: Logging for Registry events is needed, which can be done in the Sysmon configuration (events 12 and 13).
- Effort: master
Password Change On Directory Service Restore Mode (DSRM) Account
The Directory Service Restore Mode (DSRM) account is a local administrator account on Domain Controllers. Attackers may change the password to gain persistence.
- Effort: intermediate
Phorpiex DriveMgr Command
Detects specific command used by the Phorpiex botnet to execute a copy of the loader during its self-spreading stage. As described by Microsoft, this behavior is unique and easily identifiable due to the use of folders named with underscores "__" and the PE name "DriveMgr.exe".
- Effort: elementary
Possible Malicious File Double Extension
Detects request to potential malicious file with double extension
- Effort: elementary
Possible Replay Attack
This event can be a sign of Kerberos replay attack or, among other things, network device configuration or routing problems.
- Effort: master
Potential Azure AD Phishing Page (Adversary-in-the-Middle)
Detects an HTTP request to an URL typical of the Azure AD authentication flow, but towards a domain that is not one the legitimate Microsoft domains used for Azure AD authentication.
- Effort: intermediate
Potential Bazar Loader User-Agents
Detects potential Bazar loader communications through the user-agent
- Effort: elementary
Potential Lemon Duck User-Agent
Detects LemonDuck user agent. The format used two sets of alphabetical characters separated by dashes, for example "User-Agent: Lemon-Duck-[A-Z]-[A-Z]".
- Effort: elementary
Potential LokiBot User-Agent
Detects potential LokiBot communications through the user-agent
- Effort: intermediate
PowerCat Function Loading
Detect a basic execution of PowerCat. PowerCat is a PowerShell function allowing to do basic connections, file transfer, shells, relays, generate payloads.
- Effort: intermediate
PowerShell AMSI Deactivation Bypass Using .NET Reflection
Detects Request to amsiInitFailed that can be used to disable AMSI (Antimalware Scan Interface) Scanning. More information about Antimalware Scan Interface https://docs.microsoft.com/en-us/windows/win32/amsi/antimalware-scan-interface-portal.
- Effort: advanced
PowerShell Commands Invocation
Detects the execution to invoke a powershell command. This was used in an intrusion using Gootloader to access Mimikatz.
- Effort: advanced
PowerShell Data Compressed
Detects data compression through a PowerShell command (could be used by an adversary for exfiltration).
- Effort: advanced
PowerShell EncodedCommand
Detects popular file extensions in commands obfuscated in base64 run through the EncodedCommand option.
- Effort: advanced
PowerShell Invoke Expression With Registry
Detects keywords from well-known PowerShell techniques to get registry key values
- Effort: advanced
PowerView commandlets 1
Detects PowerView commandlets which perform network and Windows domain enumeration and exploitation. It provides replaces for almost all Windows net commands, letting you query users, machines, domain controllers, user descriptions, share, sessions, and more.
- Effort: advanced
PowerView commandlets 2
Detects PowerView commandlets which perform network and Windows domain enumeration and exploitation. It provides replaces for almost all Windows net commands, letting you query users, machines, domain controllers, user descriptions, share, sessions, and more.
- Effort: master
Powershell AMSI Bypass
This rule aims to detect attempts to bypass AMSI in powershell using specific techniques.
- Effort: advanced
Powershell UploadString Function
Powershell's uploadXXX functions are a category of methods which can be used to exfiltrate data through native means on a Windows host.
- Effort: advanced
Powershell Web Request And Windows Script
Detects the use of PowerShell web request method combined with Windows Script utilities. This has been observed being used by some malware loaders.
- Effort: intermediate
Privilege Escalation Awesome Scripts (PEAS)
Detect PEAS privileges escalation scripts and binaries
- Effort: elementary
Process Memory Dump Using Comsvcs
Detects the use of comsvcs in command line to dump a specific process memory. This technique is used by attackers for privilege escalation and pivot.
- Effort: intermediate
Process Memory Dump Using Rdrleakdiag
Detects the use of rdrleakdiag.exe in command line to dump the memory of a process. This technique is used by attackers for privilege escalation and pivot.
- Effort: elementary
Process Trace Alteration
PTrace syscall provides a means by which one process ("tracer") may observe and control the execution of another process ("tracee") and examine and change the tracee's memory and registers. Attacker might want to abuse ptrace functionnality to analyse memory process. It requires to be admin or set ptrace_scope to 0 to allow all user to trace any process.
- Effort: advanced
ProxyShell Microsoft Exchange Suspicious Paths
Detects suspicious calls to Microsoft Exchange resources, in locations related to webshells observed in campaigns using this vulnerability.
- Effort: elementary
PsExec Process
Detects PsExec execution, command line which contains pstools or installation of the PsExec service. PsExec is a SysInternals which can be used to execute a program on another computer. The tool is as much used by attackers as by administrators.
- Effort: advanced
Putty Sessions Listing
Detects attempts to list Putty sessions through registry. To fully work, this rule requires to log registry accesses, which can be done with the Windows Event ID 4656 or 4663 but for that specific configuration is needed.
- Effort: master
Python HTTP Server
Detects command used to start a Simple HTTP server in Python. Threat actors could use it for data extraction, hosting a webshell or else.
- Effort: intermediate
QakBot Process Creation
Detects QakBot like process executions
- Effort: intermediate
Qakbot Persistence Using Schtasks
Detects possible Qakbot persistence using schtasks.
- Effort: intermediate
Raccine Uninstall
Detects commands that indicate a Raccine removal from an end system. Raccine is a free ransomware protection tool.
- Effort: elementary
Raccoon Stealer 2.0 Legitimate Third-Party DLL Download URL
Detects Raccoon Stealer 2.0 malware downloading legitimate third-party DLLs from its C2 server. These legitimate DLLs are used by the information stealer to collect data on the compromised hosts.
- Effort: elementary
Rclone Process
Detects Rclone executable or Rclone execution by using the process name, the execution through a command obfuscated or not.
- Effort: advanced
RedMimicry Winnti Playbook Registry Manipulation
Detects actions caused by the RedMimicry Winnti playbook. Logging for Registry events is needed in the Sysmon configuration (events 12 and 13).
- Effort: elementary
Remote Access Tool Domain
Detects traffic toward a domain flagged as a Remote Administration Tool (RAT).
- Effort: master
Remote Monitoring and Management Software - AnyDesk
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool AnyDesk.
- Effort: master
Rubeus Tool Command-line
Detects command line parameters used by Rubeus, a toolset to interact with Kerberos and abuse it.
- Effort: advanced
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
SOCKS Tunneling Tool
Detects the usage of a SOCKS tunneling tool, often used by threat actors. These tools often use the socks5 commandline argument, however socks4 can sometimes be used as well. Unfortunately, socks alone (without any number) triggered too many false positives.
- Effort: intermediate
SSH Reverse Socks
Detects the usage of the -R option combined with StrictHostKeyChecking, which is an indication of using SSH for reverse socks.
- Effort: intermediate
Sekoia.io EICAR Detection
Detects observables in Sekoia.io CTI tagged as EICAR, which are fake samples meant to test detection.
- Effort: master
SharePoint Authenticated SSRF
Detects succesful SSRF from an authenticated SharePoint user.
- Effort: elementary
Socat Relaying Socket
Socat is a linux tool used to relay local socket or internal network connection, this technics is often used by attacker to bypass security equipment such as firewall
- Effort: advanced
Socat Reverse Shell Detection
Socat is a linux tool used to relay or open reverse shell that is often used by attacker to bypass security equipment.
- Effort: elementary
Spyware Persistence Using Schtasks
Detects possible Agent Tesla or Formbook persistence using schtasks. The name of the scheduled task used by these malware is very specific (Updates/randomstring).
- Effort: intermediate
Startup Item Created
Detects when a item is added to the startup directory. An attacker can use this establish persistence.
- Effort: intermediate
Stop Backup Services
Detects adversaries attempts to stop backups services or disable Windows previous files versions feature. This could be related to ransomware operators or legit administrators. This rule relies Windows command line logging and registry logging, and PowerShell (ID 4103, 4104).
- Effort: master
Suncrypt Parameters
Detects SunCrypt ransomware's parameters, most of which are unique.
- Effort: elementary
Suspicious Cmd File Copy Command To Network Share
Copy suspicious files through Windows cmd prompt to network share
- Effort: intermediate
Suspicious Cmd.exe Command Line
Detection on suspicious cmd.exe command line seen being used by some attackers (e.g. Lazarus with Word macros). This requires Windows process command line logging.
- Effort: master
Suspicious CommandLine Lsassy Pattern
Detects the characteristic lsassy loop used to identify lsass PIDs
- Effort: intermediate
Suspicious DLL Loading By Ordinal
Detects suspicious DLL Loading by ordinal number in a non legitimate or rare folders. For example, Sofacy (APT28) used this technique to load their Trojan in a campaign of 2018.
- Effort: intermediate
Suspicious Desktopimgdownldr Execution
Detects a suspicious Desktopimgdownldr execution. Desktopimgdownldr.exe is a Windows binary used to configure lockscreen/desktop image and can be abused to download malicious file.
- Effort: intermediate
Suspicious Download Links From Legitimate Services
Detects users clicking on Google docs links to download suspicious files. This technique was used a lot by Bazar Loader in the past.
- Effort: intermediate
Suspicious Microsoft Defender Antivirus Exclusion Command
Detects PowerShell commands aiming to exclude path, process, IP address, or extension from scheduled and real-time scanning. These commands can be used by attackers or malware to avoid being detected by Windows Defender. Depending on the environment and the installed software, this detection rule could raise false positives. We recommend customizing this rule by filtering legitimate processes that use Windows Defender exclusion command in your environment.
- Effort: master
Suspicious Netsh DLL Persistence
Detects persitence via netsh helper. Netsh interacts with other operating system components using dynamic-link library (DLL) files. Adversaries may establish persistence by executing malicious content triggered by Netsh Helper DLLs.
- Effort: elementary
Suspicious PowerShell Invocations - Generic
Detects suspicious PowerShell invocation command parameters through command line logging or ScriptBlock Logging.
- Effort: advanced
Suspicious PowerShell Invocations - Specific
Detects suspicious PowerShell invocation command parameters.
- Effort: intermediate
Suspicious PowerShell Keywords
Detects keywords that could indicate the use of some PowerShell exploitation framework.
- Effort: advanced
Suspicious PrinterPorts Creation (CVE-2020-1048)
Detects new commands that add new printer port which point to suspicious file
- Effort: advanced
Suspicious Rundll32.exe Executions
The process rundll32.exe executes a newly dropped DLL with update /i in the command line. This specific technic was observed at least being used by the IcedID loading mechanism dubbed Gziploader. Some other detections are related to LOLBAS (Living Off The Land Binaries, Scripts and Libraries) usages (like the COM registering).
- Effort: intermediate
Suspicious TOR Gateway
Detects suspicious TOR gateways. Gateways are often used by the victim to pay and decrypt the encrypted files without installing TOR. Tor intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: advanced
Suspicious Taskkill Command
Detects rare taskkill command being used. It could be related to Baby Shark malware.
- Effort: intermediate
Suspicious URI Used In A Lazarus Campaign
Detects suspicious requests to a specific URI, usually on an .asp page. The website is often compromised.
- Effort: intermediate
Suspicious Windows Installer Execution
Detects suspicious execution of the Windows Installer service (msiexec.exe) which could be used to install a malicious MSI package hosted on a remote server.
- Effort: master
Suspicious certutil command
Detects suspicious certutil command which can be used by threat actors to download and/or decode payload.
- Effort: intermediate
TOR Usage Generic Rule
Detects TOR usage globally, whether the IP is a destination or source. TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
Tactical RMM Installation
Detection of common Tactical RMM installation arguments that could be abused by some attackers.
- Effort: elementary
Tmutil Delete Backups
Detects when the utility tmutil is used to delete backups. The Time Machine utility is used to restore data from backups, add or remove exclusions, and compare backups.
- Effort: elementary
Tmutil Disabled
Detects when the utility tmutil is disabled. The Time Machine utility is used to restore data from backups, add or remove exclusions, and compare backups.
- Effort: elementary
Tmutil Exclude File From Backups
Detects when the utility tmutil is used to exclude paths from backups.
- Effort: master
TrevorC2 HTTP Communication
Detects TrevorC2 HTTP communication based on the HTTP request URI and the user-agent.
- Effort: elementary
UAC Bypass Via Sdclt
Detects changes to HKCU\Software\Classes\exefile\shell\runas\command\isolatedCommand by an attacker in order to bypass User Account Control (UAC)
- Effort: elementary
Usage Of Procdump With Common Arguments
Detects the usage of Procdump sysinternals tool with some common arguments and followed by common patterns.
- Effort: advanced
Usage Of Sysinternals Tools
Detects the usage of Sysinternals Tools due to accepteula key being added to Registry. The rule detects it either from the command line usage or from the regsitry events. For the later prerequisite is logging for registry events in the Sysmon configuration (events 12 and 13).
- Effort: master
User Account Created
Detects user creation on windows servers, which shouldn't happen in an Active Directory environment. Apply this on your windows server logs and not on your DC logs. One default account defaultuser0 is excluded as only used during Windows set-up. This detection use Security Event ID 4720.
- Effort: master
User Account Deleted
Detects local user deletion
- Effort: master
Venom Multi-hop Proxy agent detection
Detects Venom Multi-hop Proxy agent.
- Effort: intermediate
WMI Install Of Binary
Detection of WMI used to install a binary on the host. It is often used by attackers as a signed binary to infect an host.
- Effort: elementary
WMIC Command To Determine The Antivirus
Detects WMIC command to determine the antivirus on a system, characteristic of the ZLoader malware (and possibly others)
- Effort: advanced
WMIC Uninstall Product
Detects products being uninstalled using WMIC command.
- Effort: intermediate
WMImplant Hack Tool
WMImplant is a powershell framework used by attacker for reconnaissance and exfiltration, this rule attempts to detect WMimplant arguments and invokes commands.
- Effort: advanced
Wdigest Enable UseLogonCredential
Detects modification of the Windows Registry value of HKLM\SYSTEM\CurrentControlSet\Control\SecurityProviders\WDigest\UseLogonCredential. This technique is used to extract passwords in clear-text using WDigest. The rule requires to log for Registry Events, which can be done using Sysmon Event IDs 12, 13 and 14.
- Effort: elementary
WiFi Credentials Harvesting Using Netsh
Detects the harvesting of WiFi credentials using netsh.exe.
- Effort: advanced
Windows Defender Logging Modification Via Registry
Detects when the logging for defender is disabled in the registry.
- Effort: elementary
Windows Firewall Changes
Detects changes on Windows Firewall configuration
- Effort: master
Windows Registry Persistence COM Key Linking
Detects COM object hijacking via TreatAs subkey. Logging for Registry events is needed in the Sysmon configuration with this kind of rule <TargetObject name="testr12" condition="end with">\TreatAs\(Default)</TargetObject>.
- Effort: master
Windows Sandbox Start
Detection of Windows Sandbox started from the command line with a config file or interactively using a WSB file.
- Effort: master
Wmic Process Call Creation
The WMI command-line (WMIC) utility provides a command-line interface for Windows Management Instrumentation (WMI). WMIC is compatible with existing shells and utility commands. Although WMI is supposed to be an administration tool, it is wildy abused by threat actors. One of the reasons is WMI is quite stealthy. This rule detects the wmic command line launching a process on a remote or local host.
- Effort: intermediate
Wmic Service Call
Detects either remote or local code execution using wmic tool.
- Effort: intermediate
XCopy Suspicious Usage
Detects the usage of xcopy with suspicious command line options (used by Judgment Panda APT in the past). The rule is based on command line only in case xcopy is renamed.
- Effort: advanced
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Web proxy |
The NetScaler appliance logs provide information about the connected client and the requested resource |
Web application firewall logs |
The NetScaler appliance logs provide information about the connected client and the requested resource |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | alert |
| Category | authentication, configuration, network |
| Type | change, connection, info, start |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "01/24/2025:12:06:37 GMT NetscalerCD07_1 0-PPE-0 : default AAA LOGIN_FAILED 73912122 0 : User testUser - Client_ip 1.2.3.4 - Failure_reason \"External authentication server denied access\" - Browser Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/131.0.0.0 Safari/537.36",
"event": {
"category": [
"authentication"
],
"code": "LOGIN_FAILED",
"dataset": "audit_aaa",
"outcome": "failure",
"reason": "External authentication server denied access",
"type": [
"start"
]
},
"@timestamp": "2025-01-24T12:06:37Z",
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"observer": {
"name": "NetscalerCD07_1"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"testUser"
]
},
"user": {
"name": "testUser"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Chrome",
"original": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/131.0.0.0 Safari/537.36",
"os": {
"name": "Windows",
"version": "10"
},
"version": "131.0.0"
}
}
{
"message": "02/17/2025:07:32:36 GMT NetscalerCD07_2 0-PPE-0 : default AAA LOGIN_FAILED 14861134 0 : User john.doe - Client_ip 1.2.3.4 - Failure_reason \"External authentication server denied access\"",
"event": {
"category": [
"authentication"
],
"code": "LOGIN_FAILED",
"dataset": "audit_aaa",
"outcome": "failure",
"reason": "External authentication server denied access",
"type": [
"start"
]
},
"@timestamp": "2025-02-17T07:32:36Z",
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"observer": {
"name": "NetscalerCD07_2"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"john.doe"
]
},
"user": {
"name": "john.doe"
}
}
{
"message": "09/30/2025:11:55:37 0-PPE-0 : default AAA Message 207030 0 : \"Authentication is rejected for johndoe (client ip : 1.2.3.4 , vserver ip: 5.6.7.8 ), extended error, if any : \"",
"event": {
"category": [
"authentication"
],
"code": "Message",
"dataset": "audit_aaa",
"outcome": "failure",
"reason": "Authentication is rejected for johndoe (client ip : 1.2.3.4 , vserver ip: 5.6.7.8 ), extended error, if any : ",
"type": [
"start"
]
},
"@timestamp": "2025-09-30T11:55:37Z",
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8"
},
"related": {
"ip": [
"1.2.3.4",
"5.6.7.8"
],
"user": [
"johndoe"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"name": "johndoe"
}
}
{
"message": "01/24/2025:12:19:12 GMT NetscalerCD07_1 0-PPE-0 : default AAATM Message 73920564 0 : \"nFactor: SESS UPDATE: flags 40001, flags2 1f20000, flags3 40, flags4 0, message length 0, sess_req flags 40000\"",
"event": {
"category": [
"network"
],
"dataset": "audit_aaatm",
"reason": "nFactor: SESS UPDATE: flags 40001, flags2 1f20000, flags3 40, flags4 0, message length 0, sess_req flags 40000",
"type": [
"info"
]
},
"@timestamp": "2025-01-24T12:19:12Z",
"observer": {
"name": "NetscalerCD07_1"
}
}
{
"message": "08/26/2025:07:22:06 GMT ADC01 0-PPE-0 : default AAATM Message 19548406 0 : \"ns_aaa_saml_parse_assertion: parsing the begg tag: AttributeValue>http://schemas.#012\"",
"event": {
"category": [
"network"
],
"dataset": "audit_aaatm",
"reason": "ns_aaa_saml_parse_assertion: parsing the begg tag: AttributeValue>http://schemas.#012",
"type": [
"info"
]
},
"@timestamp": "2025-08-26T07:22:06Z",
"observer": {
"name": "ADC01"
}
}
{
"message": "root on (null) shell_command=\"for pid in $PROF_PIDS; do kill -0 $pid > /dev/null 2>&1; if [ $? -ne 0 ]; then kill -9 $PROF_PIDS > /dev/null 2>&1; return; fi; done\"",
"event": {
"action": "execute_shell_command",
"category": [
"configuration"
],
"dataset": "audit_cmd",
"type": [
"change"
]
},
"process": {
"command_line": "for pid in $PROF_PIDS; do kill -0 $pid > /dev/null 2>&1; if [ $? -ne 0 ]; then kill -9 $PROF_PIDS > /dev/null 2>&1; return; fi; done",
"name": "bash"
},
"related": {
"user": [
"root"
]
},
"user": {
"name": "root"
}
}
{
"message": "root on /dev/pts/0 shell_command=\"PATH=/netscaler:/bin:/sbin:/usr/bin:/usr/sbin:/usr/libexec:/usr/local/bin:/usr/local/sbin:.\"",
"event": {
"action": "execute_shell_command",
"category": [
"configuration"
],
"dataset": "audit_cmd",
"type": [
"change"
]
},
"citrix": {
"adc": {
"pseudo_tty": "/dev/pts/0"
}
},
"process": {
"command_line": "PATH=/netscaler:/bin:/sbin:/usr/bin:/usr/sbin:/usr/libexec:/usr/local/bin:/usr/local/sbin:.",
"interactive": true,
"name": "bash"
},
"related": {
"user": [
"root"
]
},
"user": {
"name": "root"
}
}
{
"message": "CEF:0|Citrix|NetScaler|NS13.1|APPFW|APPFW_MULTIPLE_HEADER|6|src=1.2.3.4 geolocation=Unknown spt=61903 method=GET request=https://www.example.org/services msg=Multiple headers in request cn1=3755128 cn2=1636674 cs1=WAF_PRF_RULE1 cs2=PPE1 cs4=ALERT cs5=2023 act=blocked",
"event": {
"action": "blocked",
"category": [
"network"
],
"dataset": "alert",
"kind": "alert",
"reason": "Multiple headers in request",
"type": [
"denied"
]
},
"citrix": {
"adc": {
"alert": {
"severity": "ALERT"
}
}
},
"http": {
"request": {
"method": "GET"
}
},
"observer": {
"product": "NetScaler",
"vendor": "Citrix",
"version": "NS13.1"
},
"related": {
"ip": [
"1.2.3.4"
]
},
"rule": {
"name": "WAF_PRF_RULE1"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 61903
},
"url": {
"domain": "www.example.org",
"full": "https://www.example.org/services",
"original": "https://www.example.org/services",
"path": "/services",
"port": 443,
"registered_domain": "example.org",
"scheme": "https",
"subdomain": "www",
"top_level_domain": "org"
}
}
{
"message": "01/28/2025:13:21:01 GMT DVPXLBLINT01 0-PPE-0 : default GUI CMD_EXECUTED 13034678 0 : User john-doe - ADM_User NONE - Remote_ip 1.2.3.4 - Command \"show ssl profile integration_ssl_profile_frontend_test\" - Status \"Success\"",
"event": {
"category": [
"configuration"
],
"code": "CMD_EXECUTED",
"dataset": "audit_gui",
"outcome": "success",
"type": [
"change"
]
},
"@timestamp": "2025-01-28T13:21:01Z",
"observer": {
"name": "DVPXLBLINT01"
},
"process": {
"command_line": "show ssl profile integration_ssl_profile_frontend_test"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"john-doe"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"name": "john-doe"
}
}
{
"message": "default CMD_EXECUTED 500593 0 : User john.doe - ADM_User NONE - Remote_ip 1.2.3.4 - Command \"logout\" - Status \"Success\"",
"event": {
"category": [
"configuration"
],
"code": "CMD_EXECUTED",
"dataset": "audit_default",
"outcome": "success",
"type": [
"change"
]
},
"process": {
"command_line": "logout"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"john.doe"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"name": "john.doe"
}
}
{
"message": "2023/07/04:09:03:46 ADC 0-PPE-2 : default TCP CONN_TERMINATE 4556618 0 : Source 1.2.3.4:443 - Destination 5.6.7.8:43566 - Start Time 2023/07/04:09:03:46 - End Time 2023/07/04:09:03:46 - Total_bytes_send 473 - Total_bytes_recv 1",
"event": {
"category": [
"network"
],
"code": "CONN_TERMINATE",
"dataset": "audit_connection",
"type": [
"connection"
]
},
"@timestamp": "2023-07-04T09:03:46Z",
"citrix": {
"adc": {
"bytes": {
"received": 1,
"sent": 473
}
}
},
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8"
},
"observer": {
"name": "ADC"
},
"related": {
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "2023/07/04:09:03:46 ADC 0-PPE-0 : default TCP CONN_TERMINATE 19695388 0 : Source 1.2.3.4:5557 - Destination 5.6.7.8:39654 - Start Time 2023/07/04:09:03:01 - End Time 2023/07/04:09:03:46 - Total_bytes_send 1 - Total_bytes_recv 1",
"event": {
"category": [
"network"
],
"code": "CONN_TERMINATE",
"dataset": "audit_connection",
"type": [
"connection"
]
},
"@timestamp": "2023-07-04T09:03:46Z",
"citrix": {
"adc": {
"bytes": {
"received": 1,
"sent": 1
}
}
},
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8"
},
"observer": {
"name": "ADC"
},
"related": {
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "2023/07/04:09:03:45 ADC 0-PPE-1 : default TCP CONN_DELINK 4356922 0 : Source 1.2.3.4:13788 - Vserver 192.168.152.11:443 - NatIP 4.3.2.1:3198 - Destination 5.6.7.8:443 - Delink Time 2023/07/04:09:03:45 - Total_bytes_send 0 - Total_bytes_recv 762",
"event": {
"category": [
"network"
],
"code": "CONN_DELINK",
"dataset": "audit_connection",
"type": [
"connection"
]
},
"@timestamp": "2023-07-04T09:03:45Z",
"citrix": {
"adc": {
"bytes": {
"received": 762,
"sent": 0
},
"virtual_server": {
"ip": "192.168.152.11",
"port": "443"
}
}
},
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8"
},
"observer": {
"name": "ADC"
},
"related": {
"ip": [
"1.2.3.4",
"4.3.2.1",
"5.6.7.8"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"nat": {
"ip": "4.3.2.1"
}
}
}
{
"message": "1.2.3.4 -> 5.6.7.8 \"GET /test/v1/config/systemfile?REDACTED HTTP/1.1\" 200 14794 \"-\" \"Prometheus/2.30.0\" \"Time: 65590 microsecs\"",
"event": {
"category": [
"network"
],
"dataset": "audit_http_access",
"type": [
"connection"
]
},
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8"
},
"http": {
"request": {
"method": "GET"
},
"response": {
"body": {
"bytes": 14794
},
"status_code": 200
}
},
"related": {
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"url": {
"original": "/test/v1/config/systemfile?REDACTED",
"path": "/test/v1/config/systemfile",
"query": "REDACTED"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Other",
"original": "Prometheus/2.30.0",
"os": {
"name": "Other"
},
"version": "2.30.0"
}
}
{
"message": "1.2.3.4 -> 1.2.3.4 - - [10/Jun/2024:23:07:11 +0530] [1571] \"GET /nitro/v1/config/route6?REDACTED HTTP/1.1\" 200 1162 \"-\" \"-\" \"Time: 9797 microsecs\"",
"event": {
"category": [
"network"
],
"dataset": "audit_http_access",
"type": [
"connection"
]
},
"@timestamp": "2024-06-10T17:37:11Z",
"destination": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"http": {
"request": {
"method": "GET"
},
"response": {
"body": {
"bytes": 1162
},
"status_code": 200
}
},
"process": {
"pid": 1571
},
"related": {
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"url": {
"original": "/nitro/v1/config/route6?REDACTED",
"path": "/nitro/v1/config/route6",
"query": "REDACTED"
}
}
{
"message": "CEF:0|Citrix|NetScaler|NS13.1|APPFW|APPFW_POLICY_HIT|6|src=1.2.3.4 geolocation=Unknown spt=62919 method=GET request=https://www.example.org/services msg=Application Firewall profile invoked cn1=3864530 cn2=1644557 cs1=WAF_PRF_RULE1 cs2=PPE2 cs4=ALERT cs5=2023 act=not blocked",
"event": {
"action": "not blocked",
"category": [
"network"
],
"dataset": "alert",
"kind": "alert",
"reason": "Application Firewall profile invoked",
"type": [
"allowed"
]
},
"citrix": {
"adc": {
"alert": {
"severity": "ALERT"
}
}
},
"http": {
"request": {
"method": "GET"
}
},
"observer": {
"product": "NetScaler",
"vendor": "Citrix",
"version": "NS13.1"
},
"related": {
"ip": [
"1.2.3.4"
]
},
"rule": {
"name": "WAF_PRF_RULE1"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 62919
},
"url": {
"domain": "www.example.org",
"full": "https://www.example.org/services",
"original": "https://www.example.org/services",
"path": "/services",
"port": 443,
"registered_domain": "example.org",
"scheme": "https",
"subdomain": "www",
"top_level_domain": "org"
}
}
{
"message": "\"2023/07/04:09:03:41 ADC 0-PPE-1 : default SNMP TRAP_SENT 0 0 : appfwPolicyHit (appfwLogMsg = \"\"CEF:0|Citrix|NetScaler|NS13.1|APPFW|APPFW_POLI...\"\", nsPartitionName = default)\"",
"event": {
"category": [
"network"
],
"code": "TRAP_SENT",
"dataset": "audit_snmp",
"reason": "appfwPolicyHit (appfwLogMsg = \"\"CEF:0|Citrix|NetScaler|NS13.1|APPFW|APPFW_POLI...\"\", nsPartitionName = default)\"",
"type": [
"connection"
]
},
"@timestamp": "2023-07-04T09:03:41Z",
"observer": {
"name": "ADC"
}
}
{
"message": "01/16/2025:15:22:40 NSMPXPHOENIX 0-PPE-4 : default SSLVPN Message 855350000 0 : \"SSLVPN Mux Authorize result is Allow, Srcip: 1.2.3.4, Dstip: 5.6.7.8\"",
"event": {
"category": [
"authentication"
],
"code": "Message",
"dataset": "audit_sslvpn",
"outcome": "success",
"type": [
"start"
]
},
"@timestamp": "2025-01-16T15:22:40Z",
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8"
},
"observer": {
"name": "NSMPXPHOENIX"
},
"related": {
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "\"2023/07/04:09:03:39 ADC 0-PPE-0 : default SSLLOG SSL_HANDSHAKE_SUCCESS 19695351 0 : SPCBId 1265452 - ClientIP 1.2.3.4 - ClientPort 50130 - VserverServiceIP 192.168.152.11 - VserverServicePort 443 - ClientVersion TLSv1.2 - CipherSuite \"\"TLS1.2-ECDHE-RSA-AES256-GCM-SHA384\"\" - Session New - HandshakeTime 27 ms\"",
"event": {
"category": [
"network"
],
"code": "SSL_HANDSHAKE_SUCCESS",
"dataset": "audit_ssl",
"type": [
"connection"
]
},
"@timestamp": "2023-07-04T09:03:39Z",
"citrix": {
"adc": {
"virtual_server": {
"ip": "192.168.152.11",
"port": "443"
}
}
},
"observer": {
"name": "ADC"
},
"related": {
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 50130
},
"tls": {
"cipher": "TLS1.2-ECDHE-RSA-AES256-GCM-SHA384",
"version": "TLSv1"
}
}
{
"message": "\"2023/07/04:09:03:46 ADC 0-PPE-0 : default SSLVPN Message 19695397 0 : \"\"SSLVPN Mux Authorize result is Deny, User <user1>, Srcip: 1.2.3.4, Dstip: 5.6.7.8, denied_by_policy: SESSPOL_VPN_Remoteadmin\"\"\"",
"event": {
"category": [
"authentication"
],
"code": "Message",
"dataset": "audit_sslvpn",
"outcome": "failure",
"type": [
"start"
]
},
"@timestamp": "2023-07-04T09:03:46Z",
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8"
},
"observer": {
"name": "ADC"
},
"related": {
"ip": [
"1.2.3.4",
"5.6.7.8"
],
"user": [
"user1"
]
},
"rule": {
"name": "SESSPOL_VPN_Remoteadmin"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"name": "user1"
}
}
{
"message": "\"2023/07/04:09:03:39 ADC 0-PPE-0 : default SSLVPN NONHTTP_RESOURCEACCESS_DENIED 19695356 0 : Context user1@91.170.235.67 - SessionId: 1286 - User user1 - Client_ip 1.2.3.4 - Nat_ip 4.3.2.1 - Vserver 192.168.152.11:443 - Source 1.2.3.4:50130 - Destination 5.6.7.8:514 - Total_bytes_send 340 - Total_bytes_recv 0 - Denied_by_policy \"\"AUTHZ_DENY\"\" - Group(s) \"\"vpndsin,vpndsin\"\"\"",
"event": {
"category": [
"network"
],
"code": "NONHTTP_RESOURCEACCESS_DENIED",
"dataset": "audit_sslvpn",
"type": [
"connection"
]
},
"@timestamp": "2023-07-04T09:03:39Z",
"citrix": {
"adc": {
"virtual_server": {
"ip": "192.168.152.11",
"port": "443"
}
}
},
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8",
"port": 514
},
"observer": {
"name": "ADC"
},
"related": {
"ip": [
"1.2.3.4",
"4.3.2.1",
"5.6.7.8"
],
"user": [
"user1"
]
},
"rule": {
"name": "AUTHZ_DENY"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"nat": {
"ip": "4.3.2.1"
},
"port": 50130
},
"user": {
"name": "user1"
}
}
{
"message": "\"12/07/2023:10:58:42 GMT CXA-GAT 0-PPE-0 : default SSLVPN Message 1521206 0 : \"SSO ns_sslvpn_process_sso_conn: user john.doe@example.com clientip 1.2.3.4 request: /Citrix/CITRIXCGDWeb/clients/HTML5Client/resources/images/icon_clipboard.png sso_flags-0 p_flags-0 x_flags-200000 author_hdr_removed-0\"\"",
"event": {
"category": [
"network"
],
"code": "Message",
"dataset": "audit_sslvpn",
"type": [
"connection"
]
},
"@timestamp": "2023-12-07T10:58:42Z",
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"observer": {
"name": "CXA-GAT"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"john.doe"
]
},
"user": {
"domain": "example.com",
"name": "john.doe"
}
}
{
"message": "12/19/2024:10:37:23 GMT NetscalerCD07_1 0-PPE-0 : default SSLVPN LOGOUT 40895248 0 : Context testuser@1.2.3.4 - SessionId: 1096201 - User testuser - Client_ip 1.2.3.4 - Nat_ip \"Mapped Ip\" - Vserver 3.4.5.6:443 - Start_time \"12/19/2024:10:16:43 GMT\" - End_time \"12/19/2024:10:37:23 GMT\" - Duration 00:20:40 - Http_resources_accessed 0 - NonHttp_services_accessed 0 - Total_TCP_connections 46 - Total_UDP_flows 0 - Total_policies_allowed 46 - Total_policies_denied 0 - Total_bytes_send 0 - Total_bytes_recv 414177 - Total_compressedbytes_send 0 - Total_compressedbytes_recv 0 - Compression_ratio_send 0.00% - Compression_ratio_recv 0.00% - LogoutMethod \"Explicit\" - Group(s) \"N/A\"",
"event": {
"category": [
"network"
],
"code": "LOGOUT",
"dataset": "audit_sslvpn",
"type": [
"connection"
]
},
"@timestamp": "2024-12-19T10:37:23Z",
"citrix": {
"adc": {
"virtual_server": {
"ip": "3.4.5.6",
"port": "443"
}
}
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"observer": {
"name": "NetscalerCD07_1"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"testuser"
]
},
"user": {
"name": "testuser"
}
}
{
"message": "12/19/2024:09:40:29 GMT NetscalerCD07_1 0-PPE-0 : default SSLVPN TCPCONNSTAT 40844824 0 : Context user1@1.2.3.4 - SessionId: 1096160 - User user1 - Client_ip 1.2.3.4 - Nat_ip 5.6.7.8 - Vserver 3.4.5.6:443 - Source 1.2.3.4:59549 - Destination 3.3.3.3:443 - Start_time \"12/19/2024:09:40:29 GMT\" - End_time \"12/19/2024:09:40:29 GMT\" - Duration 00:00:00 - Total_bytes_send 0 - Total_bytes_recv 51251 - Total_compressedbytes_send 0 - Total_compressedbytes_recv 0 - Compression_ratio_send 0.00% - Compression_ratio_recv 0.00% - Access Allowed - Group(s) \"N/A\"",
"event": {
"category": [
"network"
],
"code": "TCPCONNSTAT",
"dataset": "audit_sslvpn",
"type": [
"connection"
]
},
"@timestamp": "2024-12-19T09:40:29Z",
"citrix": {
"adc": {
"virtual_server": {
"ip": "3.4.5.6",
"port": "443"
}
}
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"destination": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"port": 443
},
"observer": {
"name": "NetscalerCD07_1"
},
"related": {
"ip": [
"1.2.3.4",
"3.3.3.3"
],
"user": [
"user1"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 59549
},
"user": {
"name": "user1"
}
}
{
"message": "12/19/2024:09:40:29 GMT NetscalerCD07_1 0-PPE-0 : default SSLVPN HTTPREQUEST 40844823 0 : Context user1@1.2.3.4 - SessionId: 1096160 - example.com User user1 : Group(s) N/A : Vserver 3.4.5.6:443 - 12/19/2024:09:40:29 GMT : SSO is ON : GET /ttt.jpg - -",
"event": {
"category": [
"network"
],
"code": "HTTPREQUEST",
"dataset": "audit_sslvpn",
"type": [
"connection"
]
},
"@timestamp": "2024-12-19T09:40:29Z",
"citrix": {
"adc": {
"virtual_server": {
"ip": "3.4.5.6",
"port": "443"
}
}
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"http": {
"request": {
"method": "GET"
}
},
"observer": {
"name": "NetscalerCD07_1"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"url": {
"domain": "example.com",
"path": "/ttt.jpg",
"registered_domain": "example.com",
"top_level_domain": "com"
},
"user": {
"name": "user1"
}
}
{
"message": "08/13/2025:11:29:14 TEST01 0-PPE-1 : default SSLLOG SSL_HANDSHAKE_FAILURE 2037242 0 : SPCBId 55592 - ClientIP 1.2.3.4 - ClientPort 60892 - VserverServiceIP 3.4.5.6 - VserverServicePort 443 - ClientVersion TLSv1.2 - CipherSuite \"TLS1-AES-256-CBC-SHA\" - Session New - Reason \"Fatal alert received\"",
"event": {
"category": [
"network"
],
"code": "SSL_HANDSHAKE_FAILURE",
"dataset": "audit_ssl",
"type": [
"connection"
]
},
"@timestamp": "2025-08-13T11:29:14Z",
"citrix": {
"adc": {
"virtual_server": {
"ip": "3.4.5.6",
"port": "443"
}
}
},
"observer": {
"name": "TEST01"
},
"related": {
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 60892
},
"tls": {
"cipher": "TLS1-AES-256-CBC-SHA",
"version": "TLSv1"
}
}
{
"message": "13/08/2025:11:29:14 TEST01 0-PPE-1 : default SSLLOG SSL_HANDSHAKE_FAILURE 2037242 0 : SPCBId 55592 - ClientIP 1.2.3.4 - ClientPort 60892 - VserverServiceIP 2.3.4.5 - VserverServicePort 443 - ClientVersion TLSv1.2 - CipherSuite \"TLS1-AES-256-CBC-SHA\" - Session New - Reason \"Fatal alert received\"",
"event": {
"category": [
"network"
],
"code": "SSL_HANDSHAKE_FAILURE",
"dataset": "audit_ssl",
"type": [
"connection"
]
},
"citrix": {
"adc": {
"virtual_server": {
"ip": "2.3.4.5",
"port": "443"
}
}
},
"observer": {
"name": "TEST01"
},
"related": {
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 60892
},
"tls": {
"cipher": "TLS1-AES-256-CBC-SHA",
"version": "TLSv1"
}
}
{
"message": "01/28/2026:14:14:14 HOSTNAME 0-PPE-0 : default SSLVPN ICASTART 25487330 0 : [TECHSUPPORT][LAUNCH][TCP][CGP][ICAUUID=11111111111-11111-1111-1111-111111111] Source 2.2.2.2:49692 - Destination 1.1.1.1:2598 - customername - username:domainname user1:example - applicationName Application-Test $S3-56 - startTime \"01/28/2026:14:14:13 \" - connectionId 1111111",
"event": {
"category": [
"network"
],
"code": "ICASTART",
"dataset": "audit_sslvpn",
"type": [
"connection"
]
},
"@timestamp": "2026-01-28T14:14:14Z",
"citrix": {
"adc": {
"application_name": "Application-Test $S3-56"
}
},
"destination": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"port": 2598
},
"observer": {
"name": "HOSTNAME"
},
"related": {
"ip": [
"1.1.1.1",
"2.2.2.2"
],
"user": [
"user1"
]
},
"source": {
"address": "2.2.2.2",
"ip": "2.2.2.2",
"port": 49692
},
"user": {
"domain": "example",
"name": "user1"
}
}
{
"message": "28/01/2026:14:14:14 HOSTNAME 0-PPE-0 : default SSLVPN ICASTART 25487330 0 : [TECHSUPPORT][LAUNCH][TCP][CGP][ICAUUID=11111111111-11111-1111-1111-111111111] Source 2.2.2.2:49692 - Destination 1.1.1.1:2598 - customername - username:domainname user1:example - applicationName Application-Test $S3-56 - startTime \"28/01/2026:14:14:13 \" - connectionId 1111111",
"event": {
"category": [
"network"
],
"code": "ICASTART",
"dataset": "audit_sslvpn",
"type": [
"connection"
]
},
"citrix": {
"adc": {
"application_name": "Application-Test $S3-56"
}
},
"destination": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"port": 2598
},
"observer": {
"name": "HOSTNAME"
},
"related": {
"ip": [
"1.1.1.1",
"2.2.2.2"
],
"user": [
"user1"
]
},
"source": {
"address": "2.2.2.2",
"ip": "2.2.2.2",
"port": 49692
},
"user": {
"domain": "example",
"name": "user1"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
citrix.adc.adm_user |
keyword |
|
citrix.adc.alert.severity |
keyword |
|
citrix.adc.application_name |
keyword |
|
citrix.adc.bytes.received |
long |
|
citrix.adc.bytes.sent |
long |
|
citrix.adc.pseudo_tty |
keyword |
|
citrix.adc.virtual_server.ip |
keyword |
|
citrix.adc.virtual_server.port |
keyword |
|
client.ip |
ip |
IP address of the client. |
destination.ip |
ip |
IP address of the destination. |
destination.port |
long |
Port of the destination. |
event.action |
keyword |
The action captured by the event. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.code |
keyword |
Identification code for this event. |
event.dataset |
keyword |
Name of the dataset. |
event.kind |
keyword |
The kind of the event. The highest categorization field in the hierarchy. |
event.outcome |
keyword |
The outcome of the event. The lowest level categorization field in the hierarchy. |
event.reason |
keyword |
Reason why this event happened, according to the source |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
http.request.method |
keyword |
HTTP request method. |
http.response.body.bytes |
long |
Size in bytes of the response body. |
http.response.status_code |
long |
HTTP response status code. |
observer.name |
keyword |
Custom name of the observer. |
observer.product |
keyword |
The product name of the observer. |
observer.vendor |
keyword |
Vendor name of the observer. |
observer.version |
keyword |
Observer version. |
process.command_line |
wildcard |
Full command line that started the process. |
process.name |
keyword |
Process name. |
process.pid |
long |
Process id. |
rule.name |
keyword |
Rule name |
source.ip |
ip |
IP address of the source. |
source.nat.ip |
ip |
Source NAT ip |
source.port |
long |
Port of the source. |
tls.cipher |
keyword |
String indicating the cipher used during the current connection. |
tls.version |
keyword |
Numeric part of the version parsed from the original string. |
url.domain |
keyword |
Domain of the url. |
url.original |
wildcard |
Unmodified original url as seen in the event source. |
url.path |
wildcard |
Path of the request, such as "/search". |
user.domain |
keyword |
Name of the directory the user is a member of. |
user.name |
keyword |
Short name or login of the user. |
user_agent.name |
keyword |
Name of the user agent. |
user_agent.original |
keyword |
Unparsed user_agent string. |
user_agent.version |
keyword |
Version of the user agent. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.