Check Point
Overview
Check Point’s Next Generation Firewalls (NGFWs) are trusted by customers for their highest security effectiveness and their ability to keep organizations protected from sophisticated fifth-generation cyber-attacks. Check Point’s NGFW includes 23 Firewall models optimized for running all threat prevention technologies simultaneously, including full SSL traffic inspection, without compromising on security or performance.
- Vendor: Check Point
- Supported environment: On Premise
- Version compatibility: R81.10
- Detection based on: Telemetry, Alert
- Supported application or feature: Firewall and threat prevention
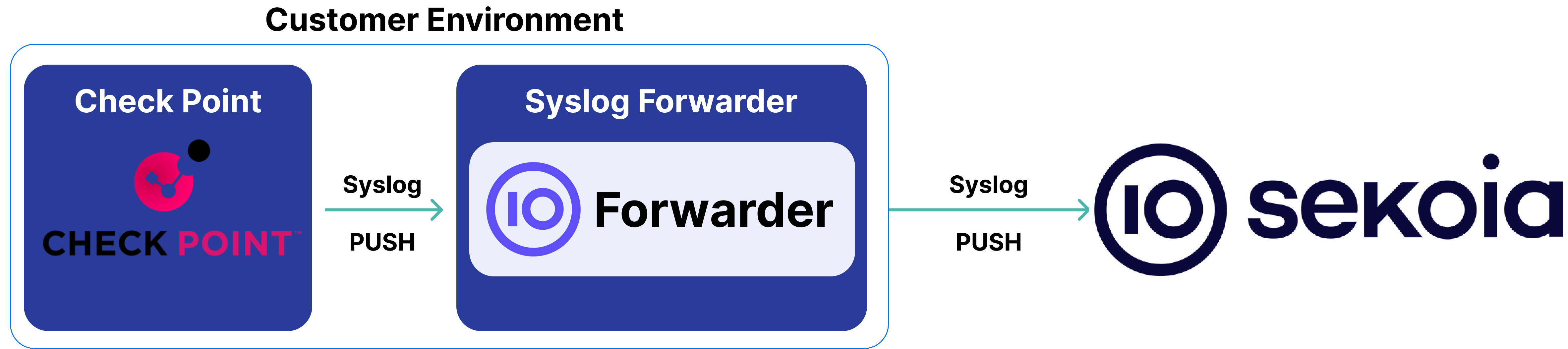
High-Level Architecture Diagram
- Type of integration: Outbound (PUSH to Sekoia.io)
- Schema
Specification
Prerequisites
- Resource:
- Self-managed syslog forwarder
- Network:
- Outbound traffic allowed
- Permissions:
- Administrator or Root access to the Check Point device
- Root access to the Linux server with the syslog forwarder
Transport Protocol/Method
- Indirect Syslog
Logs details
- Supported functionalities: See section Overview
- Supported type(s) of structure: CEF
- Supported verbosity level: Informational
Note
Log levels are based on the taxonomy of RFC5424. Adapt according to the terminology used by the editor.
Step-by-Step Configuration Procedure
Instructions on the 3rd Party Solution
The solution to collect Check Point logs leverages the Log Exporter method and Syslog forwarding.
Configure Log Exporter
- Set up the Log Exporter to send logs in the CEF format by following this guide.
Instruction on Sekoia
Configure Your Intake
This section will guide you through creating the intake object in Sekoia, which provides a unique identifier called the "Intake key." The Intake key is essential for later configuration, as it references the Community, Entity, and Parser (Intake Format) used when receiving raw events on Sekoia.
- Go to the Sekoia Intake page.
- Click on the
+ New Intakebutton at the top right of the page. - Search for your Intake by the product name in the search bar.
- Give it a Name and associate it with an Entity (and a Community if using multi-tenant mode).
- Click on
Create.
Note
For more details on how to use the Intake page and to find the Intake key you just created, refer to this documentation.
Configure a forwarder
To forward events using syslog to Sekoia.io, you need to update the syslog header with the intake key you previously created. Here is an example of your message before the forwarder
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG RAW_MESSAGE
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG [SEKOIA@53288 intake_key=\"YOUR_INTAKE_KEY\"] RAW_MESSAGE
To achieve this you can:
- Use the Sekoia.io forwarder which is the official supported way to collect data using the syslog protocol in Sekoia.io. In charge of centralizing data coming from many equipments/sources and forwarding them to Sekoia.io with the apporpriated format, it is a prepackaged option. You only have to provide your intake key as parameter.
- Use your own Syslog service instance. Maybe you already have an intance of one of these components on your side and want to reuse it in order to centralize data before forwarding them to Sekoia.io. When using this mode, you have to configure and maintain your component in order to respect the expected Sekoia.io format.
Warning
Only the Sekoia.io forwarder is officially supported. Other options are documented for reference purposes but do not have official support.
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
CEF:0|Check Point|VPN-1 & FireWall-1|Check Point|Log|HTTP_and_HTTPS_proxy|Unknown|act=Redirect destinationTranslatedAddress=1.1.1.1 destinationTranslatedPort=11680 deviceDirection=0 rt=1593013776000 sourceTranslatedAddress=0.0.0.0 sourceTranslatedPort=0 spt=53782 dpt=8080 cs2Label=Rule Name cs2=Explicit Proxy Access layer_name=Firewall layer_uuid=b8bf0a16-a447-47c3-8e7d-5e0061e17486 match_id=121 parent_rule=0 rule_action=Redirect rule_uid=37c21d26-f155-407a-9958-8584c1fd3320 ifname=eth1.60 logid=0 loguid={0x5ef37610,0x8,0x4d3c03bf,0xf33d4984} origin=2.2.2.2 originsicname=CN\\=ertfw01,O\=foomgmt.foobar.local.zazgch sequencenum=133 version=5 dst=3.3.3.3 inzone=External nat_addtnl_rulenum=0 dhost=4.4.4.4 nat_rulenum=0 outzone=External product=VPN-1 & FireWall-1 proto=6 service_id=HTTP_and_HTTPS_proxy src=5.5.5.5
CEF:0||Check Point|Application Control|Check Point|Log|Log|Unknown|act=Accept deviceDirection=0 rt=1708352128000 requestMethod=CONNECT request=https://foo.bar.com:443
conn_direction=Internal ifname=bond151.410 logid=321 loguid={0x65d3627f,0x303,0x1b6410ac,0x145ca8a5} origin=192.168.10.250
originsicname=CN\=baz-fw-internet-1,O\=HOSTNAME.intranet.corp.xd4pc5 sequencenum=1455 version=5 connection_luuid=4ac54d05-4f56-a0da-65d3-628000000003 hll_key=2847161932960334825
product=Application Control
0|Check Point|VPN-1 & FireWall-1|Check Point|Log|TCP_8000|Unknown|act=Accept deviceDirection=0 rt=1757320608000 spt=33108 dpt=8000 cs2Label=Rule Name layer_name=Company_GLOBAL_FW_Rules Security layer_uuid=11111111-1111-1111-1111-111111111111 match_id=318 parent_rule=0 rule_action=Accept rule_uid=22222222-2222-2222-2222-222222222222 conn_direction=Internal ifname=bond2.100 logid=0 loguid={0x5c4608f2,0xdc450628,0xd081d093,0x6c33af4d} origin=1.2.3.4 originsicname=CN\=F88-G1ZFW10,O\=F88mopPC01.company.com.ujwrfb sequencenum=78 version=5 dst=5.6.7.8 log_delay=1757320608 product=VPN-1 & FireWall-1 proto=6 service_id=TCP_8000 src=10.20.30.40
0|Check Point|VPN-1 & FireWall-1|Check Point|Log|Log|Unknown|act=Allow deviceDirection=1 rt=1592559930000 spt=137 dpt=137 alert=Undefined contextnum=2 ifname=eth2 logid=15 loguid={0x5eec893a,0x1c,0x47e0a0a,0xc0000000} origin=1.1.1.1 originsicname=CN\=foobarfw002,O\=foomgmt.foobar.local.zazgch sequencenum=61 version=5 context_num=2 dst=2.2.2.2 hll_key=13306743300460385727 product=VPN-1 & FireWall-1 proto=17 reason=Firewall - Protocol violation detected with protocol:(NetBIOS Name Service), matched protocol sig_id:(8), violation sig_id:(17). (500) src=3.3.3.3
CEF:0||Check Point|VPN-1 & FireWall-1|Check Point|Log|domain-udp|Unknown|act=Accept deviceDirection=0 rt=1708352128000 spt=63858 dpt=53 cs2Label=Rule Name cs2=Communication DNS
cs2=vers les ressources internes layer_name=Network layer_name=Application layer_uuid=86db1685-ca63-4fcd-b296-c15c99acfc76 layer_uuid=1d7f95ec-0774-4916-a1b4-e8ab1d2d9cae match_id=169
match_id=738197621 parent_rule=0 parent_rule=0 rule_action=Accept rule_action=Accept rule_uid=713de10c-0d41-44af-a2e3-fa4d697c515a rule_uid=9ede1042-638a-45cb-bf2f-f72f1e1b7d97
ifname=bond150.240 logid=0 loguid={0xb6666b4,0x11fbf15b,0x98b64f96,0x6772cf4d} origin=192.168.10.242 originsicname=CN\=cip-fw-core-1.intranet.corp,O\=HOSTNAME.intranet.corp.xd4pc5
sequencenum=547 version=5 dst=172.16.111.111 inzone=Internal outzone=Internal product=VPN-1 & FireWall-1 proto=17 service_id=domain-udp src=10.0.11.11
0|Check Point|VPN-1 & FireWall-1|Check Point|Decrypt|https|Unknown|act=Decrypt cs2Label=Peer Gateway cs2=1.1.1.1 deviceDirection=0 dhost= hostname@group.corp
duser=Firstname1, LASTNAME1 ( FLASTNAME1) Firstname2, Lastname2 (ADM) (FOO12345) duser=LASTNAME3, Firstname3 (ABC12345) rt=1708352039000 shost=hostname00100@group.corp spt=49967 dpt=443 suser=LASTNAME3, Firstname3
(ABC12345) cs2Label=Rule Name cs2=Implicit Cleanup layer_name=PROD_SEPTEMBRE_2020_QOS Security layer_name=PROD_SEPTEMBRE_2020_QOS Application layer_uuid=f3e58f17-af95-43fa-82a8-a10f86cd22
layer_uuid=aa29b5d0-08ef-4541-9c08-fe7335324262 match_id=129 match_id=33554431 parent_rule=0 parent_rule=0 rule_action=Accept rule_action=Accept rule_uid=310aff93-4aed-4616-a061-4aef36eebc
ifname=eth1 logid=0 loguid={0xa2198857,0x26b6c7dd,0x93bd692b,0xa64ec6bf} origin=2.2.2.2 originsicname=CN\=BODFW1,O\=FWMGNT.corpsubdomain.corp.s65fuv sequencenum=207 version=5
community=VPN_FOO_434 dst=192.168.111.111 dst_user_dn=CN\=Firstname1\, LASTNAME1,OU\=exterieur,OU\=Migration exchange faite,OU\=Migres_AD,OU\=Users,OU\=BOD,DC\=group,DC\=corp CN\= Firstname2\,
Lastname2 (ADM),OU\=Admin Accounts,OU\=ADMIN,DC\=group,DC\=corp fw_subproduct=VPN-1 https_inspection_action=Bypass inzone=External methods:=ESP: AES-256 + SHA256 + PFS (group 14)
nat_addtnl_rulenum=0 nat_rule_uid=a1fdbc3b-b993-4ea9-972c-07ae43e09acb nat_rulenum=61 outzone=Internal product=VPN-1 & FireWall-1 proto=6 scheme:=IKE service_id=https src=10.1.11.111
src_user_dn=CN\=LASTNAME3\, Firstname3,OU\=Internes,OU\=Users,OU\=ORY,DC\=group,DC\=corp vpn_feature_name=VPN
CEF: 0|Check Point|VPN-1 & FireWall-1|Check Point|Log|UDP_443|Unknown|act=Drop deviceDirection=0 duser=FIRSTNAME LASTNAME (FILA10052418) rt=1592559931000 shost=footlt327@ad.mycorp.com spt=56379 dpt=443 suser=FIRSTNAME LASTNAME (FILA10052418) cs2Label=Rule Name layer_name=Firewall layer_uuid=b8bf0a16-a447-47c3-8e7d-5e0061e17486 match_id=139 parent_rule=0 rule_action=Drop rule_uid=9c6de769-d2ab-4f1c-bd3b-5d2180af9844 ifname=Mgmt.3 logid=0 loguid={0x5eec893c,0x3,0x46416ac,0x16efadda} origin=2.2.2.2 originsicname=CN\=ertfw01,O\=foomgmt.foobar.local.zazgch sequencenum=299 version=5 dst=4.4.4.4 inzone=Internal outzone=External product=VPN-1 & FireWall-1 proto=17 service_id=UDP_443 src=3.3.3.3 src_user_dn=CN\=FIRSTNAME LASTNAME,OU\=Users,OU\=ServiceDesk,DC\=ad,DC\=mycorp,DC\=com
CEF:0|Check Point|VPN-1 & FireWall-1|Check Point|Log|Log|Unknown|act=Drop cs4Label=TCP Flags cs4=SYN-ACK deviceDirection=0 rt=1723938549000 spt=443 dpt=2384 ifname=test151.420 logid=1 loguid={0x66c136f5,0xf4,0x1b6410ac,0x151daa25} origin=1.2.3.4 originsicname=CN=cip-fw-test-1,O=CPSRVP.test.test sequencenum=103 version=5 dst=3.4.5.6 product=VPN-1 & FireWall-1 proto=6 src=1.2.3.4 tcp_packet_out_of_state=First packet isn't SYN
CEF:0||Check Point|VPN-1 & FireWall-1|Check Point|geo_protection|Log|Unknown|act=Accept
cs3Label=Protection Type cs3=geo_protection deviceDirection=0 rt=1708352128000 spt=56935 dpt=53
ifname=bond151.421 logid=65536 loguid={0x65d3627f,0x31d,0x1b6410ac,0x145ca8a5} origin=2.2.2.2
originsicname=CN\=cip-fw-internet-1,O\=HOSTNAME.intranet.corp.xd4pc5 sequencenum=1496 version=5
dst=3.3.3.3 dst_country=Other inspection_information=Geo-location inbound enforcement
inspection_profile=Block_Pays_a_Risque product=VPN-1 & FireWall-1 proto=17 src=1.1.1.1
src_country=Internal
CEF: 0|Check Point|HTTPS Inspection|Check Point|Log|Log|Unknown|act=HTTPS Bypass cs5Label=Matched Category deviceDirection=0 duser=USER-LASTNAME USER-FIRSTNAME (ULUF10004820) rt=1592559938000 shost=FooHost@ad.mycorp.com spt=56891 dpt=443 suser=USER-LASTNAME USER-FIRSTNAME (ULUF10004820) ifname=Mgmt.3 loguid={0x5eec8942,0x13,0x46416ac,0x16efadda} origin=2.2.2.2 originsicname=CN\=ertfw01,O\=foomgmt.foobar.local.zazgch sequencenum=324 version=5 dst=3.3.3.3 https_inspection_action=Bypass https_inspection_rule_id={DD126F7C-B373-4331-8632-DBA1EFDD0D6A} https_inspection_rule_name=Bypass for FooBar product=HTTPS Inspection proto=6 snid=0 src=1.1.1.1 src_user_dn=CN\=USER-LASTNAME USER-FIRSTNAME,OU\=Users,OU\=ServiceDesk,DC\=ad,DC\=mycorp,DC\=com
CEF:0||Check Point|VPN-1 & FireWall-1|Check Point|Log|https|Unknown|act=Accept app=HTTPS destinationTranslatedAddress=0.0.0.0 destinationTranslatedPort=0 deviceDirection=0
duser=LASTNAME FIRSTNAME (CORP0000583) rt=1708352128000 sourceTranslatedAddress=1.1.1.1 sourceTranslatedPort=12435 spt=56688 dpt=443 suser=LASTNAME FIRSTNAME (CORP0000583)
cs2Label=Rule Name cs2=Updatable Objects Services Microsoft layer_name=Network layer_name=Application layer_uuid=86db1685-ca63-4fcd-b296-c15c99acfc76
layer_uuid=1d7f95ec-0774-4916-a1b4-e8ab1d2d9cae match_id=267 match_id=637534254 parent_rule=0 parent_rule=0 rule_action=Accept rule_action=Accept
rule_uid=6426c486-c108-47b0-9c72-0adf917d7a0f rule_uid=bc9b26a7-f0fa-431d-81a2-6252f9f203a8 conn_direction=Outgoing contextnum=1 ifname=bond151.410 logid=0
loguid={0x611c9f51,0x8c73c182,0xe99e964e,0x2addea20} origin=192.168.111.111 originsicname=CN\=cip-fw-internet-1,O\=HOSTNAME.intranet.corp.xd4pc5 sequencenum=1271 version=5
certificate_validity=Trusted context_num=1 dst=2.2.2.2 dst_uo_icon=@app/cp_azure_azure dst_uo_name=Azure Services hll_key=6406281760033809592 https_inspection_action=Bypass
inzone=Internal nat_addtnl_rulenum=0 nat_rule_uid=1e99e081-d7f7-4bd8-b4fe-a40dc90e4230 nat_rulenum=114 needs_browse_time=1 outzone=External product=VPN-1 & FireWall-1 proto=6
service_id=https sig_id=4 sni=eu-mobile.events.data.microsoft.com src=3.3.3.3 src_user_dn=CN\=LASTNAME FIRSTNAME,OU\=Service Medical et Detection des Fraudes,OU\=Relations
Client,OU\=Direction des Opérations,OU\=Services,OU\=Users_Std_XP,OU\=Siege,OU\=France,DC\=intranet,DC\=corp tls_server_host_name=eu-mobile.events.data.microsoft.com
0|Check Point|SmartDefense|Check Point|IPS|Web Server Exposed Git Repository Information Disclosure|Very-High|act=Detect cp_severity=Very-High cnt=1 cs1Label=Threat Prevention Rule Name cs2Label=Protection ID cs2=asm_dynamic_prop_GIT_EXPOSED cs3Label=Protection Type cs3=IPS cs4Label=Protection Name cs4=Web Server Exposed Git Repository Information Disclosure cs4Label=Threat Prevention Rule ID cs4={115C1043-DF8A-48D4-96CB-0200C1F1499A} deviceDirection=1 flexNumber1Label=Confidence flexNumber1=5 flexNumber2Label=Performance Impact flexNumber2=3 flexString2Label=Attack Information flexString2=Web Server Exposed Git Repository Information Disclosure in=52 msg=Web Server Enforcement Violation out=0 request=http://9.10.11.12/.git/config requestMethod=GET rt=1722861810000 spt=51451 dpt=80 cs4Label=Threat Prevention Rule ID cs4={115C1043-DF8A-48D4-96CB-0200C1F1499A} cs4={6E7AA7B4-FD2A-40A3-ACDE-AC1182F1120F} cs1Label=Threat Prevention Rule Name cs1=Antibot + TE EAP layer_name=IPS layer_uuid={1DA55D35-9A2B-4141-A512-150DC635378B} layer_uuid={368D4C86-B4FD-4EF9-9AED-E58C4C0DEE7F} smartdefense_profile=EAP_Prevent smartdefense_profile=Profil_EAP_Anti-Bot_TE ifname=bond1.103 loguid={0x611c9f51,0x8c73c182,0xe99e964e,0x2addea20} origin=192.168.203.80 originsicname=CN\=MyGW,O\=MyDomain_Server.checkpoint.com.s6t98x sequencenum=85 version=5 description_url=GIT_EXPOSED_help.html dst=1.2.3.4 lastupdatetime=1722861871 log_id=2 policy=2016-12_Prolix_Migration-FW policy_time=1722591913 product=SmartDefense proto=6 proxy_src_ip=5.6.7.8 reject_id_kid=66b0c8f2-2-a5f697e5-ce3758d7 rule_uid=e70129a9-2a18-4075-8042-b85f0b601ca4 ser_agent_kid=Safari 4.0 session_id={0x66b06cef,0x11,0x9b1c4c53,0xdf840ae7} smartdefense_profile=EAP_Prevent src=5.6.7.8 tags=Vendor_Git Product_Web_Servers Threat_Year_2015 Threat_Prevalence_True Protection_Type_Vulnerability Product_Prevalence_Common Tuning_Non_Configurable Protocol_HTTP Direction_SERVER
CEF: 0|Check Point|HTTPS Inspection|Check Point|Log|Log|Unknown|act=Reject deviceDirection=0 duser=LASTNAME FIRSTNAME (CORPO10004953) msg=SSL version is not supported. rt=1592575034000 spt=60144 dpt=443 suser=LASTNAME FIRSTNAME (CORPO10004953) loguid={0x5eecc43b,0x2,0x46416ac,0x16efadda} origin=1.1.1.1 originsicname=CN\=foobarfw002,O\=foomgmt.foobar.local.zazgch sequencenum=148 version=5 dst=2.2.2.2 https_validation=unsupported product=HTTPS Inspection proto=6 snid=0 src=3.3.3.3 src_user_dn=CN\=LASTNAME FIRSTNAME,OU\=Users,OU\=ServiceDesk,DC\=ad,DC\=mycorp,DC\=com
0|Check Point|SmartDefense|Check Point|IPS|Syslog Message Length Enforcement|Medium|act=Detect cp_severity=Medium cnt=53 cs1Label=Threat Prevention Rule Name cs2Label=Protection ID cs2=02syslg_max_msg_len_tab cs3Label=Protection Type cs3=IPS cs4Label=Protection Name cs4=Syslog Message Length Enforcement cs4Label=Threat Prevention Rule ID cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} deviceDirection=1 flexNumber1Label=Confidence flexNumber1=1 flexNumber2Label=Performance Impact flexNumber2=2 flexString2Label=Attack Information flexString2=phpFileManager cmd Parameter Command Execution in=0 msg=Syslog Protocol Violation out=0 rt=1705349059000 spt=57789 dpt=514 Signature=CVE-1999-0063, CVE-1999-0381 cs4Label=Threat Prevention Rule ID cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs1Label=Threat Prevention Rule Name layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy ifname=eth5.996 loguid={0xc4f7efea,0x4a15abc5,0x796000a8,0x18edf12d} origin=3.4.5.6 originsicname=CN\=DN-EXAMPLE,O\=alfi.defo.ccse.nl sequencenum=12 version=5 capture_uuid={0x65a58fcb,0x1,0x4d1f8365,0xc5a8726d} description_url=02syslg_max_msg_len_tab_help.html dst=5.6.7.8 lastupdatetime=1705352059 log_id=2 policy=dn policy_time=1705348793 product=SmartDefense proto=17 rule_uid=b16110f0-fc9f-43b1-9f87-a8ad3f995237 session_id={0x65a58fc3,0x3,0x4d1f8365,0xc5a8726d} smartdefense_profile=XXXX_IPS_policy src=1.2.3.4
CEF: 0|Check Point|VPN-1 & FireWall-1|Check Point|Log|TCP_135|Unknown|act=Accept deviceDirection=0 rt=1592498107000 spt=62170 dpt=135 cs2Label=Rule Name cs2=Allow all layer_name=Firewall FooBar layer_name=FooBar_policy Application layer_uuid=66f2e247-8237-4d61-b2e9-e4595c7a439c layer_uuid=b66dac35-e2a9-4a13-91bc-21cb9cafb3da match_id=19 match_id=16777244 parent_rule=0 parent_rule=0 rule_action=Accept rule_action=Accept rule_uid=378884f4-0844-4bbb-a5cb-22e9c88d4d09 rule_uid=43b8404c-809b-4f35-927e-2c05b3d28e53 conn_direction=Internal contextnum=1 ifname=eth2 logid=0 loguid={0x5eeb97bb,0x4,0x47e0a0a,0xc0000001} origin=1.1.1.1 originsicname=CN\=foobarfw002,O\=foomgmt.foobar.local.zazgch sequencenum=19 version=5 context_num=1 dst=2.2.2.2 hll_key=5221004884709257555 inzone=Internal outzone=Internal product=VPN-1 & FireWall-1 proto=6 service_id=TCP_135 src=3.3.3.3
CEF:0||Check Point|URL Filtering|Check Point|News / Media|domain.fr|Unknown|act=Accept app=HTTP
deviceDirection=0 duser=LASTNAME FIRSTNAME (CORP0025465) requestClientApplication=Google Chrome rt=1708352128000 dpt=8080
suser=LASTNAME FIRSTNAME (CORP0025465) cp_app_risk=Unknown cp_app_risk=Unknown cs6Label=Application Name cs6=domain.fr
cs5Label=Matched Category cs5=News / Media flexString1Label=Application Signature ID cs2Label=Rule Name cs2=vers les ressources
internes app_category=News / Media app_id=0 app_id=2108684536 app_properties=News / Media,URL Filtering layer_name=Network
layer_name=Application layer_uuid=86db1685-ca63-4fcd-b296-c15c99acfc76 layer_uuid=1d7f95ec-0774-4916-a1b4-e8ab1d2d9cae
match_id=273 match_id=637534325 parent_rule=0 parent_rule=0 rule_action=Accept rule_action=Accept
rule_uid=427fb6b8-dcf9-471a-a346-7c603f4a0852 rule_uid=9ede1042-638a-45cb-bf2f-f72f1e1b7d97 cp_app_risk=Unknown
cs6Label=Application Name cs6=domain.fr cs5Label=Matched Category cs5=News / Media flexString1Label=Application Signature ID
app_category=News / Media app_id=2108684536 app_properties=News / Media,URL Filtering requestMethod=CONNECT
request=https://subdomain.domain.fr:443 conn_direction=Internal ifname=bond151.410 logid=256
loguid={0xb8627f78,0x96aeacb2,0xe1a3617f,0x615f333f} origin=192.168.111.123
originsicname=CN\=cip-fw-internet-1,O\=HOSTNAME.intranet.corp.xd4pc5 sequencenum=1362 version=5 aggregated_log_count=1
browse_time=0 client_type_os=Windows 10 connection_count=1 creation_time=1708352128 dst=192.168.111.111 duration=0
hll_key=16778521701015169890 inzone=Internal last_hit_time=1708352128 outzone=Internal product=URL Filtering proto=6
service_id=HTTP_and_HTTPS_proxy sig_id=0 src=192.168.222.222 src_user_dn=CN\=LASTNAME
FIRSTNAME,OU\=Users_CC,OU\=RC,OU\=France,DC\=intranet,DC\=corp update_count=1 user_agent=Mozilla/5.0 (Windows NT 10.0; WOW64)
AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.190 Safari/537.36
"1832941" "20Dec2019" "12:04:05" "eth1" "2.2.2.2" "Log" "Decrypt" "" "" "3.3.3.3" "1.1.1.1" "icmp" "5" "Supervision" "5-FooBar_Policy" "" "inzone: External; outzone: Internal; service_id: icmp-proto; ICMP: Echo Request; ICMP Type: 8; ICMP Code: 0" "Multi-product" "" ""#013
"22" "10Dec2019" "23:44:49" "eth1" "FOOBAR-HOST-01" "Log" "Accept" "443" "44250" "2.2.2.2" "1.1.1.1" "tcp" "81" "WebAccess Notes" "81-FooBar_Policy" "" "inzone: External; outzone: Internal; service_id: https" "Multi-product" "" ""
"21" "10Dec2019" "23:44:49" "eth1" "FOOBAR-HOST-01" "Log" "Drop" "58339" "46193" "1.1.1.1" "2.2.2.2" "tcp" "107" "Deny All" "107-FooBar_Policy" "" "inzone: External; outzone: Internal" "Security Gateway/Management" "" ""
syslog[action:"Drop"; flags:"2308"; ifdir:"inbound"; ifname:"eth1"; loguid:"{0x0,0x0,0x0,0x0}"; origin:"1.1.1.1"; time:"1617710462"; version:"1"; __policy_id_tag:"product=VPN-1 & FireWall-1[db_tag={736F50F2-40D8-124E-8D46-F7849455B8AE};mgmt=foobar;date=1615201122;policy_name=FooPolicy\]"; dst:"2.2.2.2"; inzone:"External"; origin_sic_name:"CN=HOSTBAR,O=FooBaz.prj.fr.mnkqvz"; outzone:"External"; product:"VPN-1 & FireWall-1"; proto:"6"; rule:"118"; rule_name:"Clean-up Rule"; rule_uid:"{EA9E7B59-E0DD-4AE1-A2C0-680E3C3FAADC}"; s_port:"54377"; service:"5530"; src:"3.3.3.3"; ]
syslog[action:"Accept"; flags:"18692"; ifdir:"inbound"; ifname:"eth5"; loguid:"{0x607486c9,0x1,0x151e9f0a,0xc0000000}"; origin:"1.1.1.1"; time:"1618249417"; version:"1"; __policy_id_tag:"product=VPN-1 & FireWall-1[db_tag={A8A4FD06-D819-BC43-8607-833A6D14E3A2};mgmt=HOSTBAZ;date=1617956749;policy_name=MyPolicy\]"; dst:"2.2.2.2"; icmp:"Echo Request"; icmp_code:"0"; icmp_type:"8"; inzone:"Internal"; origin_sic_name:"CN=HOSTBAR,O=FooBaz.prj.fr.mnkqvz"; outzone:"Internal"; product:"VPN-1 & FireWall-1"; proto:"1"; rule:"21"; rule_uid:"{6C86D7C0-B2C8-4222-AEF9-18CC10CEAA2B}"; service_id:"echo-request"; src:"3.3.3.3"; ]
syslog[action:"Key Install"; flags:"2304"; ifdir:"inbound"; ifname:"daemon"; loguid:"{0x0,0x0,0x0,0x0}"; origin:"1.1.1.1"; time:"1618253000"; version:"1"; community:"Lab_to_Foo"; cookiei:"c1d26a716fed4717"; cookier:"6b57dcc95790f11f"; dst:"1.1.1.1"; dstkeyid:"0x4caf71d8"; fw_subproduct:"VPN-1"; ike::"Quick Mode completion [UDP (IPv4)\]."; ike_ids::"subnet: 2.2.2.2 (mask= 255.255.254.0) and subnet: 192.168.0.0 (mask= 255.255.255.252)"; methods::"ESP: AES-256 + SHA1 + PFS (group 5)"; msgid:"4c0515ff"; origin_sic_name:"CN=HOSTBAR,O=FooBaz.prj.fr.mnkqvz"; peer_gateway:"1.1.1.1"; scheme::"IKE"; src:"1.1.1.1"; srckeyid:"0x9dea8f3a"; vpn_feature_name:"IKE"; ]
syslog[action:"Accept"; flags:"18692"; ifdir:"inbound"; ifname:"eth5"; loguid:"{0x607486c4,0xa,0x151e9f0a,0xc0000001}"; origin:"1.1.1.1"; time:"1618249412"; version:"1"; __policy_id_tag:"product=VPN-1 & FireWall-1[db_tag={A8A4FD06-D819-BC43-8607-833A6D14E3A2};mgmt=HOSTBAZ;date=1617956749;policy_name=MyPolicy\]"; dst:"192.168.99.111"; icmp:"Echo Request"; icmp_code:"0"; icmp_type:"8"; inzone:"Internal"; nat_addtnl_rulenum:"1"; nat_rulenum:"132"; origin_sic_name:"CN=HOSTBAR,O=FooBaz.prj.fr.mnkqvz"; outzone:"Internal"; product:"VPN-1 & FireWall-1"; proto:"1"; rule:"71"; rule_name:"Internet"; rule_uid:"{D67042B8-7EC2-4A9F-A047-523DE6CFF8E0}"; service_id:"echo-request"; src:"3.3.3.3"; xlatedport:"0"; xlatedst:"0.0.0.0"; xlatesport:"0"; xlatesrc:"192.168.99.1"; ]
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake Check Point NGFW. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x Check Point NGFW on ATT&CK Navigator
Account Added To A Security Enabled Group
Detection in order to investigate who has added a specific Domain User in Domain Admins or Group Policy Creator Owners (Security event 4728)
- Effort: master
Account Removed From A Security Enabled Group
Detection in order to investigate who has removed a specific Domain User in Domain Admins or Group Policy Creator Owners (Security event 4729)
- Effort: master
Active Directory Database Dump Via Ntdsutil
Detects the dump of ntdis.dit database by using the utility ntdsutil.exe. NTDS.dit database stores Active Directory data, including passwords hashes for all users in the domain.
- Effort: elementary
Burp Suite Tool Detected
Burp Suite is a cybersecurity tool. When used as a proxy service, its purpose is to intercept packets and modify them to send them to the server. Burp Collaborator is a network service that Burp Suite uses to help discover many kinds of vulnerabilities (vulnerabilities scanner).
- Effort: intermediate
CVE-2018-11776 Apache Struts2
Apache Struts versions 2.3 to 2.3.34 and 2.5 to 2.5.16 suffer from possible Remote Code Execution when alwaysSelectFullNamespace is true (either by user or a plugin like Convention Plugin) and then: results are used with no namespace and in same time, its upper package have no or wildcard namespace and similar to results, same possibility when using url tag which doesn't have value and action set and in same time, its upper package have no or wildcard namespace.
- Effort: intermediate
CVE-2019-0604 SharePoint
Detects the exploitation of the SharePoint vulnerability (CVE-2019-0604).
- Effort: advanced
CVE-2020-0688 Microsoft Exchange Server Exploit
Detects the exploitation of CVE-2020-0688. The POC exploit a .NET serialization vulnerability in the Exchange Control Panel (ECP) web page. The vulnerability is due to Microsoft Exchange Server not randomizing the keys on a per-installation basis resulting in them using the same validationKey and decryptionKey values. With knowledge of these, values an attacker can craft a special viewstate to use an OS command to be executed by NT_AUTHORITY\SYSTEM using .NET deserialization. To exploit this vulnerability, an attacker needs to leverage the credentials of an account it had already compromised to authenticate to OWA.
- Effort: elementary
CVE-2020-1147 SharePoint
Detection of SharePoint vulnerability CVE-2020-1147.
- Effort: advanced
CVE-2020-14882 Oracle WebLogic Server
Detects the exploitation of the Oracle WebLogic Server vulnerability (CVE-2020-16952).
- Effort: advanced
CVE-2020-17530 Apache Struts RCE
Detects the exploitation of the Apache Struts RCE vulnerability (CVE-2020-17530).
- Effort: intermediate
CVE-2021-20021 SonicWall Unauthenticated Administrator Access
Detects the exploitation of SonicWall Unauthenticated Admin Access.
- Effort: advanced
CVE-2021-20023 SonicWall Arbitrary File Read
Detects Arbitrary File Read, which can be used with other vulnerabilities as a mean to obtain outputs generated by attackers, or sensitive data.
- Effort: advanced
CVE-2021-21972 VMware vCenter
The vSphere Client (HTML5) contains a remote code execution vulnerability in a vCenter Server plugin. A malicious actor with network access to port 443 may exploit this issue to execute commands with unrestricted privileges on the underlying operating system that hosts vCenter Server. This affects VMware vCenter Server (7.x before 7.0 U1c, 6.7 before 6.7 U3l and 6.5 before 6.5 U3n) and VMware Cloud Foundation (4.x before 4.2 and 3.x before 3.10.1.2). POST request on the following PATH "/ui/vropspluginui/rest/services/uploadova". If in response body (500) the words it has "uploadFile", that means the vCenter is available to accept files via POST without any restrictions.
- Effort: intermediate
CVE-2021-21985 VMware vCenter
The VMware vSphere Client (HTML5) contains a remote code execution vulnerability due to lack of input validation in the Virtual SAN Health Check plug-in which is enabled by default in vCenter Server. A malicious actor with network access to port 443 may exploit this issue to execute commands with unrestricted privileges on the underlying operating system that hosts vCenter Server. This affects VMware vCenter Server (7.0 before 7.0 U2b, 6.7 before 6.7 U3n and 6.5 before 6.5 U3p) and VMware Cloud Foundation (4.x before 4.2.1 and 3.x before 3.10.2.1).
- Effort: advanced
CVE-2021-22123 Fortinet FortiWeb OS Command Injection
Detects Fortinet FortiWeb OS Command Injection (August 2021) vulnerability exploitation attempt. A remote, authenticated attacker can execute arbitrary commands on the system hosting a vulnerable FortiWeb WAF by sending a POST request with the command in the name field. At the time of writing this rule, it would appear that the request would respond in code 500 for a successful exploitation attempt.
- Effort: advanced
CVE-2021-22893 Pulse Connect Secure RCE Vulnerability
Detects potential exploitation of the authentication by-pass vulnerability that can allow an unauthenticated user to perform remote arbitrary file execution on the Pulse Connect Secure gateway. It is highly recommended to apply the Pulse Secure mitigations and seach for indicators of compromise on affected servers if you are in doubt over the integrity of your Pulse Connect Secure product.
- Effort: intermediate
CVE-2021-26855 Exchange SSRF
Detects the exploitation of ProyxLogon vulerability on Exchange servers.
- Effort: advanced
Computer Account Deleted
Detects computer account deletion.
- Effort: master
Correlation Potential DNS Tunnel
Detects domain name which is longer than 62 characters and requested at least 50 times in a 10 minutes range time. Long domain names are distinctive of DNS tunnels.
- Effort: advanced
Covenant Default HTTP Beaconing
Detects potential Covenant communications through the user-agent and specific urls
- Effort: intermediate
Cryptomining
Detection of domain names potentially related to cryptomining activities.
- Effort: master
Detect requests to Konni C2 servers
This rule detects requests to Konni C2 servers. These patterns come from an analysis done in 2022, September.
- Effort: elementary
Discord Suspicious Download
Discord is a messaging application. It allows users to create their own communities to share messages and attachments. Those attachments have little to no overview and can be downloaded by almost anyone, which has been abused by attackers to host malicious payloads.
- Effort: advanced
Domain Trust Created Or Removed
A trust was created or removed to a domain. An attacker could perform that in order to do lateral movement easily between domains or shutdown the ability of two domains to communicate.
- Effort: advanced
Dynamic DNS Contacted
Detect communication with dynamic dns domain. This kind of domain is often used by attackers. This rule can trigger false positive in non-controlled environment because dynamic dns is not always malicious.
- Effort: master
EvilProxy Phishing Domain
Detects subdomains potentially generated by the EvilProxy adversary-in-the-middle phishing platform. Inspect the other subdomains of the domain to identify the landing page, and determine if the user submitted credentials. This rule has a small percentage of false positives on legitimate domains.
- Effort: intermediate
Exfiltration Domain
Detects traffic toward a domain flagged as a possible exfiltration vector.
- Effort: master
FoggyWeb HTTP Default GET/POST Requests
Detects GET or POST request pattern observed within the first FoggyWeb campaign detected by Microsoft.
- Effort: advanced
Internet Scanner
Detects known scanner IP addresses. Alert is only raised when the scan hits an opened port, on TCP or UDP. This could be a very noisy rule, so be careful to check your detection perimeter before activation.
- Effort: master
Internet Scanner Target
Detects known scanner IP addresses. Alert is only raised when the scan hits an opened port, on TCP or UDP and group by target address. This could be a very noisy rule, so be careful to check your detection perimeter before activation.
- Effort: master
Koadic MSHTML Command
Detects Koadic payload using MSHTML module
- Effort: intermediate
Nimbo-C2 User Agent
Nimbo-C2 Uses an unusual User-Agent format in its implants.
- Effort: intermediate
Password Change On Directory Service Restore Mode (DSRM) Account
The Directory Service Restore Mode (DSRM) account is a local administrator account on Domain Controllers. Attackers may change the password to gain persistence.
- Effort: intermediate
Possible Malicious File Double Extension
Detects request to potential malicious file with double extension
- Effort: elementary
Possible Replay Attack
This event can be a sign of Kerberos replay attack or, among other things, network device configuration or routing problems.
- Effort: master
Potential Bazar Loader User-Agents
Detects potential Bazar loader communications through the user-agent
- Effort: elementary
Potential DNS Tunnel
Detects domain name which is longer than 62 characters. Long domain names are distinctive of DNS tunnels.
- Effort: advanced
Potential Lemon Duck User-Agent
Detects LemonDuck user agent. The format used two sets of alphabetical characters separated by dashes, for example "User-Agent: Lemon-Duck-[A-Z]-[A-Z]".
- Effort: elementary
Potential LokiBot User-Agent
Detects potential LokiBot communications through the user-agent
- Effort: intermediate
Privilege Escalation Awesome Scripts (PEAS)
Detect PEAS privileges escalation scripts and binaries
- Effort: elementary
ProxyShell Microsoft Exchange Suspicious Paths
Detects suspicious calls to Microsoft Exchange resources, in locations related to webshells observed in campaigns using this vulnerability.
- Effort: elementary
Raccoon Stealer 2.0 Legitimate Third-Party DLL Download URL
Detects Raccoon Stealer 2.0 malware downloading legitimate third-party DLLs from its C2 server. These legitimate DLLs are used by the information stealer to collect data on the compromised hosts.
- Effort: elementary
Remote Access Tool Domain
Detects traffic toward a domain flagged as a Remote Administration Tool (RAT).
- Effort: master
Remote Monitoring and Management Software - AnyDesk
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool AnyDesk.
- Effort: master
Remote Monitoring and Management Software - Atera
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool Atera.
- Effort: master
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
Sekoia.io EICAR Detection
Detects observables in Sekoia.io CTI tagged as EICAR, which are fake samples meant to test detection.
- Effort: master
Suspicious Download Links From Legitimate Services
Detects users clicking on Google docs links to download suspicious files. This technique was used a lot by Bazar Loader in the past.
- Effort: intermediate
Suspicious TOR Gateway
Detects suspicious TOR gateways. Gateways are often used by the victim to pay and decrypt the encrypted files without installing TOR. Tor intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: advanced
Suspicious URI Used In A Lazarus Campaign
Detects suspicious requests to a specific URI, usually on an .asp page. The website is often compromised.
- Effort: intermediate
TOR Usage
Detects TOR usage, based on the IP address and the destination port (filtered on NTP). TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
TOR Usage Generic Rule
Detects TOR usage globally, whether the IP is a destination or source. TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
Telegram Bot API Request
Detects suspicious DNS queries to api.telegram.org used by Telegram Bots of any kind
- Effort: advanced
TrevorC2 HTTP Communication
Detects TrevorC2 HTTP communication based on the HTTP request URI and the user-agent.
- Effort: elementary
User Account Created
Detects user creation on windows servers, which shouldn't happen in an Active Directory environment. Apply this on your windows server logs and not on your DC logs. One default account defaultuser0 is excluded as only used during Windows set-up. This detection use Security Event ID 4720.
- Effort: master
User Account Deleted
Detects local user deletion
- Effort: master
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Network device logs |
Check Point can record traffic events flowing through their firewall. |
Network protocol analysis |
Check Point firewall does traffic analysis at physical/data/transport layers |
Web logs |
Domain names are extracted from HTTP traffic |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "CEF:0|Check Point|VPN-1 & FireWall-1|Check Point|Log|HTTP_and_HTTPS_proxy|Unknown|act=Redirect destinationTranslatedAddress=1.1.1.1 destinationTranslatedPort=11680 deviceDirection=0 rt=1593013776000 sourceTranslatedAddress=0.0.0.0 sourceTranslatedPort=0 spt=53782 dpt=8080 cs2Label=Rule Name cs2=Explicit Proxy Access layer_name=Firewall layer_uuid=b8bf0a16-a447-47c3-8e7d-5e0061e17486 match_id=121 parent_rule=0 rule_action=Redirect rule_uid=37c21d26-f155-407a-9958-8584c1fd3320 ifname=eth1.60 logid=0 loguid={0x5ef37610,0x8,0x4d3c03bf,0xf33d4984} origin=2.2.2.2 originsicname=CN\\\\=ertfw01,O\\=foomgmt.foobar.local.zazgch sequencenum=133 version=5 dst=3.3.3.3 inzone=External nat_addtnl_rulenum=0 dhost=4.4.4.4 nat_rulenum=0 outzone=External product=VPN-1 & FireWall-1 proto=6 service_id=HTTP_and_HTTPS_proxy src=5.5.5.5",
"event": {
"code": "Log",
"outcome": "success"
},
"action": {
"name": "redirect",
"outcome": "success",
"properties": {
"loguid": "{0x5ef37610,0x8,0x4d3c03bf,0xf33d4984}",
"nat_addtnl_rulenum": "0",
"nat_rulenum": "0",
"observer_type": "VPN-1 & FireWall-1",
"origin": "2.2.2.2",
"originsicname": "CN=ertfw01,O=foomgmt.foobar.local.zazgch",
"product": "VPN-1 & FireWall-1",
"rule_name": "Explicit Proxy Access"
},
"target": "network-traffic"
},
"destination": {
"address": "3.3.3.3",
"domain": "4.4.4.4",
"ip": "3.3.3.3",
"nat": {
"ip": "1.1.1.1",
"port": 11680
},
"port": 8080,
"size_in_char": 7
},
"log": {
"hostname": "ertfw01"
},
"network": {
"direction": "inbound",
"transport": "tcp"
},
"observer": {
"egress": {
"zone": "External"
},
"ingress": {
"interface": {
"name": "eth1.60"
},
"zone": "External"
}
},
"related": {
"hosts": [
"4.4.4.4"
],
"ip": [
"0.0.0.0",
"1.1.1.1",
"3.3.3.3",
"5.5.5.5"
]
},
"rule": {
"uuid": "37c21d26-f155-407a-9958-8584c1fd3320",
"version": "5"
},
"service": {
"id": "HTTP_and_HTTPS_proxy"
},
"source": {
"address": "5.5.5.5",
"ip": "5.5.5.5",
"nat": {
"ip": "0.0.0.0",
"port": 0
},
"port": 53782
}
}
{
"message": "CEF:0||Check Point|Application Control|Check Point|Log|Log|Unknown|act=Accept deviceDirection=0 rt=1708352128000 requestMethod=CONNECT request=https://foo.bar.com:443 \nconn_direction=Internal ifname=bond151.410 logid=321 loguid={0x65d3627f,0x303,0x1b6410ac,0x145ca8a5} origin=192.168.10.250 \noriginsicname=CN\\=baz-fw-internet-1,O\\=HOSTNAME.intranet.corp.xd4pc5 sequencenum=1455 version=5 connection_luuid=4ac54d05-4f56-a0da-65d3-628000000003 hll_key=2847161932960334825 \nproduct=Application Control",
"event": {
"code": "Log",
"outcome": "success"
},
"action": {
"name": "accept",
"outcome": "success",
"properties": {
"loguid": "{0x65d3627f,0x303,0x1b6410ac,0x145ca8a5}",
"observer_type": "Application Control",
"origin": "192.168.10.250",
"originsicname": "CN=baz-fw-internet-1,O=HOSTNAME.intranet.corp.xd4pc5",
"product": "Application Control"
}
},
"http": {
"request": {
"method": "CONNECT"
}
},
"log": {
"hostname": "baz-fw-internet-1"
},
"network": {
"direction": "internal"
},
"observer": {
"ingress": {
"interface": {
"name": "bond151.410"
}
}
},
"rule": {
"version": "5"
},
"url": {
"domain": "foo.bar.com",
"full": "https://foo.bar.com:443",
"original": "https://foo.bar.com:443",
"port": 443,
"registered_domain": "bar.com",
"scheme": "https",
"subdomain": "foo",
"top_level_domain": "com"
}
}
{
"message": "0|Check Point|VPN-1 & FireWall-1|Check Point|Log|TCP_8000|Unknown|act=Accept deviceDirection=0 rt=1757320608000 spt=33108 dpt=8000 cs2Label=Rule Name layer_name=Company_GLOBAL_FW_Rules Security layer_uuid=11111111-1111-1111-1111-111111111111 match_id=318 parent_rule=0 rule_action=Accept rule_uid=22222222-2222-2222-2222-222222222222 conn_direction=Internal ifname=bond2.100 logid=0 loguid={0x5c4608f2,0xdc450628,0xd081d093,0x6c33af4d} origin=1.2.3.4 originsicname=CN\\=F88-G1ZFW10,O\\=F88mopPC01.company.com.ujwrfb sequencenum=78 version=5 dst=5.6.7.8 log_delay=1757320608 product=VPN-1 & FireWall-1 proto=6 service_id=TCP_8000 src=10.20.30.40",
"event": {
"code": "Log",
"outcome": "success"
},
"action": {
"name": "accept",
"outcome": "success",
"properties": {
"loguid": "{0x5c4608f2,0xdc450628,0xd081d093,0x6c33af4d}",
"observer_type": "VPN-1 & FireWall-1",
"origin": "1.2.3.4",
"originsicname": "CN=F88-G1ZFW10,O=F88mopPC01.company.com.ujwrfb",
"product": "VPN-1 & FireWall-1"
},
"target": "network-traffic"
},
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8",
"port": 8000
},
"log": {
"hostname": "F88-G1ZFW10"
},
"network": {
"direction": "internal",
"transport": "tcp"
},
"observer": {
"ingress": {
"interface": {
"name": "bond2.100"
}
}
},
"related": {
"ip": [
"10.20.30.40",
"5.6.7.8"
]
},
"rule": {
"uuid": "22222222-2222-2222-2222-222222222222",
"version": "5"
},
"service": {
"id": "TCP_8000"
},
"source": {
"address": "10.20.30.40",
"ip": "10.20.30.40",
"port": 33108
}
}
{
"message": "0|Check Point|VPN-1 & FireWall-1|Check Point|Log|Log|Unknown|act=Allow deviceDirection=1 rt=1592559930000 spt=137 dpt=137 alert=Undefined contextnum=2 ifname=eth2 logid=15 loguid={0x5eec893a,0x1c,0x47e0a0a,0xc0000000} origin=1.1.1.1 originsicname=CN\\=foobarfw002,O\\=foomgmt.foobar.local.zazgch sequencenum=61 version=5 context_num=2 dst=2.2.2.2 hll_key=13306743300460385727 product=VPN-1 & FireWall-1 proto=17 reason=Firewall - Protocol violation detected with protocol:(NetBIOS Name Service), matched protocol sig_id:(8), violation sig_id:(17). (500) src=3.3.3.3",
"event": {
"code": "Log",
"outcome": "success"
},
"action": {
"name": "allow",
"outcome": "success",
"properties": {
"loguid": "{0x5eec893a,0x1c,0x47e0a0a,0xc0000000}",
"observer_type": "VPN-1 & FireWall-1",
"origin": "1.1.1.1",
"originsicname": "CN=foobarfw002,O=foomgmt.foobar.local.zazgch",
"product": "VPN-1 & FireWall-1"
},
"target": "network-traffic"
},
"destination": {
"address": "2.2.2.2",
"ip": "2.2.2.2",
"port": 137
},
"log": {
"hostname": "foobarfw002"
},
"network": {
"direction": "outbound",
"transport": "udp"
},
"observer": {
"ingress": {
"interface": {
"name": "eth2"
}
}
},
"related": {
"ip": [
"2.2.2.2",
"3.3.3.3"
]
},
"rule": {
"version": "5"
},
"source": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"port": 137
}
}
{
"message": "CEF:0||Check Point|VPN-1 & FireWall-1|Check Point|Log|domain-udp|Unknown|act=Accept deviceDirection=0 rt=1708352128000 spt=63858 dpt=53 cs2Label=Rule Name cs2=Communication DNS \n cs2=vers les ressources internes layer_name=Network layer_name=Application layer_uuid=86db1685-ca63-4fcd-b296-c15c99acfc76 layer_uuid=1d7f95ec-0774-4916-a1b4-e8ab1d2d9cae match_id=169 \n match_id=738197621 parent_rule=0 parent_rule=0 rule_action=Accept rule_action=Accept rule_uid=713de10c-0d41-44af-a2e3-fa4d697c515a rule_uid=9ede1042-638a-45cb-bf2f-f72f1e1b7d97 \n ifname=bond150.240 logid=0 loguid={0xb6666b4,0x11fbf15b,0x98b64f96,0x6772cf4d} origin=192.168.10.242 originsicname=CN\\=cip-fw-core-1.intranet.corp,O\\=HOSTNAME.intranet.corp.xd4pc5 \n sequencenum=547 version=5 dst=172.16.111.111 inzone=Internal outzone=Internal product=VPN-1 & FireWall-1 proto=17 service_id=domain-udp src=10.0.11.11",
"event": {
"code": "Log",
"outcome": "success"
},
"action": {
"name": "accept",
"outcome": "success",
"properties": {
"loguid": "{0xb6666b4,0x11fbf15b,0x98b64f96,0x6772cf4d}",
"observer_type": "VPN-1 & FireWall-1",
"origin": "192.168.10.242",
"originsicname": "CN=cip-fw-core-1.intranet.corp,O=HOSTNAME.intranet.corp.xd4pc5",
"product": "VPN-1 & FireWall-1",
"rule_name": "Communication DNS"
},
"target": "network-traffic"
},
"destination": {
"address": "172.16.111.111",
"ip": "172.16.111.111",
"port": 53
},
"log": {
"hostname": "cip-fw-core-1.intranet.corp"
},
"network": {
"direction": "inbound",
"transport": "udp"
},
"observer": {
"egress": {
"zone": "Internal"
},
"ingress": {
"interface": {
"name": "bond150.240"
},
"zone": "Internal"
}
},
"related": {
"ip": [
"10.0.11.11",
"172.16.111.111"
]
},
"rule": {
"uuid": "713de10c-0d41-44af-a2e3-fa4d697c515a",
"version": "5"
},
"service": {
"id": "domain-udp"
},
"source": {
"address": "10.0.11.11",
"ip": "10.0.11.11",
"port": 63858
}
}
{
"message": "0|Check Point|VPN-1 & FireWall-1|Check Point|Decrypt|https|Unknown|act=Decrypt cs2Label=Peer Gateway cs2=1.1.1.1 deviceDirection=0 dhost= hostname@group.corp \n duser=Firstname1, LASTNAME1 ( FLASTNAME1) Firstname2, Lastname2 (ADM) (FOO12345) duser=LASTNAME3, Firstname3 (ABC12345) rt=1708352039000 shost=hostname00100@group.corp spt=49967 dpt=443 suser=LASTNAME3, Firstname3 \n (ABC12345) cs2Label=Rule Name cs2=Implicit Cleanup layer_name=PROD_SEPTEMBRE_2020_QOS Security layer_name=PROD_SEPTEMBRE_2020_QOS Application layer_uuid=f3e58f17-af95-43fa-82a8-a10f86cd22 \n layer_uuid=aa29b5d0-08ef-4541-9c08-fe7335324262 match_id=129 match_id=33554431 parent_rule=0 parent_rule=0 rule_action=Accept rule_action=Accept rule_uid=310aff93-4aed-4616-a061-4aef36eebc \n ifname=eth1 logid=0 loguid={0xa2198857,0x26b6c7dd,0x93bd692b,0xa64ec6bf} origin=2.2.2.2 originsicname=CN\\=BODFW1,O\\=FWMGNT.corpsubdomain.corp.s65fuv sequencenum=207 version=5 \n community=VPN_FOO_434 dst=192.168.111.111 dst_user_dn=CN\\=Firstname1\\, LASTNAME1,OU\\=exterieur,OU\\=Migration exchange faite,OU\\=Migres_AD,OU\\=Users,OU\\=BOD,DC\\=group,DC\\=corp CN\\= Firstname2\\, \n Lastname2 (ADM),OU\\=Admin Accounts,OU\\=ADMIN,DC\\=group,DC\\=corp fw_subproduct=VPN-1 https_inspection_action=Bypass inzone=External methods:=ESP: AES-256 + SHA256 + PFS (group 14) \n nat_addtnl_rulenum=0 nat_rule_uid=a1fdbc3b-b993-4ea9-972c-07ae43e09acb nat_rulenum=61 outzone=Internal product=VPN-1 & FireWall-1 proto=6 scheme:=IKE service_id=https src=10.1.11.111 \n src_user_dn=CN\\=LASTNAME3\\, Firstname3,OU\\=Internes,OU\\=Users,OU\\=ORY,DC\\=group,DC\\=corp vpn_feature_name=VPN ",
"event": {
"code": "Decrypt",
"outcome": "success"
},
"action": {
"name": "decrypt",
"outcome": "success",
"properties": {
"community": "VPN_FOO_434",
"loguid": "{0xa2198857,0x26b6c7dd,0x93bd692b,0xa64ec6bf}",
"nat_addtnl_rulenum": "0",
"nat_rulenum": "61",
"observer_type": "VPN-1 & FireWall-1",
"origin": "2.2.2.2",
"originsicname": "CN=BODFW1,O=FWMGNT.corpsubdomain.corp.s65fuv",
"product": "VPN-1 & FireWall-1",
"subproduct": "VPN-1",
"vpn_feature_name": "VPN"
},
"target": "network-traffic"
},
"destination": {
"address": "192.168.111.111",
"domain": "hostname@group.corp",
"ip": "192.168.111.111",
"port": 443,
"size_in_char": 19,
"user": {
"name": "Firstname1, LASTNAME1 ( FLASTNAME1) Firstname2, Lastname2 (ADM) (FOO12345)"
}
},
"log": {
"hostname": "BODFW1"
},
"network": {
"direction": "inbound",
"transport": "6 scheme:=ike"
},
"observer": {
"egress": {
"zone": "Internal"
},
"ingress": {
"interface": {
"name": "eth1"
},
"zone": "External methods:=ESP: AES-256 + SHA256 + PFS (group 14)"
}
},
"related": {
"hosts": [
"hostname00100@group.corp",
"hostname@group.corp"
],
"ip": [
"10.1.11.111",
"192.168.111.111"
],
"user": [
"Firstname1, LASTNAME1 ( FLASTNAME1) Firstname2, Lastname2 (ADM) (FOO12345)",
"LASTNAME3, Firstname3 (ABC12345)"
]
},
"rule": {
"uuid": "310aff93-4aed-4616-a061-4aef36eebc",
"version": "5"
},
"service": {
"id": "https"
},
"source": {
"address": "10.1.11.111",
"domain": "hostname00100@group.corp",
"ip": "10.1.11.111",
"port": 49967,
"size_in_char": 24,
"user": {
"name": "LASTNAME3, Firstname3 (ABC12345)"
}
}
}
{
"message": "CEF: 0|Check Point|VPN-1 & FireWall-1|Check Point|Log|UDP_443|Unknown|act=Drop deviceDirection=0 duser=FIRSTNAME LASTNAME (FILA10052418) rt=1592559931000 shost=footlt327@ad.mycorp.com spt=56379 dpt=443 suser=FIRSTNAME LASTNAME (FILA10052418) cs2Label=Rule Name layer_name=Firewall layer_uuid=b8bf0a16-a447-47c3-8e7d-5e0061e17486 match_id=139 parent_rule=0 rule_action=Drop rule_uid=9c6de769-d2ab-4f1c-bd3b-5d2180af9844 ifname=Mgmt.3 logid=0 loguid={0x5eec893c,0x3,0x46416ac,0x16efadda} origin=2.2.2.2 originsicname=CN\\=ertfw01,O\\=foomgmt.foobar.local.zazgch sequencenum=299 version=5 dst=4.4.4.4 inzone=Internal outzone=External product=VPN-1 & FireWall-1 proto=17 service_id=UDP_443 src=3.3.3.3 src_user_dn=CN\\=FIRSTNAME LASTNAME,OU\\=Users,OU\\=ServiceDesk,DC\\=ad,DC\\=mycorp,DC\\=com",
"event": {
"code": "Log",
"outcome": "success"
},
"action": {
"name": "drop",
"outcome": "success",
"properties": {
"loguid": "{0x5eec893c,0x3,0x46416ac,0x16efadda}",
"observer_type": "VPN-1 & FireWall-1",
"origin": "2.2.2.2",
"originsicname": "CN=ertfw01,O=foomgmt.foobar.local.zazgch",
"product": "VPN-1 & FireWall-1"
},
"target": "network-traffic"
},
"destination": {
"address": "4.4.4.4",
"ip": "4.4.4.4",
"port": 443,
"user": {
"name": "FIRSTNAME LASTNAME (FILA10052418)"
}
},
"log": {
"hostname": "ertfw01"
},
"network": {
"direction": "inbound",
"transport": "udp"
},
"observer": {
"egress": {
"zone": "External"
},
"ingress": {
"interface": {
"name": "Mgmt.3"
},
"zone": "Internal"
}
},
"related": {
"hosts": [
"footlt327@ad.mycorp.com"
],
"ip": [
"3.3.3.3",
"4.4.4.4"
],
"user": [
"FIRSTNAME LASTNAME (FILA10052418)"
]
},
"rule": {
"uuid": "9c6de769-d2ab-4f1c-bd3b-5d2180af9844",
"version": "5"
},
"service": {
"id": "UDP_443"
},
"source": {
"address": "3.3.3.3",
"domain": "footlt327@ad.mycorp.com",
"ip": "3.3.3.3",
"port": 56379,
"size_in_char": 23,
"user": {
"name": "FIRSTNAME LASTNAME (FILA10052418)"
}
}
}
{
"message": "CEF:0|Check Point|VPN-1 & FireWall-1|Check Point|Log|Log|Unknown|act=Drop cs4Label=TCP Flags cs4=SYN-ACK deviceDirection=0 rt=1723938549000 spt=443 dpt=2384 ifname=test151.420 logid=1 loguid={0x66c136f5,0xf4,0x1b6410ac,0x151daa25} origin=1.2.3.4 originsicname=CN=cip-fw-test-1,O=CPSRVP.test.test sequencenum=103 version=5 dst=3.4.5.6 product=VPN-1 & FireWall-1 proto=6 src=1.2.3.4 tcp_packet_out_of_state=First packet isn't SYN",
"event": {
"code": "Log",
"outcome": "success"
},
"action": {
"name": "drop",
"outcome": "success",
"properties": {
"loguid": "{0x66c136f5,0xf4,0x1b6410ac,0x151daa25}",
"observer_type": "VPN-1 & FireWall-1",
"origin": "1.2.3.4",
"originsicname": "CN=cip-fw-test-1,O=CPSRVP.test.test",
"product": "VPN-1 & FireWall-1"
},
"target": "network-traffic"
},
"checkpoint": {
"firewall": {
"tcp_flags": "SYN-ACK"
}
},
"destination": {
"address": "3.4.5.6",
"ip": "3.4.5.6",
"port": 2384
},
"log": {
"hostname": "cip-fw-test-1"
},
"network": {
"direction": "inbound",
"transport": "tcp"
},
"observer": {
"ingress": {
"interface": {
"name": "test151.420"
}
}
},
"related": {
"ip": [
"1.2.3.4",
"3.4.5.6"
]
},
"rule": {
"version": "5"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 443
}
}
{
"message": "CEF:0||Check Point|VPN-1 & FireWall-1|Check Point|geo_protection|Log|Unknown|act=Accept \ncs3Label=Protection Type cs3=geo_protection deviceDirection=0 rt=1708352128000 spt=56935 dpt=53 \nifname=bond151.421 logid=65536 loguid={0x65d3627f,0x31d,0x1b6410ac,0x145ca8a5} origin=2.2.2.2 \noriginsicname=CN\\=cip-fw-internet-1,O\\=HOSTNAME.intranet.corp.xd4pc5 sequencenum=1496 version=5 \ndst=3.3.3.3 dst_country=Other inspection_information=Geo-location inbound enforcement \ninspection_profile=Block_Pays_a_Risque product=VPN-1 & FireWall-1 proto=17 src=1.1.1.1 \nsrc_country=Internal",
"event": {
"code": "geo_protection",
"outcome": "success"
},
"action": {
"name": "accept",
"outcome": "success",
"properties": {
"loguid": "{0x65d3627f,0x31d,0x1b6410ac,0x145ca8a5}",
"observer_type": "VPN-1 & FireWall-1",
"origin": "2.2.2.2",
"originsicname": "CN=cip-fw-internet-1,O=HOSTNAME.intranet.corp.xd4pc5",
"product": "VPN-1 & FireWall-1"
},
"target": "network-traffic"
},
"destination": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"port": 53
},
"log": {
"hostname": "cip-fw-internet-1"
},
"network": {
"direction": "inbound",
"transport": "udp"
},
"observer": {
"ingress": {
"interface": {
"name": "bond151.421"
}
}
},
"related": {
"ip": [
"1.1.1.1",
"3.3.3.3"
]
},
"rule": {
"version": "5"
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"port": 56935
}
}
{
"message": "CEF: 0|Check Point|HTTPS Inspection|Check Point|Log|Log|Unknown|act=HTTPS Bypass cs5Label=Matched Category deviceDirection=0 duser=USER-LASTNAME USER-FIRSTNAME (ULUF10004820) rt=1592559938000 shost=FooHost@ad.mycorp.com spt=56891 dpt=443 suser=USER-LASTNAME USER-FIRSTNAME (ULUF10004820) ifname=Mgmt.3 loguid={0x5eec8942,0x13,0x46416ac,0x16efadda} origin=2.2.2.2 originsicname=CN\\=ertfw01,O\\=foomgmt.foobar.local.zazgch sequencenum=324 version=5 dst=3.3.3.3 https_inspection_action=Bypass https_inspection_rule_id={DD126F7C-B373-4331-8632-DBA1EFDD0D6A} https_inspection_rule_name=Bypass for FooBar product=HTTPS Inspection proto=6 snid=0 src=1.1.1.1 src_user_dn=CN\\=USER-LASTNAME USER-FIRSTNAME,OU\\=Users,OU\\=ServiceDesk,DC\\=ad,DC\\=mycorp,DC\\=com",
"event": {
"code": "Log",
"outcome": "success"
},
"action": {
"name": "https bypass",
"outcome": "success",
"properties": {
"loguid": "{0x5eec8942,0x13,0x46416ac,0x16efadda}",
"observer_type": "HTTPS Inspection",
"origin": "2.2.2.2",
"originsicname": "CN=ertfw01,O=foomgmt.foobar.local.zazgch",
"product": "HTTPS Inspection"
},
"target": "network-traffic"
},
"destination": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"port": 443,
"user": {
"name": "USER-LASTNAME USER-FIRSTNAME (ULUF10004820)"
}
},
"log": {
"hostname": "ertfw01"
},
"network": {
"direction": "inbound",
"transport": "tcp"
},
"observer": {
"ingress": {
"interface": {
"name": "Mgmt.3"
}
}
},
"related": {
"hosts": [
"FooHost@ad.mycorp.com"
],
"ip": [
"1.1.1.1",
"3.3.3.3"
],
"user": [
"USER-LASTNAME USER-FIRSTNAME (ULUF10004820)"
]
},
"rule": {
"version": "5"
},
"source": {
"address": "1.1.1.1",
"domain": "FooHost@ad.mycorp.com",
"ip": "1.1.1.1",
"port": 56891,
"size_in_char": 21,
"user": {
"name": "USER-LASTNAME USER-FIRSTNAME (ULUF10004820)"
}
}
}
{
"message": "CEF:0||Check Point|VPN-1 & FireWall-1|Check Point|Log|https|Unknown|act=Accept app=HTTPS destinationTranslatedAddress=0.0.0.0 destinationTranslatedPort=0 deviceDirection=0 \nduser=LASTNAME FIRSTNAME (CORP0000583) rt=1708352128000 sourceTranslatedAddress=1.1.1.1 sourceTranslatedPort=12435 spt=56688 dpt=443 suser=LASTNAME FIRSTNAME (CORP0000583) \ncs2Label=Rule Name cs2=Updatable Objects Services Microsoft layer_name=Network layer_name=Application layer_uuid=86db1685-ca63-4fcd-b296-c15c99acfc76 \nlayer_uuid=1d7f95ec-0774-4916-a1b4-e8ab1d2d9cae match_id=267 match_id=637534254 parent_rule=0 parent_rule=0 rule_action=Accept rule_action=Accept \nrule_uid=6426c486-c108-47b0-9c72-0adf917d7a0f rule_uid=bc9b26a7-f0fa-431d-81a2-6252f9f203a8 conn_direction=Outgoing contextnum=1 ifname=bond151.410 logid=0 \nloguid={0x611c9f51,0x8c73c182,0xe99e964e,0x2addea20} origin=192.168.111.111 originsicname=CN\\=cip-fw-internet-1,O\\=HOSTNAME.intranet.corp.xd4pc5 sequencenum=1271 version=5 \ncertificate_validity=Trusted context_num=1 dst=2.2.2.2 dst_uo_icon=@app/cp_azure_azure dst_uo_name=Azure Services hll_key=6406281760033809592 https_inspection_action=Bypass \ninzone=Internal nat_addtnl_rulenum=0 nat_rule_uid=1e99e081-d7f7-4bd8-b4fe-a40dc90e4230 nat_rulenum=114 needs_browse_time=1 outzone=External product=VPN-1 & FireWall-1 proto=6 \nservice_id=https sig_id=4 sni=eu-mobile.events.data.microsoft.com src=3.3.3.3 src_user_dn=CN\\=LASTNAME FIRSTNAME,OU\\=Service Medical et Detection des Fraudes,OU\\=Relations \nClient,OU\\=Direction des Op\u00e9rations,OU\\=Services,OU\\=Users_Std_XP,OU\\=Siege,OU\\=France,DC\\=intranet,DC\\=corp tls_server_host_name=eu-mobile.events.data.microsoft.com",
"event": {
"code": "Log",
"outcome": "success"
},
"action": {
"name": "accept",
"outcome": "success",
"properties": {
"loguid": "{0x611c9f51,0x8c73c182,0xe99e964e,0x2addea20}",
"nat_addtnl_rulenum": "0",
"nat_rulenum": "114",
"observer_type": "VPN-1 & FireWall-1",
"origin": "192.168.111.111",
"originsicname": "CN=cip-fw-internet-1,O=HOSTNAME.intranet.corp.xd4pc5",
"product": "VPN-1 & FireWall-1",
"rule_name": "Updatable Objects Services Microsoft"
},
"target": "network-traffic"
},
"destination": {
"address": "2.2.2.2",
"ip": "2.2.2.2",
"nat": {
"ip": "0.0.0.0",
"port": 0
},
"port": 443,
"user": {
"name": "LASTNAME FIRSTNAME (CORP0000583)"
}
},
"log": {
"hostname": "cip-fw-internet-1"
},
"network": {
"direction": "outgoing",
"protocol": "https",
"transport": "tcp"
},
"observer": {
"egress": {
"zone": "External"
},
"ingress": {
"interface": {
"name": "bond151.410"
},
"zone": "Internal"
}
},
"related": {
"ip": [
"0.0.0.0",
"1.1.1.1",
"2.2.2.2",
"3.3.3.3"
],
"user": [
"LASTNAME FIRSTNAME (CORP0000583)"
]
},
"rule": {
"uuid": "6426c486-c108-47b0-9c72-0adf917d7a0f",
"version": "5"
},
"service": {
"id": "https"
},
"source": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"nat": {
"ip": "1.1.1.1",
"port": 12435
},
"port": 56688,
"user": {
"name": "LASTNAME FIRSTNAME (CORP0000583)"
}
}
}
{
"message": "0|Check Point|SmartDefense|Check Point|IPS|Web Server Exposed Git Repository Information Disclosure|Very-High|act=Detect cp_severity=Very-High cnt=1 cs1Label=Threat Prevention Rule Name cs2Label=Protection ID cs2=asm_dynamic_prop_GIT_EXPOSED cs3Label=Protection Type cs3=IPS cs4Label=Protection Name cs4=Web Server Exposed Git Repository Information Disclosure cs4Label=Threat Prevention Rule ID cs4={115C1043-DF8A-48D4-96CB-0200C1F1499A} deviceDirection=1 flexNumber1Label=Confidence flexNumber1=5 flexNumber2Label=Performance Impact flexNumber2=3 flexString2Label=Attack Information flexString2=Web Server Exposed Git Repository Information Disclosure in=52 msg=Web Server Enforcement Violation out=0 request=http://9.10.11.12/.git/config requestMethod=GET rt=1722861810000 spt=51451 dpt=80 cs4Label=Threat Prevention Rule ID cs4={115C1043-DF8A-48D4-96CB-0200C1F1499A} cs4={6E7AA7B4-FD2A-40A3-ACDE-AC1182F1120F} cs1Label=Threat Prevention Rule Name cs1=Antibot + TE EAP layer_name=IPS layer_uuid={1DA55D35-9A2B-4141-A512-150DC635378B} layer_uuid={368D4C86-B4FD-4EF9-9AED-E58C4C0DEE7F} smartdefense_profile=EAP_Prevent smartdefense_profile=Profil_EAP_Anti-Bot_TE ifname=bond1.103 loguid={0x611c9f51,0x8c73c182,0xe99e964e,0x2addea20} origin=192.168.203.80 originsicname=CN\\=MyGW,O\\=MyDomain_Server.checkpoint.com.s6t98x sequencenum=85 version=5 description_url=GIT_EXPOSED_help.html dst=1.2.3.4 lastupdatetime=1722861871 log_id=2 policy=2016-12_Prolix_Migration-FW policy_time=1722591913 product=SmartDefense proto=6 proxy_src_ip=5.6.7.8 reject_id_kid=66b0c8f2-2-a5f697e5-ce3758d7 rule_uid=e70129a9-2a18-4075-8042-b85f0b601ca4 ser_agent_kid=Safari 4.0 session_id={0x66b06cef,0x11,0x9b1c4c53,0xdf840ae7} smartdefense_profile=EAP_Prevent src=5.6.7.8 tags=Vendor_Git Product_Web_Servers Threat_Year_2015 Threat_Prevalence_True Protection_Type_Vulnerability Product_Prevalence_Common Tuning_Non_Configurable Protocol_HTTP Direction_SERVER",
"event": {
"code": "IPS",
"message": "Web Server Enforcement Violation",
"outcome": "success"
},
"action": {
"name": "detect",
"outcome": "success",
"outcome_reason": "Web Server Enforcement Violation",
"properties": {
"loguid": "{0x611c9f51,0x8c73c182,0xe99e964e,0x2addea20}",
"observer_type": "SmartDefense",
"origin": "192.168.203.80",
"originsicname": "CN=MyGW,O=MyDomain_Server.checkpoint.com.s6t98x",
"product": "SmartDefense"
},
"target": "network-traffic"
},
"destination": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 80
},
"http": {
"request": {
"method": "GET"
}
},
"log": {
"hostname": "MyGW",
"level": "Very-High"
},
"network": {
"direction": "outbound",
"forwarded_ip": "5.6.7.8",
"transport": "tcp"
},
"observer": {
"ingress": {
"interface": {
"name": "bond1.103"
}
}
},
"related": {
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"rule": {
"uuid": "e70129a9-2a18-4075-8042-b85f0b601ca4",
"version": "5"
},
"source": {
"address": "5.6.7.8",
"ip": "5.6.7.8",
"port": 51451
},
"url": {
"domain": "9.10.11.12",
"full": "http://9.10.11.12/.git/config",
"original": "http://9.10.11.12/.git/config",
"path": "/.git/config",
"port": 80,
"scheme": "http"
}
}
{
"message": "CEF: 0|Check Point|HTTPS Inspection|Check Point|Log|Log|Unknown|act=Reject deviceDirection=0 duser=LASTNAME FIRSTNAME (CORPO10004953) msg=SSL version is not supported. rt=1592575034000 spt=60144 dpt=443 suser=LASTNAME FIRSTNAME (CORPO10004953) loguid={0x5eecc43b,0x2,0x46416ac,0x16efadda} origin=1.1.1.1 originsicname=CN\\=foobarfw002,O\\=foomgmt.foobar.local.zazgch sequencenum=148 version=5 dst=2.2.2.2 https_validation=unsupported product=HTTPS Inspection proto=6 snid=0 src=3.3.3.3 src_user_dn=CN\\=LASTNAME FIRSTNAME,OU\\=Users,OU\\=ServiceDesk,DC\\=ad,DC\\=mycorp,DC\\=com",
"event": {
"code": "Log",
"message": "SSL version is not supported.",
"outcome": "success"
},
"action": {
"name": "reject",
"outcome": "success",
"outcome_reason": "SSL version is not supported.",
"properties": {
"loguid": "{0x5eecc43b,0x2,0x46416ac,0x16efadda}",
"observer_type": "HTTPS Inspection",
"origin": "1.1.1.1",
"originsicname": "CN=foobarfw002,O=foomgmt.foobar.local.zazgch",
"product": "HTTPS Inspection"
},
"target": "network-traffic"
},
"destination": {
"address": "2.2.2.2",
"ip": "2.2.2.2",
"port": 443,
"user": {
"name": "LASTNAME FIRSTNAME (CORPO10004953)"
}
},
"log": {
"hostname": "foobarfw002"
},
"network": {
"direction": "inbound",
"transport": "tcp"
},
"related": {
"ip": [
"2.2.2.2",
"3.3.3.3"
],
"user": [
"LASTNAME FIRSTNAME (CORPO10004953)"
]
},
"rule": {
"version": "5"
},
"source": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"port": 60144,
"user": {
"name": "LASTNAME FIRSTNAME (CORPO10004953)"
}
}
}
{
"message": "0|Check Point|SmartDefense|Check Point|IPS|Syslog Message Length Enforcement|Medium|act=Detect cp_severity=Medium cnt=53 cs1Label=Threat Prevention Rule Name cs2Label=Protection ID cs2=02syslg_max_msg_len_tab cs3Label=Protection Type cs3=IPS cs4Label=Protection Name cs4=Syslog Message Length Enforcement cs4Label=Threat Prevention Rule ID cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} deviceDirection=1 flexNumber1Label=Confidence flexNumber1=1 flexNumber2Label=Performance Impact flexNumber2=2 flexString2Label=Attack Information flexString2=phpFileManager cmd Parameter Command Execution in=0 msg=Syslog Protocol Violation out=0 rt=1705349059000 spt=57789 dpt=514 Signature=CVE-1999-0063, CVE-1999-0381 cs4Label=Threat Prevention Rule ID cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs4={C29BF96E-4967-4BC0-9759-8CD2E668D37E} cs1Label=Threat Prevention Rule Name layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_name=dn Threat Prevention layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} layer_uuid={FB7CC4DE-9326-4CB5-9CDF-33A2996F1F57} smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy smartdefense_profile=XXXX_IPS_policy ifname=eth5.996 loguid={0xc4f7efea,0x4a15abc5,0x796000a8,0x18edf12d} origin=3.4.5.6 originsicname=CN\\=DN-EXAMPLE,O\\=alfi.defo.ccse.nl sequencenum=12 version=5 capture_uuid={0x65a58fcb,0x1,0x4d1f8365,0xc5a8726d} description_url=02syslg_max_msg_len_tab_help.html dst=5.6.7.8 lastupdatetime=1705352059 log_id=2 policy=dn policy_time=1705348793 product=SmartDefense proto=17 rule_uid=b16110f0-fc9f-43b1-9f87-a8ad3f995237 session_id={0x65a58fc3,0x3,0x4d1f8365,0xc5a8726d} smartdefense_profile=XXXX_IPS_policy src=1.2.3.4",
"event": {
"code": "IPS",
"message": "Syslog Protocol Violation",
"outcome": "success"
},
"action": {
"name": "detect",
"outcome": "success",
"outcome_reason": "Syslog Protocol Violation",
"properties": {
"loguid": "{0xc4f7efea,0x4a15abc5,0x796000a8,0x18edf12d}",
"observer_type": "SmartDefense",
"origin": "3.4.5.6",
"originsicname": "CN=DN-EXAMPLE,O=alfi.defo.ccse.nl",
"product": "SmartDefense",
"signature": [
"CVE-1999-0063",
"CVE-1999-0381"
]
},
"target": "network-traffic"
},
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8",
"port": 514
},
"log": {
"hostname": "DN-EXAMPLE",
"level": "Medium"
},
"network": {
"direction": "outbound",
"transport": "udp"
},
"observer": {
"ingress": {
"interface": {
"name": "eth5.996"
}
}
},
"related": {
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"rule": {
"uuid": "b16110f0-fc9f-43b1-9f87-a8ad3f995237",
"version": "5"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 57789
}
}
{
"message": "CEF: 0|Check Point|VPN-1 & FireWall-1|Check Point|Log|TCP_135|Unknown|act=Accept deviceDirection=0 rt=1592498107000 spt=62170 dpt=135 cs2Label=Rule Name cs2=Allow all layer_name=Firewall FooBar layer_name=FooBar_policy Application layer_uuid=66f2e247-8237-4d61-b2e9-e4595c7a439c layer_uuid=b66dac35-e2a9-4a13-91bc-21cb9cafb3da match_id=19 match_id=16777244 parent_rule=0 parent_rule=0 rule_action=Accept rule_action=Accept rule_uid=378884f4-0844-4bbb-a5cb-22e9c88d4d09 rule_uid=43b8404c-809b-4f35-927e-2c05b3d28e53 conn_direction=Internal contextnum=1 ifname=eth2 logid=0 loguid={0x5eeb97bb,0x4,0x47e0a0a,0xc0000001} origin=1.1.1.1 originsicname=CN\\=foobarfw002,O\\=foomgmt.foobar.local.zazgch sequencenum=19 version=5 context_num=1 dst=2.2.2.2 hll_key=5221004884709257555 inzone=Internal outzone=Internal product=VPN-1 & FireWall-1 proto=6 service_id=TCP_135 src=3.3.3.3",
"event": {
"code": "Log",
"outcome": "success"
},
"action": {
"name": "accept",
"outcome": "success",
"properties": {
"loguid": "{0x5eeb97bb,0x4,0x47e0a0a,0xc0000001}",
"observer_type": "VPN-1 & FireWall-1",
"origin": "1.1.1.1",
"originsicname": "CN=foobarfw002,O=foomgmt.foobar.local.zazgch",
"product": "VPN-1 & FireWall-1",
"rule_name": "Allow all"
},
"target": "network-traffic"
},
"destination": {
"address": "2.2.2.2",
"ip": "2.2.2.2",
"port": 135
},
"log": {
"hostname": "foobarfw002"
},
"network": {
"direction": "internal",
"transport": "tcp"
},
"observer": {
"egress": {
"zone": "Internal"
},
"ingress": {
"interface": {
"name": "eth2"
},
"zone": "Internal"
}
},
"related": {
"ip": [
"2.2.2.2",
"3.3.3.3"
]
},
"rule": {
"uuid": "378884f4-0844-4bbb-a5cb-22e9c88d4d09",
"version": "5"
},
"service": {
"id": "TCP_135"
},
"source": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"port": 62170
}
}
{
"message": "CEF:0||Check Point|URL Filtering|Check Point|News / Media|domain.fr|Unknown|act=Accept app=HTTP \ndeviceDirection=0 duser=LASTNAME FIRSTNAME (CORP0025465) requestClientApplication=Google Chrome rt=1708352128000 dpt=8080 \nsuser=LASTNAME FIRSTNAME (CORP0025465) cp_app_risk=Unknown cp_app_risk=Unknown cs6Label=Application Name cs6=domain.fr \ncs5Label=Matched Category cs5=News / Media flexString1Label=Application Signature ID cs2Label=Rule Name cs2=vers les ressources\ninternes app_category=News / Media app_id=0 app_id=2108684536 app_properties=News / Media,URL Filtering layer_name=Network \nlayer_name=Application layer_uuid=86db1685-ca63-4fcd-b296-c15c99acfc76 layer_uuid=1d7f95ec-0774-4916-a1b4-e8ab1d2d9cae \nmatch_id=273 match_id=637534325 parent_rule=0 parent_rule=0 rule_action=Accept rule_action=Accept \nrule_uid=427fb6b8-dcf9-471a-a346-7c603f4a0852 rule_uid=9ede1042-638a-45cb-bf2f-f72f1e1b7d97 cp_app_risk=Unknown \ncs6Label=Application Name cs6=domain.fr cs5Label=Matched Category cs5=News / Media flexString1Label=Application Signature ID \napp_category=News / Media app_id=2108684536 app_properties=News / Media,URL Filtering requestMethod=CONNECT \nrequest=https://subdomain.domain.fr:443 conn_direction=Internal ifname=bond151.410 logid=256 \nloguid={0xb8627f78,0x96aeacb2,0xe1a3617f,0x615f333f} origin=192.168.111.123 \noriginsicname=CN\\=cip-fw-internet-1,O\\=HOSTNAME.intranet.corp.xd4pc5 sequencenum=1362 version=5 aggregated_log_count=1 \nbrowse_time=0 client_type_os=Windows 10 connection_count=1 creation_time=1708352128 dst=192.168.111.111 duration=0 \nhll_key=16778521701015169890 inzone=Internal last_hit_time=1708352128 outzone=Internal product=URL Filtering proto=6 \nservice_id=HTTP_and_HTTPS_proxy sig_id=0 src=192.168.222.222 src_user_dn=CN\\=LASTNAME \nFIRSTNAME,OU\\=Users_CC,OU\\=RC,OU\\=France,DC\\=intranet,DC\\=corp update_count=1 user_agent=Mozilla/5.0 (Windows NT 10.0; WOW64) \nAppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.190 Safari/537.36",
"event": {
"code": "News / Media",
"outcome": "success"
},
"action": {
"name": "accept",
"outcome": "success",
"properties": {
"loguid": "{0xb8627f78,0x96aeacb2,0xe1a3617f,0x615f333f}",
"observer_type": "URL Filtering",
"origin": "192.168.111.123",
"originsicname": "CN=cip-fw-internet-1,O=HOSTNAME.intranet.corp.xd4pc5",
"product": "URL Filtering",
"rule_name": "vers les ressources\ninternes"
},
"target": "network-traffic"
},
"destination": {
"address": "192.168.111.111",
"ip": "192.168.111.111",
"port": 8080,
"user": {
"name": "LASTNAME FIRSTNAME (CORP0025465)"
}
},
"http": {
"request": {
"method": "CONNECT"
}
},
"log": {
"hostname": "cip-fw-internet-1"
},
"network": {
"direction": "internal",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"zone": "Internal"
},
"ingress": {
"interface": {
"name": "bond151.410"
},
"zone": "Internal"
}
},
"related": {
"ip": [
"192.168.111.111",
"192.168.222.222"
],
"user": [
"LASTNAME FIRSTNAME (CORP0025465)"
]
},
"rule": {
"uuid": "427fb6b8-dcf9-471a-a346-7c603f4a0852",
"version": "5"
},
"service": {
"id": "HTTP_and_HTTPS_proxy"
},
"source": {
"address": "192.168.222.222",
"ip": "192.168.222.222",
"user": {
"name": "LASTNAME FIRSTNAME (CORP0025465)"
}
},
"url": {
"domain": "subdomain.domain.fr",
"full": "https://subdomain.domain.fr:443",
"original": "https://subdomain.domain.fr:443",
"port": 443,
"registered_domain": "domain.fr",
"scheme": "https",
"subdomain": "subdomain",
"top_level_domain": "fr"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Chrome",
"original": "Mozilla/5.0 (Windows NT 10.0; WOW64) \nAppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.190 Safari/537.36",
"os": {
"name": "Windows",
"version": "10"
},
"version": "88.0.4324"
}
}
{
"message": "\"1832941\" \"20Dec2019\" \"12:04:05\" \"eth1\" \"2.2.2.2\" \"Log\" \"Decrypt\" \"\" \"\" \"3.3.3.3\" \"1.1.1.1\" \"icmp\" \"5\" \"Supervision\" \"5-FooBar_Policy\" \"\" \"inzone: External; outzone: Internal; service_id: icmp-proto; ICMP: Echo Request; ICMP Type: 8; ICMP Code: 0\" \"Multi-product\" \"\" \"\"#013",
"event": {
"outcome": "success"
},
"action": {
"name": "decrypt",
"outcome": "success",
"target": "network-traffic"
},
"destination": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"host": {
"name": "2.2.2.2"
},
"network": {
"transport": "icmp"
},
"related": {
"ip": [
"1.1.1.1",
"3.3.3.3"
]
},
"source": {
"address": "3.3.3.3",
"ip": "3.3.3.3"
}
}
{
"message": "\"22\" \"10Dec2019\" \"23:44:49\" \"eth1\" \"FOOBAR-HOST-01\" \"Log\" \"Accept\" \"443\" \"44250\" \"2.2.2.2\" \"1.1.1.1\" \"tcp\" \"81\" \"WebAccess Notes\" \"81-FooBar_Policy\" \"\" \"inzone: External; outzone: Internal; service_id: https\" \"Multi-product\" \"\" \"\"",
"event": {
"outcome": "success"
},
"action": {
"name": "accept",
"outcome": "success",
"target": "network-traffic"
},
"destination": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"port": 443
},
"host": {
"name": "FOOBAR-HOST-01"
},
"network": {
"transport": "tcp"
},
"related": {
"ip": [
"1.1.1.1",
"2.2.2.2"
]
},
"source": {
"address": "2.2.2.2",
"ip": "2.2.2.2",
"port": 44250
}
}
{
"message": "\"21\" \"10Dec2019\" \"23:44:49\" \"eth1\" \"FOOBAR-HOST-01\" \"Log\" \"Drop\" \"58339\" \"46193\" \"1.1.1.1\" \"2.2.2.2\" \"tcp\" \"107\" \"Deny All\" \"107-FooBar_Policy\" \"\" \"inzone: External; outzone: Internal\" \"Security Gateway/Management\" \"\" \"\"",
"event": {
"outcome": "success"
},
"action": {
"name": "drop",
"outcome": "success",
"target": "network-traffic"
},
"destination": {
"address": "2.2.2.2",
"ip": "2.2.2.2",
"port": 58339
},
"host": {
"name": "FOOBAR-HOST-01"
},
"network": {
"transport": "tcp"
},
"related": {
"ip": [
"1.1.1.1",
"2.2.2.2"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"port": 46193
}
}
{
"message": "syslog[action:\"Drop\"; flags:\"2308\"; ifdir:\"inbound\"; ifname:\"eth1\"; loguid:\"{0x0,0x0,0x0,0x0}\"; origin:\"1.1.1.1\"; time:\"1617710462\"; version:\"1\"; __policy_id_tag:\"product=VPN-1 & FireWall-1[db_tag={736F50F2-40D8-124E-8D46-F7849455B8AE};mgmt=foobar;date=1615201122;policy_name=FooPolicy\\]\"; dst:\"2.2.2.2\"; inzone:\"External\"; origin_sic_name:\"CN=HOSTBAR,O=FooBaz.prj.fr.mnkqvz\"; outzone:\"External\"; product:\"VPN-1 & FireWall-1\"; proto:\"6\"; rule:\"118\"; rule_name:\"Clean-up Rule\"; rule_uid:\"{EA9E7B59-E0DD-4AE1-A2C0-680E3C3FAADC}\"; s_port:\"54377\"; service:\"5530\"; src:\"3.3.3.3\"; ]",
"event": {
"code": "{0x0,0x0,0x0,0x0}",
"outcome": "success"
},
"action": {
"name": "drop",
"outcome": "success",
"properties": {
"__policy_id_tag": "product=VPN-1 & FireWall-1[db_tag={736F50F2-40D8-124E-8D46-F7849455B8AE};mgmt=foobar;date=1615201122;policy_name=FooPolicy\\]",
"flags": "2308",
"loguid": "{0x0,0x0,0x0,0x0}",
"origin": "1.1.1.1",
"origin_sic_name": "CN=HOSTBAR,O=FooBaz.prj.fr.mnkqvz",
"product": "VPN-1 & FireWall-1"
},
"target": "network-traffic"
},
"destination": {
"address": "2.2.2.2",
"ip": "2.2.2.2",
"port": 5530
},
"network": {
"direction": "inbound",
"transport": "tcp"
},
"observer": {
"egress": {
"zone": "External"
},
"ingress": {
"interface": {
"name": "eth1"
},
"zone": "External"
}
},
"related": {
"ip": [
"2.2.2.2",
"3.3.3.3"
]
},
"rule": {
"id": "118",
"name": "Clean-up Rule",
"uuid": "{EA9E7B59-E0DD-4AE1-A2C0-680E3C3FAADC}",
"version": "1"
},
"source": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"port": 54377
}
}
{
"message": "syslog[action:\"Accept\"; flags:\"18692\"; ifdir:\"inbound\"; ifname:\"eth5\"; loguid:\"{0x607486c9,0x1,0x151e9f0a,0xc0000000}\"; origin:\"1.1.1.1\"; time:\"1618249417\"; version:\"1\"; __policy_id_tag:\"product=VPN-1 & FireWall-1[db_tag={A8A4FD06-D819-BC43-8607-833A6D14E3A2};mgmt=HOSTBAZ;date=1617956749;policy_name=MyPolicy\\]\"; dst:\"2.2.2.2\"; icmp:\"Echo Request\"; icmp_code:\"0\"; icmp_type:\"8\"; inzone:\"Internal\"; origin_sic_name:\"CN=HOSTBAR,O=FooBaz.prj.fr.mnkqvz\"; outzone:\"Internal\"; product:\"VPN-1 & FireWall-1\"; proto:\"1\"; rule:\"21\"; rule_uid:\"{6C86D7C0-B2C8-4222-AEF9-18CC10CEAA2B}\"; service_id:\"echo-request\"; src:\"3.3.3.3\"; ]",
"event": {
"code": "{0x607486c9,0x1,0x151e9f0a,0xc0000000}",
"outcome": "success"
},
"action": {
"name": "accept",
"outcome": "success",
"properties": {
"__policy_id_tag": "product=VPN-1 & FireWall-1[db_tag={A8A4FD06-D819-BC43-8607-833A6D14E3A2};mgmt=HOSTBAZ;date=1617956749;policy_name=MyPolicy\\]",
"flags": "18692",
"icmp_code": "0",
"icmp_message": "Echo Request",
"icmp_type": "8",
"loguid": "{0x607486c9,0x1,0x151e9f0a,0xc0000000}",
"origin": "1.1.1.1",
"origin_sic_name": "CN=HOSTBAR,O=FooBaz.prj.fr.mnkqvz",
"product": "VPN-1 & FireWall-1"
},
"target": "network-traffic"
},
"destination": {
"address": "2.2.2.2",
"ip": "2.2.2.2"
},
"network": {
"direction": "inbound",
"transport": "icmp"
},
"observer": {
"egress": {
"zone": "Internal"
},
"ingress": {
"interface": {
"name": "eth5"
},
"zone": "Internal"
}
},
"related": {
"ip": [
"2.2.2.2",
"3.3.3.3"
]
},
"rule": {
"id": "21",
"uuid": "{6C86D7C0-B2C8-4222-AEF9-18CC10CEAA2B}",
"version": "1"
},
"service": {
"id": "echo-request"
},
"source": {
"address": "3.3.3.3",
"ip": "3.3.3.3"
}
}
{
"message": "syslog[action:\"Key Install\"; flags:\"2304\"; ifdir:\"inbound\"; ifname:\"daemon\"; loguid:\"{0x0,0x0,0x0,0x0}\"; origin:\"1.1.1.1\"; time:\"1618253000\"; version:\"1\"; community:\"Lab_to_Foo\"; cookiei:\"c1d26a716fed4717\"; cookier:\"6b57dcc95790f11f\"; dst:\"1.1.1.1\"; dstkeyid:\"0x4caf71d8\"; fw_subproduct:\"VPN-1\"; ike::\"Quick Mode completion [UDP (IPv4)\\].\"; ike_ids::\"subnet: 2.2.2.2 (mask= 255.255.254.0) and subnet: 192.168.0.0 (mask= 255.255.255.252)\"; methods::\"ESP: AES-256 + SHA1 + PFS (group 5)\"; msgid:\"4c0515ff\"; origin_sic_name:\"CN=HOSTBAR,O=FooBaz.prj.fr.mnkqvz\"; peer_gateway:\"1.1.1.1\"; scheme::\"IKE\"; src:\"1.1.1.1\"; srckeyid:\"0x9dea8f3a\"; vpn_feature_name:\"IKE\"; ]",
"event": {
"code": "{0x0,0x0,0x0,0x0}",
"outcome": "success"
},
"action": {
"name": "key install",
"outcome": "success",
"properties": {
"community": "Lab_to_Foo",
"destination_key_id": "0x4caf71d8",
"encryption_methods": "ESP: AES-256 + SHA1 + PFS (group 5)",
"encryption_scheme": "IKE",
"flags": "2304",
"ike_ids": "subnet: 2.2.2.2 (mask= 255.255.254.0) and subnet: 192.168.0.0 (mask= 255.255.255.252)",
"ike_initiator_cookie": "c1d26a716fed4717",
"ike_mode": "Quick Mode completion [UDP (IPv4)\\].",
"ike_responder_cookie": "6b57dcc95790f11f",
"loguid": "{0x0,0x0,0x0,0x0}",
"origin": "1.1.1.1",
"origin_sic_name": "CN=HOSTBAR,O=FooBaz.prj.fr.mnkqvz",
"source_key_id": "0x9dea8f3a",
"subproduct": "VPN-1",
"vpn_feature_name": "IKE",
"vpn_peer_gateway": "1.1.1.1"
}
},
"destination": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"network": {
"direction": "inbound"
},
"observer": {
"ingress": {
"interface": {
"name": "daemon"
}
}
},
"related": {
"ip": [
"1.1.1.1"
]
},
"rule": {
"version": "1"
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
}
}
{
"message": "syslog[action:\"Accept\"; flags:\"18692\"; ifdir:\"inbound\"; ifname:\"eth5\"; loguid:\"{0x607486c4,0xa,0x151e9f0a,0xc0000001}\"; origin:\"1.1.1.1\"; time:\"1618249412\"; version:\"1\"; __policy_id_tag:\"product=VPN-1 & FireWall-1[db_tag={A8A4FD06-D819-BC43-8607-833A6D14E3A2};mgmt=HOSTBAZ;date=1617956749;policy_name=MyPolicy\\]\"; dst:\"192.168.99.111\"; icmp:\"Echo Request\"; icmp_code:\"0\"; icmp_type:\"8\"; inzone:\"Internal\"; nat_addtnl_rulenum:\"1\"; nat_rulenum:\"132\"; origin_sic_name:\"CN=HOSTBAR,O=FooBaz.prj.fr.mnkqvz\"; outzone:\"Internal\"; product:\"VPN-1 & FireWall-1\"; proto:\"1\"; rule:\"71\"; rule_name:\"Internet\"; rule_uid:\"{D67042B8-7EC2-4A9F-A047-523DE6CFF8E0}\"; service_id:\"echo-request\"; src:\"3.3.3.3\"; xlatedport:\"0\"; xlatedst:\"0.0.0.0\"; xlatesport:\"0\"; xlatesrc:\"192.168.99.1\"; ]",
"event": {
"code": "{0x607486c4,0xa,0x151e9f0a,0xc0000001}",
"outcome": "success"
},
"action": {
"name": "accept",
"outcome": "success",
"properties": {
"__policy_id_tag": "product=VPN-1 & FireWall-1[db_tag={A8A4FD06-D819-BC43-8607-833A6D14E3A2};mgmt=HOSTBAZ;date=1617956749;policy_name=MyPolicy\\]",
"flags": "18692",
"icmp_code": "0",
"icmp_message": "Echo Request",
"icmp_type": "8",
"loguid": "{0x607486c4,0xa,0x151e9f0a,0xc0000001}",
"nat_addtnl_rulenum": "1",
"nat_rulenum": "132",
"origin": "1.1.1.1",
"origin_sic_name": "CN=HOSTBAR,O=FooBaz.prj.fr.mnkqvz",
"product": "VPN-1 & FireWall-1"
},
"target": "network-traffic"
},
"destination": {
"address": "192.168.99.111",
"ip": "192.168.99.111",
"nat": {
"ip": "0.0.0.0",
"port": 0
}
},
"network": {
"direction": "inbound",
"transport": "icmp"
},
"observer": {
"egress": {
"zone": "Internal"
},
"ingress": {
"interface": {
"name": "eth5"
},
"zone": "Internal"
}
},
"related": {
"ip": [
"0.0.0.0",
"192.168.99.1",
"192.168.99.111",
"3.3.3.3"
]
},
"rule": {
"id": "71",
"name": "Internet",
"uuid": "{D67042B8-7EC2-4A9F-A047-523DE6CFF8E0}",
"version": "1"
},
"service": {
"id": "echo-request"
},
"source": {
"address": "3.3.3.3",
"ip": "3.3.3.3",
"nat": {
"ip": "192.168.99.1",
"port": 0
}
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
action.properties.__policy_id_tag |
keyword |
|
action.properties.community |
keyword |
|
action.properties.destination_key_id |
keyword |
|
action.properties.encryption_methods |
keyword |
|
action.properties.encryption_scheme |
keyword |
|
action.properties.flags |
keyword |
|
action.properties.icmp_code |
keyword |
|
action.properties.icmp_message |
keyword |
|
action.properties.icmp_type |
keyword |
|
action.properties.ike_ids |
keyword |
|
action.properties.ike_initiator_cookie |
keyword |
|
action.properties.ike_mode |
keyword |
|
action.properties.ike_responder_cookie |
keyword |
|
action.properties.loguid |
keyword |
|
action.properties.nat_addtnl_rulenum |
keyword |
|
action.properties.nat_rulenum |
keyword |
|
action.properties.observer_type |
keyword |
|
action.properties.origin |
keyword |
|
action.properties.origin_sic_name |
keyword |
|
action.properties.originsicname |
keyword |
|
action.properties.product |
keyword |
|
action.properties.reject_category |
keyword |
|
action.properties.rule_name |
keyword |
|
action.properties.signature |
array |
|
action.properties.source_key_id |
keyword |
|
action.properties.subproduct |
keyword |
|
action.properties.vpn_feature_name |
keyword |
|
action.properties.vpn_peer_gateway |
keyword |
|
action.target |
keyword |
|
checkpoint.firewall.tcp_flags |
keyword |
The control flag of the data flow |
destination.address |
keyword |
Destination network address. |
destination.domain |
keyword |
The domain name of the destination. |
destination.ip |
ip |
IP address of the destination. |
destination.nat.ip |
ip |
Destination NAT ip |
destination.nat.port |
long |
Destination NAT Port |
destination.port |
long |
Port of the destination. |
destination.size_in_char |
number |
|
destination.user.name |
keyword |
Short name or login of the user. |
event.code |
keyword |
Identification code for this event. |
host.name |
keyword |
Name of the host. |
http.request.method |
keyword |
HTTP request method. |
log.level |
keyword |
Log level of the log event. |
network.direction |
keyword |
Direction of the network traffic. |
network.forwarded_ip |
ip |
Host IP address when the source IP address is the proxy. |
network.protocol |
keyword |
Application protocol name. |
network.transport |
keyword |
Protocol Name corresponding to the field iana_number. |
observer.egress.zone |
keyword |
Observer Egress zone |
observer.ingress.interface.name |
keyword |
Interface name |
observer.ingress.zone |
keyword |
Observer ingress zone |
rule.id |
keyword |
Rule ID |
rule.name |
keyword |
Rule name |
rule.uuid |
keyword |
Rule UUID |
rule.version |
keyword |
Rule version |
service.id |
keyword |
Unique identifier of the running service. |
source.address |
keyword |
Source network address. |
source.domain |
keyword |
The domain name of the source. |
source.ip |
ip |
IP address of the source. |
source.nat.ip |
ip |
Source NAT ip |
source.nat.port |
long |
Source NAT port |
source.port |
long |
Port of the source. |
source.size_in_char |
number |
|
source.user.name |
keyword |
Short name or login of the user. |
url.full |
wildcard |
Full unparsed URL. |
url.original |
wildcard |
Unmodified original url as seen in the event source. |
user_agent.original |
keyword |
Unparsed user_agent string. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.
Further readings
- The code of the Intake format is available here.
- Log Exporter Configuration