Fortigate
Overview
The range of Fortigate firewalls is a complete appliance solution whose security functions are highly developed. The firewalls run on the FortiOS operating system.
- Vendor: Fortinet
- Supported environment: On Premise, Cloud
- Version compatibility, if applicable:
- Detection based on: Security Alerts / Network Telemetry
- Supported application or feature: Traffic, Web, URL Filtering, VPN
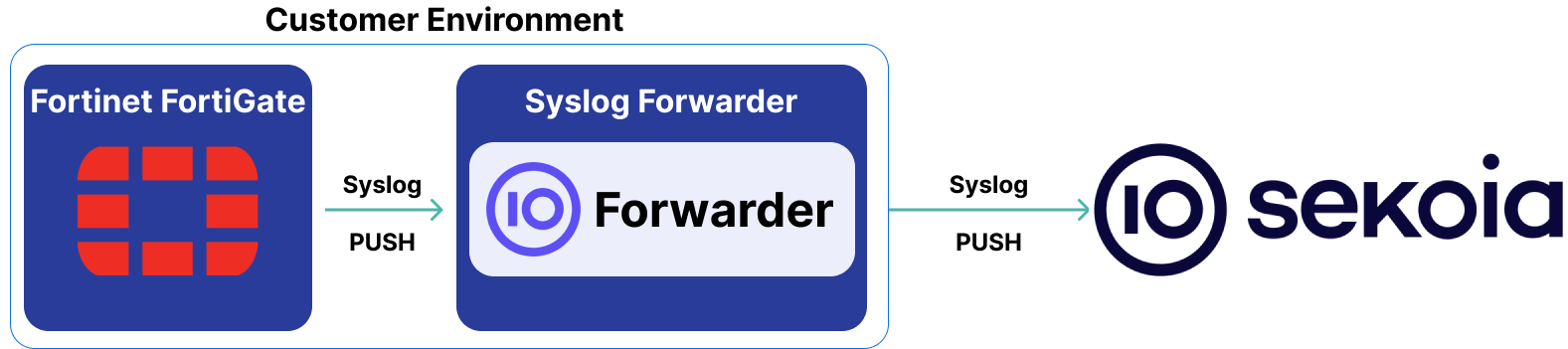
High-Level Architecture Diagram
- Type of integration: Outbound (PUSH to Sekoia.io)
- Schema
Specification
Prerequisites
- Resource:
- Self-managed syslog forwarder
- Network:
- Outbound traffic allowed
- Permissions:
- Administrator rights on the Fortigate
- Root access to the Linux server with the syslog forwarder
Transport Protocol/Method
- Indirect Syslog
Logs details
- Supported functionalities: See section Overview
- Supported type(s) of structure: Standard, CSV, CEF (Common Event Format)
- Supported verbosity level: Alert
Note
Log levels are based on the taxonomy of RFC5424. Adapt according to the terminology used by the editor.
Step-by-Step Configuration Procedure
Instructions on the 3rd Party Solution
Forward Fortigate Logs to Sekoia.io
This setup guide will show you how to forward your Fortigate logs to Sekoia.io by means of a syslog transport channel.
Detailed Procedure:
-
Fortigate Logs:
- On Fortigate appliances, most of the important hardware and software activities that are relevant for security detection and analysis are logged into three files:
- Traffic: Local out traffic, Denied traffic, Allowed traffic
- Web
- URL Filtering
- VPN
-
Transport to the Concentrator:
- Prerequisites:
- Administrator rights on the Fortigate
-
Traffic towards the syslog concentrator must be open on
TCP/514 -
Configure Fortigate:
- The first step is to configure Fortigate to log the awaited traffic.
- You can configure FortiOS to send log messages to remote syslog servers in standard, CSV, or CEF (Common Event Format) format. These three formats are accepted by the Sekoia.io intake.
-
To enable syslog, log into the CLI and enter the following commands:
config log syslogd setting set status enable set port 514 set mode reliable set server [IP address of syslog server] set facility user set format rfc5424 end -
Most FortiGate features are enabled for logging by default. Ensure they are enabled by executing the following command:
show full-configuration -
Make sure the Traffic, Web, and URL Filtering features are enabled for logging with the following commands:
config log syslogd filter set forward-traffic enable set local-traffic enable set multicast-traffic enable .... set vpn enable set web enable set url-filter enable end -
With some Fortigate appliances, it may not be possible to do the above configuration through the command line. An alternative method is to use the graphical interface and go to the
Log Settingsmenu. From there you can choose every logging option withinEvent LoggingandLocal Traffic Logexcept for theDeniedoptions. -
To use the CEF format, use the following commands:
config log syslogd setting set format cef end
Configure a forwarder
To forward events using syslog to Sekoia.io, you need to update the syslog header with the intake key you previously created. Here is an example of your message before the forwarder
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG RAW_MESSAGE
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG [SEKOIA@53288 intake_key=\"YOUR_INTAKE_KEY\"] RAW_MESSAGE
To achieve this you can:
- Use the Sekoia.io forwarder which is the official supported way to collect data using the syslog protocol in Sekoia.io. In charge of centralizing data coming from many equipments/sources and forwarding them to Sekoia.io with the apporpriated format, it is a prepackaged option. You only have to provide your intake key as parameter.
- Use your own Syslog service instance. Maybe you already have an intance of one of these components on your side and want to reuse it in order to centralize data before forwarding them to Sekoia.io. When using this mode, you have to configure and maintain your component in order to respect the expected Sekoia.io format.
Warning
Only the Sekoia.io forwarder is officially supported. Other options are documented for reference purposes but do not have official support.
Instruction on Sekoia
Configure Your Intake
This section will guide you through creating the intake object in Sekoia, which provides a unique identifier called the "Intake key." The Intake key is essential for later configuration, as it references the Community, Entity, and Parser (Intake Format) used when receiving raw events on Sekoia.
- Go to the Sekoia Intake page.
- Click on the
+ New Intakebutton at the top right of the page. - Search for your Intake by the product name in the search bar.
- Give it a Name and associate it with an Entity (and a Community if using multi-tenant mode).
- Click on
Create.
Note
For more details on how to use the Intake page and to find the Intake key you just created, refer to this documentation.
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
CEF:0|Fortinet|Fortigate|v6.2.9|32102|event:system|7|deviceExternalId=FGVM2V0000171868 FortinetFortiGatelogid=0100032102 cat=event:system FortinetFortiGatesubtype=system FortinetFortiGatelevel=alert FortinetFortiGatevd=root FortinetFortiGateeventtime=1637681708541881380 FortinetFortiGatetz=+0100 FortinetFortiGatelogdesc=Configuration changed duser= sproc=console msg=Configuration is changed in the admin session
CEF:0|Fortinet|Fortigate|v6.0.3|24576|utm:dlp dlp block|4|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0954024576 cat=utm:dlp FTNTFGTsubtype=dlp FTNTFGTeventtype=dlp FTNTFGTlevel=warning FTNTFGTvd=vdom1 FTNTFGTeventtime=1545949776 FTNTFGTfilteridx=1 FTNTFGTdlpextra=test-dlp3 FTNTFGTfiltertype=file-type FTNTFGTfiltercat=file FTNTFGTseverity=medium FTNTFGTpolicyid=1 externalId=12680 FTNTFGTepoch=418303178 FTNTFGTeventid=0 duser=bob src=10.1.100.11 spt=33638 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined dst=example.com dpt=80 deviceOutboundInterface=port11 FTNTFGTdstintfrole=undefined proto=6 app=HTTP FTNTFGTfiletype=gif deviceDirection=0 act=block dhost=example.com request=/dlp/flower.gif requestClientApplication=curl/7.47.0 fname=flower.gif fsize=1209 FTNTFGTprofile=test-dlp
CEF:0|Fortinet|Fortigate|v6.0.3|54802|dns:dns-response pass|3|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=1501054802 cat=dns:dns-response FTNTFGTsubtype=dns-response FTNTFGTlevel=notice FTNTFGTvd=vdom1 FTNTFGTeventtime=1545950726 FTNTFGTpolicyid=1 externalId=13355 duser=bob src=10.1.100.11 spt=54621 deviceInboundInterface=port12 FTNTFGTsrcintfrole=lan dst=172.16.200.55 dpt=53 deviceOutboundInterface=port11 FTNTFGTdstintfrole=wan proto=17 FTNTFGTprofile=default FTNTFGTsrcmac=a2:e9:00:ec:40:01 FTNTFGTxid=5137 FTNTFGTqname=example.org FTNTFGTqtype=A FTNTFGTqtypeval=1 FTNTFGTqclass=IN FTNTFGTipaddr=104.80.89.26, 104.80.89.24 msg=Domain is monitored act=pass FTNTFGTcat=52 FTNTFGTcatdesc=Information Technology
time=15:51:59 devname="my-device" devid="1111111111111111" eventtime=1668001919663486001 tz="+0100" logid="1500054000" type="utm" subtype="dns" eventtype="dns-query" level="information" vd="root" policyid=1685 poluuid="4470d4c5-7e12-4a8f-a369-08eff4a43b5b" policytype="policy" sessionid=933308058 srcip=1.2.3.4 srcport=35305 srccountry="Reserved" srcintf="INTF-1" srcintfrole="undefined" dstip=192.0.2.1 dstport=53 dstcountry="Reserved" dstintf="INTF-2" dstintfrole="lan" proto=17 profile="DNS Filtering Normal" xid=42240 qtype="NS" qtypeval=2 qclass="IN"
time=15:58:39 devname="dev-name" devid="1111111111111111" eventtime=1668002319383195535 tz="+0100" logid="1500054000" type="utm" subtype="dns" eventtype="dns-query" level="information" vd="root" policyid=770 poluuid="f2aef0f2-a721-49cf-9dd3-b27f7f5b90bc" policytype="policy" sessionid=933538554 user="user1" srcip=1.2.3.4 srcport=45362 srccountry="Reserved" srcintf="intf-1" srcintfrole="undefined" dstip=192.0.2.1 dstport=53 dstcountry="Reserved" dstintf="intf-2" dstintfrole="undefined" proto=17 profile="DNS Filtering Normal" xid=32649 qname="[example.com]" qtype="A" qtypeval=1 qclass="IN"
CEF:0|Fortinet|Fortigate|v6.0.3|16384|utm:ips signature reset|7|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0419016384 cat=utm:ips FTNTFGTsubtype=ips FTNTFGTeventtype=signature FTNTFGTlevel=alert FTNTFGTvd=vdom1 FTNTFGTeventtime=1545938887 FTNTFGTseverity=info src=example.com FTNTFGTsrccountry=Reserved dst=10.1.100.11 deviceInboundInterface=port11 FTNTFGTsrcintfrole=undefined deviceOutboundInterface=port12 FTNTFGTdstintfrole=undefined externalId=901 act=reset proto=6 app=HTTP FTNTFGTpolicyid=1 FTNTFGTattack=Eicar.Virus.Test.File spt=80 dpt=44362 dhost=example.com request=/virus/eicar.com deviceDirection=0 FTNTFGTattackid=29844 FTNTFGTprofile=test-ips FTNTFGTref=http://www.fortinet.com/ids/VID29844 duser=bob FTNTFGTincidentserialno=877326946 msg=file_transfer: Eicar.Virus.Test.File,
time=17:24:16 devname="abc" devid="1" logid="0101037130" type="event" subtype="vpn" level="error" vd="root" eventtime=1580142256 logdesc="Progress IPsec phase 2" msg="progress IPsec phase 2" action="negotiate" remip=1.1.1.1 locip=192.0.2.1 remport=500 locport=500 outintf="N/A" cookies="07f928d94dd975ea/89b1d990f54f0b82" user="N/A" group="N/A" xauthuser="N/A" xauthgroup="N/A" assignip=N/A vpntunnel="VPN-FOOBAR" status="failure" init="local" exch="CREATE_CHILD" dir="inbound" role="initiator" result="ERROR" version="IKEv2"
time=16:48:00 devname="abc" devid="1" logid="0100032003" type="event" subtype="system" level="information" vd="root" eventtime=1619621280 logdesc="Admin logout successful" sn="1619620402" user="test" ui="jsconsole" method="jsconsole" srcip=1.1.1.1 dstip=192.0.2.1 action="logout" status="success" duration=878 reason="exit" msg="Administrator test logged out from jsconsole"
time=16:23:50 devname="abc" devid="1" logid="0100032011" type="event" subtype="system" level="notice" vd="PRX1-AA" eventtime=1619619830 logdesc="Disk log rolled" action="roll-log" reason="file-size" log="tlog" msg="Disk log has rolled."
CEF:0|Fortinet|Fortigate|v6.0.3|61002|utm:ssh ssh-command passthrough|3|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=1600061002 cat=utm:ssh FTNTFGTsubtype=ssh FTNTFGTeventtype=ssh-command FTNTFGTlevel=notice FTNTFGTvd=vdom1 FTNTFGTeventtime=1545950175 FTNTFGTpolicyid=1 externalId=12921 duser=bob FTNTFGTprofile=test-ssh src=10.1.100.11 spt=56698 dst=172.16.200.55 dpt=22 deviceInboundInterface=port12 FTNTFGTsrcintfrole=lan deviceOutboundInterface=port11 FTNTFGTdstintfrole=wan proto=6 act=passthrough FTNTFGTlogin=root FTNTFGTcommand=ls FTNTFGTseverity=low
CEF:0|Fortinet|Fortigate|v6.0.3|44032|utm:voip voip permit start|2|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0814044032 cat=utm:voip FTNTFGTsubtype=voip FTNTFGTeventtype=voip FTNTFGTlevel=information FTNTFGTvd=vdom1 FTNTFGTeventtime=1545958028 externalId=18975 FTNTFGTepoch=0 FTNTFGTevent_id=6857 src=10.1.100.11 spt=5060 dst=172.16.200.55 dpt=5060 proto=17 deviceInboundInterface=port12 deviceOutboundInterface=port11 FTNTFGTpolicy_id=1 FTNTFGTprofile=default FTNTFGTvoip_proto=sip FTNTFGTkind=call act=permit outcome=start FTNTFGTduration=0 FTNTFGTdir=session_origin FTNTFGTcall_id=3444-13134@127.0.0.1 suser=user1 duser=user1
time=15:29:39 devname="abc" devid="1" logid="0105048039" type="event" subtype="wad" level="error" vd="PRX1-AA" eventtime=1619616579 logdesc="SSL fatal alert sent" session_id=473f963d policyid=0 srcip=192.0.2.1 srcport=47782 dstip=1.1.1.1 dstport=8002 action="send" alert="2" desc="illegal parameter" msg="SSL Alert sent"
CEF:0|Fortinet|Fortigate|v6.0.3|30258|utm:waf waf-http-constraint passthrough|4|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=1203030258 cat=utm:waf FTNTFGTsubtype=waf FTNTFGTeventtype=waf-http-constraint FTNTFGTlevel=warning FTNTFGTvd=vdom1 FTNTFGTeventtime=1545951320 FTNTFGTpolicyid=1 externalId=13614 duser=bob FTNTFGTprofile=waf_test src=10.1.100.11 spt=57304 dst=example.com dpt=80 deviceInboundInterface=port12 FTNTFGTsrcintfrole=lan deviceOutboundInterface=port11 FTNTFGTdstintfrole=wan proto=6 app=HTTP request=http://example.com/index.html?https://example.com/ FTNTFGTseverity=medium act=passthrough deviceDirection=0 requestClientApplication=curl/7.47.0 FTNTFGTconstraint=url-param-num FTNTFGTrawdata=Method\=GET|User-Agent\=curl/7.47.0
0|Fortinet|Fortigate|v6.0.3|18433|utm:anomaly anomaly clear_session|7|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0720018433 cat=utm:anomaly FTNTFGTsubtype=anomaly FTNTFGTeventtype=anomaly FTNTFGTlevel=alert FTNTFGTvd=vdom1 FTNTFGTeventtime=1545939604 FTNTFGTseverity=critical src=10.1.100.11 FTNTFGTsrccountry=Reserved dst=172.16.200.55 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined externalId=0 act=clear_session proto=1 app=PING cnt=1 FTNTFGTattack=icmp_flood FTNTFGTicmpid=0x3053 FTNTFGTicmptype=0x08 FTNTFGTicmpcode=0x00 FTNTFGTattackid=16777316 FTNTFGTpolicyid=1 FTNTFGTpolicytype=DoS-policy FTNTFGTref=http://www.fortinet.com/ids/VID16777316 msg=anomaly: icmp_flood, 51 > threshold 50 FTNTFGTcrscore=50 FTNTFGTcrlevel=critical
CEF:0|Fortinet|Fortigate|v5.6.0|18433|anomaly:anomaly clear_ session|7|FTNTFGTlogid=0720018433 cat=anomaly:anomaly FTNTFGTsubtype=anomaly FTNTFGTlevel=alert FTNTFGTvd=vdom1 FTNTFGTseverity=critical src=1.1.1.1 dst=192.0.2.1 deviceInboundInterface=port15 externalId=0 act=clear_session proto=1 app=icmp/146/81 cnt=306 FTNTFGTattack=icmp_flood dpt=20882 FTNTFGTicmptype=0x92 FTNTFGTicmpcode=0x51 FTNTFGTattackid=16777316 FTNTFGTprofile=DoS-policy1 cs2=http://www.fortinet.com/ids/VID16777316 cs2Label=Reference msg=anomaly: icmp_flood, 34 > threshold 25, repeats 306 times FTNTFGTcrscore=50 FTNTFGTcrlevel=critical
date=2016-02-12,time=14:10:42,logid=0720018433,type=anomaly,subtype=anomaly,level=alert,vd="vdom1",severity=critical,srcip=1.1.1.1,dstip=192.0.2.1,srcintf="port15",sessionid=0,action=clear_session,proto=1,service="icmp/146/81",count=306,attack="icmp_ flood",dstport=20882,icmptype=0x92,icmpcode=0x51,attackid=16777316,profile="DoS-policy1",ref="http://www.fortinet.com/ids/VID16777316",msg="anomaly: icmp_flood, 34 > threshold 25, repeats 306 times",crscore=50,crlevel=critical
date=2016-02-12 time=14:10:42 logid=0720018433 type=anomaly subtype=anomaly level=alert vd="vdom1" severity=critical srcip=1.1.1.1 dstip=192.0.2.1 srcintf="port15" sessionid=0 action=clear_session proto=1 service="icmp/146/81" count=306 attack="icmp_ flood" dstport=20882 icmptype=0x92 icmpcode=0x51 attackid=16777316 profile="DoS-policy1" ref="http://www.fortinet.com/ids/VID16777316" msg="anomaly: icmp_flood, 34 > threshold 25, repeats 306 times" crscore=50 crlevel=critical
CEF:0|Fortinet|Fortigate|v6.0.3|08192|utm:virus infected blocked|4|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0211008192 cat=utm:virus FTNTFGTsubtype=virus FTNTFGTeventtype=infected FTNTFGTlevel=warning FTNTFGTvd=vdom1 FTNTFGTeventtime=1545938448 msg=File is infected. act=blocked app=HTTP externalId=695 src=10.1.100.11 dst=example.com spt=44356 dpt=80 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined deviceOutboundInterface=port11 FTNTFGTdstintfrole=undefined FTNTFGTpolicyid=1 proto=6 deviceDirection=0 fname=eicar.com FTNTFGTquarskip=File-was-not-quarantined. FTNTFGTvirus=EICAR_TEST_FILE FTNTFGTdtype=Virus FTNTFGTref=http://www.fortinet.com/ve?vn\=EICAR_TEST_FILE FTNTFGTvirusid=2172 request=http://example.com/virus/eicar.com FTNTFGTprofile=g-default duser=bob requestClientApplication=curl/7.47.0 FTNTFGTanalyticscksum=275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f FTNTFGTanalyticssubmit=false FTNTFGTcrscore=50 FTNTFGTcrlevel=critical
CEF:0|Fortinet|Fortigate|v5.6.0|08192|utm:virus infected blocked|4|FTNTFGTlogid=0211008192 cat=utm:virus FTNTFGTsubtype=virus FTNTFGTeventtype=infected FTNTFGTlevel=warning FTNTFGTvd=vdom1 msg=File is infected act=blocked app=HTTP externalId=56633 src=1.1.1.1 dst=192.0.2.1 spt=45719 dpt=80 deviceInboundInterface=port15 deviceOutboundInterface=port19 proto=6 deviceDirection=0 fname=eicar.com FTNTFGTchecksum=1dd02bdb FTNTFGTquarskip=No-skip cs1=EICAR_TEST_FILE cs1Label=Virus FTNTFGTdtype=Virus cs2=http://www.fortinet.com/ve?vn\=EICAR_TEST_FILE cs2Label=Reference FTNTFGTvirusid=2172 request=http://example.net/eicar.com FTNTFGTprofile=default duser= requestClientApplication=Wget/1 10 2 FTNTFGTanalyticscksum=131f95c51cc819465fa1797f6ccacf9d494aaaff46fa3eac73ae63ffbdfd8267 FTNTFGTanalyticssubmit=false FTNTFGTcrscore=50 FTNTFGTcrlevel=critical
time=09:47:30 devname="TEST_DEV_NAME1" devid="TEST_DEV_ID" logid="1059028704" type="utm" subtype="app-ctrl" eventtype="app-ctrl-all" level="information" vd="root" eventtime=1741250850 appid=0000 srcip=1.2.3.4 dstip=3.4.5.6 srcport=11116 dstport=80 srcintf="root-enoveo0" srcintfrole="undefined" dstintf="internet-100" dstintfrole="undefined" proto=6 service="HTTP" direction="outgoing" policyid=293 sessionid=1947800834 applist="g-default" appcat="Web.Client" app="HTTP.BROWSER_Firefox" action="pass" hostname="example.com" incidentserialno=235885632 url="/canonical.html" msg="Web.Client: HTTP.BROWSER_Firefox," apprisk="elevated"
0|Fortinet|Fortigate|v7.2.10|28704|utm:app-ctrl signature|2|deviceExternalId=FG3H0E5819900415 FTNTFGTeventtime=1741265077985865088 FTNTFGTtz=+0100 FTNTFGTlogid=1059028704 cat=utm:app-ctrl FTNTFGTsubtype=app-ctrl FTNTFGTeventtype=signature FTNTFGTlevel=information FTNTFGTvd=root FTNTFGTappid=16420 duser=testUser FTNTFGTgroup=testGroup src=1.2.3.4 FTNTFGTsrccountry=Reserved dst=3.4.5.6 FTNTFGTdstcountry=United States spt=52854 dpt=443 deviceInboundInterface=vlan-1024 FTNTFGTsrcintfrole=lan deviceOutboundInterface=vlan-1033 FTNTFGTdstintfrole=wan proto=6 app=HTTPS deviceDirection=0 FTNTFGTpolicyid=5 externalId=70046266 FTNTFGTapplist=app-ctrl-bme act=pass FTNTFGTappcat=Video/Audio FTNTFGTapp=YouTube_Video.Access dhost=example.com FTNTFGTincidentserialno=231408777 request=/youtubei/v1/player?https://example.com/ requestClientApplication=Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.0.0 Safari/537.36 FTNTFGThttpmethod=POST FTNTFGTreferralurl=https://example.com/ msg=Video/Audio: YouTube_Video.Access FTNTFGTclouduser=1.2.3.4 fname=LA CACABOX sur REPO & AMONG-US 3D - POTATOZ VOD FTNTFGTapprisk=elevated FTNTFGTcloudaction=others
0|Fortinet|Fortigate|v7.0.17|08192|utm:virus infected|4|deviceExternalId=FG120GTK24003942 FTNTFGTeventtime=1741264893005614373 FTNTFGTtz=+0100 FTNTFGTlogid=0211008192 cat=utm:virus FTNTFGTsubtype=virus FTNTFGTeventtype=infected FTNTFGTlevel=warning FTNTFGTvd=root FTNTFGTpolicyid=7 FTNTFGTpoluuid=poluuid FTNTFGTpolicytype=policy msg=File is infected. act=blocked app=IMAP externalId=2861718763 src=1.2.3.4 dst=3.4.5.6 spt=54364 dpt=143 FTNTFGTsrccountry=Reserved FTNTFGTdstcountry=France deviceInboundInterface=400-TOXIII FTNTFGTsrcintfrole=lan deviceOutboundInterface=port1 FTNTFGTdstintfrole=wan FTNTFGTsrcuuid=dstuuuid FTNTFGTdstuuid=dstuuuid proto=6 deviceDirection=0 fname=BULLETIN-TABLE-OVALE.docx FTNTFGTquarskip=Quarantine-disabled FTNTFGTvirus=MSOffice/Agent.PCL!tr.dldr FTNTFGTviruscat=Virus FTNTFGTdtype=av-engine FTNTFGTref=http://test.com/ve?vn\=sdkdksdkds FTNTFGTvirusid=8032867 FTNTFGTprofile=default suser=user1 duser=user1 FTNTFGTrecipient=\\"testUser@test.test\\" FTNTFGTanalyticscksum=383b017352d7602c7603f5d36a9c3beb23df2f183116e0cc3d81e158e978ee7d FTNTFGTanalyticssubmit=false FTNTFGTcrscore=50 FTNTFGTcraction=2 FTNTFGTcrlevel=critical
CEF:0|Fortinet|Fortigate|v6.0.3|28704|utm:app-ctrl app-ctrl-all pass|2|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=1059028704 cat=utm:app-ctrl FTNTFGTsubtype=app-ctrl FTNTFGTeventtype=app-ctrl-all FTNTFGTlevel=information FTNTFGTvd=vdom1 FTNTFGTeventtime=1545949688 FTNTFGTappid=34050 src=10.1.100.11 dst=192.0.2.1 spt=56826 dpt=80 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined deviceOutboundInterface=port11 FTNTFGTdstintfrole=undefined proto=6 app=HTTP deviceDirection=1 FTNTFGTpolicyid=1 externalId=12567 FTNTFGTapplist=g-default FTNTFGTappcat=Web.Client FTNTFGTapp=HTTP.BROWSER_Firefox act=pass dhost=example.com FTNTFGTincidentserialno=1702350499 request=/success.txt msg=Web.Client: HTTP.BROWSER_Firefox, FTNTFGTapprisk=elevated suser=example.com\\alice
date=2018-12-29 time=15:30:25 logid="0419016384" type="utm" subtype="ips" eventtype="signature" level="alert" vd="vdom1" eventtime=1540852225 severity="info" srcip=1.2.3.4 srccountry="Reserved" dstip=example.com srcintf="dmz" srcintfrole="lan" dstintf="wan1" dstintfrole="wan" sessionid=4205 action="reset" proto=6 service="HTTP" policyid=1 attack="Virus.File" srcport=53330 dstport=80 hostname="example.com" url="/cgi-bin/upload.py?https://example.com/" direction="outgoing" attackid=29844 profile="ips-test" ref="http://www.fortinet.com/ids/VID29844" incidentserialno=2111356281 msg="file_transfer: Virus.File,"
date=2018-12-29 time=14:50:47 logid="0419016384" type="utm" subtype="ips" eventtype="signature" level="alert" vd="vdom1" eventtime=1540849847 severity="info" srcip=1.2.3.4 srccountry="Reserved" dstip=example.com srcintf="dmz" srcintfrole="lan" dstintf="wan1" dstintfrole="wan" sessionid=2979 action="reset" proto=6 service="HTTP" policyid=1 attack="Virus.File" srcport=46552 dstport=80 hostname="example.com" url="/virus/example.com" direction="incoming" attackid=29844 profile="ips-test" ref="http://www.fortinet.com/ids/VID29844" incidentserialno=122164746 msg="file_transfer: Virus.File,"
time=15:05:54 devname="INFRA1" devid="DEVICE" eventtime=1752152754192314929 tz="+0200" logid="0100000001" type="event" subtype="system" level="information" vd="INFRA" logdesc="DHCP Ack log" interface="VLAN1" dhcp_msg="Ack" mac="AA:BB:CC:DD:EE:FF" ip=1.2.3.4 lease=432000 hostname="HOSTNAME" msg="DHCP server sends a DHCPACK"
date=2018-12-27,time=14:45:26,logid="1501054802",type="dns",subtype="dns-response",level="notice",vd="vdom1",eventtime=1545950726,policyid=1,sessionid=13355,user="bob",srcip=1.1.1.1,srcport=54621,srcintf="port12",srcintfrole="lan",dstip=192.0.2.1,dstport=53,dstintf="port11",dstintfrole="wan",proto=17,profile="default",srcmac="02:00:00:00:00:00",xid=5137,qname="example.com",qtype="A",qtypeval=1,qclass="IN",ipaddr="104.80.89.26, 104.80.89.24",msg="Domain is monitored",action="pass",cat=52,catdesc="Information Technology"
time=11:36:13 devname="PC-01-OS1" devid="XXXXXXXXXXXX" eventtime=1721727373453168766 tz="+0200" logid="010000000" type="event" subtype="system" level="information" vd="AAAA-AA" logdesc="Object attribute configured" user="username" ui="GUI(192.0.2.1)" action="Edit" cfgtid=111111111 uuid="xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxx" cfgpath="firewall.policy" cfgobj="756" cfgattr="service[svc-win->svc-repo-linux-port]" msg="Edit firewall.policy 756"
CEF:0|Fortinet|Fortigate|v6.0.3|20503|utm:emailfilter smtp log-only|2|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0508020503 cat=utm:emailfilter FTNTFGTsubtype=emailfilter FTNTFGTeventtype=smtp FTNTFGTlevel=information FTNTFGTvd=vdom1 FTNTFGTeventtime=1545939418 FTNTFGTpolicyid=1 externalId=1135 duser=bob src=10.1.100.11 spt=35969 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined dst=172.18.62.158 dpt=25 deviceOutboundInterface=port11 FTNTFGTdstintfrole=undefined proto=6 app=SMTP FTNTFGTprofile=test-spam act=log-only suser=user1 duser=test1@server88.qa.fortinet.com FTNTFGTsender=user1 FTNTFGTrecipient=test1@server88.qa.fortinet.com deviceDirection=1 msg=general email log FTNTFGTsubject=hello_world2 FTNTFGTsize=216 FTNTFGTattachment=no
type="event" subtype="system" level="information" vd="root" logdesc="Object attribute configured" user="admin" ui="jsconsole(127.0.0.1)" action="Add" cfgtid=1234567890 cfgpath="system.admin" cfgobj="vOcep" cfgattr="password[*]accprofile[super_admin]vdom[root]" msg="Add system.admin vOcep"
type="event" subtype="system" level="information" vd="root" logdesc="Admin login successful" sn="1234567890" user="admin" ui="jsconsole" method="jsconsole" srcip=1.1.1.1 dstip=1.1.1.1 action="login" status="success" reason="none" profile="super_admin" msg="Administrator admin logged in successfully from jsconsole"
CEF:0|Fortinet|Fortigate|v6.0.3|32002|event:system login failed|7|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0100032002 cat=event:system FTNTFGTsubtype=system FTNTFGTlevel=alert FTNTFGTvd=vdom1 FTNTFGTeventtime=1545938140 FTNTFGTlogdesc=Admin login failed FTNTFGTsn=0 duser=user1 sproc=https(172.16.200.254) FTNTFGTmethod=https src=172.16.200.254 dst=172.16.200.1 act=login outcome=failed reason=name_invalid msg=Administrator user1 login failed from https(172.16.200.254) because of invalid user name
CEF:0|Fortinet|Fortigate|v6.0.3|43008|event:user authentication success|3|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0102043008 cat=event:user FTNTFGTsubtype=user FTNTFGTlevel=notice FTNTFGTvd=vdom1 FTNTFGTeventtime=1545938255 FTNTFGTlogdesc=Authentication success src=10.1.100.11 dst=172.16.200.55 FTNTFGTpolicyid=1 deviceInboundInterface=port12 duser=bob FTNTFGTgroup=N/A FTNTFGTauthproto=TELNET(10.1.100.11) act=authentication outcome=success reason=N/A msg=User bob succeeded in authentication
devname=".self" devid="1111111111111111" vd="root" itime=1725479662 date="2024-09-04" time="19:54:22" tz="+0000" type="appevent" user="system" user_from="system" logid="222222" subtype="logdev" eventtype="logging-status" level="warning" desc="Device offline" logdev_id="ABCDEFGHIJKLMNOP" logdev_name="LOGDEV-NAME" logdev_offline_duration=69138 logdev_last_logging=1721331330 msg="Did not receive any log from device LOGDEV-NAME[ABCDEFGHIJKLMNOP] in past 48d18m52s (69138 minutes)."
time=10:59:48 devname="FW-001" devid="xxxxxxxxxx" eventtime=1720429188081127405 tz="+0200" logid="0000000" type="utm" subtype="webfilter" eventtype="ftgd_allow" level="notice" vd="root" policyid=00000 poluuid="xxxxxx-xxxx-xxxx-xxxxxx" policytype="policy" sessionid=111111111 srcip=192.0.2.1 srcport=1000 srccountry="France" srcintf="aaaaaaaaa" srcintfrole="wan" srcuuid="xxxxxx-xxxx-xxxx-xxxxxxxxxxx" dstip=10.0.0.1 dstport=80 dstcountry="Reserved" dstintf="aaaaaaaa" dstintfrole="lan" dstuuid="xxxxxxx-xxxx-xxxx-xxxxxxxxxxxx" proto=6 service="HTTP" hostname="example.com" forwardedfor="1.2.3.4" profile="monitor-all" action="passthrough" reqtype="direct" url="http://example.com/" sentbyte=270 rcvdbyte=0 direction="outgoing" msg="URL belongs to an allowed category in policy" method="domain" cat=51 catdesc="Government and Legal Organizations"
timestamp=1746183115 devname="devName1" devid="devId" vd="root" date=2025-05-02 time=10:51:55 eventtime=1746175915421843994 tz="+0200" logid="1000000000" type="utm" subtype="app-ctrl" eventtype="signature" level="information" appid=15893 srcip=1.2.3.4 srccountry="Spain" dstip=3.4.5.6 dstcountry="Reserved" srcport=39972 dstport=80 srcintf="port2" srcintfrole="wan" dstintf="port3" dstintfrole="dmz" proto=6 service="HTTP" direction="outgoing" policyid=120 poluuid="5187b416-87fa-51ec-c830-268b6371a3ac" policytype="policy" sessionid=11111111 applist="block-high-risk" action="pass" appcat="Web.Client" app="HTTP.BROWSER" hostname="example.com" incidentserialno=10101 url="/test/version_test_v2.php" httpmethod="GET" msg="Web.Client: HTTP.BROWSER" apprisk="medium" forwardedfor="5.6.7.8,6.7.8.9"
time=11:09:50 devname="abc" devid="1" logid="1059028704" type="utm" subtype="app-ctrl" eventtype="app-ctrl-all" level="information" vd="root" eventtime=1579860590 appid=40568 srcip=1.1.1.1 dstip=192.0.2.1 srcport=33345 dstport=443 srcintf="test" srcintfrole="undefined" dstintf="port1" dstintfrole="undefined" proto=6 service="HTTPS" direction="outgoing" policyid=1 sessionid=1508480438 applist="default" appcat="Web.Client" app="HTTPS.BROWSER" action="pass" hostname="example.com" incidentserialno=455926217 url="/" msg="Web.Client: HTTPS.BROWSER," apprisk="medium"
time=15:22:43 devname="abc" devid="1" logid="0000000011" type="traffic" subtype="forward" level="warning" vd="root" eventtime=1602591763587868496 tz="+0300" srcip=1.1.1.1 identifier=256 srcintf="internal" srcintfrole="lan" dstip=192.0.2.1 dstintf="wan1" dstintfrole="wan" srcuuid="b22e6ef4-2e38-51ea-72c9-53b2da2e20f5" dstuuid="052bdbce-823a-51e9-eb23-7a3e819fea4f" poluuid="1520e1aa-823a-51e9-984f-a55e1f39b3c7" sessionid=706677975 proto=1 action="ip-conn" policyid=1 policytype="policy" service="icmp/0/8" dstcountry="Netherlands" srccountry="Reserved" appcat="unscanned" crscore=5 craction=262144 crlevel="low"
time=13:02:14 devname="abc" devid="1" logid="0001000014" type="traffic" subtype="local" level="notice" vd="root" eventtime=1602586934900309053 tz="+0200" srcip=00192.0.2.100:00:00:00 identifier=0 srcintf="AVR-GUEST-AP" srcintfrole="lan" dstip=12192.0.2.116 dstintf="unknown0" dstintfrole="undefined" sessionid=1395131 proto=58 action="accept" policyid=0 policytype="local-in-policy6" service="icmp6/143/0" trandisp="noop" app="icmp6/143/0" duration=60 sentbyte=76 rcvdbyte=0 sentpkt=1 rcvdpkt=0 appcat="unscanned"
CEF:0|Fortinet|Fortigate|v6.0.10|00014|traffic:local accept|3|deviceExternalId=FGVM2V0000171868 FortinetFortiGatelogid=0001000014 cat=traffic:local FortinetFortiGatesubtype=local FortinetFortiGatelevel=notice FortinetFortiGatevd=root FortinetFortiGateeventtime=1602663098 src=1.1.1.1 deviceInboundInterface=port1 FortinetFortiGatesrcintfrole=undefined dst=192.0.2.1 deviceOutboundInterface=root FortinetFortiGatedstintfrole=undefined externalId=4887198 proto=1 FortinetFortiGateaction=accept FortinetFortiGatepolicyid=0 FortinetFortiGatepolicytype=local-in-policy app=icmp/8/0 FortinetFortiGatedstcountry=Reserved FortinetFortiGatesrccountry=China FortinetFortiGatetrandisp=noop FortinetFortiGateapp=icmp/8/0 FortinetFortiGateduration=61 out=84 in=84 FortinetFortiGatesentpkt=1 FortinetFortiGatercvdpkt=1 FortinetFortiGateappcat=unscanned
time=18:58:47 devname="NAME_1" devid="ABCDEFG123456789" eventtime=1746291526925867188 tz="+0200" logid="0123456789" type="utm" subtype="ips" eventtype="malicious-url" level="warning" vd="Cristal" severity="high" srcip=1.2.3.4 srccountry="Reserved" dstip=5.6.7.8 dstcountry="Reserved" srcintf="Vlan15" srcintfrole="lan" dstintf="Vlan15" dstintfrole="lan" sessionid=1234567890 action="dropped" proto=6 service="HTTP" policyid=23 poluuid="11111111-1111-1111-1111-111111111111" policytype="policy" srcport=53335 dstport=8001 attack="malicious-url" direction="outgoing" msg="URL blocked by malicious-url-list" profile="IPS_Block_Profile" crscore=30 craction=8192 crlevel="high" hostname="example.com" url="/" agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/136.0.0.0 Safari/537.36 Edg/136.0.0.0" httpmethod="CONNECT"
time=14:22:37 devname="abc" devid="1" logid="0000000013" type="traffic" subtype="forward" level="notice" vd="ROUTER" eventtime=1602591758311908837 tz="+0200" srcip=1.1.1.1 identifier=29027 srcintf="test1" srcintfrole="undefined" dstip=192.0.2.1 dstintf="test" dstintfrole="undefined" sessionid=3558919660 proto=1 action="accept" policyid=637 policytype="policy" poluuid="b23818a6-8f49-51ea-9db7-4e4965a3483c" service="PING" dstcountry="Reserved" srccountry="Reserved" trandisp="noop" duration=64 sentbyte=420 rcvdbyte=420 sentpkt=5 rcvdpkt=5 appcat="unscanned"
eventtime=1741264760483566820 tz="+0100" logid="0116047301" type="event" subtype="rest-api" level="information" vd="root" logdesc="REST API request success" user="user1" ui="GUI(1.2.3.4)" method="GET" path="system.usb-log" status="200" url="/api/v2/monitor/system/usb-log?https://example.com/"
CEF:0|Fortinet|Fortigate|v6.0.4|32021|event:system login failed|7|deviceExternalId=FGVM2V0000171868 FortinetFortiGatelogid=0100032021 cat=event:system FortinetFortiGatesubtype=system FortinetFortiGatelevel=alert FortinetFortiGatevd=root FortinetFortiGateeventtime=1579172447 FortinetFortiGatelogdesc=Admin login disabled sproc=1.1.1.1 FortinetFortiGateaction=login outcome=failed reason=exceed_limit msg=Login disabled from IP 1.1.1.1 for 60 seconds because of 3 bad attempts
CEF:0|Fortinet|Fortigate|v6.0.10|39943|event:vpn ssl-new-con|2|deviceExternalId=FGT3HD3916803645 FTNTFGTlogid=0101039943 cat=event:vpn FTNTFGTsubtype=vpn FTNTFGTlevel=information FTNTFGTvd=root FTNTFGTeventtime=1637338258 FTNTFGTlogdesc=SSL VPN new connection act=ssl-new-con FTNTFGTtunneltype=ssl FTNTFGTtunnelid=0 dst=192.0.2.1 duser=N/A FTNTFGTgroup=N/A FTNTFGTdst_host=N/A reason=N/A msg=SSL new connection
0|Fortinet|FortiGate-100F|7.2.8,build1639 (GA)|0100032001|system event login|4|start=Mar 06 2025 13:38:52 logver=1111111 deviceExternalId=devExtID dvchost=TESTHOST vd=root eventtime=1741264732502103430 tz=+0100 logid=0100032001 cat=event subtype=system deviceSeverity=information logdesc=Admin login successful sn=1741264732 duser=admin sproc=ssh(1.2.3.4) method=ssh src=1.2.3.4 dst=192.0.2.1 act=login status=success reason=none profile=super_admin msg=Administrator admin logged in successfully from ssh(1.2.3.4) tz="+0000"
0|Fortinet|FortiGate-100F|7.2.8,build1639 (GA)|0100032001|system event login|4|start=Mar 06 2025 13:38:52 logver=702081639 deviceExternalId=FGTESTID dvchost=FGTESTHOST vd=root eventtime=1741264732502103430 tz=+0100 logid=0100032001 cat=event subtype=system deviceSeverity=information logdesc=Admin login successful sn=1741264732 duser=test sproc=ssh(1.2.3.4) method=ssh src=1.2.3.4 dst=3.4.5.6 act=login status=success reason=none profile=super_admin msg=Administrator test logged in successfully from ssh(1.2.3.4) tz="+0000"
time=13:39:08 devname="testHost" devid="testSerialNumber" eventtime=1741264747895826299 tz="+0100" logid="0100032003" type="event" subtype="system" level="information" vd="root" logdesc="Admin logout successful" sn="1741264747" user="user1" ui="https(5.6.7.8)" method="https" srcip=5.6.7.8 dstip=4.5.6.7 action="logout" status="success" duration=0 reason="exit" msg="Administrator user1 logged out from https(5.6.7.8)"
time=13:39:08 devname="testHostname" devid="testSerialNumber" eventtime=1741264747895826299 tz="+0100" logid="0100032003" type="event" subtype="system" level="information" vd="root" logdesc="Admin logout successful" sn="1741264747" user="testUser" ui="https(3.4.5.6)" method="https" srcip=3.4.5.6 dstip=1.2.3.4 action="logout" status="success" duration=0 reason="exit" msg="Administrator testUser logged out from https(3.4.5.6)"
time=13:39:08 devname="TESTDEVNAME" devid="TESTDEVID" eventtime=1741264747895826299 tz="+0100" logid="0100032003" type="event" subtype="system" level="information" vd="root" logdesc="Admin logout successful" sn="1741264747" user="user1" ui="https(1.2.3.4)" method="https" srcip=1.2.3.4 dstip=192.0.2.1 action="logout" status="success" duration=0 reason="exit" msg="Administrator user1 logged out from https(1.2.3.4)"
time=12:35:04 devname="DEVNAME01" devid="FGT123456ABCDEF" eventtime=1748601303656994360 tz="+0200" logid="0123456789" type="event" subtype="system" level="information" vd="root" logdesc="Attribute configured" user="admin" ui="jsconsole(1.2.3.4)" action="Edit" cfgtid=987654321 cfgpath="system.settings" cfgattr="gui-sslvpn[disable->enable]" msg="Edit system.settings "
time=12:35:04 devname="TESTDEVNAME" devid="TESTDEVID" eventtime=1748601303656994360 tz="+0200" logid="0100044546" type="event" subtype="system" level="information" vd="root" logdesc="Attribute configured" user="admin" ui="jsconsole(1.2.3.4)" action="Edit" cfgtid=153616384 cfgpath="system.settings" cfgattr="gui-sslvpn[disable->enable]" msg="Edit system.settings "
time=16:22:20 timestamp=1762528940 devname="FortiAuthenticator" devid="TEST_DEV_ID" vd="root" itime=1762528940 faclogindex="111111111" logid="20320" logdesc="AUTH_FAIL_USER_TEST_EVENT_DAT" type="event" subtype="Authentication" level="information" user="user1" nas="1.2.3.4" userip=192.0.2.1 action="Authentication" status="Failed" msg="User authentication from 192.0.2.1 (mschap) with no token failed: user not found" tz="+0100"
time=16:22:20 timestamp=1762528940 devname="FortiAuthenticator" devid="TEST_DEVICE_ID" vd="root" itime=1762528940 faclogindex="8321046" logid="20320" logdesc="AUTH_FAIL_USER_TEST_EVENT" type="event" subtype="Authentication" level="information" user="user1" nas="2.3.4.5" userip=192.0.2.1 action="Authentication" status="Failed" msg="User authentication from 192.0.2.1 (mschap) with no token failed: user not found" tz="+0100"
time=16:22:20 timestamp=1762528940 devname="FortiAuthenticator" devid="TEST_DEVICE_ID" vd="root" itime=1762528941 faclogindex="8321052" logid="20320" logdesc="AUTH_FAIL_USER_TEST_EVENT" type="event" subtype="Authentication" level="information" user="user1" nas="2.3.4.5" userip=192.0.2.1 action="Authentication" status="Failed" msg="User authentication from 192.0.2.1 (chap) with no token failed: user not found" tz="+0100"
time=13:53:24 devname="TEST_DEV_NAME" devid="DEVID1111111" eventtime=1749038004142040029 tz="+0200" logid="0100044547" type="event" subtype="system" level="information" vd="root" logdesc="Object attribute configured" user="admin" ui="GUI(1.1.1.1)" action="Add" cfgtid=1231232131 uuid="0000000-413a-51f0-3994-9f8f05c1432f" cfgpath="firewall.policy" cfgobj="6" cfgattr="name[vpn_remote_0]srcintf[TestTest]dstintf[internal]action[accept]srcaddr[TestTest]dstaddr[TestTest]schedule[always]service[ALL]comments[VPN: TestTest (Created by VPN wizard)]" msg="Add firewall.policy 6"
time=10:24:24 devname="TESTDEVNAME" devid="TESTTEST0000000" eventtime=1752819965 tz="+0200" logid="010000000000" type="event" subtype="system" level="information" vd="root" logdesc="Object attribute configured" user="user1" ui="GUI(192.0.2.1)" action="Add" cfgtid=1111111 uuid="0000000000-413a-51f0-3994-9f8f05c1432f" cfgpath="firewall.policy" cfgobj="6" cfgattr="name[vpn_TestTest_remote_0]srcintf[TestTest]dstintf[internal]action[accept]srcaddr[TestTest_remote]dstaddr[TestTest_local]schedule[always]service[ALL]comments[VPN: TestTest (Created by VPN wizard)]" msg="Add firewall.policy 6"
time=10:33:11 devname="FW-TTTTTTTT-1" devid="TESTDEV21111111" eventtime=1693557190787280122 tz="+0200" logid="0100044547" type="event" subtype="system" level="information" vd="TEST-APP" logdesc="Object attribute configured" user="admin" ui="RESTAPI(1.1.1.1)" action="Add" cfgtid=111111111 cfgpath="firewall.policy" cfgobj="95" cfgattr="uuid[0000000000-48a2-51ee-9a4e-d49ca8f62bfb]srcintf[Z_INTERCO]dstintf[Z_APP]action[accept]srcaddr[Nw-3.3.3.3-AdministrateursDN]dstaddr[Host-2.2.2.2-VIP_PROD]schedule[always]service[HTTPS PING]utm-status[enable]ssl-ssh-profile[certificate-inspection]ips-sensor[Sensor_Web]logtraffic[all]" msg="Add firewall.policy 95"
time=09:47:39 devname="TESTDEVNAME" devid="TESTDEVID01" logid="0100044547" type="event" subtype="system" level="information" vd="Part" eventtime=1645001259 logdesc="Object attribute configured" user="user1" ui="fgfm_tunnel" action="Add" cfgtid=1623130112 cfgpath="firewall.address" cfgobj="TEST1.1.1.1" cfgattr="uuid[00000000-8f03-51ec-de75-17ef43f88c98]subnet[2.1.1.1 255.255.255.255]" msg="Add firewall.address B2.1.1.1"
time=15:27:40 devname="TEST_DEV_NAME" devid="TEST_DEV_ID" logid="0100044546" type="event" subtype="system" level="information" vd="root" eventtime=1647440860 logdesc="Attribute configured" user="user1" ui="ssh(192.0.2.1)" action="Edit" cfgtid=613613570 cfgpath="log.syslogd.setting" cfgattr="server[1.2.1.1->1.2.2.2]" msg="Edit log.syslogd.setting "
time=16:03:54 devname="TEST_DEV_NAME" devid="TEST_DEV_ID" logid="0100044547" type="event" subtype="system" level="information" vd="Int" eventtime=1668524634891048583 tz="+0100" logdesc="Object attribute configured" user="user1" ui="fgfm_tunnel" action="Edit" cfgtid=146604040 cfgpath="firewall.policy" cfgobj="506" cfgattr="ips-sensor[g-default->default]application-list[g-default->default]" msg="Edit firewall.policy 506"
time=15:27:41 devname="TEST_DEV_NAME" devid="TEST_DEV_ID" logid="0100044546" type="event" subtype="system" level="information" vd="root" eventtime=1647440861 logdesc="Attribute configured" user="testuser" ui="ha_daemon" action="Edit" cfgtid=17898414 cfgpath="log.syslogd.setting" cfgattr="server[1.2.1.1->1.2.2.2]" msg="Edit log.syslogd.setting "
time=09:35:30 devname="eee-111-111-ff-11" devid="FG00000000000000" eventtime=1735202130361752831 tz="+0100" logid="0000000011" type="traffic" subtype="forward" level="notice" vd="EFF" srcip=1.2.3.4 srcport=10000 srcintf="EFF-WAN-0000" srcintfrole="lan" dstip=5.6.7.8 dstport=443 dstintf="EFF-DMZ-0000" dstintfrole="lan" srccountry="France" dstcountry="France" sessionid=400190000 proto=6 action="client-rst" policyid=1018 policytype="policy" poluuid="38fa6456-a819-51ef-3c99-000000000000000000" service="HTTPS" trandisp="dnat" tranip=1.2.3.4 tranport=443 duration=6 sentbyte=100 rcvdbyte=52 sentpkt=2 rcvdpkt=1 appcat="unscanned"
time=14:53:11 devname="FFF00D_TEST02" devid="FGT3HD300000000" eventtime=1735000001620000000 tz="+0100" logid="0000000010" type="traffic" subtype="forward" level="notice" vd="root" srcip=1.2.3.4 srcport=50000 srcintf="ssl.root" srcintfrole="undefined" dstip=192.0.2.1 dstport=80 dstintf="VPNM-TEST" dstintfrole="undefined" srccountry="Reserved" dstcountry="Reserved" sessionid=100100046 proto=6 action="close" policyid=274 policytype="policy" poluuid="ac8ed64c-54e7-51eb-3525-d610000000000" user="user1" group="TEST-SAML" authserver="azure-saml" service="HTTP" trandisp="snat" transip=192.0.2.1 transport=50066 duration=7 sentbyte=18800 rcvdbyte=7900 sentpkt=30 rcvdpkt=29 vpn="VPNM-TEST" vpntype="ipsec-static" appcat="unscanned"
timestamp=1698046849 devname="abc" devid="1" vd="root" date=2023-10-23 time=00:40:49 eventtime=1698046849852012802 tz="-0700" logid="0101037130" type="utm" subtype="ips" eventtype="signature" level="alert" severity="low" srcip=1.2.3.4 srccountry="Reserved" dstip=192.0.2.1 dstcountry="Reserved" srcintf="port2" srcintfrole="undefined" dstintf="port2" dstintfrole="undefined" sessionid=1234567890 action="detected" proto=6 service="HTTP" policyid=494 poluuid="aecacfaf-8d3f-4809-a60f-bf873e0fcab3" policytype="policy" attack="Qualys.Vulnerability.Scanner" srcport=37364 dstport=80 hostname="example.com" url="/cgi/rocket.pl?https://example.com/" direction="outgoing" attackid=45660 profile="Example_IPS" ref="http://www.fortinet.com/ids/VID45660" incidentserialno=1234567 msg="tools: Qualys.Vulnerability.Scanner" crscore=5 craction=32768 crlevel="low"
time=08:32:58 devname="NAME_1" devid="ABCDEFG123456789" eventtime=1746599578550052585 tz="+0200" logid="0000000020" type="traffic" subtype="forward" level="notice" vd="Cristal" srcip=1.2.3.4 srcport=57974 srcintf="Vlan15" srcintfrole="lan" dstip=5.6.7.8 dstport=7224 dstintf="Vlan3200" dstintfrole="lan" srccountry="Reserved" dstcountry="Reserved" sessionid=1234567890 proto=6 action="accept" policyid=4 policytype="policy" poluuid="11111111-1111-1111-1111-111111111111" policyname="Cristal6 vers interne" service="tcp/7224" trandisp="noop" duration=1697591 sentbyte=12604185928 rcvdbyte=24366746607 sentpkt=133755826 rcvdpkt=115991007 appcat="unscanned" sentdelta=771825 rcvddelta=4330052
time=15:15:29 devname="TESTDEVNAME" devid="TESTDEVIT" eventtime=1758287729906413196 tz="+0200" logid="0123456789" type="utm" subtype="ips" eventtype="signature" level="alert" vd="VIRTUALDOMAIN" severity="medium" srcip=1.2.3.4 srccountry="Reserved" dstip=5.6.7.8 dstcountry="Reserved" srcintf="INTF_1" srcintfrole="undefined" dstintf="INTF_2" dstintfrole="undefined" sessionid=234567890 action="dropped" proto=6 service="HTTP" policyid=49 poluuid="3eee479c-acfe-4861-941a-291eb6d1360d" policytype="policy" attack="HTTP.Referer.Header.SQL.Injection" srcport=57561 dstport=80 hostname="example.com" url="/" agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/99.0.4844.0 Safari/537.36" httpmethod="GET" referralurl="https://example.com/" direction="outgoing" attackid=12345 profile="Sensor_Web" ref="http://www.fortinet.com/ids/VID12345" incidentserialno=11223344 msg="web_misc: HTTP.Referer.Header.SQL.Injection" forwardedfor="9.10.11.12" crscore=10 craction=16384 crlevel="medium"
time=16:45:21 devname="TEST_DEVICE" devid="TEST_DEVICE_ID" eventtime=1770824721111372922 tz="+0100" logid="XXXXXXXXXX" type="event" subtype="system" level="information" vd="root" logdesc="SSL connection failed" dstip=N/A dstport=N/A reason="self-signed certificate in certificate chain" action="info" status="failure" msg="Certificate is invalid, subject: /C=XX/ST=XXXXXXXX/L=XXXXXXXXX/O=Fortinet/OU=Certificate Authority/CN=XXXXXXXXXXXXX/emailAddress=example@example.com"
time=14:01:16 devname="NAME_1" devid="ABCDEFG123456789" eventtime=1746446476968701953 tz="+0200" logid="1234567890" type="utm" subtype="ips" eventtype="signature" level="alert" vd="VD_Int" severity="critical" srcip=1.2.3.4 srccountry="France" dstip=5.6.7.8 dstcountry="Reserved" srcintf="port24" srcintfrole="undefined" dstintf="Vlan3194" dstintfrole="lan" sessionid=3017954790 action="dropped" proto=6 service="SSL" policyid=41 poluuid="11111111-1111-1111-1111-111111111111" policytype="policy" attack="OpenSSL.Heartbleed.Attack" srcport=61087 dstport=443 hostname="example.com" url="/" direction="outgoing" attackid=38315 profile="IPS_Block_Profile" ref="http://www.fortinet.com/ids/VID38315" incidentserialno=261102216 msg="applications: OpenSSL.Heartbleed.Attack, OpenSSL Heartbleed" crscore=50 craction=4096 crlevel="critical"
time=08:20:44 devname="computer-039482" devid="C10382849" eventtime=1669620044749365658 tz="+0100" logid="0000000020" type="traffic" subtype="forward" level="notice" vd="root" srcip=1.2.3.4 srcname="example.com" srcport=52272 srcintf="ID102" srcintfrole="lan" dstip=5.6.7.8 dstport=443 dstintf="ID015" dstintfrole="wan" srcuuid="ccd49675-9207-46cf-9c4b-8d522c2b977e" srccountry="Reserved" dstinetsvc="Microsoft-Office365.Published" dstcountry="France" dstregion="Ile-de-France" dstcity="Paris" dstreputation=5 sessionid=111111111 proto=6 action="accept" policyid=37 policytype="policy" poluuid="6a8f76d0-1459-4ddb-948a-62700ddbf241" service="Microsoft-Office365.Published" trandisp="snat" transip=4.3.2.1 transport=52272 duration=258 sentbyte=160972 rcvdbyte=58449 sentpkt=333 rcvdpkt=192 vwlid=8 vwlquality="Seq_num(13 ID015), alive, custom1: 78.211: 0.000% 7.754 0.067 897379Kbps, selected" vwlname="TO-INTERNET" appcat="unscanned" sentdelta=31328 rcvddelta=10476 srchwvendor="Dell" devtype="Home & Office" srcfamily="Computer" osname="Windows" srcswversion="10" unauthuser="example.com\jdoe" unauthusersource="kerberos" mastersrcmac="02:00:00:00:00:00" srcmac="02:00:00:00:00:00" srcserver=0
timestamp=1759197338 devname="my-device" devid="1111111111111111" vd="root" itime=1759186539 logver=0704072731 date=2025-09-30 time=00:55:38 eventtime="1759186539261872875" tz="+0200" logid="1500054000" type="utm" subtype="ips" eventtype=signature level="alert" severity="high" srcip=192.168.2.1 srccountry="Reserved" dstip=1.2.3.4 dstcountry="Reserved" srcintf="x8" srcintfrole="dmz" dstintf="INTF-2" dstintfrole="lan" sessionid=123456789 action="dropped" proto=6 service="HTTPS" policyid=84 poluuid="46e3c770-bcb4-4ba5-a98e-0873f6023aae" policytype="policy" attack="Adobe.ColdFusion.CVE-2023-44352.Reflected.XSS" srcport=53369 dstport=443 hostname="example.com" url="/8tlck5A7%22%3E%3Cscript%3Ealert(document.domain)%3C/script%3E/..CFIDE/wizards/common/_authenticatewizarduser.cfm" agent="Mozilla/5.0 (Knoppix; Linux i686) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36" httpmethod=GET direction=outgoing attackid=54356 profile=default ref=http://www.fortinet.com/ids/VID54356 incidentserialno=201043218 msg="applications3: Adobe.ColdFusion.CVE-2023-44352.Reflected.XSS" forwardedfor=5.6.7.8:51912 crscore=30 craction=8192 crlevel="high"
timestamp=1742602531 devname="XXX" devid="XXX" vd="root" date=2025-03-22 time=00:15:31 eventtime=1742613330828471629 tz="-0300" logid="0000000013" type="traffic" subtype="forward" level="notice" srcip=1.2.3.4 srcport=60568 srcintf="port1" srcintfrole="undefined" dstip=192.0.2.1 dstport=53 dstintf="XXX" dstintfrole="undefined" srccountry="Reserved" dstcountry="Japan" sessionid=496025498 proto=17 action="accept" policyid=398 policytype="policy" poluuid="poluuidvalue" service="udp-53" trandisp="noop" appid=16195 app="DNS" appcat="Network.Service" apprisk="elevated" applist="XXX" duration=180 sentbyte=0 rcvdbyte=0 sentpkt=0 rcvdpkt=0 vpntype="ipsecvpn" utmaction="block" countips=1 crscore=30 craction=8192
CEF:0|Fortinet|FortiGate-1000C|5.6.14,build1727 (GA)|0000000020|forward traffic accept|5|start=Oct 12 2022 12:50:31 logver=506141727 deviceExternalId=FGT123 dvchost=FW-123 ad.vd=root ad.logid=0000000020 cat=traffic ad.subtype=forward deviceSeverity=notice ad.eventtime=1665571831 src=1.1.1.1 spt=55390 deviceInboundInterface=abc ad.srcintfrole=undefined dst=192.0.2.1 dpt=1522 deviceOutboundInterface=efg ad.dstintfrole=lan foo.poluuid=ec6ff8fe-5e41-51ec-bcbe-9e5484033dc8 externalID=3812440508 proto=6 act=accept ad.policyid=185 ad.policytype=policy app=SQLNET-1522 ad.dstcountry=Reserved ad.srccountry=Reserved ad.trandisp=noop ad.duration=268 out=202 in=52 ad.sentpkt=3 ad.rcvdpkt=1 ad.appcat=unscanned ad.sentdelta=0 ad.rcvddelta=0 tz="+0200"
CEF:0|Fortinet|Fortigate|v6.0.4|00013|traffic:forward timeout|3|deviceExternalId=FGVM2V0000171868 FortinetFortiGatelogid=0000000013 cat=traffic:forward FortinetFortiGatesubtype=forward FortinetFortiGatelevel=notice FortinetFortiGatevd=root FortinetFortiGateeventtime=1572471876 src=1.1.1.1 spt=49260 deviceInboundInterface=port1 FortinetFortiGatesrcintfrole=undefined dst=192.0.2.1 dpt=80 deviceOutboundInterface=port2 FortinetFortiGatedstintfrole=undefined FortinetFortiGatepoluuid=bafe134e-c0ad-51e8-ed9c-52f798dd69d4 externalId=12812952 proto=6 FortinetFortiGateaction=timeout FortinetFortiGatepolicyid=1 FortinetFortiGatepolicytype=policy app=HTTP FortinetFortiGatedstcountry=Reserved FortinetFortiGatesrccountry=United States FortinetFortiGatetrandisp=dnat destinationTranslatedAddress=192.0.2.1 destinationTranslatedPort=80 FortinetFortiGateduration=20 out=48 in=144 FortinetFortiGatesentpkt=1 FortinetFortiGatercvdpkt=3 FortinetFortiGateappcat=unscanned FortinetFortiGatecrscore=5 FortinetFortiGatecraction=262144 FortinetFortiGatecrlevel=low
CEF:0|Fortinet|Fortigate|v6.0.3|00013|traffic:forward close|3|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0000000013 cat=traffic:forward FTNTFGTsubtype=forward FTNTFGTlevel=notice FTNTFGTvd=vdom1 FTNTFGTeventtime=1545937675 src=10.1.100.11 spt=54190 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined dst=192.0.2.1 dpt=443 deviceOutboundInterface=port11 FTNTFGTdstintfrole=undefined FTNTFGTpoluuid=c2d460aa-fe6f-51e8-9505-41b5117dfdd4 externalId=402 proto=6 act=close FTNTFGTpolicyid=1 FTNTFGTpolicytype=policy app=HTTPS FTNTFGTdstcountry=United States FTNTFGTsrccountry=Reserved FTNTFGTtrandisp=snat sourceTranslatedAddress=172.16.200.1 sourceTranslatedPort=54190 FTNTFGTappid=40568 FTNTFGTapp=HTTPS.BROWSER FTNTFGTappcat=Web.Client FTNTFGTapprisk=medium FTNTFGTapplist=g-default FTNTFGTduration=2 out=3652 in=146668 FTNTFGTsentpkt=58 FTNTFGTrcvdpkt=105 FTNTFGTutmaction=allow FTNTFGTcountapp=2
CEF:0|Fortinet|Fortigate|v7.2.8|00013|traffic:forward client-rst|3|deviceExternalId=FGTEXAMPLE subtype=forward FTNTFGTlevel=notice FTNTFGTvd=root src=1.2.3.4 shost=example.com spt=59020 deviceInboundInterface=LAN-EX-SRV FTNTFGTsrcintfrole=lan dst=5.6.7.8 dpt=65359 deviceOutboundInterface=CASio-1_0 FTNTFGTdstintfrole=wan FTNTFGTsrccountry=Reserved FTNTFGTdstcountry=Reserved externalId=26368100 proto=6 act=client-rst FTNTFGTpolicyid=353 FTNTFGTpolicytype=policy FTNTFGTpoluuid=2967ec4c-c4d7-51ed-30a5-720dc6023629 FTNTFGTpolicyname=AD-CASio_TO_DC app=tcp/65359 FTNTFGTtrandisp=noop FTNTFGTduration=175 out=3608 in=2571 FTNTFGTsentpkt=15 FTNTFGTrcvdpkt=11 FTNTFGTvpntype=ipsecvpn FTNTFGTvwlid=4 FTNTFGTvwlquality=Seq_num(1 CASIio-1_0), alive, selected FTNTFGTvwlname=TO_JOE FTNTFGTappcat=unscanned FTNTFGTpsrcport=58624 FTNTFGTpdstport=135 FTNTFGTsentdelta=80 FTNTFGTrcvddelta=2519 FTNTFGTsrchwvendor=VMware FTNTFGTosname=Windows FTNTFGTsrcswversion=10 FTNTFGTunauthuser=REDACTED FTNTFGTunauthusersource=kerberos FTNTFGTmastersrcmac=02:00:00:00:00:00 FTNTFGTsrcmac=02:00:00:00:00:00 FTNTFGTsrcserver=0
0|Fortinet|Fortigate|v7.2.10|00011|traffic:forward ip-conn|4|deviceExternalId=FGT40FTK23052620 FTNTFGTeventtime=1737553257865429339 FTNTFGTtz=+0100 FTNTFGTlogid=0000000011 cat=traffic:forward FTNTFGTsubtype=forward FTNTFGTlevel=warning FTNTFGTvd=root src=1.2.3.4 shost=example.com spt=53272 deviceInboundInterface=interface_02 FTNTFGTsrcintfrole=lan dst=5.6.7.8 dpt=443 deviceOutboundInterface=interface_01 FTNTFGTdstintfrole=undefined FTNTFGTsrccountry=Reserved FTNTFGTdstcountry=France externalId=1248357 proto=6 act=ip-conn FTNTFGTpolicyid=6 FTNTFGTpolicytype=policy FTNTFGTpoluuid=c2d241ae-2bb9-51ee-e76b-094ea7f446e8 app=HTTPS FTNTFGTappcat=unscanned FTNTFGTcrscore=5 FTNTFGTcraction=262144 FTNTFGTcrlevel=low FTNTFGTosname=Windows FTNTFGTsrcswversion=10 / 2016 FTNTFGTunauthuser=jdoe FTNTFGTunauthusersource=kerberos FTNTFGTmastersrcmac=02:00:00:00:00:00 FTNTFGTsrcmac=02:00:00:00:00:00 FTNTFGTsrcserver=0
```<br><br><i>(created from <a href=https://sekoia8055.zendesk.com/agent/tickets/5534>Zendesk ticket #5534</a>)<br> gz#5534</i>
CEF:0|Fortinet|Fortigate|v7.4.9|00013|traffic:forward close|3|deviceExternalId=FGTEXAMPLE FTNTFGTeventtime=1762443492031974938 FTNTFGTtz=+0100 FTNTFGTlogid=0000000013 cat=traffic:forward FTNTFGTsubtype=forward FTNTFGTlevel=notice FTNTFGTvd=root src=1.2.3.4 spt=64746 deviceInboundInterface=port2 FTNTFGTsrcintfrole=dmz dst=192.168.115.11 dpt=8093 deviceOutboundInterface=port10 FTNTFGTdstintfrole=dmz FTNTFGTsrccountry=Reserved FTNTFGTdstcountry=Reserved externalId=1234 proto=6 act=close FTNTFGTpolicyid=859 FTNTFGTpolicytype=policy FTNTFGTpoluuid=00000000-0000-0000-0000-000000000000 FTNTFGTpolicyname=Filtrage ID Eset app=TCP_8093 FTNTFGTtrandisp=noop FTNTFGTappid=47013 FTNTFGTapp=SSL_TLSv1.3 FTNTFGTappcat=Network.Service FTNTFGTapprisk=medium FTNTFGTapplist=g-APP_MONITOR FTNTFGTduration=92 out=1504 in=2647 FTNTFGTsentpkt=9 FTNTFGTrcvdpkt=9 FTNTFGTutmaction=allow FTNTFGTcountapp=2
CEF:0|Fortinet|Fortigate|v7.4.9|00013|traffic:forward client-rst|3|deviceExternalId=FGTEXAMPLE FTNTFGTeventtime=1762521404541985717 FTNTFGTtz=+0100 FTNTFGTlogid=0000000013 cat=traffic:forward FTNTFGTsubtype=forward FTNTFGTlevel=notice FTNTFGTvd=root src=1.2.3.4 spt=56006 deviceInboundInterface=port2 FTNTFGTsrcintfrole=dmz dst=192.168.100.7 dpt=8080 deviceOutboundInterface=port1 FTNTFGTdstintfrole=dmz FTNTFGTsrccountry=Reserved FTNTFGTdstcountry=Reserved externalId=1234 proto=6 act=client-rst FTNTFGTpolicyid=860 FTNTFGTpolicytype=policy FTNTFGTpoluuid=00000000-0000-0000-0000-000000000000 FTNTFGTpolicyname=Filtrage ID Proxy duser=USER1 FTNTFGTauthserver=FSSO_collector_agent-1 FTNTFGTdstuser=USER2 app=http_https_proxy FTNTFGTtrandisp=noop FTNTFGTappid=52305 FTNTFGTapp=TrendMicro.IWSVA FTNTFGTappcat=Cloud.IT FTNTFGTapprisk=low FTNTFGTapplist=g-APP_MONITOR FTNTFGTduration=35 out=440 in=518 FTNTFGTsentpkt=5 FTNTFGTrcvdpkt=5 FTNTFGTutmaction=allow FTNTFGTcountapp=2 FTNTFGTcrscore=10 FTNTFGTcraction=1048576 msg=Connection Failed
CEF:0|Fortinet|Fortigate|v5.6.0|00013|traffic:forward close|3|FTNTFGTlogid=0000000013 cat=traffic:forward FTNTFGTsubtype=forward FTNTFGTlevel=notice FTNTFGTvd=vdom1 src=hostname shost=example spt=45719 deviceInboundInterface=port15 dst=hostname dhost=hostname dpt=80 deviceOutboundInterface=port19 FTNTFGTpoluuid=61c4243a-34ba-51e5-c32a-3859389a5162 externalId=56633 proto=6 act=close cs5=10 cs5Label=Policy Id FTNTFGTdstcountry=Reserved FTNTFGTsrccountry=Reserved FTNTFGTtrandisp=snat sourceTranslatedAddress=1.1.1.1 sourceTranslatedPort=45719 app=HTTP FTNTFGTappid=38783 FTNTFGTapp=Wget.Like FTNTFGTappcat=General.Interest FTNTFGTapprisk=low FTNTFGTapplist=default FTNTFGTappact=detected cn1=7 cn1Label=Duration out=398 in=1605 cn2=5 cn2Label=Packets Sent cn3=5 cn3Label=Packets Received FTNTFGTutmaction=block FTNTFGTcountav=1 FTNTFGTcountapp=1 FTNTFGTcrscore=50 FTNTFGTcraction=2
date=2018-07-26,time=16:51:36,logid="0000000013",type="traffic",subtype="forward",level="notice",vd="root",eventtime=1532616695,srcip=1.1.1.1,srcport=10016,srcintf="test",srcintfrole="undefined",dstip=192.0.2.1,dstport=20,dstintf="dmz1",dstintfrole="dmz",sessionid=10006,proto=6,action="accept",policyid=1,policytype="policy",service="tcp/20",dstcountry="France",srccountry="United States",trandisp="noop",appid=35421,app="application",appcat="Storage.Backup",apprisk="medium",applist="default",duration=10,sentbyte=2000,rcvdbyte=1000,sentpkt=0,rcvdpkt=0,utmaction="allow",countapp=1,devtype="iPad",osname="Apple",osversion="ver",mastersrcmac="02:00:00:00:00:00",srcmac="02:00:00:00:00:00",srcserver=0,dstdevtype="Android Phone",dstosname="Android",dstosversion="ver",masterdstmac="02:00:00:00:00:00",dstmac="02:00:00:00:00:00",dstserver=0,utmref=65491-194
date=2018-07-26 time=16:51:36 logid="0000000013" type="traffic" subtype="forward" level="notice" vd="root" eventtime=1532616695 srcip=1.1.1.1 srcport=10016 srcintf="test" srcintfrole="undefined" dstip=192.0.2.1 dstport=20 dstintf="test1" dstintfrole="dmz" sessionid=10006 proto=6 action="accept" policyid=1 policytype="policy" service="tcp/20" dstcountry="France" srccountry="United States" trandisp="noop" appid=35421 app="Dropbox_File.Download" appcat="Storage.Backup" apprisk="medium" applist="default" duration=10 sentbyte=2000 rcvdbyte=1000 sentpkt=0 rcvdpkt=0 utmaction="allow" countapp=1 devtype="iPad" osname="Apple" osversion="ver" mastersrcmac="02:00:00:00:00:00" srcmac="02:00:00:00:00:00" srcserver=0 dstdevtype="Android Phone" dstosname="Android" dstosversion="ver" masterdstmac="02:00:00:00:00:00" dstmac="02:00:00:00:00:00" dstserver=0 utmref=65491-194
date=2021-06-21 time=09:38:29 devname="abc" devid="1" logid="0000000010" type="traffic" subtype="forward" level="notice" vd="PRX1-AA" eventtime=1624261109 srcip=1.1.1.1 srcport=50592 srcintf="port2" srcintfrole="dmz" dstip=192.0.2.1 dstport=443 dstintf="test" dstintfrole="wan" sessionid=1224900441 poluuid="1eb429d4-ff52-51ea-d119-d1db60e409a6" dstcountry="United Kingdom" srccountry="Reserved" service="HTTPS" wanoptapptype="web-proxy" proto=6 action="accept" duration=37 policyid=1 policytype="proxy-policy" wanin=5851 rcvdbyte=5851 wanout=2523 lanin=2769 sentbyte=2769 lanout=5923 appcat="unscanned" utmaction="allow" countweb=1
CEF:0|Fortinet|Fortigate|v6.4.9|00011|traffic:forward dns|4|deviceExternalId=FG5H0ETB19909686 FTNTFGTeventtime=1662381825920035319 FTNTFGTtz=+0200 FTNTFGTlogid=0000000011 cat=traffic:forward FTNTFGTsubtype=forward FTNTFGTlevel=warning FTNTFGTvd=root src=172.16.222.150 spt=49956 deviceInboundInterface=port1 FTNTFGTsrcintfrole=wan dst=172.18.67.10 dpt=53 deviceOutboundInterface=RWC FRANCE 2023 FTNTFGTdstintfrole=lan FTNTFGTsrccountry=Reserved FTNTFGTdstcountry=Reserved externalId=1797928567 proto=17 act=dns FTNTFGTpolicyid=30 FTNTFGTpolicytype=policy FTNTFGTpoluuid=6c8b6672-0b92-51ea-95a0-556c3c0fdb8f FTNTFGTpolicyname=CLT-RWC2023-001 FTNTFGTcentralnatid=6 app=DNS FTNTFGTappcat=unscanned FTNTFGTcrscore=5 FTNTFGTcraction=262144 FTNTFGTcrlevel=low FTNTFGTdsthwvendor=VMware FTNTFGTdstdevtype=Server FTNTFGTdstfamily=Virtual Machine FTNTFGTdstosname=Windows FTNTFGTdsthwversion=Workstation Pro FTNTFGTdstswversion=7 FTNTFGTmasterdstmac=02:00:00:00:00:00 FTNTFGTdstmac=02:00:00:00:00:00 FTNTFGTdstserver=0
date=2018-07-26 time=14:56:21 devname="abc" devid="1" logid="0000000013" type="traffic" subtype="forward" level="notice" vd="root" eventtime=1609941381 srcip=1.1.1.1 srcport=52125 srcintf="port9" srcintfrole="undefined" dstip=192.0.2.1 dstport=3727 dstintf="port10" dstintfrole="undefined" poluuid="d77c53b2-a3c6-51e9-49b2-61c9e68c1f7e" sessionid=578033623 proto=6 action="server-rst" policyid=207 policytype="policy" service="tcp/3727" dstcountry="France" srccountry="Netherlands" trandisp="dnat" tranip=192.0.2.1 tranport=3727 duration=5 sentbyte=80 rcvdbyte=40 sentpkt=2 rcvdpkt=1 appcat="unscanned" dstdevtype="Router/NAT Device" dstdevcategory="Windows Device" masterdstmac="02:00:00:00:00:00" dstmac="02:00:00:00:00:00" dstserver=1
timestamp=1709762763 devname="FW-001" devid="FG100D6G11111111" vd="root" date=2024-03-06 time=22:06:03 logid="0000000013" type="traffic" subtype="forward" level="notice" eventtime=1709762764028577926 tz="+0000" srcip=1.2.3.4 srcname="example.com" srcport=62979 srcintf="Port3.999" srcintfrole="lan" dstip=5.6.7.8 dstport=53 dstintf="wan1" dstintfrole="undefined" sessionid=538959618 proto=17 action="accept" policyid=41 policytype="policy" poluuid="703570eee-edfc-4565-8599-c6a75fd3e1e8" service="DNS" dstcountry="France" srccountry="Reserved" trandisp="snat" transip=192.0.2.1 transport=62979 appid=16195 app="DNS" appcat="Network.Service" apprisk="elevated" applist="EMEA_Monitor" duration=189 sentbyte=285 rcvdbyte=0 sentpkt=5 rcvdpkt=0 osname="Windows" srcswversion="10" mastersrcmac="02:00:00:00:00:00" srcmac="02:00:00:00:00:00" srcserver=0
timestamp=1732640381 devname="12_LE_XXXXX-60F" devid="xxxxxxxxxxxxxxxxxxx" vd="root" date=2024-11-26 time=16:59:41 eventtime=1732633180924621531 tz="+0200" logid="0000000013" type="traffic" subtype="forward" level="notice" srcip=1.2.3.4 srcname="example.com" srcport=56745 srcintf="internal" srcintfrole="undefined" dstip=192.0.2.1 dstport=80 dstintf="wan1" dstintfrole="undefined" srccountry="Reserved" dstcountry="Egypt" sessionid=157131884 proto=6 action="close" policyid=12 policytype="policy" poluuid="c1353c04-b6ee-51ea-9664-c8541f024774" policyname="LAN to Internet" service="HTTP" trandisp="snat" transip=192.0.2.1 transport=56745 appid=15893 app="HTTP.BROWSER" appcat="Web.Client" apprisk="medium" applist="block-high-risk" duration=1 sentbyte=483 rcvdbyte=399 sentpkt=7 rcvdpkt=5 wanin=187 wanout=111 lanin=111 lanout=187 utmaction="allow" countweb=1 osname="Windows" srcswversion="10" mastersrcmac="02:00:00:00:00:00" srcmac="02:00:00:00:00:00" srcserver=0
logver=704072731 timestamp=1744010938 devname="my-device" devid="1111111111111111" vd="root" date=2025-04-07 time=07:28:58 eventtime=1744010938310787908 logid="0000000020" type="traffic" subtype="forward" level="notice" srcip=1.2.3.4 srcport=55880 srcintf="ssl.root" srcintfrole="undefined" dstip=5.6.7.8 dstport=22 dstintf="VLAN-4002" dstintfrole="lan" srcuuid="d24dfae2-ee8d-4319-ac8a-f49fb888f8c3" dstuuid="1949578e-2022-47e4-a779-069cfca42d20" srccountry="Reserved" dstcountry="Reserved" sessionid=123 proto=6 action="accept" policyid=9 policytype="policy" poluuid="194b8d20-da82-4838-ae8c-712bcdb8eba7" policyname="sslvpn_2_prd-vault-net" user="john.doe,cn=john.doe" group="my-group" service="SSH" trandisp="snat" transip=192.0.2.1 transport=55880 appcat="unscanned" duration=9380 sentbyte=215866 rcvdbyte=515657 sentpkt=2954 rcvdpkt=2055 sentdelta=156 rcvddelta=80 durationdelta=120 sentpktdelta=2 rcvdpktdelta=1 dsthwvendor="Fortinet" dstdevtype="Router" masterdstmac="02:00:00:00:00:00" dstmac="02:00:00:00:00:00" dstserver=0 tz="+0000"
time=10:11:05 devname=MYDEVICE device_id=1111111111111111 log_id=000000001 type=traffic subtype=slb_http pri=information vd=waf msg_id=123456 duration=2742 ibytes=4513 obytes=4518 proto=6 service="https" src="1.2.3.4" src_port=52412 dst="5.6.7.8" dst_port=443 trans_src="9.10.11.12" trans_src_port=56484 trans_dst="13.14.15.16" trans_dst_port=80 policy="VS_FRED_PROD_WEB" action="user1" http_method="get" http_host="example.com" http_agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/138.0.0.0 Safari/537.36" http_url="/api/v2/Users" http_qry="ciId=82613&onlyActive=true&/api/v2/Users" http_referer="https://example.com/index" http_cookie="COOKIES" http_retcode="200" user="user1" usrgrp="user1" auth_status="user1" srccountry="Reunion" dstcountry="Reserved" real_server="PROD_WEB01_13.14.15.16"
logver=60 timestamp=1566916060 tz="UTC+2" devname="abc" devid="1" vd="IPSEC" date=2019-08-27 time=16:27:40 logid="0101039949" type="event" subtype="vpn" level="information" eventtime=1566916060 logdesc="SSL VPN statistics" action="tunnel-stats" tunneltype="ssl-tunnel" tunnelid=1995 remip=1.1.1.1 tunnelip=192.0.2.1 user="test" group="GRP_Generic_JAIL_VPN" dst_host="N/A" nextstat=600 duration=8437 sentbyte=71524041 rcvdbyte=6151809 msg="SSL tunnel statistics"
time=12:02:57 devname="abc" devid="1" logid="0101037141" type="event" subtype="vpn" level="notice" vd="root" eventtime=1614855777 logdesc="IPsec tunnel statistics" msg="IPsec tunnel statistics" action="tunnel-stats" remip=1.1.1.1 locip=192.0.2.1 remport=500 locport=500 outintf="N/A" cookies="9b064274e0648c03/662c2b1264a2295e" user="N/A" group="N/A" xauthuser="N/A" xauthgroup="N/A" assignip=N/A vpntunnel="VPN-HELPLINE" tunnelip=N/A tunnelid=0 tunneltype="ipsec" duration=102908570 sentbyte=7649 rcvdbyte=0 nextstat=600
time=14:38:46 devname="abc" devid="1" logid="0101041987" type="event" subtype="vpn" level="information" vd="root" eventtime=1615469926 logdesc="Certificate updated" action="info" cert-type="CRL" status="success" name="CRL_1" method="HTTP" reason="N/A" msg="A certificate is updated"
time=17:43:43 devname="FW-FOOBAR" devid="FG123" eventtime=1665675824075327440 tz="+0200" logid="0101039426" type="event" subtype="vpn" level="alert" vd="root" logdesc="SSL VPN login fail" action="ssl-login-fail" tunneltype="ssl-web" tunnelid=0 remip=1.1.1.1 user="user1" group="N/A" dst_host="N/A" reason="sslvpn_login_cert_checked_error" msg="SSL user failed to logged in"
time=17:43:43 devname="FW-FOOBAR" devid="FG123" eventtime=1665675824075327440 tz="+0200" logid="0101039426" type="event" subtype="vpn" level="alert" vd="root" logdesc="SSL VPN login fail" action="ssl-login-fail" tunneltype="ssl-web" tunnelid=0 remip="N/A" user="user1" group="N/A" dst_host="N/A" reason="sslvpn_login_cert_checked_error" msg="SSL user failed to logged in"
eventtime=1741260033782633377 tz="+0100" logid="0319013317" type="utm" subtype="webfilter" eventtype="urlmonitor" level="notice" vd="root" policyid=32 poluuid="test-pol-uuid" policytype="proxy-policy" sessionid=1139869359 user="user1" group="ADMIN" authserver="TEST_AUTH_SERVER" srcip=1.2.3.4 srcport=18355 srccountry="Japan" srcintf="port2" srcintfrole="lan" dstip=3.4.5.6 dstport=443 dstcountry="United States" dstintf="Orange_Pro" dstintfrole="wan" proto=6 service="HTTPS" hostname="example.com" profile="TEST_AUTH_SERVER Web Defaut" action="passthrough" reqtype="direct" url="https://example.com/" sentbyte=421 rcvdbyte=0 direction="outgoing" msg="URL has been visited" method="ip" cat=255
time=12:20:33 devname="testDev" devid="FGVM2VTM21000062" eventtime=1741260033527521837 tz="+0100" logid="0317013312" type="utm" subtype="webfilter" eventtype="ftgd_allow" level="notice" vd="root" policyid=106 poluuid="test-pol-uuid" policytype="policy" sessionid=958259665 srcip=1.2.3.4 srcport=55377 srccountry="Reserved" srcintf="T_testDev" srcintfrole="undefined" srcuuid="test-src-uuid" dstip=3.4.5.6 dstport=80 dstcountry="France" dstintf="port4" dstintfrole="undefined" dstuuid="test-dst-uuid" proto=6 service="HTTP" hostname="example.com" profile="Filtrage_web_Avancé" action="passthrough" reqtype="direct" url="http://example.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%123123123%3D" sentbyte=400 rcvdbyte=0 direction="outgoing" msg="URL belongs to an allowed category in policy" method="domain" cat=50 catdesc="Information and Computer Security"
CEF:0|Fortinet|Fortigate|v6.0.3|13056|utm:webfilter ftgd_blk blocked|4|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0316013056 cat=utm:webfilter FTNTFGTsubtype=webfilter FTNTFGTeventtype=ftgd_blk FTNTFGTlevel=warning FTNTFGTvd=vdom1 FTNTFGTeventtime=1545938629 FTNTFGTpolicyid=1 externalId=764 duser=example.com\\\\bob src=10.1.100.11 spt=59194 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined dst=192.0.2.1 dpt=80 deviceOutboundInterface=port11 FTNTFGTdstintfrole=undefined proto=6 app=HTTP dhost=example.com FTNTFGTprofile=g-default act=blocked FTNTFGTreqtype=direct request=/bizsquads out=96 in=0 deviceDirection=1 msg=URL belongs to a denied category in policy FTNTFGTmethod=domain FTNTFGTcat=26 requestContext=Malicious Websites FTNTFGTcrscore=60 FTNTFGTcrlevel=high
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake Fortinet FortiGate. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x Fortinet FortiGate on ATT&CK Navigator
Account Added To A Security Enabled Group
Detection in order to investigate who has added a specific Domain User in Domain Admins or Group Policy Creator Owners (Security event 4728)
- Effort: master
Account Removed From A Security Enabled Group
Detection in order to investigate who has removed a specific Domain User in Domain Admins or Group Policy Creator Owners (Security event 4729)
- Effort: master
Advanced IP Scanner
Detects the use of Advanced IP Scanner. Seems to be a popular tool for ransomware groups.
- Effort: master
Backup Catalog Deleted
The rule detects when the Backup Catalog has been deleted. It means the administrators will not be able to access any backups that were created earlier to perform recoveries. This is often being done using the wbadmin.exe tool.
- Effort: intermediate
Bazar Loader DGA (Domain Generation Algorithm)
Detects Bazar Loader domains based on the Bazar Loader DGA
- Effort: elementary
Burp Suite Tool Detected
Burp Suite is a cybersecurity tool. When used as a proxy service, its purpose is to intercept packets and modify them to send them to the server. Burp Collaborator is a network service that Burp Suite uses to help discover many kinds of vulnerabilities (vulnerabilities scanner).
- Effort: intermediate
CVE-2018-11776 Apache Struts2
Apache Struts versions 2.3 to 2.3.34 and 2.5 to 2.5.16 suffer from possible Remote Code Execution when alwaysSelectFullNamespace is true (either by user or a plugin like Convention Plugin) and then: results are used with no namespace and in same time, its upper package have no or wildcard namespace and similar to results, same possibility when using url tag which doesn't have value and action set and in same time, its upper package have no or wildcard namespace.
- Effort: intermediate
CVE-2019-0604 SharePoint
Detects the exploitation of the SharePoint vulnerability (CVE-2019-0604).
- Effort: advanced
CVE-2020-0688 Microsoft Exchange Server Exploit
Detects the exploitation of CVE-2020-0688. The POC exploit a .NET serialization vulnerability in the Exchange Control Panel (ECP) web page. The vulnerability is due to Microsoft Exchange Server not randomizing the keys on a per-installation basis resulting in them using the same validationKey and decryptionKey values. With knowledge of these, values an attacker can craft a special viewstate to use an OS command to be executed by NT_AUTHORITY\SYSTEM using .NET deserialization. To exploit this vulnerability, an attacker needs to leverage the credentials of an account it had already compromised to authenticate to OWA.
- Effort: elementary
CVE-2020-1147 SharePoint
Detection of SharePoint vulnerability CVE-2020-1147.
- Effort: advanced
CVE-2020-14882 Oracle WebLogic Server
Detects the exploitation of the Oracle WebLogic Server vulnerability (CVE-2020-16952).
- Effort: advanced
CVE-2020-17530 Apache Struts RCE
Detects the exploitation of the Apache Struts RCE vulnerability (CVE-2020-17530).
- Effort: intermediate
CVE-2021-20021 SonicWall Unauthenticated Administrator Access
Detects the exploitation of SonicWall Unauthenticated Admin Access.
- Effort: advanced
CVE-2021-20023 SonicWall Arbitrary File Read
Detects Arbitrary File Read, which can be used with other vulnerabilities as a mean to obtain outputs generated by attackers, or sensitive data.
- Effort: advanced
CVE-2021-21972 VMware vCenter
The vSphere Client (HTML5) contains a remote code execution vulnerability in a vCenter Server plugin. A malicious actor with network access to port 443 may exploit this issue to execute commands with unrestricted privileges on the underlying operating system that hosts vCenter Server. This affects VMware vCenter Server (7.x before 7.0 U1c, 6.7 before 6.7 U3l and 6.5 before 6.5 U3n) and VMware Cloud Foundation (4.x before 4.2 and 3.x before 3.10.1.2). POST request on the following PATH "/ui/vropspluginui/rest/services/uploadova". If in response body (500) the words it has "uploadFile", that means the vCenter is available to accept files via POST without any restrictions.
- Effort: intermediate
CVE-2021-21985 VMware vCenter
The VMware vSphere Client (HTML5) contains a remote code execution vulnerability due to lack of input validation in the Virtual SAN Health Check plug-in which is enabled by default in vCenter Server. A malicious actor with network access to port 443 may exploit this issue to execute commands with unrestricted privileges on the underlying operating system that hosts vCenter Server. This affects VMware vCenter Server (7.0 before 7.0 U2b, 6.7 before 6.7 U3n and 6.5 before 6.5 U3p) and VMware Cloud Foundation (4.x before 4.2.1 and 3.x before 3.10.2.1).
- Effort: advanced
CVE-2021-22123 Fortinet FortiWeb OS Command Injection
Detects Fortinet FortiWeb OS Command Injection (August 2021) vulnerability exploitation attempt. A remote, authenticated attacker can execute arbitrary commands on the system hosting a vulnerable FortiWeb WAF by sending a POST request with the command in the name field. At the time of writing this rule, it would appear that the request would respond in code 500 for a successful exploitation attempt.
- Effort: advanced
CVE-2021-22893 Pulse Connect Secure RCE Vulnerability
Detects potential exploitation of the authentication by-pass vulnerability that can allow an unauthenticated user to perform remote arbitrary file execution on the Pulse Connect Secure gateway. It is highly recommended to apply the Pulse Secure mitigations and seach for indicators of compromise on affected servers if you are in doubt over the integrity of your Pulse Connect Secure product.
- Effort: intermediate
CVE-2021-26855 Exchange SSRF
Detects the exploitation of ProyxLogon vulerability on Exchange servers.
- Effort: advanced
Certify Or Certipy
Detects the use of certify and certipy which are two different tools used to enumerate and abuse Active Directory Certificate Services.
- Effort: advanced
Cobalt Strike DNS Beaconing
Detects suspicious DNS queries known from Cobalt Strike beacons. The threshold is more than 50 suspicious DNS requests to avoid false positives.
- Effort: advanced
Cobalt Strike Default Beacons Names
Detects the default names of Cobalt Strike beacons / payloads.
- Effort: intermediate
Computer Account Deleted
Detects computer account deletion.
- Effort: master
Correlation Fortigate Multi Alert From One Internal Ip
This rule detect an internal asset that targets a destination IP address with several threat
- Effort: master
Correlation Fortigate Multi Dest From One Internal Ip
This rule detect an internal asset that targets several destination IP address with the same threat
- Effort: master
Correlation Potential DNS Tunnel
Detects domain name which is longer than 62 characters and requested at least 50 times in a 10 minutes range time. Long domain names are distinctive of DNS tunnels.
- Effort: advanced
Covenant Default HTTP Beaconing
Detects potential Covenant communications through the user-agent and specific urls
- Effort: intermediate
Credential Dump Tools Related Files
Detects processes or file names related to credential dumping tools and the dropped files they generate by default.
- Effort: advanced
Cryptomining
Detection of domain names potentially related to cryptomining activities.
- Effort: master
DHCP Server Error Failed Loading the CallOut DLL
This rule detects a DHCP server error in which a specified Callout DLL (in registry) could not be loaded.
- Effort: intermediate
DHCP Server Loaded the CallOut DLL
This rule detects a DHCP server in which a specified Callout DLL (in registry) was loaded. This would indicate a succesful attack against DHCP service allowing to disrupt the service or alter the integrity of the responses.
- Effort: intermediate
DNS Server Error Failed Loading The ServerLevelPluginDLL
This rule detects a DNS server error in which a specified plugin DLL (in registry) could not be loaded. This requires the dedicated Windows event provider Microsoft-Windows-DNS-Server-Service.
- Effort: master
Detect requests to Konni C2 servers
This rule detects requests to Konni C2 servers. These patterns come from an analysis done in 2022, September.
- Effort: elementary
Discord Suspicious Download
Discord is a messaging application. It allows users to create their own communities to share messages and attachments. Those attachments have little to no overview and can be downloaded by almost anyone, which has been abused by attackers to host malicious payloads.
- Effort: advanced
Domain Trust Created Or Removed
A trust was created or removed to a domain. An attacker could perform that in order to do lateral movement easily between domains or shutdown the ability of two domains to communicate.
- Effort: advanced
Dynamic DNS Contacted
Detect communication with dynamic dns domain. This kind of domain is often used by attackers. This rule can trigger false positive in non-controlled environment because dynamic dns is not always malicious.
- Effort: master
EvilProxy Phishing Domain
Detects subdomains potentially generated by the EvilProxy adversary-in-the-middle phishing platform. Inspect the other subdomains of the domain to identify the landing page, and determine if the user submitted credentials. This rule has a small percentage of false positives on legitimate domains.
- Effort: intermediate
Exfiltration Domain
Detects traffic toward a domain flagged as a possible exfiltration vector.
- Effort: master
FoggyWeb HTTP Default GET/POST Requests
Detects GET or POST request pattern observed within the first FoggyWeb campaign detected by Microsoft.
- Effort: advanced
Fortigate IPS Critical Alert
Fortigate intrusion detection alert with critical severity.
- Effort: master
Fortigate IPS High Severity Alert
Fortigate intrusion detection alert with high severity.
- Effort: master
HTA Infection Chains
Detect the creation of a ZIP file and an HTA file as it is often used in infection chains. Furthermore it also detects the use of suspicious processes launched by explorer.exe combined with the creation of an HTA file, since it is also often used in infection chains (LNK - HTA for instance).
- Effort: advanced
HTML Smuggling Suspicious Usage
Based on several samples from different botnets, this rule aims at detecting HTML infection chain by looking for HTML created files followed by suspicious files being executed.
- Effort: advanced
HackTools Suspicious Names
Quick-win rule to detect the default process names or file names of several HackTools.
- Effort: advanced
ISO LNK Infection Chain
Detection of an ISO (or any other similar archive file) downloaded file, followed by a child-process of explorer, which is characteristic of an infection using an ISO containing an LNK file. For events with host.name.
- Effort: master
Internet Scanner
Detects known scanner IP addresses. Alert is only raised when the scan hits an opened port, on TCP or UDP. This could be a very noisy rule, so be careful to check your detection perimeter before activation.
- Effort: master
Internet Scanner Target
Detects known scanner IP addresses. Alert is only raised when the scan hits an opened port, on TCP or UDP and group by target address. This could be a very noisy rule, so be careful to check your detection perimeter before activation.
- Effort: master
Koadic MSHTML Command
Detects Koadic payload using MSHTML module
- Effort: intermediate
Login Brute-Force Successful On SentinelOne EDR Management Console
A user has attempted to login several times (brute-force) on the SentinelOne EDR Management Console and succeeded to login.
- Effort: master
Microsoft Defender Antivirus History Deleted
Windows Defender history has been deleted. Could be an attempt by an attacker to remove its traces.
- Effort: master
Microsoft Defender Antivirus Tampering Detected
Detection of Windows Defender Tampering, from definitions' deletion to deactivation of parts or all of Defender.
- Effort: advanced
Microsoft Defender Antivirus Threat Detected
Detection of a windows defender alert indicating the presence of potential malware
- Effort: advanced
Nimbo-C2 User Agent
Nimbo-C2 Uses an unusual User-Agent format in its implants.
- Effort: intermediate
Password Change On Directory Service Restore Mode (DSRM) Account
The Directory Service Restore Mode (DSRM) account is a local administrator account on Domain Controllers. Attackers may change the password to gain persistence.
- Effort: intermediate
PasswordDump SecurityXploded Tool
Detects the execution of the PasswordDump SecurityXploded Tool
- Effort: elementary
Possible Malicious File Double Extension
Detects request to potential malicious file with double extension
- Effort: elementary
Possible Replay Attack
This event can be a sign of Kerberos replay attack or, among other things, network device configuration or routing problems.
- Effort: master
Potential Bazar Loader User-Agents
Detects potential Bazar loader communications through the user-agent
- Effort: elementary
Potential DNS Tunnel
Detects domain name which is longer than 62 characters. Long domain names are distinctive of DNS tunnels.
- Effort: advanced
Potential Lemon Duck User-Agent
Detects LemonDuck user agent. The format used two sets of alphabetical characters separated by dashes, for example "User-Agent: Lemon-Duck-[A-Z]-[A-Z]".
- Effort: elementary
Potential LokiBot User-Agent
Detects potential LokiBot communications through the user-agent
- Effort: intermediate
Potential RDP Connection To Non-Domain Host
Detects logons using NTLM to hosts that are potentially not part of the domain using RDP (TermSrv). Event ID 8001 corresponds to outgoing NTLM authentication traffic and TermSrv stands for RDP Terminal Services Server. Check if the contacted host is legitimate. To use this detection rule, enable logging of outbound NTLM authentications on all domain controllers, using the following Group Policy (GPO) - Computer Configuration > Policies > Windows Settings > Security Settings > Local Policies > Security Options > Network security: Restrict NTLM: Outgoing NTLM traffic to remote servers -> Define this policy setting: Audit all.
- Effort: master
Privilege Escalation Awesome Scripts (PEAS)
Detect PEAS privileges escalation scripts and binaries
- Effort: elementary
ProxyShell Microsoft Exchange Suspicious Paths
Detects suspicious calls to Microsoft Exchange resources, in locations related to webshells observed in campaigns using this vulnerability.
- Effort: elementary
RTLO Character
Detects RTLO (Right-To-Left character) in file and process names.
- Effort: elementary
Raccoon Stealer 2.0 Legitimate Third-Party DLL Download URL
Detects Raccoon Stealer 2.0 malware downloading legitimate third-party DLLs from its C2 server. These legitimate DLLs are used by the information stealer to collect data on the compromised hosts.
- Effort: elementary
Remote Access Tool Domain
Detects traffic toward a domain flagged as a Remote Administration Tool (RAT).
- Effort: master
Remote Monitoring and Management Software - AnyDesk
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool AnyDesk.
- Effort: master
Remote Monitoring and Management Software - Atera
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool Atera.
- Effort: master
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
Sekoia.io EICAR Detection
Detects observables in Sekoia.io CTI tagged as EICAR, which are fake samples meant to test detection.
- Effort: master
Sliver DNS Beaconing
Detects suspicious DNS queries known from Sliver beaconing
- Effort: intermediate
Suspicious Download Links From Legitimate Services
Detects users clicking on Google docs links to download suspicious files. This technique was used a lot by Bazar Loader in the past.
- Effort: intermediate
Suspicious File Name
Detects suspicious file name possibly linked to malicious tool.
- Effort: advanced
Suspicious PROCEXP152.sys File Created In Tmp
Detects the creation of the PROCEXP152.sys file in the application-data local temporary folder. This driver is used by Sysinternals Process Explorer but also by KDU (https://github.com/hfiref0x/KDU) or Ghost-In-The-Logs (https://github.com/bats3c/Ghost-In-The-Logs), which uses KDU. Note - Clever attackers may easily bypass this detection by just renaming the driver filename. Therefore just Medium-level and don't rely on it.
- Effort: advanced
Suspicious TOR Gateway
Detects suspicious TOR gateways. Gateways are often used by the victim to pay and decrypt the encrypted files without installing TOR. Tor intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: advanced
Suspicious URI Used In A Lazarus Campaign
Detects suspicious requests to a specific URI, usually on an .asp page. The website is often compromised.
- Effort: intermediate
TOR Usage
Detects TOR usage, based on the IP address and the destination port (filtered on NTP). TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
TOR Usage Generic Rule
Detects TOR usage globally, whether the IP is a destination or source. TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
Telegram Bot API Request
Detects suspicious DNS queries to api.telegram.org used by Telegram Bots of any kind
- Effort: advanced
TrevorC2 HTTP Communication
Detects TrevorC2 HTTP communication based on the HTTP request URI and the user-agent.
- Effort: elementary
User Account Created
Detects user creation on windows servers, which shouldn't happen in an Active Directory environment. Apply this on your windows server logs and not on your DC logs. One default account defaultuser0 is excluded as only used during Windows set-up. This detection use Security Event ID 4720.
- Effort: master
User Account Deleted
Detects local user deletion
- Effort: master
WCE wceaux.dll Creation
Detects wceaux.dll creation while Windows Credentials Editor (WCE) is executed.
- Effort: intermediate
ZIP LNK Infection Chain
Detection of an ZIP download followed by a child-process of explorer, followed by multiple Windows processes.This is widely used as an infection chain mechanism.
- Effort: advanced
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Network device logs |
FortiGate can record traffic logs flowing through their firewall. |
Network intrusion detection system |
Security logs provided by FortiGate include intrusion prevention related records. |
Web application firewall logs |
FortiWeb appliances and virtual appliances record WAF information. |
Web logs |
WAF information produces by FortiWeb units can record permited URL access. |
DNS records |
Both DNS queries and responses handled by the FortiGate domain name servers can be recorded. |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "CEF:0|Fortinet|Fortigate|v6.2.9|32102|event:system|7|deviceExternalId=FGVM2V0000171868 FortinetFortiGatelogid=0100032102 cat=event:system FortinetFortiGatesubtype=system FortinetFortiGatelevel=alert FortinetFortiGatevd=root FortinetFortiGateeventtime=1637681708541881380 FortinetFortiGatetz=+0100 FortinetFortiGatelogdesc=Configuration changed duser= sproc=console msg=Configuration is changed in the admin session",
"event": {
"category": "event",
"code": "0100032102",
"dataset": "event:system",
"reason": "Configuration is changed in the admin session",
"timezone": "+0100"
},
"@timestamp": "2021-11-23T15:35:08.541882Z",
"action": {
"outcome_reason": "Configuration is changed in the admin session",
"type": "system"
},
"fortinet": {
"fortigate": {
"virtual_domain": "root"
}
},
"log": {
"description": "Configuration changed",
"level": "alert"
},
"observer": {
"serial_number": "FGVM2V0000171868",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.2.9"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.3|24576|utm:dlp dlp block|4|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0954024576 cat=utm:dlp FTNTFGTsubtype=dlp FTNTFGTeventtype=dlp FTNTFGTlevel=warning FTNTFGTvd=vdom1 FTNTFGTeventtime=1545949776 FTNTFGTfilteridx=1 FTNTFGTdlpextra=test-dlp3 FTNTFGTfiltertype=file-type FTNTFGTfiltercat=file FTNTFGTseverity=medium FTNTFGTpolicyid=1 externalId=12680 FTNTFGTepoch=418303178 FTNTFGTeventid=0 duser=bob src=10.1.100.11 spt=33638 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined dst=example.com dpt=80 deviceOutboundInterface=port11 FTNTFGTdstintfrole=undefined proto=6 app=HTTP FTNTFGTfiletype=gif deviceDirection=0 act=block dhost=example.com request=/dlp/flower.gif requestClientApplication=curl/7.47.0 fname=flower.gif fsize=1209 FTNTFGTprofile=test-dlp",
"event": {
"action": "block",
"category": "utm",
"code": "0954024576",
"dataset": "utm:dlp",
"outcome": "success"
},
"@timestamp": "2018-12-27T22:29:36Z",
"action": {
"name": "block",
"outcome": "success",
"target": "network-traffic",
"type": "dlp"
},
"destination": {
"address": "example.com",
"domain": "example.com",
"port": 80,
"user": {
"name": "bob"
}
},
"file": {
"name": "flower.gif",
"size": 1209
},
"fortinet": {
"fortigate": {
"event": {
"severity": "medium"
},
"policyid": "1",
"security_profile": "test-dlp",
"virtual_domain": "vdom1"
}
},
"log": {
"level": "warning"
},
"network": {
"application": "HTTP",
"direction": "inbound",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port11"
}
},
"ingress": {
"interface": {
"name": "port12"
}
},
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"10.1.100.11"
],
"user": [
"bob"
]
},
"source": {
"address": "10.1.100.11",
"ip": "10.1.100.11",
"port": 33638
},
"url": {
"original": "/dlp/flower.gif",
"path": "/dlp/flower.gif"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "curl",
"original": "curl/7.47.0",
"os": {
"name": "Other"
},
"version": "7.47.0"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.3|54802|dns:dns-response pass|3|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=1501054802 cat=dns:dns-response FTNTFGTsubtype=dns-response FTNTFGTlevel=notice FTNTFGTvd=vdom1 FTNTFGTeventtime=1545950726 FTNTFGTpolicyid=1 externalId=13355 duser=bob src=10.1.100.11 spt=54621 deviceInboundInterface=port12 FTNTFGTsrcintfrole=lan dst=172.16.200.55 dpt=53 deviceOutboundInterface=port11 FTNTFGTdstintfrole=wan proto=17 FTNTFGTprofile=default FTNTFGTsrcmac=a2:e9:00:ec:40:01 FTNTFGTxid=5137 FTNTFGTqname=example.org FTNTFGTqtype=A FTNTFGTqtypeval=1 FTNTFGTqclass=IN FTNTFGTipaddr=104.80.89.26, 104.80.89.24 msg=Domain is monitored act=pass FTNTFGTcat=52 FTNTFGTcatdesc=Information Technology",
"event": {
"action": "pass",
"category": "dns",
"code": "1501054802",
"dataset": "dns:dns-response",
"outcome": "success",
"reason": "Domain is monitored"
},
"@timestamp": "2018-12-27T22:45:26Z",
"action": {
"name": "pass",
"outcome": "success",
"outcome_reason": "Domain is monitored",
"target": "network-traffic",
"type": "dns-response"
},
"destination": {
"address": "172.16.200.55",
"ip": "172.16.200.55",
"port": 53,
"user": {
"name": "bob"
}
},
"dns": {
"question": {
"class": "IN",
"name": "example.org",
"registered_domain": "example.org",
"top_level_domain": "org",
"type": "A"
},
"rrname": "example.org",
"rrtype": "A"
},
"fortinet": {
"fortigate": {
"policyid": "1",
"security_profile": "default",
"virtual_domain": "vdom1"
}
},
"log": {
"level": "notice"
},
"network": {
"transport": "udp"
},
"observer": {
"egress": {
"interface": {
"alias": "wan",
"name": "port11"
}
},
"ingress": {
"interface": {
"alias": "lan",
"name": "port12"
}
},
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"hosts": [
"example.org"
],
"ip": [
"10.1.100.11",
"172.16.200.55"
],
"user": [
"bob"
]
},
"rule": {
"category": "Information Technology"
},
"source": {
"address": "10.1.100.11",
"ip": "10.1.100.11",
"mac": "a2:e9:00:ec:40:01",
"port": 54621
}
}
{
"message": "time=15:51:59 devname=\"my-device\" devid=\"1111111111111111\" eventtime=1668001919663486001 tz=\"+0100\" logid=\"1500054000\" type=\"utm\" subtype=\"dns\" eventtype=\"dns-query\" level=\"information\" vd=\"root\" policyid=1685 poluuid=\"4470d4c5-7e12-4a8f-a369-08eff4a43b5b\" policytype=\"policy\" sessionid=933308058 srcip=1.2.3.4 srcport=35305 srccountry=\"Reserved\" srcintf=\"INTF-1\" srcintfrole=\"undefined\" dstip=192.0.2.1 dstport=53 dstcountry=\"Reserved\" dstintf=\"INTF-2\" dstintfrole=\"lan\" proto=17 profile=\"DNS Filtering Normal\" xid=42240 qtype=\"NS\" qtypeval=2 qclass=\"IN\"",
"event": {
"category": "utm",
"code": "1500054000",
"timezone": "+0100"
},
"@timestamp": "2022-11-09T13:51:59.663486Z",
"action": {
"target": "network-traffic",
"type": "dns"
},
"destination": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"port": 53
},
"dns": {
"question": {
"class": "IN",
"type": "NS"
},
"rrtype": "NS"
},
"fortinet": {
"fortigate": {
"event": {
"type": "utm"
},
"policyid": "1685",
"policytype": "policy",
"poluuid": "4470d4c5-7e12-4a8f-a369-08eff4a43b5b",
"security_profile": "DNS Filtering Normal",
"sessionid": "933308058",
"virtual_domain": "root"
}
},
"log": {
"hostname": "my-device",
"level": "information"
},
"network": {
"transport": "udp"
},
"observer": {
"egress": {
"interface": {
"alias": "lan",
"name": "INTF-2"
}
},
"hostname": "my-device",
"ingress": {
"interface": {
"name": "INTF-1"
}
},
"serial_number": "1111111111111111"
},
"related": {
"hosts": [
"my-device"
],
"ip": [
"1.2.3.4",
"192.0.2.1"
]
},
"rule": {
"ruleset": "policy"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 35305
}
}
{
"message": "time=15:58:39 devname=\"dev-name\" devid=\"1111111111111111\" eventtime=1668002319383195535 tz=\"+0100\" logid=\"1500054000\" type=\"utm\" subtype=\"dns\" eventtype=\"dns-query\" level=\"information\" vd=\"root\" policyid=770 poluuid=\"f2aef0f2-a721-49cf-9dd3-b27f7f5b90bc\" policytype=\"policy\" sessionid=933538554 user=\"user1\" srcip=1.2.3.4 srcport=45362 srccountry=\"Reserved\" srcintf=\"intf-1\" srcintfrole=\"undefined\" dstip=192.0.2.1 dstport=53 dstcountry=\"Reserved\" dstintf=\"intf-2\" dstintfrole=\"undefined\" proto=17 profile=\"DNS Filtering Normal\" xid=32649 qname=\"[example.com]\" qtype=\"A\" qtypeval=1 qclass=\"IN\"",
"event": {
"category": "utm",
"code": "1500054000",
"timezone": "+0100"
},
"@timestamp": "2022-11-09T13:58:39.383196Z",
"action": {
"target": "network-traffic",
"type": "dns"
},
"destination": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"port": 53
},
"dns": {
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "A"
},
"rrname": "example.com",
"rrtype": "A"
},
"fortinet": {
"fortigate": {
"event": {
"type": "utm"
},
"policyid": "770",
"policytype": "policy",
"poluuid": "f2aef0f2-a721-49cf-9dd3-b27f7f5b90bc",
"security_profile": "DNS Filtering Normal",
"sessionid": "933538554",
"virtual_domain": "root"
}
},
"log": {
"hostname": "dev-name",
"level": "information"
},
"network": {
"transport": "udp"
},
"observer": {
"egress": {
"interface": {
"name": "intf-2"
}
},
"hostname": "dev-name",
"ingress": {
"interface": {
"name": "intf-1"
}
},
"serial_number": "1111111111111111"
},
"related": {
"hosts": [
"dev-name",
"example.com"
],
"ip": [
"1.2.3.4",
"192.0.2.1"
],
"user": [
"user1"
]
},
"rule": {
"ruleset": "policy"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 45362,
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.3|16384|utm:ips signature reset|7|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0419016384 cat=utm:ips FTNTFGTsubtype=ips FTNTFGTeventtype=signature FTNTFGTlevel=alert FTNTFGTvd=vdom1 FTNTFGTeventtime=1545938887 FTNTFGTseverity=info src=example.com FTNTFGTsrccountry=Reserved dst=10.1.100.11 deviceInboundInterface=port11 FTNTFGTsrcintfrole=undefined deviceOutboundInterface=port12 FTNTFGTdstintfrole=undefined externalId=901 act=reset proto=6 app=HTTP FTNTFGTpolicyid=1 FTNTFGTattack=Eicar.Virus.Test.File spt=80 dpt=44362 dhost=example.com request=/virus/eicar.com deviceDirection=0 FTNTFGTattackid=29844 FTNTFGTprofile=test-ips FTNTFGTref=http://www.fortinet.com/ids/VID29844 duser=bob FTNTFGTincidentserialno=877326946 msg=file_transfer: Eicar.Virus.Test.File,",
"event": {
"action": "reset",
"category": "utm",
"code": "0419016384",
"dataset": "utm:ips",
"outcome": "success",
"reason": "file_transfer: Eicar.Virus.Test.File,"
},
"@timestamp": "2018-12-27T19:28:07Z",
"action": {
"name": "reset",
"outcome": "success",
"outcome_reason": "file_transfer: Eicar.Virus.Test.File,",
"target": "network-traffic",
"type": "ips"
},
"destination": {
"address": "10.1.100.11",
"domain": "example.com",
"ip": "10.1.100.11",
"port": 44362,
"user": {
"name": "bob"
}
},
"fortinet": {
"fortigate": {
"attack": {
"id": "29844",
"name": "Eicar.Virus.Test.File"
},
"event": {
"severity": "info"
},
"policyid": "1",
"security_profile": "test-ips",
"virtual_domain": "vdom1"
}
},
"log": {
"level": "alert"
},
"network": {
"application": "HTTP",
"direction": "inbound",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port12"
}
},
"ingress": {
"interface": {
"name": "port11"
}
},
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"10.1.100.11"
],
"user": [
"bob"
]
},
"source": {
"port": 80
},
"url": {
"original": "/virus/eicar.com",
"path": "/virus/eicar.com"
}
}
{
"message": "time=17:24:16 devname=\"abc\" devid=\"1\" logid=\"0101037130\" type=\"event\" subtype=\"vpn\" level=\"error\" vd=\"root\" eventtime=1580142256 logdesc=\"Progress IPsec phase 2\" msg=\"progress IPsec phase 2\" action=\"negotiate\" remip=1.1.1.1 locip=192.0.2.1 remport=500 locport=500 outintf=\"N/A\" cookies=\"07f928d94dd975ea/89b1d990f54f0b82\" user=\"N/A\" group=\"N/A\" xauthuser=\"N/A\" xauthgroup=\"N/A\" assignip=N/A vpntunnel=\"VPN-FOOBAR\" status=\"failure\" init=\"local\" exch=\"CREATE_CHILD\" dir=\"inbound\" role=\"initiator\" result=\"ERROR\" version=\"IKEv2\"",
"event": {
"action": "negotiate",
"category": "event",
"code": "0101037130",
"dataset": "event:vpn",
"outcome": "failure",
"reason": "progress IPsec phase 2"
},
"@timestamp": "2020-01-27T16:24:16Z",
"action": {
"name": "negotiate",
"outcome": "failure",
"outcome_reason": "progress IPsec phase 2",
"target": "network-traffic",
"type": "vpn"
},
"destination": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"port": 500
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"tunnel": {
"name": "VPN-FOOBAR",
"version": "IKEv2"
},
"virtual_domain": "root"
}
},
"log": {
"description": "Progress IPsec phase 2",
"hostname": "abc",
"level": "error"
},
"observer": {
"hostname": "abc",
"serial_number": "1"
},
"related": {
"hosts": [
"abc"
],
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"port": 500
}
}
{
"message": "time=16:48:00 devname=\"abc\" devid=\"1\" logid=\"0100032003\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"root\" eventtime=1619621280 logdesc=\"Admin logout successful\" sn=\"1619620402\" user=\"test\" ui=\"jsconsole\" method=\"jsconsole\" srcip=1.1.1.1 dstip=192.0.2.1 action=\"logout\" status=\"success\" duration=878 reason=\"exit\" msg=\"Administrator test logged out from jsconsole\"",
"event": {
"action": "logout",
"category": "event",
"code": "0100032003",
"dataset": "event:system",
"duration": 878000000000,
"outcome": "success",
"provider": "jsconsole",
"reason": "exit"
},
"@timestamp": "2021-04-28T14:48:00Z",
"action": {
"name": "logout",
"outcome": "success",
"outcome_reason": "Administrator test logged out from jsconsole",
"target": "network-traffic",
"type": "system"
},
"destination": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"method": "jsconsole",
"sn": "1619620402",
"virtual_domain": "root"
}
},
"log": {
"description": "Admin logout successful",
"hostname": "abc",
"level": "information"
},
"observer": {
"hostname": "abc",
"serial_number": "1"
},
"related": {
"hosts": [
"abc"
],
"ip": [
"1.1.1.1",
"192.0.2.1"
],
"user": [
"test"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"user": {
"name": "test"
}
},
"user": {
"name": "test"
}
}
{
"message": "time=16:23:50 devname=\"abc\" devid=\"1\" logid=\"0100032011\" type=\"event\" subtype=\"system\" level=\"notice\" vd=\"PRX1-AA\" eventtime=1619619830 logdesc=\"Disk log rolled\" action=\"roll-log\" reason=\"file-size\" log=\"tlog\" msg=\"Disk log has rolled.\"",
"event": {
"action": "roll-log",
"category": "event",
"code": "0100032011",
"dataset": "event:system",
"outcome": "success",
"reason": "file-size"
},
"@timestamp": "2021-04-28T14:23:50Z",
"action": {
"name": "roll-log",
"outcome": "success",
"outcome_reason": "Disk log has rolled.",
"type": "system"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"virtual_domain": "PRX1-AA"
}
},
"log": {
"description": "Disk log rolled",
"hostname": "abc",
"level": "notice"
},
"observer": {
"hostname": "abc",
"serial_number": "1"
},
"related": {
"hosts": [
"abc"
]
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.3|61002|utm:ssh ssh-command passthrough|3|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=1600061002 cat=utm:ssh FTNTFGTsubtype=ssh FTNTFGTeventtype=ssh-command FTNTFGTlevel=notice FTNTFGTvd=vdom1 FTNTFGTeventtime=1545950175 FTNTFGTpolicyid=1 externalId=12921 duser=bob FTNTFGTprofile=test-ssh src=10.1.100.11 spt=56698 dst=172.16.200.55 dpt=22 deviceInboundInterface=port12 FTNTFGTsrcintfrole=lan deviceOutboundInterface=port11 FTNTFGTdstintfrole=wan proto=6 act=passthrough FTNTFGTlogin=root FTNTFGTcommand=ls FTNTFGTseverity=low",
"event": {
"action": "passthrough",
"category": "utm",
"code": "1600061002",
"dataset": "utm:ssh",
"outcome": "success"
},
"@timestamp": "2018-12-27T22:36:15Z",
"action": {
"name": "passthrough",
"outcome": "success",
"target": "network-traffic",
"type": "ssh"
},
"destination": {
"address": "172.16.200.55",
"ip": "172.16.200.55",
"port": 22,
"user": {
"name": "bob"
}
},
"fortinet": {
"fortigate": {
"event": {
"severity": "low"
},
"policyid": "1",
"security_profile": "test-ssh",
"virtual_domain": "vdom1"
}
},
"log": {
"level": "notice"
},
"network": {
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "wan",
"name": "port11"
}
},
"ingress": {
"interface": {
"alias": "lan",
"name": "port12"
}
},
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"ip": [
"10.1.100.11",
"172.16.200.55"
],
"user": [
"bob"
]
},
"source": {
"address": "10.1.100.11",
"ip": "10.1.100.11",
"port": 56698
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.3|44032|utm:voip voip permit start|2|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0814044032 cat=utm:voip FTNTFGTsubtype=voip FTNTFGTeventtype=voip FTNTFGTlevel=information FTNTFGTvd=vdom1 FTNTFGTeventtime=1545958028 externalId=18975 FTNTFGTepoch=0 FTNTFGTevent_id=6857 src=10.1.100.11 spt=5060 dst=172.16.200.55 dpt=5060 proto=17 deviceInboundInterface=port12 deviceOutboundInterface=port11 FTNTFGTpolicy_id=1 FTNTFGTprofile=default FTNTFGTvoip_proto=sip FTNTFGTkind=call act=permit outcome=start FTNTFGTduration=0 FTNTFGTdir=session_origin FTNTFGTcall_id=3444-13134@127.0.0.1 suser=user1 duser=user1",
"event": {
"action": "permit",
"category": "utm",
"code": "0814044032",
"dataset": "utm:voip",
"outcome": "start"
},
"@timestamp": "2018-12-28T00:47:08Z",
"action": {
"name": "permit",
"outcome": "start",
"target": "network-traffic",
"type": "voip"
},
"destination": {
"address": "172.16.200.55",
"ip": "172.16.200.55",
"port": 5060,
"user": {
"name": "user1"
}
},
"fortinet": {
"fortigate": {
"security_profile": "default",
"virtual_domain": "vdom1"
}
},
"log": {
"level": "information"
},
"network": {
"transport": "udp"
},
"observer": {
"egress": {
"interface": {
"name": "port11"
}
},
"ingress": {
"interface": {
"name": "port12"
}
},
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"ip": [
"10.1.100.11",
"172.16.200.55"
],
"user": [
"user1"
]
},
"source": {
"address": "10.1.100.11",
"ip": "10.1.100.11",
"port": 5060,
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "time=15:29:39 devname=\"abc\" devid=\"1\" logid=\"0105048039\" type=\"event\" subtype=\"wad\" level=\"error\" vd=\"PRX1-AA\" eventtime=1619616579 logdesc=\"SSL fatal alert sent\" session_id=473f963d policyid=0 srcip=192.0.2.1 srcport=47782 dstip=1.1.1.1 dstport=8002 action=\"send\" alert=\"2\" desc=\"illegal parameter\" msg=\"SSL Alert sent\"",
"event": {
"action": "send",
"category": "event",
"code": "0105048039",
"dataset": "utm:wad",
"outcome": "success",
"reason": "SSL Alert sent",
"type": "illegal parameter"
},
"@timestamp": "2021-04-28T13:29:39Z",
"action": {
"name": "send",
"outcome": "success",
"outcome_reason": "SSL Alert sent",
"target": "network-traffic",
"type": "wad"
},
"destination": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"port": 8002
},
"fortinet": {
"fortigate": {
"event": {
"desc": "illegal parameter",
"type": "event"
},
"policyid": "0",
"virtual_domain": "PRX1-AA"
}
},
"log": {
"description": "SSL fatal alert sent",
"hostname": "abc",
"level": "error"
},
"observer": {
"hostname": "abc",
"serial_number": "1"
},
"related": {
"hosts": [
"abc"
],
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"port": 47782
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.3|30258|utm:waf waf-http-constraint passthrough|4|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=1203030258 cat=utm:waf FTNTFGTsubtype=waf FTNTFGTeventtype=waf-http-constraint FTNTFGTlevel=warning FTNTFGTvd=vdom1 FTNTFGTeventtime=1545951320 FTNTFGTpolicyid=1 externalId=13614 duser=bob FTNTFGTprofile=waf_test src=10.1.100.11 spt=57304 dst=example.com dpt=80 deviceInboundInterface=port12 FTNTFGTsrcintfrole=lan deviceOutboundInterface=port11 FTNTFGTdstintfrole=wan proto=6 app=HTTP request=http://example.com/index.html?https://example.com/ FTNTFGTseverity=medium act=passthrough deviceDirection=0 requestClientApplication=curl/7.47.0 FTNTFGTconstraint=url-param-num FTNTFGTrawdata=Method\\=GET|User-Agent\\=curl/7.47.0",
"event": {
"action": "passthrough",
"category": "utm",
"code": "1203030258",
"dataset": "utm:waf",
"outcome": "success"
},
"@timestamp": "2018-12-27T22:55:20Z",
"action": {
"name": "passthrough",
"outcome": "success",
"target": "network-traffic",
"type": "waf"
},
"destination": {
"address": "example.com",
"port": 80,
"user": {
"name": "bob"
}
},
"fortinet": {
"fortigate": {
"event": {
"severity": "medium"
},
"policyid": "1",
"security_profile": "waf_test",
"virtual_domain": "vdom1"
}
},
"log": {
"level": "warning"
},
"network": {
"application": "HTTP",
"direction": "inbound",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "wan",
"name": "port11"
}
},
"ingress": {
"interface": {
"alias": "lan",
"name": "port12"
}
},
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"ip": [
"10.1.100.11"
],
"user": [
"bob"
]
},
"source": {
"address": "10.1.100.11",
"ip": "10.1.100.11",
"port": 57304
},
"url": {
"domain": "example.com",
"full": "http://example.com/index.html?https://example.com/",
"original": "http://example.com/index.html?https://example.com/",
"path": "/index.html",
"port": 80,
"query": "https://example.com/",
"registered_domain": "example.com",
"scheme": "http",
"top_level_domain": "com"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "curl",
"original": "curl/7.47.0",
"os": {
"name": "Other"
},
"version": "7.47.0"
}
}
{
"message": "0|Fortinet|Fortigate|v6.0.3|18433|utm:anomaly anomaly clear_session|7|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0720018433 cat=utm:anomaly FTNTFGTsubtype=anomaly FTNTFGTeventtype=anomaly FTNTFGTlevel=alert FTNTFGTvd=vdom1 FTNTFGTeventtime=1545939604 FTNTFGTseverity=critical src=10.1.100.11 FTNTFGTsrccountry=Reserved dst=172.16.200.55 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined externalId=0 act=clear_session proto=1 app=PING cnt=1 FTNTFGTattack=icmp_flood FTNTFGTicmpid=0x3053 FTNTFGTicmptype=0x08 FTNTFGTicmpcode=0x00 FTNTFGTattackid=16777316 FTNTFGTpolicyid=1 FTNTFGTpolicytype=DoS-policy FTNTFGTref=http://www.fortinet.com/ids/VID16777316 msg=anomaly: icmp_flood, 51 > threshold 50 FTNTFGTcrscore=50 FTNTFGTcrlevel=critical",
"event": {
"action": "clear_session",
"category": "utm",
"code": "0720018433",
"dataset": "utm:anomaly",
"outcome": "success",
"reason": "anomaly: icmp_flood, 51 > threshold 50"
},
"@timestamp": "2018-12-27T19:40:04Z",
"action": {
"name": "clear_session",
"outcome": "success",
"outcome_reason": "anomaly: icmp_flood, 51 > threshold 50",
"properties": {
"icmp_code": "0x00",
"icmp_type": "0x08"
},
"target": "network-traffic",
"type": "anomaly"
},
"destination": {
"address": "172.16.200.55",
"ip": "172.16.200.55"
},
"fortinet": {
"fortigate": {
"attack": {
"id": "16777316",
"name": "icmp_flood"
},
"event": {
"severity": "critical"
},
"icmp": {
"request": {
"code": "0x00",
"type": "0x08"
}
},
"policyid": "1",
"policytype": "DoS-policy",
"threat": {
"level": "critical",
"score": 50
},
"virtual_domain": "vdom1"
}
},
"log": {
"level": "alert"
},
"network": {
"application": "PING",
"protocol": "ping",
"transport": "icmp"
},
"observer": {
"ingress": {
"interface": {
"name": "port12"
}
},
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"ip": [
"10.1.100.11",
"172.16.200.55"
]
},
"rule": {
"ruleset": "DoS-policy"
},
"source": {
"address": "10.1.100.11",
"ip": "10.1.100.11"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v5.6.0|18433|anomaly:anomaly clear_ session|7|FTNTFGTlogid=0720018433 cat=anomaly:anomaly FTNTFGTsubtype=anomaly FTNTFGTlevel=alert FTNTFGTvd=vdom1 FTNTFGTseverity=critical src=1.1.1.1 dst=192.0.2.1 deviceInboundInterface=port15 externalId=0 act=clear_session proto=1 app=icmp/146/81 cnt=306 FTNTFGTattack=icmp_flood dpt=20882 FTNTFGTicmptype=0x92 FTNTFGTicmpcode=0x51 FTNTFGTattackid=16777316 FTNTFGTprofile=DoS-policy1 cs2=http://www.fortinet.com/ids/VID16777316 cs2Label=Reference msg=anomaly: icmp_flood, 34 > threshold 25, repeats 306 times FTNTFGTcrscore=50 FTNTFGTcrlevel=critical",
"event": {
"action": "clear_session",
"category": "anomaly",
"code": "0720018433",
"dataset": "utm:anomaly",
"outcome": "success",
"reason": "anomaly: icmp_flood, 34 > threshold 25, repeats 306 times"
},
"action": {
"name": "clear_session",
"outcome": "success",
"outcome_reason": "anomaly: icmp_flood, 34 > threshold 25, repeats 306 times",
"properties": {
"icmp_code": "0x51",
"icmp_type": "0x92"
},
"target": "network-traffic",
"type": "anomaly"
},
"destination": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"port": 20882
},
"fortinet": {
"fortigate": {
"attack": {
"id": "16777316",
"name": "icmp_flood"
},
"event": {
"severity": "critical"
},
"icmp": {
"request": {
"code": "0x51",
"type": "0x92"
}
},
"security_profile": "DoS-policy1",
"threat": {
"level": "critical",
"score": 50
},
"virtual_domain": "vdom1"
}
},
"log": {
"level": "alert"
},
"network": {
"application": "icmp/146/81",
"protocol": "icmp/146/81",
"transport": "icmp"
},
"observer": {
"ingress": {
"interface": {
"name": "port15"
}
},
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v5.6.0"
},
"related": {
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
}
}
{
"message": "date=2016-02-12,time=14:10:42,logid=0720018433,type=anomaly,subtype=anomaly,level=alert,vd=\"vdom1\",severity=critical,srcip=1.1.1.1,dstip=192.0.2.1,srcintf=\"port15\",sessionid=0,action=clear_session,proto=1,service=\"icmp/146/81\",count=306,attack=\"icmp_ flood\",dstport=20882,icmptype=0x92,icmpcode=0x51,attackid=16777316,profile=\"DoS-policy1\",ref=\"http://www.fortinet.com/ids/VID16777316\",msg=\"anomaly: icmp_flood, 34 > threshold 25, repeats 306 times\",crscore=50,crlevel=critical",
"event": {
"action": "clear_session",
"category": "anomaly",
"code": "0720018433",
"dataset": "utm:anomaly",
"outcome": "success",
"reason": "anomaly: icmp_flood, 34 > threshold 25, repeats 306 times"
},
"action": {
"name": "clear_session",
"outcome": "success",
"outcome_reason": "anomaly: icmp_flood, 34 > threshold 25, repeats 306 times",
"properties": {
"icmp_code": "0x51",
"icmp_type": "0x92"
},
"target": "network-traffic",
"type": "anomaly"
},
"destination": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"port": 20882
},
"fortinet": {
"fortigate": {
"attack": {
"id": "16777316",
"name": "icmp_ flood"
},
"event": {
"severity": "critical",
"type": "anomaly"
},
"icmp": {
"request": {
"code": "0x51",
"type": "0x92"
}
},
"security_profile": "DoS-policy1",
"sessionid": "0",
"threat": {
"level": "critical",
"score": 50
},
"virtual_domain": "vdom1"
}
},
"log": {
"level": "alert"
},
"network": {
"protocol": "icmp/146/81",
"transport": "icmp"
},
"observer": {
"ingress": {
"interface": {
"name": "port15"
}
}
},
"related": {
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
}
}
{
"message": "date=2016-02-12 time=14:10:42 logid=0720018433 type=anomaly subtype=anomaly level=alert vd=\"vdom1\" severity=critical srcip=1.1.1.1 dstip=192.0.2.1 srcintf=\"port15\" sessionid=0 action=clear_session proto=1 service=\"icmp/146/81\" count=306 attack=\"icmp_ flood\" dstport=20882 icmptype=0x92 icmpcode=0x51 attackid=16777316 profile=\"DoS-policy1\" ref=\"http://www.fortinet.com/ids/VID16777316\" msg=\"anomaly: icmp_flood, 34 > threshold 25, repeats 306 times\" crscore=50 crlevel=critical",
"event": {
"action": "clear_session",
"category": "anomaly",
"code": "0720018433",
"dataset": "utm:anomaly",
"outcome": "success",
"reason": "anomaly: icmp_flood, 34 > threshold 25, repeats 306 times"
},
"action": {
"name": "clear_session",
"outcome": "success",
"outcome_reason": "anomaly: icmp_flood, 34 > threshold 25, repeats 306 times",
"properties": {
"icmp_code": "0x51",
"icmp_type": "0x92"
},
"target": "network-traffic",
"type": "anomaly"
},
"destination": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"port": 20882
},
"fortinet": {
"fortigate": {
"attack": {
"id": "16777316",
"name": "icmp_ flood"
},
"event": {
"severity": "critical",
"type": "anomaly"
},
"icmp": {
"request": {
"code": "0x51",
"type": "0x92"
}
},
"security_profile": "DoS-policy1",
"sessionid": "0",
"threat": {
"level": "critical",
"score": 50
},
"virtual_domain": "vdom1"
}
},
"log": {
"level": "alert"
},
"network": {
"protocol": "icmp/146/81",
"transport": "icmp"
},
"observer": {
"ingress": {
"interface": {
"name": "port15"
}
}
},
"related": {
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.3|08192|utm:virus infected blocked|4|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0211008192 cat=utm:virus FTNTFGTsubtype=virus FTNTFGTeventtype=infected FTNTFGTlevel=warning FTNTFGTvd=vdom1 FTNTFGTeventtime=1545938448 msg=File is infected. act=blocked app=HTTP externalId=695 src=10.1.100.11 dst=example.com spt=44356 dpt=80 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined deviceOutboundInterface=port11 FTNTFGTdstintfrole=undefined FTNTFGTpolicyid=1 proto=6 deviceDirection=0 fname=eicar.com FTNTFGTquarskip=File-was-not-quarantined. FTNTFGTvirus=EICAR_TEST_FILE FTNTFGTdtype=Virus FTNTFGTref=http://www.fortinet.com/ve?vn\\=EICAR_TEST_FILE FTNTFGTvirusid=2172 request=http://example.com/virus/eicar.com FTNTFGTprofile=g-default duser=bob requestClientApplication=curl/7.47.0 FTNTFGTanalyticscksum=275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f FTNTFGTanalyticssubmit=false FTNTFGTcrscore=50 FTNTFGTcrlevel=critical",
"event": {
"action": "blocked",
"category": "utm",
"code": "0211008192",
"dataset": "utm:virus",
"outcome": "success",
"reason": "File is infected."
},
"@timestamp": "2018-12-27T19:20:48Z",
"action": {
"name": "blocked",
"outcome": "success",
"outcome_reason": "File is infected.",
"target": "network-traffic",
"type": "virus"
},
"destination": {
"address": "example.com",
"port": 80,
"user": {
"name": "bob"
}
},
"file": {
"name": "eicar.com"
},
"fortinet": {
"fortigate": {
"policyid": "1",
"security_profile": "g-default",
"threat": {
"level": "critical",
"score": 50
},
"virtual_domain": "vdom1"
}
},
"log": {
"level": "warning"
},
"network": {
"application": "HTTP",
"direction": "inbound",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port11"
}
},
"ingress": {
"interface": {
"name": "port12"
}
},
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"ip": [
"10.1.100.11"
],
"user": [
"bob"
]
},
"source": {
"address": "10.1.100.11",
"ip": "10.1.100.11",
"port": 44356
},
"url": {
"domain": "example.com",
"full": "http://example.com/virus/eicar.com",
"original": "http://example.com/virus/eicar.com",
"path": "/virus/eicar.com",
"port": 80,
"registered_domain": "example.com",
"scheme": "http",
"top_level_domain": "com"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "curl",
"original": "curl/7.47.0",
"os": {
"name": "Other"
},
"version": "7.47.0"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v5.6.0|08192|utm:virus infected blocked|4|FTNTFGTlogid=0211008192 cat=utm:virus FTNTFGTsubtype=virus FTNTFGTeventtype=infected FTNTFGTlevel=warning FTNTFGTvd=vdom1 msg=File is infected act=blocked app=HTTP externalId=56633 src=1.1.1.1 dst=192.0.2.1 spt=45719 dpt=80 deviceInboundInterface=port15 deviceOutboundInterface=port19 proto=6 deviceDirection=0 fname=eicar.com FTNTFGTchecksum=1dd02bdb FTNTFGTquarskip=No-skip cs1=EICAR_TEST_FILE cs1Label=Virus FTNTFGTdtype=Virus cs2=http://www.fortinet.com/ve?vn\\=EICAR_TEST_FILE cs2Label=Reference FTNTFGTvirusid=2172 request=http://example.net/eicar.com FTNTFGTprofile=default duser= requestClientApplication=Wget/1 10 2 FTNTFGTanalyticscksum=131f95c51cc819465fa1797f6ccacf9d494aaaff46fa3eac73ae63ffbdfd8267 FTNTFGTanalyticssubmit=false FTNTFGTcrscore=50 FTNTFGTcrlevel=critical",
"event": {
"action": "blocked",
"category": "utm",
"code": "0211008192",
"dataset": "utm:virus",
"outcome": "success",
"reason": "File is infected"
},
"action": {
"name": "blocked",
"outcome": "success",
"outcome_reason": "File is infected",
"target": "network-traffic",
"type": "virus"
},
"destination": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"port": 80
},
"file": {
"name": "eicar.com"
},
"fortinet": {
"fortigate": {
"security_profile": "default",
"threat": {
"level": "critical",
"score": 50
},
"virtual_domain": "vdom1"
}
},
"log": {
"level": "warning"
},
"network": {
"application": "HTTP",
"direction": "inbound",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port19"
}
},
"ingress": {
"interface": {
"name": "port15"
}
},
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v5.6.0"
},
"related": {
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"port": 45719
},
"url": {
"domain": "example.net",
"full": "http://example.net/eicar.com",
"original": "http://example.net/eicar.com",
"path": "/eicar.com",
"port": 80,
"registered_domain": "example.net",
"scheme": "http",
"top_level_domain": "net"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Wget",
"original": "Wget/1 10 2",
"os": {
"name": "Other"
},
"version": "1"
}
}
{
"message": "time=09:47:30 devname=\"TEST_DEV_NAME1\" devid=\"TEST_DEV_ID\" logid=\"1059028704\" type=\"utm\" subtype=\"app-ctrl\" eventtype=\"app-ctrl-all\" level=\"information\" vd=\"root\" eventtime=1741250850 appid=0000 srcip=1.2.3.4 dstip=3.4.5.6 srcport=11116 dstport=80 srcintf=\"root-enoveo0\" srcintfrole=\"undefined\" dstintf=\"internet-100\" dstintfrole=\"undefined\" proto=6 service=\"HTTP\" direction=\"outgoing\" policyid=293 sessionid=1947800834 applist=\"g-default\" appcat=\"Web.Client\" app=\"HTTP.BROWSER_Firefox\" action=\"pass\" hostname=\"example.com\" incidentserialno=235885632 url=\"/canonical.html\" msg=\"Web.Client: HTTP.BROWSER_Firefox,\" apprisk=\"elevated\"",
"event": {
"action": "pass",
"category": "utm",
"code": "1059028704",
"dataset": "utm:app-ctrl",
"outcome": "success",
"reason": "Web.Client: HTTP.BROWSER_Firefox,"
},
"@timestamp": "2025-03-06T08:47:30Z",
"action": {
"name": "pass",
"outcome": "success",
"outcome_reason": "Web.Client: HTTP.BROWSER_Firefox,",
"target": "network-traffic",
"type": "app-ctrl"
},
"destination": {
"address": "3.4.5.6",
"domain": "example.com",
"ip": "3.4.5.6",
"port": 80
},
"file": {
"name": "canonical.html"
},
"fortinet": {
"fortigate": {
"applist": "g-default",
"apprisk": "elevated",
"event": {
"type": "utm"
},
"policyid": "293",
"sessionid": "1947800834",
"virtual_domain": "root"
}
},
"log": {
"hostname": "TEST_DEV_NAME1",
"level": "information"
},
"network": {
"application": "HTTP.BROWSER_Firefox",
"direction": "outbound",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "internet-100"
}
},
"hostname": "TEST_DEV_NAME1",
"ingress": {
"interface": {
"name": "root-enoveo0"
}
},
"serial_number": "TEST_DEV_ID"
},
"related": {
"hosts": [
"TEST_DEV_NAME1",
"example.com"
],
"ip": [
"1.2.3.4",
"3.4.5.6"
]
},
"rule": {
"apprisk": "elevated",
"category": "Web.Client",
"ruleset": "g-default"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 11116
},
"url": {
"original": "/canonical.html",
"path": "/canonical.html"
}
}
{
"message": "0|Fortinet|Fortigate|v7.2.10|28704|utm:app-ctrl signature|2|deviceExternalId=FG3H0E5819900415 FTNTFGTeventtime=1741265077985865088 FTNTFGTtz=+0100 FTNTFGTlogid=1059028704 cat=utm:app-ctrl FTNTFGTsubtype=app-ctrl FTNTFGTeventtype=signature FTNTFGTlevel=information FTNTFGTvd=root FTNTFGTappid=16420 duser=testUser FTNTFGTgroup=testGroup src=1.2.3.4 FTNTFGTsrccountry=Reserved dst=3.4.5.6 FTNTFGTdstcountry=United States spt=52854 dpt=443 deviceInboundInterface=vlan-1024 FTNTFGTsrcintfrole=lan deviceOutboundInterface=vlan-1033 FTNTFGTdstintfrole=wan proto=6 app=HTTPS deviceDirection=0 FTNTFGTpolicyid=5 externalId=70046266 FTNTFGTapplist=app-ctrl-bme act=pass FTNTFGTappcat=Video/Audio FTNTFGTapp=YouTube_Video.Access dhost=example.com FTNTFGTincidentserialno=231408777 request=/youtubei/v1/player?https://example.com/ requestClientApplication=Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.0.0 Safari/537.36 FTNTFGThttpmethod=POST FTNTFGTreferralurl=https://example.com/ msg=Video/Audio: YouTube_Video.Access FTNTFGTclouduser=1.2.3.4 fname=LA CACABOX sur REPO & AMONG-US 3D - POTATOZ VOD FTNTFGTapprisk=elevated FTNTFGTcloudaction=others",
"event": {
"action": "pass",
"category": "utm",
"code": "1059028704",
"dataset": "utm:app-ctrl",
"outcome": "success",
"reason": "Video/Audio: YouTube_Video.Access",
"timezone": "+0100"
},
"@timestamp": "2025-03-06T12:44:37.985865Z",
"action": {
"name": "pass",
"outcome": "success",
"outcome_reason": "Video/Audio: YouTube_Video.Access",
"target": "network-traffic",
"type": "app-ctrl"
},
"destination": {
"address": "3.4.5.6",
"domain": "example.com",
"geo": {
"country_name": "United States"
},
"ip": "3.4.5.6",
"port": 443,
"user": {
"name": "testUser"
}
},
"file": {
"name": "LA CACABOX sur REPO & AMONG-US 3D - POTATOZ VOD"
},
"fortinet": {
"fortigate": {
"applist": "app-ctrl-bme",
"apprisk": "elevated",
"policyid": "5",
"virtual_domain": "root"
}
},
"group": {
"name": "testGroup"
},
"http": {
"request": {
"method": "POST",
"referrer": "https://example.com/"
}
},
"log": {
"level": "information"
},
"network": {
"application": "HTTPS",
"direction": "inbound",
"protocol": "https",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "wan",
"name": "vlan-1033"
}
},
"ingress": {
"interface": {
"alias": "lan",
"name": "vlan-1024"
}
},
"serial_number": "FG3H0E5819900415",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v7.2.10"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4",
"3.4.5.6"
],
"user": [
"testUser"
]
},
"rule": {
"apprisk": "elevated",
"category": "Video/Audio",
"ruleset": "app-ctrl-bme"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 52854
},
"url": {
"original": "/youtubei/v1/player?https://example.com/",
"path": "/youtubei/v1/player",
"query": "https://example.com/"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Chrome",
"original": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.0.0 Safari/537.36",
"os": {
"name": "Windows",
"version": "10"
},
"version": "122.0.0"
}
}
{
"message": "0|Fortinet|Fortigate|v7.0.17|08192|utm:virus infected|4|deviceExternalId=FG120GTK24003942 FTNTFGTeventtime=1741264893005614373 FTNTFGTtz=+0100 FTNTFGTlogid=0211008192 cat=utm:virus FTNTFGTsubtype=virus FTNTFGTeventtype=infected FTNTFGTlevel=warning FTNTFGTvd=root FTNTFGTpolicyid=7 FTNTFGTpoluuid=poluuid FTNTFGTpolicytype=policy msg=File is infected. act=blocked app=IMAP externalId=2861718763 src=1.2.3.4 dst=3.4.5.6 spt=54364 dpt=143 FTNTFGTsrccountry=Reserved FTNTFGTdstcountry=France deviceInboundInterface=400-TOXIII FTNTFGTsrcintfrole=lan deviceOutboundInterface=port1 FTNTFGTdstintfrole=wan FTNTFGTsrcuuid=dstuuuid FTNTFGTdstuuid=dstuuuid proto=6 deviceDirection=0 fname=BULLETIN-TABLE-OVALE.docx FTNTFGTquarskip=Quarantine-disabled FTNTFGTvirus=MSOffice/Agent.PCL!tr.dldr FTNTFGTviruscat=Virus FTNTFGTdtype=av-engine FTNTFGTref=http://test.com/ve?vn\\=sdkdksdkds FTNTFGTvirusid=8032867 FTNTFGTprofile=default suser=user1 duser=user1 FTNTFGTrecipient=\\\\\"testUser@test.test\\\\\" FTNTFGTanalyticscksum=383b017352d7602c7603f5d36a9c3beb23df2f183116e0cc3d81e158e978ee7d FTNTFGTanalyticssubmit=false FTNTFGTcrscore=50 FTNTFGTcraction=2 FTNTFGTcrlevel=critical",
"event": {
"action": "blocked",
"category": "utm",
"code": "0211008192",
"dataset": "utm:virus",
"outcome": "success",
"reason": "File is infected.",
"timezone": "+0100"
},
"@timestamp": "2025-03-06T12:41:33.005615Z",
"action": {
"name": "blocked",
"outcome": "success",
"outcome_reason": "File is infected.",
"target": "network-traffic",
"type": "virus"
},
"destination": {
"address": "3.4.5.6",
"geo": {
"country_name": "France"
},
"ip": "3.4.5.6",
"port": 143,
"user": {
"name": "user1"
}
},
"file": {
"name": "BULLETIN-TABLE-OVALE.docx"
},
"fortinet": {
"fortigate": {
"policyid": "7",
"policytype": "policy",
"poluuid": "poluuid",
"security_profile": "default",
"threat": {
"level": "critical",
"score": 50,
"type": 2
},
"virtual_domain": "root"
}
},
"log": {
"level": "warning"
},
"network": {
"application": "IMAP",
"direction": "inbound",
"protocol": "imap",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "wan",
"name": "port1"
}
},
"ingress": {
"interface": {
"alias": "lan",
"name": "400-TOXIII"
}
},
"serial_number": "FG120GTK24003942",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v7.0.17"
},
"related": {
"ip": [
"1.2.3.4",
"3.4.5.6"
],
"user": [
"user1"
]
},
"rule": {
"ruleset": "policy"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 54364,
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.3|28704|utm:app-ctrl app-ctrl-all pass|2|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=1059028704 cat=utm:app-ctrl FTNTFGTsubtype=app-ctrl FTNTFGTeventtype=app-ctrl-all FTNTFGTlevel=information FTNTFGTvd=vdom1 FTNTFGTeventtime=1545949688 FTNTFGTappid=34050 src=10.1.100.11 dst=192.0.2.1 spt=56826 dpt=80 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined deviceOutboundInterface=port11 FTNTFGTdstintfrole=undefined proto=6 app=HTTP deviceDirection=1 FTNTFGTpolicyid=1 externalId=12567 FTNTFGTapplist=g-default FTNTFGTappcat=Web.Client FTNTFGTapp=HTTP.BROWSER_Firefox act=pass dhost=example.com FTNTFGTincidentserialno=1702350499 request=/success.txt msg=Web.Client: HTTP.BROWSER_Firefox, FTNTFGTapprisk=elevated suser=example.com\\\\alice",
"event": {
"action": "pass",
"category": "utm",
"code": "1059028704",
"dataset": "utm:app-ctrl",
"outcome": "success",
"reason": "Web.Client: HTTP.BROWSER_Firefox,"
},
"@timestamp": "2018-12-27T22:28:08Z",
"action": {
"name": "pass",
"outcome": "success",
"outcome_reason": "Web.Client: HTTP.BROWSER_Firefox,",
"target": "network-traffic",
"type": "app-ctrl"
},
"destination": {
"address": "192.0.2.1",
"domain": "example.com",
"ip": "192.0.2.1",
"port": 80
},
"fortinet": {
"fortigate": {
"applist": "g-default",
"apprisk": "elevated",
"policyid": "1",
"virtual_domain": "vdom1"
}
},
"log": {
"level": "information"
},
"network": {
"application": "HTTP",
"direction": "outbound",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port11"
}
},
"ingress": {
"interface": {
"name": "port12"
}
},
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"10.1.100.11",
"192.0.2.1"
],
"user": [
"alice"
]
},
"rule": {
"apprisk": "elevated",
"category": "Web.Client",
"ruleset": "g-default"
},
"source": {
"address": "10.1.100.11",
"ip": "10.1.100.11",
"port": 56826,
"user": {
"domain": "example.com",
"name": "alice"
}
},
"url": {
"original": "/success.txt",
"path": "/success.txt"
},
"user": {
"name": "alice"
}
}
{
"message": "date=2018-12-29 time=15:30:25 logid=\"0419016384\" type=\"utm\" subtype=\"ips\" eventtype=\"signature\" level=\"alert\" vd=\"vdom1\" eventtime=1540852225 severity=\"info\" srcip=1.2.3.4 srccountry=\"Reserved\" dstip=example.com srcintf=\"dmz\" srcintfrole=\"lan\" dstintf=\"wan1\" dstintfrole=\"wan\" sessionid=4205 action=\"reset\" proto=6 service=\"HTTP\" policyid=1 attack=\"Virus.File\" srcport=53330 dstport=80 hostname=\"example.com\" url=\"/cgi-bin/upload.py?https://example.com/\" direction=\"outgoing\" attackid=29844 profile=\"ips-test\" ref=\"http://www.fortinet.com/ids/VID29844\" incidentserialno=2111356281 msg=\"file_transfer: Virus.File,\"",
"event": {
"action": "reset",
"category": "utm",
"code": "0419016384",
"outcome": "success",
"reason": "file_transfer: Virus.File,"
},
"@timestamp": "2018-10-29T22:30:25Z",
"action": {
"name": "reset",
"outcome": "success",
"outcome_reason": "file_transfer: Virus.File,",
"target": "network-traffic",
"type": "ips"
},
"destination": {
"address": "example.com",
"domain": "example.com",
"port": 80
},
"fortinet": {
"fortigate": {
"attack": {
"id": "29844",
"name": "Virus.File"
},
"event": {
"severity": "info",
"type": "utm"
},
"policyid": "1",
"security_profile": "ips-test",
"sessionid": "4205",
"virtual_domain": "vdom1"
}
},
"log": {
"level": "alert"
},
"network": {
"direction": "outbound",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "wan",
"name": "wan1"
}
},
"ingress": {
"interface": {
"alias": "lan",
"name": "dmz"
}
}
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 53330
},
"url": {
"original": "/cgi-bin/upload.py?https://example.com/",
"path": "/cgi-bin/upload.py",
"query": "https://example.com/"
}
}
{
"message": "date=2018-12-29 time=14:50:47 logid=\"0419016384\" type=\"utm\" subtype=\"ips\" eventtype=\"signature\" level=\"alert\" vd=\"vdom1\" eventtime=1540849847 severity=\"info\" srcip=1.2.3.4 srccountry=\"Reserved\" dstip=example.com srcintf=\"dmz\" srcintfrole=\"lan\" dstintf=\"wan1\" dstintfrole=\"wan\" sessionid=2979 action=\"reset\" proto=6 service=\"HTTP\" policyid=1 attack=\"Virus.File\" srcport=46552 dstport=80 hostname=\"example.com\" url=\"/virus/example.com\" direction=\"incoming\" attackid=29844 profile=\"ips-test\" ref=\"http://www.fortinet.com/ids/VID29844\" incidentserialno=122164746 msg=\"file_transfer: Virus.File,\"",
"event": {
"action": "reset",
"category": "utm",
"code": "0419016384",
"outcome": "success",
"reason": "file_transfer: Virus.File,"
},
"@timestamp": "2018-10-29T21:50:47Z",
"action": {
"name": "reset",
"outcome": "success",
"outcome_reason": "file_transfer: Virus.File,",
"target": "network-traffic",
"type": "ips"
},
"destination": {
"address": "example.com",
"domain": "example.com",
"port": 80
},
"fortinet": {
"fortigate": {
"attack": {
"id": "29844",
"name": "Virus.File"
},
"event": {
"severity": "info",
"type": "utm"
},
"policyid": "1",
"security_profile": "ips-test",
"sessionid": "2979",
"virtual_domain": "vdom1"
}
},
"log": {
"level": "alert"
},
"network": {
"direction": "inbound",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "wan",
"name": "wan1"
}
},
"ingress": {
"interface": {
"alias": "lan",
"name": "dmz"
}
}
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 46552
},
"url": {
"original": "/virus/example.com",
"path": "/virus/example.com"
}
}
{
"message": "time=15:05:54 devname=\"INFRA1\" devid=\"DEVICE\" eventtime=1752152754192314929 tz=\"+0200\" logid=\"0100000001\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"INFRA\" logdesc=\"DHCP Ack log\" interface=\"VLAN1\" dhcp_msg=\"Ack\" mac=\"AA:BB:CC:DD:EE:FF\" ip=1.2.3.4 lease=432000 hostname=\"HOSTNAME\" msg=\"DHCP server sends a DHCPACK\"",
"event": {
"category": "event",
"code": "0100000001",
"dataset": "event:system",
"reason": "DHCP server sends a DHCPACK",
"timezone": "+0200"
},
"@timestamp": "2025-07-10T13:05:54.192315Z",
"action": {
"outcome_reason": "DHCP server sends a DHCPACK",
"target": "network-traffic",
"type": "system"
},
"destination": {
"address": "HOSTNAME",
"domain": "HOSTNAME"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"virtual_domain": "INFRA"
}
},
"log": {
"description": "DHCP Ack log",
"hostname": "INFRA1",
"level": "information"
},
"observer": {
"hostname": "INFRA1",
"serial_number": "DEVICE"
},
"related": {
"hosts": [
"HOSTNAME",
"INFRA1"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "AA:BB:CC:DD:EE:FF"
}
}
{
"message": "date=2018-12-27,time=14:45:26,logid=\"1501054802\",type=\"dns\",subtype=\"dns-response\",level=\"notice\",vd=\"vdom1\",eventtime=1545950726,policyid=1,sessionid=13355,user=\"bob\",srcip=1.1.1.1,srcport=54621,srcintf=\"port12\",srcintfrole=\"lan\",dstip=192.0.2.1,dstport=53,dstintf=\"port11\",dstintfrole=\"wan\",proto=17,profile=\"default\",srcmac=\"02:00:00:00:00:00\",xid=5137,qname=\"example.com\",qtype=\"A\",qtypeval=1,qclass=\"IN\",ipaddr=\"104.80.89.26, 104.80.89.24\",msg=\"Domain is monitored\",action=\"pass\",cat=52,catdesc=\"Information Technology\"",
"event": {
"action": "pass",
"category": "dns",
"code": "1501054802",
"dataset": "dns:dns-response",
"outcome": "success",
"reason": "Domain is monitored"
},
"@timestamp": "2018-12-27T22:45:26Z",
"action": {
"name": "pass",
"outcome": "success",
"outcome_reason": "Domain is monitored",
"target": "network-traffic",
"type": "dns-response"
},
"destination": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"port": 53
},
"dns": {
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "A"
},
"rrname": "example.com",
"rrtype": "A"
},
"fortinet": {
"fortigate": {
"event": {
"type": "dns"
},
"policyid": "1",
"security_profile": "default",
"sessionid": "13355",
"virtual_domain": "vdom1"
}
},
"log": {
"level": "notice"
},
"network": {
"transport": "udp"
},
"observer": {
"egress": {
"interface": {
"alias": "wan",
"name": "port11"
}
},
"ingress": {
"interface": {
"alias": "lan",
"name": "port12"
}
}
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.1.1.1",
"192.0.2.1"
],
"user": [
"bob"
]
},
"rule": {
"category": "Information Technology"
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"mac": "02:00:00:00:00:00",
"port": 54621,
"user": {
"name": "bob"
}
},
"user": {
"name": "bob"
}
}
{
"message": "time=11:36:13 devname=\"PC-01-OS1\" devid=\"XXXXXXXXXXXX\" eventtime=1721727373453168766 tz=\"+0200\" logid=\"010000000\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"AAAA-AA\" logdesc=\"Object attribute configured\" user=\"username\" ui=\"GUI(192.0.2.1)\" action=\"Edit\" cfgtid=111111111 uuid=\"xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxx\" cfgpath=\"firewall.policy\" cfgobj=\"756\" cfgattr=\"service[svc-win->svc-repo-linux-port]\" msg=\"Edit firewall.policy 756\"",
"event": {
"action": "Edit",
"category": "event",
"code": "010000000",
"dataset": "event:system",
"outcome": "success",
"reason": "Edit firewall.policy 756",
"timezone": "+0200"
},
"@timestamp": "2024-07-23T09:36:13.453169Z",
"action": {
"name": "Edit",
"outcome": "success",
"outcome_reason": "Edit firewall.policy 756",
"type": "system"
},
"fortinet": {
"fortigate": {
"cfgattr": "service[svc-win->svc-repo-linux-port]",
"cfgpath": "firewall.policy",
"cfgtid": "111111111",
"event": {
"type": "event"
},
"poluuid": "xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxx",
"virtual_domain": "AAAA-AA"
}
},
"log": {
"description": "Object attribute configured",
"hostname": "PC-01-OS1",
"level": "information"
},
"observer": {
"hostname": "PC-01-OS1",
"serial_number": "XXXXXXXXXXXX"
},
"related": {
"hosts": [
"PC-01-OS1"
],
"ip": [
"192.0.2.1"
],
"user": [
"username"
]
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"user": {
"name": "username"
}
},
"user": {
"name": "username"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.3|20503|utm:emailfilter smtp log-only|2|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0508020503 cat=utm:emailfilter FTNTFGTsubtype=emailfilter FTNTFGTeventtype=smtp FTNTFGTlevel=information FTNTFGTvd=vdom1 FTNTFGTeventtime=1545939418 FTNTFGTpolicyid=1 externalId=1135 duser=bob src=10.1.100.11 spt=35969 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined dst=172.18.62.158 dpt=25 deviceOutboundInterface=port11 FTNTFGTdstintfrole=undefined proto=6 app=SMTP FTNTFGTprofile=test-spam act=log-only suser=user1 duser=test1@server88.qa.fortinet.com FTNTFGTsender=user1 FTNTFGTrecipient=test1@server88.qa.fortinet.com deviceDirection=1 msg=general email log FTNTFGTsubject=hello_world2 FTNTFGTsize=216 FTNTFGTattachment=no",
"event": {
"action": "log-only",
"category": "utm",
"code": "0508020503",
"dataset": "utm:emailfilter",
"outcome": "success",
"reason": "general email log"
},
"@timestamp": "2018-12-27T19:36:58Z",
"action": {
"name": "log-only",
"outcome": "success",
"outcome_reason": "general email log",
"target": "network-traffic",
"type": "emailfilter"
},
"destination": {
"address": "172.18.62.158",
"ip": "172.18.62.158",
"port": 25,
"user": {
"name": "bob"
}
},
"fortinet": {
"fortigate": {
"policyid": "1",
"security_profile": "test-spam",
"virtual_domain": "vdom1"
}
},
"log": {
"level": "information"
},
"network": {
"application": "SMTP",
"direction": "outbound",
"protocol": "smtp",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port11"
}
},
"ingress": {
"interface": {
"name": "port12"
}
},
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"ip": [
"10.1.100.11",
"172.18.62.158"
],
"user": [
"bob",
"user1"
]
},
"source": {
"address": "10.1.100.11",
"ip": "10.1.100.11",
"port": 35969,
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "type=\"event\" subtype=\"system\" level=\"information\" vd=\"root\" logdesc=\"Object attribute configured\" user=\"admin\" ui=\"jsconsole(127.0.0.1)\" action=\"Add\" cfgtid=1234567890 cfgpath=\"system.admin\" cfgobj=\"vOcep\" cfgattr=\"password[*]accprofile[super_admin]vdom[root]\" msg=\"Add system.admin vOcep\"",
"event": {
"action": "Add",
"category": "event",
"dataset": "event:system",
"outcome": "success",
"reason": "Add system.admin vOcep"
},
"action": {
"name": "Add",
"outcome": "success",
"outcome_reason": "Add system.admin vOcep",
"type": "system"
},
"fortinet": {
"fortigate": {
"cfgattr": "password[*]accprofile[super_admin]vdom[root]",
"cfgpath": "system.admin",
"cfgtid": "1234567890",
"event": {
"type": "event"
},
"virtual_domain": "root"
}
},
"log": {
"description": "Object attribute configured",
"level": "information"
},
"related": {
"ip": [
"127.0.0.1"
],
"user": [
"admin"
]
},
"source": {
"address": "127.0.0.1",
"ip": "127.0.0.1",
"user": {
"name": "admin"
}
},
"user": {
"name": "admin"
}
}
{
"message": "type=\"event\" subtype=\"system\" level=\"information\" vd=\"root\" logdesc=\"Admin login successful\" sn=\"1234567890\" user=\"admin\" ui=\"jsconsole\" method=\"jsconsole\" srcip=1.1.1.1 dstip=1.1.1.1 action=\"login\" status=\"success\" reason=\"none\" profile=\"super_admin\" msg=\"Administrator admin logged in successfully from jsconsole\"",
"event": {
"action": "login",
"category": "event",
"dataset": "event:system",
"outcome": "success",
"provider": "jsconsole",
"reason": "none"
},
"action": {
"name": "login",
"outcome": "success",
"outcome_reason": "Administrator admin logged in successfully from jsconsole",
"target": "network-traffic",
"type": "system"
},
"destination": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"method": "jsconsole",
"security_profile": "super_admin",
"sn": "1234567890",
"virtual_domain": "root"
}
},
"log": {
"description": "Admin login successful",
"level": "information"
},
"related": {
"ip": [
"1.1.1.1"
],
"user": [
"admin"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"user": {
"name": "admin"
}
},
"user": {
"name": "admin"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.3|32002|event:system login failed|7|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0100032002 cat=event:system FTNTFGTsubtype=system FTNTFGTlevel=alert FTNTFGTvd=vdom1 FTNTFGTeventtime=1545938140 FTNTFGTlogdesc=Admin login failed FTNTFGTsn=0 duser=user1 sproc=https(172.16.200.254) FTNTFGTmethod=https src=172.16.200.254 dst=172.16.200.1 act=login outcome=failed reason=name_invalid msg=Administrator user1 login failed from https(172.16.200.254) because of invalid user name",
"event": {
"action": "login",
"category": "event",
"code": "0100032002",
"dataset": "event:system",
"outcome": "failure",
"provider": "https",
"reason": "name_invalid"
},
"@timestamp": "2018-12-27T19:15:40Z",
"action": {
"name": "login",
"outcome": "failure",
"outcome_reason": "Administrator user1 login failed from https(172.16.200.254) because of invalid user name",
"target": "network-traffic",
"type": "system"
},
"destination": {
"address": "172.16.200.1",
"ip": "172.16.200.1",
"user": {
"name": "user1"
}
},
"fortinet": {
"fortigate": {
"sn": "0",
"virtual_domain": "vdom1"
}
},
"log": {
"description": "Admin login failed",
"level": "alert"
},
"network": {
"protocol": "https"
},
"observer": {
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"ip": [
"172.16.200.1",
"172.16.200.254"
],
"user": [
"user1"
]
},
"source": {
"address": "172.16.200.254",
"ip": "172.16.200.254"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.3|43008|event:user authentication success|3|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0102043008 cat=event:user FTNTFGTsubtype=user FTNTFGTlevel=notice FTNTFGTvd=vdom1 FTNTFGTeventtime=1545938255 FTNTFGTlogdesc=Authentication success src=10.1.100.11 dst=172.16.200.55 FTNTFGTpolicyid=1 deviceInboundInterface=port12 duser=bob FTNTFGTgroup=N/A FTNTFGTauthproto=TELNET(10.1.100.11) act=authentication outcome=success reason=N/A msg=User bob succeeded in authentication",
"event": {
"action": "authentication",
"category": "event",
"code": "0102043008",
"dataset": "event:user",
"outcome": "success",
"reason": "User bob succeeded in authentication"
},
"@timestamp": "2018-12-27T19:17:35Z",
"action": {
"name": "authentication",
"outcome": "success",
"outcome_reason": "User bob succeeded in authentication",
"target": "network-traffic",
"type": "user"
},
"destination": {
"address": "172.16.200.55",
"ip": "172.16.200.55",
"user": {
"name": "bob"
}
},
"fortinet": {
"fortigate": {
"policyid": "1",
"virtual_domain": "vdom1"
}
},
"log": {
"description": "Authentication success",
"level": "notice"
},
"observer": {
"ingress": {
"interface": {
"name": "port12"
}
},
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"ip": [
"10.1.100.11",
"172.16.200.55"
],
"user": [
"bob"
]
},
"source": {
"address": "10.1.100.11",
"ip": "10.1.100.11"
}
}
{
"message": "devname=\".self\" devid=\"1111111111111111\" vd=\"root\" itime=1725479662 date=\"2024-09-04\" time=\"19:54:22\" tz=\"+0000\" type=\"appevent\" user=\"system\" user_from=\"system\" logid=\"222222\" subtype=\"logdev\" eventtype=\"logging-status\" level=\"warning\" desc=\"Device offline\" logdev_id=\"ABCDEFGHIJKLMNOP\" logdev_name=\"LOGDEV-NAME\" logdev_offline_duration=69138 logdev_last_logging=1721331330 msg=\"Did not receive any log from device LOGDEV-NAME[ABCDEFGHIJKLMNOP] in past 48d18m52s (69138 minutes).\"",
"event": {
"category": "appevent",
"code": "222222",
"reason": "Did not receive any log from device LOGDEV-NAME[ABCDEFGHIJKLMNOP] in past 48d18m52s (69138 minutes).",
"start": "2024-09-04T19:54:22Z",
"timezone": "+0000",
"type": "Device offline"
},
"action": {
"outcome_reason": "Did not receive any log from device LOGDEV-NAME[ABCDEFGHIJKLMNOP] in past 48d18m52s (69138 minutes).",
"type": "logdev"
},
"fortinet": {
"fortigate": {
"event": {
"desc": "Device offline",
"type": "appevent"
},
"logdev": {
"id": "ABCDEFGHIJKLMNOP",
"last_logging": "2024-07-18T19:35:30.000000Z",
"name": "LOGDEV-NAME"
},
"virtual_domain": "root"
}
},
"log": {
"hostname": ".self",
"level": "warning"
},
"observer": {
"hostname": ".self",
"serial_number": "1111111111111111"
},
"related": {
"hosts": [
".self"
],
"user": [
"system"
]
},
"source": {
"user": {
"name": "system"
}
},
"user": {
"name": "system"
}
}
{
"message": "time=10:59:48 devname=\"FW-001\" devid=\"xxxxxxxxxx\" eventtime=1720429188081127405 tz=\"+0200\" logid=\"0000000\" type=\"utm\" subtype=\"webfilter\" eventtype=\"ftgd_allow\" level=\"notice\" vd=\"root\" policyid=00000 poluuid=\"xxxxxx-xxxx-xxxx-xxxxxx\" policytype=\"policy\" sessionid=111111111 srcip=192.0.2.1 srcport=1000 srccountry=\"France\" srcintf=\"aaaaaaaaa\" srcintfrole=\"wan\" srcuuid=\"xxxxxx-xxxx-xxxx-xxxxxxxxxxx\" dstip=10.0.0.1 dstport=80 dstcountry=\"Reserved\" dstintf=\"aaaaaaaa\" dstintfrole=\"lan\" dstuuid=\"xxxxxxx-xxxx-xxxx-xxxxxxxxxxxx\" proto=6 service=\"HTTP\" hostname=\"example.com\" forwardedfor=\"1.2.3.4\" profile=\"monitor-all\" action=\"passthrough\" reqtype=\"direct\" url=\"http://example.com/\" sentbyte=270 rcvdbyte=0 direction=\"outgoing\" msg=\"URL belongs to an allowed category in policy\" method=\"domain\" cat=51 catdesc=\"Government and Legal Organizations\"",
"event": {
"action": "passthrough",
"category": "utm",
"code": "0000000",
"outcome": "success",
"provider": "domain",
"reason": "URL belongs to an allowed category in policy",
"timezone": "+0200"
},
"@timestamp": "2024-07-08T08:59:48.081128Z",
"action": {
"name": "passthrough",
"outcome": "success",
"outcome_reason": "URL belongs to an allowed category in policy",
"target": "network-traffic",
"type": "webfilter"
},
"destination": {
"address": "10.0.0.1",
"bytes": 0,
"domain": "example.com",
"ip": "10.0.0.1",
"port": 80
},
"fortinet": {
"fortigate": {
"event": {
"type": "utm"
},
"method": "domain",
"policyid": "00000",
"policytype": "policy",
"poluuid": "xxxxxx-xxxx-xxxx-xxxxxx",
"security_profile": "monitor-all",
"sessionid": "111111111",
"virtual_domain": "root"
}
},
"log": {
"hostname": "FW-001",
"level": "notice"
},
"network": {
"bytes": 270,
"direction": "outbound",
"forwarded_ip": "1.2.3.4",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "lan",
"name": "aaaaaaaa"
}
},
"hostname": "FW-001",
"ingress": {
"interface": {
"alias": "wan",
"name": "aaaaaaaaa"
}
},
"serial_number": "xxxxxxxxxx"
},
"related": {
"hosts": [
"FW-001",
"example.com"
],
"ip": [
"10.0.0.1",
"192.0.2.1"
]
},
"rule": {
"category": "Government and Legal Organizations",
"ruleset": "policy"
},
"source": {
"address": "192.0.2.1",
"bytes": 270,
"geo": {
"country_name": "France"
},
"ip": "192.0.2.1",
"port": 1000
},
"url": {
"domain": "example.com",
"full": "http://example.com/",
"original": "http://example.com/",
"path": "/",
"port": 80,
"registered_domain": "example.com",
"scheme": "http",
"top_level_domain": "com"
}
}
{
"message": "timestamp=1746183115 devname=\"devName1\" devid=\"devId\" vd=\"root\" date=2025-05-02 time=10:51:55 eventtime=1746175915421843994 tz=\"+0200\" logid=\"1000000000\" type=\"utm\" subtype=\"app-ctrl\" eventtype=\"signature\" level=\"information\" appid=15893 srcip=1.2.3.4 srccountry=\"Spain\" dstip=3.4.5.6 dstcountry=\"Reserved\" srcport=39972 dstport=80 srcintf=\"port2\" srcintfrole=\"wan\" dstintf=\"port3\" dstintfrole=\"dmz\" proto=6 service=\"HTTP\" direction=\"outgoing\" policyid=120 poluuid=\"5187b416-87fa-51ec-c830-268b6371a3ac\" policytype=\"policy\" sessionid=11111111 applist=\"block-high-risk\" action=\"pass\" appcat=\"Web.Client\" app=\"HTTP.BROWSER\" hostname=\"example.com\" incidentserialno=10101 url=\"/test/version_test_v2.php\" httpmethod=\"GET\" msg=\"Web.Client: HTTP.BROWSER\" apprisk=\"medium\" forwardedfor=\"5.6.7.8,6.7.8.9\"",
"event": {
"action": "pass",
"category": "utm",
"code": "1000000000",
"dataset": "utm:app-ctrl",
"outcome": "success",
"reason": "Web.Client: HTTP.BROWSER",
"timezone": "+0200"
},
"@timestamp": "2025-05-02T08:51:55.421844Z",
"action": {
"name": "pass",
"outcome": "success",
"outcome_reason": "Web.Client: HTTP.BROWSER",
"target": "network-traffic",
"type": "app-ctrl"
},
"destination": {
"address": "3.4.5.6",
"domain": "example.com",
"ip": "3.4.5.6",
"port": 80
},
"file": {
"name": "version_test_v2.php"
},
"fortinet": {
"fortigate": {
"applist": "block-high-risk",
"apprisk": "medium",
"event": {
"type": "utm"
},
"policyid": "120",
"policytype": "policy",
"poluuid": "5187b416-87fa-51ec-c830-268b6371a3ac",
"sessionid": "11111111",
"virtual_domain": "root"
}
},
"http": {
"request": {
"method": "GET"
}
},
"log": {
"hostname": "devName1",
"level": "information"
},
"network": {
"application": "HTTP.BROWSER",
"direction": "outbound",
"forwarded_ip": [
"5.6.7.8",
"6.7.8.9"
],
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "dmz",
"name": "port3"
}
},
"hostname": "devName1",
"ingress": {
"interface": {
"alias": "wan",
"name": "port2"
}
},
"serial_number": "devId"
},
"related": {
"hosts": [
"devName1",
"example.com"
],
"ip": [
"1.2.3.4",
"3.4.5.6"
]
},
"rule": {
"apprisk": "medium",
"category": "Web.Client",
"ruleset": "block-high-risk"
},
"source": {
"address": "1.2.3.4",
"geo": {
"country_name": "Spain"
},
"ip": "1.2.3.4",
"port": 39972
},
"url": {
"original": "/test/version_test_v2.php",
"path": "/test/version_test_v2.php"
}
}
{
"message": "time=11:09:50 devname=\"abc\" devid=\"1\" logid=\"1059028704\" type=\"utm\" subtype=\"app-ctrl\" eventtype=\"app-ctrl-all\" level=\"information\" vd=\"root\" eventtime=1579860590 appid=40568 srcip=1.1.1.1 dstip=192.0.2.1 srcport=33345 dstport=443 srcintf=\"test\" srcintfrole=\"undefined\" dstintf=\"port1\" dstintfrole=\"undefined\" proto=6 service=\"HTTPS\" direction=\"outgoing\" policyid=1 sessionid=1508480438 applist=\"default\" appcat=\"Web.Client\" app=\"HTTPS.BROWSER\" action=\"pass\" hostname=\"example.com\" incidentserialno=455926217 url=\"/\" msg=\"Web.Client: HTTPS.BROWSER,\" apprisk=\"medium\"",
"event": {
"action": "pass",
"category": "utm",
"code": "1059028704",
"dataset": "utm:app-ctrl",
"outcome": "success",
"reason": "Web.Client: HTTPS.BROWSER,"
},
"@timestamp": "2020-01-24T10:09:50Z",
"action": {
"name": "pass",
"outcome": "success",
"outcome_reason": "Web.Client: HTTPS.BROWSER,",
"target": "network-traffic",
"type": "app-ctrl"
},
"destination": {
"address": "192.0.2.1",
"domain": "example.com",
"ip": "192.0.2.1",
"port": 443
},
"fortinet": {
"fortigate": {
"applist": "default",
"apprisk": "medium",
"event": {
"type": "utm"
},
"policyid": "1",
"sessionid": "1508480438",
"virtual_domain": "root"
}
},
"log": {
"hostname": "abc",
"level": "information"
},
"network": {
"application": "HTTPS.BROWSER",
"direction": "outbound",
"protocol": "https",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port1"
}
},
"hostname": "abc",
"ingress": {
"interface": {
"name": "test"
}
},
"serial_number": "1"
},
"related": {
"hosts": [
"abc",
"example.com"
],
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"rule": {
"apprisk": "medium",
"category": "Web.Client",
"ruleset": "default"
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"port": 33345
},
"url": {
"original": "/",
"path": "/"
}
}
{
"message": " time=15:22:43 devname=\"abc\" devid=\"1\" logid=\"0000000011\" type=\"traffic\" subtype=\"forward\" level=\"warning\" vd=\"root\" eventtime=1602591763587868496 tz=\"+0300\" srcip=1.1.1.1 identifier=256 srcintf=\"internal\" srcintfrole=\"lan\" dstip=192.0.2.1 dstintf=\"wan1\" dstintfrole=\"wan\" srcuuid=\"b22e6ef4-2e38-51ea-72c9-53b2da2e20f5\" dstuuid=\"052bdbce-823a-51e9-eb23-7a3e819fea4f\" poluuid=\"1520e1aa-823a-51e9-984f-a55e1f39b3c7\" sessionid=706677975 proto=1 action=\"ip-conn\" policyid=1 policytype=\"policy\" service=\"icmp/0/8\" dstcountry=\"Netherlands\" srccountry=\"Reserved\" appcat=\"unscanned\" crscore=5 craction=262144 crlevel=\"low\"",
"event": {
"action": "ip-conn",
"category": "traffic",
"code": "0000000011",
"dataset": "traffic:forward",
"outcome": "success",
"timezone": "+0300"
},
"@timestamp": "2020-10-13T12:22:43.587868Z",
"action": {
"name": "ip-conn",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "192.0.2.1",
"geo": {
"country_name": "Netherlands"
},
"ip": "192.0.2.1"
},
"fortinet": {
"fortigate": {
"event": {
"type": "traffic"
},
"policyid": "1",
"policytype": "policy",
"poluuid": "1520e1aa-823a-51e9-984f-a55e1f39b3c7",
"sessionid": "706677975",
"threat": {
"level": "low",
"score": 5,
"type": 262144
},
"virtual_domain": "root"
}
},
"log": {
"hostname": "abc",
"level": "warning"
},
"network": {
"protocol": "icmp/0/8",
"transport": "icmp"
},
"observer": {
"egress": {
"interface": {
"alias": "wan",
"name": "wan1"
}
},
"hostname": "abc",
"ingress": {
"interface": {
"alias": "lan",
"name": "internal"
}
},
"serial_number": "1"
},
"related": {
"hosts": [
"abc"
],
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"rule": {
"category": "unscanned",
"ruleset": "policy"
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
}
}
{
"message": " time=13:02:14 devname=\"abc\" devid=\"1\" logid=\"0001000014\" type=\"traffic\" subtype=\"local\" level=\"notice\" vd=\"root\" eventtime=1602586934900309053 tz=\"+0200\" srcip=00192.0.2.100:00:00:00 identifier=0 srcintf=\"AVR-GUEST-AP\" srcintfrole=\"lan\" dstip=12192.0.2.116 dstintf=\"unknown0\" dstintfrole=\"undefined\" sessionid=1395131 proto=58 action=\"accept\" policyid=0 policytype=\"local-in-policy6\" service=\"icmp6/143/0\" trandisp=\"noop\" app=\"icmp6/143/0\" duration=60 sentbyte=76 rcvdbyte=0 sentpkt=1 rcvdpkt=0 appcat=\"unscanned\"",
"event": {
"action": "accept",
"category": "traffic",
"code": "0001000014",
"dataset": "traffic:local",
"duration": 60000000000,
"outcome": "success",
"timezone": "+0200"
},
"@timestamp": "2020-10-13T11:02:14.900309Z",
"action": {
"name": "accept",
"outcome": "success",
"target": "network-traffic",
"type": "local"
},
"destination": {
"address": "12192.0.2.116",
"bytes": 0,
"packets": 0
},
"fortinet": {
"fortigate": {
"event": {
"type": "traffic"
},
"nat_translation_type": "noop",
"policyid": "0",
"policytype": "local-in-policy6",
"sessionid": "1395131",
"virtual_domain": "root"
}
},
"log": {
"hostname": "abc",
"level": "notice"
},
"network": {
"application": "icmp6/143/0",
"bytes": 76,
"protocol": "icmp6/143/0",
"transport": "ipv6-icmp"
},
"observer": {
"egress": {
"interface": {
"name": "unknown0"
}
},
"hostname": "abc",
"ingress": {
"interface": {
"alias": "lan",
"name": "AVR-GUEST-AP"
}
},
"serial_number": "1"
},
"related": {
"hosts": [
"abc"
]
},
"rule": {
"category": "unscanned",
"ruleset": "local-in-policy6"
},
"source": {
"bytes": 76,
"packets": 1
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.10|00014|traffic:local accept|3|deviceExternalId=FGVM2V0000171868 FortinetFortiGatelogid=0001000014 cat=traffic:local FortinetFortiGatesubtype=local FortinetFortiGatelevel=notice FortinetFortiGatevd=root FortinetFortiGateeventtime=1602663098 src=1.1.1.1 deviceInboundInterface=port1 FortinetFortiGatesrcintfrole=undefined dst=192.0.2.1 deviceOutboundInterface=root FortinetFortiGatedstintfrole=undefined externalId=4887198 proto=1 FortinetFortiGateaction=accept FortinetFortiGatepolicyid=0 FortinetFortiGatepolicytype=local-in-policy app=icmp/8/0 FortinetFortiGatedstcountry=Reserved FortinetFortiGatesrccountry=China FortinetFortiGatetrandisp=noop FortinetFortiGateapp=icmp/8/0 FortinetFortiGateduration=61 out=84 in=84 FortinetFortiGatesentpkt=1 FortinetFortiGatercvdpkt=1 FortinetFortiGateappcat=unscanned",
"event": {
"action": "accept",
"category": "traffic",
"code": "0001000014",
"dataset": "traffic:local",
"duration": 61000000000,
"outcome": "success"
},
"@timestamp": "2020-10-14T08:11:38Z",
"action": {
"name": "accept",
"outcome": "success",
"target": "network-traffic",
"type": "local"
},
"destination": {
"address": "192.0.2.1",
"bytes": 84,
"ip": "192.0.2.1",
"packets": 1
},
"fortinet": {
"fortigate": {
"nat_translation_type": "noop",
"policyid": "0",
"policytype": "local-in-policy",
"virtual_domain": "root"
}
},
"log": {
"level": "notice"
},
"network": {
"application": "icmp/8/0",
"bytes": 168,
"protocol": "icmp/8/0",
"transport": "icmp"
},
"observer": {
"egress": {
"interface": {
"name": "root"
}
},
"ingress": {
"interface": {
"name": "port1"
}
},
"serial_number": "FGVM2V0000171868",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.10"
},
"related": {
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"rule": {
"category": "unscanned",
"ruleset": "local-in-policy"
},
"source": {
"address": "1.1.1.1",
"bytes": 84,
"geo": {
"country_name": "China"
},
"ip": "1.1.1.1",
"packets": 1
}
}
{
"message": "time=18:58:47 devname=\"NAME_1\" devid=\"ABCDEFG123456789\" eventtime=1746291526925867188 tz=\"+0200\" logid=\"0123456789\" type=\"utm\" subtype=\"ips\" eventtype=\"malicious-url\" level=\"warning\" vd=\"Cristal\" severity=\"high\" srcip=1.2.3.4 srccountry=\"Reserved\" dstip=5.6.7.8 dstcountry=\"Reserved\" srcintf=\"Vlan15\" srcintfrole=\"lan\" dstintf=\"Vlan15\" dstintfrole=\"lan\" sessionid=1234567890 action=\"dropped\" proto=6 service=\"HTTP\" policyid=23 poluuid=\"11111111-1111-1111-1111-111111111111\" policytype=\"policy\" srcport=53335 dstport=8001 attack=\"malicious-url\" direction=\"outgoing\" msg=\"URL blocked by malicious-url-list\" profile=\"IPS_Block_Profile\" crscore=30 craction=8192 crlevel=\"high\" hostname=\"example.com\" url=\"/\" agent=\"Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/136.0.0.0 Safari/537.36 Edg/136.0.0.0\" httpmethod=\"CONNECT\"",
"event": {
"action": "dropped",
"category": "utm",
"code": "0123456789",
"outcome": "success",
"reason": "URL blocked by malicious-url-list",
"timezone": "+0200"
},
"@timestamp": "2025-05-03T16:58:46.925867Z",
"action": {
"name": "dropped",
"outcome": "success",
"outcome_reason": "URL blocked by malicious-url-list",
"target": "network-traffic",
"type": "ips"
},
"destination": {
"address": "5.6.7.8",
"domain": "example.com",
"ip": "5.6.7.8",
"port": 8001
},
"fortinet": {
"fortigate": {
"attack": {
"name": "malicious-url"
},
"event": {
"severity": "high",
"type": "utm"
},
"policyid": "23",
"policytype": "policy",
"poluuid": "11111111-1111-1111-1111-111111111111",
"security_profile": "IPS_Block_Profile",
"sessionid": "1234567890",
"threat": {
"level": "high",
"score": 30,
"type": 8192
},
"virtual_domain": "Cristal"
}
},
"http": {
"request": {
"method": "CONNECT"
}
},
"log": {
"hostname": "NAME_1",
"level": "warning"
},
"network": {
"direction": "outbound",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "lan",
"name": "Vlan15"
}
},
"hostname": "NAME_1",
"ingress": {
"interface": {
"alias": "lan",
"name": "Vlan15"
}
},
"serial_number": "ABCDEFG123456789"
},
"related": {
"hosts": [
"NAME_1",
"example.com"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"rule": {
"ruleset": "policy"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 53335
},
"url": {
"original": "/",
"path": "/"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Edge",
"original": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/136.0.0.0 Safari/537.36 Edg/136.0.0.0",
"os": {
"name": "Windows",
"version": "10"
},
"version": "136.0.0"
}
}
{
"message": " time=14:22:37 devname=\"abc\" devid=\"1\" logid=\"0000000013\" type=\"traffic\" subtype=\"forward\" level=\"notice\" vd=\"ROUTER\" eventtime=1602591758311908837 tz=\"+0200\" srcip=1.1.1.1 identifier=29027 srcintf=\"test1\" srcintfrole=\"undefined\" dstip=192.0.2.1 dstintf=\"test\" dstintfrole=\"undefined\" sessionid=3558919660 proto=1 action=\"accept\" policyid=637 policytype=\"policy\" poluuid=\"b23818a6-8f49-51ea-9db7-4e4965a3483c\" service=\"PING\" dstcountry=\"Reserved\" srccountry=\"Reserved\" trandisp=\"noop\" duration=64 sentbyte=420 rcvdbyte=420 sentpkt=5 rcvdpkt=5 appcat=\"unscanned\"",
"event": {
"action": "accept",
"category": "traffic",
"code": "0000000013",
"dataset": "traffic:forward",
"duration": 64000000000,
"outcome": "success",
"timezone": "+0200"
},
"@timestamp": "2020-10-13T12:22:38.311909Z",
"action": {
"name": "accept",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "192.0.2.1",
"bytes": 420,
"ip": "192.0.2.1",
"packets": 5
},
"fortinet": {
"fortigate": {
"event": {
"type": "traffic"
},
"nat_translation_type": "noop",
"policyid": "637",
"policytype": "policy",
"poluuid": "b23818a6-8f49-51ea-9db7-4e4965a3483c",
"sessionid": "3558919660",
"virtual_domain": "ROUTER"
}
},
"log": {
"hostname": "abc",
"level": "notice"
},
"network": {
"bytes": 840,
"protocol": "ping",
"transport": "icmp"
},
"observer": {
"egress": {
"interface": {
"name": "test"
}
},
"hostname": "abc",
"ingress": {
"interface": {
"name": "test1"
}
},
"serial_number": "1"
},
"related": {
"hosts": [
"abc"
],
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"rule": {
"category": "unscanned",
"ruleset": "policy"
},
"source": {
"address": "1.1.1.1",
"bytes": 420,
"ip": "1.1.1.1",
"packets": 5
}
}
{
"message": "eventtime=1741264760483566820 tz=\"+0100\" logid=\"0116047301\" type=\"event\" subtype=\"rest-api\" level=\"information\" vd=\"root\" logdesc=\"REST API request success\" user=\"user1\" ui=\"GUI(1.2.3.4)\" method=\"GET\" path=\"system.usb-log\" status=\"200\" url=\"/api/v2/monitor/system/usb-log?https://example.com/\"",
"event": {
"category": "event",
"code": "0116047301",
"outcome": "200",
"provider": "GET",
"timezone": "+0100"
},
"@timestamp": "2025-03-06T12:39:20.483567Z",
"action": {
"outcome": "200",
"type": "rest-api"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"virtual_domain": "root"
}
},
"http": {
"request": {
"method": "GET"
}
},
"log": {
"description": "REST API request success",
"level": "information"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"user": {
"name": "user1"
}
},
"url": {
"original": "/api/v2/monitor/system/usb-log?https://example.com/",
"path": "/api/v2/monitor/system/usb-log",
"query": "https://example.com/"
},
"user": {
"name": "user1"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.4|32021|event:system login failed|7|deviceExternalId=FGVM2V0000171868 FortinetFortiGatelogid=0100032021 cat=event:system FortinetFortiGatesubtype=system FortinetFortiGatelevel=alert FortinetFortiGatevd=root FortinetFortiGateeventtime=1579172447 FortinetFortiGatelogdesc=Admin login disabled sproc=1.1.1.1 FortinetFortiGateaction=login outcome=failed reason=exceed_limit msg=Login disabled from IP 1.1.1.1 for 60 seconds because of 3 bad attempts",
"event": {
"action": "login",
"category": "event",
"code": "0100032021",
"dataset": "event:system",
"outcome": "failure",
"reason": "exceed_limit"
},
"@timestamp": "2020-01-16T11:00:47Z",
"action": {
"name": "login",
"outcome": "failure",
"outcome_reason": "Login disabled from IP 1.1.1.1 for 60 seconds because of 3 bad attempts",
"type": "system"
},
"fortinet": {
"fortigate": {
"virtual_domain": "root"
}
},
"log": {
"description": "Admin login disabled",
"level": "alert"
},
"observer": {
"serial_number": "FGVM2V0000171868",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.4"
},
"related": {
"ip": [
"1.1.1.1"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.10|39943|event:vpn ssl-new-con|2|deviceExternalId=FGT3HD3916803645 FTNTFGTlogid=0101039943 cat=event:vpn FTNTFGTsubtype=vpn FTNTFGTlevel=information FTNTFGTvd=root FTNTFGTeventtime=1637338258 FTNTFGTlogdesc=SSL VPN new connection act=ssl-new-con FTNTFGTtunneltype=ssl FTNTFGTtunnelid=0 dst=192.0.2.1 duser=N/A FTNTFGTgroup=N/A FTNTFGTdst_host=N/A reason=N/A msg=SSL new connection",
"event": {
"action": "ssl-new-con",
"category": "event",
"code": "0101039943",
"dataset": "event:vpn",
"outcome": "success",
"reason": "SSL new connection"
},
"@timestamp": "2021-11-19T16:10:58Z",
"action": {
"name": "ssl-new-con",
"outcome": "success",
"outcome_reason": "SSL new connection",
"type": "vpn"
},
"destination": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"fortinet": {
"fortigate": {
"tunnel": {
"id": "0",
"type": "ssl"
},
"virtual_domain": "root"
}
},
"log": {
"description": "SSL VPN new connection",
"level": "information"
},
"observer": {
"serial_number": "FGT3HD3916803645",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.10"
},
"related": {
"ip": [
"192.0.2.1"
]
}
}
{
"message": "0|Fortinet|FortiGate-100F|7.2.8,build1639 (GA)|0100032001|system event login|4|start=Mar 06 2025 13:38:52 logver=1111111 deviceExternalId=devExtID dvchost=TESTHOST vd=root eventtime=1741264732502103430 tz=+0100 logid=0100032001 cat=event subtype=system deviceSeverity=information logdesc=Admin login successful sn=1741264732 duser=admin sproc=ssh(1.2.3.4) method=ssh src=1.2.3.4 dst=192.0.2.1 act=login status=success reason=none profile=super_admin msg=Administrator admin logged in successfully from ssh(1.2.3.4) tz=\"+0000\"",
"event": {
"action": "login",
"category": "event",
"code": "0100032001",
"dataset": "event:system",
"outcome": "success",
"provider": "ssh",
"reason": "none",
"timezone": "+0100"
},
"@timestamp": "2025-03-06T12:38:52.502104Z",
"action": {
"name": "login",
"outcome": "success",
"outcome_reason": "Administrator admin logged in successfully from ssh(1.2.3.4)",
"target": "network-traffic",
"type": "system"
},
"destination": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"user": {
"name": "admin"
}
},
"fortinet": {
"fortigate": {
"log_version": "1111111",
"security_profile": "super_admin",
"sn": "1741264732",
"virtual_domain": "root"
}
},
"log": {
"description": "Admin login successful"
},
"network": {
"protocol": "ssh"
},
"observer": {
"serial_number": "devExtID",
"type": "FortiGate-100F",
"vendor": "Fortinet",
"version": "7.2.8,build1639 (GA)"
},
"related": {
"ip": [
"1.2.3.4",
"192.0.2.1"
],
"user": [
"admin"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
}
}
{
"message": "0|Fortinet|FortiGate-100F|7.2.8,build1639 (GA)|0100032001|system event login|4|start=Mar 06 2025 13:38:52 logver=702081639 deviceExternalId=FGTESTID dvchost=FGTESTHOST vd=root eventtime=1741264732502103430 tz=+0100 logid=0100032001 cat=event subtype=system deviceSeverity=information logdesc=Admin login successful sn=1741264732 duser=test sproc=ssh(1.2.3.4) method=ssh src=1.2.3.4 dst=3.4.5.6 act=login status=success reason=none profile=super_admin msg=Administrator test logged in successfully from ssh(1.2.3.4) tz=\"+0000\"\ntime=13:39:08 devname=\"testHost\" devid=\"testSerialNumber\" eventtime=1741264747895826299 tz=\"+0100\" logid=\"0100032003\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"root\" logdesc=\"Admin logout successful\" sn=\"1741264747\" user=\"user1\" ui=\"https(5.6.7.8)\" method=\"https\" srcip=5.6.7.8 dstip=4.5.6.7 action=\"logout\" status=\"success\" duration=0 reason=\"exit\" msg=\"Administrator user1 logged out from https(5.6.7.8)\"",
"event": {
"action": "login",
"category": "event",
"code": "0100032001",
"dataset": "event:system",
"outcome": "success",
"provider": "ssh",
"reason": "none",
"timezone": "+0100"
},
"@timestamp": "2025-03-06T12:38:52.502104Z",
"action": {
"name": "login",
"outcome": "success",
"outcome_reason": "Administrator test logged in successfully from ssh(1.2.3.4)",
"target": "network-traffic",
"type": "system"
},
"destination": {
"address": "4.5.6.7",
"ip": "3.4.5.6",
"user": {
"name": "test"
}
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"log_version": "702081639",
"security_profile": "super_admin",
"sn": "1741264732",
"virtual_domain": "root"
}
},
"log": {
"description": "Admin login successful",
"hostname": "testHost",
"level": "information"
},
"network": {
"protocol": "ssh"
},
"observer": {
"hostname": "testHost",
"serial_number": "testSerialNumber",
"type": "FortiGate-100F",
"vendor": "Fortinet",
"version": "7.2.8,build1639 (GA)"
},
"related": {
"hosts": [
"testHost"
],
"ip": [
"1.2.3.4",
"3.4.5.6"
],
"user": [
"test",
"user1"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "time=13:39:08 devname=\"testHostname\" devid=\"testSerialNumber\" eventtime=1741264747895826299 tz=\"+0100\" logid=\"0100032003\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"root\" logdesc=\"Admin logout successful\" sn=\"1741264747\" user=\"testUser\" ui=\"https(3.4.5.6)\" method=\"https\" srcip=3.4.5.6 dstip=1.2.3.4 action=\"logout\" status=\"success\" duration=0 reason=\"exit\" msg=\"Administrator testUser logged out from https(3.4.5.6)\"",
"event": {
"action": "logout",
"category": "event",
"code": "0100032003",
"dataset": "event:system",
"outcome": "success",
"provider": "https",
"reason": "exit",
"timezone": "+0100"
},
"@timestamp": "2025-03-06T12:39:07.895826Z",
"action": {
"name": "logout",
"outcome": "success",
"outcome_reason": "Administrator testUser logged out from https(3.4.5.6)",
"target": "network-traffic",
"type": "system"
},
"destination": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"sn": "1741264747",
"virtual_domain": "root"
}
},
"log": {
"description": "Admin logout successful",
"hostname": "testHostname",
"level": "information"
},
"network": {
"protocol": "https"
},
"observer": {
"hostname": "testHostname",
"serial_number": "testSerialNumber"
},
"related": {
"hosts": [
"testHostname"
],
"ip": [
"1.2.3.4",
"3.4.5.6"
],
"user": [
"testUser"
]
},
"source": {
"address": "3.4.5.6",
"ip": "3.4.5.6",
"user": {
"name": "testUser"
}
},
"user": {
"name": "testUser"
}
}
{
"message": "time=13:39:08 devname=\"TESTDEVNAME\" devid=\"TESTDEVID\" eventtime=1741264747895826299 tz=\"+0100\" logid=\"0100032003\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"root\" logdesc=\"Admin logout successful\" sn=\"1741264747\" user=\"user1\" ui=\"https(1.2.3.4)\" method=\"https\" srcip=1.2.3.4 dstip=192.0.2.1 action=\"logout\" status=\"success\" duration=0 reason=\"exit\" msg=\"Administrator user1 logged out from https(1.2.3.4)\"",
"event": {
"action": "logout",
"category": "event",
"code": "0100032003",
"dataset": "event:system",
"outcome": "success",
"provider": "https",
"reason": "exit",
"timezone": "+0100"
},
"@timestamp": "2025-03-06T12:39:07.895826Z",
"action": {
"name": "logout",
"outcome": "success",
"outcome_reason": "Administrator user1 logged out from https(1.2.3.4)",
"target": "network-traffic",
"type": "system"
},
"destination": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"sn": "1741264747",
"virtual_domain": "root"
}
},
"log": {
"description": "Admin logout successful",
"hostname": "TESTDEVNAME",
"level": "information"
},
"network": {
"protocol": "https"
},
"observer": {
"hostname": "TESTDEVNAME",
"serial_number": "TESTDEVID"
},
"related": {
"hosts": [
"TESTDEVNAME"
],
"ip": [
"1.2.3.4",
"192.0.2.1"
],
"user": [
"user1"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "time=12:35:04 devname=\"DEVNAME01\" devid=\"FGT123456ABCDEF\" eventtime=1748601303656994360 tz=\"+0200\" logid=\"0123456789\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"root\" logdesc=\"Attribute configured\" user=\"admin\" ui=\"jsconsole(1.2.3.4)\" action=\"Edit\" cfgtid=987654321 cfgpath=\"system.settings\" cfgattr=\"gui-sslvpn[disable->enable]\" msg=\"Edit system.settings \"",
"event": {
"action": "Edit",
"category": "event",
"code": "0123456789",
"dataset": "event:system",
"outcome": "success",
"reason": "Edit system.settings",
"timezone": "+0200"
},
"@timestamp": "2025-05-30T10:35:03.656994Z",
"action": {
"name": "Edit",
"outcome": "success",
"outcome_reason": "Edit system.settings",
"type": "system"
},
"fortinet": {
"fortigate": {
"cfgattr": "gui-sslvpn[disable->enable]",
"cfgpath": "system.settings",
"cfgtid": "987654321",
"event": {
"type": "event"
},
"virtual_domain": "root"
}
},
"log": {
"description": "Attribute configured",
"hostname": "DEVNAME01",
"level": "information"
},
"observer": {
"hostname": "DEVNAME01",
"serial_number": "FGT123456ABCDEF"
},
"related": {
"hosts": [
"DEVNAME01"
],
"ip": [
"1.2.3.4"
],
"user": [
"admin"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"user": {
"name": "admin"
}
},
"user": {
"name": "admin"
}
}
{
"message": "time=12:35:04 devname=\"TESTDEVNAME\" devid=\"TESTDEVID\" eventtime=1748601303656994360 tz=\"+0200\" logid=\"0100044546\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"root\" logdesc=\"Attribute configured\" user=\"admin\" ui=\"jsconsole(1.2.3.4)\" action=\"Edit\" cfgtid=153616384 cfgpath=\"system.settings\" cfgattr=\"gui-sslvpn[disable->enable]\" msg=\"Edit system.settings \"",
"event": {
"action": "Edit",
"category": "event",
"code": "0100044546",
"dataset": "event:system",
"outcome": "success",
"reason": "Edit system.settings",
"timezone": "+0200"
},
"@timestamp": "2025-05-30T10:35:03.656994Z",
"action": {
"name": "Edit",
"outcome": "success",
"outcome_reason": "Edit system.settings",
"type": "system"
},
"fortinet": {
"fortigate": {
"cfgattr": "gui-sslvpn[disable->enable]",
"cfgpath": "system.settings",
"cfgtid": "153616384",
"event": {
"type": "event"
},
"virtual_domain": "root"
}
},
"log": {
"description": "Attribute configured",
"hostname": "TESTDEVNAME",
"level": "information"
},
"observer": {
"hostname": "TESTDEVNAME",
"serial_number": "TESTDEVID"
},
"related": {
"hosts": [
"TESTDEVNAME"
],
"ip": [
"1.2.3.4"
],
"user": [
"admin"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"user": {
"name": "admin"
}
},
"user": {
"name": "admin"
}
}
{
"message": "time=16:22:20 timestamp=1762528940 devname=\"FortiAuthenticator\" devid=\"TEST_DEV_ID\" vd=\"root\" itime=1762528940 faclogindex=\"111111111\" logid=\"20320\" logdesc=\"AUTH_FAIL_USER_TEST_EVENT_DAT\" type=\"event\" subtype=\"Authentication\" level=\"information\" user=\"user1\" nas=\"1.2.3.4\" userip=192.0.2.1 action=\"Authentication\" status=\"Failed\" msg=\"User authentication from 192.0.2.1 (mschap) with no token failed: user not found\" tz=\"+0100\"",
"event": {
"action": "Authentication",
"category": "event",
"code": "20320",
"outcome": "Failed",
"reason": "User authentication from 192.0.2.1 (mschap) with no token failed: user not found",
"start": "2025-11-07T15:22:20Z",
"timezone": "+0100"
},
"@timestamp": "2025-11-07T14:22:20Z",
"action": {
"name": "Authentication",
"outcome": "Failed",
"outcome_reason": "User authentication from 192.0.2.1 (mschap) with no token failed: user not found",
"type": "Authentication"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"virtual_domain": "root"
}
},
"log": {
"description": "AUTH_FAIL_USER_TEST_EVENT_DAT",
"hostname": "FortiAuthenticator",
"level": "information"
},
"observer": {
"hostname": "FortiAuthenticator",
"serial_number": "TEST_DEV_ID"
},
"related": {
"hosts": [
"FortiAuthenticator"
],
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "time=16:22:20 timestamp=1762528940 devname=\"FortiAuthenticator\" devid=\"TEST_DEVICE_ID\" vd=\"root\" itime=1762528940 faclogindex=\"8321046\" logid=\"20320\" logdesc=\"AUTH_FAIL_USER_TEST_EVENT\" type=\"event\" subtype=\"Authentication\" level=\"information\" user=\"user1\" nas=\"2.3.4.5\" userip=192.0.2.1 action=\"Authentication\" status=\"Failed\" msg=\"User authentication from 192.0.2.1 (mschap) with no token failed: user not found\" tz=\"+0100\"",
"event": {
"action": "Authentication",
"category": "event",
"code": "20320",
"outcome": "Failed",
"reason": "User authentication from 192.0.2.1 (mschap) with no token failed: user not found",
"start": "2025-11-07T15:22:20Z",
"timezone": "+0100"
},
"@timestamp": "2025-11-07T14:22:20Z",
"action": {
"name": "Authentication",
"outcome": "Failed",
"outcome_reason": "User authentication from 192.0.2.1 (mschap) with no token failed: user not found",
"type": "Authentication"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"virtual_domain": "root"
}
},
"log": {
"description": "AUTH_FAIL_USER_TEST_EVENT",
"hostname": "FortiAuthenticator",
"level": "information"
},
"observer": {
"hostname": "FortiAuthenticator",
"serial_number": "TEST_DEVICE_ID"
},
"related": {
"hosts": [
"FortiAuthenticator"
],
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "time=16:22:20 timestamp=1762528940 devname=\"FortiAuthenticator\" devid=\"TEST_DEVICE_ID\" vd=\"root\" itime=1762528941 faclogindex=\"8321052\" logid=\"20320\" logdesc=\"AUTH_FAIL_USER_TEST_EVENT\" type=\"event\" subtype=\"Authentication\" level=\"information\" user=\"user1\" nas=\"2.3.4.5\" userip=192.0.2.1 action=\"Authentication\" status=\"Failed\" msg=\"User authentication from 192.0.2.1 (chap) with no token failed: user not found\" tz=\"+0100\"",
"event": {
"action": "Authentication",
"category": "event",
"code": "20320",
"outcome": "Failed",
"reason": "User authentication from 192.0.2.1 (chap) with no token failed: user not found",
"start": "2025-11-07T15:22:21Z",
"timezone": "+0100"
},
"@timestamp": "2025-11-07T14:22:20Z",
"action": {
"name": "Authentication",
"outcome": "Failed",
"outcome_reason": "User authentication from 192.0.2.1 (chap) with no token failed: user not found",
"type": "Authentication"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"virtual_domain": "root"
}
},
"log": {
"description": "AUTH_FAIL_USER_TEST_EVENT",
"hostname": "FortiAuthenticator",
"level": "information"
},
"observer": {
"hostname": "FortiAuthenticator",
"serial_number": "TEST_DEVICE_ID"
},
"related": {
"hosts": [
"FortiAuthenticator"
],
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "time=13:53:24 devname=\"TEST_DEV_NAME\" devid=\"DEVID1111111\" eventtime=1749038004142040029 tz=\"+0200\" logid=\"0100044547\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"root\" logdesc=\"Object attribute configured\" user=\"admin\" ui=\"GUI(1.1.1.1)\" action=\"Add\" cfgtid=1231232131 uuid=\"0000000-413a-51f0-3994-9f8f05c1432f\" cfgpath=\"firewall.policy\" cfgobj=\"6\" cfgattr=\"name[vpn_remote_0]srcintf[TestTest]dstintf[internal]action[accept]srcaddr[TestTest]dstaddr[TestTest]schedule[always]service[ALL]comments[VPN: TestTest (Created by VPN wizard)]\" msg=\"Add firewall.policy 6\"",
"event": {
"action": "Add",
"category": "event",
"code": "0100044547",
"dataset": "event:system",
"outcome": "success",
"reason": "Add firewall.policy 6",
"timezone": "+0200"
},
"@timestamp": "2025-06-04T11:53:24.142040Z",
"action": {
"name": "Add",
"outcome": "success",
"outcome_reason": "Add firewall.policy 6",
"type": "system"
},
"fortinet": {
"fortigate": {
"cfgattr": "name[vpn_remote_0]srcintf[TestTest]dstintf[internal]action[accept]srcaddr[TestTest]dstaddr[TestTest]schedule[always]service[ALL]comments[VPN: TestTest (Created by VPN wizard)]",
"cfgpath": "firewall.policy",
"cfgtid": "1231232131",
"event": {
"type": "event"
},
"poluuid": "0000000-413a-51f0-3994-9f8f05c1432f",
"virtual_domain": "root"
}
},
"log": {
"description": "Object attribute configured",
"hostname": "TEST_DEV_NAME",
"level": "information"
},
"observer": {
"hostname": "TEST_DEV_NAME",
"serial_number": "DEVID1111111"
},
"related": {
"hosts": [
"TEST_DEV_NAME"
],
"ip": [
"1.1.1.1"
],
"user": [
"admin"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"user": {
"name": "admin"
}
},
"user": {
"name": "admin"
}
}
{
"message": "time=10:24:24 devname=\"TESTDEVNAME\" devid=\"TESTTEST0000000\" eventtime=1752819965 tz=\"+0200\" logid=\"010000000000\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"root\" logdesc=\"Object attribute configured\" user=\"user1\" ui=\"GUI(192.0.2.1)\" action=\"Add\" cfgtid=1111111 uuid=\"0000000000-413a-51f0-3994-9f8f05c1432f\" cfgpath=\"firewall.policy\" cfgobj=\"6\" cfgattr=\"name[vpn_TestTest_remote_0]srcintf[TestTest]dstintf[internal]action[accept]srcaddr[TestTest_remote]dstaddr[TestTest_local]schedule[always]service[ALL]comments[VPN: TestTest (Created by VPN wizard)]\" msg=\"Add firewall.policy 6\"",
"event": {
"action": "Add",
"category": "event",
"code": "010000000000",
"dataset": "event:system",
"outcome": "success",
"reason": "Add firewall.policy 6",
"timezone": "+0200"
},
"@timestamp": "2025-07-18T06:26:05Z",
"action": {
"name": "Add",
"outcome": "success",
"outcome_reason": "Add firewall.policy 6",
"type": "system"
},
"fortinet": {
"fortigate": {
"cfgattr": "name[vpn_TestTest_remote_0]srcintf[TestTest]dstintf[internal]action[accept]srcaddr[TestTest_remote]dstaddr[TestTest_local]schedule[always]service[ALL]comments[VPN: TestTest (Created by VPN wizard)]",
"cfgpath": "firewall.policy",
"cfgtid": "1111111",
"event": {
"type": "event"
},
"poluuid": "0000000000-413a-51f0-3994-9f8f05c1432f",
"virtual_domain": "root"
}
},
"log": {
"description": "Object attribute configured",
"hostname": "TESTDEVNAME",
"level": "information"
},
"observer": {
"hostname": "TESTDEVNAME",
"serial_number": "TESTTEST0000000"
},
"related": {
"hosts": [
"TESTDEVNAME"
],
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "time=10:33:11 devname=\"FW-TTTTTTTT-1\" devid=\"TESTDEV21111111\" eventtime=1693557190787280122 tz=\"+0200\" logid=\"0100044547\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"TEST-APP\" logdesc=\"Object attribute configured\" user=\"admin\" ui=\"RESTAPI(1.1.1.1)\" action=\"Add\" cfgtid=111111111 cfgpath=\"firewall.policy\" cfgobj=\"95\" cfgattr=\"uuid[0000000000-48a2-51ee-9a4e-d49ca8f62bfb]srcintf[Z_INTERCO]dstintf[Z_APP]action[accept]srcaddr[Nw-3.3.3.3-AdministrateursDN]dstaddr[Host-2.2.2.2-VIP_PROD]schedule[always]service[HTTPS PING]utm-status[enable]ssl-ssh-profile[certificate-inspection]ips-sensor[Sensor_Web]logtraffic[all]\" msg=\"Add firewall.policy 95\"",
"event": {
"action": "Add",
"category": "event",
"code": "0100044547",
"dataset": "event:system",
"outcome": "success",
"reason": "Add firewall.policy 95",
"timezone": "+0200"
},
"@timestamp": "2023-09-01T08:33:10.787280Z",
"action": {
"name": "Add",
"outcome": "success",
"outcome_reason": "Add firewall.policy 95",
"type": "system"
},
"fortinet": {
"fortigate": {
"cfgattr": "uuid[0000000000-48a2-51ee-9a4e-d49ca8f62bfb]srcintf[Z_INTERCO]dstintf[Z_APP]action[accept]srcaddr[Nw-3.3.3.3-AdministrateursDN]dstaddr[Host-2.2.2.2-VIP_PROD]schedule[always]service[HTTPS PING]utm-status[enable]ssl-ssh-profile[certificate-inspection]ips-sensor[Sensor_Web]logtraffic[all]",
"cfgpath": "firewall.policy",
"cfgtid": "111111111",
"event": {
"type": "event"
},
"virtual_domain": "TEST-APP"
}
},
"log": {
"description": "Object attribute configured",
"hostname": "FW-TTTTTTTT-1",
"level": "information"
},
"observer": {
"hostname": "FW-TTTTTTTT-1",
"serial_number": "TESTDEV21111111"
},
"related": {
"hosts": [
"FW-TTTTTTTT-1"
],
"ip": [
"1.1.1.1"
],
"user": [
"admin"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"user": {
"name": "admin"
}
},
"user": {
"name": "admin"
}
}
{
"message": "time=09:47:39 devname=\"TESTDEVNAME\" devid=\"TESTDEVID01\" logid=\"0100044547\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"Part\" eventtime=1645001259 logdesc=\"Object attribute configured\" user=\"user1\" ui=\"fgfm_tunnel\" action=\"Add\" cfgtid=1623130112 cfgpath=\"firewall.address\" cfgobj=\"TEST1.1.1.1\" cfgattr=\"uuid[00000000-8f03-51ec-de75-17ef43f88c98]subnet[2.1.1.1 255.255.255.255]\" msg=\"Add firewall.address B2.1.1.1\"",
"event": {
"action": "Add",
"category": "event",
"code": "0100044547",
"dataset": "event:system",
"outcome": "success",
"reason": "Add firewall.address B2.1.1.1"
},
"@timestamp": "2022-02-16T08:47:39Z",
"action": {
"name": "Add",
"outcome": "success",
"outcome_reason": "Add firewall.address B2.1.1.1",
"type": "system"
},
"fortinet": {
"fortigate": {
"cfgattr": "uuid[00000000-8f03-51ec-de75-17ef43f88c98]subnet[2.1.1.1 255.255.255.255]",
"cfgpath": "firewall.address",
"cfgtid": "1623130112",
"event": {
"type": "event"
},
"virtual_domain": "Part"
}
},
"log": {
"description": "Object attribute configured",
"hostname": "TESTDEVNAME",
"level": "information"
},
"observer": {
"hostname": "TESTDEVNAME",
"serial_number": "TESTDEVID01"
},
"related": {
"hosts": [
"TESTDEVNAME"
],
"user": [
"user1"
]
},
"source": {
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "time=15:27:40 devname=\"TEST_DEV_NAME\" devid=\"TEST_DEV_ID\" logid=\"0100044546\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"root\" eventtime=1647440860 logdesc=\"Attribute configured\" user=\"user1\" ui=\"ssh(192.0.2.1)\" action=\"Edit\" cfgtid=613613570 cfgpath=\"log.syslogd.setting\" cfgattr=\"server[1.2.1.1->1.2.2.2]\" msg=\"Edit log.syslogd.setting \"",
"event": {
"action": "Edit",
"category": "event",
"code": "0100044546",
"dataset": "event:system",
"outcome": "success",
"reason": "Edit log.syslogd.setting"
},
"@timestamp": "2022-03-16T14:27:40Z",
"action": {
"name": "Edit",
"outcome": "success",
"outcome_reason": "Edit log.syslogd.setting",
"type": "system"
},
"fortinet": {
"fortigate": {
"cfgattr": "server[1.2.1.1->1.2.2.2]",
"cfgpath": "log.syslogd.setting",
"cfgtid": "613613570",
"event": {
"type": "event"
},
"virtual_domain": "root"
}
},
"log": {
"description": "Attribute configured",
"hostname": "TEST_DEV_NAME",
"level": "information"
},
"observer": {
"hostname": "TEST_DEV_NAME",
"serial_number": "TEST_DEV_ID"
},
"related": {
"hosts": [
"TEST_DEV_NAME"
],
"ip": [
"192.0.2.1"
],
"user": [
"user1"
]
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "time=16:03:54 devname=\"TEST_DEV_NAME\" devid=\"TEST_DEV_ID\" logid=\"0100044547\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"Int\" eventtime=1668524634891048583 tz=\"+0100\" logdesc=\"Object attribute configured\" user=\"user1\" ui=\"fgfm_tunnel\" action=\"Edit\" cfgtid=146604040 cfgpath=\"firewall.policy\" cfgobj=\"506\" cfgattr=\"ips-sensor[g-default->default]application-list[g-default->default]\" msg=\"Edit firewall.policy 506\"",
"event": {
"action": "Edit",
"category": "event",
"code": "0100044547",
"dataset": "event:system",
"outcome": "success",
"reason": "Edit firewall.policy 506",
"timezone": "+0100"
},
"@timestamp": "2022-11-15T15:03:54.891049Z",
"action": {
"name": "Edit",
"outcome": "success",
"outcome_reason": "Edit firewall.policy 506",
"type": "system"
},
"fortinet": {
"fortigate": {
"cfgattr": "ips-sensor[g-default->default]application-list[g-default->default]",
"cfgpath": "firewall.policy",
"cfgtid": "146604040",
"event": {
"type": "event"
},
"virtual_domain": "Int"
}
},
"log": {
"description": "Object attribute configured",
"hostname": "TEST_DEV_NAME",
"level": "information"
},
"observer": {
"hostname": "TEST_DEV_NAME",
"serial_number": "TEST_DEV_ID"
},
"related": {
"hosts": [
"TEST_DEV_NAME"
],
"user": [
"user1"
]
},
"source": {
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "time=15:27:41 devname=\"TEST_DEV_NAME\" devid=\"TEST_DEV_ID\" logid=\"0100044546\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"root\" eventtime=1647440861 logdesc=\"Attribute configured\" user=\"testuser\" ui=\"ha_daemon\" action=\"Edit\" cfgtid=17898414 cfgpath=\"log.syslogd.setting\" cfgattr=\"server[1.2.1.1->1.2.2.2]\" msg=\"Edit log.syslogd.setting \"",
"event": {
"action": "Edit",
"category": "event",
"code": "0100044546",
"dataset": "event:system",
"outcome": "success",
"reason": "Edit log.syslogd.setting"
},
"@timestamp": "2022-03-16T14:27:41Z",
"action": {
"name": "Edit",
"outcome": "success",
"outcome_reason": "Edit log.syslogd.setting",
"type": "system"
},
"fortinet": {
"fortigate": {
"cfgattr": "server[1.2.1.1->1.2.2.2]",
"cfgpath": "log.syslogd.setting",
"cfgtid": "17898414",
"event": {
"type": "event"
},
"virtual_domain": "root"
}
},
"log": {
"description": "Attribute configured",
"hostname": "TEST_DEV_NAME",
"level": "information"
},
"observer": {
"hostname": "TEST_DEV_NAME",
"serial_number": "TEST_DEV_ID"
},
"related": {
"hosts": [
"TEST_DEV_NAME"
],
"user": [
"testuser"
]
},
"source": {
"user": {
"name": "testuser"
}
},
"user": {
"name": "testuser"
}
}
{
"message": "time=09:35:30 devname=\"eee-111-111-ff-11\" devid=\"FG00000000000000\" eventtime=1735202130361752831 tz=\"+0100\" logid=\"0000000011\" type=\"traffic\" subtype=\"forward\" level=\"notice\" vd=\"EFF\" srcip=1.2.3.4 srcport=10000 srcintf=\"EFF-WAN-0000\" srcintfrole=\"lan\" dstip=5.6.7.8 dstport=443 dstintf=\"EFF-DMZ-0000\" dstintfrole=\"lan\" srccountry=\"France\" dstcountry=\"France\" sessionid=400190000 proto=6 action=\"client-rst\" policyid=1018 policytype=\"policy\" poluuid=\"38fa6456-a819-51ef-3c99-000000000000000000\" service=\"HTTPS\" trandisp=\"dnat\" tranip=1.2.3.4 tranport=443 duration=6 sentbyte=100 rcvdbyte=52 sentpkt=2 rcvdpkt=1 appcat=\"unscanned\"",
"event": {
"action": "client-rst",
"category": "traffic",
"code": "0000000011",
"dataset": "traffic:forward",
"duration": 6000000000,
"outcome": "success",
"timezone": "+0100"
},
"@timestamp": "2024-12-26T08:35:30.361753Z",
"action": {
"name": "client-rst",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "5.6.7.8",
"bytes": 52,
"geo": {
"country_name": "France"
},
"ip": "5.6.7.8",
"nat": {
"ip": "1.2.3.4"
},
"packets": 1,
"port": 443
},
"fortinet": {
"fortigate": {
"event": {
"type": "traffic"
},
"nat_translation_type": "dnat",
"policyid": "1018",
"policytype": "policy",
"poluuid": "38fa6456-a819-51ef-3c99-000000000000000000",
"sessionid": "400190000",
"virtual_domain": "EFF"
}
},
"log": {
"hostname": "eee-111-111-ff-11",
"level": "notice"
},
"network": {
"bytes": 152,
"protocol": "https",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "lan",
"name": "EFF-DMZ-0000"
}
},
"hostname": "eee-111-111-ff-11",
"ingress": {
"interface": {
"alias": "lan",
"name": "EFF-WAN-0000"
}
},
"serial_number": "FG00000000000000"
},
"related": {
"hosts": [
"eee-111-111-ff-11"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"rule": {
"category": "unscanned",
"ruleset": "policy"
},
"source": {
"address": "1.2.3.4",
"bytes": 100,
"geo": {
"country_name": "France"
},
"ip": "1.2.3.4",
"packets": 2,
"port": 10000
}
}
{
"message": "time=14:53:11 devname=\"FFF00D_TEST02\" devid=\"FGT3HD300000000\" eventtime=1735000001620000000 tz=\"+0100\" logid=\"0000000010\" type=\"traffic\" subtype=\"forward\" level=\"notice\" vd=\"root\" srcip=1.2.3.4 srcport=50000 srcintf=\"ssl.root\" srcintfrole=\"undefined\" dstip=192.0.2.1 dstport=80 dstintf=\"VPNM-TEST\" dstintfrole=\"undefined\" srccountry=\"Reserved\" dstcountry=\"Reserved\" sessionid=100100046 proto=6 action=\"close\" policyid=274 policytype=\"policy\" poluuid=\"ac8ed64c-54e7-51eb-3525-d610000000000\" user=\"user1\" group=\"TEST-SAML\" authserver=\"azure-saml\" service=\"HTTP\" trandisp=\"snat\" transip=192.0.2.1 transport=50066 duration=7 sentbyte=18800 rcvdbyte=7900 sentpkt=30 rcvdpkt=29 vpn=\"VPNM-TEST\" vpntype=\"ipsec-static\" appcat=\"unscanned\"",
"event": {
"action": "close",
"category": "traffic",
"code": "0000000010",
"dataset": "traffic:forward",
"duration": 7000000000,
"outcome": "success",
"timezone": "+0100"
},
"@timestamp": "2024-12-24T00:26:41.620000Z",
"action": {
"name": "close",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "192.0.2.1",
"bytes": 7900,
"ip": "192.0.2.1",
"packets": 29,
"port": 80
},
"fortinet": {
"fortigate": {
"event": {
"type": "traffic"
},
"nat_translation_type": "snat",
"policyid": "274",
"policytype": "policy",
"poluuid": "ac8ed64c-54e7-51eb-3525-d610000000000",
"sessionid": "100100046",
"virtual_domain": "root",
"vpntype": "ipsec-static"
}
},
"group": {
"name": "TEST-SAML"
},
"log": {
"hostname": "FFF00D_TEST02",
"level": "notice"
},
"network": {
"bytes": 26700,
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "VPNM-TEST"
}
},
"hostname": "FFF00D_TEST02",
"ingress": {
"interface": {
"name": "ssl.root"
}
},
"serial_number": "FGT3HD300000000"
},
"related": {
"hosts": [
"FFF00D_TEST02"
],
"ip": [
"1.2.3.4",
"192.0.2.1"
],
"user": [
"user1"
]
},
"rule": {
"category": "unscanned",
"ruleset": "policy"
},
"source": {
"address": "1.2.3.4",
"bytes": 18800,
"ip": "1.2.3.4",
"nat": {
"ip": "192.0.2.1"
},
"packets": 30,
"port": 50000,
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "timestamp=1698046849 devname=\"abc\" devid=\"1\" vd=\"root\" date=2023-10-23 time=00:40:49 eventtime=1698046849852012802 tz=\"-0700\" logid=\"0101037130\" type=\"utm\" subtype=\"ips\" eventtype=\"signature\" level=\"alert\" severity=\"low\" srcip=1.2.3.4 srccountry=\"Reserved\" dstip=192.0.2.1 dstcountry=\"Reserved\" srcintf=\"port2\" srcintfrole=\"undefined\" dstintf=\"port2\" dstintfrole=\"undefined\" sessionid=1234567890 action=\"detected\" proto=6 service=\"HTTP\" policyid=494 poluuid=\"aecacfaf-8d3f-4809-a60f-bf873e0fcab3\" policytype=\"policy\" attack=\"Qualys.Vulnerability.Scanner\" srcport=37364 dstport=80 hostname=\"example.com\" url=\"/cgi/rocket.pl?https://example.com/\" direction=\"outgoing\" attackid=45660 profile=\"Example_IPS\" ref=\"http://www.fortinet.com/ids/VID45660\" incidentserialno=1234567 msg=\"tools: Qualys.Vulnerability.Scanner\" crscore=5 craction=32768 crlevel=\"low\"\n",
"event": {
"action": "detected",
"category": "utm",
"code": "0101037130",
"outcome": "success",
"reason": "tools: Qualys.Vulnerability.Scanner",
"timezone": "-0700"
},
"@timestamp": "2023-10-23T07:40:49.852013Z",
"action": {
"name": "detected",
"outcome": "success",
"outcome_reason": "tools: Qualys.Vulnerability.Scanner",
"target": "network-traffic",
"type": "ips"
},
"destination": {
"address": "192.0.2.1",
"domain": "example.com",
"ip": "192.0.2.1",
"port": 80
},
"fortinet": {
"fortigate": {
"attack": {
"id": "45660",
"name": "Qualys.Vulnerability.Scanner"
},
"event": {
"severity": "low",
"type": "utm"
},
"policyid": "494",
"policytype": "policy",
"poluuid": "aecacfaf-8d3f-4809-a60f-bf873e0fcab3",
"security_profile": "Example_IPS",
"sessionid": "1234567890",
"threat": {
"level": "low",
"score": 5,
"type": 32768
},
"virtual_domain": "root"
}
},
"log": {
"hostname": "abc",
"level": "alert"
},
"network": {
"direction": "outbound",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port2"
}
},
"hostname": "abc",
"ingress": {
"interface": {
"name": "port2"
}
},
"serial_number": "1"
},
"related": {
"hosts": [
"abc",
"example.com"
],
"ip": [
"1.2.3.4",
"192.0.2.1"
]
},
"rule": {
"ruleset": "policy"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 37364
},
"url": {
"original": "/cgi/rocket.pl?https://example.com/",
"path": "/cgi/rocket.pl",
"query": "https://example.com/"
}
}
{
"message": "time=08:32:58 devname=\"NAME_1\" devid=\"ABCDEFG123456789\" eventtime=1746599578550052585 tz=\"+0200\" logid=\"0000000020\" type=\"traffic\" subtype=\"forward\" level=\"notice\" vd=\"Cristal\" srcip=1.2.3.4 srcport=57974 srcintf=\"Vlan15\" srcintfrole=\"lan\" dstip=5.6.7.8 dstport=7224 dstintf=\"Vlan3200\" dstintfrole=\"lan\" srccountry=\"Reserved\" dstcountry=\"Reserved\" sessionid=1234567890 proto=6 action=\"accept\" policyid=4 policytype=\"policy\" poluuid=\"11111111-1111-1111-1111-111111111111\" policyname=\"Cristal6 vers interne\" service=\"tcp/7224\" trandisp=\"noop\" duration=1697591 sentbyte=12604185928 rcvdbyte=24366746607 sentpkt=133755826 rcvdpkt=115991007 appcat=\"unscanned\" sentdelta=771825 rcvddelta=4330052",
"event": {
"action": "accept",
"category": "traffic",
"code": "0000000020",
"dataset": "traffic:forward",
"duration": 1697591000000000,
"outcome": "success",
"timezone": "+0200"
},
"@timestamp": "2025-05-07T06:32:58.550053Z",
"action": {
"name": "accept",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "5.6.7.8",
"bytes": 4330052,
"ip": "5.6.7.8",
"packets": 115991007,
"port": 7224
},
"fortinet": {
"fortigate": {
"event": {
"type": "traffic"
},
"nat_translation_type": "noop",
"policyid": "4",
"policyname": "Cristal6 vers interne",
"policytype": "policy",
"poluuid": "11111111-1111-1111-1111-111111111111",
"sessionid": "1234567890",
"total": {
"duration": 1697591000000000,
"received_bytes": 24366746607,
"sent_bytes": 12604185928,
"sent_packets": 133755826
},
"virtual_domain": "Cristal"
}
},
"log": {
"hostname": "NAME_1",
"level": "notice"
},
"network": {
"bytes": 5101877,
"protocol": "tcp/7224",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "lan",
"name": "Vlan3200"
}
},
"hostname": "NAME_1",
"ingress": {
"interface": {
"alias": "lan",
"name": "Vlan15"
}
},
"serial_number": "ABCDEFG123456789"
},
"related": {
"hosts": [
"NAME_1"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"rule": {
"category": "unscanned",
"ruleset": "policy"
},
"source": {
"address": "1.2.3.4",
"bytes": 771825,
"ip": "1.2.3.4",
"packets": 133755826,
"port": 57974
}
}
{
"message": "time=15:15:29 devname=\"TESTDEVNAME\" devid=\"TESTDEVIT\" eventtime=1758287729906413196 tz=\"+0200\" logid=\"0123456789\" type=\"utm\" subtype=\"ips\" eventtype=\"signature\" level=\"alert\" vd=\"VIRTUALDOMAIN\" severity=\"medium\" srcip=1.2.3.4 srccountry=\"Reserved\" dstip=5.6.7.8 dstcountry=\"Reserved\" srcintf=\"INTF_1\" srcintfrole=\"undefined\" dstintf=\"INTF_2\" dstintfrole=\"undefined\" sessionid=234567890 action=\"dropped\" proto=6 service=\"HTTP\" policyid=49 poluuid=\"3eee479c-acfe-4861-941a-291eb6d1360d\" policytype=\"policy\" attack=\"HTTP.Referer.Header.SQL.Injection\" srcport=57561 dstport=80 hostname=\"example.com\" url=\"/\" agent=\"Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/99.0.4844.0 Safari/537.36\" httpmethod=\"GET\" referralurl=\"https://example.com/\" direction=\"outgoing\" attackid=12345 profile=\"Sensor_Web\" ref=\"http://www.fortinet.com/ids/VID12345\" incidentserialno=11223344 msg=\"web_misc: HTTP.Referer.Header.SQL.Injection\" forwardedfor=\"9.10.11.12\" crscore=10 craction=16384 crlevel=\"medium\"",
"event": {
"action": "dropped",
"category": "utm",
"code": "0123456789",
"outcome": "success",
"reason": "web_misc: HTTP.Referer.Header.SQL.Injection",
"timezone": "+0200"
},
"@timestamp": "2025-09-19T13:15:29.906413Z",
"action": {
"name": "dropped",
"outcome": "success",
"outcome_reason": "web_misc: HTTP.Referer.Header.SQL.Injection",
"target": "network-traffic",
"type": "ips"
},
"destination": {
"address": "5.6.7.8",
"domain": "example.com",
"ip": "5.6.7.8",
"port": 80
},
"fortinet": {
"fortigate": {
"attack": {
"id": "12345",
"name": "HTTP.Referer.Header.SQL.Injection"
},
"event": {
"severity": "medium",
"type": "utm"
},
"policyid": "49",
"policytype": "policy",
"poluuid": "3eee479c-acfe-4861-941a-291eb6d1360d",
"security_profile": "Sensor_Web",
"sessionid": "234567890",
"threat": {
"level": "medium",
"score": 10,
"type": 16384
},
"virtual_domain": "VIRTUALDOMAIN"
}
},
"http": {
"request": {
"method": "GET",
"referrer": "https://example.com/"
}
},
"log": {
"hostname": "TESTDEVNAME",
"level": "alert"
},
"network": {
"direction": "outbound",
"forwarded_ip": "9.10.11.12",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "INTF_2"
}
},
"hostname": "TESTDEVNAME",
"ingress": {
"interface": {
"name": "INTF_1"
}
},
"serial_number": "TESTDEVIT"
},
"related": {
"hosts": [
"TESTDEVNAME",
"example.com"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"rule": {
"ruleset": "policy"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 57561
},
"url": {
"original": "/",
"path": "/"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Chrome",
"original": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/99.0.4844.0 Safari/537.36",
"os": {
"name": "Windows",
"version": "10"
},
"version": "99.0.4844"
}
}
{
"message": "time=16:45:21 devname=\"TEST_DEVICE\" devid=\"TEST_DEVICE_ID\" eventtime=1770824721111372922 tz=\"+0100\" logid=\"XXXXXXXXXX\" type=\"event\" subtype=\"system\" level=\"information\" vd=\"root\" logdesc=\"SSL connection failed\" dstip=N/A dstport=N/A reason=\"self-signed certificate in certificate chain\" action=\"info\" status=\"failure\" msg=\"Certificate is invalid, subject: /C=XX/ST=XXXXXXXX/L=XXXXXXXXX/O=Fortinet/OU=Certificate Authority/CN=XXXXXXXXXXXXX/emailAddress=example@example.com\"",
"event": {
"action": "info",
"category": "event",
"code": "XXXXXXXXXX",
"dataset": "event:system",
"outcome": "failure",
"reason": "self-signed certificate in certificate chain",
"timezone": "+0100"
},
"@timestamp": "2026-02-11T15:45:21.111373Z",
"action": {
"name": "info",
"outcome": "failure",
"outcome_reason": "Certificate is invalid, subject: /C=XX/ST=XXXXXXXX/L=XXXXXXXXX/O=Fortinet/OU=Certificate Authority/CN=XXXXXXXXXXXXX/emailAddress=example@example.com",
"type": "system"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"virtual_domain": "root"
}
},
"log": {
"description": "SSL connection failed",
"hostname": "TEST_DEVICE",
"level": "information"
},
"observer": {
"hostname": "TEST_DEVICE",
"serial_number": "TEST_DEVICE_ID"
},
"related": {
"hosts": [
"TEST_DEVICE"
]
}
}
{
"message": "time=14:01:16 devname=\"NAME_1\" devid=\"ABCDEFG123456789\" eventtime=1746446476968701953 tz=\"+0200\" logid=\"1234567890\" type=\"utm\" subtype=\"ips\" eventtype=\"signature\" level=\"alert\" vd=\"VD_Int\" severity=\"critical\" srcip=1.2.3.4 srccountry=\"France\" dstip=5.6.7.8 dstcountry=\"Reserved\" srcintf=\"port24\" srcintfrole=\"undefined\" dstintf=\"Vlan3194\" dstintfrole=\"lan\" sessionid=3017954790 action=\"dropped\" proto=6 service=\"SSL\" policyid=41 poluuid=\"11111111-1111-1111-1111-111111111111\" policytype=\"policy\" attack=\"OpenSSL.Heartbleed.Attack\" srcport=61087 dstport=443 hostname=\"example.com\" url=\"/\" direction=\"outgoing\" attackid=38315 profile=\"IPS_Block_Profile\" ref=\"http://www.fortinet.com/ids/VID38315\" incidentserialno=261102216 msg=\"applications: OpenSSL.Heartbleed.Attack, OpenSSL Heartbleed\" crscore=50 craction=4096 crlevel=\"critical\"",
"event": {
"action": "dropped",
"category": "utm",
"code": "1234567890",
"outcome": "success",
"reason": "applications: OpenSSL.Heartbleed.Attack, OpenSSL Heartbleed",
"timezone": "+0200"
},
"@timestamp": "2025-05-05T12:01:16.968702Z",
"action": {
"name": "dropped",
"outcome": "success",
"outcome_reason": "applications: OpenSSL.Heartbleed.Attack, OpenSSL Heartbleed",
"target": "network-traffic",
"type": "ips"
},
"destination": {
"address": "5.6.7.8",
"domain": "example.com",
"ip": "5.6.7.8",
"port": 443
},
"fortinet": {
"fortigate": {
"attack": {
"id": "38315",
"name": "OpenSSL.Heartbleed.Attack"
},
"event": {
"severity": "critical",
"type": "utm"
},
"policyid": "41",
"policytype": "policy",
"poluuid": "11111111-1111-1111-1111-111111111111",
"security_profile": "IPS_Block_Profile",
"sessionid": "3017954790",
"threat": {
"level": "critical",
"score": 50,
"type": 4096
},
"virtual_domain": "VD_Int"
}
},
"log": {
"hostname": "NAME_1",
"level": "alert"
},
"network": {
"direction": "outbound",
"protocol": "ssl",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "lan",
"name": "Vlan3194"
}
},
"hostname": "NAME_1",
"ingress": {
"interface": {
"name": "port24"
}
},
"serial_number": "ABCDEFG123456789"
},
"related": {
"hosts": [
"NAME_1",
"example.com"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"rule": {
"ruleset": "policy"
},
"source": {
"address": "1.2.3.4",
"geo": {
"country_name": "France"
},
"ip": "1.2.3.4",
"port": 61087
},
"url": {
"original": "/",
"path": "/"
}
}
{
"message": "time=08:20:44 devname=\"computer-039482\" devid=\"C10382849\" eventtime=1669620044749365658 tz=\"+0100\" logid=\"0000000020\" type=\"traffic\" subtype=\"forward\" level=\"notice\" vd=\"root\" srcip=1.2.3.4 srcname=\"example.com\" srcport=52272 srcintf=\"ID102\" srcintfrole=\"lan\" dstip=5.6.7.8 dstport=443 dstintf=\"ID015\" dstintfrole=\"wan\" srcuuid=\"ccd49675-9207-46cf-9c4b-8d522c2b977e\" srccountry=\"Reserved\" dstinetsvc=\"Microsoft-Office365.Published\" dstcountry=\"France\" dstregion=\"Ile-de-France\" dstcity=\"Paris\" dstreputation=5 sessionid=111111111 proto=6 action=\"accept\" policyid=37 policytype=\"policy\" poluuid=\"6a8f76d0-1459-4ddb-948a-62700ddbf241\" service=\"Microsoft-Office365.Published\" trandisp=\"snat\" transip=4.3.2.1 transport=52272 duration=258 sentbyte=160972 rcvdbyte=58449 sentpkt=333 rcvdpkt=192 vwlid=8 vwlquality=\"Seq_num(13 ID015), alive, custom1: 78.211: 0.000% 7.754 0.067 897379Kbps, selected\" vwlname=\"TO-INTERNET\" appcat=\"unscanned\" sentdelta=31328 rcvddelta=10476 srchwvendor=\"Dell\" devtype=\"Home & Office\" srcfamily=\"Computer\" osname=\"Windows\" srcswversion=\"10\" unauthuser=\"example.com\\jdoe\" unauthusersource=\"kerberos\" mastersrcmac=\"02:00:00:00:00:00\" srcmac=\"02:00:00:00:00:00\" srcserver=0",
"event": {
"action": "accept",
"category": "traffic",
"code": "0000000020",
"dataset": "traffic:forward",
"duration": 258000000000,
"outcome": "success",
"timezone": "+0100"
},
"@timestamp": "2022-11-28T07:20:44.749366Z",
"action": {
"name": "accept",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "5.6.7.8",
"bytes": 10476,
"geo": {
"city_name": "Paris",
"country_name": "France",
"region_name": "Ile-de-France"
},
"ip": "5.6.7.8",
"packets": 192,
"port": 443
},
"fortinet": {
"fortigate": {
"dst_internet_service": "Microsoft-Office365.Published",
"dst_reputation": 5,
"event": {
"type": "traffic"
},
"nat_translation_type": "snat",
"policyid": "37",
"policytype": "policy",
"poluuid": "6a8f76d0-1459-4ddb-948a-62700ddbf241",
"sessionid": "111111111",
"total": {
"duration": 258000000000,
"received_bytes": 58449,
"sent_bytes": 160972,
"sent_packets": 333
},
"user": {
"source": "kerberos"
},
"virtual_domain": "root"
}
},
"host": {
"name": "example.com",
"os": {
"family": "Windows"
}
},
"log": {
"hostname": "computer-039482",
"level": "notice"
},
"network": {
"bytes": 41804,
"protocol": "microsoft-office365.published",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "wan",
"name": "ID015"
}
},
"hostname": "computer-039482",
"ingress": {
"interface": {
"alias": "lan",
"name": "ID102"
}
},
"serial_number": "C10382849"
},
"related": {
"hosts": [
"computer-039482"
],
"ip": [
"1.2.3.4",
"4.3.2.1",
"5.6.7.8"
],
"user": [
"jdoe"
]
},
"rule": {
"category": "unscanned",
"ruleset": "policy"
},
"source": {
"address": "1.2.3.4",
"bytes": 31328,
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00",
"nat": {
"ip": "4.3.2.1"
},
"packets": 333,
"port": 52272
},
"user": {
"domain": "example.com",
"name": "jdoe"
}
}
{
"message": "timestamp=1759197338 devname=\"my-device\" devid=\"1111111111111111\" vd=\"root\" itime=1759186539 logver=0704072731 date=2025-09-30 time=00:55:38 eventtime=\"1759186539261872875\" tz=\"+0200\" logid=\"1500054000\" type=\"utm\" subtype=\"ips\" eventtype=signature level=\"alert\" severity=\"high\" srcip=192.168.2.1 srccountry=\"Reserved\" dstip=1.2.3.4 dstcountry=\"Reserved\" srcintf=\"x8\" srcintfrole=\"dmz\" dstintf=\"INTF-2\" dstintfrole=\"lan\" sessionid=123456789 action=\"dropped\" proto=6 service=\"HTTPS\" policyid=84 poluuid=\"46e3c770-bcb4-4ba5-a98e-0873f6023aae\" policytype=\"policy\" attack=\"Adobe.ColdFusion.CVE-2023-44352.Reflected.XSS\" srcport=53369 dstport=443 hostname=\"example.com\" url=\"/8tlck5A7%22%3E%3Cscript%3Ealert(document.domain)%3C/script%3E/..CFIDE/wizards/common/_authenticatewizarduser.cfm\" agent=\"Mozilla/5.0 (Knoppix; Linux i686) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36\" httpmethod=GET direction=outgoing attackid=54356 profile=default ref=http://www.fortinet.com/ids/VID54356 incidentserialno=201043218 msg=\"applications3: Adobe.ColdFusion.CVE-2023-44352.Reflected.XSS\" forwardedfor=5.6.7.8:51912 crscore=30 craction=8192 crlevel=\"high\"",
"event": {
"action": "dropped",
"category": "utm",
"code": "1500054000",
"outcome": "success",
"reason": "applications3: Adobe.ColdFusion.CVE-2023-44352.Reflected.XSS",
"start": "2025-09-29T22:55:39Z",
"timezone": "+0200"
},
"@timestamp": "2025-09-29T22:55:39.261873Z",
"action": {
"name": "dropped",
"outcome": "success",
"outcome_reason": "applications3: Adobe.ColdFusion.CVE-2023-44352.Reflected.XSS",
"target": "network-traffic",
"type": "ips"
},
"destination": {
"address": "1.2.3.4",
"domain": "example.com",
"ip": "1.2.3.4",
"port": 443
},
"fortinet": {
"fortigate": {
"attack": {
"id": "54356",
"name": "Adobe.ColdFusion.CVE-2023-44352.Reflected.XSS"
},
"event": {
"severity": "high",
"type": "utm"
},
"log_version": "0704072731",
"policyid": "84",
"policytype": "policy",
"poluuid": "46e3c770-bcb4-4ba5-a98e-0873f6023aae",
"security_profile": "default",
"sessionid": "123456789",
"threat": {
"level": "high",
"score": 30,
"type": 8192
},
"virtual_domain": "root"
}
},
"http": {
"request": {
"method": "GET"
}
},
"log": {
"hostname": "my-device",
"level": "alert"
},
"network": {
"direction": "outbound",
"forwarded_ip": "5.6.7.8",
"protocol": "https",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "lan",
"name": "INTF-2"
}
},
"hostname": "my-device",
"ingress": {
"interface": {
"alias": "dmz",
"name": "x8"
}
},
"serial_number": "1111111111111111"
},
"related": {
"hosts": [
"example.com",
"my-device"
],
"ip": [
"1.2.3.4",
"192.168.2.1"
]
},
"rule": {
"ruleset": "policy"
},
"source": {
"address": "192.168.2.1",
"ip": "192.168.2.1",
"port": 53369
},
"url": {
"original": "/8tlck5A7%22%3E%3Cscript%3Ealert(document.domain)%3C/script%3E/..CFIDE/wizards/common/_authenticatewizarduser.cfm",
"path": "/8tlck5A7%22%3E%3Cscript%3Ealert(document.domain)%3C/script%3E/..CFIDE/wizards/common/_authenticatewizarduser.cfm"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Chrome",
"original": "Mozilla/5.0 (Knoppix; Linux i686) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36",
"os": {
"name": "Linux"
},
"version": "120.0.0"
}
}
{
"message": "timestamp=1742602531 devname=\"XXX\" devid=\"XXX\" vd=\"root\" date=2025-03-22 time=00:15:31 eventtime=1742613330828471629 tz=\"-0300\" logid=\"0000000013\" type=\"traffic\" subtype=\"forward\" level=\"notice\" srcip=1.2.3.4 srcport=60568 srcintf=\"port1\" srcintfrole=\"undefined\" dstip=192.0.2.1 dstport=53 dstintf=\"XXX\" dstintfrole=\"undefined\" srccountry=\"Reserved\" dstcountry=\"Japan\" sessionid=496025498 proto=17 action=\"accept\" policyid=398 policytype=\"policy\" poluuid=\"poluuidvalue\" service=\"udp-53\" trandisp=\"noop\" appid=16195 app=\"DNS\" appcat=\"Network.Service\" apprisk=\"elevated\" applist=\"XXX\" duration=180 sentbyte=0 rcvdbyte=0 sentpkt=0 rcvdpkt=0 vpntype=\"ipsecvpn\" utmaction=\"block\" countips=1 crscore=30 craction=8192",
"event": {
"action": "accept",
"category": "traffic",
"code": "0000000013",
"dataset": "traffic:forward",
"duration": 180000000000,
"outcome": "success",
"timezone": "-0300"
},
"@timestamp": "2025-03-22T03:15:30.828472Z",
"action": {
"name": "accept",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "192.0.2.1",
"bytes": 0,
"geo": {
"country_name": "Japan"
},
"ip": "192.0.2.1",
"packets": 0,
"port": 53
},
"fortinet": {
"fortigate": {
"applist": "XXX",
"apprisk": "elevated",
"event": {
"type": "traffic"
},
"nat_translation_type": "noop",
"policyid": "398",
"policytype": "policy",
"poluuid": "poluuidvalue",
"sessionid": "496025498",
"threat": {
"score": 30,
"type": 8192
},
"utmaction": "block",
"virtual_domain": "root",
"vpntype": "ipsecvpn"
}
},
"log": {
"hostname": "XXX",
"level": "notice"
},
"network": {
"application": "DNS",
"bytes": 0,
"protocol": "udp-53",
"transport": "udp"
},
"observer": {
"egress": {
"interface": {
"name": "XXX"
}
},
"hostname": "XXX",
"ingress": {
"interface": {
"name": "port1"
}
},
"serial_number": "XXX"
},
"related": {
"hosts": [
"XXX"
],
"ip": [
"1.2.3.4",
"192.0.2.1"
]
},
"rule": {
"apprisk": "elevated",
"category": "Network.Service",
"ruleset": "XXX"
},
"source": {
"address": "1.2.3.4",
"bytes": 0,
"ip": "1.2.3.4",
"packets": 0,
"port": 60568
}
}
{
"message": "CEF:0|Fortinet|FortiGate-1000C|5.6.14,build1727 (GA)|0000000020|forward traffic accept|5|start=Oct 12 2022 12:50:31 logver=506141727 deviceExternalId=FGT123 dvchost=FW-123 ad.vd=root ad.logid=0000000020 cat=traffic ad.subtype=forward deviceSeverity=notice ad.eventtime=1665571831 src=1.1.1.1 spt=55390 deviceInboundInterface=abc ad.srcintfrole=undefined dst=192.0.2.1 dpt=1522 deviceOutboundInterface=efg ad.dstintfrole=lan foo.poluuid=ec6ff8fe-5e41-51ec-bcbe-9e5484033dc8 externalID=3812440508 proto=6 act=accept ad.policyid=185 ad.policytype=policy app=SQLNET-1522 ad.dstcountry=Reserved ad.srccountry=Reserved ad.trandisp=noop ad.duration=268 out=202 in=52 ad.sentpkt=3 ad.rcvdpkt=1 ad.appcat=unscanned ad.sentdelta=0 ad.rcvddelta=0 tz=\"+0200\"",
"event": {
"action": "accept",
"category": "traffic",
"code": "0000000020",
"dataset": "traffic",
"outcome": "success",
"timezone": "+0200"
},
"@timestamp": "2022-10-12T10:50:31Z",
"action": {
"name": "accept",
"outcome": "success",
"target": "network-traffic"
},
"destination": {
"address": "192.0.2.1",
"bytes": 52,
"ip": "192.0.2.1",
"port": 1522
},
"fortinet": {
"fortigate": {
"log_version": "506141727"
}
},
"network": {
"application": "SQLNET-1522",
"bytes": 254,
"protocol": "sqlnet-1522",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "efg"
}
},
"ingress": {
"interface": {
"name": "abc"
}
},
"serial_number": "FGT123",
"type": "FortiGate-1000C",
"vendor": "Fortinet",
"version": "5.6.14,build1727 (GA)"
},
"related": {
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"source": {
"address": "1.1.1.1",
"bytes": 202,
"ip": "1.1.1.1",
"port": 55390
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.4|00013|traffic:forward timeout|3|deviceExternalId=FGVM2V0000171868 FortinetFortiGatelogid=0000000013 cat=traffic:forward FortinetFortiGatesubtype=forward FortinetFortiGatelevel=notice FortinetFortiGatevd=root FortinetFortiGateeventtime=1572471876 src=1.1.1.1 spt=49260 deviceInboundInterface=port1 FortinetFortiGatesrcintfrole=undefined dst=192.0.2.1 dpt=80 deviceOutboundInterface=port2 FortinetFortiGatedstintfrole=undefined FortinetFortiGatepoluuid=bafe134e-c0ad-51e8-ed9c-52f798dd69d4 externalId=12812952 proto=6 FortinetFortiGateaction=timeout FortinetFortiGatepolicyid=1 FortinetFortiGatepolicytype=policy app=HTTP FortinetFortiGatedstcountry=Reserved FortinetFortiGatesrccountry=United States FortinetFortiGatetrandisp=dnat destinationTranslatedAddress=192.0.2.1 destinationTranslatedPort=80 FortinetFortiGateduration=20 out=48 in=144 FortinetFortiGatesentpkt=1 FortinetFortiGatercvdpkt=3 FortinetFortiGateappcat=unscanned FortinetFortiGatecrscore=5 FortinetFortiGatecraction=262144 FortinetFortiGatecrlevel=low",
"event": {
"action": "timeout",
"category": "traffic",
"code": "0000000013",
"dataset": "traffic:forward",
"duration": 20000000000,
"outcome": "success"
},
"@timestamp": "2019-10-30T21:44:36Z",
"action": {
"name": "timeout",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "192.0.2.1",
"bytes": 144,
"ip": "192.0.2.1",
"nat": {
"ip": "192.0.2.1",
"port": 80
},
"packets": 3,
"port": 80
},
"fortinet": {
"fortigate": {
"nat_translation_type": "dnat",
"policyid": "1",
"policytype": "policy",
"poluuid": "bafe134e-c0ad-51e8-ed9c-52f798dd69d4",
"threat": {
"level": "low",
"score": 5,
"type": 262144
},
"virtual_domain": "root"
}
},
"log": {
"level": "notice"
},
"network": {
"application": "HTTP",
"bytes": 192,
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port2"
}
},
"ingress": {
"interface": {
"name": "port1"
}
},
"serial_number": "FGVM2V0000171868",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.4"
},
"related": {
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"rule": {
"category": "unscanned",
"ruleset": "policy"
},
"source": {
"address": "1.1.1.1",
"bytes": 48,
"geo": {
"country_name": "United States"
},
"ip": "1.1.1.1",
"packets": 1,
"port": 49260
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.3|00013|traffic:forward close|3|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0000000013 cat=traffic:forward FTNTFGTsubtype=forward FTNTFGTlevel=notice FTNTFGTvd=vdom1 FTNTFGTeventtime=1545937675 src=10.1.100.11 spt=54190 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined dst=192.0.2.1 dpt=443 deviceOutboundInterface=port11 FTNTFGTdstintfrole=undefined FTNTFGTpoluuid=c2d460aa-fe6f-51e8-9505-41b5117dfdd4 externalId=402 proto=6 act=close FTNTFGTpolicyid=1 FTNTFGTpolicytype=policy app=HTTPS FTNTFGTdstcountry=United States FTNTFGTsrccountry=Reserved FTNTFGTtrandisp=snat sourceTranslatedAddress=172.16.200.1 sourceTranslatedPort=54190 FTNTFGTappid=40568 FTNTFGTapp=HTTPS.BROWSER FTNTFGTappcat=Web.Client FTNTFGTapprisk=medium FTNTFGTapplist=g-default FTNTFGTduration=2 out=3652 in=146668 FTNTFGTsentpkt=58 FTNTFGTrcvdpkt=105 FTNTFGTutmaction=allow FTNTFGTcountapp=2",
"event": {
"action": "close",
"category": "traffic",
"code": "0000000013",
"dataset": "traffic:forward",
"duration": 2000000000,
"outcome": "success"
},
"@timestamp": "2018-12-27T19:07:55Z",
"action": {
"name": "close",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "192.0.2.1",
"bytes": 146668,
"geo": {
"country_name": "United States"
},
"ip": "192.0.2.1",
"packets": 105,
"port": 443
},
"fortinet": {
"fortigate": {
"applist": "g-default",
"apprisk": "medium",
"nat_translation_type": "snat",
"policyid": "1",
"policytype": "policy",
"poluuid": "c2d460aa-fe6f-51e8-9505-41b5117dfdd4",
"utmaction": "allow",
"virtual_domain": "vdom1"
}
},
"log": {
"level": "notice"
},
"network": {
"application": "HTTPS",
"bytes": 150320,
"protocol": "https",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port11"
}
},
"ingress": {
"interface": {
"name": "port12"
}
},
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"ip": [
"10.1.100.11",
"172.16.200.1",
"192.0.2.1"
]
},
"rule": {
"apprisk": "medium",
"category": "Web.Client",
"ruleset": "g-default"
},
"source": {
"address": "10.1.100.11",
"bytes": 3652,
"ip": "10.1.100.11",
"nat": {
"ip": "172.16.200.1",
"port": 54190
},
"packets": 58,
"port": 54190
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v7.2.8|00013|traffic:forward client-rst|3|deviceExternalId=FGTEXAMPLE subtype=forward FTNTFGTlevel=notice FTNTFGTvd=root src=1.2.3.4 shost=example.com spt=59020 deviceInboundInterface=LAN-EX-SRV FTNTFGTsrcintfrole=lan dst=5.6.7.8 dpt=65359 deviceOutboundInterface=CASio-1_0 FTNTFGTdstintfrole=wan FTNTFGTsrccountry=Reserved FTNTFGTdstcountry=Reserved externalId=26368100 proto=6 act=client-rst FTNTFGTpolicyid=353 FTNTFGTpolicytype=policy FTNTFGTpoluuid=2967ec4c-c4d7-51ed-30a5-720dc6023629 FTNTFGTpolicyname=AD-CASio_TO_DC app=tcp/65359 FTNTFGTtrandisp=noop FTNTFGTduration=175 out=3608 in=2571 FTNTFGTsentpkt=15 FTNTFGTrcvdpkt=11 FTNTFGTvpntype=ipsecvpn FTNTFGTvwlid=4 FTNTFGTvwlquality=Seq_num(1 CASIio-1_0), alive, selected FTNTFGTvwlname=TO_JOE FTNTFGTappcat=unscanned FTNTFGTpsrcport=58624 FTNTFGTpdstport=135 FTNTFGTsentdelta=80 FTNTFGTrcvddelta=2519 FTNTFGTsrchwvendor=VMware FTNTFGTosname=Windows FTNTFGTsrcswversion=10 FTNTFGTunauthuser=REDACTED FTNTFGTunauthusersource=kerberos FTNTFGTmastersrcmac=02:00:00:00:00:00 FTNTFGTsrcmac=02:00:00:00:00:00 FTNTFGTsrcserver=0\n",
"event": {
"action": "client-rst",
"category": "traffic",
"code": "00013",
"dataset": "traffic:forward",
"duration": 175000000000,
"outcome": "success"
},
"action": {
"name": "client-rst",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "5.6.7.8",
"bytes": 2571,
"ip": "5.6.7.8",
"packets": 11,
"port": 65359
},
"fortinet": {
"fortigate": {
"nat_translation_type": "noop",
"policyid": "353",
"policyname": "AD-CASio_TO_DC",
"policytype": "policy",
"poluuid": "2967ec4c-c4d7-51ed-30a5-720dc6023629",
"user": {
"source": "kerberos"
},
"virtual_domain": "root",
"vpntype": "ipsecvpn"
}
},
"host": {
"os": {
"family": "Windows"
}
},
"log": {
"level": "notice"
},
"network": {
"application": "tcp/65359",
"bytes": 6179,
"protocol": "tcp/65359",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "wan",
"name": "CASio-1_0"
}
},
"ingress": {
"interface": {
"alias": "lan",
"name": "LAN-EX-SRV"
}
},
"serial_number": "FGTEXAMPLE",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v7.2.8"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
],
"user": [
"REDACTED"
]
},
"rule": {
"category": "unscanned",
"ruleset": "policy"
},
"source": {
"address": "example.com",
"bytes": 3608,
"domain": "example.com",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00",
"packets": 15,
"port": 59020,
"registered_domain": "example.com",
"top_level_domain": "com"
},
"user": {
"name": "REDACTED"
}
}
{
"message": "0|Fortinet|Fortigate|v7.2.10|00011|traffic:forward ip-conn|4|deviceExternalId=FGT40FTK23052620 FTNTFGTeventtime=1737553257865429339 FTNTFGTtz=+0100 FTNTFGTlogid=0000000011 cat=traffic:forward FTNTFGTsubtype=forward FTNTFGTlevel=warning FTNTFGTvd=root src=1.2.3.4 shost=example.com spt=53272 deviceInboundInterface=interface_02 FTNTFGTsrcintfrole=lan dst=5.6.7.8 dpt=443 deviceOutboundInterface=interface_01 FTNTFGTdstintfrole=undefined FTNTFGTsrccountry=Reserved FTNTFGTdstcountry=France externalId=1248357 proto=6 act=ip-conn FTNTFGTpolicyid=6 FTNTFGTpolicytype=policy FTNTFGTpoluuid=c2d241ae-2bb9-51ee-e76b-094ea7f446e8 app=HTTPS FTNTFGTappcat=unscanned FTNTFGTcrscore=5 FTNTFGTcraction=262144 FTNTFGTcrlevel=low FTNTFGTosname=Windows FTNTFGTsrcswversion=10 / 2016 FTNTFGTunauthuser=jdoe FTNTFGTunauthusersource=kerberos FTNTFGTmastersrcmac=02:00:00:00:00:00 FTNTFGTsrcmac=02:00:00:00:00:00 FTNTFGTsrcserver=0\n```<br><br><i>(created from <a href=https://sekoia8055.zendesk.com/agent/tickets/5534>Zendesk ticket #5534</a>)<br> gz#5534</i>",
"event": {
"action": "ip-conn",
"category": "traffic",
"code": "0000000011",
"dataset": "traffic:forward",
"outcome": "success",
"timezone": "+0100"
},
"@timestamp": "2025-01-22T13:40:57.865429Z",
"action": {
"name": "ip-conn",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "5.6.7.8",
"geo": {
"country_name": "France"
},
"ip": "5.6.7.8",
"port": 443
},
"fortinet": {
"fortigate": {
"policyid": "6",
"policytype": "policy",
"poluuid": "c2d241ae-2bb9-51ee-e76b-094ea7f446e8",
"threat": {
"level": "low",
"score": 5,
"type": 262144
},
"user": {
"source": "kerberos"
},
"virtual_domain": "root"
}
},
"host": {
"os": {
"family": "Windows"
}
},
"log": {
"level": "warning"
},
"network": {
"application": "HTTPS",
"protocol": "https",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "interface_01"
}
},
"ingress": {
"interface": {
"alias": "lan",
"name": "interface_02"
}
},
"serial_number": "FGT40FTK23052620",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v7.2.10"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
],
"user": [
"jdoe"
]
},
"rule": {
"category": "unscanned",
"ruleset": "policy"
},
"source": {
"address": "example.com",
"domain": "example.com",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00",
"port": 53272,
"registered_domain": "example.com",
"top_level_domain": "com"
},
"user": {
"name": "jdoe"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v7.4.9|00013|traffic:forward close|3|deviceExternalId=FGTEXAMPLE FTNTFGTeventtime=1762443492031974938 FTNTFGTtz=+0100 FTNTFGTlogid=0000000013 cat=traffic:forward FTNTFGTsubtype=forward FTNTFGTlevel=notice FTNTFGTvd=root src=1.2.3.4 spt=64746 deviceInboundInterface=port2 FTNTFGTsrcintfrole=dmz dst=192.168.115.11 dpt=8093 deviceOutboundInterface=port10 FTNTFGTdstintfrole=dmz FTNTFGTsrccountry=Reserved FTNTFGTdstcountry=Reserved externalId=1234 proto=6 act=close FTNTFGTpolicyid=859 FTNTFGTpolicytype=policy FTNTFGTpoluuid=00000000-0000-0000-0000-000000000000 FTNTFGTpolicyname=Filtrage ID Eset app=TCP_8093 FTNTFGTtrandisp=noop FTNTFGTappid=47013 FTNTFGTapp=SSL_TLSv1.3 FTNTFGTappcat=Network.Service FTNTFGTapprisk=medium FTNTFGTapplist=g-APP_MONITOR FTNTFGTduration=92 out=1504 in=2647 FTNTFGTsentpkt=9 FTNTFGTrcvdpkt=9 FTNTFGTutmaction=allow FTNTFGTcountapp=2",
"event": {
"action": "close",
"category": "traffic",
"code": "0000000013",
"dataset": "traffic:forward",
"duration": 92000000000,
"outcome": "success",
"timezone": "+0100"
},
"@timestamp": "2025-11-06T15:38:12.031975Z",
"action": {
"name": "close",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "192.168.115.11",
"bytes": 2647,
"ip": "192.168.115.11",
"packets": 9,
"port": 8093
},
"fortinet": {
"fortigate": {
"applist": "g-APP_MONITOR",
"apprisk": "medium",
"nat_translation_type": "noop",
"policyid": "859",
"policyname": "Filtrage ID Eset",
"policytype": "policy",
"poluuid": "00000000-0000-0000-0000-000000000000",
"utmaction": "allow",
"virtual_domain": "root"
}
},
"log": {
"level": "notice"
},
"network": {
"application": "TCP_8093",
"bytes": 4151,
"protocol": "tcp_8093",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "dmz",
"name": "port10"
}
},
"ingress": {
"interface": {
"alias": "dmz",
"name": "port2"
}
},
"serial_number": "FGTEXAMPLE",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v7.4.9"
},
"related": {
"ip": [
"1.2.3.4",
"192.168.115.11"
]
},
"rule": {
"apprisk": "medium",
"category": "Network.Service",
"ruleset": "g-APP_MONITOR"
},
"source": {
"address": "1.2.3.4",
"bytes": 1504,
"ip": "1.2.3.4",
"packets": 9,
"port": 64746
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v7.4.9|00013|traffic:forward client-rst|3|deviceExternalId=FGTEXAMPLE FTNTFGTeventtime=1762521404541985717 FTNTFGTtz=+0100 FTNTFGTlogid=0000000013 cat=traffic:forward FTNTFGTsubtype=forward FTNTFGTlevel=notice FTNTFGTvd=root src=1.2.3.4 spt=56006 deviceInboundInterface=port2 FTNTFGTsrcintfrole=dmz dst=192.168.100.7 dpt=8080 deviceOutboundInterface=port1 FTNTFGTdstintfrole=dmz FTNTFGTsrccountry=Reserved FTNTFGTdstcountry=Reserved externalId=1234 proto=6 act=client-rst FTNTFGTpolicyid=860 FTNTFGTpolicytype=policy FTNTFGTpoluuid=00000000-0000-0000-0000-000000000000 FTNTFGTpolicyname=Filtrage ID Proxy duser=USER1 FTNTFGTauthserver=FSSO_collector_agent-1 FTNTFGTdstuser=USER2 app=http_https_proxy FTNTFGTtrandisp=noop FTNTFGTappid=52305 FTNTFGTapp=TrendMicro.IWSVA FTNTFGTappcat=Cloud.IT FTNTFGTapprisk=low FTNTFGTapplist=g-APP_MONITOR FTNTFGTduration=35 out=440 in=518 FTNTFGTsentpkt=5 FTNTFGTrcvdpkt=5 FTNTFGTutmaction=allow FTNTFGTcountapp=2 FTNTFGTcrscore=10 FTNTFGTcraction=1048576 msg=Connection Failed",
"event": {
"action": "client-rst",
"category": "traffic",
"code": "0000000013",
"dataset": "traffic:forward",
"duration": 35000000000,
"outcome": "success",
"reason": "Connection Failed",
"timezone": "+0100"
},
"@timestamp": "2025-11-07T13:16:44.541986Z",
"action": {
"name": "client-rst",
"outcome": "success",
"outcome_reason": "Connection Failed",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "192.168.100.7",
"bytes": 518,
"ip": "192.168.100.7",
"packets": 5,
"port": 8080,
"user": {
"name": "USER2"
}
},
"fortinet": {
"fortigate": {
"applist": "g-APP_MONITOR",
"apprisk": "low",
"nat_translation_type": "noop",
"policyid": "860",
"policyname": "Filtrage ID Proxy",
"policytype": "policy",
"poluuid": "00000000-0000-0000-0000-000000000000",
"threat": {
"score": 10,
"type": 1048576
},
"utmaction": "allow",
"virtual_domain": "root"
}
},
"log": {
"level": "notice"
},
"network": {
"application": "http_https_proxy",
"bytes": 958,
"protocol": "http_https_proxy",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "dmz",
"name": "port1"
}
},
"ingress": {
"interface": {
"alias": "dmz",
"name": "port2"
}
},
"serial_number": "FGTEXAMPLE",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v7.4.9"
},
"related": {
"ip": [
"1.2.3.4",
"192.168.100.7"
],
"user": [
"USER1",
"USER2"
]
},
"rule": {
"apprisk": "low",
"category": "Cloud.IT",
"ruleset": "g-APP_MONITOR"
},
"source": {
"address": "1.2.3.4",
"bytes": 440,
"ip": "1.2.3.4",
"packets": 5,
"port": 56006,
"user": {
"name": "USER1"
}
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v5.6.0|00013|traffic:forward close|3|FTNTFGTlogid=0000000013 cat=traffic:forward FTNTFGTsubtype=forward FTNTFGTlevel=notice FTNTFGTvd=vdom1 src=hostname shost=example spt=45719 deviceInboundInterface=port15 dst=hostname dhost=hostname dpt=80 deviceOutboundInterface=port19 FTNTFGTpoluuid=61c4243a-34ba-51e5-c32a-3859389a5162 externalId=56633 proto=6 act=close cs5=10 cs5Label=Policy Id FTNTFGTdstcountry=Reserved FTNTFGTsrccountry=Reserved FTNTFGTtrandisp=snat sourceTranslatedAddress=1.1.1.1 sourceTranslatedPort=45719 app=HTTP FTNTFGTappid=38783 FTNTFGTapp=Wget.Like FTNTFGTappcat=General.Interest FTNTFGTapprisk=low FTNTFGTapplist=default FTNTFGTappact=detected cn1=7 cn1Label=Duration out=398 in=1605 cn2=5 cn2Label=Packets Sent cn3=5 cn3Label=Packets Received FTNTFGTutmaction=block FTNTFGTcountav=1 FTNTFGTcountapp=1 FTNTFGTcrscore=50 FTNTFGTcraction=2",
"event": {
"action": "close",
"category": "traffic",
"code": "0000000013",
"dataset": "traffic:forward",
"outcome": "success"
},
"action": {
"name": "close",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "hostname",
"bytes": 1605,
"domain": "hostname",
"packets": 5,
"port": 80
},
"fortinet": {
"fortigate": {
"applist": "default",
"apprisk": "low",
"nat_translation_type": "snat",
"poluuid": "61c4243a-34ba-51e5-c32a-3859389a5162",
"threat": {
"score": 50,
"type": 2
},
"utmaction": "block",
"virtual_domain": "vdom1"
}
},
"log": {
"level": "notice"
},
"network": {
"application": "HTTP",
"bytes": 2003,
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port19"
}
},
"ingress": {
"interface": {
"name": "port15"
}
},
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v5.6.0"
},
"related": {
"hosts": [
"example",
"hostname"
],
"ip": [
"1.1.1.1"
]
},
"rule": {
"apprisk": "low",
"category": "General.Interest",
"ruleset": "default"
},
"source": {
"address": "example",
"bytes": 398,
"domain": "example",
"nat": {
"ip": "1.1.1.1",
"port": 45719
},
"packets": 5,
"port": 45719
}
}
{
"message": "date=2018-07-26,time=16:51:36,logid=\"0000000013\",type=\"traffic\",subtype=\"forward\",level=\"notice\",vd=\"root\",eventtime=1532616695,srcip=1.1.1.1,srcport=10016,srcintf=\"test\",srcintfrole=\"undefined\",dstip=192.0.2.1,dstport=20,dstintf=\"dmz1\",dstintfrole=\"dmz\",sessionid=10006,proto=6,action=\"accept\",policyid=1,policytype=\"policy\",service=\"tcp/20\",dstcountry=\"France\",srccountry=\"United States\",trandisp=\"noop\",appid=35421,app=\"application\",appcat=\"Storage.Backup\",apprisk=\"medium\",applist=\"default\",duration=10,sentbyte=2000,rcvdbyte=1000,sentpkt=0,rcvdpkt=0,utmaction=\"allow\",countapp=1,devtype=\"iPad\",osname=\"Apple\",osversion=\"ver\",mastersrcmac=\"02:00:00:00:00:00\",srcmac=\"02:00:00:00:00:00\",srcserver=0,dstdevtype=\"Android Phone\",dstosname=\"Android\",dstosversion=\"ver\",masterdstmac=\"02:00:00:00:00:00\",dstmac=\"02:00:00:00:00:00\",dstserver=0,utmref=65491-194",
"event": {
"action": "accept",
"category": "traffic",
"code": "0000000013",
"dataset": "traffic:forward",
"duration": 10000000000,
"outcome": "success"
},
"@timestamp": "2018-07-26T14:51:35Z",
"action": {
"name": "accept",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "192.0.2.1",
"bytes": 1000,
"geo": {
"country_name": "France"
},
"ip": "192.0.2.1",
"mac": "02:00:00:00:00:00",
"packets": 0,
"port": 20
},
"fortinet": {
"fortigate": {
"applist": "default",
"apprisk": "medium",
"event": {
"type": "traffic"
},
"nat_translation_type": "noop",
"policyid": "1",
"policytype": "policy",
"sessionid": "10006",
"utmaction": "allow",
"virtual_domain": "root"
}
},
"host": {
"os": {
"family": "Apple"
}
},
"log": {
"level": "notice"
},
"network": {
"application": "application",
"bytes": 3000,
"protocol": "tcp/20",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "dmz",
"name": "dmz1"
}
},
"ingress": {
"interface": {
"name": "test"
}
}
},
"related": {
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"rule": {
"apprisk": "medium",
"category": "Storage.Backup",
"ruleset": "default"
},
"source": {
"address": "1.1.1.1",
"bytes": 2000,
"geo": {
"country_name": "United States"
},
"ip": "1.1.1.1",
"mac": "02:00:00:00:00:00",
"packets": 0,
"port": 10016
}
}
{
"message": "date=2018-07-26 time=16:51:36 logid=\"0000000013\" type=\"traffic\" subtype=\"forward\" level=\"notice\" vd=\"root\" eventtime=1532616695 srcip=1.1.1.1 srcport=10016 srcintf=\"test\" srcintfrole=\"undefined\" dstip=192.0.2.1 dstport=20 dstintf=\"test1\" dstintfrole=\"dmz\" sessionid=10006 proto=6 action=\"accept\" policyid=1 policytype=\"policy\" service=\"tcp/20\" dstcountry=\"France\" srccountry=\"United States\" trandisp=\"noop\" appid=35421 app=\"Dropbox_File.Download\" appcat=\"Storage.Backup\" apprisk=\"medium\" applist=\"default\" duration=10 sentbyte=2000 rcvdbyte=1000 sentpkt=0 rcvdpkt=0 utmaction=\"allow\" countapp=1 devtype=\"iPad\" osname=\"Apple\" osversion=\"ver\" mastersrcmac=\"02:00:00:00:00:00\" srcmac=\"02:00:00:00:00:00\" srcserver=0 dstdevtype=\"Android Phone\" dstosname=\"Android\" dstosversion=\"ver\" masterdstmac=\"02:00:00:00:00:00\" dstmac=\"02:00:00:00:00:00\" dstserver=0 utmref=65491-194",
"event": {
"action": "accept",
"category": "traffic",
"code": "0000000013",
"dataset": "traffic:forward",
"duration": 10000000000,
"outcome": "success"
},
"@timestamp": "2018-07-26T14:51:35Z",
"action": {
"name": "accept",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "192.0.2.1",
"bytes": 1000,
"geo": {
"country_name": "France"
},
"ip": "192.0.2.1",
"mac": "02:00:00:00:00:00",
"packets": 0,
"port": 20
},
"fortinet": {
"fortigate": {
"applist": "default",
"apprisk": "medium",
"event": {
"type": "traffic"
},
"nat_translation_type": "noop",
"policyid": "1",
"policytype": "policy",
"sessionid": "10006",
"utmaction": "allow",
"virtual_domain": "root"
}
},
"host": {
"os": {
"family": "Apple"
}
},
"log": {
"level": "notice"
},
"network": {
"application": "Dropbox_File.Download",
"bytes": 3000,
"protocol": "tcp/20",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "dmz",
"name": "test1"
}
},
"ingress": {
"interface": {
"name": "test"
}
}
},
"related": {
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"rule": {
"apprisk": "medium",
"category": "Storage.Backup",
"ruleset": "default"
},
"source": {
"address": "1.1.1.1",
"bytes": 2000,
"geo": {
"country_name": "United States"
},
"ip": "1.1.1.1",
"mac": "02:00:00:00:00:00",
"packets": 0,
"port": 10016
}
}
{
"message": "date=2021-06-21 time=09:38:29 devname=\"abc\" devid=\"1\" logid=\"0000000010\" type=\"traffic\" subtype=\"forward\" level=\"notice\" vd=\"PRX1-AA\" eventtime=1624261109 srcip=1.1.1.1 srcport=50592 srcintf=\"port2\" srcintfrole=\"dmz\" dstip=192.0.2.1 dstport=443 dstintf=\"test\" dstintfrole=\"wan\" sessionid=1224900441 poluuid=\"1eb429d4-ff52-51ea-d119-d1db60e409a6\" dstcountry=\"United Kingdom\" srccountry=\"Reserved\" service=\"HTTPS\" wanoptapptype=\"web-proxy\" proto=6 action=\"accept\" duration=37 policyid=1 policytype=\"proxy-policy\" wanin=5851 rcvdbyte=5851 wanout=2523 lanin=2769 sentbyte=2769 lanout=5923 appcat=\"unscanned\" utmaction=\"allow\" countweb=1",
"event": {
"action": "accept",
"category": "traffic",
"code": "0000000010",
"dataset": "traffic:forward",
"duration": 37000000000,
"outcome": "success"
},
"@timestamp": "2021-06-21T07:38:29Z",
"action": {
"name": "accept",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "192.0.2.1",
"bytes": 5851,
"geo": {
"country_name": "United Kingdom"
},
"ip": "192.0.2.1",
"port": 443
},
"fortinet": {
"fortigate": {
"event": {
"type": "traffic"
},
"policyid": "1",
"policytype": "proxy-policy",
"poluuid": "1eb429d4-ff52-51ea-d119-d1db60e409a6",
"sessionid": "1224900441",
"utmaction": "allow",
"virtual_domain": "PRX1-AA"
}
},
"log": {
"hostname": "abc",
"level": "notice"
},
"network": {
"bytes": 8620,
"protocol": "https",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "wan",
"name": "test"
}
},
"hostname": "abc",
"ingress": {
"interface": {
"alias": "dmz",
"name": "port2"
}
},
"serial_number": "1"
},
"related": {
"hosts": [
"abc"
],
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"rule": {
"category": "unscanned",
"ruleset": "proxy-policy"
},
"source": {
"address": "1.1.1.1",
"bytes": 2769,
"ip": "1.1.1.1",
"port": 50592
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.4.9|00011|traffic:forward dns|4|deviceExternalId=FG5H0ETB19909686 FTNTFGTeventtime=1662381825920035319 FTNTFGTtz=+0200 FTNTFGTlogid=0000000011 cat=traffic:forward FTNTFGTsubtype=forward FTNTFGTlevel=warning FTNTFGTvd=root src=172.16.222.150 spt=49956 deviceInboundInterface=port1 FTNTFGTsrcintfrole=wan dst=172.18.67.10 dpt=53 deviceOutboundInterface=RWC FRANCE 2023 FTNTFGTdstintfrole=lan FTNTFGTsrccountry=Reserved FTNTFGTdstcountry=Reserved externalId=1797928567 proto=17 act=dns FTNTFGTpolicyid=30 FTNTFGTpolicytype=policy FTNTFGTpoluuid=6c8b6672-0b92-51ea-95a0-556c3c0fdb8f FTNTFGTpolicyname=CLT-RWC2023-001 FTNTFGTcentralnatid=6 app=DNS FTNTFGTappcat=unscanned FTNTFGTcrscore=5 FTNTFGTcraction=262144 FTNTFGTcrlevel=low FTNTFGTdsthwvendor=VMware FTNTFGTdstdevtype=Server FTNTFGTdstfamily=Virtual Machine FTNTFGTdstosname=Windows FTNTFGTdsthwversion=Workstation Pro FTNTFGTdstswversion=7 FTNTFGTmasterdstmac=02:00:00:00:00:00 FTNTFGTdstmac=02:00:00:00:00:00 FTNTFGTdstserver=0",
"event": {
"action": "dns",
"category": "traffic",
"code": "0000000011",
"dataset": "traffic:forward",
"outcome": "success",
"timezone": "+0200"
},
"@timestamp": "2022-09-05T12:43:45.920035Z",
"action": {
"name": "dns",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "172.18.67.10",
"ip": "172.18.67.10",
"mac": "02:00:00:00:00:00",
"port": 53
},
"fortinet": {
"fortigate": {
"policyid": "30",
"policyname": "CLT-RWC2023-001",
"policytype": "policy",
"poluuid": "6c8b6672-0b92-51ea-95a0-556c3c0fdb8f",
"threat": {
"level": "low",
"score": 5,
"type": 262144
},
"virtual_domain": "root"
}
},
"log": {
"level": "warning"
},
"network": {
"application": "DNS",
"protocol": "dns",
"transport": "udp"
},
"observer": {
"egress": {
"interface": {
"alias": "lan",
"name": "RWC FRANCE 2023"
}
},
"ingress": {
"interface": {
"alias": "wan",
"name": "port1"
}
},
"serial_number": "FG5H0ETB19909686",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.4.9"
},
"related": {
"ip": [
"172.16.222.150",
"172.18.67.10"
]
},
"rule": {
"category": "unscanned",
"ruleset": "policy"
},
"source": {
"address": "172.16.222.150",
"ip": "172.16.222.150",
"port": 49956
}
}
{
"message": "date=2018-07-26 time=14:56:21 devname=\"abc\" devid=\"1\" logid=\"0000000013\" type=\"traffic\" subtype=\"forward\" level=\"notice\" vd=\"root\" eventtime=1609941381 srcip=1.1.1.1 srcport=52125 srcintf=\"port9\" srcintfrole=\"undefined\" dstip=192.0.2.1 dstport=3727 dstintf=\"port10\" dstintfrole=\"undefined\" poluuid=\"d77c53b2-a3c6-51e9-49b2-61c9e68c1f7e\" sessionid=578033623 proto=6 action=\"server-rst\" policyid=207 policytype=\"policy\" service=\"tcp/3727\" dstcountry=\"France\" srccountry=\"Netherlands\" trandisp=\"dnat\" tranip=192.0.2.1 tranport=3727 duration=5 sentbyte=80 rcvdbyte=40 sentpkt=2 rcvdpkt=1 appcat=\"unscanned\" dstdevtype=\"Router/NAT Device\" dstdevcategory=\"Windows Device\" masterdstmac=\"02:00:00:00:00:00\" dstmac=\"02:00:00:00:00:00\" dstserver=1",
"event": {
"action": "server-rst",
"category": "traffic",
"code": "0000000013",
"dataset": "traffic:forward",
"duration": 5000000000,
"outcome": "success"
},
"@timestamp": "2021-01-06T13:56:21Z",
"action": {
"name": "server-rst",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "192.0.2.1",
"bytes": 40,
"geo": {
"country_name": "France"
},
"ip": "192.0.2.1",
"mac": "02:00:00:00:00:00",
"nat": {
"ip": "192.0.2.1"
},
"packets": 1,
"port": 3727
},
"fortinet": {
"fortigate": {
"event": {
"type": "traffic"
},
"nat_translation_type": "dnat",
"policyid": "207",
"policytype": "policy",
"poluuid": "d77c53b2-a3c6-51e9-49b2-61c9e68c1f7e",
"sessionid": "578033623",
"virtual_domain": "root"
}
},
"log": {
"hostname": "abc",
"level": "notice"
},
"network": {
"bytes": 120,
"protocol": "tcp/3727",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port10"
}
},
"hostname": "abc",
"ingress": {
"interface": {
"name": "port9"
}
},
"serial_number": "1"
},
"related": {
"hosts": [
"abc"
],
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"rule": {
"category": "unscanned",
"ruleset": "policy"
},
"source": {
"address": "1.1.1.1",
"bytes": 80,
"geo": {
"country_name": "Netherlands"
},
"ip": "1.1.1.1",
"packets": 2,
"port": 52125
}
}
{
"message": "timestamp=1709762763 devname=\"FW-001\" devid=\"FG100D6G11111111\" vd=\"root\" date=2024-03-06 time=22:06:03 logid=\"0000000013\" type=\"traffic\" subtype=\"forward\" level=\"notice\" eventtime=1709762764028577926 tz=\"+0000\" srcip=1.2.3.4 srcname=\"example.com\" srcport=62979 srcintf=\"Port3.999\" srcintfrole=\"lan\" dstip=5.6.7.8 dstport=53 dstintf=\"wan1\" dstintfrole=\"undefined\" sessionid=538959618 proto=17 action=\"accept\" policyid=41 policytype=\"policy\" poluuid=\"703570eee-edfc-4565-8599-c6a75fd3e1e8\" service=\"DNS\" dstcountry=\"France\" srccountry=\"Reserved\" trandisp=\"snat\" transip=192.0.2.1 transport=62979 appid=16195 app=\"DNS\" appcat=\"Network.Service\" apprisk=\"elevated\" applist=\"EMEA_Monitor\" duration=189 sentbyte=285 rcvdbyte=0 sentpkt=5 rcvdpkt=0 osname=\"Windows\" srcswversion=\"10\" mastersrcmac=\"02:00:00:00:00:00\" srcmac=\"02:00:00:00:00:00\" srcserver=0",
"event": {
"action": "accept",
"category": "traffic",
"code": "0000000013",
"dataset": "traffic:forward",
"duration": 189000000000,
"outcome": "success",
"timezone": "+0000"
},
"@timestamp": "2024-03-06T22:06:04.028578Z",
"action": {
"name": "accept",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "5.6.7.8",
"bytes": 0,
"geo": {
"country_name": "France"
},
"ip": "5.6.7.8",
"packets": 0,
"port": 53
},
"fortinet": {
"fortigate": {
"applist": "EMEA_Monitor",
"apprisk": "elevated",
"event": {
"type": "traffic"
},
"nat_translation_type": "snat",
"policyid": "41",
"policytype": "policy",
"poluuid": "703570eee-edfc-4565-8599-c6a75fd3e1e8",
"sessionid": "538959618",
"virtual_domain": "root"
}
},
"host": {
"name": "example.com",
"os": {
"family": "Windows"
}
},
"log": {
"hostname": "FW-001",
"level": "notice"
},
"network": {
"application": "DNS",
"bytes": 285,
"protocol": "dns",
"transport": "udp"
},
"observer": {
"egress": {
"interface": {
"name": "wan1"
}
},
"hostname": "FW-001",
"ingress": {
"interface": {
"alias": "lan",
"name": "Port3.999"
}
},
"serial_number": "FG100D6G11111111"
},
"related": {
"hosts": [
"FW-001"
],
"ip": [
"1.2.3.4",
"192.0.2.1",
"5.6.7.8"
]
},
"rule": {
"apprisk": "elevated",
"category": "Network.Service",
"ruleset": "EMEA_Monitor"
},
"source": {
"address": "1.2.3.4",
"bytes": 285,
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00",
"nat": {
"ip": "192.0.2.1"
},
"packets": 5,
"port": 62979
}
}
{
"message": "timestamp=1732640381 devname=\"12_LE_XXXXX-60F\" devid=\"xxxxxxxxxxxxxxxxxxx\" vd=\"root\" date=2024-11-26 time=16:59:41 eventtime=1732633180924621531 tz=\"+0200\" logid=\"0000000013\" type=\"traffic\" subtype=\"forward\" level=\"notice\" srcip=1.2.3.4 srcname=\"example.com\" srcport=56745 srcintf=\"internal\" srcintfrole=\"undefined\" dstip=192.0.2.1 dstport=80 dstintf=\"wan1\" dstintfrole=\"undefined\" srccountry=\"Reserved\" dstcountry=\"Egypt\" sessionid=157131884 proto=6 action=\"close\" policyid=12 policytype=\"policy\" poluuid=\"c1353c04-b6ee-51ea-9664-c8541f024774\" policyname=\"LAN to Internet\" service=\"HTTP\" trandisp=\"snat\" transip=192.0.2.1 transport=56745 appid=15893 app=\"HTTP.BROWSER\" appcat=\"Web.Client\" apprisk=\"medium\" applist=\"block-high-risk\" duration=1 sentbyte=483 rcvdbyte=399 sentpkt=7 rcvdpkt=5 wanin=187 wanout=111 lanin=111 lanout=187 utmaction=\"allow\" countweb=1 osname=\"Windows\" srcswversion=\"10\" mastersrcmac=\"02:00:00:00:00:00\" srcmac=\"02:00:00:00:00:00\" srcserver=0",
"event": {
"action": "close",
"category": "traffic",
"code": "0000000013",
"dataset": "traffic:forward",
"duration": 1000000000,
"outcome": "success",
"timezone": "+0200"
},
"@timestamp": "2024-11-26T14:59:40.924622Z",
"action": {
"name": "close",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "192.0.2.1",
"bytes": 399,
"geo": {
"country_name": "Egypt"
},
"ip": "192.0.2.1",
"packets": 5,
"port": 80
},
"fortinet": {
"fortigate": {
"applist": "block-high-risk",
"apprisk": "medium",
"event": {
"type": "traffic"
},
"nat_translation_type": "snat",
"policyid": "12",
"policyname": "LAN to Internet",
"policytype": "policy",
"poluuid": "c1353c04-b6ee-51ea-9664-c8541f024774",
"sessionid": "157131884",
"utmaction": "allow",
"virtual_domain": "root"
}
},
"host": {
"name": "example.com",
"os": {
"family": "Windows"
}
},
"log": {
"hostname": "12_LE_XXXXX-60F",
"level": "notice"
},
"network": {
"application": "HTTP.BROWSER",
"bytes": 882,
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "wan1"
}
},
"hostname": "12_LE_XXXXX-60F",
"ingress": {
"interface": {
"name": "internal"
}
},
"serial_number": "xxxxxxxxxxxxxxxxxxx"
},
"related": {
"hosts": [
"12_LE_XXXXX-60F"
],
"ip": [
"1.2.3.4",
"192.0.2.1"
]
},
"rule": {
"apprisk": "medium",
"category": "Web.Client",
"ruleset": "block-high-risk"
},
"source": {
"address": "1.2.3.4",
"bytes": 483,
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00",
"nat": {
"ip": "192.0.2.1"
},
"packets": 7,
"port": 56745
}
}
{
"message": "logver=704072731 timestamp=1744010938 devname=\"my-device\" devid=\"1111111111111111\" vd=\"root\" date=2025-04-07 time=07:28:58 eventtime=1744010938310787908 logid=\"0000000020\" type=\"traffic\" subtype=\"forward\" level=\"notice\" srcip=1.2.3.4 srcport=55880 srcintf=\"ssl.root\" srcintfrole=\"undefined\" dstip=5.6.7.8 dstport=22 dstintf=\"VLAN-4002\" dstintfrole=\"lan\" srcuuid=\"d24dfae2-ee8d-4319-ac8a-f49fb888f8c3\" dstuuid=\"1949578e-2022-47e4-a779-069cfca42d20\" srccountry=\"Reserved\" dstcountry=\"Reserved\" sessionid=123 proto=6 action=\"accept\" policyid=9 policytype=\"policy\" poluuid=\"194b8d20-da82-4838-ae8c-712bcdb8eba7\" policyname=\"sslvpn_2_prd-vault-net\" user=\"john.doe,cn=john.doe\" group=\"my-group\" service=\"SSH\" trandisp=\"snat\" transip=192.0.2.1 transport=55880 appcat=\"unscanned\" duration=9380 sentbyte=215866 rcvdbyte=515657 sentpkt=2954 rcvdpkt=2055 sentdelta=156 rcvddelta=80 durationdelta=120 sentpktdelta=2 rcvdpktdelta=1 dsthwvendor=\"Fortinet\" dstdevtype=\"Router\" masterdstmac=\"02:00:00:00:00:00\" dstmac=\"02:00:00:00:00:00\" dstserver=0 tz=\"+0000\"",
"event": {
"action": "accept",
"category": "traffic",
"code": "0000000020",
"dataset": "traffic:forward",
"duration": 120000000000,
"outcome": "success",
"timezone": "+0000"
},
"@timestamp": "2025-04-07T07:28:58.310788Z",
"action": {
"name": "accept",
"outcome": "success",
"target": "network-traffic",
"type": "forward"
},
"destination": {
"address": "5.6.7.8",
"bytes": 80,
"ip": "5.6.7.8",
"mac": "02:00:00:00:00:00",
"packets": 1,
"port": 22
},
"fortinet": {
"fortigate": {
"event": {
"type": "traffic"
},
"log_version": "704072731",
"nat_translation_type": "snat",
"policyid": "9",
"policyname": "sslvpn_2_prd-vault-net",
"policytype": "policy",
"poluuid": "194b8d20-da82-4838-ae8c-712bcdb8eba7",
"sessionid": "123",
"total": {
"duration": 9380000000000,
"received_bytes": 515657,
"sent_bytes": 215866,
"sent_packets": 2954
},
"virtual_domain": "root"
}
},
"group": {
"name": "my-group"
},
"log": {
"hostname": "my-device",
"level": "notice"
},
"network": {
"bytes": 236,
"protocol": "ssh",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "lan",
"name": "VLAN-4002"
}
},
"hostname": "my-device",
"ingress": {
"interface": {
"name": "ssl.root"
}
},
"serial_number": "1111111111111111"
},
"related": {
"hosts": [
"my-device"
],
"ip": [
"1.2.3.4",
"192.0.2.1",
"5.6.7.8"
],
"user": [
"john.doe"
]
},
"rule": {
"category": "unscanned",
"ruleset": "policy"
},
"source": {
"address": "1.2.3.4",
"bytes": 156,
"ip": "1.2.3.4",
"nat": {
"ip": "192.0.2.1"
},
"packets": 2,
"port": 55880,
"user": {
"full_name": "john.doe,cn=john.doe",
"name": "john.doe"
}
},
"user": {
"full_name": "john.doe,cn=john.doe",
"name": "john.doe"
}
}
{
"message": "time=10:11:05 devname=MYDEVICE device_id=1111111111111111 log_id=000000001 type=traffic subtype=slb_http pri=information vd=waf msg_id=123456 duration=2742 ibytes=4513 obytes=4518 proto=6 service=\"https\" src=\"1.2.3.4\" src_port=52412 dst=\"5.6.7.8\" dst_port=443 trans_src=\"9.10.11.12\" trans_src_port=56484 trans_dst=\"13.14.15.16\" trans_dst_port=80 policy=\"VS_FRED_PROD_WEB\" action=\"user1\" http_method=\"get\" http_host=\"example.com\" http_agent=\"Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/138.0.0.0 Safari/537.36\" http_url=\"/api/v2/Users\" http_qry=\"ciId=82613&onlyActive=true&/api/v2/Users\" http_referer=\"https://example.com/index\" http_cookie=\"COOKIES\" http_retcode=\"200\" user=\"user1\" usrgrp=\"user1\" auth_status=\"user1\" srccountry=\"Reunion\" dstcountry=\"Reserved\" real_server=\"PROD_WEB01_13.14.15.16\"",
"event": {
"action": "user1",
"category": "traffic",
"duration": 2742000000000,
"outcome": "success"
},
"action": {
"name": "user1",
"outcome": "success",
"target": "network-traffic",
"type": "slb_http"
},
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8"
},
"fortinet": {
"fortigate": {
"event": {
"type": "traffic"
},
"virtual_domain": "waf"
}
},
"http": {
"request": {
"referrer": "https://example.com/index"
}
},
"log": {
"hostname": "MYDEVICE"
},
"network": {
"protocol": "https",
"transport": "tcp"
},
"observer": {
"hostname": "MYDEVICE"
},
"related": {
"hosts": [
"MYDEVICE"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
],
"user": [
"user1"
]
},
"source": {
"address": "1.2.3.4",
"geo": {
"country_name": "Reunion"
},
"ip": "1.2.3.4",
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "logver=60 timestamp=1566916060 tz=\"UTC+2\" devname=\"abc\" devid=\"1\" vd=\"IPSEC\" date=2019-08-27 time=16:27:40 logid=\"0101039949\" type=\"event\" subtype=\"vpn\" level=\"information\" eventtime=1566916060 logdesc=\"SSL VPN statistics\" action=\"tunnel-stats\" tunneltype=\"ssl-tunnel\" tunnelid=1995 remip=1.1.1.1 tunnelip=192.0.2.1 user=\"test\" group=\"GRP_Generic_JAIL_VPN\" dst_host=\"N/A\" nextstat=600 duration=8437 sentbyte=71524041 rcvdbyte=6151809 msg=\"SSL tunnel statistics\"\n",
"event": {
"action": "tunnel-stats",
"category": "event",
"code": "0101039949",
"dataset": "event:vpn",
"duration": 8437000000000,
"outcome": "success",
"reason": "SSL tunnel statistics",
"timezone": "UTC+2"
},
"@timestamp": "2019-08-27T14:27:40Z",
"action": {
"name": "tunnel-stats",
"outcome": "success",
"outcome_reason": "SSL tunnel statistics",
"target": "network-traffic",
"type": "vpn"
},
"destination": {
"bytes": 6151809
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"log_version": "60",
"tunnel": {
"id": "1995",
"ip": "192.0.2.1",
"type": "ssl-tunnel"
},
"virtual_domain": "IPSEC"
}
},
"group": {
"name": "GRP_Generic_JAIL_VPN"
},
"log": {
"description": "SSL VPN statistics",
"hostname": "abc",
"level": "information"
},
"network": {
"bytes": 77675850
},
"observer": {
"hostname": "abc",
"serial_number": "1"
},
"related": {
"hosts": [
"abc"
],
"ip": [
"1.1.1.1",
"192.0.2.1"
],
"user": [
"test"
]
},
"source": {
"address": "1.1.1.1",
"bytes": 71524041,
"ip": "1.1.1.1",
"nat": {
"ip": "192.0.2.1"
},
"user": {
"name": "test"
}
},
"user": {
"name": "test"
}
}
{
"message": " time=12:02:57 devname=\"abc\" devid=\"1\" logid=\"0101037141\" type=\"event\" subtype=\"vpn\" level=\"notice\" vd=\"root\" eventtime=1614855777 logdesc=\"IPsec tunnel statistics\" msg=\"IPsec tunnel statistics\" action=\"tunnel-stats\" remip=1.1.1.1 locip=192.0.2.1 remport=500 locport=500 outintf=\"N/A\" cookies=\"9b064274e0648c03/662c2b1264a2295e\" user=\"N/A\" group=\"N/A\" xauthuser=\"N/A\" xauthgroup=\"N/A\" assignip=N/A vpntunnel=\"VPN-HELPLINE\" tunnelip=N/A tunnelid=0 tunneltype=\"ipsec\" duration=102908570 sentbyte=7649 rcvdbyte=0 nextstat=600",
"event": {
"action": "tunnel-stats",
"category": "event",
"code": "0101037141",
"dataset": "event:vpn",
"duration": 102908570000000000,
"outcome": "success",
"reason": "IPsec tunnel statistics"
},
"@timestamp": "2021-03-04T11:02:57Z",
"action": {
"name": "tunnel-stats",
"outcome": "success",
"outcome_reason": "IPsec tunnel statistics",
"target": "network-traffic",
"type": "vpn"
},
"destination": {
"address": "192.0.2.1",
"bytes": 0,
"ip": "192.0.2.1",
"port": 500
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"tunnel": {
"id": "0",
"name": "VPN-HELPLINE",
"type": "ipsec"
},
"virtual_domain": "root"
}
},
"log": {
"description": "IPsec tunnel statistics",
"hostname": "abc",
"level": "notice"
},
"network": {
"bytes": 7649
},
"observer": {
"hostname": "abc",
"serial_number": "1"
},
"related": {
"hosts": [
"abc"
],
"ip": [
"1.1.1.1",
"192.0.2.1"
]
},
"source": {
"address": "1.1.1.1",
"bytes": 7649,
"ip": "1.1.1.1",
"port": 500
}
}
{
"message": " time=14:38:46 devname=\"abc\" devid=\"1\" logid=\"0101041987\" type=\"event\" subtype=\"vpn\" level=\"information\" vd=\"root\" eventtime=1615469926 logdesc=\"Certificate updated\" action=\"info\" cert-type=\"CRL\" status=\"success\" name=\"CRL_1\" method=\"HTTP\" reason=\"N/A\" msg=\"A certificate is updated\"",
"event": {
"action": "CRL_1",
"category": "event",
"code": "0101041987",
"dataset": "event:vpn",
"outcome": "success",
"provider": "HTTP",
"reason": "A certificate is updated"
},
"@timestamp": "2021-03-11T13:38:46Z",
"action": {
"name": "CRL_1",
"outcome": "success",
"outcome_reason": "A certificate is updated",
"type": "vpn"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"virtual_domain": "root"
}
},
"http": {
"request": {
"method": "HTTP"
}
},
"log": {
"description": "Certificate updated",
"hostname": "abc",
"level": "information"
},
"observer": {
"hostname": "abc",
"serial_number": "1"
},
"related": {
"hosts": [
"abc"
]
}
}
{
"message": "time=17:43:43 devname=\"FW-FOOBAR\" devid=\"FG123\" eventtime=1665675824075327440 tz=\"+0200\" logid=\"0101039426\" type=\"event\" subtype=\"vpn\" level=\"alert\" vd=\"root\" logdesc=\"SSL VPN login fail\" action=\"ssl-login-fail\" tunneltype=\"ssl-web\" tunnelid=0 remip=1.1.1.1 user=\"user1\" group=\"N/A\" dst_host=\"N/A\" reason=\"sslvpn_login_cert_checked_error\" msg=\"SSL user failed to logged in\"",
"event": {
"action": "ssl-login-fail",
"category": "event",
"code": "0101039426",
"dataset": "event:vpn",
"outcome": "failure",
"reason": "sslvpn_login_cert_checked_error",
"timezone": "+0200"
},
"@timestamp": "2022-10-13T15:43:44.075328Z",
"action": {
"name": "ssl-login-fail",
"outcome": "failure",
"outcome_reason": "SSL user failed to logged in",
"type": "vpn"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"tunnel": {
"id": "0",
"type": "ssl-web"
},
"virtual_domain": "root"
}
},
"log": {
"description": "SSL VPN login fail",
"hostname": "FW-FOOBAR",
"level": "alert"
},
"observer": {
"hostname": "FW-FOOBAR",
"serial_number": "FG123"
},
"related": {
"hosts": [
"FW-FOOBAR"
],
"ip": [
"1.1.1.1"
],
"user": [
"user1"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1",
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "time=17:43:43 devname=\"FW-FOOBAR\" devid=\"FG123\" eventtime=1665675824075327440 tz=\"+0200\" logid=\"0101039426\" type=\"event\" subtype=\"vpn\" level=\"alert\" vd=\"root\" logdesc=\"SSL VPN login fail\" action=\"ssl-login-fail\" tunneltype=\"ssl-web\" tunnelid=0 remip=\"N/A\" user=\"user1\" group=\"N/A\" dst_host=\"N/A\" reason=\"sslvpn_login_cert_checked_error\" msg=\"SSL user failed to logged in\"",
"event": {
"action": "ssl-login-fail",
"category": "event",
"code": "0101039426",
"dataset": "event:vpn",
"outcome": "failure",
"reason": "sslvpn_login_cert_checked_error",
"timezone": "+0200"
},
"@timestamp": "2022-10-13T15:43:44.075328Z",
"action": {
"name": "ssl-login-fail",
"outcome": "failure",
"outcome_reason": "SSL user failed to logged in",
"type": "vpn"
},
"fortinet": {
"fortigate": {
"event": {
"type": "event"
},
"tunnel": {
"id": "0",
"type": "ssl-web"
},
"virtual_domain": "root"
}
},
"log": {
"description": "SSL VPN login fail",
"hostname": "FW-FOOBAR",
"level": "alert"
},
"observer": {
"hostname": "FW-FOOBAR",
"serial_number": "FG123"
},
"related": {
"hosts": [
"FW-FOOBAR"
],
"user": [
"user1"
]
},
"source": {
"user": {
"name": "user1"
}
},
"user": {
"name": "user1"
}
}
{
"message": "eventtime=1741260033782633377 tz=\"+0100\" logid=\"0319013317\" type=\"utm\" subtype=\"webfilter\" eventtype=\"urlmonitor\" level=\"notice\" vd=\"root\" policyid=32 poluuid=\"test-pol-uuid\" policytype=\"proxy-policy\" sessionid=1139869359 user=\"user1\" group=\"ADMIN\" authserver=\"TEST_AUTH_SERVER\" srcip=1.2.3.4 srcport=18355 srccountry=\"Japan\" srcintf=\"port2\" srcintfrole=\"lan\" dstip=3.4.5.6 dstport=443 dstcountry=\"United States\" dstintf=\"Orange_Pro\" dstintfrole=\"wan\" proto=6 service=\"HTTPS\" hostname=\"example.com\" profile=\"TEST_AUTH_SERVER Web Defaut\" action=\"passthrough\" reqtype=\"direct\" url=\"https://example.com/\" sentbyte=421 rcvdbyte=0 direction=\"outgoing\" msg=\"URL has been visited\" method=\"ip\" cat=255",
"event": {
"action": "passthrough",
"category": "utm",
"code": "0319013317",
"outcome": "success",
"provider": "ip",
"reason": "URL has been visited",
"timezone": "+0100"
},
"@timestamp": "2025-03-06T11:20:33.782634Z",
"action": {
"name": "passthrough",
"outcome": "success",
"outcome_reason": "URL has been visited",
"target": "network-traffic",
"type": "webfilter"
},
"destination": {
"address": "3.4.5.6",
"bytes": 0,
"domain": "example.com",
"geo": {
"country_name": "United States"
},
"ip": "3.4.5.6",
"port": 443
},
"fortinet": {
"fortigate": {
"event": {
"type": "utm"
},
"method": "ip",
"policyid": "32",
"policytype": "proxy-policy",
"poluuid": "test-pol-uuid",
"security_profile": "TEST_AUTH_SERVER Web Defaut",
"sessionid": "1139869359",
"virtual_domain": "root"
}
},
"group": {
"name": "ADMIN"
},
"log": {
"level": "notice"
},
"network": {
"bytes": 421,
"direction": "outbound",
"protocol": "https",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"alias": "wan",
"name": "Orange_Pro"
}
},
"ingress": {
"interface": {
"alias": "lan",
"name": "port2"
}
}
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4",
"3.4.5.6"
],
"user": [
"user1"
]
},
"rule": {
"ruleset": "proxy-policy"
},
"source": {
"address": "1.2.3.4",
"bytes": 421,
"geo": {
"country_name": "Japan"
},
"ip": "1.2.3.4",
"port": 18355,
"user": {
"name": "user1"
}
},
"url": {
"domain": "example.com",
"full": "https://example.com/",
"original": "https://example.com/",
"path": "/",
"port": 443,
"registered_domain": "example.com",
"scheme": "https",
"top_level_domain": "com"
},
"user": {
"name": "user1"
}
}
{
"message": "time=12:20:33 devname=\"testDev\" devid=\"FGVM2VTM21000062\" eventtime=1741260033527521837 tz=\"+0100\" logid=\"0317013312\" type=\"utm\" subtype=\"webfilter\" eventtype=\"ftgd_allow\" level=\"notice\" vd=\"root\" policyid=106 poluuid=\"test-pol-uuid\" policytype=\"policy\" sessionid=958259665 srcip=1.2.3.4 srcport=55377 srccountry=\"Reserved\" srcintf=\"T_testDev\" srcintfrole=\"undefined\" srcuuid=\"test-src-uuid\" dstip=3.4.5.6 dstport=80 dstcountry=\"France\" dstintf=\"port4\" dstintfrole=\"undefined\" dstuuid=\"test-dst-uuid\" proto=6 service=\"HTTP\" hostname=\"example.com\" profile=\"Filtrage_web_Avanc\u00e9\" action=\"passthrough\" reqtype=\"direct\" url=\"http://example.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%123123123%3D\" sentbyte=400 rcvdbyte=0 direction=\"outgoing\" msg=\"URL belongs to an allowed category in policy\" method=\"domain\" cat=50 catdesc=\"Information and Computer Security\"",
"event": {
"action": "passthrough",
"category": "utm",
"code": "0317013312",
"outcome": "success",
"provider": "domain",
"reason": "URL belongs to an allowed category in policy",
"timezone": "+0100"
},
"@timestamp": "2025-03-06T11:20:33.527522Z",
"action": {
"name": "passthrough",
"outcome": "success",
"outcome_reason": "URL belongs to an allowed category in policy",
"target": "network-traffic",
"type": "webfilter"
},
"destination": {
"address": "3.4.5.6",
"bytes": 0,
"domain": "example.com",
"geo": {
"country_name": "France"
},
"ip": "3.4.5.6",
"port": 80
},
"fortinet": {
"fortigate": {
"event": {
"type": "utm"
},
"method": "domain",
"policyid": "106",
"policytype": "policy",
"poluuid": "test-pol-uuid",
"security_profile": "Filtrage_web_Avanc\u00e9",
"sessionid": "958259665",
"virtual_domain": "root"
}
},
"log": {
"hostname": "testDev",
"level": "notice"
},
"network": {
"bytes": 400,
"direction": "outbound",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port4"
}
},
"hostname": "testDev",
"ingress": {
"interface": {
"name": "T_testDev"
}
},
"serial_number": "FGVM2VTM21000062"
},
"related": {
"hosts": [
"example.com",
"testDev"
],
"ip": [
"1.2.3.4",
"3.4.5.6"
]
},
"rule": {
"category": "Information and Computer Security",
"ruleset": "policy"
},
"source": {
"address": "1.2.3.4",
"bytes": 400,
"ip": "1.2.3.4",
"port": 55377
},
"url": {
"domain": "example.com",
"full": "http://example.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%123123123%3D",
"original": "http://example.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%123123123%3D",
"path": "/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%123123123%3D",
"port": 80,
"registered_domain": "example.com",
"scheme": "http",
"top_level_domain": "com"
}
}
{
"message": "CEF:0|Fortinet|Fortigate|v6.0.3|13056|utm:webfilter ftgd_blk blocked|4|deviceExternalId=FGT5HD3915800610 FTNTFGTlogid=0316013056 cat=utm:webfilter FTNTFGTsubtype=webfilter FTNTFGTeventtype=ftgd_blk FTNTFGTlevel=warning FTNTFGTvd=vdom1 FTNTFGTeventtime=1545938629 FTNTFGTpolicyid=1 externalId=764 duser=example.com\\\\\\\\bob src=10.1.100.11 spt=59194 deviceInboundInterface=port12 FTNTFGTsrcintfrole=undefined dst=192.0.2.1 dpt=80 deviceOutboundInterface=port11 FTNTFGTdstintfrole=undefined proto=6 app=HTTP dhost=example.com FTNTFGTprofile=g-default act=blocked FTNTFGTreqtype=direct request=/bizsquads out=96 in=0 deviceDirection=1 msg=URL belongs to a denied category in policy FTNTFGTmethod=domain FTNTFGTcat=26 requestContext=Malicious Websites FTNTFGTcrscore=60 FTNTFGTcrlevel=high",
"event": {
"action": "blocked",
"category": "utm",
"code": "0316013056",
"dataset": "utm:webfilter",
"outcome": "success",
"provider": "domain",
"reason": "URL belongs to a denied category in policy"
},
"@timestamp": "2018-12-27T19:23:49Z",
"action": {
"name": "blocked",
"outcome": "success",
"outcome_reason": "URL belongs to a denied category in policy",
"target": "network-traffic",
"type": "webfilter"
},
"destination": {
"address": "192.0.2.1",
"bytes": 0,
"domain": "example.com",
"ip": "192.0.2.1",
"port": 80,
"user": {
"domain": "example.com",
"name": "bob"
}
},
"fortinet": {
"fortigate": {
"method": "domain",
"policyid": "1",
"security_profile": "g-default",
"threat": {
"level": "high",
"score": 60
},
"virtual_domain": "vdom1"
}
},
"log": {
"level": "warning"
},
"network": {
"application": "HTTP",
"bytes": 96,
"direction": "outbound",
"protocol": "http",
"transport": "tcp"
},
"observer": {
"egress": {
"interface": {
"name": "port11"
}
},
"ingress": {
"interface": {
"name": "port12"
}
},
"serial_number": "FGT5HD3915800610",
"type": "Fortigate",
"vendor": "Fortinet",
"version": "v6.0.3"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"10.1.100.11",
"192.0.2.1"
],
"user": [
"bob"
]
},
"rule": {
"category": "Malicious Websites"
},
"source": {
"address": "10.1.100.11",
"bytes": 96,
"ip": "10.1.100.11",
"port": 59194
},
"url": {
"original": "/bizsquads",
"path": "/bizsquads"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
action.properties.icmp_code |
keyword |
ICMP code (backward compatibility) |
action.properties.icmp_type |
keyword |
ICMP type (backward compatibility) |
action.target |
keyword |
Target of the action (backward compatibility) |
destination.address |
keyword |
Destination network address. |
destination.bytes |
long |
Bytes sent from the destination to the source. |
destination.domain |
keyword |
The domain name of the destination. |
destination.geo.city_name |
keyword |
City name. |
destination.geo.country_name |
keyword |
Country name. |
destination.geo.region_name |
keyword |
Region name. |
destination.ip |
ip |
IP address of the destination. |
destination.mac |
keyword |
MAC address of the destination. |
destination.nat.ip |
ip |
Destination NAT ip |
destination.nat.port |
long |
Destination NAT Port |
destination.packets |
long |
Packets sent from the destination to the source. |
destination.port |
long |
Port of the destination. |
destination.user.domain |
keyword |
Name of the directory the user is a member of. |
destination.user.full_name |
keyword |
User's full name, if available. |
destination.user.name |
keyword |
Short name or login of the user. |
dns.question.class |
keyword |
The class of records being queried. |
dns.question.name |
keyword |
The name being queried. |
dns.question.type |
keyword |
The type of record being queried. |
dns.rrname |
keyword |
DNS requested name (backward compatibility) |
dns.rrtype |
keyword |
DNS request type (backward compatibility) |
event.action |
keyword |
The action captured by the event. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.code |
keyword |
Identification code for this event. |
event.dataset |
keyword |
Name of the dataset. |
event.duration |
long |
Duration of the event in nanoseconds. |
event.provider |
keyword |
Source of the event. |
event.reason |
keyword |
Reason why this event happened, according to the source |
event.start |
date |
event.start contains the date when the event started or when the activity was first observed. |
event.timezone |
keyword |
Event time zone. |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
file.name |
keyword |
Name of the file including the extension, without the directory. |
file.size |
long |
File size in bytes. |
fortinet.fortigate.applist |
keyword |
|
fortinet.fortigate.apprisk |
keyword |
Risk level of the application. |
fortinet.fortigate.attack.id |
keyword |
ID of the detected attack |
fortinet.fortigate.attack.name |
keyword |
Name of the detected attack |
fortinet.fortigate.cfgattr |
keyword |
Configuration attribute |
fortinet.fortigate.cfgpath |
keyword |
Configuration path |
fortinet.fortigate.cfgtid |
keyword |
Transaction ID of the configuration |
fortinet.fortigate.dst_internet_service |
keyword |
Destination Internet Service |
fortinet.fortigate.dst_reputation |
integer |
Destination reputation |
fortinet.fortigate.event.desc |
keyword |
Type of log. |
fortinet.fortigate.event.severity |
keyword |
Anomaly severity as reported by Fortigate |
fortinet.fortigate.event.type |
keyword |
Type of the event. |
fortinet.fortigate.icmp.request.code |
keyword |
The request code. |
fortinet.fortigate.icmp.request.type |
keyword |
The request type. |
fortinet.fortigate.log_version |
keyword |
Log version |
fortinet.fortigate.logdev.id |
keyword |
ID of the device that generated the log. |
fortinet.fortigate.logdev.last_logging |
date |
Last logging time of the device. |
fortinet.fortigate.logdev.name |
keyword |
Name of the device that generated the log. |
fortinet.fortigate.method |
keyword |
|
fortinet.fortigate.nat_translation_type |
keyword |
NAT translation type. |
fortinet.fortigate.policyid |
keyword |
ID of the policy |
fortinet.fortigate.policyname |
keyword |
Policy name |
fortinet.fortigate.policytype |
keyword |
Policy type |
fortinet.fortigate.poluuid |
keyword |
UUID of pol |
fortinet.fortigate.security_profile |
keyword |
Name of the security profile used in the event |
fortinet.fortigate.sessionid |
keyword |
Session ID |
fortinet.fortigate.sn |
keyword |
Serial number of the security fabric |
fortinet.fortigate.src_internet_service |
keyword |
Source Internet Service |
fortinet.fortigate.threat.level |
keyword |
Threat level of the event |
fortinet.fortigate.threat.score |
long |
Threat score of the event |
fortinet.fortigate.threat.type |
long |
Threat type of the event |
fortinet.fortigate.total.duration |
long |
Duration in nanoseconds of the whole event |
fortinet.fortigate.total.received_bytes |
long |
Total of bytes which are received during the whole event |
fortinet.fortigate.total.received_packets |
long |
Total of packets which are received during the whole event |
fortinet.fortigate.total.sent_bytes |
long |
Total of bytes which are sent during the whole event |
fortinet.fortigate.total.sent_packets |
long |
Total of packets which are sent during the whole event |
fortinet.fortigate.tunnel.id |
keyword |
The id of the tunnel |
fortinet.fortigate.tunnel.ip |
keyword |
The ip of the tunnel |
fortinet.fortigate.tunnel.name |
keyword |
The name of the tunnel |
fortinet.fortigate.tunnel.type |
keyword |
The type of the tunnel |
fortinet.fortigate.tunnel.version |
keyword |
The version of the tunnel |
fortinet.fortigate.user.source |
keyword |
The source of the username |
fortinet.fortigate.utmaction |
keyword |
UTM action taken by Fortigate |
fortinet.fortigate.virtual_domain |
keyword |
Name of the virtual domain in which the event was observed |
fortinet.fortigate.vpntype |
keyword |
VPN type |
group.name |
keyword |
Name of the group. |
host.name |
keyword |
Name of the host. |
host.os.family |
keyword |
OS family (such as redhat, debian, freebsd, windows). |
http.request.method |
keyword |
HTTP request method. |
http.request.referrer |
keyword |
Referrer for this HTTP request. |
log.level |
keyword |
Log level of the log event. |
network.application |
keyword |
Application level protocol name. |
network.bytes |
long |
Total bytes transferred in both directions. |
network.forwarded_ip |
ip |
Host IP address when the source IP address is the proxy. |
network.protocol |
keyword |
Application protocol name. |
network.transport |
keyword |
Protocol Name corresponding to the field iana_number. |
observer.egress.interface.alias |
keyword |
Interface alias |
observer.egress.interface.name |
keyword |
Interface name |
observer.hostname |
keyword |
Hostname of the observer. |
observer.ingress.interface.alias |
keyword |
Interface alias |
observer.ingress.interface.name |
keyword |
Interface name |
observer.serial_number |
keyword |
Observer serial number. |
observer.type |
keyword |
The type of the observer the data is coming from. |
observer.vendor |
keyword |
Vendor name of the observer. |
observer.version |
keyword |
Observer version. |
rule.apprisk |
keyword |
App risk reported by Fortigate (backward compatibility) |
rule.category |
keyword |
Rule category |
rule.ruleset |
keyword |
Rule ruleset |
source.bytes |
long |
Bytes sent from the source to the destination. |
source.domain |
keyword |
The domain name of the source. |
source.geo.country_name |
keyword |
Country name. |
source.ip |
ip |
IP address of the source. |
source.mac |
keyword |
MAC address of the source. |
source.nat.ip |
ip |
Source NAT ip |
source.nat.port |
long |
Source NAT port |
source.packets |
long |
Packets sent from the source to the destination. |
source.port |
long |
Port of the source. |
source.user.domain |
keyword |
Name of the directory the user is a member of. |
source.user.full_name |
keyword |
User's full name, if available. |
source.user.name |
keyword |
Short name or login of the user. |
url.full |
wildcard |
Full unparsed URL. |
url.original |
wildcard |
Unmodified original url as seen in the event source. |
user.domain |
keyword |
Name of the directory the user is a member of. |
user.full_name |
keyword |
User's full name, if available. |
user.name |
keyword |
Short name or login of the user. |
user_agent.original |
keyword |
Unparsed user_agent string. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.