Juniper Next Gen Firewall
Overview
Juniper Next-Generation Firewall (NGFW) services provide a set of cyber defenses that, together, reduce your attack surface. With the SRX Series firewall and Juniper Secure Edge at their core, high-performance NGFW services deliver integrated threat protection, application recognition, user identification services, and large-scale content inspection.
- Vendor: Juniper
- Supported environment: On Premise
- Detection based on: Telemetry
- Supported application or feature: Firewall logs
Warning
Important note - This format is currently in beta. We highly value your feedback to improve its performance.
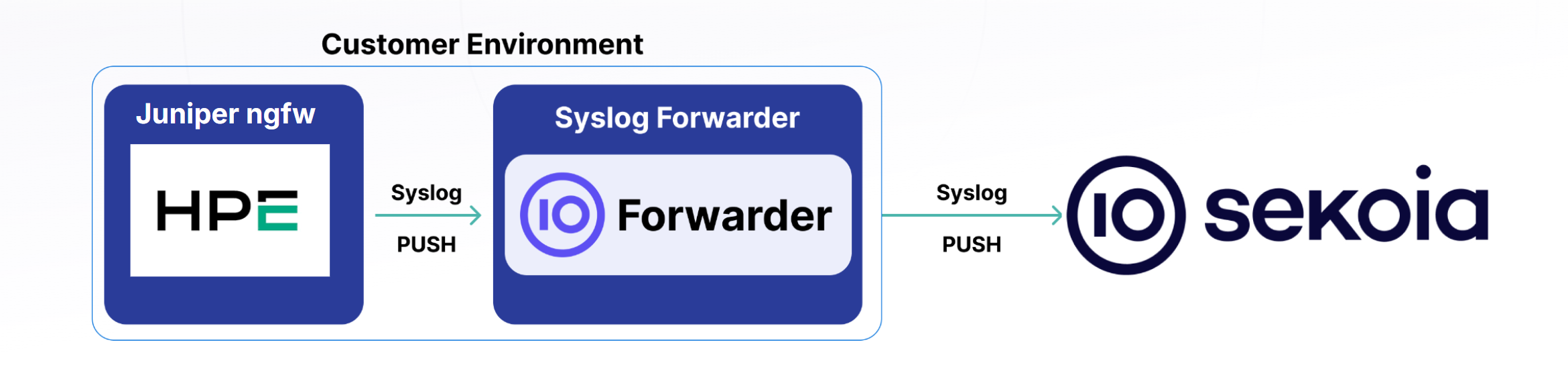
High-Level Architecture Diagram
- Type of integration: Outbound (PUSH to Sekoia.io)
- Schema
Specification
Prerequisites
- Resource:
- Self-managed syslog forwarder
- Network:
- Outbound traffic allowed
- Permissions:
- Root access to the Juniper appliance
- Root access to the Linux server with the syslog forwarder
Transport Protocol/Method
- Indirect Syslog
Logs details
- Supported functionalities: See section Overview
- Supported type(s) of structure: Syslog
- Supported verbosity level: Informational
Note
Log levels are based on the taxonomy of RFC5424. Adapt according to the terminology used by the editor.
Step-by-Step Quick Configuration Procedure
- Log in to your Juniper NGFW appliance.
-
Set up the log service :
Note : if your security policy requires extra-security (ex: tls) between the application and the syslog forwarder, modify the configuration accordingly
set security log mode stream set security log format syslog set security log source-interface {CHANGE_WITH_YOUR_INTERFACE}} -
Set up the destination log server (forwarder) parameters :
Note : if your security policy requires extra-security (ex: tls) between the application and the syslog forwarder, modify the configuration accordingly
set security log stream sekoia_forwarder format syslog set security log stream sekoia_forwarder host {IP_OF_YOUR_SEKOIA_FORWARDER} port {SEKOIA_FORWARDER_SPECIFIC_PORT} set security log stream sekoia_forwarder category {ADAPT_TO_YOUR_NEEDS}
Note
If you encounter any issues during the configuration specified in this section "Instructions on the 3rd Party Solution," please do not hesitate to contact your editor. We also welcome any suggestions for improving our documentation to better serve your needs.
Instruction on Sekoia
Configure Your Intake
This section will guide you through creating the intake object in Sekoia, which provides a unique identifier called the "Intake key." The Intake key is essential for later configuration, as it references the Community, Entity, and Parser (Intake Format) used when receiving raw events on Sekoia.
- Go to the Sekoia Intake page.
- Click on the
+ New Intakebutton at the top right of the page. - Search for your Intake by the product name in the search bar.
- Give it a Name and associate it with an Entity (and a Community if using multi-tenant mode).
- Click on
Create.
Note
For more details on how to use the Intake page and to find the Intake key you just created, refer to this documentation.
Configure a forwarder
To forward events using syslog to Sekoia.io, you need to update the syslog header with the intake key you previously created. Here is an example of your message before the forwarder
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG RAW_MESSAGE
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG [SEKOIA@53288 intake_key=\"YOUR_INTAKE_KEY\"] RAW_MESSAGE
To achieve this you can:
- Use the Sekoia.io forwarder which is the official supported way to collect data using the syslog protocol in Sekoia.io. In charge of centralizing data coming from many equipments/sources and forwarding them to Sekoia.io with the apporpriated format, it is a prepackaged option. You only have to provide your intake key as parameter.
- Use your own Syslog service instance. Maybe you already have an intance of one of these components on your side and want to reuse it in order to centralize data before forwarding them to Sekoia.io. When using this mode, you have to configure and maintain your component in order to respect the expected Sekoia.io format.
Warning
Only the Sekoia.io forwarder is officially supported. Other options are documented for reference purposes but do not have official support.
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
l2ald[111111]: L2ALD_ST_CTL_IN_EFFECT: ge-1/0/10.0: storm control in effect on the port
RT_FLOW_SESSION_CLOSE: session closed TCP CLIENT RST: 1.2.3.4/37769->5.6.7.8/25 0x0 junos-smtp 1.2.3.4/37769->5.6.7.8/25 0x0 N/A N/A static rule FML03P_SMTP03 6 Internet_to_AAAA_FO_002 Internet AAAA_FO 154619140403 60(52906) 47(26103) 3 UNKNOWN UNKNOWN N/A(N/A) reth2.1010 UNKNOWN N/A N/A -1 N/A NA 0 0.0.0.0/0->0.0.0.0/0 NA NA N/A N/A Off root 0 N/A N/A N/A N/A N/A
RT_FLOW_SESSION_CLOSE [junos@2636.1.1.1.2.142 reason="TCP FIN" source-address="192.168.1.1" source-port="56732" destination-address="192.168.1.2" destination-port="8080" connection-tag="0" service-name="None" nat-source-address="192.168.1.1" nat-source-port="56732" nat-destination-address="192.168.1.2" nat-destination-port="8080" nat-connection-tag="0" src-nat-rule-type="N/A" src-nat-rule-name="N/A" dst-nat-rule-type="N/A" dst-nat-rule-name="N/A" protocol-id="6" policy-name="AAAAA_IP-RULE_to_PROXY(global)" source-zone-name="custom_zone_name" destination-zone-name="custom_zone_name2" session-id="107377361044" packets-from-client="17" bytes-from-client="3676" packets-from-server="13" bytes-from-server="7867" elapsed-time="2" application="UNKNOWN" nested-application="UNKNOWN" username="N/A" roles="N/A" packet-incoming-interface="reth0.3252" encrypted="UNKNOWN" application-category="N/A" application-sub-category="N/A" application-risk="-1" application-characteristics="N/A" secure-web-proxy-session-type="NA" peer-session-id="0" peer-source-address="0.0.0.0" peer-source-port="0" peer-destination-address="0.0.0.0" peer-destination-port="0" hostname="NA NA" src-vrf-grp="N/A" dst-vrf-grp="N/A" tunnel-inspection="Off" tunnel-inspection-policy-set="root" session-flag="0" source-tenant="N/A" destination-service="N/A"]
RT_FLOW_SESSION_CREATE: session created 1.2.3.4/46087->5.6.7.8/25 0x0 junos-smtp 1.2.3.4/46087->5.6.7.8/25 0x0 N/A N/A static rule FML03P_SMTP03 6 Internet_to_AAAA_FO_002 Internet AAAA_FO 158913894867 N/A(N/A) reth2.1010 UNKNOWN UNKNOWN UNKNOWN N/A N/A -1 N/A N/A N/A Off root N/A N/A N/A N/A
RT_FLOW_SESSION_DENY [junos@2636.1.1.1.2.142 source-address="192.168.1.11" source-port="62224" destination-address="192.168.1.12" destination-port="443" connection-tag="0" service-name="junos-https" protocol-id="6" icmp-type="0" policy-name="POLICY_DENY_all" source-zone-name="custom_zone_name" destination-zone-name="custom_zone_name2" application="UNKNOWN" nested-application="UNKNOWN" username="N/A" roles="N/A" packet-incoming-interface="reth0.3249" encrypted="No" reason="Denied by policy" session-id="25775358241" application-category="N/A" application-sub-category="N/A" application-risk="-1" application-characteristics="N/A" src-vrf-grp="N/A" dst-vrf-grp="N/A" source-tenant="N/A" destination-service="N/A"]
RT_SCREEN_ICMP [attack-name="Address sweep!" source-address="192.168.1.2" destination-address="192.168.1.1" source-zone-name="custom_zone_name" interface-name="reth1.603" action="alarm-without-drop"]
xntpd: kernel time sync enabled 2001
mgd[94759]: UI_AUTH_EVENT: Authenticated user 'jdoe' assigned to class 'super-user'
mgd[8682]: UI_CHILD_START: Starting child '/usr/libexec/ui/ntpsync'
mgd[78145]: UI_CHILD_STATUS: Cleanup child '/sbin/ifinfo', PID 78147, status 0
mgd[22688]: UI_CMDLINE_READ_LINE: User 'jdoe' command 'show configuration system | display inheritance defaults | display xml | match host-name | no-more '
mgd[31767]: UI_JUNOSCRIPT_CMD: User 'jdoe' used JUNOScript client to run command 'request-authentication user=root logname=root host=localhost agent=mgd current-directory=/var/home/remote_superuser pid=31501 ppid=18835'
mgd[54999]: UI_LOGIN_EVENT: User 'jdoe' login, class 'j-ids' [54999], ssh-connection '192.168.1.1 40382 192.168.1.2 22', client-mode 'cli'
mgd[87462]: UI_LOGOUT_EVENT: User 'root' logout
1,2025/08/07 10:59:08,016301006286,SYSTEM,auth,2817,2025/08/07 10:59:09,,auth-success,Auth_Seq_RAH,0,0,general,informational,"Kerberos SSO authenticated for user 'jdoe'. realm 'test.local', auth profile 'Auth_Seq_RAH', vsys 'shared',",7503878598546507619,0x0,0,0,0,0,,localhost,0,0,2025-08-07T10:59:09.193+02:00
/usr/sbin/cron[41404]: (root) CMD ( sh /var/etc/ukern_gbl_rotate.sh)
/usr/sbin/cron[36324]: (root) MAIL (mailed 39 bytes of output but got status 0x0001 )
keyadmin[95280]: dump_assn: found old association 192.168.1.1:179 md5 00000003:0x3356785a4e5949306c
rshd[93991]: root@192.168.1.1 as root: cmd='rcp -t //var/etc/dynamic_address.id+'
sshd[88235]: Failed password for jdoe from 192.168.1.1 port 60002 ssh2
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Network device logs |
None |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | alert, event |
| Category | `` |
| Type | `` |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "l2ald[111111]: L2ALD_ST_CTL_IN_EFFECT: ge-1/0/10.0: storm control in effect on the port",
"event": {
"action": "L2ALD_ST_CTL_IN_EFFECT",
"category": [
"network"
],
"kind": "event",
"provider": "l2ald",
"type": [
"info"
]
},
"log": {
"description": "ge-1/0/10.0: storm control in effect on the port"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
}
}
{
"message": "RT_FLOW_SESSION_CLOSE: session closed TCP CLIENT RST: 1.2.3.4/37769->5.6.7.8/25 0x0 junos-smtp 1.2.3.4/37769->5.6.7.8/25 0x0 N/A N/A static rule FML03P_SMTP03 6 Internet_to_AAAA_FO_002 Internet AAAA_FO 154619140403 60(52906) 47(26103) 3 UNKNOWN UNKNOWN N/A(N/A) reth2.1010 UNKNOWN N/A N/A -1 N/A NA 0 0.0.0.0/0->0.0.0.0/0 NA NA N/A N/A Off root 0 N/A N/A N/A N/A N/A",
"event": {
"action": "RT_FLOW_SESSION_CLOSE",
"category": [
"network",
"session"
],
"dataset": "RT_FLOW",
"duration": 3000000000,
"kind": "event",
"outcome": "success",
"reason": "TCP CLIENT RST",
"type": [
"connection",
"end"
]
},
"destination": {
"address": "5.6.7.8",
"bytes": 26103,
"ip": "5.6.7.8",
"nat": {
"ip": "5.6.7.8",
"port": 25
},
"packets": 47,
"port": 25
},
"juniper": {
"ngfw": {
"application": {
"risk": "-1"
},
"connection_tag": "0",
"destination": {
"nat": {
"rule": {
"name": "FML03P_SMTP03",
"type": "static rule"
}
}
},
"flow": {
"encrypted": false
},
"nat": {
"connection_tag": "0"
},
"policy": {
"name": "Internet_to_AAAA_FO_002"
},
"tunnel": {
"inspection": false
}
}
},
"log": {
"description": "session closed TCP CLIENT RST: 1.2.3.4/37769->5.6.7.8/25 0x0 junos-smtp 1.2.3.4/37769->5.6.7.8/25 0x0 N/A N/A static rule FML03P_SMTP03 6 Internet_to_AAAA_FO_002 Internet AAAA_FO 154619140403 60(52906) 47(26103) 3 UNKNOWN UNKNOWN N/A(N/A) reth2.1010 UNKNOWN N/A N/A -1 N/A NA 0 0.0.0.0/0->0.0.0.0/0 NA NA N/A N/A Off root 0 N/A N/A N/A N/A N/A",
"syslog": {
"appname": "RT_FLOW"
}
},
"network": {
"iana_number": "6"
},
"observer": {
"egress": {
"zone": "AAAA_FO"
},
"ingress": {
"interface": {
"name": "reth2.1010"
},
"zone": "Internet"
},
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"related": {
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"service": {
"name": "junos-smtp"
},
"source": {
"address": "1.2.3.4",
"bytes": 52906,
"ip": "1.2.3.4",
"nat": {
"ip": "1.2.3.4",
"port": 37769
},
"packets": 60,
"port": 37769
}
}
{
"message": "RT_FLOW_SESSION_CLOSE [junos@2636.1.1.1.2.142 reason=\"TCP FIN\" source-address=\"192.168.1.1\" source-port=\"56732\" destination-address=\"192.168.1.2\" destination-port=\"8080\" connection-tag=\"0\" service-name=\"None\" nat-source-address=\"192.168.1.1\" nat-source-port=\"56732\" nat-destination-address=\"192.168.1.2\" nat-destination-port=\"8080\" nat-connection-tag=\"0\" src-nat-rule-type=\"N/A\" src-nat-rule-name=\"N/A\" dst-nat-rule-type=\"N/A\" dst-nat-rule-name=\"N/A\" protocol-id=\"6\" policy-name=\"AAAAA_IP-RULE_to_PROXY(global)\" source-zone-name=\"custom_zone_name\" destination-zone-name=\"custom_zone_name2\" session-id=\"107377361044\" packets-from-client=\"17\" bytes-from-client=\"3676\" packets-from-server=\"13\" bytes-from-server=\"7867\" elapsed-time=\"2\" application=\"UNKNOWN\" nested-application=\"UNKNOWN\" username=\"N/A\" roles=\"N/A\" packet-incoming-interface=\"reth0.3252\" encrypted=\"UNKNOWN\" application-category=\"N/A\" application-sub-category=\"N/A\" application-risk=\"-1\" application-characteristics=\"N/A\" secure-web-proxy-session-type=\"NA\" peer-session-id=\"0\" peer-source-address=\"0.0.0.0\" peer-source-port=\"0\" peer-destination-address=\"0.0.0.0\" peer-destination-port=\"0\" hostname=\"NA NA\" src-vrf-grp=\"N/A\" dst-vrf-grp=\"N/A\" tunnel-inspection=\"Off\" tunnel-inspection-policy-set=\"root\" session-flag=\"0\" source-tenant=\"N/A\" destination-service=\"N/A\"]",
"event": {
"action": "RT_FLOW_SESSION_CLOSE",
"category": [
"network",
"session"
],
"dataset": "RT_FLOW",
"duration": 2000000000,
"kind": "event",
"outcome": "success",
"reason": "TCP FIN",
"type": [
"connection",
"end"
]
},
"destination": {
"address": "192.168.1.2",
"bytes": 7867,
"ip": "192.168.1.2",
"nat": {
"ip": "192.168.1.2",
"port": 8080
},
"packets": 13,
"port": 8080
},
"juniper": {
"ngfw": {
"application": {
"risk": "-1"
},
"connection_tag": "0",
"flow": {
"encrypted": false
},
"nat": {
"connection_tag": "0"
},
"policy": {
"name": "AAAAA_IP-RULE_to_PROXY(global)"
},
"tunnel": {
"inspection": false
}
}
},
"log": {
"syslog": {
"appname": "RT_FLOW"
}
},
"network": {
"iana_number": "6"
},
"observer": {
"egress": {
"zone": "custom_zone_name2"
},
"ingress": {
"interface": {
"name": "reth0.3252"
},
"zone": "custom_zone_name"
},
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"related": {
"ip": [
"192.168.1.1",
"192.168.1.2"
]
},
"source": {
"address": "192.168.1.1",
"bytes": 3676,
"ip": "192.168.1.1",
"nat": {
"ip": "192.168.1.1",
"port": 56732
},
"packets": 17,
"port": 56732
}
}
{
"message": "RT_FLOW_SESSION_CREATE: session created 1.2.3.4/46087->5.6.7.8/25 0x0 junos-smtp 1.2.3.4/46087->5.6.7.8/25 0x0 N/A N/A static rule FML03P_SMTP03 6 Internet_to_AAAA_FO_002 Internet AAAA_FO 158913894867 N/A(N/A) reth2.1010 UNKNOWN UNKNOWN UNKNOWN N/A N/A -1 N/A N/A N/A Off root N/A N/A N/A N/A",
"event": {
"action": "RT_FLOW_SESSION_CREATE",
"category": [
"network",
"session"
],
"dataset": "RT_FLOW",
"kind": "event",
"outcome": "success",
"type": [
"connection",
"start"
]
},
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8",
"nat": {
"ip": "5.6.7.8",
"port": 25
},
"port": 25
},
"juniper": {
"ngfw": {
"application": {
"risk": "-1"
},
"connection_tag": "0",
"destination": {
"nat": {
"rule": {
"name": "FML03P_SMTP03",
"type": "static rule"
}
}
},
"flow": {
"encrypted": false
},
"nat": {
"connection_tag": "0"
},
"policy": {
"name": "Internet_to_AAAA_FO_002"
},
"tunnel": {
"inspection": false
}
}
},
"log": {
"description": "session created 1.2.3.4/46087->5.6.7.8/25 0x0 junos-smtp 1.2.3.4/46087->5.6.7.8/25 0x0 N/A N/A static rule FML03P_SMTP03 6 Internet_to_AAAA_FO_002 Internet AAAA_FO 158913894867 N/A(N/A) reth2.1010 UNKNOWN UNKNOWN UNKNOWN N/A N/A -1 N/A N/A N/A Off root N/A N/A N/A N/A",
"syslog": {
"appname": "RT_FLOW"
}
},
"network": {
"iana_number": "6"
},
"observer": {
"egress": {
"zone": "AAAA_FO"
},
"ingress": {
"interface": {
"name": "reth2.1010"
},
"zone": "Internet"
},
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"related": {
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"service": {
"name": "junos-smtp"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"nat": {
"ip": "1.2.3.4",
"port": 46087
},
"port": 46087
}
}
{
"message": "RT_FLOW_SESSION_DENY [junos@2636.1.1.1.2.142 source-address=\"192.168.1.11\" source-port=\"62224\" destination-address=\"192.168.1.12\" destination-port=\"443\" connection-tag=\"0\" service-name=\"junos-https\" protocol-id=\"6\" icmp-type=\"0\" policy-name=\"POLICY_DENY_all\" source-zone-name=\"custom_zone_name\" destination-zone-name=\"custom_zone_name2\" application=\"UNKNOWN\" nested-application=\"UNKNOWN\" username=\"N/A\" roles=\"N/A\" packet-incoming-interface=\"reth0.3249\" encrypted=\"No\" reason=\"Denied by policy\" session-id=\"25775358241\" application-category=\"N/A\" application-sub-category=\"N/A\" application-risk=\"-1\" application-characteristics=\"N/A\" src-vrf-grp=\"N/A\" dst-vrf-grp=\"N/A\" source-tenant=\"N/A\" destination-service=\"N/A\"]",
"event": {
"action": "RT_FLOW_SESSION_DENY",
"category": [
"network",
"session"
],
"dataset": "RT_FLOW",
"kind": "event",
"outcome": "success",
"reason": "Denied by policy",
"type": [
"connection",
"denied",
"start"
]
},
"destination": {
"address": "192.168.1.12",
"ip": "192.168.1.12",
"port": 443
},
"juniper": {
"ngfw": {
"application": {
"risk": "-1"
},
"connection_tag": "0",
"flow": {
"encrypted": false
},
"policy": {
"name": "POLICY_DENY_all"
}
}
},
"log": {
"syslog": {
"appname": "RT_FLOW"
}
},
"network": {
"iana_number": "6"
},
"observer": {
"egress": {
"zone": "custom_zone_name2"
},
"ingress": {
"interface": {
"name": "reth0.3249"
},
"zone": "custom_zone_name"
},
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"related": {
"ip": [
"192.168.1.11",
"192.168.1.12"
]
},
"service": {
"name": "junos-https"
},
"source": {
"address": "192.168.1.11",
"ip": "192.168.1.11",
"port": 62224
}
}
{
"message": "RT_SCREEN_ICMP [attack-name=\"Address sweep!\" source-address=\"192.168.1.2\" destination-address=\"192.168.1.1\" source-zone-name=\"custom_zone_name\" interface-name=\"reth1.603\" action=\"alarm-without-drop\"]",
"event": {
"action": "RT_SCREEN_ICMP",
"category": [
"intrusion_detection"
],
"dataset": "RT_IDS",
"kind": "alert",
"outcome": "success",
"type": [
"allowed"
]
},
"destination": {
"address": "192.168.1.1",
"ip": "192.168.1.1"
},
"juniper": {
"ngfw": {
"ids": {
"action": {
"name": "alarm-without-drop"
},
"attack": {
"name": "Address sweep!"
}
}
}
},
"log": {
"syslog": {
"appname": "RT_IDS"
}
},
"observer": {
"ingress": {
"interface": {
"name": "reth1.603"
},
"zone": "custom_zone_name"
},
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"related": {
"ip": [
"192.168.1.1",
"192.168.1.2"
]
},
"source": {
"address": "192.168.1.2",
"ip": "192.168.1.2"
}
}
{
"message": "xntpd: kernel time sync enabled 2001",
"event": {
"category": [
"network"
],
"kind": "event",
"provider": "xntpd",
"type": [
"info"
]
},
"log": {
"description": "kernel time sync enabled 2001"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
}
}
{
"message": "mgd[94759]: UI_AUTH_EVENT: Authenticated user 'jdoe' assigned to class 'super-user'",
"event": {
"action": "UI_AUTH_EVENT",
"category": [
"authentication"
],
"kind": "event",
"outcome": "success",
"provider": "mgd",
"type": [
"start"
]
},
"log": {
"description": "Authenticated user 'jdoe' assigned to class 'super-user'"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"related": {
"user": [
"jdoe"
]
},
"user": {
"name": "jdoe",
"roles": "super-user"
}
}
{
"message": "mgd[8682]: UI_CHILD_START: Starting child '/usr/libexec/ui/ntpsync'",
"event": {
"action": "UI_CHILD_START",
"category": [
"process"
],
"kind": "event",
"outcome": "success",
"provider": "mgd",
"type": [
"start"
]
},
"log": {
"description": "Starting child '/usr/libexec/ui/ntpsync'"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"process": {
"name": "/usr/libexec/ui/ntpsync"
}
}
{
"message": "mgd[78145]: UI_CHILD_STATUS: Cleanup child '/sbin/ifinfo', PID 78147, status 0",
"event": {
"action": "UI_CHILD_STATUS",
"category": [
"process"
],
"kind": "event",
"provider": "mgd",
"type": [
"info"
]
},
"log": {
"description": "Cleanup child '/sbin/ifinfo', PID 78147, status 0"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"process": {
"exit_code": 0,
"name": "/sbin/ifinfo",
"pid": 78147
}
}
{
"message": "mgd[22688]: UI_CMDLINE_READ_LINE: User 'jdoe' command 'show configuration system | display inheritance defaults | display xml | match host-name | no-more '",
"event": {
"action": "UI_CMDLINE_READ_LINE",
"category": [
"process"
],
"kind": "event",
"outcome": "success",
"provider": "mgd",
"type": [
"access"
]
},
"log": {
"description": "User 'jdoe' command 'show configuration system | display inheritance defaults | display xml | match host-name | no-more '"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"process": {
"command_line": "show configuration system | display inheritance defaults | display xml | match host-name | no-more "
},
"related": {
"user": [
"jdoe"
]
},
"user": {
"name": "jdoe"
}
}
{
"message": "mgd[31767]: UI_JUNOSCRIPT_CMD: User 'jdoe' used JUNOScript client to run command 'request-authentication user=root logname=root host=localhost agent=mgd current-directory=/var/home/remote_superuser pid=31501 ppid=18835'",
"event": {
"action": "UI_JUNOSCRIPT_CMD",
"category": [
"process"
],
"kind": "event",
"provider": "mgd",
"type": [
"info"
]
},
"juniper": {
"ngfw": {
"client_mode": "junoscript"
}
},
"log": {
"description": "User 'jdoe' used JUNOScript client to run command 'request-authentication user=root logname=root host=localhost agent=mgd current-directory=/var/home/remote_superuser pid=31501 ppid=18835'"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"process": {
"command_line": "request-authentication user=root logname=root host=localhost agent=mgd current-directory=/var/home/remote_superuser pid=31501 ppid=18835"
},
"related": {
"user": [
"jdoe"
]
},
"user": {
"name": "jdoe"
}
}
{
"message": "mgd[54999]: UI_LOGIN_EVENT: User 'jdoe' login, class 'j-ids' [54999], ssh-connection '192.168.1.1 40382 192.168.1.2 22', client-mode 'cli'",
"event": {
"action": "UI_LOGIN_EVENT",
"category": [
"authentication"
],
"kind": "event",
"outcome": "success",
"provider": "mgd",
"type": [
"start"
]
},
"destination": {
"address": "192.168.1.2",
"ip": "192.168.1.2",
"port": 22
},
"juniper": {
"ngfw": {
"client_mode": "cli"
}
},
"log": {
"description": "User 'jdoe' login, class 'j-ids' [54999], ssh-connection '192.168.1.1 40382 192.168.1.2 22', client-mode 'cli'"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"related": {
"ip": [
"192.168.1.1",
"192.168.1.2"
],
"user": [
"jdoe"
]
},
"source": {
"address": "192.168.1.1",
"ip": "192.168.1.1",
"port": 40382
},
"user": {
"name": "jdoe",
"roles": "j-ids"
}
}
{
"message": "mgd[87462]: UI_LOGOUT_EVENT: User 'root' logout",
"event": {
"action": "UI_LOGOUT_EVENT",
"category": [
"authentication"
],
"kind": "event",
"outcome": "success",
"provider": "mgd",
"type": [
"end"
]
},
"log": {
"description": "User 'root' logout"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"related": {
"user": [
"root"
]
},
"user": {
"name": "root"
}
}
{
"message": "1,2025/08/07 10:59:08,016301006286,SYSTEM,auth,2817,2025/08/07 10:59:09,,auth-success,Auth_Seq_RAH,0,0,general,informational,\"Kerberos SSO authenticated for user 'jdoe'. realm 'test.local', auth profile 'Auth_Seq_RAH', vsys 'shared',\",7503878598546507619,0x0,0,0,0,0,,localhost,0,0,2025-08-07T10:59:09.193+02:00",
"event": {
"action": "auth-success",
"category": [
"authentication"
],
"kind": "event",
"outcome": "success",
"provider": "system",
"type": [
"start"
]
},
"@timestamp": "2025-08-07T08:59:09.193000Z",
"host": {
"name": "localhost"
},
"log": {
"description": "Kerberos SSO authenticated for user 'jdoe'. realm 'test.local', auth profile 'Auth_Seq_RAH', vsys 'shared',"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"related": {
"user": [
"jdoe"
]
},
"service": {
"name": "Kerberos SSO"
},
"user": {
"domain": "test.local",
"name": "jdoe"
}
}
{
"message": "/usr/sbin/cron[41404]: (root) CMD ( sh /var/etc/ukern_gbl_rotate.sh)",
"event": {
"action": "CMD",
"category": [
"process"
],
"kind": "event",
"provider": "cron",
"type": [
"info"
]
},
"log": {
"description": "(root) CMD ( sh /var/etc/ukern_gbl_rotate.sh)"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"process": {
"command_line": "sh /var/etc/ukern_gbl_rotate.sh",
"user": {
"name": "root"
}
}
}
{
"message": "/usr/sbin/cron[36324]: (root) MAIL (mailed 39 bytes of output but got status 0x0001 )",
"event": {
"action": "MAIL",
"category": [
"process"
],
"kind": "event",
"provider": "cron",
"type": [
"info"
]
},
"error": {
"code": "0001"
},
"log": {
"description": "(root) MAIL (mailed 39 bytes of output but got status 0x0001 )"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"process": {
"user": {
"name": "root"
}
},
"source": {
"bytes": 39
}
}
{
"message": "keyadmin[95280]: dump_assn: found old association 192.168.1.1:179 md5 00000003:0x3356785a4e5949306c",
"event": {
"action": "dump_assn",
"category": [
"network"
],
"kind": "event",
"provider": "keyadmin",
"type": [
"info"
]
},
"log": {
"description": "found old association 192.168.1.1:179 md5 00000003:0x3356785a4e5949306c"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
}
}
{
"message": "rshd[93991]: root@192.168.1.1 as root: cmd='rcp -t //var/etc/dynamic_address.id+'",
"event": {
"category": [
"process"
],
"kind": "event",
"provider": "rshd",
"type": [
"info"
]
},
"log": {
"description": "cmd='rcp -t //var/etc/dynamic_address.id+'"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"process": {
"command_line": "rcp -t //var/etc/dynamic_address.id+",
"user": {
"name": "root"
}
},
"related": {
"ip": [
"192.168.1.1"
],
"user": [
"root"
]
},
"source": {
"address": "192.168.1.1",
"ip": "192.168.1.1"
},
"user": {
"name": "root"
}
}
{
"message": "sshd[88235]: Failed password for jdoe from 192.168.1.1 port 60002 ssh2",
"event": {
"action": "Failed password",
"category": [
"authentication"
],
"kind": "event",
"outcome": "failure",
"provider": "sshd",
"type": [
"start"
]
},
"log": {
"description": "Failed password for jdoe from 192.168.1.1 port 60002 ssh2"
},
"observer": {
"product": "ngfw",
"type": "firewall",
"vendor": "Juniper Networks"
},
"related": {
"ip": [
"192.168.1.1"
],
"user": [
"jdoe"
]
},
"source": {
"address": "192.168.1.1",
"ip": "192.168.1.1",
"port": 60002
},
"user": {
"name": "jdoe"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
destination.bytes |
long |
Bytes sent from the destination to the source. |
destination.domain |
keyword |
The domain name of the destination. |
destination.ip |
ip |
IP address of the destination. |
destination.nat.ip |
ip |
Destination NAT ip |
destination.nat.port |
long |
Destination NAT Port |
destination.packets |
long |
Packets sent from the destination to the source. |
destination.port |
long |
Port of the destination. |
error.code |
keyword |
Error code describing the error. |
error.message |
match_only_text |
Error message. |
event.action |
keyword |
The action captured by the event. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.dataset |
keyword |
Name of the dataset. |
event.duration |
long |
Duration of the event in nanoseconds. |
event.kind |
keyword |
The kind of the event. The highest categorization field in the hierarchy. |
event.outcome |
keyword |
The outcome of the event. The lowest level categorization field in the hierarchy. |
event.provider |
keyword |
Source of the event. |
event.reason |
keyword |
Reason why this event happened, according to the source |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
file.path |
keyword |
Full path to the file, including the file name. |
host.name |
keyword |
Name of the host. |
juniper.ngfw.application.category |
keyword |
Juniper ngfw application category |
juniper.ngfw.application.name |
keyword |
Juniper ngfw application name |
juniper.ngfw.application.risk |
keyword |
Juniper ngfw application risk |
juniper.ngfw.application.sub_category |
keyword |
Juniper ngfw application sub category |
juniper.ngfw.client_mode |
keyword |
Juniper's client mode (ex. junoscript, UI, cli ...) |
juniper.ngfw.connection_tag |
keyword |
Juniper connection tag |
juniper.ngfw.destination.nat.rule.name |
keyword |
Juniper destination nat rule name |
juniper.ngfw.destination.nat.rule.type |
keyword |
Juniper destination nat rule type |
juniper.ngfw.flow.encrypted |
boolean |
Juniper flow encryption boolean |
juniper.ngfw.ids.action.name |
keyword |
Juniper ids action name |
juniper.ngfw.ids.attack.name |
keyword |
Juniper srx attack name detected by IDS |
juniper.ngfw.nat.connection_tag |
keyword |
Juniper nat connection tag |
juniper.ngfw.nested_application.name |
keyword |
Juniper ngfw nested application name |
juniper.ngfw.policy.name |
keyword |
Juniper policy name |
juniper.ngfw.source.nat.rule.name |
keyword |
Juniper source nat rule name |
juniper.ngfw.source.nat.rule.type |
keyword |
Juniper source nat rule type |
juniper.ngfw.tunnel.inspection |
boolean |
Juniper srx tunnel inspection boolean |
network.application |
keyword |
Application level protocol name. |
network.iana_number |
keyword |
IANA Protocol Number. |
network.protocol |
keyword |
Application protocol name. |
observer.egress.zone |
keyword |
Observer Egress zone |
observer.ingress.interface.name |
keyword |
Interface name |
observer.ingress.zone |
keyword |
Observer ingress zone |
observer.product |
keyword |
The product name of the observer. |
observer.type |
keyword |
The type of the observer the data is coming from. |
observer.vendor |
keyword |
Vendor name of the observer. |
observer.version |
keyword |
Observer version. |
process.args |
keyword |
Array of process arguments. |
process.command_line |
wildcard |
Full command line that started the process. |
process.exit_code |
long |
The exit code of the process. |
process.name |
keyword |
Process name. |
process.pid |
long |
Process id. |
service.name |
keyword |
Name of the service. |
source.bytes |
long |
Bytes sent from the source to the destination. |
source.ip |
ip |
IP address of the source. |
source.nat.ip |
ip |
Source NAT ip |
source.nat.port |
long |
Source NAT port |
source.packets |
long |
Packets sent from the source to the destination. |
source.port |
long |
Port of the source. |
user.domain |
keyword |
Name of the directory the user is a member of. |
user.name |
keyword |
Short name or login of the user. |
user.roles |
keyword |
Array of user roles at the time of the event. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.