Seckiot Citadelle
Overview
Seckiot Citadelle is an integrated cybersecurity platform designed for industrial control systems (ICS) and operational technology (OT) environments, providing comprehensive threat detection, asset discovery, and vulnerability management to safeguard critical infrastructure.
- Vendor: Seckiot
- Supported environment: On Premise & Cloud
- Version compatibility, if applicable: 25.5 and more
- Detection based on: Alerts, Telemetry
- Supported application or feature: Network protocol analysis
Specification
Prerequisites
- Network:
- Outbound traffic allowed
- Permissions:
- Administrator or Root access to the Seckiot Citadelle appliance
Transport Protocol/Method
- Direct HTTPS
Logs details
- Supported functionalities: See section Overview
- Supported type(s) of structure: JSON
- Supported verbosity level: Alert
Step-by-Step Configuration Procedure
Instruction on Sekoia
Configure Your Intake
This section will guide you through creating the intake object in Sekoia, which provides a unique identifier called the "Intake key." The Intake key is essential for later configuration, as it references the Community, Entity, and Parser (Intake Format) used when receiving raw events on Sekoia.
- Go to the Sekoia Intake page.
- Click on the
+ New Intakebutton at the top right of the page. - Search for your Intake by the product name in the search bar.
- Give it a Name and associate it with an Entity (and a Community if using multi-tenant mode).
- Click on
Create.
Note
For more details on how to use the Intake page and to find the Intake key you just created, refer to this documentation.
Configure Seckiot Alert Forwarding
- Log in to the Seckiot platform.
- In the left panel, click on
Capture architecture. -
Click on
Add -> Add a forwarder
-
Select the forwarder type
Sekoia.io -
Enter a
Nameto identify the forwarder, then go back to the intake you created earlier in stepConfigure Your Intakein the Sekoia platform. Finally, copy your intake key into theIntake Keyfield.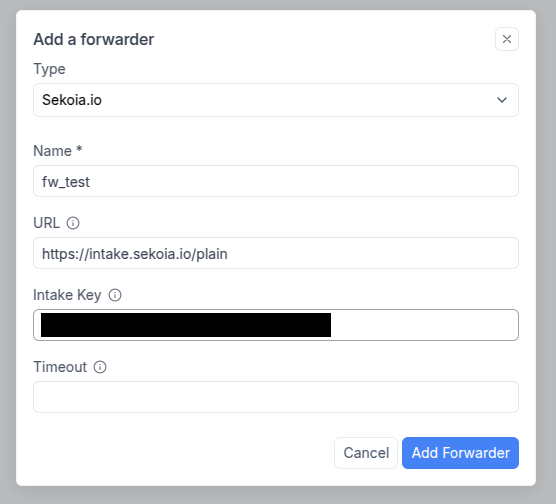
-
Click
Add Forwarder
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Network intrusion detection system |
Seckiot Citadelle identify suspicious behaviors by providing alerts logs |
Network device logs |
The logs provided by Seckiot Citadelle give a good overview of the network activity |
Network protocol analysis |
The logs offered by Seckiot Citadelle provide traffic analysis |
Asset Management |
Seckiot Citadelle identify all devices and provide a complete visibility |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "{\"device\":[],\"event\":{\"code\":[],\"severity\":1,\"outcome\":\"unknown\",\"created\":\"2025-03-12T08:51:28.586238Z\",\"category\":[\"info\"],\"ingested\":\"2025-03-12T08:51:28.586238Z\",\"kind\":\"alert\",\"type\":[\"info\"]},\"forwarders\":[\"fw_sekoiaIO\"],\"destination\":{\"vendor\":\"Fortinet, Inc.\",\"port\":58629,\"ip\":\"10.0.10.100\",\"mac\":\"08:5B:0E:97:AE:C6\"},\"skt\":{\"module\":\"Detection Engine\",\"sniffer\":\"5c418977-9069-49d1-936c-28586fe5c2a2\",\"assets\":[{\"first_seen\":\"2025-03-05T12:37:56.174487Z\",\"last_seen\":\"2025-03-12T08:50:59.469469Z\",\"name\":\"INLNFW01.infralab.local\",\"category\":\"IT\",\"hardware_vendor\":\"LANNER ELECTRONICS, INC.\",\"level\":3,\"primary_ip\":\"5d1330ac-1f3f-44ab-a704-68c894e5c207\",\"id\":\"8e27e500-d1c4-44b4-b36b-c6bb47d0993c\",\"entity\":\"router\",\"description\":\"pfSense INLNFW01.infralab.local 2.7.0-RELEASE FreeBSD 14.0-CURRENT amd64\",\"localisation\":\"LAB 10.0.1.201 ge.1.26\"},{\"system\":\"Microsoft Windows\",\"first_seen\":\"2025-03-05T12:37:56.077529Z\",\"last_seen\":\"2025-03-12T08:51:00.348Z\",\"name\":\"10.0.1.254\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"level\":3,\"primary_ip\":\"124ce9f2-9b54-4b22-a2f9-844bab52a961\",\"id\":\"6f5f0755-d57c-48ae-a2da-333991fa87c4\",\"entity\":\"router\",\"localisation\":\"lab 10.0.21.91 1/2/1\"}],\"capture_zone\":\"c1b5d877-a026-456f-90a7-526c4e463431\",\"session\":\"5e7cbf37e63b831b69dedfc2761802ca\",\"alert_id\":\"0a98ae42-e7f9-46da-845e-acc9a8583c59\",\"sensor\":\"TF-VIVIENBREVET-0-SENSOR-0\"},\"@timestamp\":\"2025-03-12T08:51:28.586238Z\",\"network\":{\"transport\":\"UDP\",\"protocol\":\"dns\"},\"@version\":\"1\",\"source\":{\"vendor\":\"LANNER ELECTRONICS, INC.\",\"port\":53,\"ip\":\"10.80.10.254\",\"mac\":\"00:90:0B:AF:92:A6\"},\"observer\":{\"name\":\"\",\"vendor\":\"Seckiot\",\"product\":\"Seckiot Citadelle\",\"_type\":\"NIDS\",\"version\":\"\"},\"rule\":{\"description\":\"Large number of requests sent from the same machine to the same machine on different ports using only a UDP packet to see if the port is open or closed. This is typically used by the tool NMAP.\",\"uuid\":\"51186749-7415-46be-90e5-000000000080\",\"name\":\"Network Service Discovery - UDP Scan Port\",\"version\":\"1\",\"author\":\"Seckiot\"}}\n",
"event": {
"category": [
"info"
],
"kind": "alert",
"severity": 1,
"type": [
"info"
]
},
"destination": {
"address": "10.0.10.100",
"ip": "10.0.10.100",
"mac": "08:5B:0E:97:AE:C6",
"port": 58629
},
"observer": {
"product": "Seckiot Citadelle",
"type": "NIDS",
"vendor": "Seckiot"
},
"related": {
"ip": [
"10.0.10.100",
"10.80.10.254"
]
},
"rule": {
"author": "Seckiot",
"description": "Large number of requests sent from the same machine to the same machine on different ports using only a UDP packet to see if the port is open or closed. This is typically used by the tool NMAP.",
"id": "51186749-7415-46be-90e5-000000000080",
"name": "Network Service Discovery - UDP Scan Port",
"version": "1"
},
"seckiot": {
"alert": {
"id": "0a98ae42-e7f9-46da-845e-acc9a8583c59"
},
"assets": {
"category": [
"IT",
"IT"
],
"description": [
"pfSense INLNFW01.infralab.local 2.7.0-RELEASE FreeBSD 14.0-CURRENT amd64",
"unknown"
],
"entity": [
"router",
"router"
],
"id": [
"6f5f0755-d57c-48ae-a2da-333991fa87c4",
"8e27e500-d1c4-44b4-b36b-c6bb47d0993c"
],
"localisation": [
"LAB 10.0.1.201 ge.1.26",
"lab 10.0.21.91 1/2/1"
],
"name": [
"10.0.1.254",
"INLNFW01.infralab.local"
],
"perdue_level": [
"3",
"3"
],
"system": [
"Microsoft Windows",
"unknown"
],
"version": [
"unknown",
"unknown"
]
},
"catch_area": {
"name": "c1b5d877-a026-456f-90a7-526c4e463431"
},
"module": "Detection Engine",
"sensor": {
"name": "TF-VIVIENBREVET-0-SENSOR-0"
},
"sniffer": {
"name": "5c418977-9069-49d1-936c-28586fe5c2a2"
}
},
"source": {
"address": "10.80.10.254",
"ip": "10.80.10.254",
"mac": "00:90:0B:AF:92:A6",
"port": 53
}
}
{
"message": "{\"device\":[],\"event\":{\"code\":[],\"severity\":1,\"outcome\":\"unknown\",\"created\":\"2025-03-12T07:31:28.525356Z\",\"category\":[\"info\"],\"ingested\":\"2025-03-12T07:31:28.525356Z\",\"kind\":\"alert\",\"type\":[\"info\"]},\"forwarders\":[\"fw_sekoiaIO\"],\"destination\":{\"vendor\":\"VMware, Inc.\",\"port\":4739,\"ip\":\"10.0.12.1\",\"mac\":\"00:0C:29:B0:79:1C\"},\"skt\":{\"module\":\"Detection Engine\",\"sniffer\":\"5c418977-9069-49d1-936c-28586fe5c2a2\",\"assets\":[{\"system\":\"Microsoft Windows\",\"first_seen\":\"2025-03-05T12:37:56.077529Z\",\"last_seen\":\"2025-03-12T07:31:12.375646Z\",\"name\":\"10.0.1.254\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"level\":3,\"primary_ip\":\"124ce9f2-9b54-4b22-a2f9-844bab52a961\",\"id\":\"6f5f0755-d57c-48ae-a2da-333991fa87c4\",\"entity\":\"router\",\"localisation\":\"lab 10.0.21.91 1/2/1\"},{\"first_seen\":\"2025-03-06T13:57:58.838858Z\",\"last_seen\":\"2025-03-12T07:30:53.844522Z\",\"name\":\"LABNFW02.lab.local\",\"category\":\"IT\",\"hardware_vendor\":\"Fortinet, Inc.\",\"level\":3,\"primary_ip\":\"cf6c6028-83cc-4121-842b-8a3923a093db\",\"id\":\"01f7a81d-5e0d-4c85-a5ca-a64cbad23515\",\"entity\":\"router\",\"description\":\"Firewall Site 2\",\"localisation\":\"BD 10.2.1.200 fe.1.12\"},{\"system\":\"Microsoft Windows Server 2019 Standard\",\"first_seen\":\"2025-03-05T12:37:53.554365Z\",\"last_seen\":\"2025-03-12T07:31:11.928426Z\",\"name\":\"LABSTIA02\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"modele\":\"VMware7,1\",\"level\":3,\"version\":\"17763.4737\",\"primary_ip\":\"23569d10-2580-40ed-b47c-8dee7dec5070\",\"id\":\"c1d78ed5-7663-4dbb-8d1c-cfc9b5bd23ca\",\"entity\":\"virtual-server\",\"description\":\"\",\"localisation\":\"lab 10.0.21.91 1/1/1\"},{\"system\":\"Microsoft Windows 2016+ Server\",\"first_seen\":\"2025-03-06T13:57:57.628789Z\",\"last_seen\":\"2025-03-12T07:31:21.084186Z\",\"name\":\"LABSKEP01\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"level\":3,\"version\":\"10.0.10011.16384\",\"primary_ip\":\"41010435-c9ce-4158-8759-88ad91c32ede\",\"id\":\"154e6092-db3d-4bef-bf07-bf0ca2ba15a2\",\"entity\":\"virtual-server\",\"description\":\"\",\"localisation\":\"BD 10.2.1.200 ge.1.25\"},{\"system\":\"Microsoft Windows Server 2019 Standard\",\"first_seen\":\"2025-03-06T13:49:56.593575Z\",\"last_seen\":\"2025-03-12T07:31:12.347024Z\",\"name\":\"LABSAD01\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"modele\":\"VMware7,1\",\"level\":3,\"version\":\"17763.379\",\"primary_ip\":\"7524efed-8f77-4f40-be72-5771a56e2f47\",\"id\":\"07f5a027-73be-4bb9-a629-f97dcf210a16\",\"entity\":\"domain-controller\",\"description\":\"DC 1\",\"localisation\":\"Lab 10.0.11.200 Gi0/1\"}],\"capture_zone\":\"c1b5d877-a026-456f-90a7-526c4e463431\",\"session\":\"75e5ebe68661b2f1500432fb9a889df2\",\"alert_id\":\"b4eaea3e-d7bf-4792-b007-9a6731444e64\",\"sensor\":\"TF-VIVIENBREVET-0-SENSOR-0\"},\"@timestamp\":\"2025-03-12T07:31:28.525356Z\",\"network\":{\"transport\":\"UDP\",\"protocol\":\"iana_ipfix\"},\"@version\":\"1\",\"source\":{\"vendor\":\"VMware, Inc.\",\"port\":8346,\"ip\":\"10.0.12.254\",\"mac\":\"00:0C:29:A2:6D:3F\"},\"observer\":{\"name\":\"\",\"vendor\":\"Seckiot\",\"product\":\"Seckiot Citadelle\",\"_type\":\"NIDS\",\"version\":\"\"},\"rule\":{\"description\":\"A UDP flood Denial of Service attack involves sending a large number of UDP packets to random ports on a target. This overloads the target's network and resources, leading to performance degradation or unavailability of the service to legitimate users.\",\"uuid\":\"51186749-7415-46be-90e5-000000000087\",\"name\":\"Denial Of Service - UDP Flood\",\"version\":\"1\",\"author\":\"Seckiot\"}}\n",
"event": {
"category": [
"info"
],
"kind": "alert",
"severity": 1,
"type": [
"info"
]
},
"destination": {
"address": "10.0.12.1",
"ip": "10.0.12.1",
"mac": "00:0C:29:B0:79:1C",
"port": 4739
},
"observer": {
"product": "Seckiot Citadelle",
"type": "NIDS",
"vendor": "Seckiot"
},
"related": {
"ip": [
"10.0.12.1",
"10.0.12.254"
]
},
"rule": {
"author": "Seckiot",
"description": "A UDP flood Denial of Service attack involves sending a large number of UDP packets to random ports on a target. This overloads the target's network and resources, leading to performance degradation or unavailability of the service to legitimate users.",
"id": "51186749-7415-46be-90e5-000000000087",
"name": "Denial Of Service - UDP Flood",
"version": "1"
},
"seckiot": {
"alert": {
"id": "b4eaea3e-d7bf-4792-b007-9a6731444e64"
},
"assets": {
"category": [
"IT",
"IT",
"IT",
"IT",
"IT"
],
"description": [
"DC 1",
"Firewall Site 2",
"unknown",
"unknown",
"unknown"
],
"entity": [
"domain-controller",
"router",
"router",
"virtual-server",
"virtual-server"
],
"id": [
"01f7a81d-5e0d-4c85-a5ca-a64cbad23515",
"07f5a027-73be-4bb9-a629-f97dcf210a16",
"154e6092-db3d-4bef-bf07-bf0ca2ba15a2",
"6f5f0755-d57c-48ae-a2da-333991fa87c4",
"c1d78ed5-7663-4dbb-8d1c-cfc9b5bd23ca"
],
"localisation": [
"BD 10.2.1.200 fe.1.12",
"BD 10.2.1.200 ge.1.25",
"Lab 10.0.11.200 Gi0/1",
"lab 10.0.21.91 1/1/1",
"lab 10.0.21.91 1/2/1"
],
"name": [
"10.0.1.254",
"LABNFW02.lab.local",
"LABSAD01",
"LABSKEP01",
"LABSTIA02"
],
"perdue_level": [
"3",
"3",
"3",
"3",
"3"
],
"system": [
"Microsoft Windows",
"Microsoft Windows 2016+ Server",
"Microsoft Windows Server 2019 Standard",
"Microsoft Windows Server 2019 Standard",
"unknown"
],
"version": [
"10.0.10011.16384",
"17763.379",
"17763.4737",
"unknown",
"unknown"
]
},
"catch_area": {
"name": "c1b5d877-a026-456f-90a7-526c4e463431"
},
"module": "Detection Engine",
"sensor": {
"name": "TF-VIVIENBREVET-0-SENSOR-0"
},
"sniffer": {
"name": "5c418977-9069-49d1-936c-28586fe5c2a2"
}
},
"source": {
"address": "10.0.12.254",
"ip": "10.0.12.254",
"mac": "00:0C:29:A2:6D:3F",
"port": 8346
}
}
{
"message": "{\"device\":[],\"event\":{\"code\":[],\"severity\":7,\"outcome\":\"unknown\",\"created\":\"2025-03-12T13:34:04.407568Z\",\"category\":[\"info\"],\"ingested\":\"2025-03-12T13:34:04.407568Z\",\"kind\":\"alert\",\"type\":[\"info\"]},\"forwarders\":[\"fw_sekoiaIO\"],\"observer\":{\"name\":\"\",\"vendor\":\"Seckiot\",\"product\":\"Seckiot Citadelle\",\"_type\":\"NIDS\",\"version\":\"\"},\"skt\":{\"module\":\"Cartography\",\"sniffer\":\"\",\"assets\":[{\"name\":\"2.22.251.11\",\"first_seen\":\"2025-03-12T13:33:48Z\",\"last_seen\":\"2025-03-12T13:34:04.348385Z\",\"id\":\"f2fd51d8-81c0-477b-abba-4894f1b8421d\"}],\"capture_zone\":\"\",\"alert_id\":\"b70ec8e1-432b-4293-bbcf-5ee94bf5e9df\",\"sensor\":\"\"},\"@timestamp\":\"2025-03-12T13:34:04.407568Z\",\"rule\":{\"description\":\"Asset `2.22.251.11` created\",\"uuid\":\"00000000-0000-0000-0000-000000000001\",\"name\":\"Unknown Device in the Network\",\"version\":\"1\",\"author\":\"Seckiot\"},\"@version\":\"1\"}\n",
"event": {
"category": [
"info"
],
"id": "00000000-0000-0000-0000-000000000000",
"kind": "alert",
"severity": 7,
"type": [
"info"
]
},
"observer": {
"product": "Seckiot Citadelle",
"type": "NIDS",
"vendor": "Seckiot"
},
"rule": {
"author": "Seckiot",
"description": "Asset `2.22.251.11` created",
"id": "00000000-0000-0000-0000-000000000001",
"name": "Unknown Device in the Network",
"version": "1"
},
"seckiot": {
"alert": {
"id": "b70ec8e1-432b-4293-bbcf-5ee94bf5e9df"
},
"assets": {
"category": [
"unknown"
],
"description": [
"unknown"
],
"entity": [
"unknown"
],
"id": [
"f2fd51d8-81c0-477b-abba-4894f1b8421d"
],
"localisation": [
"unknown"
],
"name": [
"2.22.251.11"
],
"perdue_level": [
"unknown"
],
"system": [
"unknown"
],
"version": [
"unknown"
]
},
"module": "Cartography"
},
"sekoiaio": {
"intake": {
"dialect": "test",
"dialect_uuid": "00000000-0000-0000-0000-000000000000",
"parsing_status": "success"
}
}
}
{
"message": "{\"device\":[],\"event\":{\"code\":[],\"severity\":1,\"outcome\":\"unknown\",\"created\":\"2025-03-12T09:29:10.485097Z\",\"category\":[\"info\"],\"ingested\":\"2025-03-12T09:29:10.485097Z\",\"kind\":\"alert\",\"type\":[\"info\"]},\"forwarders\":[\"fw_sekoiaIO\"],\"destination\":{\"ip\":\"20.10.113.82\",\"port\":443},\"skt\":{\"module\":\"Cartography\",\"sniffer\":\"br0\",\"assets\":[{\"name\":\"20.10.113.82\",\"first_seen\":\"2025-03-12T09:28:40Z\",\"last_seen\":\"2025-03-12T09:29:09.346448Z\",\"id\":\"ec4353eb-0c7c-4fe6-8523-21d840b37dbf\"},{\"system\":\"Microsoft Windows 2016+ Server\",\"first_seen\":\"2025-03-05T12:37:53.554365Z\",\"last_seen\":\"2025-03-12T09:29:07.350067Z\",\"name\":\"LABSWKS01\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"level\":3,\"version\":\"10.0.10011.16384\",\"primary_ip\":\"3a41f5fb-ecc9-4d8b-b2d0-6a94765445c9\",\"id\":\"4d5b3e7c-d058-4123-ac3b-a4788fc5c7af\",\"entity\":\"virtual-server\",\"description\":\"\",\"localisation\":\"Lab 10.0.11.200 Gi0/8\"}],\"capture_zone\":\"default\",\"session\":\"27c24bfb94ca28d0d9401b9d06fc91fb\",\"alert_id\":\"be97c9ee-bfa3-4306-9945-eac29847f06f\",\"sensor\":\"TF-VIVIENBREVET-0-SENSOR-0\"},\"@timestamp\":\"2025-03-12T09:29:10.485097Z\",\"network\":{\"protocol\":\"TLS\"},\"@version\":\"1\",\"source\":{\"vendor\":\"VMware, Inc.\",\"port\":50335,\"ip\":\"10.0.101.50\",\"mac\":\"00:0C:29:D1:22:2E\"},\"observer\":{\"name\":\"\",\"vendor\":\"Seckiot\",\"product\":\"Seckiot Citadelle\",\"_type\":\"NIDS\",\"version\":\"\"},\"rule\":{\"description\":\"New link detected between LABSWKS01 and 20.10.113.82\",\"uuid\":\"00000000-0000-0000-0000-000000000012\",\"name\":\"New Link Between Two Assets\",\"version\":\"1\",\"author\":\"Seckiot\"}}\n",
"event": {
"category": [
"info"
],
"kind": "alert",
"severity": 1,
"type": [
"info"
]
},
"destination": {
"address": "20.10.113.82",
"ip": "20.10.113.82",
"port": 443
},
"observer": {
"product": "Seckiot Citadelle",
"type": "NIDS",
"vendor": "Seckiot"
},
"related": {
"ip": [
"10.0.101.50",
"20.10.113.82"
]
},
"rule": {
"author": "Seckiot",
"description": "New link detected between LABSWKS01 and 20.10.113.82",
"id": "00000000-0000-0000-0000-000000000012",
"name": "New Link Between Two Assets",
"version": "1"
},
"seckiot": {
"alert": {
"id": "be97c9ee-bfa3-4306-9945-eac29847f06f"
},
"assets": {
"category": [
"IT",
"unknown"
],
"description": [
"unknown",
"unknown"
],
"entity": [
"unknown",
"virtual-server"
],
"id": [
"4d5b3e7c-d058-4123-ac3b-a4788fc5c7af",
"ec4353eb-0c7c-4fe6-8523-21d840b37dbf"
],
"localisation": [
"Lab 10.0.11.200 Gi0/8",
"unknown"
],
"name": [
"20.10.113.82",
"LABSWKS01"
],
"perdue_level": [
"3",
"unknown"
],
"system": [
"Microsoft Windows 2016+ Server",
"unknown"
],
"version": [
"10.0.10011.16384",
"unknown"
]
},
"catch_area": {
"name": "default"
},
"module": "Cartography",
"sensor": {
"name": "TF-VIVIENBREVET-0-SENSOR-0"
},
"sniffer": {
"name": "br0"
}
},
"source": {
"address": "10.0.101.50",
"ip": "10.0.101.50",
"mac": "00:0C:29:D1:22:2E",
"port": 50335
}
}
{
"message": "{\"device\":[],\"event\":{\"code\":[],\"severity\":7,\"outcome\":\"unknown\",\"created\":\"2025-03-12T13:34:06.487415Z\",\"category\":[\"info\"],\"ingested\":\"2025-03-12T13:34:06.487415Z\",\"kind\":\"alert\",\"type\":[\"info\"]},\"forwarders\":[\"fw_sekoiaIO\"],\"destination\":{\"ip\":\"2.22.251.11\",\"port\":443},\"skt\":{\"module\":\"Cartography\",\"sniffer\":\"br0\",\"assets\":[{\"name\":\"2.22.251.11\",\"first_seen\":\"2025-03-12T13:33:48Z\",\"last_seen\":\"2025-03-12T13:34:04.348385Z\",\"id\":\"f2fd51d8-81c0-477b-abba-4894f1b8421d\"}],\"capture_zone\":\"default\",\"session\":\"81335dd9a786a0688197ea861a2ee3db\",\"alert_id\":\"ee2b728e-aa6b-4f49-990d-48c7d2498e1f\",\"sensor\":\"TF-VIVIENBREVET-0-SENSOR-0\"},\"@timestamp\":\"2025-03-12T13:34:06.487415Z\",\"network\":{\"protocol\":\"TLS\"},\"@version\":\"1\",\"source\":{\"vendor\":\"VMware, Inc.\",\"port\":50569,\"ip\":\"10.80.10.1\",\"mac\":\"00:0C:29:A2:6D:3F\"},\"observer\":{\"name\":\"\",\"vendor\":\"Seckiot\",\"product\":\"Seckiot Citadelle\",\"_type\":\"NIDS\",\"version\":\"\"},\"rule\":{\"description\":\"New server port 2.22.251.11:443 (default) detected on 2.22.251.11\",\"uuid\":\"00000000-0000-0000-0000-000000000002\",\"name\":\"New Open Server Port\",\"version\":\"1\",\"author\":\"Seckiot\"}}\n",
"event": {
"category": [
"info"
],
"id": "00000000-0000-0000-0000-000000000000",
"kind": "alert",
"severity": 7,
"type": [
"info"
]
},
"destination": {
"address": "2.22.251.11",
"ip": "2.22.251.11",
"port": 443
},
"observer": {
"product": "Seckiot Citadelle",
"type": "NIDS",
"vendor": "Seckiot"
},
"related": {
"ip": [
"10.80.10.1",
"2.22.251.11"
]
},
"rule": {
"author": "Seckiot",
"description": "New server port 2.22.251.11:443 (default) detected on 2.22.251.11",
"id": "00000000-0000-0000-0000-000000000002",
"name": "New Open Server Port",
"version": "1"
},
"seckiot": {
"alert": {
"id": "ee2b728e-aa6b-4f49-990d-48c7d2498e1f"
},
"assets": {
"category": [
"unknown"
],
"description": [
"unknown"
],
"entity": [
"unknown"
],
"id": [
"f2fd51d8-81c0-477b-abba-4894f1b8421d"
],
"localisation": [
"unknown"
],
"name": [
"2.22.251.11"
],
"perdue_level": [
"unknown"
],
"system": [
"unknown"
],
"version": [
"unknown"
]
},
"catch_area": {
"name": "default"
},
"module": "Cartography",
"sensor": {
"name": "TF-VIVIENBREVET-0-SENSOR-0"
},
"sniffer": {
"name": "br0"
}
},
"sekoiaio": {
"intake": {
"dialect": "test",
"dialect_uuid": "00000000-0000-0000-0000-000000000000",
"parsing_status": "success"
}
},
"source": {
"address": "10.80.10.1",
"ip": "10.80.10.1",
"mac": "00:0C:29:A2:6D:3F",
"port": 50569
}
}
{
"message": "{\"device\":[],\"event\":{\"code\":[],\"severity\":7,\"outcome\":\"unknown\",\"created\":\"2025-03-06T14:05:57.457022Z\",\"category\":[\"info\"],\"ingested\":\"2025-03-06T14:05:57.457022Z\",\"kind\":\"alert\",\"type\":[\"info\"]},\"forwarders\":[\"fw_sekoiaIO\"],\"observer\":{\"name\":\"\",\"vendor\":\"Seckiot\",\"product\":\"Seckiot Citadelle\",\"_type\":\"NIDS\",\"version\":\"\"},\"skt\":{\"module\":\"CVE\",\"sniffer\":\"\",\"assets\":[{\"system\":\"Microsoft Windows Server 2019 Standard\",\"first_seen\":\"2025-03-06T13:49:56.593575Z\",\"last_seen\":\"2025-03-06T14:05:55.420426Z\",\"name\":\"LABSAD01\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"modele\":\"VMware7,1\",\"level\":3,\"version\":\"17763.379\",\"primary_ip\":\"7524efed-8f77-4f40-be72-5771a56e2f47\",\"id\":\"07f5a027-73be-4bb9-a629-f97dcf210a16\",\"entity\":\"domain-controller\",\"description\":\"DC 1\",\"localisation\":\"Lab 10.0.11.200 Gi0/1\"}],\"capture_zone\":\"\",\"alert_id\":\"d66a025c-6e51-42a4-88f9-50bb719b1ac1\",\"sensor\":\"\"},\"vulnerability\":{\"severity\":\"medium\",\"scanner\":{\"vendor\":\"Seckiot\"},\"reference\":\"http://www.exploit-db.com/exploits/26528/,http://www.exploit-db.com/exploits/26528/\",\"enumeration\":\"CVE\",\"id\":\"CVE-2013-1414\",\"description\":\"New vulnerability CVE-2013-1414 detected on LABSAD01\",\"score\":{\"base\":\"5.1\",\"version\":\"3.1\"},\"category\":null,\"classification\":\"CVSS\"},\"@timestamp\":\"2025-03-06T14:05:57.457022Z\",\"rule\":{\"description\":\"New vulnerability CVE-2013-1414 detected on LABSAD01\",\"uuid\":\"00000000-0000-0000-0000-000000000003\",\"name\":\"Nouvelle Vuln\u00e9rabilit\u00e9 D\u00e9couverte\",\"version\":\"1\",\"author\":\"seckiot\"},\"@version\":\"1\"}\n",
"event": {
"category": [
"info"
],
"id": "00000000-0000-0000-0000-000000000000",
"kind": "alert",
"severity": 7,
"type": [
"info"
]
},
"observer": {
"product": "Seckiot Citadelle",
"type": "NIDS",
"vendor": "Seckiot"
},
"rule": {
"author": "seckiot",
"description": "New vulnerability CVE-2013-1414 detected on LABSAD01",
"id": "00000000-0000-0000-0000-000000000003",
"name": "Nouvelle Vuln\u00e9rabilit\u00e9 D\u00e9couverte",
"version": "1"
},
"seckiot": {
"alert": {
"id": "d66a025c-6e51-42a4-88f9-50bb719b1ac1"
},
"assets": {
"category": [
"IT"
],
"description": [
"DC 1"
],
"entity": [
"domain-controller"
],
"id": [
"07f5a027-73be-4bb9-a629-f97dcf210a16"
],
"localisation": [
"Lab 10.0.11.200 Gi0/1"
],
"name": [
"LABSAD01"
],
"perdue_level": [
"3"
],
"system": [
"Microsoft Windows Server 2019 Standard"
],
"version": [
"17763.379"
]
},
"module": "CVE"
},
"sekoiaio": {
"intake": {
"dialect": "test",
"dialect_uuid": "00000000-0000-0000-0000-000000000000",
"parsing_status": "success"
}
},
"vulnerability": {
"classification": "CVSS",
"description": "New vulnerability CVE-2013-1414 detected on LABSAD01",
"enumeration": "CVE",
"id": "CVE-2013-1414",
"reference": "http://www.exploit-db.com/exploits/26528/,http://www.exploit-db.com/exploits/26528/",
"scanner": {
"vendor": "Seckiot"
},
"score": {
"base": 5.1,
"version": "3.1"
},
"severity": "medium"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
destination.ip |
ip |
IP address of the destination. |
destination.mac |
keyword |
MAC address of the destination. |
destination.port |
long |
Port of the destination. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.kind |
keyword |
The kind of the event. The highest categorization field in the hierarchy. |
event.outcome |
keyword |
The outcome of the event. The lowest level categorization field in the hierarchy. |
event.severity |
long |
Numeric severity of the event. |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
network.protocol |
keyword |
Application protocol name. |
network.transport |
keyword |
Protocol Name corresponding to the field iana_number. |
observer.name |
keyword |
Custom name of the observer. |
observer.product |
keyword |
The product name of the observer. |
observer.type |
keyword |
The type of the observer the data is coming from. |
observer.vendor |
keyword |
Vendor name of the observer. |
observer.version |
keyword |
Observer version. |
rule.author |
keyword |
Rule author |
rule.description |
keyword |
Rule description |
rule.id |
keyword |
Rule ID |
rule.name |
keyword |
Rule name |
rule.version |
keyword |
Rule version |
seckiot.alert.id |
text |
Unique ID of the alert |
seckiot.assets.category |
text |
Category of the asset IT/OT/IOT |
seckiot.assets.description |
text |
Description of the asset |
seckiot.assets.entity |
text |
Entity of the asset |
seckiot.assets.id |
text |
Unique ID of the asset |
seckiot.assets.localisation |
text |
Localisation of the asset |
seckiot.assets.name |
text |
Name of the asset |
seckiot.assets.perdue_level |
text |
Perdue level of the asset, between 0 and 6 |
seckiot.assets.system |
text |
Name of operating system |
seckiot.assets.version |
text |
OS version of the asset |
seckiot.catch_area.name |
text |
Name of the catch area where the flow has been captured |
seckiot.module |
text |
Seckiot module definition |
seckiot.sensor.name |
text |
Name of the sensor which capture the flow |
seckiot.sniffer.name |
text |
Name of the sniffer which capture the flow |
source.ip |
ip |
IP address of the source. |
source.mac |
keyword |
MAC address of the source. |
source.port |
long |
Port of the source. |
vulnerability.category |
keyword |
Category of a vulnerability. |
vulnerability.classification |
keyword |
Classification of the vulnerability. |
vulnerability.description |
keyword |
Description of the vulnerability. |
vulnerability.enumeration |
keyword |
Identifier of the vulnerability. |
vulnerability.id |
keyword |
ID of the vulnerability. |
vulnerability.reference |
keyword |
Reference of the vulnerability. |
vulnerability.report_id |
keyword |
Scan identification number. |
vulnerability.scanner.vendor |
keyword |
Name of the scanner vendor. |
vulnerability.score.base |
float |
Vulnerability Base score. |
vulnerability.score.environmental |
float |
Vulnerability Environmental score. |
vulnerability.score.temporal |
float |
Vulnerability Temporal score. |
vulnerability.score.version |
keyword |
CVSS version. |
vulnerability.severity |
keyword |
Severity of the vulnerability. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake Seckiot Citadelle. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x Seckiot Citadelle on ATT&CK Navigator
Cryptomining
Detection of domain names potentially related to cryptomining activities.
- Effort: master
Dynamic DNS Contacted
Detect communication with dynamic dns domain. This kind of domain is often used by attackers. This rule can trigger false positive in non-controlled environment because dynamic dns is not always malicious.
- Effort: master
Exfiltration Domain
Detects traffic toward a domain flagged as a possible exfiltration vector.
- Effort: master
Remote Access Tool Domain
Detects traffic toward a domain flagged as a Remote Administration Tool (RAT).
- Effort: master
Remote Monitoring and Management Software - AnyDesk
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool AnyDesk.
- Effort: master
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
Sekoia.io EICAR Detection
Detects observables in Sekoia.io CTI tagged as EICAR, which are fake samples meant to test detection.
- Effort: master
TOR Usage
Detects TOR usage, based on the IP address and the destination port (filtered on NTP). TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
TOR Usage Generic Rule
Detects TOR usage globally, whether the IP is a destination or source. TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Network intrusion detection system |
Seckiot Citadelle identify suspicious behaviors by providing alerts logs |
Network device logs |
The logs provided by Seckiot Citadelle give a good overview of the network activity |
Network protocol analysis |
The logs offered by Seckiot Citadelle provide traffic analysis |
Asset Management |
Seckiot Citadelle identify all devices and provide a complete visibility |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "{\"device\":[],\"event\":{\"code\":[],\"severity\":1,\"outcome\":\"unknown\",\"created\":\"2025-03-12T08:51:28.586238Z\",\"category\":[\"info\"],\"ingested\":\"2025-03-12T08:51:28.586238Z\",\"kind\":\"alert\",\"type\":[\"info\"]},\"forwarders\":[\"fw_sekoiaIO\"],\"destination\":{\"vendor\":\"Fortinet, Inc.\",\"port\":58629,\"ip\":\"10.0.10.100\",\"mac\":\"08:5B:0E:97:AE:C6\"},\"skt\":{\"module\":\"Detection Engine\",\"sniffer\":\"5c418977-9069-49d1-936c-28586fe5c2a2\",\"assets\":[{\"first_seen\":\"2025-03-05T12:37:56.174487Z\",\"last_seen\":\"2025-03-12T08:50:59.469469Z\",\"name\":\"INLNFW01.infralab.local\",\"category\":\"IT\",\"hardware_vendor\":\"LANNER ELECTRONICS, INC.\",\"level\":3,\"primary_ip\":\"5d1330ac-1f3f-44ab-a704-68c894e5c207\",\"id\":\"8e27e500-d1c4-44b4-b36b-c6bb47d0993c\",\"entity\":\"router\",\"description\":\"pfSense INLNFW01.infralab.local 2.7.0-RELEASE FreeBSD 14.0-CURRENT amd64\",\"localisation\":\"LAB 10.0.1.201 ge.1.26\"},{\"system\":\"Microsoft Windows\",\"first_seen\":\"2025-03-05T12:37:56.077529Z\",\"last_seen\":\"2025-03-12T08:51:00.348Z\",\"name\":\"10.0.1.254\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"level\":3,\"primary_ip\":\"124ce9f2-9b54-4b22-a2f9-844bab52a961\",\"id\":\"6f5f0755-d57c-48ae-a2da-333991fa87c4\",\"entity\":\"router\",\"localisation\":\"lab 10.0.21.91 1/2/1\"}],\"capture_zone\":\"c1b5d877-a026-456f-90a7-526c4e463431\",\"session\":\"5e7cbf37e63b831b69dedfc2761802ca\",\"alert_id\":\"0a98ae42-e7f9-46da-845e-acc9a8583c59\",\"sensor\":\"TF-VIVIENBREVET-0-SENSOR-0\"},\"@timestamp\":\"2025-03-12T08:51:28.586238Z\",\"network\":{\"transport\":\"UDP\",\"protocol\":\"dns\"},\"@version\":\"1\",\"source\":{\"vendor\":\"LANNER ELECTRONICS, INC.\",\"port\":53,\"ip\":\"10.80.10.254\",\"mac\":\"00:90:0B:AF:92:A6\"},\"observer\":{\"name\":\"\",\"vendor\":\"Seckiot\",\"product\":\"Seckiot Citadelle\",\"_type\":\"NIDS\",\"version\":\"\"},\"rule\":{\"description\":\"Large number of requests sent from the same machine to the same machine on different ports using only a UDP packet to see if the port is open or closed. This is typically used by the tool NMAP.\",\"uuid\":\"51186749-7415-46be-90e5-000000000080\",\"name\":\"Network Service Discovery - UDP Scan Port\",\"version\":\"1\",\"author\":\"Seckiot\"}}\n",
"event": {
"category": [
"info"
],
"kind": "alert",
"severity": 1,
"type": [
"info"
]
},
"destination": {
"address": "10.0.10.100",
"ip": "10.0.10.100",
"mac": "08:5B:0E:97:AE:C6",
"port": 58629
},
"observer": {
"product": "Seckiot Citadelle",
"type": "NIDS",
"vendor": "Seckiot"
},
"related": {
"ip": [
"10.0.10.100",
"10.80.10.254"
]
},
"rule": {
"author": "Seckiot",
"description": "Large number of requests sent from the same machine to the same machine on different ports using only a UDP packet to see if the port is open or closed. This is typically used by the tool NMAP.",
"id": "51186749-7415-46be-90e5-000000000080",
"name": "Network Service Discovery - UDP Scan Port",
"version": "1"
},
"seckiot": {
"alert": {
"id": "0a98ae42-e7f9-46da-845e-acc9a8583c59"
},
"assets": {
"category": [
"IT",
"IT"
],
"description": [
"pfSense INLNFW01.infralab.local 2.7.0-RELEASE FreeBSD 14.0-CURRENT amd64",
"unknown"
],
"entity": [
"router",
"router"
],
"id": [
"6f5f0755-d57c-48ae-a2da-333991fa87c4",
"8e27e500-d1c4-44b4-b36b-c6bb47d0993c"
],
"localisation": [
"LAB 10.0.1.201 ge.1.26",
"lab 10.0.21.91 1/2/1"
],
"name": [
"10.0.1.254",
"INLNFW01.infralab.local"
],
"perdue_level": [
"3",
"3"
],
"system": [
"Microsoft Windows",
"unknown"
],
"version": [
"unknown",
"unknown"
]
},
"catch_area": {
"name": "c1b5d877-a026-456f-90a7-526c4e463431"
},
"module": "Detection Engine",
"sensor": {
"name": "TF-VIVIENBREVET-0-SENSOR-0"
},
"sniffer": {
"name": "5c418977-9069-49d1-936c-28586fe5c2a2"
}
},
"source": {
"address": "10.80.10.254",
"ip": "10.80.10.254",
"mac": "00:90:0B:AF:92:A6",
"port": 53
}
}
{
"message": "{\"device\":[],\"event\":{\"code\":[],\"severity\":1,\"outcome\":\"unknown\",\"created\":\"2025-03-12T07:31:28.525356Z\",\"category\":[\"info\"],\"ingested\":\"2025-03-12T07:31:28.525356Z\",\"kind\":\"alert\",\"type\":[\"info\"]},\"forwarders\":[\"fw_sekoiaIO\"],\"destination\":{\"vendor\":\"VMware, Inc.\",\"port\":4739,\"ip\":\"10.0.12.1\",\"mac\":\"00:0C:29:B0:79:1C\"},\"skt\":{\"module\":\"Detection Engine\",\"sniffer\":\"5c418977-9069-49d1-936c-28586fe5c2a2\",\"assets\":[{\"system\":\"Microsoft Windows\",\"first_seen\":\"2025-03-05T12:37:56.077529Z\",\"last_seen\":\"2025-03-12T07:31:12.375646Z\",\"name\":\"10.0.1.254\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"level\":3,\"primary_ip\":\"124ce9f2-9b54-4b22-a2f9-844bab52a961\",\"id\":\"6f5f0755-d57c-48ae-a2da-333991fa87c4\",\"entity\":\"router\",\"localisation\":\"lab 10.0.21.91 1/2/1\"},{\"first_seen\":\"2025-03-06T13:57:58.838858Z\",\"last_seen\":\"2025-03-12T07:30:53.844522Z\",\"name\":\"LABNFW02.lab.local\",\"category\":\"IT\",\"hardware_vendor\":\"Fortinet, Inc.\",\"level\":3,\"primary_ip\":\"cf6c6028-83cc-4121-842b-8a3923a093db\",\"id\":\"01f7a81d-5e0d-4c85-a5ca-a64cbad23515\",\"entity\":\"router\",\"description\":\"Firewall Site 2\",\"localisation\":\"BD 10.2.1.200 fe.1.12\"},{\"system\":\"Microsoft Windows Server 2019 Standard\",\"first_seen\":\"2025-03-05T12:37:53.554365Z\",\"last_seen\":\"2025-03-12T07:31:11.928426Z\",\"name\":\"LABSTIA02\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"modele\":\"VMware7,1\",\"level\":3,\"version\":\"17763.4737\",\"primary_ip\":\"23569d10-2580-40ed-b47c-8dee7dec5070\",\"id\":\"c1d78ed5-7663-4dbb-8d1c-cfc9b5bd23ca\",\"entity\":\"virtual-server\",\"description\":\"\",\"localisation\":\"lab 10.0.21.91 1/1/1\"},{\"system\":\"Microsoft Windows 2016+ Server\",\"first_seen\":\"2025-03-06T13:57:57.628789Z\",\"last_seen\":\"2025-03-12T07:31:21.084186Z\",\"name\":\"LABSKEP01\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"level\":3,\"version\":\"10.0.10011.16384\",\"primary_ip\":\"41010435-c9ce-4158-8759-88ad91c32ede\",\"id\":\"154e6092-db3d-4bef-bf07-bf0ca2ba15a2\",\"entity\":\"virtual-server\",\"description\":\"\",\"localisation\":\"BD 10.2.1.200 ge.1.25\"},{\"system\":\"Microsoft Windows Server 2019 Standard\",\"first_seen\":\"2025-03-06T13:49:56.593575Z\",\"last_seen\":\"2025-03-12T07:31:12.347024Z\",\"name\":\"LABSAD01\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"modele\":\"VMware7,1\",\"level\":3,\"version\":\"17763.379\",\"primary_ip\":\"7524efed-8f77-4f40-be72-5771a56e2f47\",\"id\":\"07f5a027-73be-4bb9-a629-f97dcf210a16\",\"entity\":\"domain-controller\",\"description\":\"DC 1\",\"localisation\":\"Lab 10.0.11.200 Gi0/1\"}],\"capture_zone\":\"c1b5d877-a026-456f-90a7-526c4e463431\",\"session\":\"75e5ebe68661b2f1500432fb9a889df2\",\"alert_id\":\"b4eaea3e-d7bf-4792-b007-9a6731444e64\",\"sensor\":\"TF-VIVIENBREVET-0-SENSOR-0\"},\"@timestamp\":\"2025-03-12T07:31:28.525356Z\",\"network\":{\"transport\":\"UDP\",\"protocol\":\"iana_ipfix\"},\"@version\":\"1\",\"source\":{\"vendor\":\"VMware, Inc.\",\"port\":8346,\"ip\":\"10.0.12.254\",\"mac\":\"00:0C:29:A2:6D:3F\"},\"observer\":{\"name\":\"\",\"vendor\":\"Seckiot\",\"product\":\"Seckiot Citadelle\",\"_type\":\"NIDS\",\"version\":\"\"},\"rule\":{\"description\":\"A UDP flood Denial of Service attack involves sending a large number of UDP packets to random ports on a target. This overloads the target's network and resources, leading to performance degradation or unavailability of the service to legitimate users.\",\"uuid\":\"51186749-7415-46be-90e5-000000000087\",\"name\":\"Denial Of Service - UDP Flood\",\"version\":\"1\",\"author\":\"Seckiot\"}}\n",
"event": {
"category": [
"info"
],
"kind": "alert",
"severity": 1,
"type": [
"info"
]
},
"destination": {
"address": "10.0.12.1",
"ip": "10.0.12.1",
"mac": "00:0C:29:B0:79:1C",
"port": 4739
},
"observer": {
"product": "Seckiot Citadelle",
"type": "NIDS",
"vendor": "Seckiot"
},
"related": {
"ip": [
"10.0.12.1",
"10.0.12.254"
]
},
"rule": {
"author": "Seckiot",
"description": "A UDP flood Denial of Service attack involves sending a large number of UDP packets to random ports on a target. This overloads the target's network and resources, leading to performance degradation or unavailability of the service to legitimate users.",
"id": "51186749-7415-46be-90e5-000000000087",
"name": "Denial Of Service - UDP Flood",
"version": "1"
},
"seckiot": {
"alert": {
"id": "b4eaea3e-d7bf-4792-b007-9a6731444e64"
},
"assets": {
"category": [
"IT",
"IT",
"IT",
"IT",
"IT"
],
"description": [
"DC 1",
"Firewall Site 2",
"unknown",
"unknown",
"unknown"
],
"entity": [
"domain-controller",
"router",
"router",
"virtual-server",
"virtual-server"
],
"id": [
"01f7a81d-5e0d-4c85-a5ca-a64cbad23515",
"07f5a027-73be-4bb9-a629-f97dcf210a16",
"154e6092-db3d-4bef-bf07-bf0ca2ba15a2",
"6f5f0755-d57c-48ae-a2da-333991fa87c4",
"c1d78ed5-7663-4dbb-8d1c-cfc9b5bd23ca"
],
"localisation": [
"BD 10.2.1.200 fe.1.12",
"BD 10.2.1.200 ge.1.25",
"Lab 10.0.11.200 Gi0/1",
"lab 10.0.21.91 1/1/1",
"lab 10.0.21.91 1/2/1"
],
"name": [
"10.0.1.254",
"LABNFW02.lab.local",
"LABSAD01",
"LABSKEP01",
"LABSTIA02"
],
"perdue_level": [
"3",
"3",
"3",
"3",
"3"
],
"system": [
"Microsoft Windows",
"Microsoft Windows 2016+ Server",
"Microsoft Windows Server 2019 Standard",
"Microsoft Windows Server 2019 Standard",
"unknown"
],
"version": [
"10.0.10011.16384",
"17763.379",
"17763.4737",
"unknown",
"unknown"
]
},
"catch_area": {
"name": "c1b5d877-a026-456f-90a7-526c4e463431"
},
"module": "Detection Engine",
"sensor": {
"name": "TF-VIVIENBREVET-0-SENSOR-0"
},
"sniffer": {
"name": "5c418977-9069-49d1-936c-28586fe5c2a2"
}
},
"source": {
"address": "10.0.12.254",
"ip": "10.0.12.254",
"mac": "00:0C:29:A2:6D:3F",
"port": 8346
}
}
{
"message": "{\"device\":[],\"event\":{\"code\":[],\"severity\":7,\"outcome\":\"unknown\",\"created\":\"2025-03-12T13:34:04.407568Z\",\"category\":[\"info\"],\"ingested\":\"2025-03-12T13:34:04.407568Z\",\"kind\":\"alert\",\"type\":[\"info\"]},\"forwarders\":[\"fw_sekoiaIO\"],\"observer\":{\"name\":\"\",\"vendor\":\"Seckiot\",\"product\":\"Seckiot Citadelle\",\"_type\":\"NIDS\",\"version\":\"\"},\"skt\":{\"module\":\"Cartography\",\"sniffer\":\"\",\"assets\":[{\"name\":\"2.22.251.11\",\"first_seen\":\"2025-03-12T13:33:48Z\",\"last_seen\":\"2025-03-12T13:34:04.348385Z\",\"id\":\"f2fd51d8-81c0-477b-abba-4894f1b8421d\"}],\"capture_zone\":\"\",\"alert_id\":\"b70ec8e1-432b-4293-bbcf-5ee94bf5e9df\",\"sensor\":\"\"},\"@timestamp\":\"2025-03-12T13:34:04.407568Z\",\"rule\":{\"description\":\"Asset `2.22.251.11` created\",\"uuid\":\"00000000-0000-0000-0000-000000000001\",\"name\":\"Unknown Device in the Network\",\"version\":\"1\",\"author\":\"Seckiot\"},\"@version\":\"1\"}\n",
"event": {
"category": [
"info"
],
"id": "00000000-0000-0000-0000-000000000000",
"kind": "alert",
"severity": 7,
"type": [
"info"
]
},
"observer": {
"product": "Seckiot Citadelle",
"type": "NIDS",
"vendor": "Seckiot"
},
"rule": {
"author": "Seckiot",
"description": "Asset `2.22.251.11` created",
"id": "00000000-0000-0000-0000-000000000001",
"name": "Unknown Device in the Network",
"version": "1"
},
"seckiot": {
"alert": {
"id": "b70ec8e1-432b-4293-bbcf-5ee94bf5e9df"
},
"assets": {
"category": [
"unknown"
],
"description": [
"unknown"
],
"entity": [
"unknown"
],
"id": [
"f2fd51d8-81c0-477b-abba-4894f1b8421d"
],
"localisation": [
"unknown"
],
"name": [
"2.22.251.11"
],
"perdue_level": [
"unknown"
],
"system": [
"unknown"
],
"version": [
"unknown"
]
},
"module": "Cartography"
},
"sekoiaio": {
"intake": {
"dialect": "test",
"dialect_uuid": "00000000-0000-0000-0000-000000000000",
"parsing_status": "success"
}
}
}
{
"message": "{\"device\":[],\"event\":{\"code\":[],\"severity\":1,\"outcome\":\"unknown\",\"created\":\"2025-03-12T09:29:10.485097Z\",\"category\":[\"info\"],\"ingested\":\"2025-03-12T09:29:10.485097Z\",\"kind\":\"alert\",\"type\":[\"info\"]},\"forwarders\":[\"fw_sekoiaIO\"],\"destination\":{\"ip\":\"20.10.113.82\",\"port\":443},\"skt\":{\"module\":\"Cartography\",\"sniffer\":\"br0\",\"assets\":[{\"name\":\"20.10.113.82\",\"first_seen\":\"2025-03-12T09:28:40Z\",\"last_seen\":\"2025-03-12T09:29:09.346448Z\",\"id\":\"ec4353eb-0c7c-4fe6-8523-21d840b37dbf\"},{\"system\":\"Microsoft Windows 2016+ Server\",\"first_seen\":\"2025-03-05T12:37:53.554365Z\",\"last_seen\":\"2025-03-12T09:29:07.350067Z\",\"name\":\"LABSWKS01\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"level\":3,\"version\":\"10.0.10011.16384\",\"primary_ip\":\"3a41f5fb-ecc9-4d8b-b2d0-6a94765445c9\",\"id\":\"4d5b3e7c-d058-4123-ac3b-a4788fc5c7af\",\"entity\":\"virtual-server\",\"description\":\"\",\"localisation\":\"Lab 10.0.11.200 Gi0/8\"}],\"capture_zone\":\"default\",\"session\":\"27c24bfb94ca28d0d9401b9d06fc91fb\",\"alert_id\":\"be97c9ee-bfa3-4306-9945-eac29847f06f\",\"sensor\":\"TF-VIVIENBREVET-0-SENSOR-0\"},\"@timestamp\":\"2025-03-12T09:29:10.485097Z\",\"network\":{\"protocol\":\"TLS\"},\"@version\":\"1\",\"source\":{\"vendor\":\"VMware, Inc.\",\"port\":50335,\"ip\":\"10.0.101.50\",\"mac\":\"00:0C:29:D1:22:2E\"},\"observer\":{\"name\":\"\",\"vendor\":\"Seckiot\",\"product\":\"Seckiot Citadelle\",\"_type\":\"NIDS\",\"version\":\"\"},\"rule\":{\"description\":\"New link detected between LABSWKS01 and 20.10.113.82\",\"uuid\":\"00000000-0000-0000-0000-000000000012\",\"name\":\"New Link Between Two Assets\",\"version\":\"1\",\"author\":\"Seckiot\"}}\n",
"event": {
"category": [
"info"
],
"kind": "alert",
"severity": 1,
"type": [
"info"
]
},
"destination": {
"address": "20.10.113.82",
"ip": "20.10.113.82",
"port": 443
},
"observer": {
"product": "Seckiot Citadelle",
"type": "NIDS",
"vendor": "Seckiot"
},
"related": {
"ip": [
"10.0.101.50",
"20.10.113.82"
]
},
"rule": {
"author": "Seckiot",
"description": "New link detected between LABSWKS01 and 20.10.113.82",
"id": "00000000-0000-0000-0000-000000000012",
"name": "New Link Between Two Assets",
"version": "1"
},
"seckiot": {
"alert": {
"id": "be97c9ee-bfa3-4306-9945-eac29847f06f"
},
"assets": {
"category": [
"IT",
"unknown"
],
"description": [
"unknown",
"unknown"
],
"entity": [
"unknown",
"virtual-server"
],
"id": [
"4d5b3e7c-d058-4123-ac3b-a4788fc5c7af",
"ec4353eb-0c7c-4fe6-8523-21d840b37dbf"
],
"localisation": [
"Lab 10.0.11.200 Gi0/8",
"unknown"
],
"name": [
"20.10.113.82",
"LABSWKS01"
],
"perdue_level": [
"3",
"unknown"
],
"system": [
"Microsoft Windows 2016+ Server",
"unknown"
],
"version": [
"10.0.10011.16384",
"unknown"
]
},
"catch_area": {
"name": "default"
},
"module": "Cartography",
"sensor": {
"name": "TF-VIVIENBREVET-0-SENSOR-0"
},
"sniffer": {
"name": "br0"
}
},
"source": {
"address": "10.0.101.50",
"ip": "10.0.101.50",
"mac": "00:0C:29:D1:22:2E",
"port": 50335
}
}
{
"message": "{\"device\":[],\"event\":{\"code\":[],\"severity\":7,\"outcome\":\"unknown\",\"created\":\"2025-03-12T13:34:06.487415Z\",\"category\":[\"info\"],\"ingested\":\"2025-03-12T13:34:06.487415Z\",\"kind\":\"alert\",\"type\":[\"info\"]},\"forwarders\":[\"fw_sekoiaIO\"],\"destination\":{\"ip\":\"2.22.251.11\",\"port\":443},\"skt\":{\"module\":\"Cartography\",\"sniffer\":\"br0\",\"assets\":[{\"name\":\"2.22.251.11\",\"first_seen\":\"2025-03-12T13:33:48Z\",\"last_seen\":\"2025-03-12T13:34:04.348385Z\",\"id\":\"f2fd51d8-81c0-477b-abba-4894f1b8421d\"}],\"capture_zone\":\"default\",\"session\":\"81335dd9a786a0688197ea861a2ee3db\",\"alert_id\":\"ee2b728e-aa6b-4f49-990d-48c7d2498e1f\",\"sensor\":\"TF-VIVIENBREVET-0-SENSOR-0\"},\"@timestamp\":\"2025-03-12T13:34:06.487415Z\",\"network\":{\"protocol\":\"TLS\"},\"@version\":\"1\",\"source\":{\"vendor\":\"VMware, Inc.\",\"port\":50569,\"ip\":\"10.80.10.1\",\"mac\":\"00:0C:29:A2:6D:3F\"},\"observer\":{\"name\":\"\",\"vendor\":\"Seckiot\",\"product\":\"Seckiot Citadelle\",\"_type\":\"NIDS\",\"version\":\"\"},\"rule\":{\"description\":\"New server port 2.22.251.11:443 (default) detected on 2.22.251.11\",\"uuid\":\"00000000-0000-0000-0000-000000000002\",\"name\":\"New Open Server Port\",\"version\":\"1\",\"author\":\"Seckiot\"}}\n",
"event": {
"category": [
"info"
],
"id": "00000000-0000-0000-0000-000000000000",
"kind": "alert",
"severity": 7,
"type": [
"info"
]
},
"destination": {
"address": "2.22.251.11",
"ip": "2.22.251.11",
"port": 443
},
"observer": {
"product": "Seckiot Citadelle",
"type": "NIDS",
"vendor": "Seckiot"
},
"related": {
"ip": [
"10.80.10.1",
"2.22.251.11"
]
},
"rule": {
"author": "Seckiot",
"description": "New server port 2.22.251.11:443 (default) detected on 2.22.251.11",
"id": "00000000-0000-0000-0000-000000000002",
"name": "New Open Server Port",
"version": "1"
},
"seckiot": {
"alert": {
"id": "ee2b728e-aa6b-4f49-990d-48c7d2498e1f"
},
"assets": {
"category": [
"unknown"
],
"description": [
"unknown"
],
"entity": [
"unknown"
],
"id": [
"f2fd51d8-81c0-477b-abba-4894f1b8421d"
],
"localisation": [
"unknown"
],
"name": [
"2.22.251.11"
],
"perdue_level": [
"unknown"
],
"system": [
"unknown"
],
"version": [
"unknown"
]
},
"catch_area": {
"name": "default"
},
"module": "Cartography",
"sensor": {
"name": "TF-VIVIENBREVET-0-SENSOR-0"
},
"sniffer": {
"name": "br0"
}
},
"sekoiaio": {
"intake": {
"dialect": "test",
"dialect_uuid": "00000000-0000-0000-0000-000000000000",
"parsing_status": "success"
}
},
"source": {
"address": "10.80.10.1",
"ip": "10.80.10.1",
"mac": "00:0C:29:A2:6D:3F",
"port": 50569
}
}
{
"message": "{\"device\":[],\"event\":{\"code\":[],\"severity\":7,\"outcome\":\"unknown\",\"created\":\"2025-03-06T14:05:57.457022Z\",\"category\":[\"info\"],\"ingested\":\"2025-03-06T14:05:57.457022Z\",\"kind\":\"alert\",\"type\":[\"info\"]},\"forwarders\":[\"fw_sekoiaIO\"],\"observer\":{\"name\":\"\",\"vendor\":\"Seckiot\",\"product\":\"Seckiot Citadelle\",\"_type\":\"NIDS\",\"version\":\"\"},\"skt\":{\"module\":\"CVE\",\"sniffer\":\"\",\"assets\":[{\"system\":\"Microsoft Windows Server 2019 Standard\",\"first_seen\":\"2025-03-06T13:49:56.593575Z\",\"last_seen\":\"2025-03-06T14:05:55.420426Z\",\"name\":\"LABSAD01\",\"category\":\"IT\",\"hardware_vendor\":\"VMware, Inc.\",\"modele\":\"VMware7,1\",\"level\":3,\"version\":\"17763.379\",\"primary_ip\":\"7524efed-8f77-4f40-be72-5771a56e2f47\",\"id\":\"07f5a027-73be-4bb9-a629-f97dcf210a16\",\"entity\":\"domain-controller\",\"description\":\"DC 1\",\"localisation\":\"Lab 10.0.11.200 Gi0/1\"}],\"capture_zone\":\"\",\"alert_id\":\"d66a025c-6e51-42a4-88f9-50bb719b1ac1\",\"sensor\":\"\"},\"vulnerability\":{\"severity\":\"medium\",\"scanner\":{\"vendor\":\"Seckiot\"},\"reference\":\"http://www.exploit-db.com/exploits/26528/,http://www.exploit-db.com/exploits/26528/\",\"enumeration\":\"CVE\",\"id\":\"CVE-2013-1414\",\"description\":\"New vulnerability CVE-2013-1414 detected on LABSAD01\",\"score\":{\"base\":\"5.1\",\"version\":\"3.1\"},\"category\":null,\"classification\":\"CVSS\"},\"@timestamp\":\"2025-03-06T14:05:57.457022Z\",\"rule\":{\"description\":\"New vulnerability CVE-2013-1414 detected on LABSAD01\",\"uuid\":\"00000000-0000-0000-0000-000000000003\",\"name\":\"Nouvelle Vuln\u00e9rabilit\u00e9 D\u00e9couverte\",\"version\":\"1\",\"author\":\"seckiot\"},\"@version\":\"1\"}\n",
"event": {
"category": [
"info"
],
"id": "00000000-0000-0000-0000-000000000000",
"kind": "alert",
"severity": 7,
"type": [
"info"
]
},
"observer": {
"product": "Seckiot Citadelle",
"type": "NIDS",
"vendor": "Seckiot"
},
"rule": {
"author": "seckiot",
"description": "New vulnerability CVE-2013-1414 detected on LABSAD01",
"id": "00000000-0000-0000-0000-000000000003",
"name": "Nouvelle Vuln\u00e9rabilit\u00e9 D\u00e9couverte",
"version": "1"
},
"seckiot": {
"alert": {
"id": "d66a025c-6e51-42a4-88f9-50bb719b1ac1"
},
"assets": {
"category": [
"IT"
],
"description": [
"DC 1"
],
"entity": [
"domain-controller"
],
"id": [
"07f5a027-73be-4bb9-a629-f97dcf210a16"
],
"localisation": [
"Lab 10.0.11.200 Gi0/1"
],
"name": [
"LABSAD01"
],
"perdue_level": [
"3"
],
"system": [
"Microsoft Windows Server 2019 Standard"
],
"version": [
"17763.379"
]
},
"module": "CVE"
},
"sekoiaio": {
"intake": {
"dialect": "test",
"dialect_uuid": "00000000-0000-0000-0000-000000000000",
"parsing_status": "success"
}
},
"vulnerability": {
"classification": "CVSS",
"description": "New vulnerability CVE-2013-1414 detected on LABSAD01",
"enumeration": "CVE",
"id": "CVE-2013-1414",
"reference": "http://www.exploit-db.com/exploits/26528/,http://www.exploit-db.com/exploits/26528/",
"scanner": {
"vendor": "Seckiot"
},
"score": {
"base": 5.1,
"version": "3.1"
},
"severity": "medium"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
destination.ip |
ip |
IP address of the destination. |
destination.mac |
keyword |
MAC address of the destination. |
destination.port |
long |
Port of the destination. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.kind |
keyword |
The kind of the event. The highest categorization field in the hierarchy. |
event.outcome |
keyword |
The outcome of the event. The lowest level categorization field in the hierarchy. |
event.severity |
long |
Numeric severity of the event. |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
network.protocol |
keyword |
Application protocol name. |
network.transport |
keyword |
Protocol Name corresponding to the field iana_number. |
observer.name |
keyword |
Custom name of the observer. |
observer.product |
keyword |
The product name of the observer. |
observer.type |
keyword |
The type of the observer the data is coming from. |
observer.vendor |
keyword |
Vendor name of the observer. |
observer.version |
keyword |
Observer version. |
rule.author |
keyword |
Rule author |
rule.description |
keyword |
Rule description |
rule.id |
keyword |
Rule ID |
rule.name |
keyword |
Rule name |
rule.version |
keyword |
Rule version |
seckiot.alert.id |
text |
Unique ID of the alert |
seckiot.assets.category |
text |
Category of the asset IT/OT/IOT |
seckiot.assets.description |
text |
Description of the asset |
seckiot.assets.entity |
text |
Entity of the asset |
seckiot.assets.id |
text |
Unique ID of the asset |
seckiot.assets.localisation |
text |
Localisation of the asset |
seckiot.assets.name |
text |
Name of the asset |
seckiot.assets.perdue_level |
text |
Perdue level of the asset, between 0 and 6 |
seckiot.assets.system |
text |
Name of operating system |
seckiot.assets.version |
text |
OS version of the asset |
seckiot.catch_area.name |
text |
Name of the catch area where the flow has been captured |
seckiot.module |
text |
Seckiot module definition |
seckiot.sensor.name |
text |
Name of the sensor which capture the flow |
seckiot.sniffer.name |
text |
Name of the sniffer which capture the flow |
source.ip |
ip |
IP address of the source. |
source.mac |
keyword |
MAC address of the source. |
source.port |
long |
Port of the source. |
vulnerability.category |
keyword |
Category of a vulnerability. |
vulnerability.classification |
keyword |
Classification of the vulnerability. |
vulnerability.description |
keyword |
Description of the vulnerability. |
vulnerability.enumeration |
keyword |
Identifier of the vulnerability. |
vulnerability.id |
keyword |
ID of the vulnerability. |
vulnerability.reference |
keyword |
Reference of the vulnerability. |
vulnerability.report_id |
keyword |
Scan identification number. |
vulnerability.scanner.vendor |
keyword |
Name of the scanner vendor. |
vulnerability.score.base |
float |
Vulnerability Base score. |
vulnerability.score.environmental |
float |
Vulnerability Environmental score. |
vulnerability.score.temporal |
float |
Vulnerability Temporal score. |
vulnerability.score.version |
keyword |
CVSS version. |
vulnerability.severity |
keyword |
Severity of the vulnerability. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.