Ubika Cloud Protector Alerts
Overview
Ubika Cloud Protector is a cloud-native security solution, providing advanced threat detection and data protection to secure cloud environments, enabling real-time monitoring and mitigation of risks in cloud-based infrastructures.
- Vendor:Ubika
- Supported environment: SaaS
- Detection based on: Alert
- Supported application or feature: Web application firewall logs
Configure
How to get API keys info
3 information are required to collect data from Ubika:
- The
provider name(available in Ubika interface) - The
tenant name(available in Ubika interface) - A
token(provided by Ubika support team)
Warning
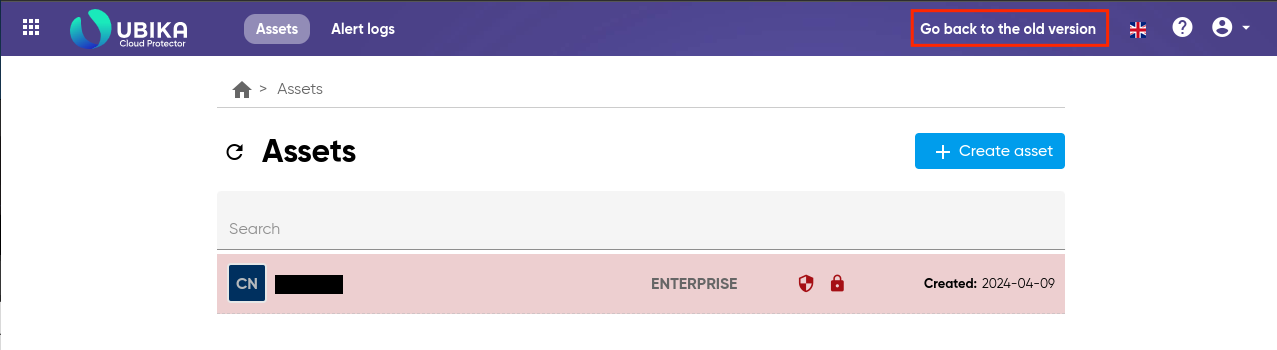
The following instructions are based on the old interface of Ubika Cloud Protector. Please, switch to the old interface if you use the new one.
To get API keys info:
- Log in the Ubika Cloud protector
-
Go to
Account>API Access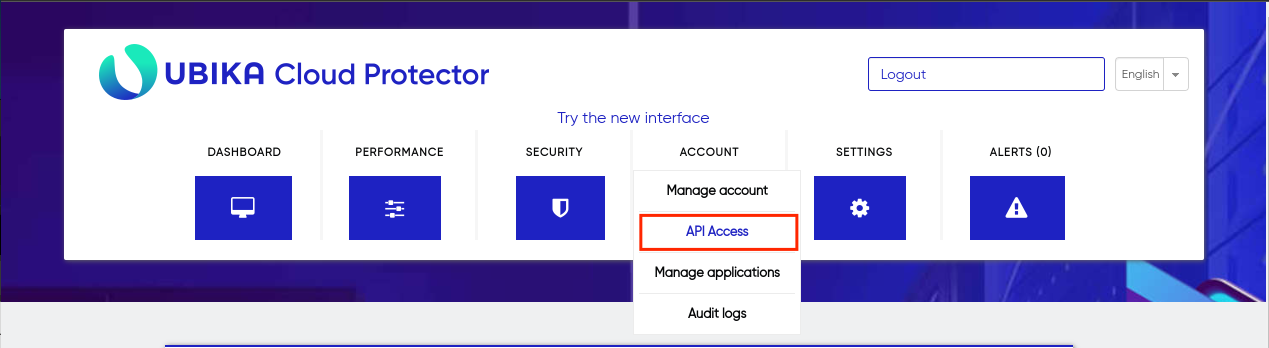
-
In the
API KEYS INFOsection, please note theprovider nameand thetenant name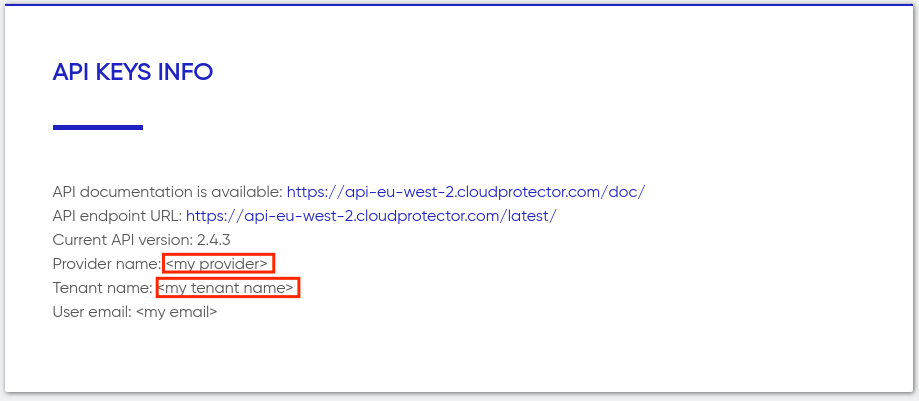
-
Finally, contact
Ubika supportto request atokenfor the legacy API. This specifictokencannot be retrieved through the Ubika interface at the moment.
Create your intake
- Go to the intake page and create a new intake from the
Ubika Cloud Protector. - Set the intake account configuration with the
provider,tenantandtokenfrom theHow to get API keys infostep
Enjoy your events on the Events page
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
{
"application_id": "www.some-app.com",
"id": "4.1.4.0",
"reason": "module_name == 'eaccess' and event.SECURITY_URL == '/phpinfo.php' and event.SECURITY_ATTACKID == '10527-0 ' and tokens['http_ea__block_reason'] == 'http_blacklist' and tokens['http_ea__block_part'] == 'uri' and tokens['http_ea_bl__is_custom_rule'] == False and tokens['http_ea_seclist__is_combine_rule'] == False and tokens['http_ea_seclist__is_virtual_patching'] == False",
"http_method": "GET",
"rule_id": "10527-0 ",
"attack_family": "Information Disclosure",
"ip_source": "1.2.3.4",
"traffic_id": "ZhVpbQoAQi8AAE2yAksAAAAA",
"path": "/phpinfo.php",
"timestamp": 1712679277
}
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake Ubika Cloud Protector Alerts. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x Ubika Cloud Protector Alerts on ATT&CK Navigator
Cryptomining
Detection of domain names potentially related to cryptomining activities.
- Effort: master
Discord Suspicious Download
Discord is a messaging application. It allows users to create their own communities to share messages and attachments. Those attachments have little to no overview and can be downloaded by almost anyone, which has been abused by attackers to host malicious payloads.
- Effort: advanced
Dynamic DNS Contacted
Detect communication with dynamic dns domain. This kind of domain is often used by attackers. This rule can trigger false positive in non-controlled environment because dynamic dns is not always malicious.
- Effort: master
Exfiltration Domain
Detects traffic toward a domain flagged as a possible exfiltration vector.
- Effort: master
Koadic MSHTML Command
Detects Koadic payload using MSHTML module
- Effort: intermediate
Potential Azure AD Phishing Page (Adversary-in-the-Middle)
Detects an HTTP request to an URL typical of the Azure AD authentication flow, but towards a domain that is not one the legitimate Microsoft domains used for Azure AD authentication.
- Effort: intermediate
Remote Access Tool Domain
Detects traffic toward a domain flagged as a Remote Administration Tool (RAT).
- Effort: master
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
Sekoia.io EICAR Detection
Detects observables in Sekoia.io CTI tagged as EICAR, which are fake samples meant to test detection.
- Effort: master
TOR Usage Generic Rule
Detects TOR usage globally, whether the IP is a destination or source. TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Web application firewall logs |
Ubika detects and mitigates threats against web applications and APIs |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | alert |
| Category | intrusion_detection |
| Type | blocked |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "{\"application_id\": \"www.some-app.com\", \"id\": \"4.1.4.0\", \"reason\": \"module_name == 'eaccess' and event.SECURITY_URL == '/phpinfo.php' and event.SECURITY_ATTACKID == '10527-0 ' and tokens['http_ea__block_reason'] == 'http_blacklist' and tokens['http_ea__block_part'] == 'uri' and tokens['http_ea_bl__is_custom_rule'] == False and tokens['http_ea_seclist__is_combine_rule'] == False and tokens['http_ea_seclist__is_virtual_patching'] == False\", \"http_method\": \"GET\", \"rule_id\": \"10527-0 \", \"attack_family\": \"Information Disclosure\", \"ip_source\": \"1.2.3.4\", \"traffic_id\": \"ZhVpbQoAQi8AAE2yAksAAAAA\", \"path\": \"/phpinfo.php\", \"timestamp\": 1712679277}",
"event": {
"category": [
"intrusion_detection"
],
"kind": "alert",
"reason": "module_name == 'eaccess' and event.SECURITY_URL == '/phpinfo.php' and event.SECURITY_ATTACKID == '10527-0 ' and tokens['http_ea__block_reason'] == 'http_blacklist' and tokens['http_ea__block_part'] == 'uri' and tokens['http_ea_bl__is_custom_rule'] == False and tokens['http_ea_seclist__is_combine_rule'] == False and tokens['http_ea_seclist__is_virtual_patching'] == False",
"type": [
"blocked"
]
},
"@timestamp": "2024-04-09T16:14:37Z",
"http": {
"request": {
"method": "GET"
}
},
"observer": {
"product": "Cloud protector",
"vendor": "Ubika"
},
"related": {
"ip": [
"1.2.3.4"
]
},
"rule": {
"id": "10527-0"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"ubika": {
"cloud_protector": {
"application_id": "www.some-app.com",
"attack_family": "Information Disclosure"
}
},
"url": {
"path": "/phpinfo.php"
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.kind |
keyword |
The kind of the event. The highest categorization field in the hierarchy. |
event.reason |
keyword |
Reason why this event happened, according to the source |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
http.request.method |
keyword |
HTTP request method. |
observer.product |
keyword |
The product name of the observer. |
observer.vendor |
keyword |
Vendor name of the observer. |
rule.id |
keyword |
Rule ID |
source.ip |
ip |
IP address of the source. |
ubika.cloud_protector.application_id |
keyword |
Website server name |
ubika.cloud_protector.attack_family |
keyword |
The nature of the attack |
url.path |
wildcard |
Path of the request, such as "/search". |
url.query |
keyword |
Query string of the request. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.