Varonis Data Security
Overview
Varonis offers solutions to track and protect data.
- Vendor: Varonis
- Supported environment: SaaS
- Detection based on: Alert
- Supported application or feature: Data loss prevention
Configure
This setup guide will show you how to forward your Varonis Data Security logs to Sekoia.io by means of a syslog transport channel.
Prerequisites
- Have an internal log concentrator (Rsyslog)
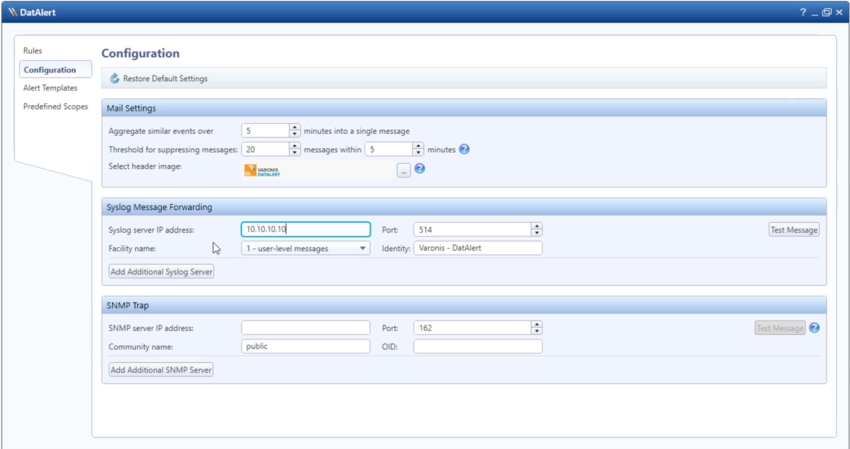
Enable Syslog forwarding for Varonis Data Security
You can configure the Syslog server address in DatAlert so that alerts are sent to SEKOIA. To configure the Syslog server address in DatAlert:
- In DatAdvantage, select
Tools>DatAlert. DatAlert is displayed. - From the left menu, select
Configuration. - In the
Syslog Message Forwardingsection, fill the Syslog server IP address and the Port with the ip address and the port of the log concentrator. - The expected severity is
info - Click OK
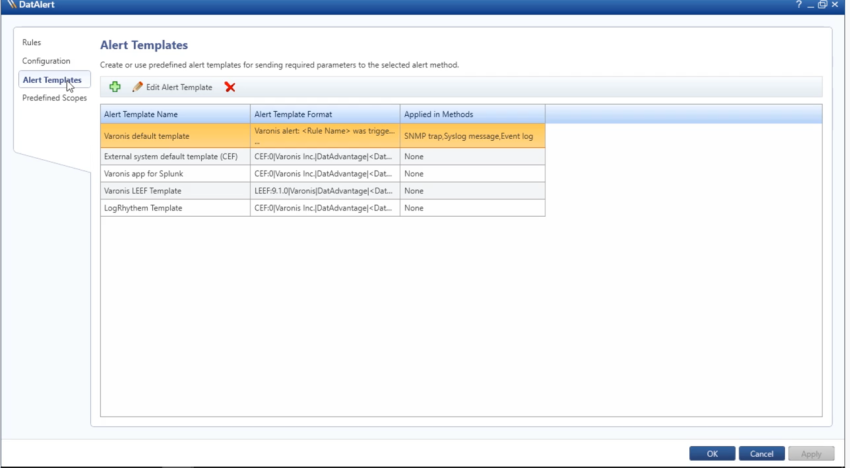
Create a message forwarding template
- In DatAlert, select
Alert Templates - Select
External system default template (CEF)and clickEdit Alert Template - In
Apply to alert methods, selectSyslog message - Click OK
Create the intake
Go to the intake page and create a new intake from the format Varonis Data Security
Warning
Sekoia expects to receive events based on a date in UTC. Be sure to change the Varonis settings accordingly on the appliance with their assistance. Or create a self managed Custom Format on Sekoia by duplicating our built-in Varonis Intake and adapt the set_timestamp Stage accordingly.
Forward logs to Sekoia.io
Please consult the Syslog Forwarding documentation to forward these logs to Sekoia.io.
Currently, the syslog format generated by Varonis does not comply with RFC standards. As a result, the transmitted data is not inherently compatible with the Sekoia forwarder. Therefore, it is necessary to refer to this documentation in order to extend the default configuration of the forwarder (available since version 2.4) and add this specific configuration for Varonis logs:
input(type="im$PROTOCOL" port="$PORT" ruleset="remoteVaronis")
template(name="SEKOIAIO_Varonis_Template" type="string" string="<%pri%>1 %timegenerated:::date-rfc3339% %hostname% $APP-NAME - LOG [SEKOIA@53288 intake_key=\"$INTAKE-KEY\"] %msg:R,ERE,1,FIELD:.*(CEF.*)$--end%\n")
ruleset(name="remoteVaronis"){
action(
name="varonis"
type="omfwd"
protocol="tcp"
target="intake.sekoia.io"
port="10514"
TCP_Framing="octet-counted"
StreamDriver="gtls"
StreamDriverMode="1"
StreamDriverAuthMode="x509/name"
StreamDriverPermittedPeers="intake.sekoia.io"
Template="SEKOIAIO_Varonis_Template"
)
}
Note
Don't forget to replace the variables $PROTOCOL (tcp or udp) to choose the protocol by which Varonis logs are received, the $PORT of entry, your $APP-NAME syslog, and your $INTAKE-KEY Sekoia.
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
CEF:0|Varonis|DatAdvantage|0.0.1|666|Alert|Medium|cat=Alert cs1=joh.doe@gmail.com cs3=runme.exe cs5=Mon Aug 1 06:40:30 2022 deviceCustomDate1=Mon Aug 1 06:40:35 2022 suser=fool rt=2023-06-09T14:16:15.212418 cs2=Abnormal admin behavior: access to atypical mailboxes cn1=Rule Name end=2023-06-09T14:16:15.212435 duser=root dhost=127.0.0.1 filePath=~/pub.key act=Alert dvchost=HOSTNAME dvc=192.168.0.1 outcome=failure msg=Hello externalId=172ae7a0-e2c6-4b0d-a48e-b2cb8ead2481
0|Varonis Inc.|DatAdvantage|8.6.32|5011|User locked out|3|rt=Oct 14 2024 11:33:57 cat=Alert cs2=Lockout: Multiple account lock-out events cs2Label=RuleName cn1=136 cn1Label=RuleID end=Oct 14 2024 11:33:51 duser=COMPANY.LOCAL\John Doe dhost=Host filePath=COMPANY.LOCAL/Company/arborescence/John DOE fname=John DOE act=User locked out dvchost= dvc= outcome=Success msg= cs3= cs3Label=AttachmentName cs4=http://srv-gar-vardsp/DatAdvantage/#/app/analytics/entity/Alert/12345678-abcd-1234-5678-abcdef012345 cs4Label=ClientAccessType deviceCustomDate1= fileType= cs1= cs1Label=MailRecipient suser= cs5= cs5Label=MailboxAccessType cnt=5 cs6= cs6Label=ChangedPermissions oldFilePermission= filePermission= dpriv= start=Oct 14 2024 11:29:48 DescriptionRule=Several account lock-out events occurred within a short time frame. This may indicate a brute-force attack aimed at stealing users' credentials, or causing a denial-of-service for multiple users. DescriptionAlert= RuleStoryline= Path=COMPANY.LOCAL/Company/arborescence/John DOE ActingObjectSAM=doe_j ActingObjectDomaineName=COMPANY.LOCAL AlertCategory=Intrusion AffectedObjectSAM=doe_j AffectedObjectDomain=COMPANY.LOCAL DestinationDip= DestinationDeviceName=
CEF:0|Varonis|DatAdvantage|0.0.1|666|Alert|Medium|cat=Alert cs2=SomeRule cs2Label=RuleName cn1=Some rule description cn1Label=RuleID end= duser= dhost=1.2.3.4 filePath= fname= act= dvchost= outcome= msg= cs3= cs3Label=AttachmentName cs4= cs4Label=ClientAccessType deviceCustomDate1= fileType= cs1= cs1Label=MailRecipient suser= cs5= cs5Label=MailboxAccessType cnt= cs6= cs6Label=ChangedPermissions oldFilePermission=555 filePermission=777 dpriv= start=
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake Varonis Data Security. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x Varonis Data Security on ATT&CK Navigator
Adidnsdump Enumeration
Detects use of the tool adidnsdump for enumeration and discovering DNS records.
- Effort: advanced
Advanced IP Scanner
Detects the use of Advanced IP Scanner. Seems to be a popular tool for ransomware groups.
- Effort: master
Certify Or Certipy
Detects the use of certify and certipy which are two different tools used to enumerate and abuse Active Directory Certificate Services.
- Effort: advanced
Cobalt Strike Default Beacons Names
Detects the default names of Cobalt Strike beacons / payloads.
- Effort: intermediate
Credential Dump Tools Related Files
Detects processes or file names related to credential dumping tools and the dropped files they generate by default.
- Effort: advanced
Cryptomining
Detection of domain names potentially related to cryptomining activities.
- Effort: master
Dynamic DNS Contacted
Detect communication with dynamic dns domain. This kind of domain is often used by attackers. This rule can trigger false positive in non-controlled environment because dynamic dns is not always malicious.
- Effort: master
Exfiltration Domain
Detects traffic toward a domain flagged as a possible exfiltration vector.
- Effort: master
HTA Infection Chains
Detect the creation of a ZIP file and an HTA file as it is often used in infection chains. Furthermore it also detects the use of suspicious processes launched by explorer.exe combined with the creation of an HTA file, since it is also often used in infection chains (LNK - HTA for instance).
- Effort: advanced
HTML Smuggling Suspicious Usage
Based on several samples from different botnets, this rule aims at detecting HTML infection chain by looking for HTML created files followed by suspicious files being executed.
- Effort: advanced
HackTools Suspicious Names
Quick-win rule to detect the default process names or file names of several HackTools.
- Effort: advanced
ISO LNK Infection Chain
Detection of an ISO (or any other similar archive file) downloaded file, followed by a child-process of explorer, which is characteristic of an infection using an ISO containing an LNK file. For events with host.name.
- Effort: master
NTDS.dit File In Suspicious Directory
The file NTDS.dit is supposed to be located mainly in C:\Windows\NTDS. The rule checks whether the file is in a legitimate directory or not (through file creation events). This is usually really suspicious and could indicate an attacker trying copy the file to then look for users password hashes.
- Effort: advanced
OneNote Embedded File
Detects creation or uses of OneNote embedded files with unusual extensions.
- Effort: intermediate
PasswordDump SecurityXploded Tool
Detects the execution of the PasswordDump SecurityXploded Tool
- Effort: elementary
Process Trace Alteration
PTrace syscall provides a means by which one process ("tracer") may observe and control the execution of another process ("tracee") and examine and change the tracee's memory and registers. Attacker might want to abuse ptrace functionnality to analyse memory process. It requires to be admin or set ptrace_scope to 0 to allow all user to trace any process.
- Effort: advanced
RTLO Character
Detects RTLO (Right-To-Left character) in file and process names.
- Effort: elementary
Remote Access Tool Domain
Detects traffic toward a domain flagged as a Remote Administration Tool (RAT).
- Effort: master
Remote Monitoring and Management Software - AnyDesk
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool AnyDesk.
- Effort: master
Remote Monitoring and Management Software - Atera
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool Atera.
- Effort: master
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
Sekoia.io EICAR Detection
Detects observables in Sekoia.io CTI tagged as EICAR, which are fake samples meant to test detection.
- Effort: master
Suspicious Email Attachment Received
Detects email containing a suspicious file as an attachment, based on its extension.
- Effort: advanced
Suspicious File Name
Detects suspicious file name possibly linked to malicious tool.
- Effort: advanced
Suspicious PROCEXP152.sys File Created In Tmp
Detects the creation of the PROCEXP152.sys file in the application-data local temporary folder. This driver is used by Sysinternals Process Explorer but also by KDU (https://github.com/hfiref0x/KDU) or Ghost-In-The-Logs (https://github.com/bats3c/Ghost-In-The-Logs), which uses KDU. Note - Clever attackers may easily bypass this detection by just renaming the driver filename. Therefore just Medium-level and don't rely on it.
- Effort: advanced
TOR Usage Generic Rule
Detects TOR usage globally, whether the IP is a destination or source. TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
Varonis Many Accounts Disabled
This rule identifies a high number of account disabled.
- Effort: master
Varonis Many File Created and Deleted
This rule identifies a high number of file created and deleted on the same host. It is a typical ransomware behavior.
- Effort: master
Varonis Massive Dowloads By A Single User
This rule identifies a high number of File dowloaded by a single user.
- Effort: master
WCE wceaux.dll Creation
Detects wceaux.dll creation while Windows Credentials Editor (WCE) is executed.
- Effort: intermediate
Webshell Creation
Detects possible webshell file creation. It requires File Creation monitoring, which can be done using Sysmon's Event ID 11. However the recommended SwiftOnSecurity configuration does not fully cover the needs for this rule, it needs to be updated with the proper file names extensions.
- Effort: master
ZIP LNK Infection Chain
Detection of an ZIP download followed by a child-process of explorer, followed by multiple Windows processes.This is widely used as an infection chain mechanism.
- Effort: advanced
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Data loss prevention |
Varonis detects data exportation |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | alert |
| Category | `` |
| Type | info |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "CEF:0|Varonis|DatAdvantage|0.0.1|666|Alert|Medium|cat=Alert cs1=joh.doe@gmail.com cs3=runme.exe cs5=Mon Aug 1 06:40:30 2022 deviceCustomDate1=Mon Aug 1 06:40:35 2022 suser=fool rt=2023-06-09T14:16:15.212418 cs2=Abnormal admin behavior: access to atypical mailboxes cn1=Rule Name end=2023-06-09T14:16:15.212435 duser=root dhost=127.0.0.1 filePath=~/pub.key act=Alert dvchost=HOSTNAME dvc=192.168.0.1 outcome=failure msg=Hello externalId=172ae7a0-e2c6-4b0d-a48e-b2cb8ead2481",
"event": {
"action": "Alert",
"category": [
"email"
],
"dataset": "Alert",
"end": "2023-06-09T14:16:15.212435Z",
"kind": "alert",
"reason": "Hello",
"type": [
"info"
]
},
"@timestamp": "2023-06-09T14:16:15.212418Z",
"email": {
"attachments": [
{
"file": {
"name": "runme.exe"
}
}
],
"delivery_timestamp": "2022-08-01T06:40:35Z",
"from": {
"address": "fool"
},
"to": {
"address": "joh.doe@gmail.com"
}
},
"file": {
"directory": "~",
"name": "pub.key",
"path": "~/pub.key"
},
"host": {
"name": "127.0.0.1"
},
"observer": {
"product": "DatAdvantage",
"vendor": "Varonis",
"version": "0.0.1"
},
"related": {
"hosts": [
"HOSTNAME"
],
"ip": [
"192.168.0.1"
],
"user": [
"root"
]
},
"rule": {
"description": "Abnormal admin behavior: access to atypical mailboxes",
"id": "666",
"name": "Rule Name"
},
"source": {
"address": "HOSTNAME",
"domain": "HOSTNAME",
"ip": "192.168.0.1"
},
"user": {
"name": "root"
},
"varonis": {
"datalert": {
"id": "172ae7a0-e2c6-4b0d-a48e-b2cb8ead2481",
"outcome": "failure"
}
}
}
{
"message": "0|Varonis Inc.|DatAdvantage|8.6.32|5011|User locked out|3|rt=Oct 14 2024 11:33:57 cat=Alert cs2=Lockout: Multiple account lock-out events cs2Label=RuleName cn1=136 cn1Label=RuleID end=Oct 14 2024 11:33:51 duser=COMPANY.LOCAL\\John Doe dhost=Host filePath=COMPANY.LOCAL/Company/arborescence/John DOE fname=John DOE act=User locked out dvchost= dvc= outcome=Success msg= cs3= cs3Label=AttachmentName cs4=http://srv-gar-vardsp/DatAdvantage/#/app/analytics/entity/Alert/12345678-abcd-1234-5678-abcdef012345 cs4Label=ClientAccessType deviceCustomDate1= fileType= cs1= cs1Label=MailRecipient suser= cs5= cs5Label=MailboxAccessType cnt=5 cs6= cs6Label=ChangedPermissions oldFilePermission= filePermission= dpriv= start=Oct 14 2024 11:29:48 DescriptionRule=Several account lock-out events occurred within a short time frame. This may indicate a brute-force attack aimed at stealing users' credentials, or causing a denial-of-service for multiple users. DescriptionAlert= RuleStoryline= Path=COMPANY.LOCAL/Company/arborescence/John DOE ActingObjectSAM=doe_j ActingObjectDomaineName=COMPANY.LOCAL AlertCategory=Intrusion AffectedObjectSAM=doe_j AffectedObjectDomain=COMPANY.LOCAL DestinationDip= DestinationDeviceName=",
"event": {
"action": "User locked out",
"category": [
"intrusion_detection"
],
"dataset": "Alert",
"end": "2024-10-14T11:33:51Z",
"kind": "alert",
"severity": 3,
"type": [
"info"
],
"url": "http://srv-gar-vardsp/DatAdvantage/#/app/analytics/entity/Alert/12345678-abcd-1234-5678-abcdef012345"
},
"@timestamp": "2024-10-14T11:29:48Z",
"destination": {
"user": {
"domain": "COMPANY.LOCAL",
"name": "doe_j"
}
},
"file": {
"name": "John DOE",
"path": "COMPANY.LOCAL/Company/arborescence/John DOE"
},
"host": {
"name": "Host"
},
"observer": {
"product": "DatAdvantage",
"vendor": "Varonis Inc.",
"version": "8.6.32"
},
"related": {
"user": [
"John Doe",
"doe_j"
]
},
"rule": {
"description": "Several account lock-out events occurred within a short time frame. This may indicate a brute-force attack aimed at stealing users' credentials, or causing a denial-of-service for multiple users.",
"id": "136",
"name": "Lockout: Multiple account lock-out events"
},
"source": {
"user": {
"domain": "COMPANY.LOCAL",
"name": "doe_j"
}
},
"user": {
"domain": "COMPANY.LOCAL",
"name": "John Doe"
},
"varonis": {
"datalert": {
"num_events": 5,
"outcome": "Success"
}
}
}
{
"message": "CEF:0|Varonis|DatAdvantage|0.0.1|666|Alert|Medium|cat=Alert cs2=SomeRule cs2Label=RuleName cn1=Some rule description cn1Label=RuleID end= duser= dhost=1.2.3.4 filePath= fname= act= dvchost= outcome= msg= cs3= cs3Label=AttachmentName cs4= cs4Label=ClientAccessType deviceCustomDate1= fileType= cs1= cs1Label=MailRecipient suser= cs5= cs5Label=MailboxAccessType cnt= cs6= cs6Label=ChangedPermissions oldFilePermission=555 filePermission=777 dpriv= start=",
"event": {
"category": [
"network"
],
"dataset": "Alert",
"kind": "alert",
"type": [
"info"
]
},
"host": {
"name": "1.2.3.4"
},
"observer": {
"product": "DatAdvantage",
"vendor": "Varonis",
"version": "0.0.1"
},
"rule": {
"description": "SomeRule",
"id": "666",
"name": "SomeRule"
},
"varonis": {
"datalert": {
"file": {
"old_permission": "555",
"permission": "777"
}
}
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
destination.ip |
ip |
IP address of the destination. |
destination.user.domain |
keyword |
Name of the directory the user is a member of. |
destination.user.name |
keyword |
Short name or login of the user. |
email.attachments |
nested |
List of objects describing the attachments. |
email.delivery_timestamp |
date |
Date and time when message was delivered. |
email.from.address |
keyword |
The sender's email address. |
email.to.address |
keyword |
Email address of recipient |
event.action |
keyword |
The action captured by the event. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.dataset |
keyword |
Name of the dataset. |
event.end |
date |
event.end contains the date when the event ended or when the activity was last observed. |
event.kind |
keyword |
The kind of the event. The highest categorization field in the hierarchy. |
event.reason |
keyword |
Reason why this event happened, according to the source |
event.severity |
long |
Numeric severity of the event. |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
event.url |
keyword |
Event investigation URL |
file.name |
keyword |
Name of the file including the extension, without the directory. |
file.path |
keyword |
Full path to the file, including the file name. |
host.name |
keyword |
Name of the host. |
observer.product |
keyword |
The product name of the observer. |
observer.vendor |
keyword |
Vendor name of the observer. |
observer.version |
keyword |
Observer version. |
rule.description |
keyword |
Rule description |
rule.id |
keyword |
Rule ID |
rule.name |
keyword |
Rule name |
source.domain |
keyword |
The domain name of the source. |
source.ip |
ip |
IP address of the source. |
source.user.domain |
keyword |
Name of the directory the user is a member of. |
source.user.name |
keyword |
Short name or login of the user. |
user.domain |
keyword |
Name of the directory the user is a member of. |
user.name |
keyword |
Short name or login of the user. |
varonis.datalert.description |
keyword |
The description of the triggered alert. |
varonis.datalert.destination.device |
keyword |
The destination device name. |
varonis.datalert.file.old_permission |
keyword |
The permissions before the change. Data is not collected for all event types. |
varonis.datalert.file.permission |
keyword |
The permissions after the change. Data is not collected for all event types. |
varonis.datalert.file.permissions_change |
keyword |
The specified changes in permissions. Data is not collected for all event types. |
varonis.datalert.id |
keyword |
The ID of the triggered alert within DatAlert. |
varonis.datalert.num_events |
number |
The number of events which triggered the alert. |
varonis.datalert.outcome |
keyword |
Whether the event which triggered the alert succeeded or failed. |
varonis.datalert.rule.storyline |
keyword |
The rule storyline of the triggered alert. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.