EfficientIP SOLIDServer DDI
Overview
EfficientIP SOLIDserver suite of appliances is designed to deliver highly scalable, secure and robust virtual and hardware appliances for critical IPAM-DNS-DHCP-NTP-TFTP services.
- Vendor: EfficientIP
- Supported environment: On prem
- Version Compatibility: 8.0
- Detection based on: Telemetry
Supported versions
This integration supports the following versions: - 8.3.x - 8.4.x
Supported events
This integration supports the following events:
- DNS logs from named
Configure
In this guide, you will configure the gateway to forward events to syslog.
Prerequisites
An internal syslog concentrator is required to collect and forward events to Sekoia.io.
Enable Syslog forwarding
- Log in SOLIDServer console
-
On the left panel, click
Administration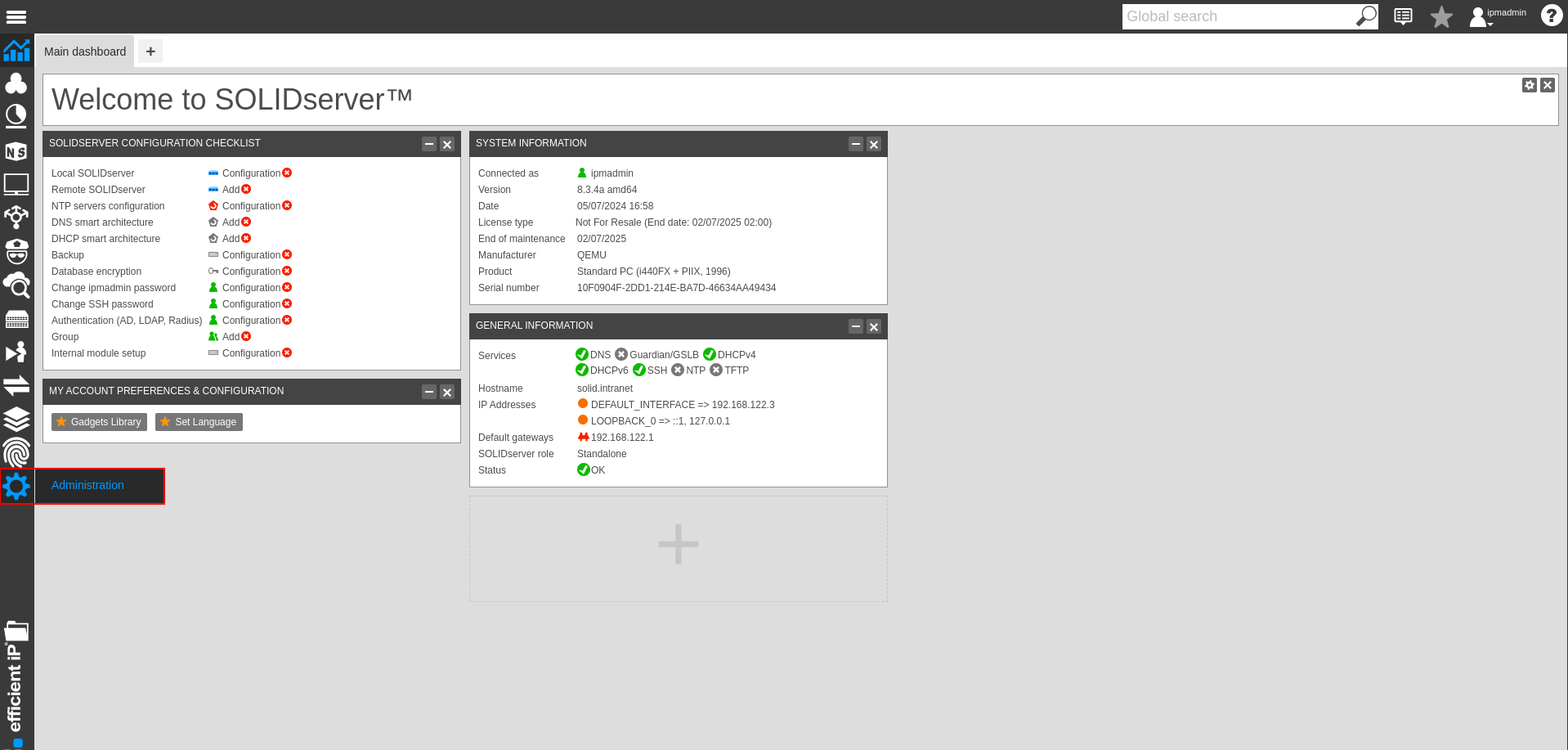
-
In the
monitoringsection, clickConfiguration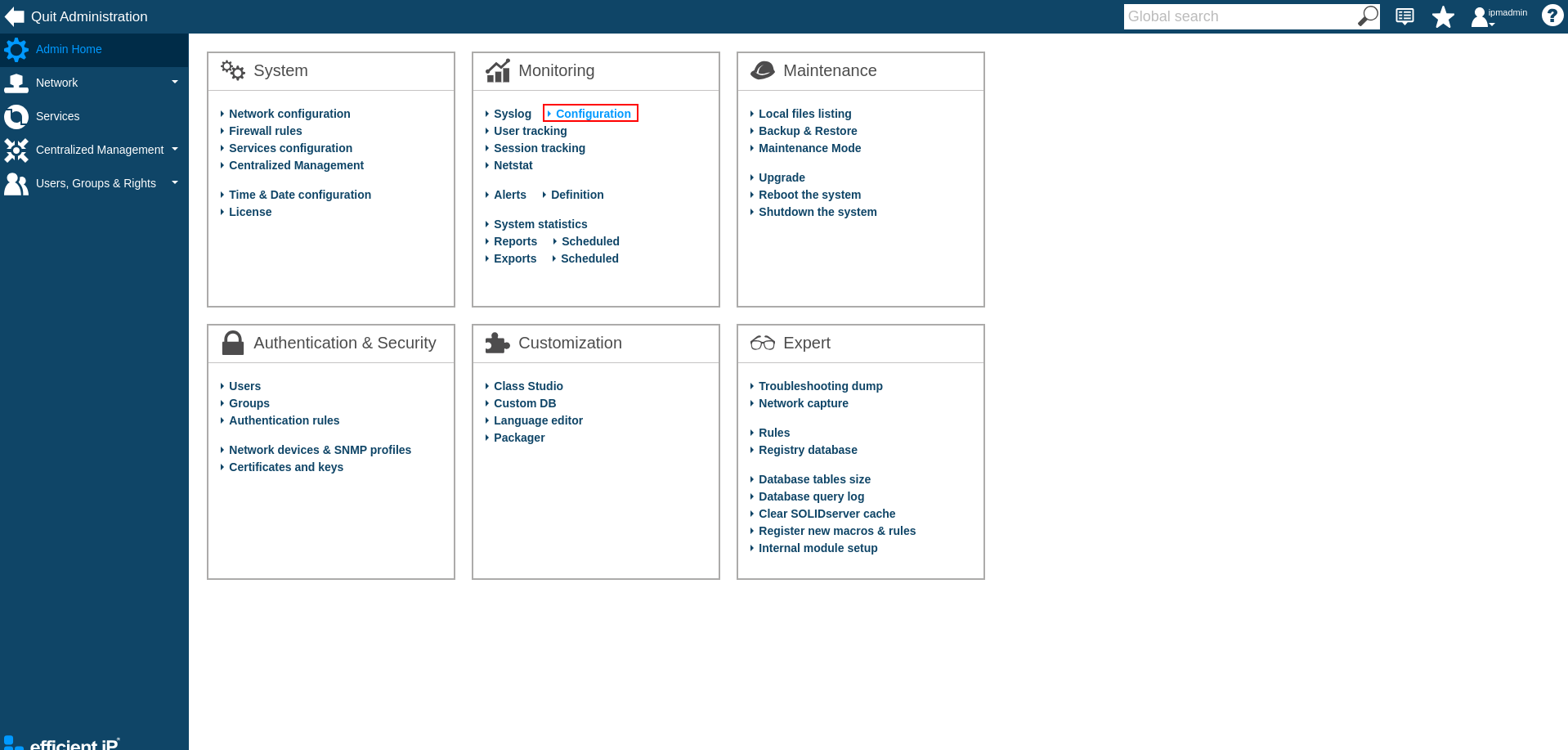
-
In the menu, click
+ Add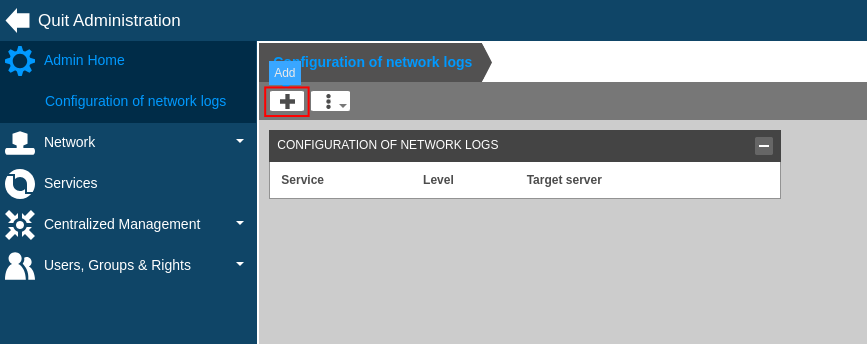
-
In the
Servicesdrop-dwon, select the following services:dns
-
In the
Target server, fill the ip address and the port of the log concentrator.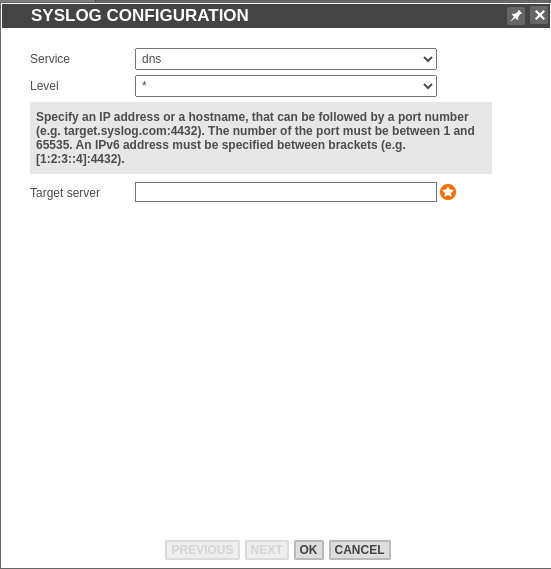
-
Click
OK
Create the intake
Go to the intake page and create a new intake from the format EfficientIP SOLIDServer DDI.
Forward logs to Sekoia.io
Please consult the Syslog Forwarding documentation to forward these logs to Sekoia.io.
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
connection refused resolving 'example.org/A/IN': 5.6.7.8#53
DHCPACK on 1.2.3.4 to 02:00:00:00:00:00 (example.com) via 1.0.0.1 [14400]
DHCPACK on 1.2.3.4 to 02:00:00:00:00:00 via 1.0.0.1 [691200]
DHCPACK on 1.2.3.4 to 02:00:00:00:00:00 via vmx1 [691200]
DHCPDISCOVER from 02:00:00:00:00:00 (example.com) via 1.0.0.1
DHCPDISCOVER from 02:00:00:00:00:00 via 1.0.0.1: load balance to peer failover-smart-dhcp.example.org
DHCPDISCOVER from 02:00:00:00:00:00 via 1.0.0.1
DHCPDISCOVER from 02:00:00:00:00:00 via 1.0.0.1: network 1.0.0.0/24: no free leases
DHCPDISCOVER from 02:00:00:00:00:00 via 1.0.0.1: unknown network segment
DHCPINFORM from 1.2.3.4 via 1.0.0.1
DHCPNACK on 1.2.3.4 to 02:00:00:00:00:00 via 1.0.0.1
DHCPNAK on 1.2.3.4 to 02:01:02:03:04:05 via vmx2
DHCPNAK on 1.2.3.4 to 02:01:02:03:04:05 via 5.6.7.8
DHCPOFFER on 1.2.3.4 to 02:00:00:00:00:00 via 1.0.0.1 [14400]
DHCPOFFER on 1.2.3.4 to 02:00:00:00:00:00 (example.com) via 1.0.0.1 [43200]
DHCPRELEASE of 1.2.3.4 from 02:00:00:00:00:00 (example.com) via vmx1 (found)
DHCPRELEASE of 1.2.3.4 from 02:00:00:00:00:00 via vmx1 (found)
DHCPREQUEST for 1.2.3.4 (192.0.2.1) from 02:00:00:00:00:00 via 1.0.0.1
DHCPREQUEST for 1.2.3.4 from 02:00:00:00:00:00 (example.com) via vmx1
DHCPREQUEST for 1.2.3.4 from 02:00:00:00:00:00 via vmx1
dns_diff_apply: host.example.org/A/IN: del not exact
DNS format error from 192.0.2.1#53 resolving example.com/AAAA for 1.2.3.4#55198: Name rlcdn.com (SOA) not subdomain of zone example.com -- invalid response
DNS format error from 1.2.3.4#53 resolving www.example.org/A for <unknown>: server sent FORMERR with echoed DNS COOKIE
FORMERR resolving 'api.example.com/AAAA/IN': 192.0.2.1#53
client 1.2.3.4#63572 (example.com): answer: example.com IN A (5.6.7.8) -> NOERROR 108 CNAME www.example.com.edgekey.net. 108 RRSIG CNAME 13 3 300 20240823013134 20240820003134 23300 example.com. ZXhhbXBsZTEyMy0xMjM= 32 CNAME example.akamaiedge.net. 20 A 9.10.11.12
client 10.242.101.27#46671 (example.com): answer: example.com IN TYPE65 (10.242.101.187) -> NOERROR
client 10.242.101.27#34229 (example.com): answer: example.com IN A (10.242.101.187) -> NOERROR 474 CNAME eip-community.hosted-by-discourse.com. 174 A 184.104.178.47
client @0x31cb8ed8daa0 1.2.3.4#47258 (example.com): view default: rpz QNAME PASSTHRU rewrite example.com/A/IN via example.com.00-whitelist
ARMING trigger on 192.0.2.1.f6:ec:1e:e3:7a:b1.ei6pt (action:QUARANTINE) (Suspicious Behavior)
DISARMING trigger on 192.0.2.1.f6:ec:1e:e3:7a:b1.ei6pt (action:QUARANTINE) (Suspicious Behavior)
List Matched 192.168.1.226#32622: query: example.com IN A (192.168.1.209) {DTP} [phishing,active30]
List Matched 192.168.1.226#46937: query: example.com IN A (192.168.1.209) {DTP,internal_clients}
client 10.242.101.27#46671: query: example.com IN TYPE65 (10.242.101.187)
client 10.242.101.27#34229: query: example.com IN A (10.242.101.187)
26914:client 1.2.3.4#52283 (example.com): answer: example.com IN TYPE65 (5.6.7.8) -> NOERROR 205 HTTPS 1 . alpn=h3,h2 ipv4hint=104.17.24.14,104.17.25.14 ipv6hint=2606:4700::6811:180e,2606:4700::6811:190e 205 RRSIG HTTPS 13
client 1.2.3.4#52023 (example.com): answer: example.com IN TYPE65 (5.6.7.8) -> NOERROR 2122 HTTPS 1 .
client 1.2.3.4#50426 (example.com): answer: example.com IN TYPE65 (1.2.3.4) -> NOERROR 238 HTTPS 1 . alpn=h3,h2 ipv4hint=5.6.7.8,9.10.11.12
client @0x7ee2b158 10.0.142.4#39897 (example.com): query: example.com IN A +E(0)K (10.0.142.2)
client @0x7ee2b158 1.2.3.4#50426: updating zone 'example.com/IN': deleting rrset at 'test.example.com' AAAA
client 1.2.3.4#63572 (example.com): answer: example.com IN A (1.2.3.4) -> NOERROR 300 A 1.2.3.4 300 A 1.2.3.4 300 RRSIG A 13 3 300 20240815085545 20240813065545 34505 test.com. xxxxxxxxxxxxx
client @0x7a4f3158 10.0.142.4#36506 (example.com): query: example.com IN A +E(0)CK (10.0.142.2)
client @0x81a97158 10.0.142.4#49968 (example.com): query: example.com IN A +E(0)DK (10.0.142.2)
client @0x7a532158 10.0.142.4#36995 (example.com): query: example.com IN A +E(0)TK (10.0.142.2)
client @0x7ee2b158 1.2.3.4#50426: received notify for zone 'example.org'
REFUSED unexpected RCODE resolving 'api.example.com/A/IN': 5.6.7.8#53
client 172.16.2.36#61806 (example.com): answer: example.com IN TYPE65 (10.211.1.201) -> NOERROR 300 CNAME example.comcdn.cloudflare.net. 300 HTTPS 1 . alpn=h2 ipv4hint=104.22.4.69,104.22.5.69,172.67.23.234 ipv6hint=2606:4700:10::6816:445,2606:4700:10::6816:545,2606:4700:10::ac43:17ea
SERVFAIL unexpected RCODE resolving 'www.example.org/A/IN': 5.6.7.8#53
client @0xc3709158 1.2.3.4#57618: view outside: received notify for zone 'rpz.example.org'
client @0x2606f9d32f20 1.2.3.4#26803 (2.23.172.in-addr.arpa): zone transfer 'example.com/IN' denied
host unreachable resolving 'example.org/A/IN': 5.6.7.8#53
loop detected resolving 'a.example.org/A'
client @0x2606f6b9f160 1.2.3.4#16385 (eu-west-3.example.org): query iterations limit reached
shut down hung fetch while resolving 'h.example.com/A'
client @0x00000b000 192.0.2.1#60000 (00000c222801.t-1733377733.i00000000.bee2333666c79f999f333001e77777c4-2000-txt.94d3f9f32f456537e1f982efdd8838888-9535-test.com): answer: example.com IN TXT +EDC (192.0.2.1) -> NOERROR 00c662201.t-173337
client @0x16a666666 192.0.2.1#611111 (example.com): answer: example.com IN A +EDC (192.0.2.1) -> NOERROR example.com. 248 AAAA test.com.test.net. test.com.test.net. 284 AAAA test-prod.test.com. test-prod.test.com. 14 AAAA test-prod
zone example.com/IN: refused notify from non-master: 1.2.3.4#49304
zone example.com/IN/outside: notify from 6.5.4.3#44152: serial 1720423233
client @0x8871827c 1.2.3.4#65213 (example.com): rpz QNAME Local-Data rewrite example.com/A/IN via example.com.fr
zone example.com/IN/outside: refused notify from non-master: 7507:2649:84be:353:95f9:eee1:65e9:44b4#47300
transfer of 'example.com/IN/outside' from 1.2.3.4#53: connected using 3.4.5.6#65242
transfer of 'example.com/IN/dmz' from 1.2.3.4#53: Transfer status: success
transfer of 'example.com/IN/dmz' from 1.2.3.4#53: Transfer completed: 1 messages, 8 records, 344 bytes, 0.026 secs (13230 bytes/sec) (serial 1720423198)
transfer of 'example.com/IN' from 1.2.3.4#53: Transfer completed: 1 messages, 5 records, 275 bytes, 0.001 secs (275000 bytes/sec) (serial 2024121937)
transfer of 'example.com/IN' from 1.2.3.4#53: Transfer completed: 1 messages, 10 records, 353 bytes, 0.026 secs (13576 bytes/sec) (serial 22910862)
client @0x8871827c 1.2.3.4#25484 (example.com): transfer of 'example.com/IN': IXFR ended: 2 messages, 422 records, 14227 bytes, 0.001 secs (14227000 bytes/sec) (serial 2024121946)
zone example.com/IN: sending notifies (serial 2024121928)
zone example.com/IN: Transfer started.
zone example.com/IN: transferred serial 2024121928
zone example.com/IN: notify from 1.2.3.4#49754: zone is up to date
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake EfficientIP SOLIDServer DDI. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x EfficientIP SOLIDServer DDI on ATT&CK Navigator
Bazar Loader DGA (Domain Generation Algorithm)
Detects Bazar Loader domains based on the Bazar Loader DGA
- Effort: elementary
Cobalt Strike DNS Beaconing
Detects suspicious DNS queries known from Cobalt Strike beacons. The threshold is more than 50 suspicious DNS requests to avoid false positives.
- Effort: advanced
Correlation Potential DNS Tunnel
Detects domain name which is longer than 62 characters and requested at least 50 times in a 10 minutes range time. Long domain names are distinctive of DNS tunnels.
- Effort: advanced
Cryptomining
Detection of domain names potentially related to cryptomining activities.
- Effort: master
Dynamic DNS Contacted
Detect communication with dynamic dns domain. This kind of domain is often used by attackers. This rule can trigger false positive in non-controlled environment because dynamic dns is not always malicious.
- Effort: master
EfficientIP SOLIDServer Suspicious Behavior
Detects when EfficientIP SOLIDServer forwards a suspicious behavior related to an IP.
- Effort: master
EvilProxy Phishing Domain
Detects subdomains potentially generated by the EvilProxy adversary-in-the-middle phishing platform. Inspect the other subdomains of the domain to identify the landing page, and determine if the user submitted credentials. This rule has a small percentage of false positives on legitimate domains.
- Effort: intermediate
Exfiltration Domain
Detects traffic toward a domain flagged as a possible exfiltration vector.
- Effort: master
Internet Scanner
Detects known scanner IP addresses. Alert is only raised when the scan hits an opened port, on TCP or UDP. This could be a very noisy rule, so be careful to check your detection perimeter before activation.
- Effort: master
Internet Scanner Target
Detects known scanner IP addresses. Alert is only raised when the scan hits an opened port, on TCP or UDP and group by target address. This could be a very noisy rule, so be careful to check your detection perimeter before activation.
- Effort: master
Potential DNS Tunnel
Detects domain name which is longer than 62 characters. Long domain names are distinctive of DNS tunnels.
- Effort: advanced
Remote Access Tool Domain
Detects traffic toward a domain flagged as a Remote Administration Tool (RAT).
- Effort: master
Remote Monitoring and Management Software - AnyDesk
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool AnyDesk.
- Effort: master
Remote Monitoring and Management Software - Atera
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool Atera.
- Effort: master
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
Sekoia.io EICAR Detection
Detects observables in Sekoia.io CTI tagged as EICAR, which are fake samples meant to test detection.
- Effort: master
Sliver DNS Beaconing
Detects suspicious DNS queries known from Sliver beaconing
- Effort: intermediate
Suspicious TOR Gateway
Detects suspicious TOR gateways. Gateways are often used by the victim to pay and decrypt the encrypted files without installing TOR. Tor intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: advanced
TOR Usage Generic Rule
Detects TOR usage globally, whether the IP is a destination or source. TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
Telegram Bot API Request
Detects suspicious DNS queries to api.telegram.org used by Telegram Bots of any kind
- Effort: advanced
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
DNS records |
EfficientIP SOLIDserver provides detailed logs on handled DNS queries |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | `` |
| Category | network |
| Type | info |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "connection refused resolving 'example.org/A/IN': 5.6.7.8#53",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"outcome": "failure",
"reason": "connection refused",
"type": [
"info"
]
},
"dns": {
"question": {
"class": "IN",
"name": "example.org",
"registered_domain": "example.org",
"top_level_domain": "org",
"type": "A"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.org"
],
"ip": [
"5.6.7.8"
]
},
"server": {
"ip": "5.6.7.8",
"port": 53
}
}
{
"message": "DHCPACK on 1.2.3.4 to 02:00:00:00:00:00 (example.com) via 1.0.0.1 [14400]",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"ip": "1.0.0.1"
},
"operation": "ack"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "example.com",
"domain": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com"
}
}
{
"message": "DHCPACK on 1.2.3.4 to 02:00:00:00:00:00 via 1.0.0.1 [691200]",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"ip": "1.0.0.1"
},
"operation": "ack"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "DHCPACK on 1.2.3.4 to 02:00:00:00:00:00 via vmx1 [691200]",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"name": "vmx1"
},
"operation": "ack"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "DHCPDISCOVER from 02:00:00:00:00:00 (example.com) via 1.0.0.1",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"ip": "1.0.0.1"
},
"operation": "discover"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
]
},
"source": {
"address": "example.com",
"domain": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com"
}
}
{
"message": "DHCPDISCOVER from 02:00:00:00:00:00 via 1.0.0.1: load balance to peer failover-smart-dhcp.example.org",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"ip": "1.0.0.1"
},
"message": "load balance to peer failover-smart-dhcp.example.org",
"operation": "discover"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
}
}
{
"message": "DHCPDISCOVER from 02:00:00:00:00:00 via 1.0.0.1",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"ip": "1.0.0.1"
},
"operation": "discover"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
}
}
{
"message": "DHCPDISCOVER from 02:00:00:00:00:00 via 1.0.0.1: network 1.0.0.0/24: no free leases",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"ip": "1.0.0.1"
},
"message": "network 1.0.0.0/24: no free leases",
"operation": "discover"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
}
}
{
"message": "DHCPDISCOVER from 02:00:00:00:00:00 via 1.0.0.1: unknown network segment",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"ip": "1.0.0.1"
},
"message": "unknown network segment",
"operation": "discover"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
}
}
{
"message": "DHCPINFORM from 1.2.3.4 via 1.0.0.1",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"ip": "1.0.0.1"
},
"operation": "inform"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "DHCPNACK on 1.2.3.4 to 02:00:00:00:00:00 via 1.0.0.1",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"ip": "1.0.0.1"
},
"operation": "nack"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "DHCPNAK on 1.2.3.4 to 02:01:02:03:04:05 via vmx2",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:01:02:03:04:05"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"name": "vmx2"
},
"operation": "nak"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "DHCPNAK on 1.2.3.4 to 02:01:02:03:04:05 via 5.6.7.8",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:01:02:03:04:05"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"ip": "5.6.7.8"
},
"operation": "nak"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "DHCPOFFER on 1.2.3.4 to 02:00:00:00:00:00 via 1.0.0.1 [14400]",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"ip": "1.0.0.1"
},
"operation": "offer"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "DHCPOFFER on 1.2.3.4 to 02:00:00:00:00:00 (example.com) via 1.0.0.1 [43200]",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"ip": "1.0.0.1"
},
"operation": "offer"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "example.com",
"domain": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com"
}
}
{
"message": "DHCPRELEASE of 1.2.3.4 from 02:00:00:00:00:00 (example.com) via vmx1 (found)",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"name": "vmx1"
},
"operation": "release",
"release_state": "found"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "example.com",
"domain": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com"
}
}
{
"message": "DHCPRELEASE of 1.2.3.4 from 02:00:00:00:00:00 via vmx1 (found)",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"name": "vmx1"
},
"operation": "release",
"release_state": "found"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "DHCPREQUEST for 1.2.3.4 (192.0.2.1) from 02:00:00:00:00:00 via 1.0.0.1",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"ip": "1.0.0.1"
},
"operation": "request"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4",
"192.0.2.1"
]
},
"server": {
"ip": "192.0.2.1"
}
}
{
"message": "DHCPREQUEST for 1.2.3.4 from 02:00:00:00:00:00 (example.com) via vmx1",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"name": "vmx1"
},
"operation": "request"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "example.com",
"domain": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com"
}
}
{
"message": "DHCPREQUEST for 1.2.3.4 from 02:00:00:00:00:00 via vmx1",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00"
},
"dns": {
"type": "query"
},
"efficientip": {
"dhcp": {
"interface": {
"name": "vmx1"
},
"operation": "request"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "dns_diff_apply: host.example.org/A/IN: del not exact",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "host.example.org",
"query": {
"class": "IN"
},
"view": "A"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
}
}
{
"message": "DNS format error from 192.0.2.1#53 resolving example.com/AAAA for 1.2.3.4#55198: Name rlcdn.com (SOA) not subdomain of zone example.com -- invalid response",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"outcome": "failure",
"reason": "Name rlcdn.com (SOA) not subdomain of zone example.com -- invalid response",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 55198
},
"dns": {
"question": {
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "AAAA"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4",
"192.0.2.1"
]
},
"server": {
"ip": "192.0.2.1",
"port": 53
}
}
{
"message": "DNS format error from 1.2.3.4#53 resolving www.example.org/A for <unknown>: server sent FORMERR with echoed DNS COOKIE",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "server sent FORMERR with echoed DNS COOKIE",
"type": [
"info"
]
},
"dns": {
"question": {
"name": "www.example.org",
"registered_domain": "example.org",
"subdomain": "www",
"top_level_domain": "org",
"type": "A"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"www.example.org"
],
"ip": [
"1.2.3.4"
]
},
"server": {
"ip": "1.2.3.4",
"port": 53
}
}
{
"message": "FORMERR resolving 'api.example.com/AAAA/IN': 192.0.2.1#53",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"outcome": "failure",
"type": [
"info"
]
},
"dns": {
"question": {
"class": "IN",
"name": "api.example.com",
"registered_domain": "example.com",
"subdomain": "api",
"top_level_domain": "com",
"type": "AAAA"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"api.example.com"
],
"ip": [
"192.0.2.1"
]
},
"server": {
"ip": "192.0.2.1",
"port": 53
}
}
{
"message": "client 1.2.3.4#63572 (example.com): answer: example.com IN A (5.6.7.8) -> NOERROR 108 CNAME www.example.com.edgekey.net. 108 RRSIG CNAME 13 3 300 20240823013134 20240820003134 23300 example.com. ZXhhbXBsZTEyMy0xMjM= 32 CNAME example.akamaiedge.net. 20 A 9.10.11.12",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 63572
},
"dns": {
"answers": [
{
"data": "www.example.com.edgekey.net.",
"ttl": 108,
"type": "CNAME"
},
{
"data": "example.akamaiedge.net.",
"ttl": 32,
"type": "CNAME"
},
{
"data": "9.10.11.12",
"ttl": 20,
"type": "A"
},
{
"data": "HTTPS",
"ttl": 108,
"type": "RSSIG"
}
],
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "A"
},
"response_code": "NOERROR",
"type": "answer"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"server": {
"ip": "5.6.7.8"
}
}
{
"message": "client 10.242.101.27#46671 (example.com): answer: example.com IN TYPE65 (10.242.101.187) -> NOERROR",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "10.242.101.27",
"ip": "10.242.101.27",
"port": 46671
},
"dns": {
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "TYPE65"
},
"response_code": "NOERROR",
"type": "answer"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"10.242.101.187",
"10.242.101.27"
]
},
"server": {
"ip": "10.242.101.187"
}
}
{
"message": "client 10.242.101.27#34229 (example.com): answer: example.com IN A (10.242.101.187) -> NOERROR 474 CNAME eip-community.hosted-by-discourse.com. 174 A 184.104.178.47",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "10.242.101.27",
"ip": "10.242.101.27",
"port": 34229
},
"dns": {
"answers": [
{
"data": "eip-community.hosted-by-discourse.com.",
"ttl": 474,
"type": "CNAME"
},
{
"data": "184.104.178.47",
"ttl": 174,
"type": "A"
}
],
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "A"
},
"response_code": "NOERROR",
"type": "answer"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"10.242.101.187",
"10.242.101.27"
]
},
"server": {
"ip": "10.242.101.187"
}
}
{
"message": "client @0x31cb8ed8daa0 1.2.3.4#47258 (example.com): view default: rpz QNAME PASSTHRU rewrite example.com/A/IN via example.com.00-whitelist",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 47258
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
},
"source": {
"name": "example.com.00-whitelist"
},
"view": "A"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "ARMING trigger on 192.0.2.1.f6:ec:1e:e3:7a:b1.ei6pt (action:QUARANTINE) (Suspicious Behavior)",
"event": {
"action": "quarantine",
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"efficientip": {
"guardian_action": "arming",
"guardian_trigger_name": "Suspicious Behavior"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"192.0.2.1"
]
}
}
{
"message": "DISARMING trigger on 192.0.2.1.f6:ec:1e:e3:7a:b1.ei6pt (action:QUARANTINE) (Suspicious Behavior)",
"event": {
"action": "quarantine",
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"efficientip": {
"guardian_action": "disarming",
"guardian_trigger_name": "Suspicious Behavior"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"192.0.2.1"
]
}
}
{
"message": "List Matched 192.168.1.226#32622: query: example.com IN A (192.168.1.209) {DTP} [phishing,active30]",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "192.168.1.226",
"ip": "192.168.1.226",
"port": 32622
},
"dns": {
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "A"
},
"type": "query"
},
"efficientip": {
"list_names": [
"DTP"
],
"tag_names": [
"active30",
"phishing"
]
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"192.168.1.209",
"192.168.1.226"
]
},
"server": {
"ip": "192.168.1.209"
}
}
{
"message": "List Matched 192.168.1.226#46937: query: example.com IN A (192.168.1.209) {DTP,internal_clients}",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "192.168.1.226",
"ip": "192.168.1.226",
"port": 46937
},
"dns": {
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "A"
},
"type": "query"
},
"efficientip": {
"list_names": [
"DTP",
"internal_clients"
]
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"192.168.1.209",
"192.168.1.226"
]
},
"server": {
"ip": "192.168.1.209"
}
}
{
"message": "client 10.242.101.27#46671: query: example.com IN TYPE65 (10.242.101.187)",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "10.242.101.27",
"ip": "10.242.101.27",
"port": 46671
},
"dns": {
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "TYPE65"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"10.242.101.187",
"10.242.101.27"
]
},
"server": {
"ip": "10.242.101.187"
}
}
{
"message": "client 10.242.101.27#34229: query: example.com IN A (10.242.101.187)",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "10.242.101.27",
"ip": "10.242.101.27",
"port": 34229
},
"dns": {
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "A"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"10.242.101.187",
"10.242.101.27"
]
},
"server": {
"ip": "10.242.101.187"
}
}
{
"message": "26914:client 1.2.3.4#52283 (example.com): answer: example.com IN TYPE65 (5.6.7.8) -> NOERROR 205 HTTPS 1 . alpn=h3,h2 ipv4hint=104.17.24.14,104.17.25.14 ipv6hint=2606:4700::6811:180e,2606:4700::6811:190e 205 RRSIG HTTPS 13",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 52283
},
"dns": {
"answers": [
{
"data": "alpn=h3,h2 ipv4hint=104.17.24.14,104.17.25.14 ipv6hint=2606:4700::6811:180e,2606:4700::6811:190e",
"ttl": 205,
"type": "HTTPS"
},
{
"data": "HTTPS",
"ttl": 205,
"type": "RSSIG"
}
],
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "TYPE65"
},
"response_code": "NOERROR",
"type": "answer"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"server": {
"ip": "5.6.7.8"
}
}
{
"message": "client 1.2.3.4#52023 (example.com): answer: example.com IN TYPE65 (5.6.7.8) -> NOERROR 2122 HTTPS 1 .",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 52023
},
"dns": {
"answers": [
{
"data": ".",
"ttl": 2122,
"type": "HTTPS"
}
],
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "TYPE65"
},
"response_code": "NOERROR",
"type": "answer"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4",
"5.6.7.8"
]
},
"server": {
"ip": "5.6.7.8"
}
}
{
"message": "client 1.2.3.4#50426 (example.com): answer: example.com IN TYPE65 (1.2.3.4) -> NOERROR 238 HTTPS 1 . alpn=h3,h2 ipv4hint=5.6.7.8,9.10.11.12",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 50426
},
"dns": {
"answers": [
{
"data": "alpn=h3,h2 ipv4hint=5.6.7.8,9.10.11.12",
"ttl": 238,
"type": "HTTPS"
}
],
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "TYPE65"
},
"response_code": "NOERROR",
"type": "answer"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4"
]
},
"server": {
"ip": "1.2.3.4"
}
}
{
"message": "client @0x7ee2b158 10.0.142.4#39897 (example.com): query: example.com IN A +E(0)K (10.0.142.2)",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "10.0.142.4",
"ip": "10.0.142.4",
"port": 39897
},
"dns": {
"header_flags": [
"RD"
],
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "A"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"10.0.142.2",
"10.0.142.4"
]
},
"server": {
"ip": "10.0.142.2"
}
}
{
"message": "client @0x7ee2b158 1.2.3.4#50426: updating zone 'example.com/IN': deleting rrset at 'test.example.com' AAAA",
"event": {
"action": "deleting",
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "rrset at 'test.example.com' AAAA",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 50426
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
}
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "client 1.2.3.4#63572 (example.com): answer: example.com IN A (1.2.3.4) -> NOERROR 300 A 1.2.3.4 300 A 1.2.3.4 300 RRSIG A 13 3 300 20240815085545 20240813065545 34505 test.com. xxxxxxxxxxxxx",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 63572
},
"dns": {
"answers": [
{
"data": "1.2.3.4",
"ttl": 300,
"type": "A"
},
{
"data": "1.2.3.4",
"ttl": 300,
"type": "A"
},
{
"data": "HTTPS",
"ttl": 300,
"type": "RSSIG"
}
],
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "A"
},
"response_code": "NOERROR",
"type": "answer"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4"
]
},
"server": {
"ip": "1.2.3.4"
}
}
{
"message": "client @0x7a4f3158 10.0.142.4#36506 (example.com): query: example.com IN A +E(0)CK (10.0.142.2)",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "10.0.142.4",
"ip": "10.0.142.4",
"port": 36506
},
"dns": {
"header_flags": [
"CD",
"RD"
],
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "A"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"10.0.142.2",
"10.0.142.4"
]
},
"server": {
"ip": "10.0.142.2"
}
}
{
"message": "client @0x81a97158 10.0.142.4#49968 (example.com): query: example.com IN A +E(0)DK (10.0.142.2)",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "10.0.142.4",
"ip": "10.0.142.4",
"port": 49968
},
"dns": {
"header_flags": [
"RD"
],
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "A"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"10.0.142.2",
"10.0.142.4"
]
},
"server": {
"ip": "10.0.142.2"
}
}
{
"message": "client @0x7a532158 10.0.142.4#36995 (example.com): query: example.com IN A +E(0)TK (10.0.142.2)",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "10.0.142.4",
"ip": "10.0.142.4",
"port": 36995
},
"dns": {
"header_flags": [
"RD"
],
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "A"
},
"type": "query"
},
"network": {
"transport": "tcp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"10.0.142.2",
"10.0.142.4"
]
},
"server": {
"ip": "10.0.142.2"
}
}
{
"message": "client @0x7ee2b158 1.2.3.4#50426: received notify for zone 'example.org'",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 50426
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.org"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "REFUSED unexpected RCODE resolving 'api.example.com/A/IN': 5.6.7.8#53",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"outcome": "failure",
"reason": "unexpected RCODE",
"type": [
"info"
]
},
"dns": {
"question": {
"class": "IN",
"name": "api.example.com",
"registered_domain": "example.com",
"subdomain": "api",
"top_level_domain": "com",
"type": "A"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"api.example.com"
],
"ip": [
"5.6.7.8"
]
},
"server": {
"ip": "5.6.7.8",
"port": 53
}
}
{
"message": "client 172.16.2.36#61806 (example.com): answer: example.com IN TYPE65 (10.211.1.201) -> NOERROR 300 CNAME example.comcdn.cloudflare.net. 300 HTTPS 1 . alpn=h2 ipv4hint=104.22.4.69,104.22.5.69,172.67.23.234 ipv6hint=2606:4700:10::6816:445,2606:4700:10::6816:545,2606:4700:10::ac43:17ea",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "172.16.2.36",
"ip": "172.16.2.36",
"port": 61806
},
"dns": {
"answers": [
{
"data": "example.comcdn.cloudflare.net.",
"ttl": 300,
"type": "CNAME"
},
{
"data": "alpn=h2 ipv4hint=104.22.4.69,104.22.5.69,172.67.23.234 ipv6hint=2606:4700:10::6816:445,2606:4700:10::6816:545,2606:4700:10::ac43:17ea",
"ttl": 300,
"type": "HTTPS"
}
],
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "TYPE65"
},
"response_code": "NOERROR",
"type": "answer"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"10.211.1.201",
"172.16.2.36"
]
},
"server": {
"ip": "10.211.1.201"
}
}
{
"message": "SERVFAIL unexpected RCODE resolving 'www.example.org/A/IN': 5.6.7.8#53",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"outcome": "failure",
"reason": "unexpected RCODE",
"type": [
"info"
]
},
"dns": {
"question": {
"class": "IN",
"name": "www.example.org",
"registered_domain": "example.org",
"subdomain": "www",
"top_level_domain": "org",
"type": "A"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"www.example.org"
],
"ip": [
"5.6.7.8"
]
},
"server": {
"ip": "5.6.7.8",
"port": 53
}
}
{
"message": "client @0xc3709158 1.2.3.4#57618: view outside: received notify for zone 'rpz.example.org'",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 57618
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "rpz.example.org"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "client @0x2606f9d32f20 1.2.3.4#26803 (2.23.172.in-addr.arpa): zone transfer 'example.com/IN' denied",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 26803
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
}
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "host unreachable resolving 'example.org/A/IN': 5.6.7.8#53",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"outcome": "failure",
"reason": "host unreachable",
"type": [
"info"
]
},
"dns": {
"question": {
"class": "IN",
"name": "example.org",
"registered_domain": "example.org",
"top_level_domain": "org",
"type": "A"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.org"
],
"ip": [
"5.6.7.8"
]
},
"server": {
"ip": "5.6.7.8",
"port": 53
}
}
{
"message": "loop detected resolving 'a.example.org/A'",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"outcome": "failure",
"reason": "loop detected",
"type": [
"info"
]
},
"dns": {
"question": {
"name": "a.example.org",
"registered_domain": "example.org",
"subdomain": "a",
"top_level_domain": "org",
"type": "A"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"a.example.org"
]
}
}
{
"message": "client @0x2606f6b9f160 1.2.3.4#16385 (eu-west-3.example.org): query iterations limit reached",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "query iterations limit reached",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 16385
},
"dns": {
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "shut down hung fetch while resolving 'h.example.com/A'",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"outcome": "failure",
"reason": "shut down hung fetch while",
"type": [
"info"
]
},
"dns": {
"question": {
"name": "h.example.com",
"registered_domain": "example.com",
"subdomain": "h",
"top_level_domain": "com",
"type": "A"
},
"type": "query"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"h.example.com"
]
}
}
{
"message": "client @0x00000b000 192.0.2.1#60000 (00000c222801.t-1733377733.i00000000.bee2333666c79f999f333001e77777c4-2000-txt.94d3f9f32f456537e1f982efdd8838888-9535-test.com): answer: example.com IN TXT +EDC (192.0.2.1) -> NOERROR 00c662201.t-173337",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"port": 60000
},
"dns": {
"answers": [
{
"data": "00c662201.t-173337"
}
],
"header_flags": [
"CD",
"RD"
],
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "TXT"
},
"response_code": "NOERROR",
"type": "answer"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"192.0.2.1"
]
},
"server": {
"ip": "192.0.2.1"
}
}
{
"message": "client @0x16a666666 192.0.2.1#611111 (example.com): answer: example.com IN A +EDC (192.0.2.1) -> NOERROR example.com. 248 AAAA test.com.test.net. test.com.test.net. 284 AAAA test-prod.test.com. test-prod.test.com. 14 AAAA test-prod",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"port": 611111
},
"dns": {
"answers": [
{
"data": "test.com.test.net."
},
{
"data": "test-prod.test.com."
},
{
"data": "test-prod"
},
{
"data": "example.com.",
"ttl": 248,
"type": "AAAA"
},
{
"data": "test.com.test.net.",
"ttl": 284,
"type": "AAAA"
},
{
"data": "test-prod.test.com.",
"ttl": 14,
"type": "AAAA"
}
],
"header_flags": [
"CD",
"RD"
],
"question": {
"class": "IN",
"name": "example.com",
"registered_domain": "example.com",
"top_level_domain": "com",
"type": "A"
},
"response_code": "NOERROR",
"type": "answer"
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"192.0.2.1"
]
},
"server": {
"ip": "192.0.2.1"
}
}
{
"message": "zone example.com/IN: refused notify from non-master: 1.2.3.4#49304",
"event": {
"action": "refused notify",
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "1.2.3.4#49304",
"type": [
"info"
]
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
},
"source": {
"name": "non-master"
}
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
}
}
{
"message": "zone example.com/IN/outside: notify from 6.5.4.3#44152: serial 1720423233",
"event": {
"action": "notify",
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "serial 1720423233",
"type": [
"info"
]
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
},
"view": "outside"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"6.5.4.3"
]
},
"source": {
"address": "6.5.4.3",
"ip": "6.5.4.3",
"port": 44152
}
}
{
"message": "client @0x8871827c 1.2.3.4#65213 (example.com): rpz QNAME Local-Data rewrite example.com/A/IN via example.com.fr",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 65213
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
},
"source": {
"name": "example.com.fr"
},
"view": "A"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "zone example.com/IN/outside: refused notify from non-master: 7507:2649:84be:353:95f9:eee1:65e9:44b4#47300",
"event": {
"action": "refused notify",
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "7507:2649:84be:353:95f9:eee1:65e9:44b4#47300",
"type": [
"info"
]
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
},
"source": {
"name": "non-master"
},
"view": "outside"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
}
}
{
"message": "transfer of 'example.com/IN/outside' from 1.2.3.4#53: connected using 3.4.5.6#65242",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "connected using 3.4.5.6#65242",
"type": [
"info"
]
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
},
"view": "outside"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 53
}
}
{
"message": "transfer of 'example.com/IN/dmz' from 1.2.3.4#53: Transfer status: success",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "Transfer status: success",
"type": [
"info"
]
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
},
"view": "dmz"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 53
}
}
{
"message": "transfer of 'example.com/IN/dmz' from 1.2.3.4#53: Transfer completed: 1 messages, 8 records, 344 bytes, 0.026 secs (13230 bytes/sec) (serial 1720423198)",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "Transfer completed: 1 messages, 8 records, 344 bytes, 0.026 secs (13230 bytes/sec) (serial 1720423198)",
"type": [
"info"
]
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
},
"view": "dmz"
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 53
}
}
{
"message": "transfer of 'example.com/IN' from 1.2.3.4#53: Transfer completed: 1 messages, 5 records, 275 bytes, 0.001 secs (275000 bytes/sec) (serial 2024121937)",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "Transfer completed: 1 messages, 5 records, 275 bytes, 0.001 secs (275000 bytes/sec) (serial 2024121937)",
"type": [
"info"
]
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
}
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 53
}
}
{
"message": "transfer of 'example.com/IN' from 1.2.3.4#53: Transfer completed: 1 messages, 10 records, 353 bytes, 0.026 secs (13576 bytes/sec) (serial 22910862)",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "Transfer completed: 1 messages, 10 records, 353 bytes, 0.026 secs (13576 bytes/sec) (serial 22910862)",
"type": [
"info"
]
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
}
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 53
}
}
{
"message": "client @0x8871827c 1.2.3.4#25484 (example.com): transfer of 'example.com/IN': IXFR ended: 2 messages, 422 records, 14227 bytes, 0.001 secs (14227000 bytes/sec) (serial 2024121946)",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "IXFR ended: 2 messages, 422 records, 14227 bytes, 0.001 secs (14227000 bytes/sec) (serial 2024121946)",
"type": [
"info"
]
},
"client": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 25484
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
}
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
}
}
{
"message": "zone example.com/IN: sending notifies (serial 2024121928)",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "sending notifies (serial 2024121928)",
"type": [
"info"
]
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
}
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
}
}
{
"message": "zone example.com/IN: Transfer started.",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "Transfer started.",
"type": [
"info"
]
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
}
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
}
}
{
"message": "zone example.com/IN: transferred serial 2024121928",
"event": {
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "transferred serial 2024121928",
"type": [
"info"
]
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
}
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
}
}
{
"message": "zone example.com/IN: notify from 1.2.3.4#49754: zone is up to date",
"event": {
"action": "notify",
"category": [
"network"
],
"dataset": "solidserver-ddi",
"reason": "zone is up to date",
"type": [
"info"
]
},
"dns": {
"type": "query"
},
"efficientip": {
"rpz": {
"domain": "example.com",
"query": {
"class": "IN"
}
}
},
"network": {
"transport": "udp"
},
"observer": {
"vendor": "EfficientIp"
},
"related": {
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 49754
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
client.ip |
ip |
IP address of the client. |
client.mac |
keyword |
MAC address of the client. |
client.port |
long |
Port of the client. |
dns.answers |
object |
Array of DNS answers. |
dns.header_flags |
keyword |
Array of DNS header flags. |
dns.question.class |
keyword |
The class of records being queried. |
dns.question.name |
keyword |
The name being queried. |
dns.question.type |
keyword |
The type of record being queried. |
dns.response_code |
keyword |
The DNS response code. |
dns.type |
keyword |
The type of DNS event captured, query or answer. |
efficientip.dhcp.interface.ip |
keyword |
The IP address of the interface that received the query |
efficientip.dhcp.interface.name |
keyword |
The name of the interface that received the query |
efficientip.dhcp.message |
keyword |
The DHCP message |
efficientip.dhcp.operation |
keyword |
The operation performed on the DHCP lease |
efficientip.dhcp.release_state |
keyword |
The state of the DHCP release |
efficientip.guardian_action |
keyword |
EfficientIP Guardian action |
efficientip.guardian_trigger_name |
keyword |
Name of the EfficientIP Guardian trigger |
efficientip.list_names |
array |
Names of the retrictions lists that matched the query |
efficientip.rpz.domain |
keyword |
The domain of the rpz zone |
efficientip.rpz.query.class |
keyword |
The query_class of the rpz request |
efficientip.rpz.source.name |
keyword |
The name of the source of the rpz request |
efficientip.rpz.view |
keyword |
The view of the rpz request |
efficientip.tag_names |
array |
List of tags that matched the query |
event.action |
keyword |
The action captured by the event. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.dataset |
keyword |
Name of the dataset. |
event.outcome |
keyword |
The outcome of the event. The lowest level categorization field in the hierarchy. |
event.reason |
keyword |
Reason why this event happened, according to the source |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
network.transport |
keyword |
Protocol Name corresponding to the field iana_number. |
observer.vendor |
keyword |
Vendor name of the observer. |
server.ip |
ip |
IP address of the server. |
server.port |
long |
Port of the server. |
source.domain |
keyword |
The domain name of the source. |
source.ip |
ip |
IP address of the source. |
source.port |
long |
Port of the source. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.