Tenable.io
Overview
Tenable.io is a cloud-based exposure and vulnerability management platform that provides continuous visibility across on‑prem, cloud, container, and web application assets, combining automated discovery and scans with risk-based prioritization to help teams find, prioritize, and remediate issues faster—backed by granular admin controls, compliance reporting, and APIs/integrations that fit seamlessly into existing IT and SecOps workflows.
- Vendor: Tenable
- Product: Tenable Vulnerability Management
- Supported environment: SaaS
Configure
How to create an API token
To connect Tenable.io to Sekoia.io, you need to create an API key pair (Access Key and Secret Key) in your Tenable.io account. Follow these steps:
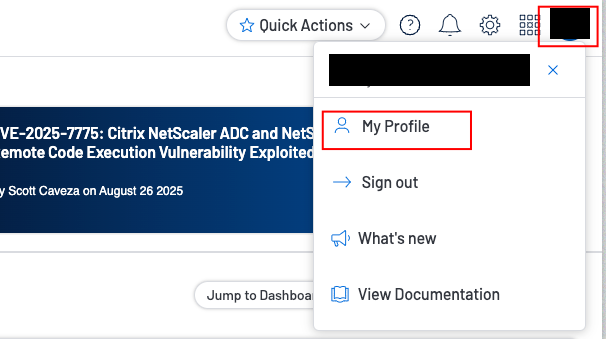
-
Access the My Account page.
-
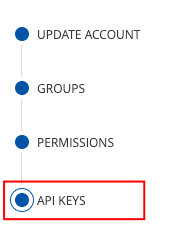
Click the API Keys tab.
-
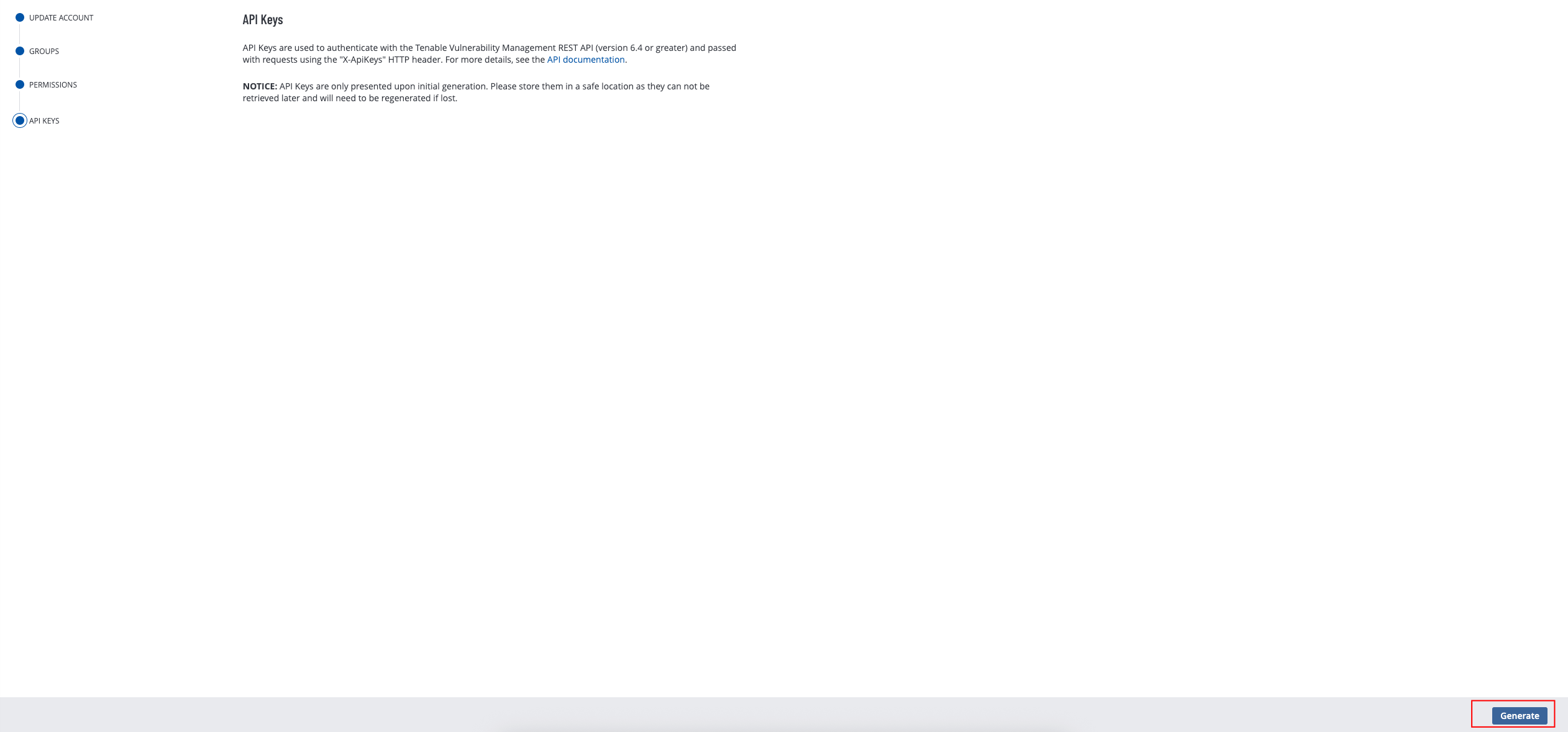
Click Generate to generate credentials.
-
Copy the new access and secret keys to a safe location and start using them in Sekoia.io.
Warning
- Any existing API keys are replaced when you click the Generate button. You must update the applications where the previous API keys were used.
- The secret key is only shown when you create it. If you lose it, you must generate a new key pair.
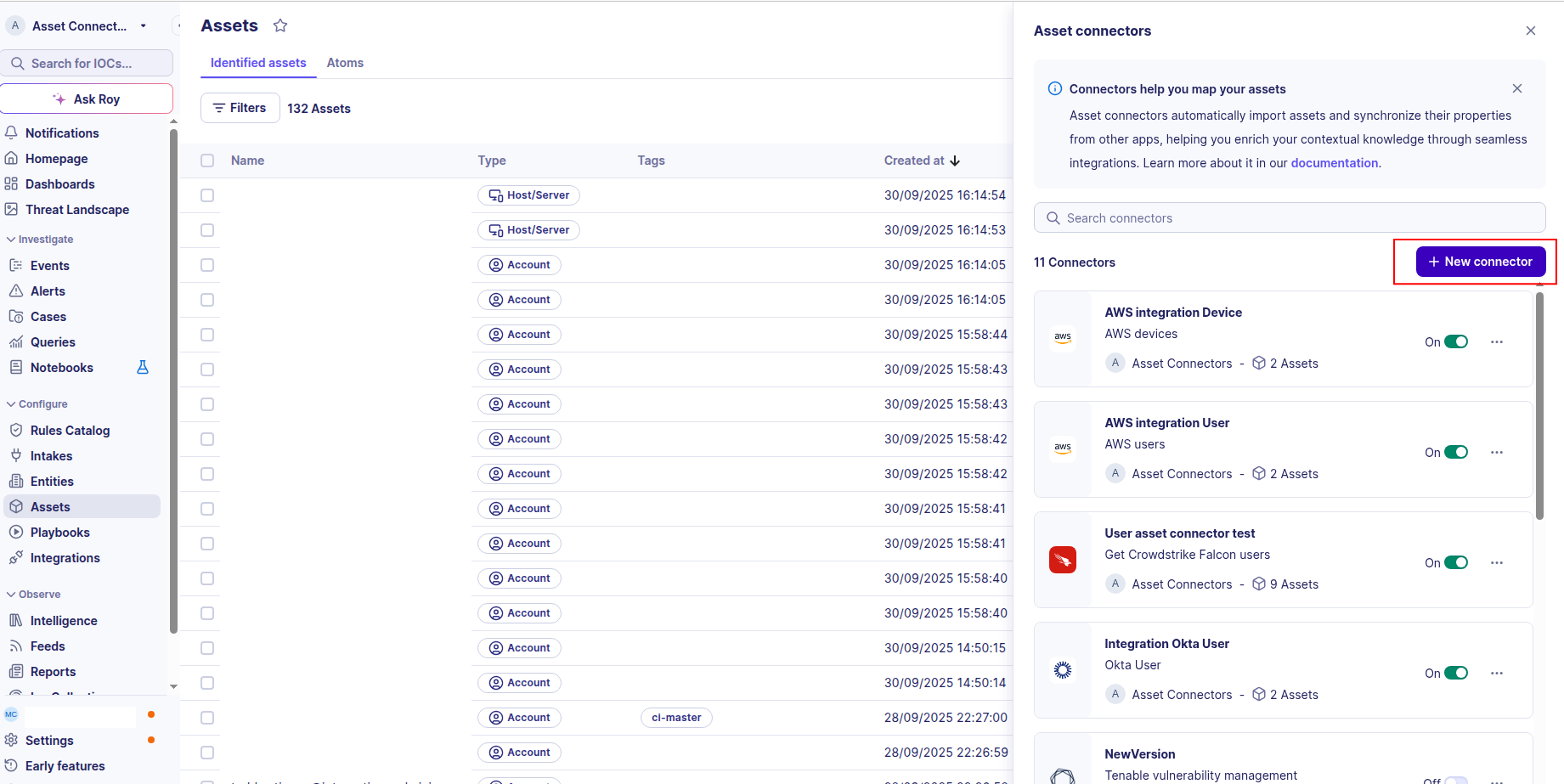
Create your asset
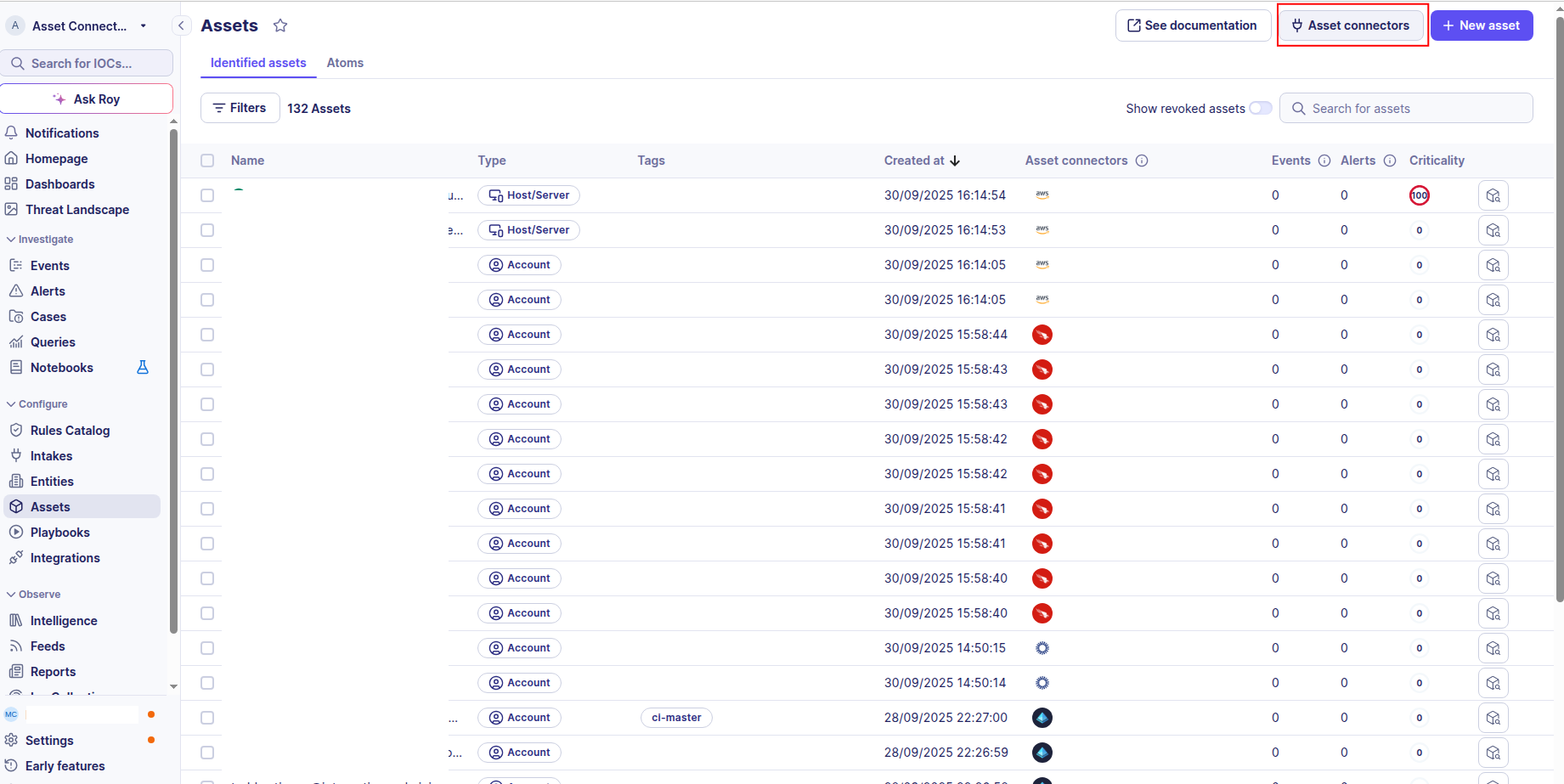
To start getting your Tenable.io assets into Sekoia.io, you need to create an asset connector on the Assets page. To do so, follow these steps:
-
Click the Asset connectors button to create a new connector.
-
Click the + New connector button.
-
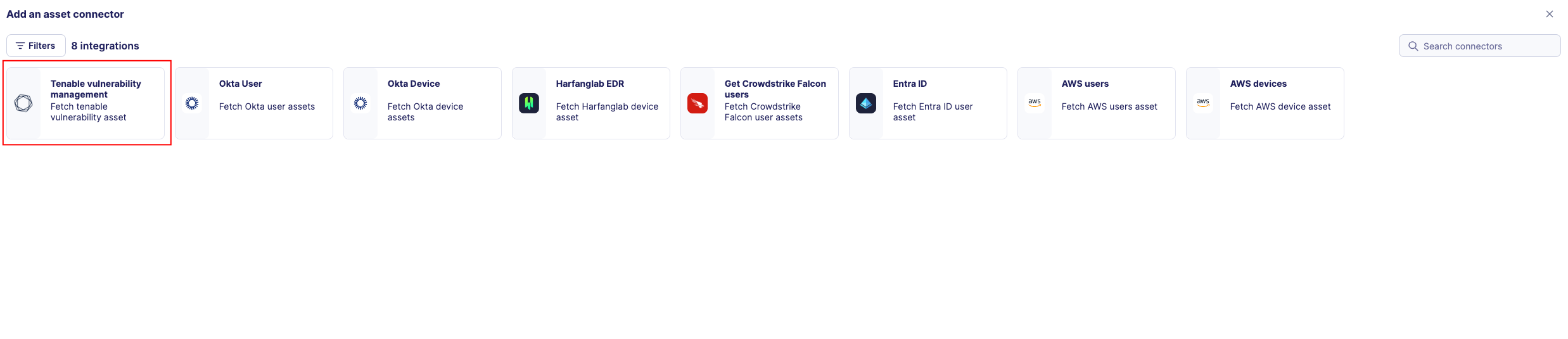
Choose Tenable Vulnerability Management, give it a name, and fill the required fields:
-
Test the connection by clicking the Test connector button.
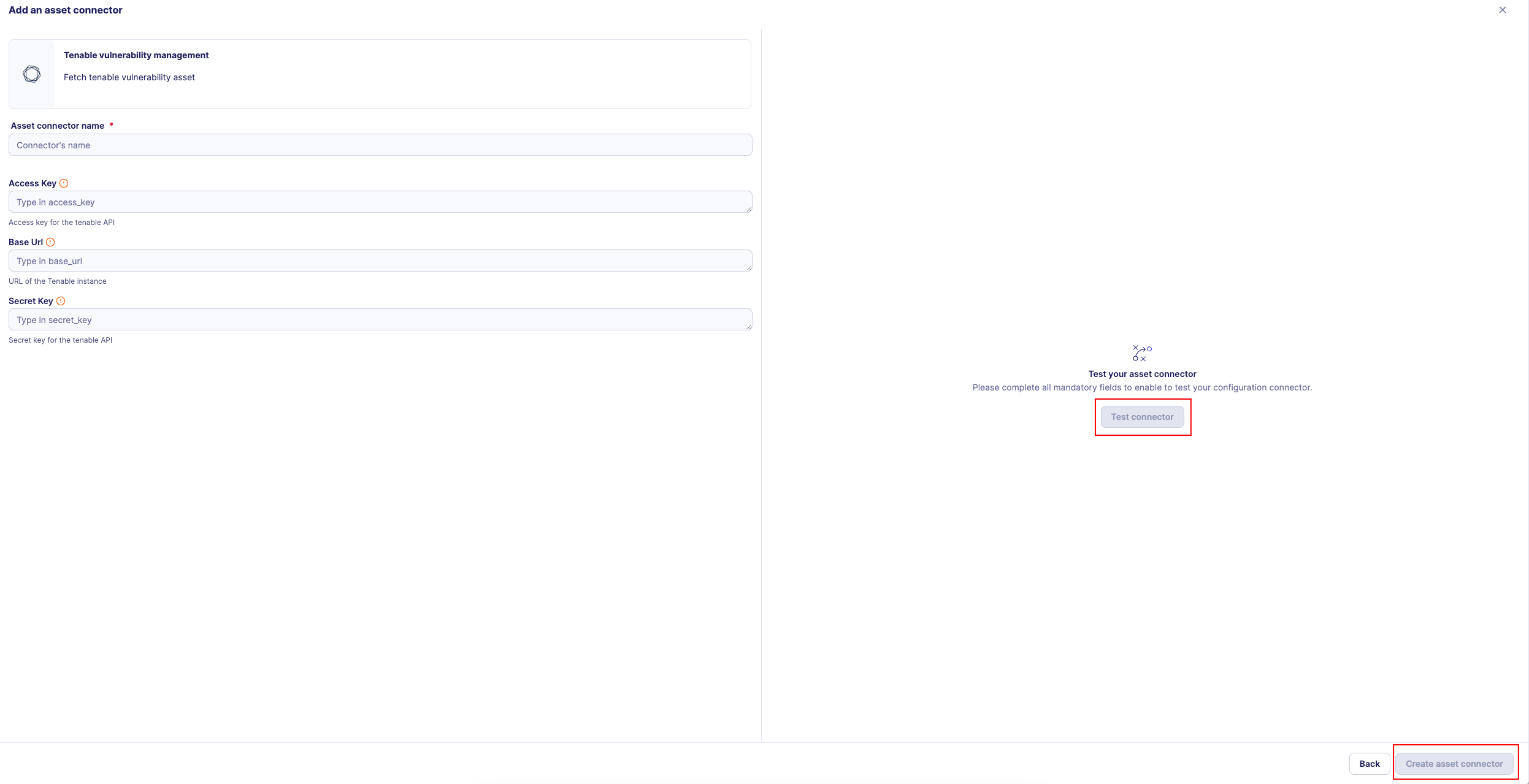
-
Click the Create asset connector button.
OCSF Mapping for Tenable Vulnerabilities
OCSF Class: vulnerability_finding
Class UID: 2002
Information Collected
The Tenable Vulnerabilities fetches comprehensive information and transforms it into the OCSF (Open Cybersecurity Schema Framework) format for standardized security monitoring and asset management.
API Response Examples
Tenable Critical Vulnerability
Critical vulnerability finding with CVE information
{
"vuln": {
"finding_id": "finding_12345",
"state": "OPEN",
"first_found": "2024-01-15T10:30:00.000Z",
"last_found": "2025-08-26T09:30:00.000Z",
"severity": "critical",
"plugin": {
"id": 11219,
"name": "Microsoft Windows SMB Shares Enumeration",
"type": "remote",
"synopsis": "The remote host is running an operating system that supports SMB.",
"description": "The remote host is running an operating system that supports SMB. It is possible to enumerate shares on the remote host.",
"see_also": [
"https://tools.ietf.org/html/rfc1001",
"https://tools.ietf.org/html/rfc1002"
],
"cve": [
"CVE-2020-1234",
"CVE-2020-5678"
],
"cvss_base_score": 9.8,
"cvss3_base_score": 9.8,
"publication_date": "2020-06-15T00:00:00.000Z",
"version": "1.42",
"vpr_v2": {
"score": 8.5
}
},
"source": "tenable_io"
},
"asset_info": {
"id": "a1b2c3d4e5f6g7h8",
"name": "PROD-SERVER-001",
"fqdn": [
"prod-server-001.example.com"
],
"hostname": [
"PROD-SERVER-001"
],
"ipv4": [
"192.168.1.50",
"10.0.0.25"
],
"system_type": [
"General Purpose"
],
"operating_system": [
"Windows Server 2019"
],
"aws_region": [
"us-east-1"
],
"first_seen": "2023-06-04T10:00:00.000Z",
"last_seen": "2025-08-26T09:30:00.000Z",
"created_at": "2023-06-04T10:00:00.000Z",
"has_agent": true,
"interfaces": [
{
"name": "eth0",
"ipv4": "192.168.1.50",
"mac": "00:1A:2B:3C:4D:5E"
}
]
}
}
Tenable Medium Vulnerability
Medium severity vulnerability finding
{
"vuln": {
"finding_id": "finding_67890",
"state": "REOPENED",
"first_found": "2024-03-20T14:15:00.000Z",
"last_found": "2025-08-20T08:45:00.000Z",
"severity": "medium",
"plugin": {
"id": 10662,
"name": "Apache Web Server Multiple Vulnerabilities",
"type": "remote",
"synopsis": "The remote host is running Apache Web Server.",
"description": "The remote host is running a version of Apache Web Server that is affected by multiple vulnerabilities.",
"see_also": [
"https://httpd.apache.org/security/vulnerabilities_24.html"
],
"cve": [
"CVE-2021-41773"
],
"cvss_base_score": 7.5,
"cvss3_base_score": 7.5,
"publication_date": "2021-10-05T00:00:00.000Z",
"version": "2.15",
"vpr_v2": {
"score": 5.2
}
},
"source": "tenable_io"
},
"asset_info": {
"id": "b2c3d4e5f6g7h8i9",
"name": "WEB-SERVER-002",
"fqdn": [
"web-server-002.example.com"
],
"hostname": [
"WEB-SERVER-002"
],
"ipv4": [
"192.168.1.60"
],
"system_type": [
"Web Server"
],
"operating_system": [
"Ubuntu 20.04 LTS"
],
"gcp_zone": [
"us-central1-a"
],
"first_seen": "2023-06-04T10:00:00.000Z",
"last_seen": "2025-08-26T09:30:00.000Z",
"created_at": "2023-06-04T10:00:00.000Z",
"has_agent": false,
"interfaces": [
{
"name": "eth0",
"ipv4": "192.168.1.60",
"mac": "00:2C:3D:4E:5F:60"
}
]
}
}
Data Mapping Table
The following table shows how source data is mapped to OCSF model fields:
| Source Field | OCSF Field Path | Description | Data Type | Logic |
|---|---|---|---|---|
vuln.state |
activity_id |
OCSF activity ID based on vulnerability state | integer |
Map OPEN=1 (Create), REOPENED=2 (Updated), FIXED=3 (Close) |
vuln.state |
activity_name |
OCSF activity name derived from vulnerability state | string |
Map state to activity name (OPEN->Create, REOPENED->Updated, FIXED->Close) |
static: Findings |
category_name |
OCSF category name for security findings | string |
Always 'Findings' for vulnerability findings |
static: 2 |
category_uid |
OCSF category UID | integer |
Always 2 for Findings category |
static: Vulnerability Finding |
class_name |
OCSF class name | string |
Always 'Vulnerability Finding' |
static: 2002 |
class_uid |
OCSF class UID | integer |
Always 2002 for Vulnerability Finding |
computed: 200200 + activity_id |
type_uid |
OCSF type UID | integer |
Base 200200 + activity_id (1=200201, 2=200202, 3=200203) |
computed: 'Vulnerability Finding: ' + activity_name |
type_name |
OCSF type name | string |
Concatenate 'Vulnerability Finding: ' with activity name |
vuln.first_found |
time |
OCSF event timestamp (vulnerability first found time) | integer |
Convert ISO 8601 to Unix epoch for OCSF event timestamp |
static: Tenable |
metadata.product.name |
Source product name | string |
Always 'Tenable' |
vuln.plugin.version |
metadata.product.version |
Plugin version stored in metadata.product.version | string |
Direct mapping of plugin version to metadata.product.version |
static: 1.6.0 |
metadata.version |
OCSF schema version | string |
Fixed OCSF schema version |
vuln.finding_id |
finding_info.uid |
Unique finding identifier | string |
Direct mapping of finding identifier |
vuln.plugin.type |
finding_info.types |
Finding types list (FindingInformation.types) | array[string] |
Wrap plugin type string in a list (e.g., ['remote'] or ['local']) |
vuln.source |
finding_info.data_sources |
Data sources list for the finding (FindingInformation.data_sources) | array[string] |
Wrap source string in a list (e.g., ['tenable_io']) |
vuln.plugin.name |
finding_info.title |
Finding title | string |
Direct mapping of plugin name as finding title |
vuln.plugin.synopsis || vuln.plugin.description |
finding_info.desc |
Finding description (FindingInformation.desc) | string |
Use synopsis if non-empty, otherwise fall back to description |
vuln.plugin.see_also[0] |
finding_info.src_url |
Primary reference URL (FindingInformation.src_url) | string |
Extract first reference URL from see_also array |
vuln.first_found |
finding_info.first_seen_time |
Finding first seen timestamp (Unix epoch) | integer |
Convert ISO 8601 to Unix epoch |
vuln.last_found |
finding_info.last_seen_time |
Finding last seen timestamp (Unix epoch) | integer |
Convert ISO 8601 to Unix epoch |
vuln.plugin.publication_date |
finding_info.created_time |
Finding/vulnerability creation timestamp (Unix epoch) | integer |
Convert ISO 8601 to Unix epoch |
static: Tenable Vulnerability Management |
finding_info.product.name |
Product providing the finding (FindingInformation.product.name) | string |
Always 'Tenable Vulnerability Management' |
static: [{phase: Other, phase_id: 99}] |
finding_info.kill_chain |
Kill chain phases (FindingInformation.kill_chain) | array[object] |
Default kill chain phase: Other (phase_id=99) |
vuln.plugin.cve[] |
vulnerabilities[].cve.uid |
CVE unique identifier (CVE.uid) | string |
Iterate over cve list; each CVE ID becomes vulnerabilities[].cve.uid |
static: CVE |
vulnerabilities[].cve.type |
CVE type identifier (CVE.type) | string |
Always 'CVE' for CVE-type vulnerabilities |
vuln.plugin.name |
vulnerabilities[].cve.title |
CVE title (CVE.title) | string |
Direct mapping of plugin name as CVE title |
vuln.plugin.description |
vulnerabilities[].cve.desc |
CVE description (CVE.desc) | string |
Direct mapping of plugin description as CVE description |
static: 2.0 |
vulnerabilities[].cve.cvss[0].version |
CVSS v2 version identifier (CVSS.version) | string |
Always '2.0' for the first CVSS entry (CVSS v2) |
vuln.plugin.cvss_base_score |
vulnerabilities[].cve.cvss[0].base_score |
CVSS v2 base score (CVSS.base_score) | double |
Direct mapping of CVSS v2 base score; only included if cvss_base_score is present |
static: 3.0 |
vulnerabilities[].cve.cvss[1].version |
CVSS v3 version identifier (CVSS.version) | string |
Always '3.0' for the second CVSS entry (CVSS v3) |
vuln.plugin.cvss3_base_score |
vulnerabilities[].cve.cvss[1].base_score |
CVSS v3 base score (CVSS.base_score) | double |
Direct mapping of CVSS v3 base score; only included if cvss3_base_score is present |
vuln.plugin.name |
vulnerabilities[].title |
Vulnerability title (VulnerabilityDetails.title) | string |
Direct mapping of plugin name as vulnerability title |
vuln.plugin.description |
vulnerabilities[].desc |
Vulnerability description (VulnerabilityDetails.desc) | string |
Direct mapping of plugin description |
vuln.plugin.see_also |
vulnerabilities[].references |
Vulnerability reference links (VulnerabilityDetails.references) | array[string] |
Direct mapping of see_also links as references |
vuln.severity |
vulnerabilities[].severity |
Vulnerability severity level (VulnerabilityDetails.severity) | string |
Direct mapping of vulnerability severity (critical, high, medium, low, info) |
static: Tenable |
vulnerabilities[].vendor_name |
Vulnerability vendor/source name (VulnerabilityDetails.vendor_name) | string |
Always 'Tenable' |
asset_info.id |
device.uid |
Device unique identifier | string |
Direct mapping of asset ID |
asset_info.system_type[0] |
device.type |
Device type (OCSF DeviceTypeStr) | string |
Map system type to DeviceTypeStr: 'server'/'general-purpose'->Server, 'desktop'->Desktop, 'laptop'->Laptop, 'tablet'->Tablet, 'mobile'->Mobile, 'virtual'/'vm'->Virtual, 'iot'->IOT, 'firewall'->Firewall, 'switch'->Switch, 'router'->Router, else->Other |
asset_info.system_type[0] |
device.type_id |
OCSF device type ID (DeviceTypeId) | integer |
Map system type to OCSF DeviceTypeId: Server=1, Desktop=2, Laptop=3, Tablet=4, Mobile=5, Virtual=6, IOT=7, Firewall=9, Switch=10, Router=12, Other=99, Unknown=0 |
asset_info.hostname[0] || asset_info.name || asset_info.fqdn[0] |
device.hostname |
Device hostname | string |
Use first hostname if available, otherwise asset name, otherwise first FQDN; fallback to 'unknown' |
asset_info.name |
device.name |
Device name | string |
Direct mapping of asset name |
asset_info.ipv4[0] |
device.ip |
Primary IPv4 address | string |
Extract first IPv4 address |
asset_info.operating_system[0] |
device.os.name |
Operating system name (OperatingSystem.name) | string |
Direct mapping of first operating system string |
asset_info.operating_system[0] |
device.os.type |
Operating system type (OSTypeStr) | string |
Map OS name to OSTypeStr: windows->windows, linux/centos/ubuntu/debian/red hat/rhel->linux, macos/mac os->macos, android->android, ios->ios, ipados->ipados, solaris->solaris, aix->aix, hp-ux/hpux->hp-ux, else->other |
asset_info.operating_system[0] |
device.os.type_id |
OCSF operating system type ID (OSTypeId) | integer |
Map OS name to OSTypeId: Windows=100, Linux=200, macOS=300, Android=201, iOS=301, iPadOS=302, Solaris=400, AIX=401, HP-UX=402, Other=99, Unknown=0 |
asset_info.interfaces |
device.network_interfaces |
Network interfaces (NetworkInterface objects) | array[object] |
Map each interface: hostname=fqdn[0] if present, ip=ipv4 if string else ipv4[0], mac=mac_address[0] if list, name=name; type/type_id derived from interface name (tunnel keywords->Tunnel/4, mobile keywords->Mobile/3, wireless keywords->Wireless/2, else->Wired/1) |
asset_info.aws_region[0] || asset_info.azure_location[0] || asset_info.gcp_zone[0] |
device.location.city |
Cloud region/location mapped to device.location.city (GeoLocation.city) | string |
Use AWS region if available, otherwise Azure location, otherwise GCP zone; stored as GeoLocation(country=None, city= |
asset_info.first_seen |
device.first_seen_time |
Device first seen timestamp (Unix epoch) | integer |
Convert ISO 8601 to Unix epoch |
asset_info.last_seen |
device.last_seen_time |
Device last seen timestamp (Unix epoch) | integer |
Convert ISO 8601 to Unix epoch |
asset_info.created_at |
device.created_time |
Device creation timestamp (Unix epoch) | integer |
Convert ISO 8601 to Unix epoch |
asset_info.has_agent |
device.is_managed |
Whether device is managed (has Tenable agent); maps to Device.is_managed | boolean |
Direct mapping of has_agent boolean as device.is_managed |
static: Tenable |
device.vendor_name |
Device vendor/source name (Device.vendor_name) | string |
Always 'Tenable' |
vuln.plugin.vpr_v2.score |
confidence |
Confidence level based on VPR v2 score | string |
Map VPR score to confidence string: >=7.0->High, >=4.0->Medium, <4.0->Low; null if VPR score absent |
vuln.plugin.vpr_v2.score |
confidence_id |
OCSF confidence ID based on VPR v2 score | integer |
Map VPR score to OCSF confidence ID: 3=High (>=7.0), 2=Medium (>=4.0 and <7.0), 1=Low (<4.0); null if VPR score absent |
vuln.plugin.vpr_v2.score |
confidence_score |
Confidence score from VPR v2 score (integer) | integer |
Cast VPR v2 score to integer; null if VPR score absent |
OCSF Model Structure
Vulnerability Finding: Create
Transformed Tenable vulnerability finding to OCSF Vulnerability Finding event
{
"activity_id": 1,
"activity_name": "Create",
"category_name": "Findings",
"category_uid": 2,
"class_name": "Vulnerability Finding",
"class_uid": 2002,
"type_name": "Vulnerability Finding: Create",
"type_uid": 200201,
"severity": "Critical",
"severity_id": 5,
"confidence_id": 3,
"time": 1705314600,
"metadata": {
"product": {
"name": "Tenable"
},
"version": "1.42"
},
"finding": {
"uid": "finding_12345",
"type": "remote",
"source": "tenable_io",
"title": "Microsoft Windows SMB Shares Enumeration",
"description": "The remote host is running an operating system that supports SMB. It is possible to enumerate shares on the remote host.",
"reference_url": "https://tools.ietf.org/html/rfc1001",
"first_seen_time": 1705314600,
"last_seen_time": 1725184200,
"created_time": 1592179200,
"product": {
"name": "Tenable Vulnerability Management"
},
"fingerprints": "N/A",
"kill_chain": [
{
"phase": "Other",
"phase_id": 99
}
]
},
"vulnerabilities": [
{
"type": "CVE",
"name": "CVE-2020-1234",
"title": "Microsoft Windows SMB Shares Enumeration",
"description": "The remote host is running an operating system that supports SMB.",
"details": "The remote host is running an operating system that supports SMB. It is possible to enumerate shares on the remote host.",
"severity": "critical",
"source": "Tenable",
"references": [
"https://tools.ietf.org/html/rfc1001",
"https://tools.ietf.org/html/rfc1002"
],
"cvss": {
"score": 9.8
},
"cvss3": {
"score": 9.8
}
}
],
"device": {
"uid": "a1b2c3d4e5f6g7h8",
"name": "PROD-SERVER-001",
"hostname": "PROD-SERVER-001",
"type": "General Purpose",
"ip": "192.168.1.50",
"has_agent": true,
"region": "us-east-1",
"source": "Tenable",
"created_time": 1685854800,
"updated_time": 1685854800,
"last_seen_time": 1725184200,
"os": {
"name": "Windows Server 2019",
"type": "Windows",
"version": "2019"
},
"network_interfaces": [
{
"name": "eth0",
"ipv4": "192.168.1.50",
"mac": "00:1A:2B:3C:4D:5E"
}
]
}
}