Cisco Identity Services Engine (ISE)
Overview
Cisco Identity Services Engine (ISE) is an intelligent security policy enforcement platform that reduces security risks by providing visibility of connections between all users and devices across all network infrastructure. This product provides exceptional control over the information and locations to which users have access on the network. This solution, and all its components, have been approved and rigorously tested as an integrated system.
- Vendor: Cisco
- Supported environment: On Premise
- Version compatibility: 3.1
- Detection based on: Telemetry
- Supported application or feature:
- AAA audit
- AAA diagnostics
- Profiler
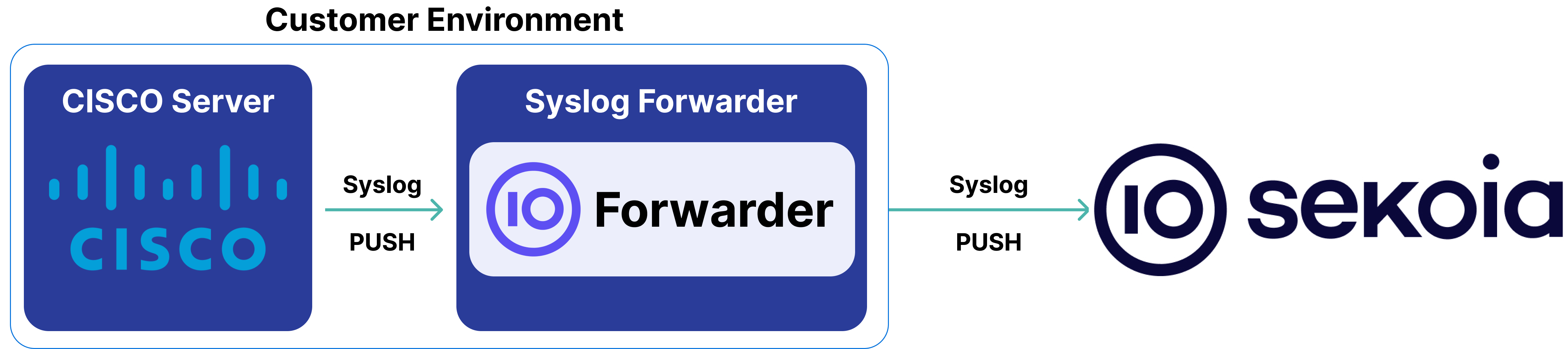
High-Level Architecture Diagram
- Type of integration: Outbound (PUSH to Sekoia.io)
- Schema
Specification
Prerequisites
- Resource:
- Self-managed syslog forwarder
- Network:
- Outbound traffic allowed
- Permissions:
- Administrator or Root access to the Cisco ISE device
- Root access to the Linux server with the syslog forwarder
Transport Protocol/Method
- Indirect Syslog
Logs details
- Supported functionalities: See section Overview
- Supported type(s) of structure: Plain text
- Supported verbosity level: Warning, Informational
Note
Log levels are based on the taxonomy of RFC5424. Adapt according to the terminology used by the editor.
Step-by-Step Configuration Procedure
Instructions on the 3rd Party Solution
This setup guide will show you how to provide an integration between Cisco Identity Services Engine events and Sekoia.io.
Enable Syslog Forwarding
- Log on your ISE Administration Interface.
- Follow this guide.
Instruction on Sekoia
Configure Your Intake
This section will guide you through creating the intake object in Sekoia, which provides a unique identifier called the "Intake key." The Intake key is essential for later configuration, as it references the Community, Entity, and Parser (Intake Format) used when receiving raw events on Sekoia.
- Go to the Sekoia Intake page.
- Click on the
+ New Intakebutton at the top right of the page. - Search for your Intake by the product name in the search bar.
- Give it a Name and associate it with an Entity (and a Community if using multi-tenant mode).
- Click on
Create.
Note
For more details on how to use the Intake page and to find the Intake key you just created, refer to this documentation.
Configure a forwarder
To forward events using syslog to Sekoia.io, you need to update the syslog header with the intake key you previously created. Here is an example of your message before the forwarder
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG RAW_MESSAGE
<%pri%>1 %timestamp:::date-rfc3339% %hostname% %app-name% %procid% LOG [SEKOIA@53288 intake_key=\"YOUR_INTAKE_KEY\"] RAW_MESSAGE
To achieve this you can:
- Use the Sekoia.io forwarder which is the official supported way to collect data using the syslog protocol in Sekoia.io. In charge of centralizing data coming from many equipments/sources and forwarding them to Sekoia.io with the apporpriated format, it is a prepackaged option. You only have to provide your intake key as parameter.
- Use your own Syslog service instance. Maybe you already have an intance of one of these components on your side and want to reuse it in order to centralize data before forwarding them to Sekoia.io. When using this mode, you have to configure and maintain your component in order to respect the expected Sekoia.io format.
Warning
Only the Sekoia.io forwarder is officially supported. Other options are documented for reference purposes but do not have official support.
Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
0003360952 1 0 2025-05-07 14:27:57.047 +02:00 0051005548 25002 INFO AD-Connector: ISE server TGT refresh succeeded, AD-Account-Name=JOHNDOE$@EXAMPLE.LOCAL, AD-Domain=EXAMPLE.LOCAL, AD-Log-Id=1234567890/1234567,
0003901877 1 0 2025-05-07 14:29:46.982 +02:00 0723317473 61026 NOTICE EAP-TLS: Shutdown secure connection with TLS peer, ConfigVersionId=360, PeerAddress=AA-BB-CC-DD-EE-FF, PeerName=CN=example.com, UniqueConnectionIdentifier =2ce4ef7a-0575-482b-8ed5-b3b068e873a1, ShutdownReason =ClosedByISE,
CISE_Administrative_and_Operational_Audit 0026935732 1 0 2025-10-23 14:26:49.538 +02:00 0264007760 51000 NOTICE Administrator-Login: Administrator authentication failed, ConfigVersionId=118, AdminInterface=GUI, AdminIPAddress=1.2.3.4, AdminName=jdoe, OperationMessageText=Authentication failed due to invalid user or password\, or account is disabled/locked,
0001514749 7 3 SelectedAuthenticationIdentityStores=Internal Endpoints, AuthenticationStatus=AuthenticationPassed, NetworkDeviceGroups=Location#All Locations#H7, NetworkDeviceGroups=Device Type#All Device Types#Cisco_3650, NetworkDeviceGroups=Groupe Imprimantes#Groupe Imprimantes, NetworkDeviceGroups=APs Indoor ou Outdoor#Groupe APs, IdentityPolicyMatchedRule=Dot1X, AuthorizationPolicyMatchedRule=Some rule, EapTunnel=EAP-FAST, EapAuthentication=EAP-MSCHAPv2, cisco-av-pair=AuthenticationIdentityStore=AD1, cisco-av-pair=FQSubjectName=000000-000-0000-00000000000#host/test, cisco-av-pair=UniqueSubjectID=XXXXXXXXXXXXXXXXXXXXX, CPMSessionID=TestSessionId, EndPointMACAddress=02:00:00:00:00:00, PostureAssessmentStatus=NotApplicable, EndPointMatchedProfile=Unknown, EapChainingResult=User failed and machine succeeded, ISEPolicySetName=WIRELESS_1X_DFS, IdentitySelectionMatchedRule=Dot1X,#015
0000248509 3 0 2025-02-18 14:34:01.264 +01:00 0005365098 5400 NOTICE Failed-Attempt: Authentication failed, ConfigVersionId=88, Device IP Address=3.4.5.6, Device Port=53874, DestinationIPAddress=5.6.7.8, DestinationPort=1812, RadiusPacketType=AccessRequest, UserName=john.doe, Protocol=Radius, NetworkDeviceName=WLAN, User-Name=john.doe, NAS-IP-Address=2.3.4.5, NAS-Port=1656127488, Called-Station-ID=1.2.3.4, Calling-Station-ID=192.0.2.1, NAS-Port-Type=Virtual, Tunnel-Client-Endpoint=(tag=0) 192.0.2.1, cisco-av-pair=mdm-tlv=device-platform=win, cisco-av-pair=mdm-tlv=device-mac=61-05-38-5c-f8-bd, cisco-av-pair=mdm-tlv=device-platform-version=10.0.26100 , cisco-av-pair=mdm-tlv=device-public-mac=61-05-38-5c-f8-bd, cisco-av-pair=mdm-tlv=device-type=Default string Default string, cisco-av-pair=mdm-tlv=ac-user-agent=AnyConnect Windows 4.6.03049,
Dec 9 17:30:23 example CISE_Passed_Authentications 0000453439 1 0 2025-12-09 17:30:23.365 +01:00 0007121364 5200 NOTICE Passed-Authentication: Authentication succeeded, ConfigVersionId=10, Device IP Address=1.2.3.4, DestinationIPAddress=5.6.7.8, DestinationPort=1812, UserName=JOHNDOE$@example.local, Protocol=Radius, NetworkDeviceName=DEVICE_NAME, User-Name=host/JOHNDOE.example.local, NAS-IP-Address=1.2.3.4, NAS-Port=1, Service-Type=Framed, Framed-MTU=1400, State=64CPMSessionID=abc12345;36SessionID=example/111111111/222222;, Called-Station-ID=02-00-00-00-00-01:InterneTLS, Calling-Station-ID=02-00-00-00-00-02, NAS-Identifier=02-00-00-00-00-01:vap4, Acct-Session-Id=ABCDEF1234567890, Acct-Multi-Session-Id=123456890ABCDEF, NAS-Port-Type=Wireless - IEEE 802.11, Connect-Info=CONNECT 54.00 Mbps / 802.11ax / RSSI: 22 / Channel: 36, undefined-186=00:01:02:04, undefined-187=00:01:02:04, undefined-188=00:01:02:01, NetworkDeviceProfileName=Cisco, NetworkDeviceProfileId=33333333-3333-3333-3333-333333333333, IsThirdPartyDeviceFlow=false, RadiusFlowType=Wireless802_1x, SSID=02-00-00-00-00-01:InterneTLS, AcsSessionID=example/111111111/222222, AuthenticationIdentityStore=AD_TEST, AuthenticationMethod=x509_PKI, SelectedAccessService=Default Network Access, SelectedAuthorizationProfiles=Cisco_VLAN_WiFi_INT_WW, IsMachineAuthentication=true, RequestLatency=61, IdentityGroup=Endpoint Identity Groups:Profiled, Step=11001, Step=11017, Step=11117, Step=15049, Step=15008, Step=15048, Step=11507, Step=12500, Step=11006, Step=11001, Step=11018, Step=12502, Step=61025, Step=12800, Step=12545, Step=12542, Step=12805, Step=12806, Step=12807, Step=12808, Step=12809, Step=12810, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12810, Step=12571, Step=12571, Step=12811, Step=12812, Step=12813, Step=12803, Step=12804, Step=12801, Step=12802, Step=12816, Step=12509, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=15041, Step=15048, Step=22072, Step=22071, Step=15013, Step=24433, Step=24325, Step=24313, Step=24319, Step=24323, Step=24700, Step=22037, Step=12506, Step=61026, Step=15036, Step=24209, Step=24211, Step=15048, Step=24433, Step=24355, Step=24435, Step=15048, Step=15048, Step=15048, Step=15016, Step=22081, Step=22080, Step=11503, Step=11002, SelectedAuthenticationIdentityStores=Preloaded_Certif_Profile_TEST, AuthenticationStatus=AuthenticationPassed, NetworkDeviceGroups=Location#All Locations#Nantes, NetworkDeviceGroups=Device Type#All Device Types#AP_EXAMPLE, NetworkDeviceGroups=IPSEC#Is IPSEC Device#No, IdentityPolicyMatchedRule=Dot1X, AuthorizationPolicyMatchedRule=USER_WIFI_INTERNE_TLS, EapAuthentication=EAP-TLS, cisco-av-pair=AuthenticationIdentityStore=AD_TEST, cisco-av-pair=FQSubjectName=44444444-4444-4444-4444-444444444444#lap-12345$@example.local, cisco-av-pair=UniqueSubjectID=11111111111111111111aaaaaaaaaaaaaaaaaaaa, Serial Number=00 01 02 03 04 05 06 07 08 09 0A 0B 0C 0D 0E 0E 10 11 12, Subject - Common Name=JOHNDOE.example.local, Subject Alternative Name=JOHNDOE.example.local, CPMSessionID=abc12345, EndPointMACAddress=02-00-00-00-00-02, PostureAssessmentStatus=NotApplicable, EndPointMatchedProfile=Intel-Device, ISEPolicySetName=REDACTED, IdentitySelectionMatchedRule=Dot1X, StepLatency=1=0;2=0;3=0;4=1;5=0;6=1;7=0;8=0;9=30;10=0;11=1;12=0;13=0;14=0;15=0;16=1;17=0;18=0;19=25;20=0;21=0;22=0;23=0;24=37;25=0;26=0;27=0;28=0;29=15;30=0;31=0;32=0;33=0;34=15;35=0;36=0;37=0;38=0;39=16;40=0;41=1;42=0;43=0;44=15;45=0;46=0;47=0;48=0;49=170;50=0;51=0;52=0;53=0;54=16;55=0;56=0;57=0;58=0;59=15;60=0;61=1;62=0;63=0;64=0;65=1;66=2;67=0;68=0;69=0;70=0;71=0;72=0;73=0;74=0;75=1;76=33;77=0;78=1;79=0;80=0;81=1;82=0;83=0;84=0;85=4;86=0;87=0;88=0;89=1;90=0;91=0;92=0;93=0;94=1;95=3;96=4;100=3;101=0;102=0;103=1;104=0;105=0;106=0;107=1, MFCInfoHardwareManufacturer=Intel Corporation, MFCInfoHardwareModel=Intel-Device, MFCInfoEndpointType=Workstation , AD-Host-Resolved-Identities=JOHNDOE$@example.local, AD-Host-Candidate-Identities=JOHNDOE$@example.local, AD-Host-Join-Point=TEST.LOCAL, StepData=5= DEVICE.Location, StepData=63=certificate for JOHNDOE.example.local, StepData=64=certificate for REDACTED, StepData=80= Normalised Radius.RadiusFlowType, StepData=81=All_User_ID_Stores, StepData=83=AD_TEST, StepData=84=AD_TEST, StepData=85=CN=JOHNDOE.example.local, JOHNDOE.example.local, JOHNDOE.example.local, StepData=86=example.local, StepData=87=example.local, StepData=89=AD_TEST, StepData=96= EndPoints.EndPointPolicy, StepData=0=AD_TEST, StepData=1=example.local, StepData=2=AD_TEST, StepData=100= AD_TEST.ExternalGroups, StepData=101= DEVICE.Device Type, StepData=102= Radius.Called-Station-ID, TotalAuthenLatency=417, ClientLatency=356, AD-Host-Resolved-DNs=CN=JOHNDOE,OU=HYBRID,OU=ORDINATEURS,DC=TEST,DC=local, AD-Host-DNS-Domain=example.local, AD-Groups-Names=example.local/SYSTEME/EXAMPLE/TEST, AD-Host-NetBios-Name=TEST, IsMachineIdentity=true, AD-Host-SamAccount-Name=JOHNDOE$, AD-Host-Qualified-Name=JOHNDOE$@example.local, allowEasyWiredSession=false, TLSCipher=ECDHE-RSA-AES256-GCM-SHA384, TLSVersion=TLSv1.2, DTLSSupport=Unknown, Subject=CN=JOHNDOE.example.local, Subject Alternative Name - DNS=JOHNDOE.example.local, Issuer=CN=REDACTED,DC=TEST,DC=local, Issuer - Common Name=REDACTED, Issuer - Domain Component=TEST, Issuer - Domain Component=local, Key Usage=0, Key Usage=2, Extended Key Usage - Name=138, Extended Key Usage - Name=132, Extended Key Usage - Name=130, Extended Key Usage - OID=1.3.6.1.4.1.311.10.3.4, Extended Key Usage - OID=1.3.6.1.5.5.7.3.4, Extended Key Usage - OID=1.3.6.1.5.5.7.3.2, Template Name=1.3.6.1.4.1.311.21.8.12772041.905510.6439332.852183.9969916.94.7965419.54627, Days to Expiry=255, Issuer - Fingerprint SHA-256=01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b, AKI=00:11:22:33:44:55:66:77:88:99:AA:BB:CC:DD:EE:FF:01:02:03:04, HostIdentityGroup=Endpoint Identity Groups:Profiled, ExternalGroups=S-1-2-3, Network Device Profile=Cisco, Location=Location#All Locations#Nantes, Device Type=Device Type#All Device Types#AP_EXAMPLE, IPSEC=IPSEC#Is IPSEC Device#No, EndPointPolicy=55555555-5555-5555-5555-555555555555, Name=Endpoint Identity Groups:Profiled, Response={User-Name=JOHNDOE$@example.local; Class=CACS:abc12345:example/111111111/222222; Tunnel-Type=(tag=1) VLAN; Tunnel-Medium-Type=(tag=1) 802; Tunnel-Private-Group-ID=(tag=1) 157; MS-MPPE-Send-Key=****; MS-MPPE-Recv-Key=****; LicenseTypes=1; },
0000005921 7 5 02-22-33-44-55-66:EVENT_REASON\,dhcp-parameter-request-list=1\, 3\, 6\, 15\, 31\, 33\, 43\, 44\, 46\, 47\, 119\, 121\, 249\, 252\,OperatingSystem=Windows\,PostureApplicable=Yes\,User-Fetch-Department=\,AD-Last-Fetch-Time=1759879885138\,Issuer=CN=COMPANY-SUB-CA\\OU=DSI\\O=COMPANY\\L=RENNES\\C=FR\,NmapSubnetScanID=0\,AD-Host-DNS-Domain=domain.example.com\,Device Identifier=\,Airespace-Wlan-Id=12\,ipv6=\,Issuer - Organization=COMPANY\,TotalAuthenLatency=2\,MatchedPolicyID=11111111-1111-1111-1111-111111111111\,Service-Type=Framed\,op=BOOTREQUEST\,UserName=j.doe@domain.example.com\,FeedService=false\,TLSVersion=TLSv1.2\,AD-Host-NetBios-Name=DOMAIN\,Issuer - Location=RENNES\,SelectedAuthorizationProfiles=PermitAccess\,host-name=example.com\,COMPANY_LAN=COMPANY_LAN#COMPANY_LAN\,Subject=CN=example.com.DOMAIN.example.com\,
0085509171 4 0 2026-01-07 19:51:20.282 +00:00 5510785544 5202 NOTICE Device-Administration: Command Authorization succeeded, ConfigVersionId=242, Device IP Address=1.1.1.1, DestinationIPAddress=2.2.2.2, DestinationPort=49, UserName=Username1, CmdSet=[ CmdAV=show CmdArgAV=ipv6 CmdArgAV=mld CmdArgAV=snooping CmdArgAV=<cr> ], Protocol=Tacacs, MatchedCommandSet=AllowAllCommands, NetworkDeviceName=example.local, Type=Authorization, Privilege-Level=1, Authen-Type=ASCII, Service=None, User=Username1, Port=tty1, Remote-Address=3.3.3.3, Authen-Method=None, Service-Argument=shell, NetworkDeviceProfileId=11111111-1111-1111-1111-111111111111, AcsSessionID=EXAMPLE/11111/22222, AuthenticationIdentityStore=IT_AD, AuthenticationMethod=Lookup, SelectedAccessService=Default Device Admin, SelectedCommandSet=AllowAllCommands, IsMachineAuthentication=false, RequestLatency=90, Step=13005, Step=15049, Step=15008, Step=15048, Step=15041,
INFO: Configuration Changed: Admin=john.doe; Object Type=EPPurgeScheduler; Object Name=f36afcff-e3af-4a70-99c0-5e5304c1c336
Oct 27 14:29:31 HOST-01 CISE_Failed_Attempts 0001027727 1 0 2025-10-27 14:29:31.301 +01:00 0015075255 5400 NOTICE Failed-Attempt: Authentication failed, ConfigVersionId=11, Device IP Address=1.2.3.4, Device Port=42568, DestinationIPAddress=1.2.3.4, DestinationPort=1812, RadiusPacketType=AccessRequest, UserName=user1, Protocol=Radius, NetworkDeviceName=DEVICE-01, User-Name=aabbccddeeff, NAS-IP-Address=1.2.3.4, NAS-Port=19, Service-Type=Call Check, Called-Station-ID=user1:, Calling-Station-ID=user1, NAS-Port-Type=Ethernet, cisco-av-pair=audit-session-id=000000000000000000000000, OriginalUserName=aabbccddeeff, NetworkDeviceProfileName=Cisco, NetworkDeviceProfileId=00000000-0000-0000-0000-000000000000, IsThirdPartyDeviceFlow=false, RadiusFlowType=WiredMAB, SSID=user1:, AcsSessionID=HOST-01/000000000/000000, AuthenticationIdentityStore=Internal Endpoints, AuthenticationMethod=Lookup, SelectedAccessService=Default Network Access, SelectedAuthorizationProfiles=DenyAccess, UseCase=Host Lookup, RequestLatency=25, IdentityGroup=Endpoint Identity Groups:Profiled, FailureReason=15039 Rejected per authorization profile, Step=11001, Step=11017, Step=11027, Step=15049, Step=15008, Step=15048, Step=15041, Step=15048, Step=15013, Step=24209, Step=24211, Step=22037, Step=15036, Step=15048, Step=15048, Step=15048, Step=24432, Step=24325, Step=24313, Step=24318, Step=24322, Step=24352, Step=24412, Step=15048, Step=15048, Step=15016, Step=15039, Step=11003, SelectedAuthenticationIdentityStores=Internal Endpoints, NetworkDeviceGroups=Location#All Locations#SITE-01, NetworkDeviceGroups=Device Type#All Device Types#SW_Vendor_Site, NetworkDeviceGroups=IPSEC#Is IPSEC Device#No, IdentityPolicyMatchedRule=MAB, AuthorizationPolicyMatchedRule=Default, cisco-av-pair=AuthenticationIdentityStore=Internal Endpoints, UserType=Host, CPMSessionID=000000000000000000000000, EndPointMACAddress=user1, EndPointMatchedProfile=VENDOR-Device, DeviceRegistrationStatus=notRegistered, ISEPolicySetName=POLICY-01, IdentitySelectionMatchedRule=MAB, StepLatency=1=0;2=1;3=0;4=0;5=0;6=1;7=0;8=1;9=0;10=1;11=0;12=0;13=12;14=5;15=0;23=3;24=0;25=1;26=0;27=0, StepData=5= DEVICE.Location, StepData=7= Normalised Radius.RadiusFlowType, StepData=8=Internal Endpoints, StepData=13= EndPoints.LogicalProfile, StepData=14= EndPoints.EndPointPolicy, StepData=15= DEVICE.Device Type, StepData=0=AD_EXAMPLE, StepData=1=user1, StepData=2=example.local, StepData=3=example.local, StepData=5=ERROR_NO_SUCH_USER, StepData=6=AD_EXAMPLE, StepData=23= AD_EXAMPLE.ExternalGroups, StepData=24= Radius.Called-Station-ID, TotalAuthenLatency=25, ClientLatency=0, DTLSSupport=Unknown, HostIdentityGroup=Endpoint Identity Groups:Profiled, Network Device Profile=Cisco, Location=Location#All Locations#SITE-01, Device Type=Device Type#All Device Types#SW_Vendor_Site, IPSEC=IPSEC#Is IPSEC Device#No, EndPointPolicy=00000000-0000-0000-0000-000000000000, Name=Endpoint Identity Groups:Profiled, Response={RadiusPacketType=AccessReject; AuthenticationResult=Passed; UserName=AA:BB:CC:DD:EE:FF; },
CISE_Failed_Attempts 0000815086 4 1 SSID=11-22-33-44-55-66, AcsSessionID=HOST_01/552714706/823738, AuthenticationIdentityStore=Internal Endpoints, AuthenticationMethod=Lookup, SelectedAccessService=Selected_Service, SelectedAuthorizationProfiles=DenyAccess, UseCase=Host Lookup, RequestLatency=12, IdentityGroup=Endpoint Identity Groups:Profiled, FailureReason=15039 Rejected per authorization profile, Step=11001, Step=11017, Step=11027, Step=15049, Step=15008, Step=15048, Step=15048, Step=15048, Step=15048, Step=15041, Step=15048, Step=15013, Step=24209, Step=24211, Step=22037, Step=15036, Step=15048, Step=15048, Step=24032, Step=24017, Step=24019, Step=24034, Step=24031, Step=24017, Step=24019, Step=15048, Step=24032, Step=24017, Step=24019, Step=24034, Step=24031, Step=24017, Step=24019, Step=15048, Step=15048, Step=15016, Step=15039, Step=11003, SelectedAuthenticationIdentityStores=Internal Endpoints, NetworkDeviceGroups=Location#All Locations#EU#France#RENNES,#15
CISE_Failed_Attempts 0000815085 5 4 IPSEC=IPSEC#Is IPSEC Device#No, Name=Endpoint Identity Groups:Profiled, Response={RadiusPacketType=AccessReject; AuthenticationResult=Passed; UserName=11:22:33:44:55:66; },#15
0000087238 3 1 AcsSessionID=ISE-CISCO/1111111/222222, AuthenticationIdentityStore=Internal Endpoints, AuthenticationMethod=Lookup, SelectedAccessService=AuthenticationMAB, SelectedAuthorizationProfiles=DenyAccess, UseCase=Host Lookup, RequestLatency=5, IdentityGroup=Endpoint Identity Groups:Unknown, FailureReason=15039 Rejected per authorization profile, Step=11001, Step=11017, Step=11027, Step=15049, Step=15008, Step=15048, Step=15048, Step=15048, Step=15041, Step=15013, Step=24209, Step=24211, Step=22037, Step=15036, Step=15016, Step=15039, Step=11003, SelectedAuthenticationIdentityStores=Internal Endpoints, NetworkDeviceGroups=Device Type#All Device Types#Switch, NetworkDeviceGroups=IPSEC#Is IPSEC Device#No, NetworkDeviceGroups=Location#All Locations, IdentityPolicyMatchedRule=Authentication Rule 1, AuthorizationPolicyMatchedRule=Default, cisco-av-pair=AuthenticationIdentityStore=Internal Endpoints, UserType=Host, CPMSessionID=ABCDEF0123456,
0000089788 3 2 EndPointMACAddress=02-11-22-33-44-55, EndPointMatchedProfile=Unknown, DeviceRegistrationStatus=notRegistered, ISEPolicySetName=MAB, IdentitySelectionMatchedRule=Authentication Rule 1, StepLatency=1=0\;2=0\;3=0\;4=0\;5=0\;6=1\;7=0\;8=0\;9=1\;10=0\;11=1\;12=0\;13=0\;14=1\;15=0\;16=0, StepData=5= DEVICE.Device Type, StepData=6= Radius.NAS-IP-Address, StepData=7= Normalised Radius.RadiusFlowType, StepData=9=Internal Endpoints, TotalAuthenLatency=4, ClientLatency=0, DTLSSupport=Unknown, HostIdentityGroup=Endpoint Identity Groups:Unknown, Network Device Profile=Cisco, Location=Location#All Locations, Device Type=Device Type#All Device Types#Switch, IPSEC=IPSEC#Is IPSEC Device#No, Name=Endpoint Identity Groups:Unknown, Response={RadiusPacketType=AccessReject; AuthenticationResult=Passed; UserName=02:00:00:00:00:00; },
INFO: 5 endpoint(s) purged successfully
2023-06-07 04:26:17.306 +0200 60198 INFO null: MnT purge event occurred, MESSAGE=completed successfully,
WARN: AcsSyslogContentAaaDiagnostics:: ACTIVE_DIRECTORY_DIAGNOSTIC_TOOL_ISSUES_FOUND need to complete
INFO: EAP Connection Timeout : Server=example.com; NAS IP Address=1.2.3.4; NAS Identifier=02:00:00:00:00:00:test1
0000738292 7 0 2025-01-09 09:28:49.914 +01:00 0043796555 5200 NOTICE Passed-Authentication: Authentication succeeded, ConfigVersionId=186, Device IP Address=192.0.2.1, DestinationIPAddress=1.2.3.4, DestinationPort=1812, UserName=user1, Protocol=Radius, NetworkDeviceName=MGCUH1-3, User-Name=user1, NAS-IP-Address=192.0.2.1, NAS-Port=1001, Service-Type=Framed, Framed-MTU=1449, State=37CPMSessionID=XXXXXXXXXXXXXX\;36SessionID=MGDFSISE2/515448264/543038\;, Called-Station-ID=02:22:33:44:55:66, Calling-Station-ID=02:22:33:44:66:77, NAS-Identifier=MGCUH1-3, NAS-Port-Type=Wireless - IEEE 802.11, NAS-Port-Id=Capwap2, EAP-Key-Name=, cisco-av-pair=service-type=Framed, cisco-av-pair=audit-session-id=XXXXXXXXXXXXXX, cisco-av-pair=method=dot1x, cisco-av-pair=cisco-wlan-ssid=DFS, Airespace-Wlan-Id=5, NetworkDeviceProfileName=Cisco, NetworkDeviceProfileId=aaaaaaaaaaaaaaaaaaaaa,#015
CISE_RADIUS_Accounting 0002391460 1 0 2025-07-30 11:50:34.267 +02:00 0023023046 3002 NOTICE Radius-Accounting: RADIUS Accounting watchdog update, ConfigVersionId=83, Device IP Address=1.2.3.4, UserName=user1, NetworkDeviceName=Test-Network-Device-Name, User-Name=user1, NAS-IP-Address=1.2.3.4, NAS-Port=50107, Framed-IP-Address=3.4.5.6, Class=CACS:0A0D00F90000001402268B53:ise/523393559/11169221, Called-Station-ID=02-00-00-00-00-00, Calling-Station-ID=user1, Acct-Status-Type=Interim-Update, Acct-Delay-Time=0, Acct-Input-Octets=1848852125, Acct-Output-Octets=2808400785, Acct-Session-Id=00000070, Acct-Input-Packets=27991836, Acct-Output-Packets=40488347, Event-Timestamp=1753869011, NAS-Port-Type=Ethernet, NAS-Port-Id=GigabitEthernet0/7, cisco-av-pair=audit-session-id=0A0D00F90000001402268B53, cisco-av-pair=vlan-id=1330, cisco-av-pair=method=mab, AcsSessionID=MGMT-ISE01/0000000000/2185126, SelectedAccessService=Default Network Access, RequestLatency=3, Step=11004, Step=11017, Step=15049, Step=15008, Step=15048, Step=15048, Step=22094, Step=11005, NetworkDeviceGroups=Location#All Locations#Test Test#LAN#ACA, NetworkDeviceGroups=Device Type#All Device Types#Switch#2960L, NetworkDeviceGroups=IPSEC#Is IPSEC Device#No, CPMSessionID=0A0D00F90000001402268B53, StepLatency=1=0\;2=0\;3=0\;4=1\;5=0\;6=1\;7=0, StepData=4= Normalised Radius.TTTTT, StepData=5= Normalised Radius.RadiusFlowType, TotalAuthenLatency=3, ClientLatency=0, Model Name=Unknown, Software Version=Unknown, Network Device Profile=Cisco, Location=Location#All Locations#Test Test#LAN#ACA, Device Type=Device Type#All Device Types#Switch#2960L, IPSEC=IPSEC#Is IPSEC Device#No,
0000000000 1 0 2025-07-29 14:07:18.047 +02:00 0000000000 51000 NOTICE Administrator-Login: Administrator authentication failed, ConfigVersionId=XX, AdminInterface=GUI, AdminIPAddress=1.2.3.4, AdminName=user1, OperationMessageText=Authentication failed due to invalid user or password, or account is disabled/locked,
CISE_Administrative_and_Operational_Audit 0000000000 1 0 2025-07-29 14:07:18.047 +02:00 0000000000 51000 NOTICE Administrator-Login: Administrator authentication failed, ConfigVersionId=XX, AdminInterface=GUI, AdminIPAddress=1.2.3.4, AdminName=user1, OperationMessageText=Authentication failed due to invalid user or password, or account is disabled/locked,
0017407182 7 4 WiFi iPhone-ABC1234 Example Cert\, iPhone-ABC1234 \, 11111111-1111-1111-1111-111111111111, StepData=34=a1.example.org, StepData=35=a1.example.org, StepData=36=b1.example.org\,Domain trust is one-way, StepData=37=example.net\,Domain trust is one-way, StepData=38=EXAMPLE.LOCAL\,Domain trust is one-way, StepData=40=ERROR_NO_SUCH_USER, StepData=41=IT_AD, StepData=51= Network Access.NetworkDeviceName, StepData=52= CERTIFICATE.Issuer - Common Name, TotalAuthenLatency=27, ClientLatency=15, IsMachineIdentity=false, allowEasyWiredSession=false, TLSCipher=ECDHE-RSA-AES256-GCM-SHA384, TLSVersion=TLSv1.2, DTLSSupport=Unknown, Subject=CN=WiFi iPhone-ABC1234 Example Cert, Subject Alternative Name - Other Name=iPhone-ABC1234 , Subject Alternative Name - DNS=11111111-1111-1111-1111-111111111111, Issuer=CN=Example Sub CA G2\,DC=a1\,DC=example.org, Issuer - Common Name=Example Sub CA G2, Issuer - Domain Component=a1, Issuer - Domain Component=example.org,
0003023466 4 3 DTLSSupport=Unknown, HostIdentityGroup=Endpoint Identity Groups:Unknown, Model Name=9800-CL, Network Device Profile=Cisco, Location=Location#All Locations#SWE#Azure, Device Type=Device Type#All Device Types#WLC9800, IPSEC=IPSEC#Is IPSEC Device#No, Name=Endpoint Identity Groups:Unknown, Response={UserName=02:00:00:00:00:01; User-Name=02-00-00-00-00-01; Class=CACS:01BCDEF023:ABC/111111/22222; cisco-av-pair=url-redirect-acl=GS-Redirect_ACL; cisco-av-pair=url-redirect=https://REDACTED; cisco-av-pair=profile-name=Unknown; LicenseTypes=1; },
0017407213 1 0 2026-01-22 17:20:22.444 +01:00 1165981159 61025 NOTICE Administrative and Operational Audit: Open secure connection with TLS peer, ConfigVersionId=167, UserName=USERNAME, ISELocalAddress=1.1.1.1:1812, ISEModuleName=EAP_SERVER, ISEServiceName=EAP-TLS Server, PeerAddress=02-00-00-00-00-01, PeerName=iPhone-ABC123 , ConnectionStatus=Succeeded, UniqueConnectionIdentifier =11111111-1111-1111-1111-111111111111,
0003023463 3 0 2026-01-22 17:20:15.900 +00:00 0196666985 3000 NOTICE Radius-Accounting: RADIUS Accounting start request, ConfigVersionId=226, Device IP Address=2.2.2.2, UserName=02-00-00-00-00-01, NetworkDeviceName=DEVICE_NAME, User-Name=02-00-00-00-00-01, NAS-IP-Address=2.2.2.2, NAS-Port=20012, Framed-IP-Address=1.1.1.1, Class=CACS:01234ABC:ABC/111111/222222, Called-Station-ID=02-00-00-00-00-02, Called-Station-ID=example:abcs, Calling-Station-ID=02-00-00-00-00-01, NAS-Identifier=DEVICE_NAME, Acct-Status-Type=Start, Acct-Delay-Time=0, Acct-Session-Id=00000123, Acct-Authentic=Remote, Event-Timestamp=1769102415, NAS-Port-Type=Wireless - IEEE 802.11, NAS-Port-Id=example, cisco-av-pair=dc-profile-name=Un-Classified Device, cisco-av-pair=dc-device-name=Unknown Device, cisco-av-pair=dc-device-class-tag=Un-Classified Device, cisco-av-pair=dc-certainty-metric=0,
0001514749 7 6 Response={Class=CACS:XXXXXXXXX:asdsa/000000/111111; Tunnel-Type=(tag=1) VLAN; Tunnel-Medium-Type=(tag=1) 802; Tunnel-Private-Group-ID=(tag=1) COMPUTER; EAP-Key-Name=EAP-Key-VALUE; MS-MPPE-Send-Key=****; MS-MPPE-Recv-Key=****; LicenseTypes=1; },#015
WARN: Dynamic Authorization Failed for Device : Server=example.com; Calling Station Id=N/A; Network device IP=1.2.3.4; Network Device
WARN: Profiler SNMP Request Failure : Server= example.com; NAD Address=1.2.3.4; Error Message=Request timed out.
WARN: TrustSec deploy verification failed to reach NAD.: Device Name=device005.internal.example.org; Device Ip=1.2.3.4; Device login username=admin
CISE_Passed_Authentications 0000815089 10 8 DC=infra,DC=xxxxx, Issuer - Common Name=XXX Devices CA, Issuer - Domain Component=xxx, Issuer - Domain Component=infra, Issuer - Domain Component=xxxxx, Key Usage=0, Key Usage=2, Extended Key Usage - Name=130, Extended Key Usage - OID=1.1.1.1.1.1.1.1.1, Template Name=2.2.2.2.2.2.2.2.2.2.2.2.2.2.2.2.2, Days to Expiry=261, Issuer - Fingerprint SHA-256=a0946a7af563dbc3397893f7313410cb9087fcab14566096e7f1b44992251e62, AKI=33:33:33:33:33:33:33:33:33:33:33:33:33:33:33:33:33:33:33:33, HostIdentityGroup=Endpoint Identity Groups:Unknown, Model Name=9200, Network Device Profile=Cisco, Location=Location#All Locations#EU#France#RENNES, Device Type=Device Type#All Device Types#Wired#Switch#Cisco, IPSEC=IPSEC#Is IPSEC Device#No, distinguishedName=CN=TEST-NAME-01,OU=Laptops,OU=Computers,OU=RUM,DC=xxx,DC=infra,DC=xxxxx, ExternalGroups=S-1-2-3-4-5-6-7,#15
0003361015 2 0 2025-05-07 14:29:08.974 +02:00 0051006044 80002 INFO Profiler: Profiler EndPoint profiling event occurred, ConfigVersionId=183, OperatingSystem=Windows 11 Entreprise, EndpointCertainityMetric=50, EndpointIPAddress=1.2.3.4, EndpointMacAddress=AA:BB:CC:DD:EE:FF, EndpointMatchedPolicy=Windows11-Workstation, EndpointOUI=Intel Corporate, EndpointPolicy=Windows11-Workstation, EndpointProperty=chaddr=AA:BB:CC:DD:EE:FF,dhcp-class-identifier=MSFT 5.0,PolicyVersion=24,dhcp-message-type=DHCPREQUEST,EndPointPolicyID=57f40927-3b0a-46b8-9f03-78d47e1383c4,LogicalProfile=,client-fqdn=abcdef.example.local,EndPointVersion=340,FirstCollection=1744718839328,CacheUpdateTime=1746620948973,StaticAssignment=false,NmapScanCount=0,PostureExpiry=,hlen=6,AD-Operating-System=Windows 11 Entreprise,AD-Join-Point=EXAMPLE.LOCAL,PortalUser=,ciaddr=0.0.0.0,BYODRegistration=Unknown,dhcp-requested-address=1.2.3.4,Total Certainty Factor=50,MDMServerID=,
Oct 27 15:20:43 HOST-01 CISE_RADIUS_Accounting 0001042079 1 0 2025-10-27 15:20:43.919 +01:00 0015337799 3002 NOTICE Radius-Accounting: RADIUS Accounting watchdog update, ConfigVersionId=11, Device IP Address=1.2.3.4, UserName=user1, NetworkDeviceName=DEVICE-02, User-Name=user1, NAS-IP-Address=1.2.3.4, NAS-Port=42, Service-Type=Framed, Framed-IP-Address=1.2.3.4, Class=CACS:000000000000000000000000:HOST-01/000000000/000000, Called-Station-ID=user1:, Calling-Station-ID=user1, Acct-Status-Type=Interim-Update, Acct-Delay-Time=0, Acct-Input-Octets=921941396, Acct-Output-Octets=0, Acct-Session-Id=0000000000000000, Acct-Authentic=RADIUS, Acct-Session-Time=570009, Acct-Input-Packets=0, Acct-Output-Packets=35, Acct-Input-Gigawords=922518720, Acct-Output-Gigawords=28, Event-Timestamp=1761574843, NAS-Port-Type=Ethernet, cisco-av-pair=audit-session-id=000000000000000000000000, AcsSessionID=HOST-01/000000000/000000, SelectedAccessService=Default Network Access, RequestLatency=2, Step=11004, Step=11017, Step=15049, Step=15008, Step=22094, Step=11005, NetworkDeviceGroups=Location#All Locations#SITE-02, NetworkDeviceGroups=Device Type#All Device Types#SW_Vendor_Site, NetworkDeviceGroups=IPSEC#Is IPSEC Device#No, CPMSessionID=000000000000000000000000, StepLatency=1=0;2=0;3=1;4=0;5=0, TotalAuthenLatency=2, ClientLatency=0, Network Device Profile=Cisco, Location=Location#All Locations#SITE-02, Device Type=Device Type#All Device Types#SW_Vendor_Site, IPSEC=IPSEC#Is IPSEC Device#No,
CISE_RADIUS_Accounting 0000493168 3 2 NetworkDeviceGroups=IPSEC#Is IPSEC Device#No, NetworkDeviceGroups=Device Type#All Device Types, CPMSessionID=111111111111111111111111, TotalAuthenLatency=2, ClientLatency=0, Model Name=Unknown, Software Version=Unknown, Network Device Profile=Cisco, Location=Location#All Locations#DC1, Device Type=Device Type#All Device Types, IPSEC=IPSEC#Is IPSEC Device#No, #15
CISE_RADIUS_Accounting 0000493146 3 1 cisco-av-pair=dc-device-name=device_01, cisco-av-pair=dc-device-class-tag=Android-Device:Android, cisco-av-pair=dc-certainty-metric=30, cisco-av-pair=11:11:11:11:11:11:11:11:11:11:11:00:00:00:01:00:00:00:00:00:00:00, cisco-av-pair=dc-protocol-map=9, cisco-av-pair=http-tlv=User-Agent=Useragent/1.6.0 (Linux; U; Android 4.4.2; ALR-H450 Build/KOT49H), cisco-av-pair=dhcp-option=host-name=device_01, cisco-av-pair=dhcp-option=dhcp-class-identifier=dhcpcd-5.5.6, cisco-av-pair=dhcp-option=dhcp-parameter-request-list=1, 33, 3, 6, 15, 28, 51, 58, 59, cisco-av-pair=audit-session-id=6BF9680A001DC135219AFBFD, cisco-av-pair=vlan-id=2001, cisco-av-pair=method=mab, cisco-av-pair=cts:security-group-tag=0006, cisco-av-pair=cisco-wlan-ssid=C-Guest, cisco-av-pair=wlan-profile-name=C-Guest-CWA, Airespace-Wlan-Id=40, AcsSessionID=HOST_01/549140223/473883, SelectedAccessService=Default Network Access,#15
0000050179 9 4 Subject - Common Name=EXAMPLE, Subject Alternative Name=EXAMPLE.intra.example.net, Subject - Organization Unit=Std, Subject - Organization Unit=Abc, Subject - Organization Unit=Def, CPMSessionID=REDACTED, EndPointMACAddress=02-00-00-00-00-01, PostureAssessmentStatus=NotApplicable, EndPointMatchedProfile=Unknown, ISEPolicySetName=Policy 802.1X, IdentitySelectionMatchedRule=Default,
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake Cisco ISE. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x Cisco ISE on ATT&CK Navigator
Burp Suite Tool Detected
Burp Suite is a cybersecurity tool. When used as a proxy service, its purpose is to intercept packets and modify them to send them to the server. Burp Collaborator is a network service that Burp Suite uses to help discover many kinds of vulnerabilities (vulnerabilities scanner).
- Effort: intermediate
CVE-2020-0688 Microsoft Exchange Server Exploit
Detects the exploitation of CVE-2020-0688. The POC exploit a .NET serialization vulnerability in the Exchange Control Panel (ECP) web page. The vulnerability is due to Microsoft Exchange Server not randomizing the keys on a per-installation basis resulting in them using the same validationKey and decryptionKey values. With knowledge of these, values an attacker can craft a special viewstate to use an OS command to be executed by NT_AUTHORITY\SYSTEM using .NET deserialization. To exploit this vulnerability, an attacker needs to leverage the credentials of an account it had already compromised to authenticate to OWA.
- Effort: elementary
CVE-2020-17530 Apache Struts RCE
Detects the exploitation of the Apache Struts RCE vulnerability (CVE-2020-17530).
- Effort: intermediate
CVE-2021-20021 SonicWall Unauthenticated Administrator Access
Detects the exploitation of SonicWall Unauthenticated Admin Access.
- Effort: advanced
CVE-2021-20023 SonicWall Arbitrary File Read
Detects Arbitrary File Read, which can be used with other vulnerabilities as a mean to obtain outputs generated by attackers, or sensitive data.
- Effort: advanced
CVE-2021-22893 Pulse Connect Secure RCE Vulnerability
Detects potential exploitation of the authentication by-pass vulnerability that can allow an unauthenticated user to perform remote arbitrary file execution on the Pulse Connect Secure gateway. It is highly recommended to apply the Pulse Secure mitigations and seach for indicators of compromise on affected servers if you are in doubt over the integrity of your Pulse Connect Secure product.
- Effort: intermediate
Cisco Identity Services Engine Configuration Changed
Cisco Identity Services Engine (ISE) has detected a device configuration changed (Added, Changed or Deleted). This should be reviewed in order to check if this an expected admin action.
- Effort: master
Correlation Potential DNS Tunnel
Detects domain name which is longer than 62 characters and requested at least 50 times in a 10 minutes range time. Long domain names are distinctive of DNS tunnels.
- Effort: advanced
Covenant Default HTTP Beaconing
Detects potential Covenant communications through the user-agent and specific urls
- Effort: intermediate
Cryptomining
Detection of domain names potentially related to cryptomining activities.
- Effort: master
Detect requests to Konni C2 servers
This rule detects requests to Konni C2 servers. These patterns come from an analysis done in 2022, September.
- Effort: elementary
Discord Suspicious Download
Discord is a messaging application. It allows users to create their own communities to share messages and attachments. Those attachments have little to no overview and can be downloaded by almost anyone, which has been abused by attackers to host malicious payloads.
- Effort: advanced
Dynamic DNS Contacted
Detect communication with dynamic dns domain. This kind of domain is often used by attackers. This rule can trigger false positive in non-controlled environment because dynamic dns is not always malicious.
- Effort: master
EvilProxy Phishing Domain
Detects subdomains potentially generated by the EvilProxy adversary-in-the-middle phishing platform. Inspect the other subdomains of the domain to identify the landing page, and determine if the user submitted credentials. This rule has a small percentage of false positives on legitimate domains.
- Effort: intermediate
Exfiltration Domain
Detects traffic toward a domain flagged as a possible exfiltration vector.
- Effort: master
Koadic MSHTML Command
Detects Koadic payload using MSHTML module
- Effort: intermediate
Nimbo-C2 User Agent
Nimbo-C2 Uses an unusual User-Agent format in its implants.
- Effort: intermediate
Possible Malicious File Double Extension
Detects request to potential malicious file with double extension
- Effort: elementary
Potential Bazar Loader User-Agents
Detects potential Bazar loader communications through the user-agent
- Effort: elementary
Potential DNS Tunnel
Detects domain name which is longer than 62 characters. Long domain names are distinctive of DNS tunnels.
- Effort: advanced
Potential Lemon Duck User-Agent
Detects LemonDuck user agent. The format used two sets of alphabetical characters separated by dashes, for example "User-Agent: Lemon-Duck-[A-Z]-[A-Z]".
- Effort: elementary
ProxyShell Microsoft Exchange Suspicious Paths
Detects suspicious calls to Microsoft Exchange resources, in locations related to webshells observed in campaigns using this vulnerability.
- Effort: elementary
Raccoon Stealer 2.0 Legitimate Third-Party DLL Download URL
Detects Raccoon Stealer 2.0 malware downloading legitimate third-party DLLs from its C2 server. These legitimate DLLs are used by the information stealer to collect data on the compromised hosts.
- Effort: elementary
Remote Access Tool Domain
Detects traffic toward a domain flagged as a Remote Administration Tool (RAT).
- Effort: master
Remote Monitoring and Management Software - AnyDesk
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool AnyDesk.
- Effort: master
Remote Monitoring and Management Software - Atera
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool Atera.
- Effort: master
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
Sekoia.io EICAR Detection
Detects observables in Sekoia.io CTI tagged as EICAR, which are fake samples meant to test detection.
- Effort: master
Suspicious Download Links From Legitimate Services
Detects users clicking on Google docs links to download suspicious files. This technique was used a lot by Bazar Loader in the past.
- Effort: intermediate
Suspicious TOR Gateway
Detects suspicious TOR gateways. Gateways are often used by the victim to pay and decrypt the encrypted files without installing TOR. Tor intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: advanced
Suspicious URI Used In A Lazarus Campaign
Detects suspicious requests to a specific URI, usually on an .asp page. The website is often compromised.
- Effort: intermediate
TOR Usage Generic Rule
Detects TOR usage globally, whether the IP is a destination or source. TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
Telegram Bot API Request
Detects suspicious DNS queries to api.telegram.org used by Telegram Bots of any kind
- Effort: advanced
TrevorC2 HTTP Communication
Detects TrevorC2 HTTP communication based on the HTTP request URI and the user-agent.
- Effort: elementary
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Authentication logs |
There's an authentification audit, control and diagnostic |
Network device configuration |
Changing conf of devices usually by the admin |
Web logs |
Cisco ISE logs provide information about the connected client and the requested resource |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | `` |
| Category | authentication, configuration, network |
| Type | change, info |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "0003360952 1 0 2025-05-07 14:27:57.047 +02:00 0051005548 25002 INFO AD-Connector: ISE server TGT refresh succeeded, AD-Account-Name=JOHNDOE$@EXAMPLE.LOCAL, AD-Domain=EXAMPLE.LOCAL, AD-Log-Id=1234567890/1234567,",
"event": {
"category": [
"authentication"
],
"reason": "ISE server TGT refresh succeeded",
"type": [
"info"
]
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"user": [
"JOHNDOE$@EXAMPLE.LOCAL"
]
},
"user": {
"domain": "EXAMPLE.LOCAL",
"name": "JOHNDOE$@EXAMPLE.LOCAL"
}
}
{
"message": "0003901877 1 0 2025-05-07 14:29:46.982 +02:00 0723317473 61026 NOTICE EAP-TLS: Shutdown secure connection with TLS peer, ConfigVersionId=360, PeerAddress=AA-BB-CC-DD-EE-FF, PeerName=CN=example.com, UniqueConnectionIdentifier =2ce4ef7a-0575-482b-8ed5-b3b068e873a1, ShutdownReason =ClosedByISE,",
"event": {
"category": [
"network"
],
"reason": "Shutdown secure connection with TLS peer",
"type": [
"info"
]
},
"destination": {
"address": "example.com",
"domain": "example.com",
"mac": "AA:BB:CC:DD:EE:FF",
"registered_domain": "example.com",
"top_level_domain": "com"
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"hosts": [
"example.com"
]
}
}
{
"message": "CISE_Administrative_and_Operational_Audit 0026935732 1 0 2025-10-23 14:26:49.538 +02:00 0264007760 51000 NOTICE Administrator-Login: Administrator authentication failed, ConfigVersionId=118, AdminInterface=GUI, AdminIPAddress=1.2.3.4, AdminName=jdoe, OperationMessageText=Authentication failed due to invalid user or password\\, or account is disabled/locked,",
"event": {
"category": [
"network"
],
"reason": "Administrator authentication failed",
"type": [
"info"
]
},
"cisco": {
"ise": {
"type": "CISE_Administrative_and_Operational_Audit"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"jdoe"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"name": "jdoe"
}
}
{
"message": "0001514749 7 3 SelectedAuthenticationIdentityStores=Internal Endpoints, AuthenticationStatus=AuthenticationPassed, NetworkDeviceGroups=Location#All Locations#H7, NetworkDeviceGroups=Device Type#All Device Types#Cisco_3650, NetworkDeviceGroups=Groupe Imprimantes#Groupe Imprimantes, NetworkDeviceGroups=APs Indoor ou Outdoor#Groupe APs, IdentityPolicyMatchedRule=Dot1X, AuthorizationPolicyMatchedRule=Some rule, EapTunnel=EAP-FAST, EapAuthentication=EAP-MSCHAPv2, cisco-av-pair=AuthenticationIdentityStore=AD1, cisco-av-pair=FQSubjectName=000000-000-0000-00000000000#host/test, cisco-av-pair=UniqueSubjectID=XXXXXXXXXXXXXXXXXXXXX, CPMSessionID=TestSessionId, EndPointMACAddress=02:00:00:00:00:00, PostureAssessmentStatus=NotApplicable, EndPointMatchedProfile=Unknown, EapChainingResult=User failed and machine succeeded, ISEPolicySetName=WIRELESS_1X_DFS, IdentitySelectionMatchedRule=Dot1X,#015",
"event": {
"category": [
"authentication"
],
"outcome": "success",
"reason": "User failed and machine succeeded",
"type": [
"info"
]
},
"cisco": {
"ise": {
"auth_method": "EAP-MSCHAPv2",
"device": {
"profile": "Unknown"
},
"location": "APs Indoor ou Outdoor#Groupe APs",
"policy": "WIRELESS_1X_DFS"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"user": [
"Unknown"
]
},
"rule": {
"name": "Dot1X"
},
"source": {
"mac": "02:00:00:00:00:00"
},
"user": {
"name": "Unknown"
}
}
{
"message": "0000248509 3 0 2025-02-18 14:34:01.264 +01:00 0005365098 5400 NOTICE Failed-Attempt: Authentication failed, ConfigVersionId=88, Device IP Address=3.4.5.6, Device Port=53874, DestinationIPAddress=5.6.7.8, DestinationPort=1812, RadiusPacketType=AccessRequest, UserName=john.doe, Protocol=Radius, NetworkDeviceName=WLAN, User-Name=john.doe, NAS-IP-Address=2.3.4.5, NAS-Port=1656127488, Called-Station-ID=1.2.3.4, Calling-Station-ID=192.0.2.1, NAS-Port-Type=Virtual, Tunnel-Client-Endpoint=(tag=0) 192.0.2.1, cisco-av-pair=mdm-tlv=device-platform=win, cisco-av-pair=mdm-tlv=device-mac=61-05-38-5c-f8-bd, cisco-av-pair=mdm-tlv=device-platform-version=10.0.26100 , cisco-av-pair=mdm-tlv=device-public-mac=61-05-38-5c-f8-bd, cisco-av-pair=mdm-tlv=device-type=Default string Default string, cisco-av-pair=mdm-tlv=ac-user-agent=AnyConnect Windows 4.6.03049,",
"event": {
"category": [
"network"
],
"reason": "Authentication failed",
"type": [
"info"
]
},
"cisco": {
"ise": {
"network": {
"device_name": "WLAN"
},
"observer": {
"interface": {
"type": "Virtual"
}
}
}
},
"destination": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 1812
},
"network": {
"protocol": "Radius"
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"ip": [
"1.2.3.4",
"192.0.2.1"
],
"user": [
"john.doe"
]
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1"
},
"user": {
"name": "john.doe"
}
}
{
"message": "Dec 9 17:30:23 example CISE_Passed_Authentications 0000453439 1 0 2025-12-09 17:30:23.365 +01:00 0007121364 5200 NOTICE Passed-Authentication: Authentication succeeded, ConfigVersionId=10, Device IP Address=1.2.3.4, DestinationIPAddress=5.6.7.8, DestinationPort=1812, UserName=JOHNDOE$@example.local, Protocol=Radius, NetworkDeviceName=DEVICE_NAME, User-Name=host/JOHNDOE.example.local, NAS-IP-Address=1.2.3.4, NAS-Port=1, Service-Type=Framed, Framed-MTU=1400, State=64CPMSessionID=abc12345;36SessionID=example/111111111/222222;, Called-Station-ID=02-00-00-00-00-01:InterneTLS, Calling-Station-ID=02-00-00-00-00-02, NAS-Identifier=02-00-00-00-00-01:vap4, Acct-Session-Id=ABCDEF1234567890, Acct-Multi-Session-Id=123456890ABCDEF, NAS-Port-Type=Wireless - IEEE 802.11, Connect-Info=CONNECT 54.00 Mbps / 802.11ax / RSSI: 22 / Channel: 36, undefined-186=00:01:02:04, undefined-187=00:01:02:04, undefined-188=00:01:02:01, NetworkDeviceProfileName=Cisco, NetworkDeviceProfileId=33333333-3333-3333-3333-333333333333, IsThirdPartyDeviceFlow=false, RadiusFlowType=Wireless802_1x, SSID=02-00-00-00-00-01:InterneTLS, AcsSessionID=example/111111111/222222, AuthenticationIdentityStore=AD_TEST, AuthenticationMethod=x509_PKI, SelectedAccessService=Default Network Access, SelectedAuthorizationProfiles=Cisco_VLAN_WiFi_INT_WW, IsMachineAuthentication=true, RequestLatency=61, IdentityGroup=Endpoint Identity Groups:Profiled, Step=11001, Step=11017, Step=11117, Step=15049, Step=15008, Step=15048, Step=11507, Step=12500, Step=11006, Step=11001, Step=11018, Step=12502, Step=61025, Step=12800, Step=12545, Step=12542, Step=12805, Step=12806, Step=12807, Step=12808, Step=12809, Step=12810, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=12810, Step=12571, Step=12571, Step=12811, Step=12812, Step=12813, Step=12803, Step=12804, Step=12801, Step=12802, Step=12816, Step=12509, Step=12505, Step=11006, Step=11001, Step=11018, Step=12504, Step=15041, Step=15048, Step=22072, Step=22071, Step=15013, Step=24433, Step=24325, Step=24313, Step=24319, Step=24323, Step=24700, Step=22037, Step=12506, Step=61026, Step=15036, Step=24209, Step=24211, Step=15048, Step=24433, Step=24355, Step=24435, Step=15048, Step=15048, Step=15048, Step=15016, Step=22081, Step=22080, Step=11503, Step=11002, SelectedAuthenticationIdentityStores=Preloaded_Certif_Profile_TEST, AuthenticationStatus=AuthenticationPassed, NetworkDeviceGroups=Location#All Locations#Nantes, NetworkDeviceGroups=Device Type#All Device Types#AP_EXAMPLE, NetworkDeviceGroups=IPSEC#Is IPSEC Device#No, IdentityPolicyMatchedRule=Dot1X, AuthorizationPolicyMatchedRule=USER_WIFI_INTERNE_TLS, EapAuthentication=EAP-TLS, cisco-av-pair=AuthenticationIdentityStore=AD_TEST, cisco-av-pair=FQSubjectName=44444444-4444-4444-4444-444444444444#lap-12345$@example.local, cisco-av-pair=UniqueSubjectID=11111111111111111111aaaaaaaaaaaaaaaaaaaa, Serial Number=00 01 02 03 04 05 06 07 08 09 0A 0B 0C 0D 0E 0E 10 11 12, Subject - Common Name=JOHNDOE.example.local, Subject Alternative Name=JOHNDOE.example.local, CPMSessionID=abc12345, EndPointMACAddress=02-00-00-00-00-02, PostureAssessmentStatus=NotApplicable, EndPointMatchedProfile=Intel-Device, ISEPolicySetName=REDACTED, IdentitySelectionMatchedRule=Dot1X, StepLatency=1=0;2=0;3=0;4=1;5=0;6=1;7=0;8=0;9=30;10=0;11=1;12=0;13=0;14=0;15=0;16=1;17=0;18=0;19=25;20=0;21=0;22=0;23=0;24=37;25=0;26=0;27=0;28=0;29=15;30=0;31=0;32=0;33=0;34=15;35=0;36=0;37=0;38=0;39=16;40=0;41=1;42=0;43=0;44=15;45=0;46=0;47=0;48=0;49=170;50=0;51=0;52=0;53=0;54=16;55=0;56=0;57=0;58=0;59=15;60=0;61=1;62=0;63=0;64=0;65=1;66=2;67=0;68=0;69=0;70=0;71=0;72=0;73=0;74=0;75=1;76=33;77=0;78=1;79=0;80=0;81=1;82=0;83=0;84=0;85=4;86=0;87=0;88=0;89=1;90=0;91=0;92=0;93=0;94=1;95=3;96=4;100=3;101=0;102=0;103=1;104=0;105=0;106=0;107=1, MFCInfoHardwareManufacturer=Intel Corporation, MFCInfoHardwareModel=Intel-Device, MFCInfoEndpointType=Workstation , AD-Host-Resolved-Identities=JOHNDOE$@example.local, AD-Host-Candidate-Identities=JOHNDOE$@example.local, AD-Host-Join-Point=TEST.LOCAL, StepData=5= DEVICE.Location, StepData=63=certificate for JOHNDOE.example.local, StepData=64=certificate for REDACTED, StepData=80= Normalised Radius.RadiusFlowType, StepData=81=All_User_ID_Stores, StepData=83=AD_TEST, StepData=84=AD_TEST, StepData=85=CN=JOHNDOE.example.local, JOHNDOE.example.local, JOHNDOE.example.local, StepData=86=example.local, StepData=87=example.local, StepData=89=AD_TEST, StepData=96= EndPoints.EndPointPolicy, StepData=0=AD_TEST, StepData=1=example.local, StepData=2=AD_TEST, StepData=100= AD_TEST.ExternalGroups, StepData=101= DEVICE.Device Type, StepData=102= Radius.Called-Station-ID, TotalAuthenLatency=417, ClientLatency=356, AD-Host-Resolved-DNs=CN=JOHNDOE,OU=HYBRID,OU=ORDINATEURS,DC=TEST,DC=local, AD-Host-DNS-Domain=example.local, AD-Groups-Names=example.local/SYSTEME/EXAMPLE/TEST, AD-Host-NetBios-Name=TEST, IsMachineIdentity=true, AD-Host-SamAccount-Name=JOHNDOE$, AD-Host-Qualified-Name=JOHNDOE$@example.local, allowEasyWiredSession=false, TLSCipher=ECDHE-RSA-AES256-GCM-SHA384, TLSVersion=TLSv1.2, DTLSSupport=Unknown, Subject=CN=JOHNDOE.example.local, Subject Alternative Name - DNS=JOHNDOE.example.local, Issuer=CN=REDACTED,DC=TEST,DC=local, Issuer - Common Name=REDACTED, Issuer - Domain Component=TEST, Issuer - Domain Component=local, Key Usage=0, Key Usage=2, Extended Key Usage - Name=138, Extended Key Usage - Name=132, Extended Key Usage - Name=130, Extended Key Usage - OID=1.3.6.1.4.1.311.10.3.4, Extended Key Usage - OID=1.3.6.1.5.5.7.3.4, Extended Key Usage - OID=1.3.6.1.5.5.7.3.2, Template Name=1.3.6.1.4.1.311.21.8.12772041.905510.6439332.852183.9969916.94.7965419.54627, Days to Expiry=255, Issuer - Fingerprint SHA-256=01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b, AKI=00:11:22:33:44:55:66:77:88:99:AA:BB:CC:DD:EE:FF:01:02:03:04, HostIdentityGroup=Endpoint Identity Groups:Profiled, ExternalGroups=S-1-2-3, Network Device Profile=Cisco, Location=Location#All Locations#Nantes, Device Type=Device Type#All Device Types#AP_EXAMPLE, IPSEC=IPSEC#Is IPSEC Device#No, EndPointPolicy=55555555-5555-5555-5555-555555555555, Name=Endpoint Identity Groups:Profiled, Response={User-Name=JOHNDOE$@example.local; Class=CACS:abc12345:example/111111111/222222; Tunnel-Type=(tag=1) VLAN; Tunnel-Medium-Type=(tag=1) 802; Tunnel-Private-Group-ID=(tag=1) 157; MS-MPPE-Send-Key=****; MS-MPPE-Recv-Key=****; LicenseTypes=1; },",
"event": {
"category": [
"authentication"
],
"outcome": "success",
"reason": "{User-Name=JOHNDOE$@example.local; Class=CACS:abc12345:example/111111111/222222; Tunnel-Type=(tag=1) VLAN; Tunnel-Medium-Type=(tag=1) 802; Tunnel-Private-Group-ID=(tag=1) 157; MS-MPPE-Send-Key=****; MS-MPPE-Recv-Key=****; LicenseTypes=1; }",
"type": [
"info"
]
},
"cisco": {
"ise": {
"acs_session_id": "example/111111111/222222",
"auth_method": "EAP-TLS",
"device": {
"profile": "Intel-Device"
},
"is_machine_identity": true,
"location": "IPSEC#Is IPSEC Device#No",
"nas": {
"identifier": "02-00-00-00-00-01:vap4"
},
"network": {
"device_name": "DEVICE_NAME"
},
"observer": {
"interface": {
"type": "Wireless - IEEE 802.11"
}
},
"policy": "REDACTED",
"step_data": {
"5_code": "DEVICE.Location"
},
"type": "CISE_Passed_Authentications"
}
},
"destination": {
"address": "5.6.7.8",
"ip": "5.6.7.8",
"mac": "02:00:00:00:00:01",
"port": 1812
},
"device": {
"id": "JOHNDOE.example.local"
},
"dns": {
"question": {
"registered_domain": "example.local"
}
},
"host": {
"name": "JOHNDOE.example.local"
},
"network": {
"protocol": "Radius"
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"ip": [
"1.2.3.4",
"5.6.7.8"
],
"user": [
"JOHNDOE$@example.local"
]
},
"rule": {
"name": "Dot1X"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:02"
},
"tls": {
"client": {
"x509": {
"issuer": {
"common_name": "REDACTED"
},
"subject": {
"alternative_names": [
"JOHNDOE.example.local"
],
"common_name": "JOHNDOE.example.local"
}
}
}
},
"user": {
"name": "JOHNDOE$@example.local"
}
}
{
"message": "0000005921 7 5 02-22-33-44-55-66:EVENT_REASON\\,dhcp-parameter-request-list=1\\, 3\\, 6\\, 15\\, 31\\, 33\\, 43\\, 44\\, 46\\, 47\\, 119\\, 121\\, 249\\, 252\\,OperatingSystem=Windows\\,PostureApplicable=Yes\\,User-Fetch-Department=\\,AD-Last-Fetch-Time=1759879885138\\,Issuer=CN=COMPANY-SUB-CA\\\\OU=DSI\\\\O=COMPANY\\\\L=RENNES\\\\C=FR\\,NmapSubnetScanID=0\\,AD-Host-DNS-Domain=domain.example.com\\,Device Identifier=\\,Airespace-Wlan-Id=12\\,ipv6=\\,Issuer - Organization=COMPANY\\,TotalAuthenLatency=2\\,MatchedPolicyID=11111111-1111-1111-1111-111111111111\\,Service-Type=Framed\\,op=BOOTREQUEST\\,UserName=j.doe@domain.example.com\\,FeedService=false\\,TLSVersion=TLSv1.2\\,AD-Host-NetBios-Name=DOMAIN\\,Issuer - Location=RENNES\\,SelectedAuthorizationProfiles=PermitAccess\\,host-name=example.com\\,COMPANY_LAN=COMPANY_LAN#COMPANY_LAN\\,Subject=CN=example.com.DOMAIN.example.com\\,",
"event": {
"category": [
"network"
],
"reason": "EVENT_REASON",
"type": [
"info"
]
},
"cisco": {
"ise": {
"dhcp": {
"message_type": "BOOTREQUEST",
"parameter_request_list": "1\\, 3\\, 6\\, 15\\, 31\\, 33\\, 43\\, 44\\, 46\\, 47\\, 119\\, 121\\, 249\\, 252"
}
}
},
"dns": {
"question": {
"registered_domain": "domain.example.com"
}
},
"host": {
"name": "example.com",
"os": {
"full": "Windows"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"user": [
"j.doe@domain.example.com"
]
},
"rule": {
"id": "11111111-1111-1111-1111-111111111111"
},
"source": {
"mac": "02:22:33:44:55:66"
},
"tls": {
"client": {
"x509": {
"issuer": {
"common_name": "COMPANY-SUB-CA",
"country": "FR",
"locality": "RENNES",
"organization": "COMPANY",
"organizational_unit": "DSI"
},
"subject": {
"common_name": "example.com.DOMAIN.example.com"
}
}
}
},
"user": {
"name": "j.doe@domain.example.com"
}
}
{
"message": "0085509171 4 0 2026-01-07 19:51:20.282 +00:00 5510785544 5202 NOTICE Device-Administration: Command Authorization succeeded, ConfigVersionId=242, Device IP Address=1.1.1.1, DestinationIPAddress=2.2.2.2, DestinationPort=49, UserName=Username1, CmdSet=[ CmdAV=show CmdArgAV=ipv6 CmdArgAV=mld CmdArgAV=snooping CmdArgAV=<cr> ], Protocol=Tacacs, MatchedCommandSet=AllowAllCommands, NetworkDeviceName=example.local, Type=Authorization, Privilege-Level=1, Authen-Type=ASCII, Service=None, User=Username1, Port=tty1, Remote-Address=3.3.3.3, Authen-Method=None, Service-Argument=shell, NetworkDeviceProfileId=11111111-1111-1111-1111-111111111111, AcsSessionID=EXAMPLE/11111/22222, AuthenticationIdentityStore=IT_AD, AuthenticationMethod=Lookup, SelectedAccessService=Default Device Admin, SelectedCommandSet=AllowAllCommands, IsMachineAuthentication=false, RequestLatency=90, Step=13005, Step=15049, Step=15008, Step=15048, Step=15041,",
"event": {
"category": [
"authentication"
],
"reason": "Command Authorization succeeded",
"type": [
"info"
]
},
"cisco": {
"ise": {
"acs_session_id": "EXAMPLE/11111/22222",
"auth_method": "ASCII",
"cmd_line": "[ CmdAV=show CmdArgAV=ipv6 CmdArgAV=mld CmdArgAV=snooping CmdArgAV=<cr> ]",
"network": {
"device_name": "example.local"
},
"policy": "Default Device Admin",
"privilege_level": "1"
}
},
"destination": {
"address": "2.2.2.2",
"ip": "2.2.2.2",
"port": 49
},
"network": {
"protocol": "Tacacs"
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"ip": [
"1.1.1.1",
"2.2.2.2"
],
"user": [
"Username1"
]
},
"source": {
"address": "1.1.1.1",
"ip": "1.1.1.1"
},
"user": {
"name": "Username1"
}
}
{
"message": "INFO: Configuration Changed: Admin=john.doe; Object Type=EPPurgeScheduler; Object Name=f36afcff-e3af-4a70-99c0-5e5304c1c336",
"event": {
"category": [
"configuration"
],
"reason": "Configuration Changed",
"type": [
"change"
]
},
"cisco": {
"ise": {
"config_action": "Changed",
"config_object": {
"name": "f36afcff-e3af-4a70-99c0-5e5304c1c336",
"type": "EPPurgeScheduler"
}
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"user": [
"john.doe"
]
},
"user": {
"name": "john.doe"
}
}
{
"message": "Oct 27 14:29:31 HOST-01 CISE_Failed_Attempts 0001027727 1 0 2025-10-27 14:29:31.301 +01:00 0015075255 5400 NOTICE Failed-Attempt: Authentication failed, ConfigVersionId=11, Device IP Address=1.2.3.4, Device Port=42568, DestinationIPAddress=1.2.3.4, DestinationPort=1812, RadiusPacketType=AccessRequest, UserName=user1, Protocol=Radius, NetworkDeviceName=DEVICE-01, User-Name=aabbccddeeff, NAS-IP-Address=1.2.3.4, NAS-Port=19, Service-Type=Call Check, Called-Station-ID=user1:, Calling-Station-ID=user1, NAS-Port-Type=Ethernet, cisco-av-pair=audit-session-id=000000000000000000000000, OriginalUserName=aabbccddeeff, NetworkDeviceProfileName=Cisco, NetworkDeviceProfileId=00000000-0000-0000-0000-000000000000, IsThirdPartyDeviceFlow=false, RadiusFlowType=WiredMAB, SSID=user1:, AcsSessionID=HOST-01/000000000/000000, AuthenticationIdentityStore=Internal Endpoints, AuthenticationMethod=Lookup, SelectedAccessService=Default Network Access, SelectedAuthorizationProfiles=DenyAccess, UseCase=Host Lookup, RequestLatency=25, IdentityGroup=Endpoint Identity Groups:Profiled, FailureReason=15039 Rejected per authorization profile, Step=11001, Step=11017, Step=11027, Step=15049, Step=15008, Step=15048, Step=15041, Step=15048, Step=15013, Step=24209, Step=24211, Step=22037, Step=15036, Step=15048, Step=15048, Step=15048, Step=24432, Step=24325, Step=24313, Step=24318, Step=24322, Step=24352, Step=24412, Step=15048, Step=15048, Step=15016, Step=15039, Step=11003, SelectedAuthenticationIdentityStores=Internal Endpoints, NetworkDeviceGroups=Location#All Locations#SITE-01, NetworkDeviceGroups=Device Type#All Device Types#SW_Vendor_Site, NetworkDeviceGroups=IPSEC#Is IPSEC Device#No, IdentityPolicyMatchedRule=MAB, AuthorizationPolicyMatchedRule=Default, cisco-av-pair=AuthenticationIdentityStore=Internal Endpoints, UserType=Host, CPMSessionID=000000000000000000000000, EndPointMACAddress=user1, EndPointMatchedProfile=VENDOR-Device, DeviceRegistrationStatus=notRegistered, ISEPolicySetName=POLICY-01, IdentitySelectionMatchedRule=MAB, StepLatency=1=0;2=1;3=0;4=0;5=0;6=1;7=0;8=1;9=0;10=1;11=0;12=0;13=12;14=5;15=0;23=3;24=0;25=1;26=0;27=0, StepData=5= DEVICE.Location, StepData=7= Normalised Radius.RadiusFlowType, StepData=8=Internal Endpoints, StepData=13= EndPoints.LogicalProfile, StepData=14= EndPoints.EndPointPolicy, StepData=15= DEVICE.Device Type, StepData=0=AD_EXAMPLE, StepData=1=user1, StepData=2=example.local, StepData=3=example.local, StepData=5=ERROR_NO_SUCH_USER, StepData=6=AD_EXAMPLE, StepData=23= AD_EXAMPLE.ExternalGroups, StepData=24= Radius.Called-Station-ID, TotalAuthenLatency=25, ClientLatency=0, DTLSSupport=Unknown, HostIdentityGroup=Endpoint Identity Groups:Profiled, Network Device Profile=Cisco, Location=Location#All Locations#SITE-01, Device Type=Device Type#All Device Types#SW_Vendor_Site, IPSEC=IPSEC#Is IPSEC Device#No, EndPointPolicy=00000000-0000-0000-0000-000000000000, Name=Endpoint Identity Groups:Profiled, Response={RadiusPacketType=AccessReject; AuthenticationResult=Passed; UserName=AA:BB:CC:DD:EE:FF; },",
"event": {
"category": [
"authentication"
],
"reason": "{RadiusPacketType=AccessReject; AuthenticationResult=Passed; UserName=AA:BB:CC:DD:EE:FF; }",
"type": [
"info"
]
},
"cisco": {
"ise": {
"acs_session_id": "HOST-01/000000000/000000",
"audit_session_id": "000000000000000000000000",
"device": {
"profile": "VENDOR-Device"
},
"location": "IPSEC#Is IPSEC Device#No",
"network": {
"device_name": "DEVICE-01"
},
"observer": {
"interface": {
"type": "Ethernet"
}
},
"policy": "POLICY-01",
"step_data": {
"5_code": "DEVICE.Location"
},
"type": "CISE_Failed_Attempts"
}
},
"destination": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"port": 1812
},
"network": {
"protocol": "Radius"
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"rule": {
"name": "MAB"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "AA:BB:CC:DD:EE:FF"
},
"user": {
"name": "user1"
}
}
{
"message": "CISE_Failed_Attempts 0000815086 4 1 SSID=11-22-33-44-55-66, AcsSessionID=HOST_01/552714706/823738, AuthenticationIdentityStore=Internal Endpoints, AuthenticationMethod=Lookup, SelectedAccessService=Selected_Service, SelectedAuthorizationProfiles=DenyAccess, UseCase=Host Lookup, RequestLatency=12, IdentityGroup=Endpoint Identity Groups:Profiled, FailureReason=15039 Rejected per authorization profile, Step=11001, Step=11017, Step=11027, Step=15049, Step=15008, Step=15048, Step=15048, Step=15048, Step=15048, Step=15041, Step=15048, Step=15013, Step=24209, Step=24211, Step=22037, Step=15036, Step=15048, Step=15048, Step=24032, Step=24017, Step=24019, Step=24034, Step=24031, Step=24017, Step=24019, Step=15048, Step=24032, Step=24017, Step=24019, Step=24034, Step=24031, Step=24017, Step=24019, Step=15048, Step=15048, Step=15016, Step=15039, Step=11003, SelectedAuthenticationIdentityStores=Internal Endpoints, NetworkDeviceGroups=Location#All Locations#EU#France#RENNES,#15",
"event": {
"category": [
"authentication"
],
"reason": "15039 Rejected per authorization profile",
"type": [
"info"
]
},
"cisco": {
"ise": {
"acs_session_id": "HOST_01/552714706/823738",
"location": "Location#All Locations#EU#France#RENNES",
"policy": "Selected_Service",
"type": "CISE_Failed_Attempts"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
}
}
{
"message": "CISE_Failed_Attempts 0000815085 5 4 IPSEC=IPSEC#Is IPSEC Device#No, Name=Endpoint Identity Groups:Profiled, Response={RadiusPacketType=AccessReject; AuthenticationResult=Passed; UserName=11:22:33:44:55:66; },#15",
"event": {
"category": [
"network"
],
"reason": "{RadiusPacketType=AccessReject; AuthenticationResult=Passed; UserName=11:22:33:44:55:66; }",
"type": [
"info"
]
},
"cisco": {
"ise": {
"type": "CISE_Failed_Attempts"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"source": {
"mac": "11:22:33:44:55:66"
}
}
{
"message": "0000087238 3 1 AcsSessionID=ISE-CISCO/1111111/222222, AuthenticationIdentityStore=Internal Endpoints, AuthenticationMethod=Lookup, SelectedAccessService=AuthenticationMAB, SelectedAuthorizationProfiles=DenyAccess, UseCase=Host Lookup, RequestLatency=5, IdentityGroup=Endpoint Identity Groups:Unknown, FailureReason=15039 Rejected per authorization profile, Step=11001, Step=11017, Step=11027, Step=15049, Step=15008, Step=15048, Step=15048, Step=15048, Step=15041, Step=15013, Step=24209, Step=24211, Step=22037, Step=15036, Step=15016, Step=15039, Step=11003, SelectedAuthenticationIdentityStores=Internal Endpoints, NetworkDeviceGroups=Device Type#All Device Types#Switch, NetworkDeviceGroups=IPSEC#Is IPSEC Device#No, NetworkDeviceGroups=Location#All Locations, IdentityPolicyMatchedRule=Authentication Rule 1, AuthorizationPolicyMatchedRule=Default, cisco-av-pair=AuthenticationIdentityStore=Internal Endpoints, UserType=Host, CPMSessionID=ABCDEF0123456,",
"event": {
"category": [
"authentication"
],
"reason": "15039 Rejected per authorization profile",
"type": [
"info"
]
},
"cisco": {
"ise": {
"acs_session_id": "ISE-CISCO/1111111/222222",
"location": "Location#All Locations",
"policy": "Default"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"rule": {
"name": "Authentication Rule 1"
}
}
{
"message": "0000089788 3 2 EndPointMACAddress=02-11-22-33-44-55, EndPointMatchedProfile=Unknown, DeviceRegistrationStatus=notRegistered, ISEPolicySetName=MAB, IdentitySelectionMatchedRule=Authentication Rule 1, StepLatency=1=0\\;2=0\\;3=0\\;4=0\\;5=0\\;6=1\\;7=0\\;8=0\\;9=1\\;10=0\\;11=1\\;12=0\\;13=0\\;14=1\\;15=0\\;16=0, StepData=5= DEVICE.Device Type, StepData=6= Radius.NAS-IP-Address, StepData=7= Normalised Radius.RadiusFlowType, StepData=9=Internal Endpoints, TotalAuthenLatency=4, ClientLatency=0, DTLSSupport=Unknown, HostIdentityGroup=Endpoint Identity Groups:Unknown, Network Device Profile=Cisco, Location=Location#All Locations, Device Type=Device Type#All Device Types#Switch, IPSEC=IPSEC#Is IPSEC Device#No, Name=Endpoint Identity Groups:Unknown, Response={RadiusPacketType=AccessReject; AuthenticationResult=Passed; UserName=02:00:00:00:00:00; },",
"event": {
"category": [
"network"
],
"reason": "{RadiusPacketType=AccessReject; AuthenticationResult=Passed; UserName=02:00:00:00:00:00; }",
"type": [
"info"
]
},
"cisco": {
"ise": {
"device": {
"profile": "Unknown"
},
"location": "Location#All Locations",
"policy": "MAB",
"step_data": {
"5_code": "DEVICE.Device Type"
}
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"rule": {
"name": "MAB"
},
"source": {
"mac": "02:11:22:33:44:55"
}
}
{
"message": "INFO: 5 endpoint(s) purged successfully",
"event": {
"reason": "5 endpoint(s) purged successfully",
"type": [
"info"
]
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
}
}
{
"message": "2023-06-07 04:26:17.306 +0200 60198 INFO null: MnT purge event occurred, MESSAGE=completed successfully,",
"event": {
"category": [
"network"
],
"reason": "MnT purge event occurred",
"type": [
"info"
]
},
"cisco": {
"ise": {
"event": {
"outcome": "success"
}
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
}
}
{
"message": "WARN: AcsSyslogContentAaaDiagnostics:: ACTIVE_DIRECTORY_DIAGNOSTIC_TOOL_ISSUES_FOUND need to complete",
"event": {
"category": [
"network"
],
"reason": "AcsSyslogContentAaaDiagnostics:: ACTIVE_DIRECTORY_DIAGNOSTIC_TOOL_ISSUES_FOUND need to complete",
"type": [
"info"
]
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
}
}
{
"message": "INFO: EAP Connection Timeout : Server=example.com; NAS IP Address=1.2.3.4; NAS Identifier=02:00:00:00:00:00:test1",
"event": {
"category": [
"network"
],
"reason": "EAP Connection Timeout",
"type": [
"info"
]
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "example.com",
"domain": "example.com",
"ip": "1.2.3.4",
"mac": "02:00:00:00:00:00",
"registered_domain": "example.com",
"top_level_domain": "com"
}
}
{
"message": "0000738292 7 0 2025-01-09 09:28:49.914 +01:00 0043796555 5200 NOTICE Passed-Authentication: Authentication succeeded, ConfigVersionId=186, Device IP Address=192.0.2.1, DestinationIPAddress=1.2.3.4, DestinationPort=1812, UserName=user1, Protocol=Radius, NetworkDeviceName=MGCUH1-3, User-Name=user1, NAS-IP-Address=192.0.2.1, NAS-Port=1001, Service-Type=Framed, Framed-MTU=1449, State=37CPMSessionID=XXXXXXXXXXXXXX\\;36SessionID=MGDFSISE2/515448264/543038\\;, Called-Station-ID=02:22:33:44:55:66, Calling-Station-ID=02:22:33:44:66:77, NAS-Identifier=MGCUH1-3, NAS-Port-Type=Wireless - IEEE 802.11, NAS-Port-Id=Capwap2, EAP-Key-Name=, cisco-av-pair=service-type=Framed, cisco-av-pair=audit-session-id=XXXXXXXXXXXXXX, cisco-av-pair=method=dot1x, cisco-av-pair=cisco-wlan-ssid=DFS, Airespace-Wlan-Id=5, NetworkDeviceProfileName=Cisco, NetworkDeviceProfileId=aaaaaaaaaaaaaaaaaaaaa,#015",
"event": {
"category": [
"network"
],
"reason": "Authentication succeeded",
"type": [
"info"
]
},
"cisco": {
"ise": {
"audit_session_id": "XXXXXXXXXXXXXX",
"auth_method": "dot1x",
"nas": {
"identifier": "MGCUH1-3"
},
"network": {
"device_name": "MGCUH1-3"
},
"observer": {
"interface": {
"name": "Capwap2",
"type": "Wireless - IEEE 802.11"
}
},
"ssid": "DFS"
}
},
"destination": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "02:22:33:44:55:66",
"port": 1812
},
"network": {
"protocol": "Radius"
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"ip": [
"1.2.3.4",
"192.0.2.1"
],
"user": [
"user1"
]
},
"source": {
"address": "192.0.2.1",
"ip": "192.0.2.1",
"mac": "02:22:33:44:66:77"
},
"user": {
"name": "user1"
}
}
{
"message": "CISE_RADIUS_Accounting 0002391460 1 0 2025-07-30 11:50:34.267 +02:00 0023023046 3002 NOTICE Radius-Accounting: RADIUS Accounting watchdog update, ConfigVersionId=83, Device IP Address=1.2.3.4, UserName=user1, NetworkDeviceName=Test-Network-Device-Name, User-Name=user1, NAS-IP-Address=1.2.3.4, NAS-Port=50107, Framed-IP-Address=3.4.5.6, Class=CACS:0A0D00F90000001402268B53:ise/523393559/11169221, Called-Station-ID=02-00-00-00-00-00, Calling-Station-ID=user1, Acct-Status-Type=Interim-Update, Acct-Delay-Time=0, Acct-Input-Octets=1848852125, Acct-Output-Octets=2808400785, Acct-Session-Id=00000070, Acct-Input-Packets=27991836, Acct-Output-Packets=40488347, Event-Timestamp=1753869011, NAS-Port-Type=Ethernet, NAS-Port-Id=GigabitEthernet0/7, cisco-av-pair=audit-session-id=0A0D00F90000001402268B53, cisco-av-pair=vlan-id=1330, cisco-av-pair=method=mab, AcsSessionID=MGMT-ISE01/0000000000/2185126, SelectedAccessService=Default Network Access, RequestLatency=3, Step=11004, Step=11017, Step=15049, Step=15008, Step=15048, Step=15048, Step=22094, Step=11005, NetworkDeviceGroups=Location#All Locations#Test Test#LAN#ACA, NetworkDeviceGroups=Device Type#All Device Types#Switch#2960L, NetworkDeviceGroups=IPSEC#Is IPSEC Device#No, CPMSessionID=0A0D00F90000001402268B53, StepLatency=1=0\\;2=0\\;3=0\\;4=1\\;5=0\\;6=1\\;7=0, StepData=4= Normalised Radius.TTTTT, StepData=5= Normalised Radius.RadiusFlowType, TotalAuthenLatency=3, ClientLatency=0, Model Name=Unknown, Software Version=Unknown, Network Device Profile=Cisco, Location=Location#All Locations#Test Test#LAN#ACA, Device Type=Device Type#All Device Types#Switch#2960L, IPSEC=IPSEC#Is IPSEC Device#No,",
"event": {
"category": [
"network"
],
"reason": "RADIUS Accounting watchdog update",
"type": [
"info"
]
},
"cisco": {
"ise": {
"acs_session_id": "MGMT-ISE01/0000000000/2185126",
"audit_session_id": "0A0D00F90000001402268B53",
"auth_method": "mab",
"device": {
"ip": "3.4.5.6"
},
"location": "IPSEC#Is IPSEC Device#No",
"network": {
"device_name": "Test-Network-Device-Name"
},
"observer": {
"interface": {
"name": "GigabitEthernet0/7",
"type": "Ethernet"
}
},
"policy": "Default Network Access",
"step_data": {
"5_code": "Normalised Radius.RadiusFlowType"
},
"type": "CISE_RADIUS_Accounting",
"vlan_id": "1330"
}
},
"destination": {
"mac": "02:00:00:00:00:00"
},
"device": {
"model": {
"name": "Unknown"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"name": "user1"
}
}
{
"message": "0000000000 1 0 2025-07-29 14:07:18.047 +02:00 0000000000 51000 NOTICE Administrator-Login: Administrator authentication failed, ConfigVersionId=XX, AdminInterface=GUI, AdminIPAddress=1.2.3.4, AdminName=user1, OperationMessageText=Authentication failed due to invalid user or password, or account is disabled/locked,",
"event": {
"category": [
"network"
],
"reason": "Administrator authentication failed",
"type": [
"info"
]
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"name": "user1"
}
}
{
"message": "CISE_Administrative_and_Operational_Audit 0000000000 1 0 2025-07-29 14:07:18.047 +02:00 0000000000 51000 NOTICE Administrator-Login: Administrator authentication failed, ConfigVersionId=XX, AdminInterface=GUI, AdminIPAddress=1.2.3.4, AdminName=user1, OperationMessageText=Authentication failed due to invalid user or password, or account is disabled/locked,",
"event": {
"category": [
"network"
],
"reason": "Administrator authentication failed",
"type": [
"info"
]
},
"cisco": {
"ise": {
"type": "CISE_Administrative_and_Operational_Audit"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"name": "user1"
}
}
{
"message": "0017407182 7 4 WiFi iPhone-ABC1234 Example Cert\\, iPhone-ABC1234 \\, 11111111-1111-1111-1111-111111111111, StepData=34=a1.example.org, StepData=35=a1.example.org, StepData=36=b1.example.org\\,Domain trust is one-way, StepData=37=example.net\\,Domain trust is one-way, StepData=38=EXAMPLE.LOCAL\\,Domain trust is one-way, StepData=40=ERROR_NO_SUCH_USER, StepData=41=IT_AD, StepData=51= Network Access.NetworkDeviceName, StepData=52= CERTIFICATE.Issuer - Common Name, TotalAuthenLatency=27, ClientLatency=15, IsMachineIdentity=false, allowEasyWiredSession=false, TLSCipher=ECDHE-RSA-AES256-GCM-SHA384, TLSVersion=TLSv1.2, DTLSSupport=Unknown, Subject=CN=WiFi iPhone-ABC1234 Example Cert, Subject Alternative Name - Other Name=iPhone-ABC1234 , Subject Alternative Name - DNS=11111111-1111-1111-1111-111111111111, Issuer=CN=Example Sub CA G2\\,DC=a1\\,DC=example.org, Issuer - Common Name=Example Sub CA G2, Issuer - Domain Component=a1, Issuer - Domain Component=example.org,",
"event": {
"category": [
"network"
],
"reason": "WiFi iPhone-ABC1234 Example Cert\\",
"type": [
"info"
]
},
"cisco": {
"ise": {
"is_machine_identity": false
}
},
"device": {
"id": "11111111-1111-1111-1111-111111111111"
},
"host": {
"name": "iPhone-ABC1234"
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"tls": {
"client": {
"x509": {
"issuer": {
"common_name": "Example Sub CA G2"
},
"subject": {
"common_name": "WiFi iPhone-ABC1234 Example Cert"
}
}
}
}
}
{
"message": "0003023466 4 3 DTLSSupport=Unknown, HostIdentityGroup=Endpoint Identity Groups:Unknown, Model Name=9800-CL, Network Device Profile=Cisco, Location=Location#All Locations#SWE#Azure, Device Type=Device Type#All Device Types#WLC9800, IPSEC=IPSEC#Is IPSEC Device#No, Name=Endpoint Identity Groups:Unknown, Response={UserName=02:00:00:00:00:01; User-Name=02-00-00-00-00-01; Class=CACS:01BCDEF023:ABC/111111/22222; cisco-av-pair=url-redirect-acl=GS-Redirect_ACL; cisco-av-pair=url-redirect=https://REDACTED; cisco-av-pair=profile-name=Unknown; LicenseTypes=1; },",
"event": {
"category": [
"network"
],
"reason": "{UserName=02:00:00:00:00:01; User-Name=02-00-00-00-00-01; Class=CACS:01BCDEF023:ABC/111111/22222; cisco-av-pair-url-redirect-acl=GS-Redirect_ACL; cisco-av-pair-url-redirect=https://REDACTED; cisco-av-pair-profile-name=Unknown; LicenseTypes=1; }",
"type": [
"info"
]
},
"cisco": {
"ise": {
"location": "Location#All Locations#SWE#Azure"
}
},
"device": {
"model": {
"name": "9800-CL"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"source": {
"mac": "02:00:00:00:00:01"
},
"url": {
"domain": "redacted",
"full": "https://REDACTED",
"original": "https://REDACTED",
"port": 443,
"scheme": "https"
}
}
{
"message": "0017407213 1 0 2026-01-22 17:20:22.444 +01:00 1165981159 61025 NOTICE Administrative and Operational Audit: Open secure connection with TLS peer, ConfigVersionId=167, UserName=USERNAME, ISELocalAddress=1.1.1.1:1812, ISEModuleName=EAP_SERVER, ISEServiceName=EAP-TLS Server, PeerAddress=02-00-00-00-00-01, PeerName=iPhone-ABC123 , ConnectionStatus=Succeeded, UniqueConnectionIdentifier =11111111-1111-1111-1111-111111111111,",
"event": {
"category": [
"network"
],
"reason": "Open secure connection with TLS peer",
"type": [
"info"
]
},
"destination": {
"address": "iPhone-ABC123",
"domain": "iPhone-ABC123",
"mac": "02:00:00:00:00:01"
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"hosts": [
"iPhone-ABC123"
],
"user": [
"USERNAME"
]
},
"user": {
"name": "USERNAME"
}
}
{
"message": "0003023463 3 0 2026-01-22 17:20:15.900 +00:00 0196666985 3000 NOTICE Radius-Accounting: RADIUS Accounting start request, ConfigVersionId=226, Device IP Address=2.2.2.2, UserName=02-00-00-00-00-01, NetworkDeviceName=DEVICE_NAME, User-Name=02-00-00-00-00-01, NAS-IP-Address=2.2.2.2, NAS-Port=20012, Framed-IP-Address=1.1.1.1, Class=CACS:01234ABC:ABC/111111/222222, Called-Station-ID=02-00-00-00-00-02, Called-Station-ID=example:abcs, Calling-Station-ID=02-00-00-00-00-01, NAS-Identifier=DEVICE_NAME, Acct-Status-Type=Start, Acct-Delay-Time=0, Acct-Session-Id=00000123, Acct-Authentic=Remote, Event-Timestamp=1769102415, NAS-Port-Type=Wireless - IEEE 802.11, NAS-Port-Id=example, cisco-av-pair=dc-profile-name=Un-Classified Device, cisco-av-pair=dc-device-name=Unknown Device, cisco-av-pair=dc-device-class-tag=Un-Classified Device, cisco-av-pair=dc-certainty-metric=0,",
"event": {
"category": [
"network"
],
"reason": "RADIUS Accounting start request",
"type": [
"info"
]
},
"cisco": {
"ise": {
"auth_method": "Remote",
"certainty_metric": "0",
"device": {
"ip": "1.1.1.1",
"model": {
"class": "Un-Classified Device"
},
"profile": "Un-Classified Device"
},
"nas": {
"identifier": "DEVICE_NAME"
},
"network": {
"device_name": "DEVICE_NAME"
},
"observer": {
"interface": {
"name": "example",
"type": "Wireless - IEEE 802.11"
}
}
}
},
"device": {
"model": {
"name": "Unknown Device"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"ip": [
"2.2.2.2"
],
"user": [
"02-00-00-00-00-01"
]
},
"source": {
"address": "2.2.2.2",
"ip": "2.2.2.2",
"mac": "02:00:00:00:00:01"
},
"user": {
"name": "02-00-00-00-00-01"
}
}
{
"message": "0001514749 7 6 Response={Class=CACS:XXXXXXXXX:asdsa/000000/111111; Tunnel-Type=(tag=1) VLAN; Tunnel-Medium-Type=(tag=1) 802; Tunnel-Private-Group-ID=(tag=1) COMPUTER; EAP-Key-Name=EAP-Key-VALUE; MS-MPPE-Send-Key=****; MS-MPPE-Recv-Key=****; LicenseTypes=1; },#015",
"event": {
"category": [
"network"
],
"reason": "{Class=CACS:XXXXXXXXX:asdsa/000000/111111; Tunnel-Type=(tag=1) VLAN; Tunnel-Medium-Type=(tag=1) 802; Tunnel-Private-Group-ID=(tag=1) COMPUTER; EAP-Key-Name=EAP-Key-VALUE; MS-MPPE-Send-Key=****; MS-MPPE-Recv-Key=****; LicenseTypes=1; }",
"type": [
"info"
]
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
}
}
{
"message": "WARN: Dynamic Authorization Failed for Device : Server=example.com; Calling Station Id=N/A; Network device IP=1.2.3.4; Network Device",
"event": {
"category": [
"network"
],
"reason": "Dynamic Authorization Failed for Device",
"type": [
"info"
]
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "example.com",
"domain": "example.com",
"ip": "1.2.3.4",
"registered_domain": "example.com",
"top_level_domain": "com"
}
}
{
"message": "WARN: Profiler SNMP Request Failure : Server= example.com; NAD Address=1.2.3.4; Error Message=Request timed out.",
"event": {
"category": [
"network"
],
"reason": "Request timed out.",
"type": [
"info"
]
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"hosts": [
"example.com"
],
"ip": [
"1.2.3.4"
]
},
"source": {
"address": "example.com",
"domain": "example.com",
"ip": "1.2.3.4",
"registered_domain": "example.com",
"top_level_domain": "com"
}
}
{
"message": "WARN: TrustSec deploy verification failed to reach NAD.: Device Name=device005.internal.example.org; Device Ip=1.2.3.4; Device login username=admin",
"event": {
"category": [
"network"
],
"reason": "TrustSec deploy verification failed to reach NAD.",
"type": [
"info"
]
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"hosts": [
"device005.internal.example.org"
],
"ip": [
"1.2.3.4"
],
"user": [
"admin"
]
},
"source": {
"address": "device005.internal.example.org",
"domain": "device005.internal.example.org",
"ip": "1.2.3.4",
"registered_domain": "example.org",
"subdomain": "device005.internal",
"top_level_domain": "org"
},
"user": {
"name": "admin"
}
}
{
"message": "CISE_Passed_Authentications 0000815089 10 8 DC=infra,DC=xxxxx, Issuer - Common Name=XXX Devices CA, Issuer - Domain Component=xxx, Issuer - Domain Component=infra, Issuer - Domain Component=xxxxx, Key Usage=0, Key Usage=2, Extended Key Usage - Name=130, Extended Key Usage - OID=1.1.1.1.1.1.1.1.1, Template Name=2.2.2.2.2.2.2.2.2.2.2.2.2.2.2.2.2, Days to Expiry=261, Issuer - Fingerprint SHA-256=a0946a7af563dbc3397893f7313410cb9087fcab14566096e7f1b44992251e62, AKI=33:33:33:33:33:33:33:33:33:33:33:33:33:33:33:33:33:33:33:33, HostIdentityGroup=Endpoint Identity Groups:Unknown, Model Name=9200, Network Device Profile=Cisco, Location=Location#All Locations#EU#France#RENNES, Device Type=Device Type#All Device Types#Wired#Switch#Cisco, IPSEC=IPSEC#Is IPSEC Device#No, distinguishedName=CN=TEST-NAME-01,OU=Laptops,OU=Computers,OU=RUM,DC=xxx,DC=infra,DC=xxxxx, ExternalGroups=S-1-2-3-4-5-6-7,#15",
"event": {
"category": [
"authentication"
],
"type": [
"info"
]
},
"cisco": {
"ise": {
"location": "Location#All Locations#EU#France#RENNES",
"type": "CISE_Passed_Authentications"
}
},
"device": {
"model": {
"name": "9200"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
}
}
{
"message": "0003361015 2 0 2025-05-07 14:29:08.974 +02:00 0051006044 80002 INFO Profiler: Profiler EndPoint profiling event occurred, ConfigVersionId=183, OperatingSystem=Windows 11 Entreprise, EndpointCertainityMetric=50, EndpointIPAddress=1.2.3.4, EndpointMacAddress=AA:BB:CC:DD:EE:FF, EndpointMatchedPolicy=Windows11-Workstation, EndpointOUI=Intel Corporate, EndpointPolicy=Windows11-Workstation, EndpointProperty=chaddr=AA:BB:CC:DD:EE:FF,dhcp-class-identifier=MSFT 5.0,PolicyVersion=24,dhcp-message-type=DHCPREQUEST,EndPointPolicyID=57f40927-3b0a-46b8-9f03-78d47e1383c4,LogicalProfile=,client-fqdn=abcdef.example.local,EndPointVersion=340,FirstCollection=1744718839328,CacheUpdateTime=1746620948973,StaticAssignment=false,NmapScanCount=0,PostureExpiry=,hlen=6,AD-Operating-System=Windows 11 Entreprise,AD-Join-Point=EXAMPLE.LOCAL,PortalUser=,ciaddr=0.0.0.0,BYODRegistration=Unknown,dhcp-requested-address=1.2.3.4,Total Certainty Factor=50,MDMServerID=,",
"event": {
"category": [
"network"
],
"reason": "Profiler EndPoint profiling event occurred",
"type": [
"info"
]
},
"cisco": {
"ise": {
"dhcp": {
"message_type": "DHCPREQUEST",
"requested_address": "1.2.3.4"
}
}
},
"host": {
"os": {
"full": "Windows 11 Entreprise"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"ip": [
"1.2.3.4"
]
},
"rule": {
"id": "57f40927-3b0a-46b8-9f03-78d47e1383c4",
"name": "Windows11-Workstation"
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4",
"mac": "AA:BB:CC:DD:EE:FF"
}
}
{
"message": "Oct 27 15:20:43 HOST-01 CISE_RADIUS_Accounting 0001042079 1 0 2025-10-27 15:20:43.919 +01:00 0015337799 3002 NOTICE Radius-Accounting: RADIUS Accounting watchdog update, ConfigVersionId=11, Device IP Address=1.2.3.4, UserName=user1, NetworkDeviceName=DEVICE-02, User-Name=user1, NAS-IP-Address=1.2.3.4, NAS-Port=42, Service-Type=Framed, Framed-IP-Address=1.2.3.4, Class=CACS:000000000000000000000000:HOST-01/000000000/000000, Called-Station-ID=user1:, Calling-Station-ID=user1, Acct-Status-Type=Interim-Update, Acct-Delay-Time=0, Acct-Input-Octets=921941396, Acct-Output-Octets=0, Acct-Session-Id=0000000000000000, Acct-Authentic=RADIUS, Acct-Session-Time=570009, Acct-Input-Packets=0, Acct-Output-Packets=35, Acct-Input-Gigawords=922518720, Acct-Output-Gigawords=28, Event-Timestamp=1761574843, NAS-Port-Type=Ethernet, cisco-av-pair=audit-session-id=000000000000000000000000, AcsSessionID=HOST-01/000000000/000000, SelectedAccessService=Default Network Access, RequestLatency=2, Step=11004, Step=11017, Step=15049, Step=15008, Step=22094, Step=11005, NetworkDeviceGroups=Location#All Locations#SITE-02, NetworkDeviceGroups=Device Type#All Device Types#SW_Vendor_Site, NetworkDeviceGroups=IPSEC#Is IPSEC Device#No, CPMSessionID=000000000000000000000000, StepLatency=1=0;2=0;3=1;4=0;5=0, TotalAuthenLatency=2, ClientLatency=0, Network Device Profile=Cisco, Location=Location#All Locations#SITE-02, Device Type=Device Type#All Device Types#SW_Vendor_Site, IPSEC=IPSEC#Is IPSEC Device#No,",
"event": {
"category": [
"network"
],
"reason": "RADIUS Accounting watchdog update",
"type": [
"info"
]
},
"cisco": {
"ise": {
"acs_session_id": "HOST-01/000000000/000000",
"audit_session_id": "000000000000000000000000",
"auth_method": "RADIUS",
"device": {
"ip": "1.2.3.4"
},
"location": "IPSEC#Is IPSEC Device#No",
"network": {
"device_name": "DEVICE-02"
},
"observer": {
"interface": {
"type": "Ethernet"
}
},
"policy": "Default Network Access",
"type": "CISE_RADIUS_Accounting"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"related": {
"ip": [
"1.2.3.4"
],
"user": [
"user1"
]
},
"source": {
"address": "1.2.3.4",
"ip": "1.2.3.4"
},
"user": {
"name": "user1"
}
}
{
"message": "CISE_RADIUS_Accounting 0000493168 3 2 NetworkDeviceGroups=IPSEC#Is IPSEC Device#No, NetworkDeviceGroups=Device Type#All Device Types, CPMSessionID=111111111111111111111111, TotalAuthenLatency=2, ClientLatency=0, Model Name=Unknown, Software Version=Unknown, Network Device Profile=Cisco, Location=Location#All Locations#DC1, Device Type=Device Type#All Device Types, IPSEC=IPSEC#Is IPSEC Device#No, #15",
"event": {
"type": [
"info"
]
},
"cisco": {
"ise": {
"location": "Device Type#All Device Types",
"type": "CISE_RADIUS_Accounting"
}
},
"device": {
"model": {
"name": "Unknown"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
}
}
{
"message": "CISE_RADIUS_Accounting 0000493146 3 1 cisco-av-pair=dc-device-name=device_01, cisco-av-pair=dc-device-class-tag=Android-Device:Android, cisco-av-pair=dc-certainty-metric=30, cisco-av-pair=11:11:11:11:11:11:11:11:11:11:11:00:00:00:01:00:00:00:00:00:00:00, cisco-av-pair=dc-protocol-map=9, cisco-av-pair=http-tlv=User-Agent=Useragent/1.6.0 (Linux; U; Android 4.4.2; ALR-H450 Build/KOT49H), cisco-av-pair=dhcp-option=host-name=device_01, cisco-av-pair=dhcp-option=dhcp-class-identifier=dhcpcd-5.5.6, cisco-av-pair=dhcp-option=dhcp-parameter-request-list=1, 33, 3, 6, 15, 28, 51, 58, 59, cisco-av-pair=audit-session-id=6BF9680A001DC135219AFBFD, cisco-av-pair=vlan-id=2001, cisco-av-pair=method=mab, cisco-av-pair=cts:security-group-tag=0006, cisco-av-pair=cisco-wlan-ssid=C-Guest, cisco-av-pair=wlan-profile-name=C-Guest-CWA, Airespace-Wlan-Id=40, AcsSessionID=HOST_01/549140223/473883, SelectedAccessService=Default Network Access,#15",
"event": {
"type": [
"info"
]
},
"cisco": {
"ise": {
"acs_session_id": "HOST_01/549140223/473883",
"audit_session_id": "6BF9680A001DC135219AFBFD",
"auth_method": "mab",
"certainty_metric": "30",
"device": {
"model": {
"class": "Android-Device:Android"
}
},
"policy": "Default Network Access",
"ssid": "C-Guest",
"type": "CISE_RADIUS_Accounting",
"vlan_id": "2001",
"wlan_id": "C-Guest-CWA"
}
},
"device": {
"model": {
"name": "device_01"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"user_agent": {
"device": {
"name": "ALR-H450"
},
"name": "Android",
"original": "Useragent/1.6.0 (Linux; U; Android 4.4.2; ALR-H450 Build/KOT49H)",
"os": {
"name": "Android",
"version": "4.4.2"
},
"version": "4.4.2"
}
}
{
"message": "0000050179 9 4 Subject - Common Name=EXAMPLE, Subject Alternative Name=EXAMPLE.intra.example.net, Subject - Organization Unit=Std, Subject - Organization Unit=Abc, Subject - Organization Unit=Def, CPMSessionID=REDACTED, EndPointMACAddress=02-00-00-00-00-01, PostureAssessmentStatus=NotApplicable, EndPointMatchedProfile=Unknown, ISEPolicySetName=Policy 802.1X, IdentitySelectionMatchedRule=Default,",
"event": {
"type": [
"info"
]
},
"cisco": {
"ise": {
"device": {
"profile": "Unknown"
},
"policy": "Policy 802.1X"
}
},
"observer": {
"product": "Cisco ISE",
"vendor": "Cisco"
},
"rule": {
"name": "Policy 802.1X"
},
"source": {
"mac": "02:00:00:00:00:01"
},
"tls": {
"client": {
"x509": {
"subject": {
"alternative_names": [
"EXAMPLE.intra.example.net"
],
"common_name": "EXAMPLE",
"organizational_unit": [
"Abc",
"Def",
"Std"
]
}
}
}
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
cisco.ise.acs_session_id |
keyword |
|
cisco.ise.audit_session_id |
keyword |
|
cisco.ise.auth_method |
keyword |
|
cisco.ise.certainty_metric |
keyword |
|
cisco.ise.cmd_line |
keyword |
|
cisco.ise.config_action |
keyword |
The action in a configuration events. (Added, Changed, Deleted) |
cisco.ise.config_object.name |
keyword |
The name of the object in the conf events |
cisco.ise.config_object.type |
keyword |
The type of the objection in the conf events |
cisco.ise.device.ip |
keyword |
|
cisco.ise.device.model.class |
keyword |
|
cisco.ise.device.profile |
keyword |
|
cisco.ise.dhcp.message_type |
keyword |
DHCP message type |
cisco.ise.dhcp.parameter_request_list |
keyword |
DHCP parameter request list |
cisco.ise.dhcp.requested_address |
keyword |
DHCP requested address |
cisco.ise.event.outcome |
keyword |
The outcome of the event |
cisco.ise.is_machine_identity |
boolean |
|
cisco.ise.location |
keyword |
|
cisco.ise.nas.identifier |
keyword |
|
cisco.ise.network.device_name |
keyword |
The network device name |
cisco.ise.observer.interface.name |
keyword |
|
cisco.ise.observer.interface.type |
keyword |
|
cisco.ise.policy |
keyword |
|
cisco.ise.privilege_level |
keyword |
|
cisco.ise.ssid |
keyword |
|
cisco.ise.step_data.5_code |
keyword |
The step data code |
cisco.ise.type |
keyword |
The type of Cisco ISE event |
cisco.ise.vlan_id |
keyword |
|
cisco.ise.wlan_id |
keyword |
|
destination.domain |
keyword |
The domain name of the destination. |
destination.ip |
ip |
IP address of the destination. |
destination.mac |
keyword |
MAC address of the destination. |
destination.port |
long |
Port of the destination. |
dns.question.registered_domain |
keyword |
The highest registered domain, stripped of the subdomain. |
event.category |
keyword |
Event category. The second categorization field in the hierarchy. |
event.outcome |
keyword |
The outcome of the event. The lowest level categorization field in the hierarchy. |
event.reason |
keyword |
Reason why this event happened, according to the source |
event.type |
keyword |
Event type. The third categorization field in the hierarchy. |
host.name |
keyword |
Name of the host. |
host.os.full |
keyword |
Operating system name, including the version or code name. |
network.protocol |
keyword |
Application protocol name. |
observer.product |
keyword |
The product name of the observer. |
observer.vendor |
keyword |
Vendor name of the observer. |
rule.id |
keyword |
Rule ID |
rule.name |
keyword |
Rule name |
source.domain |
keyword |
The domain name of the source. |
source.ip |
ip |
IP address of the source. |
source.mac |
keyword |
MAC address of the source. |
tls.client.x509.issuer.common_name |
keyword |
List of common name (CN) of issuing certificate authority. |
tls.client.x509.issuer.country |
keyword |
List of country (C) codes |
tls.client.x509.issuer.locality |
keyword |
List of locality names (L) |
tls.client.x509.issuer.organization |
keyword |
List of organizations (O) of issuing certificate authority. |
tls.client.x509.issuer.organizational_unit |
keyword |
List of organizational units (OU) of issuing certificate authority. |
tls.client.x509.subject.alternative_names |
keyword |
|
tls.client.x509.subject.common_name |
keyword |
List of common names (CN) of subject. |
tls.client.x509.subject.organizational_unit |
keyword |
List of organizational units (OU) of subject. |
url.original |
wildcard |
Unmodified original url as seen in the event source. |
user.domain |
keyword |
Name of the directory the user is a member of. |
user.name |
keyword |
Short name or login of the user. |
user_agent.original |
keyword |
Unparsed user_agent string. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.